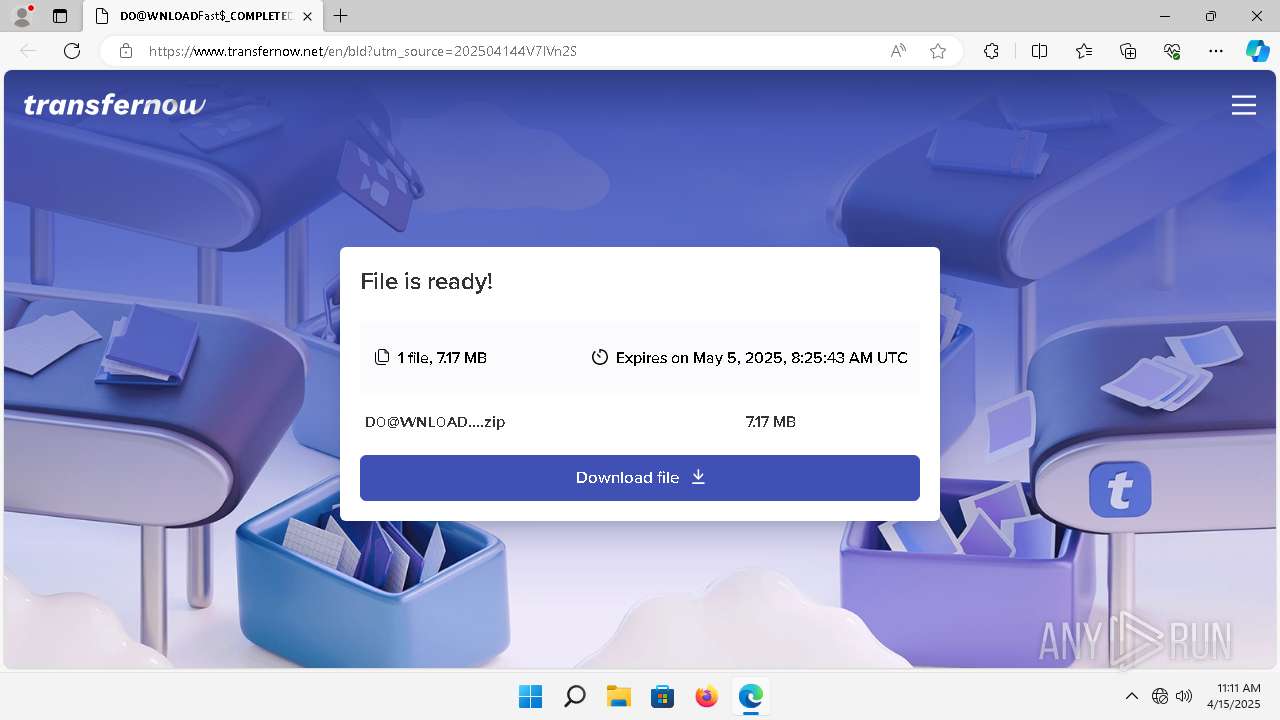
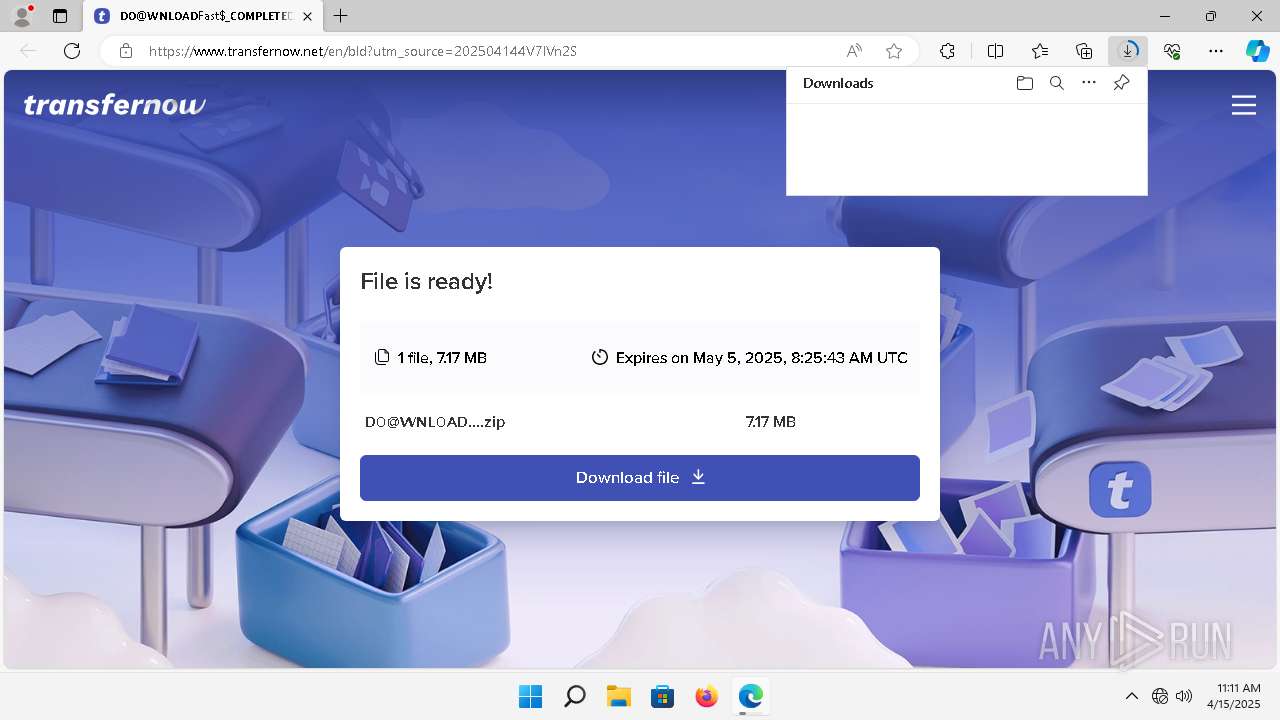
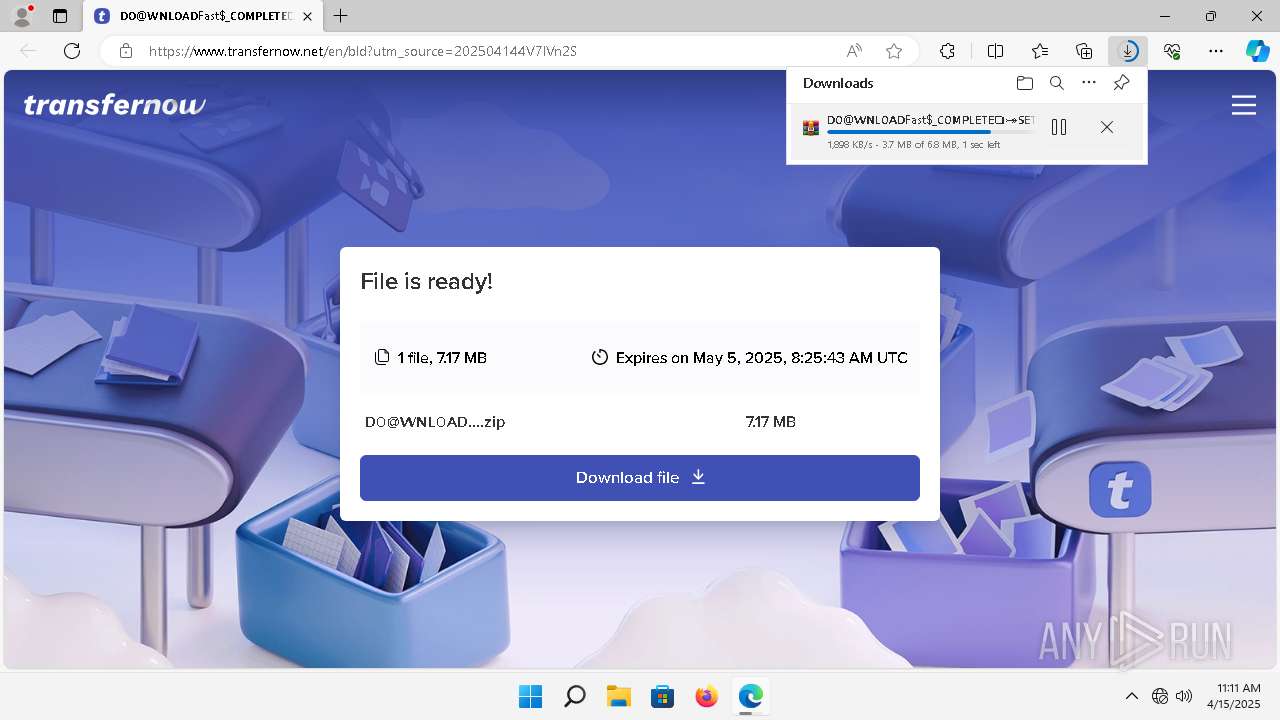
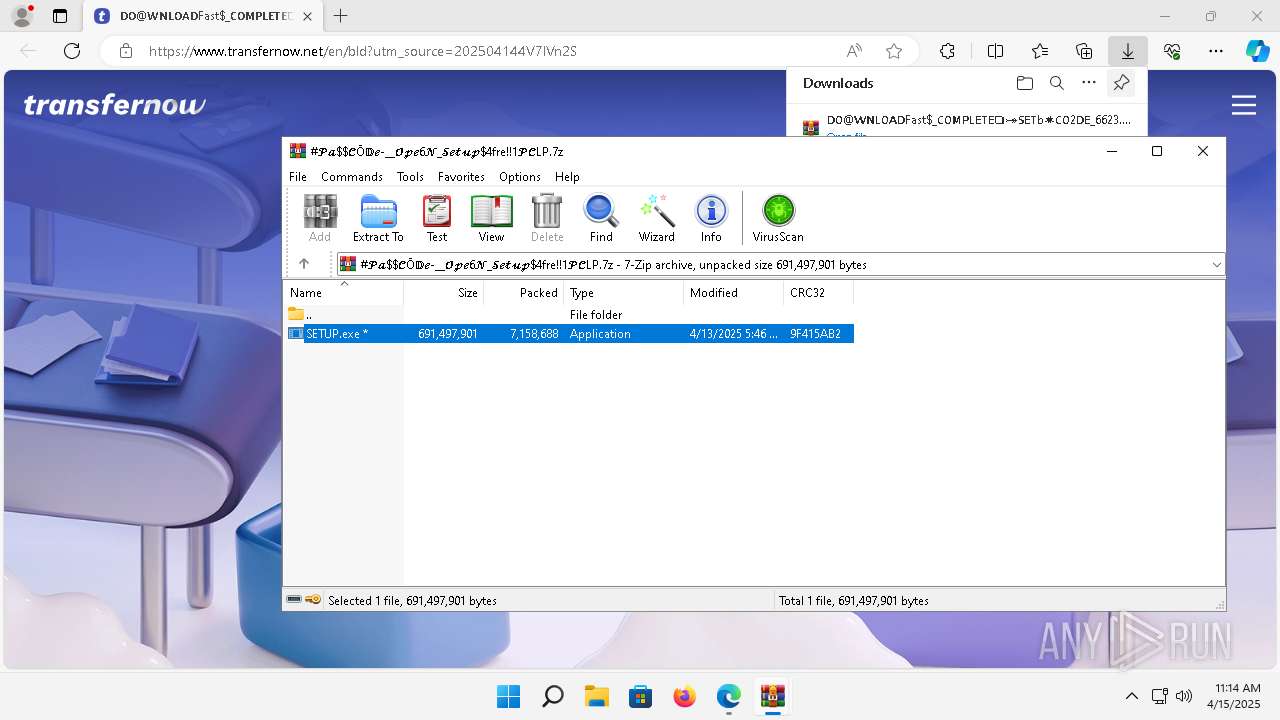
| URL: | https://www.transfernow.net/dl/202504144V7lVn2S |
| Full analysis: | https://app.any.run/tasks/159523a6-b0c1-4e45-94f6-f5e0148de232 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | April 15, 2025, 11:11:24 |
| OS: | Windows 11 Professional (build: 22000, 64 bit) |
| Tags: | |
| Indicators: | |
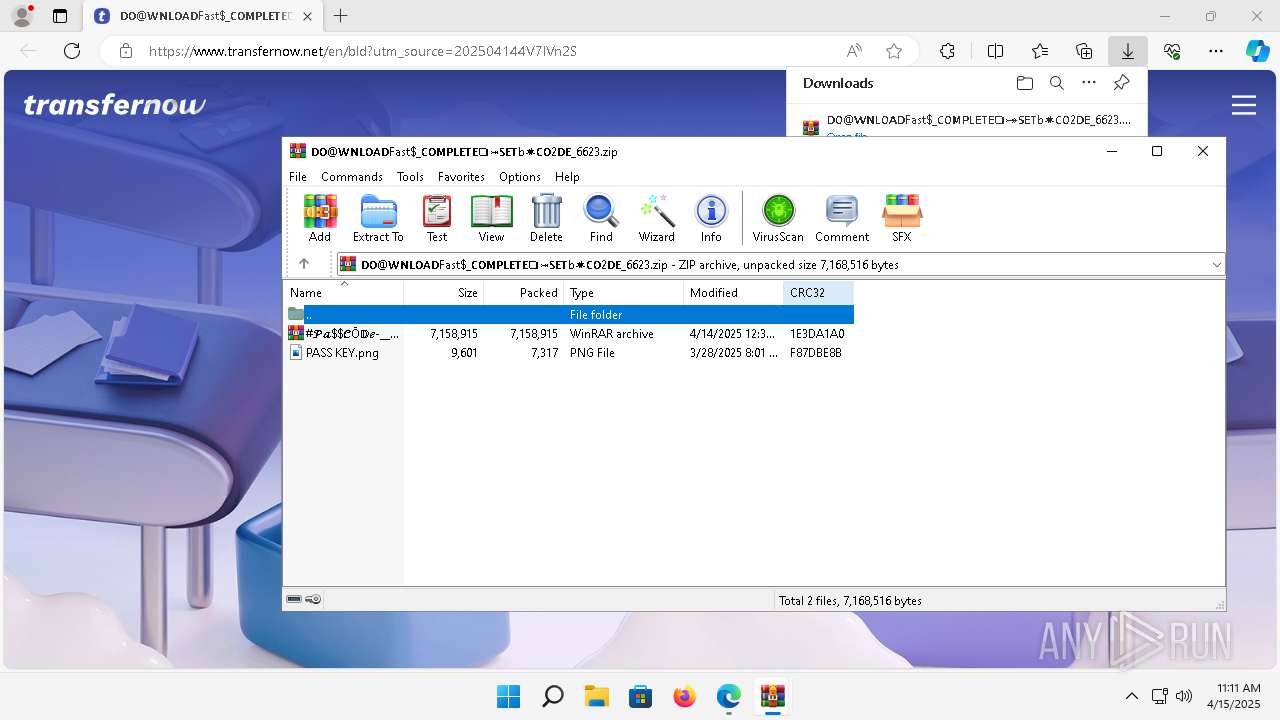
| MD5: | 2B4D1DBB48B7ABDD6FF936727795B236 |
| SHA1: | BA18BF3ABA8EB47986C0CBAC40B3875B5EB6B91E |
| SHA256: | FAEE83110FF50B7527092CD0877A1B12AE01E8DCED6EE602A588CF5A28088427 |
| SSDEEP: | 3:N8DSLIbLAgJMGRUmzKn:2OLW4b |
MALICIOUS
Executing a file with an untrusted certificate
- SETUP.exe (PID: 6852)
- KYT0UOYU18W8UHJBTK.exe (PID: 6636)
- KYT0UOYU18W8UHJBTK.exe (PID: 3420)
LUMMA mutex has been found
- SETUP.exe (PID: 6852)
Steals credentials from Web Browsers
- SETUP.exe (PID: 6852)
LUMMA has been detected (YARA)
- SETUP.exe (PID: 6852)
Actions looks like stealing of personal data
- SETUP.exe (PID: 6852)
Changes the autorun value in the registry
- reg.exe (PID: 6232)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 5932)
- WinRAR.exe (PID: 4292)
- WinRAR.exe (PID: 6528)
Application launched itself
- WinRAR.exe (PID: 5932)
- KYT0UOYU18W8UHJBTK.exe (PID: 6636)
Reads the Internet Settings
- SETUP.exe (PID: 6852)
Searches for installed software
- SETUP.exe (PID: 6852)
Reads settings of System Certificates
- SETUP.exe (PID: 6852)
- KYT0UOYU18W8UHJBTK.exe (PID: 3420)
Executable content was dropped or overwritten
- SETUP.exe (PID: 6852)
- KYT0UOYU18W8UHJBTK.exe (PID: 3420)
There is functionality for taking screenshot (YARA)
- KYT0UOYU18W8UHJBTK.exe (PID: 6636)
- KYT0UOYU18W8UHJBTK.exe (PID: 3420)
Starts CMD.EXE for commands execution
- KYT0UOYU18W8UHJBTK.exe (PID: 3420)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 6824)
Connects to unusual port
- KYT0UOYU18W8UHJBTK.exe (PID: 3420)
INFO
Reads Environment values
- identity_helper.exe (PID: 6612)
Application launched itself
- msedge.exe (PID: 4680)
Checks supported languages
- identity_helper.exe (PID: 6612)
- SETUP.exe (PID: 6852)
- KYT0UOYU18W8UHJBTK.exe (PID: 6636)
- KYT0UOYU18W8UHJBTK.exe (PID: 3420)
Reads the computer name
- identity_helper.exe (PID: 6612)
- KYT0UOYU18W8UHJBTK.exe (PID: 6636)
- SETUP.exe (PID: 6852)
- KYT0UOYU18W8UHJBTK.exe (PID: 3420)
Reads the software policy settings
- SETUP.exe (PID: 6852)
- KYT0UOYU18W8UHJBTK.exe (PID: 3420)
Create files in a temporary directory
- SETUP.exe (PID: 6852)
- KYT0UOYU18W8UHJBTK.exe (PID: 6636)
The sample compiled with english language support
- SETUP.exe (PID: 6852)
- KYT0UOYU18W8UHJBTK.exe (PID: 3420)
Compiled with Borland Delphi (YARA)
- KYT0UOYU18W8UHJBTK.exe (PID: 6636)
- KYT0UOYU18W8UHJBTK.exe (PID: 3420)
Creates files in the program directory
- KYT0UOYU18W8UHJBTK.exe (PID: 3420)
Reads Microsoft Office registry keys
- msedge.exe (PID: 4680)
Drops encrypted JS script (Microsoft Script Encoder)
- KYT0UOYU18W8UHJBTK.exe (PID: 3420)
Reads the machine GUID from the registry
- KYT0UOYU18W8UHJBTK.exe (PID: 3420)
Detects GO elliptic curve encryption (YARA)
- KYT0UOYU18W8UHJBTK.exe (PID: 3420)
Application based on Golang
- KYT0UOYU18W8UHJBTK.exe (PID: 3420)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
157
Monitored processes
52
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 600 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=3880 --field-trial-handle=1940,i,11274810972857123733,15522294254598543043,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.92 Modules
| |||||||||||||||
| 804 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2476 --field-trial-handle=1940,i,11274810972857123733,15522294254598543043,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.92 Modules
| |||||||||||||||
| 1916 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --mojo-platform-channel-handle=4992 --field-trial-handle=1940,i,11274810972857123733,15522294254598543043,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.92 Modules
| |||||||||||||||
| 2320 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.129 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.92 --initial-client-data=0x2f4,0x2f8,0x2fc,0x2ec,0x304,0x7ffc733a5fd8,0x7ffc733a5fe4,0x7ffc733a5ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.92 Modules
| |||||||||||||||
| 2460 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=3328 --field-trial-handle=1940,i,11274810972857123733,15522294254598543043,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.92 Modules
| |||||||||||||||
| 2560 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5568 --field-trial-handle=1940,i,11274810972857123733,15522294254598543043,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.92 Modules
| |||||||||||||||
| 2720 | \??\C:\Windows\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2864 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4980 --field-trial-handle=1940,i,11274810972857123733,15522294254598543043,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.92 Modules
| |||||||||||||||
| 3268 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=1936 --field-trial-handle=1940,i,11274810972857123733,15522294254598543043,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.92 Modules
| |||||||||||||||
| 3420 | C:\Users\admin\AppData\Local\Temp\KYT0UOYU18W8UHJBTK.exe | C:\Users\admin\AppData\Local\Temp\KYT0UOYU18W8UHJBTK.exe | KYT0UOYU18W8UHJBTK.exe | ||||||||||||
User: admin Company: Embarcadero Technologies, Inc. Integrity Level: MEDIUM Description: Embarcadero FMX Style Viewer Version: 17.0.4469.47716 Modules
| |||||||||||||||
Total events
20 059
Read events
19 902
Write events
154
Delete events
3
Modification events
| (PID) Process: | (4928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (4928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (4928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (4928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (4928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (4928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (4928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
Executable files
17
Suspicious files
422
Text files
51
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4680 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\parcel_tracking_db\LOG.old~RF163974.TMP | — | |
MD5:— | SHA256:— | |||
| 4680 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4680 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\discounts_db\LOG.old~RF163983.TMP | — | |
MD5:— | SHA256:— | |||
| 4680 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4680 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\PersistentOriginTrials\LOG.old~RF163983.TMP | — | |
MD5:— | SHA256:— | |||
| 4680 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4680 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF163983.TMP | — | |
MD5:— | SHA256:— | |||
| 4680 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4680 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\commerce_subscription_db\LOG.old~RF163993.TMP | — | |
MD5:— | SHA256:— | |||
| 4680 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
34
TCP/UDP connections
81
DNS requests
76
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3640 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2564 | smartscreen.exe | GET | 200 | 208.89.74.19:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?72786ad38ba5abb8 | unknown | — | — | whitelisted |
2564 | smartscreen.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4712 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1744950976&P2=404&P3=2&P4=Q9gMDLm%2ffI0QexISux8KrV5JyZDHiC4CStklzaSpSm0efRFVRE8QBriO8FksHtGZZ5Ge7Bw%2bZmzm%2fD3q9C9jig%3d%3d | unknown | — | — | whitelisted |
1352 | svchost.exe | GET | 200 | 88.221.110.216:80 | http://www.msftconnecttest.com/connecttest.txt | unknown | — | — | whitelisted |
2768 | svchost.exe | GET | 200 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?b5c209eb39f9a373 | unknown | — | — | whitelisted |
4712 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1744950976&P2=404&P3=2&P4=Q9gMDLm%2ffI0QexISux8KrV5JyZDHiC4CStklzaSpSm0efRFVRE8QBriO8FksHtGZZ5Ge7Bw%2bZmzm%2fD3q9C9jig%3d%3d | unknown | — | — | whitelisted |
4712 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1744950976&P2=404&P3=2&P4=Q9gMDLm%2ffI0QexISux8KrV5JyZDHiC4CStklzaSpSm0efRFVRE8QBriO8FksHtGZZ5Ge7Bw%2bZmzm%2fD3q9C9jig%3d%3d | unknown | — | — | whitelisted |
2768 | svchost.exe | GET | 200 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/pinrulesstl.cab?74f19306e9a7f92f | unknown | — | — | whitelisted |
2768 | svchost.exe | GET | 200 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?e8295883656f7dad | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1352 | svchost.exe | 88.221.110.147:80 | — | Akamai International B.V. | DE | unknown |
2564 | smartscreen.exe | 4.175.223.124:443 | checkappexec.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2564 | smartscreen.exe | 208.89.74.19:80 | ctldl.windowsupdate.com | — | US | whitelisted |
2564 | smartscreen.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
3952 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3820 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4680 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3820 | msedge.exe | 172.67.72.33:443 | www.transfernow.net | CLOUDFLARENET | US | unknown |
3820 | msedge.exe | 172.217.23.97:443 | clients2.googleusercontent.com | GOOGLE | US | whitelisted |
3820 | msedge.exe | 150.171.30.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
checkappexec.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
www.transfernow.net |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
clients2.google.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3820 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare R2 Storage (r2 .cloudflarestorage .com) |
3820 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare R2 Storage (r2 .cloudflarestorage .com) |
1352 | svchost.exe | Misc activity | ET INFO Microsoft Connection Test |
1664 | svchost.exe | Misc activity | ET TA_ABUSED_SERVICES DNS Query to Commonly Actor Abused Online Service (data-seed-prebsc-1-s1 .binance .org) |
3420 | KYT0UOYU18W8UHJBTK.exe | Misc activity | ET TA_ABUSED_SERVICES Observed Commonly Actor Abused Online Service Domain (data-seed-prebsc-1-s1 .binance .org in TLS SNI) |