| URL: | https://cdn.discordapp.com/attachments/1281877458529943602/1317418250962735124/Xeno.exe?ex=675e9cdb&is=675d4b5b&hm=ce54a465ad6720edf152b7d709e89e7ee0412d0f736ff312cf222e8917c6c56a& |
| Full analysis: | https://app.any.run/tasks/91e06a59-d672-4eac-bb27-c5be85308baa |
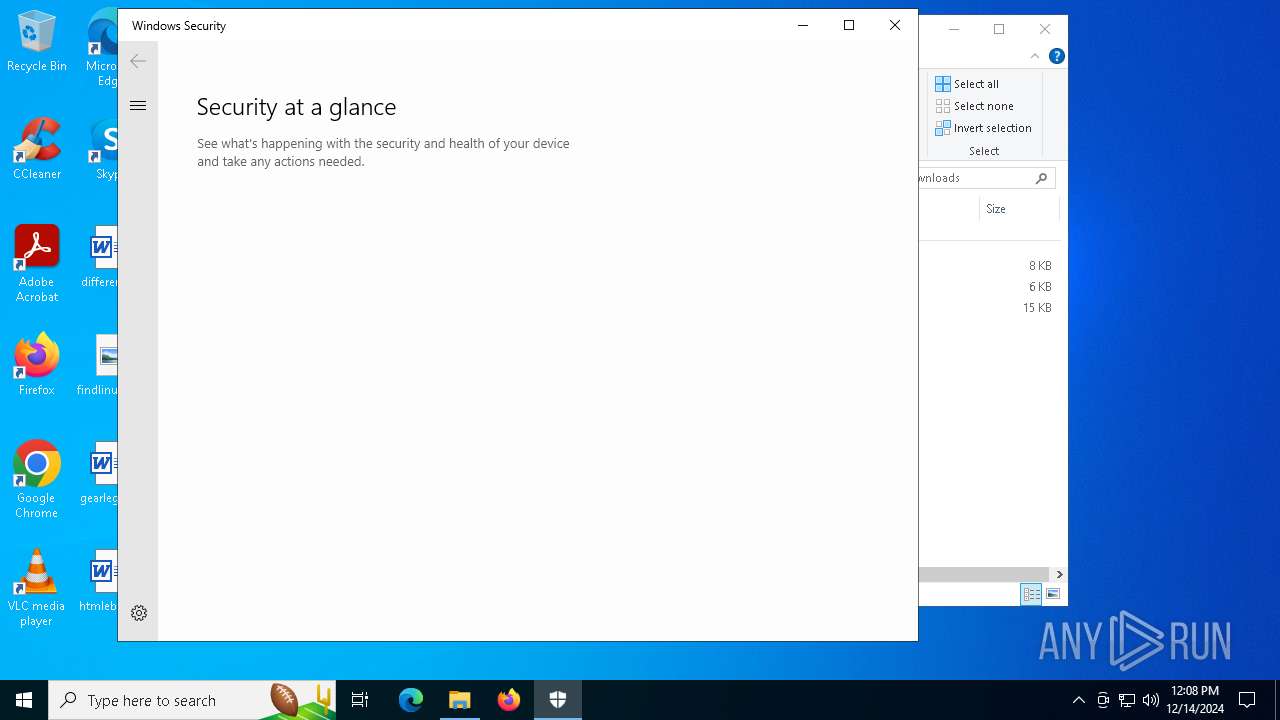
| Verdict: | Malicious activity |
| Threats: | Blank Grabber is an infostealer written in Python. It is designed to steal a wide array of data, such as browser login credentials, crypto wallets, Telegram sessions, and Discord tokens. It is an open-source malware, with its code available on GitHub and regularly receiving updates. Blank Grabber builder’s simple interface lets threat actors even with basic skills to deploy it and conduct attacks. |
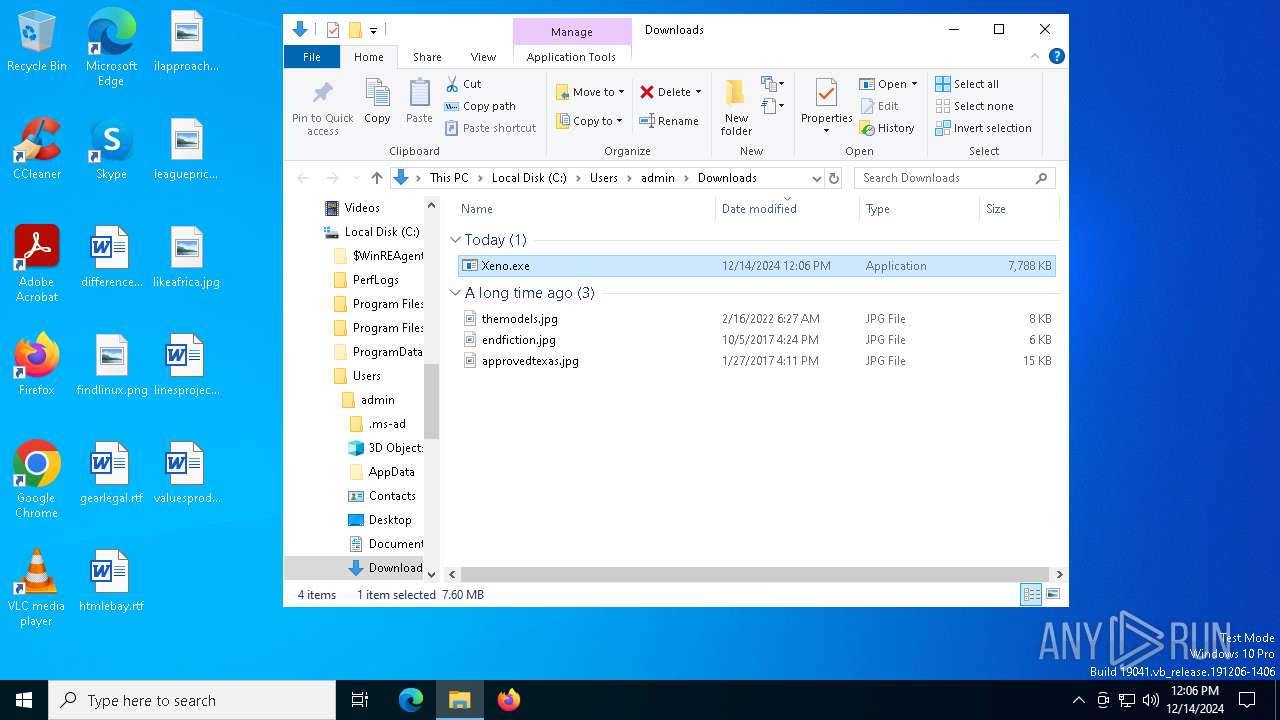
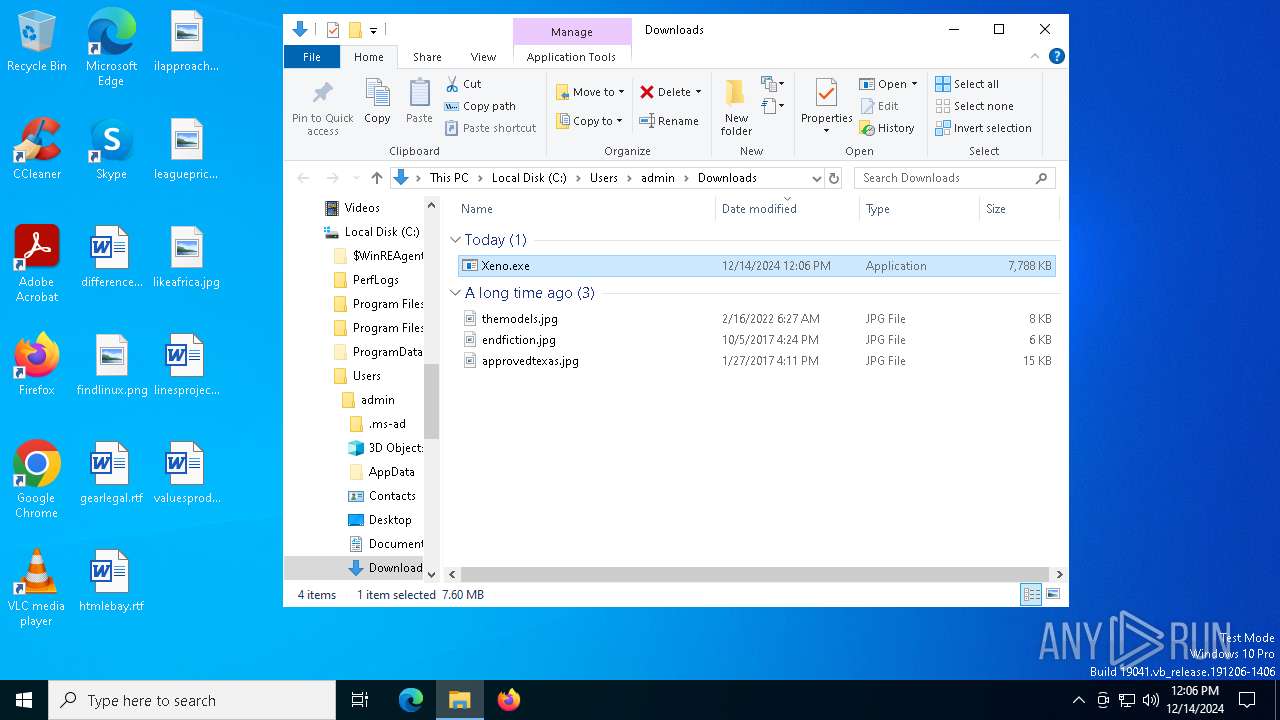
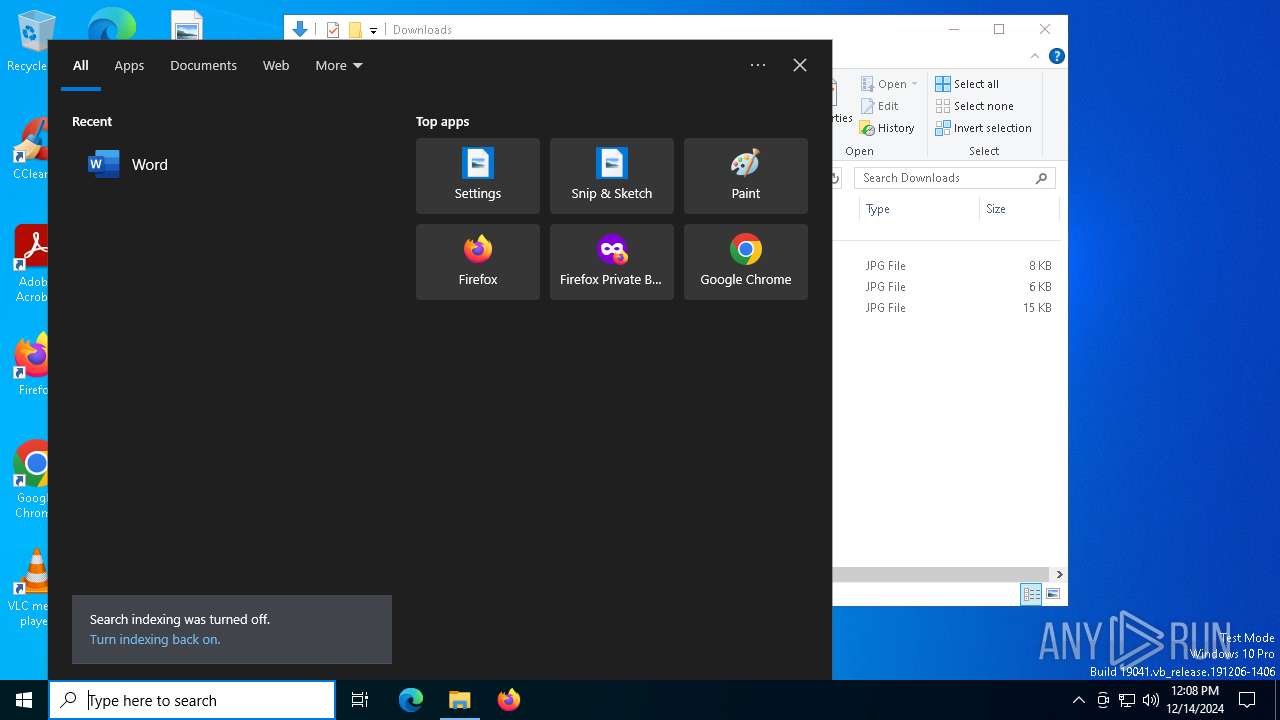
| Analysis date: | December 14, 2024, 12:06:27 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 4254CB555D8DBE5396A3E62E9D119988 |
| SHA1: | 38F407E305DE54C48E910E845919142C32D8336F |
| SHA256: | FAE370E9C60FC4B00B685EDD80CB20C239FF4D5905EDAB268E2602C2EE08D2C6 |
| SSDEEP: | 3:N8cCWdy6//OZzdCtRWZXKUWUlA0SWQ+mbaVP0dSYXQARIXVAPwRwwRUBfkXmHTqn:2cry6X2kjWZaUTlArXrYYXQAoZRfyBf0 |
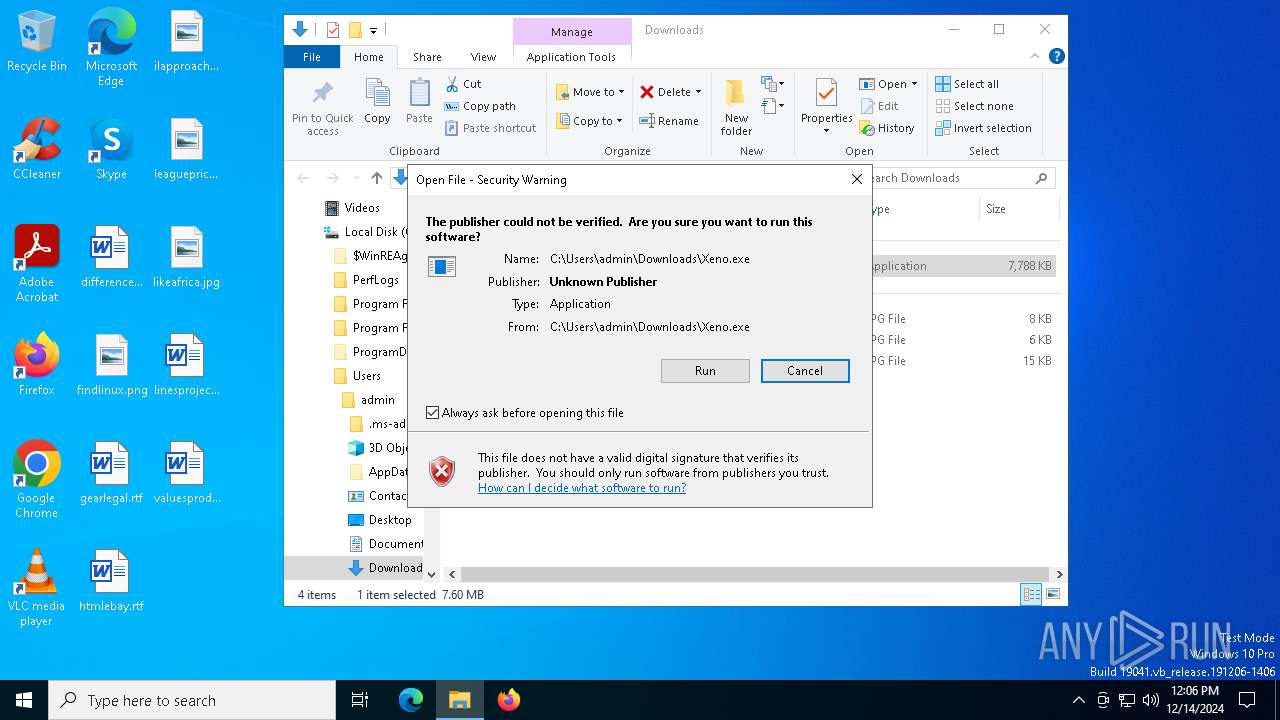
MALICIOUS
Executing a file with an untrusted certificate
- Xeno.exe (PID: 3988)
- Xeno.exe (PID: 6420)
- Xeno.exe (PID: 6176)
- Xeno.exe (PID: 7316)
BlankGrabber has been detected
- Xeno.exe (PID: 3988)
- Xeno.exe (PID: 6420)
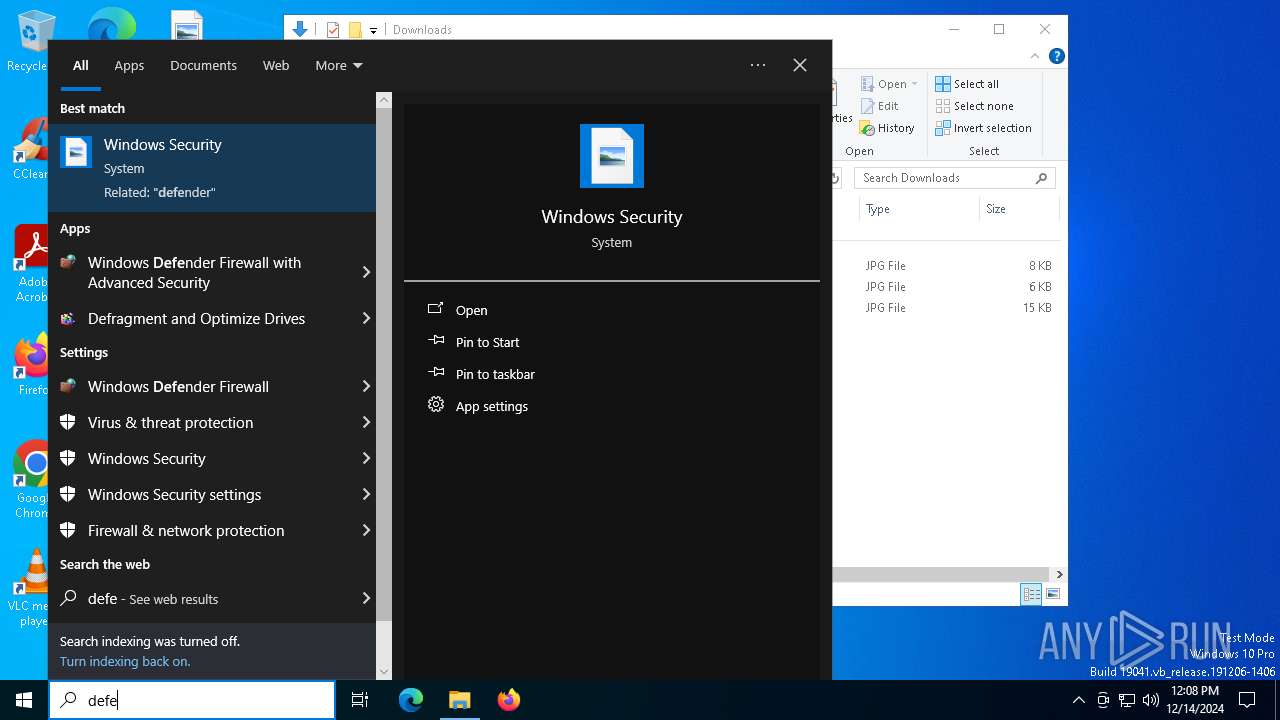
Bypass User Account Control (ComputerDefaults)
- ComputerDefaults.exe (PID: 6508)
Antivirus name has been found in the command line (generic signature)
- cmd.exe (PID: 6220)
- MpCmdRun.exe (PID: 3620)
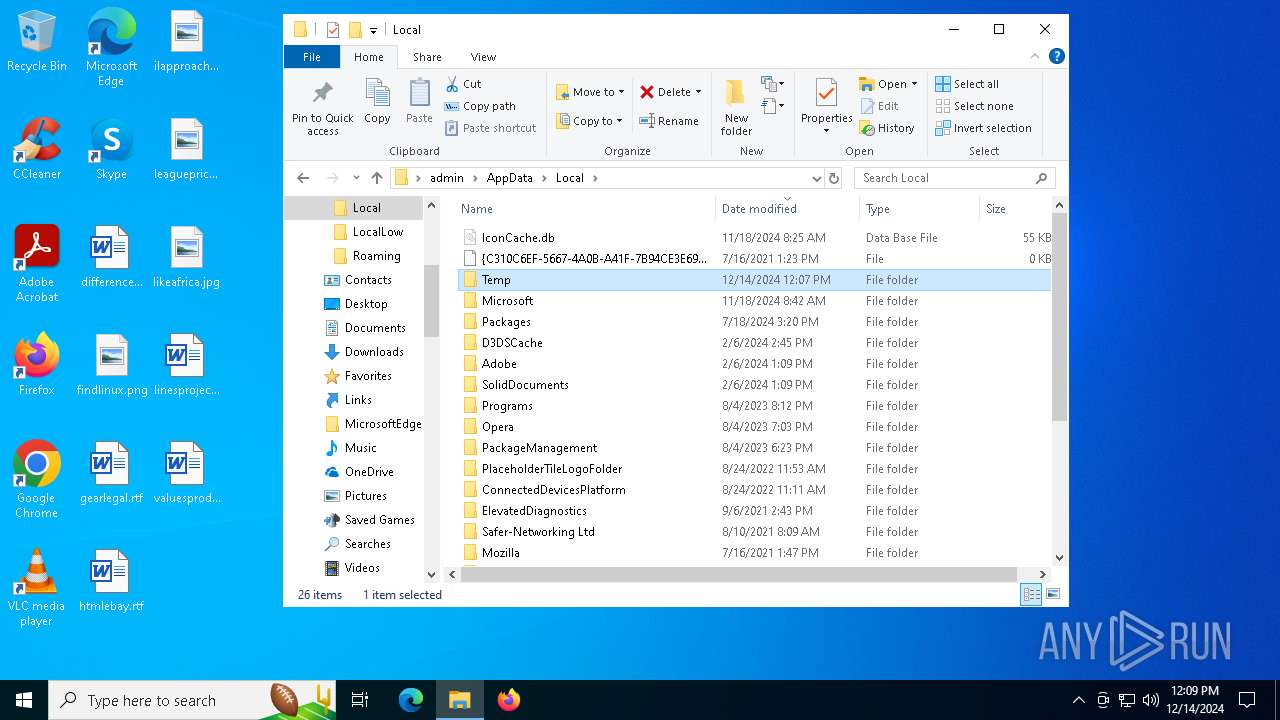
Create files in the Startup directory
- Xeno.exe (PID: 6176)
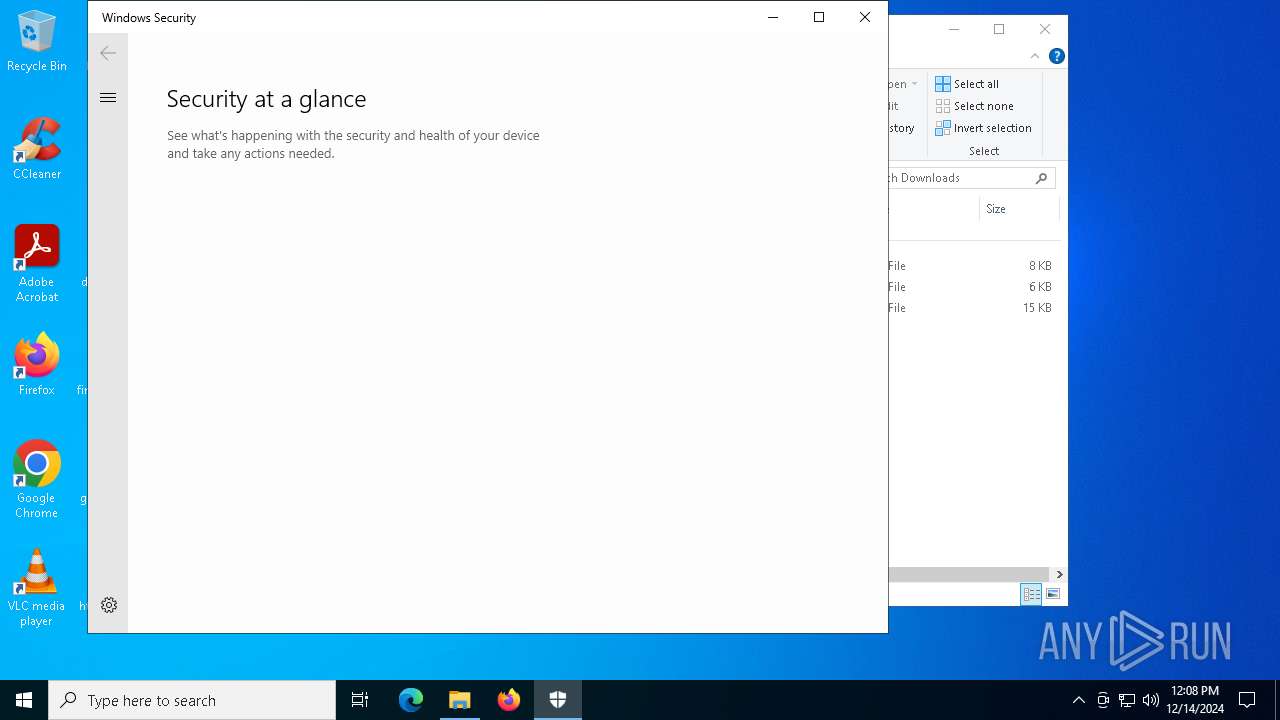
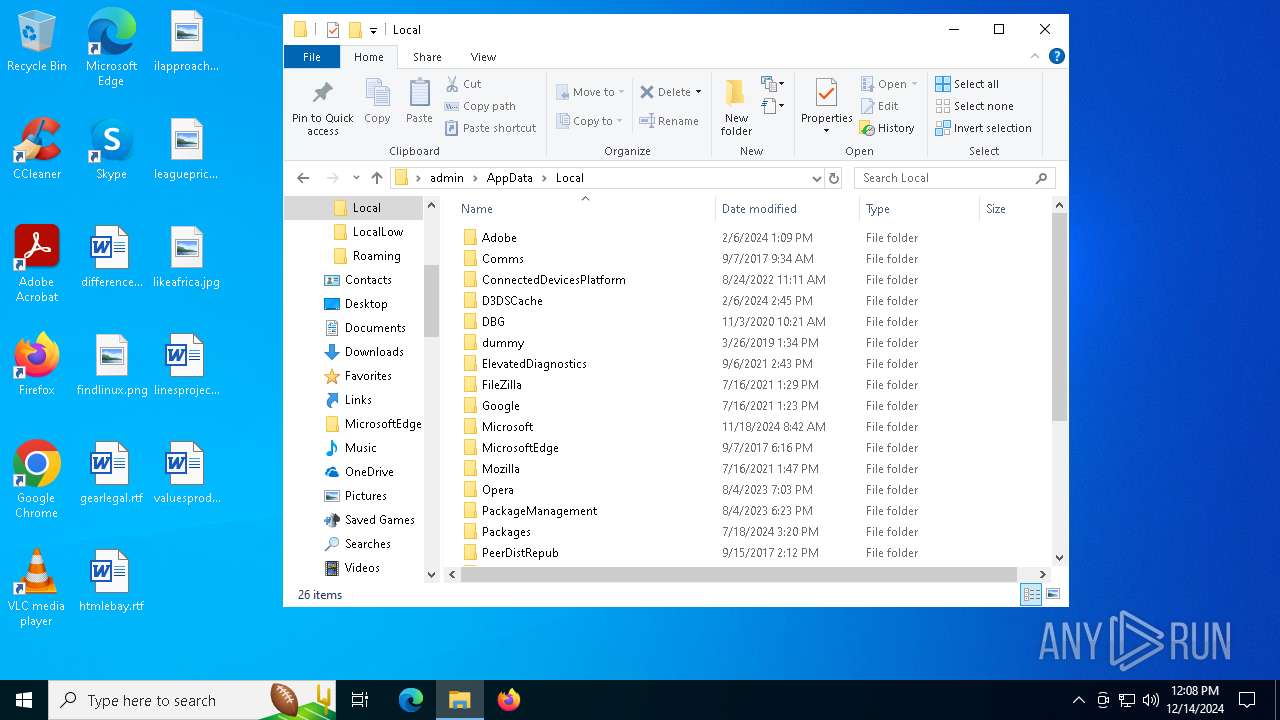
Changes Controlled Folder Access settings
- powershell.exe (PID: 7548)
Bypass User Account Control (Modify registry)
- reg.exe (PID: 836)
Adds path to the Windows Defender exclusion list
- Xeno.exe (PID: 6176)
- cmd.exe (PID: 6204)
- cmd.exe (PID: 6824)
Changes settings for protection against network attacks (IPS)
- powershell.exe (PID: 7548)
Changes settings for sending potential threat samples to Microsoft servers
- powershell.exe (PID: 7548)
Changes settings for checking scripts for malicious actions
- powershell.exe (PID: 7548)
Changes settings for real-time protection
- powershell.exe (PID: 7548)
Changes antivirus protection settings for downloading files from the Internet (IOAVProtection)
- powershell.exe (PID: 7548)
Changes settings for reporting to Microsoft Active Protection Service (MAPS)
- powershell.exe (PID: 7548)
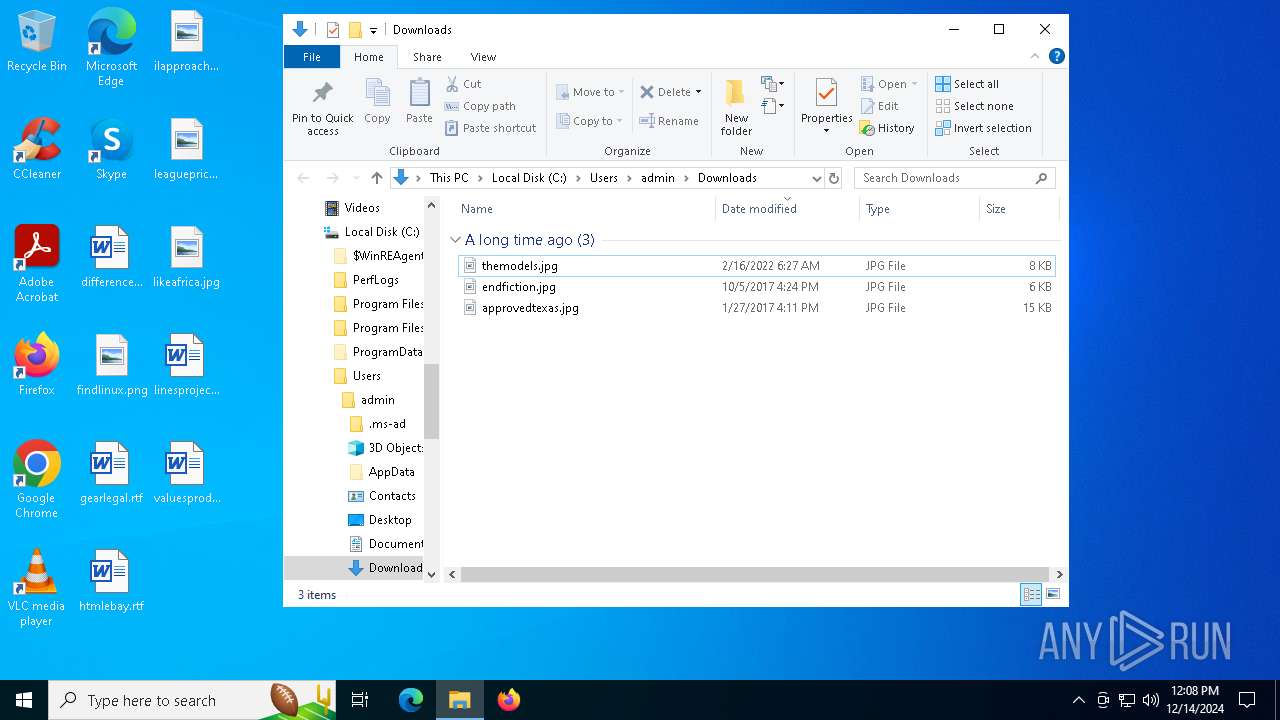
Actions looks like stealing of personal data
- Xeno.exe (PID: 6176)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 5460)
Bypass execution policy to execute commands
- powershell.exe (PID: 6520)
Resets Windows Defender malware definitions to the base version
- MpCmdRun.exe (PID: 3620)
Steals credentials from Web Browsers
- Xeno.exe (PID: 6176)
BLANKGRABBER has been detected (SURICATA)
- Xeno.exe (PID: 6176)
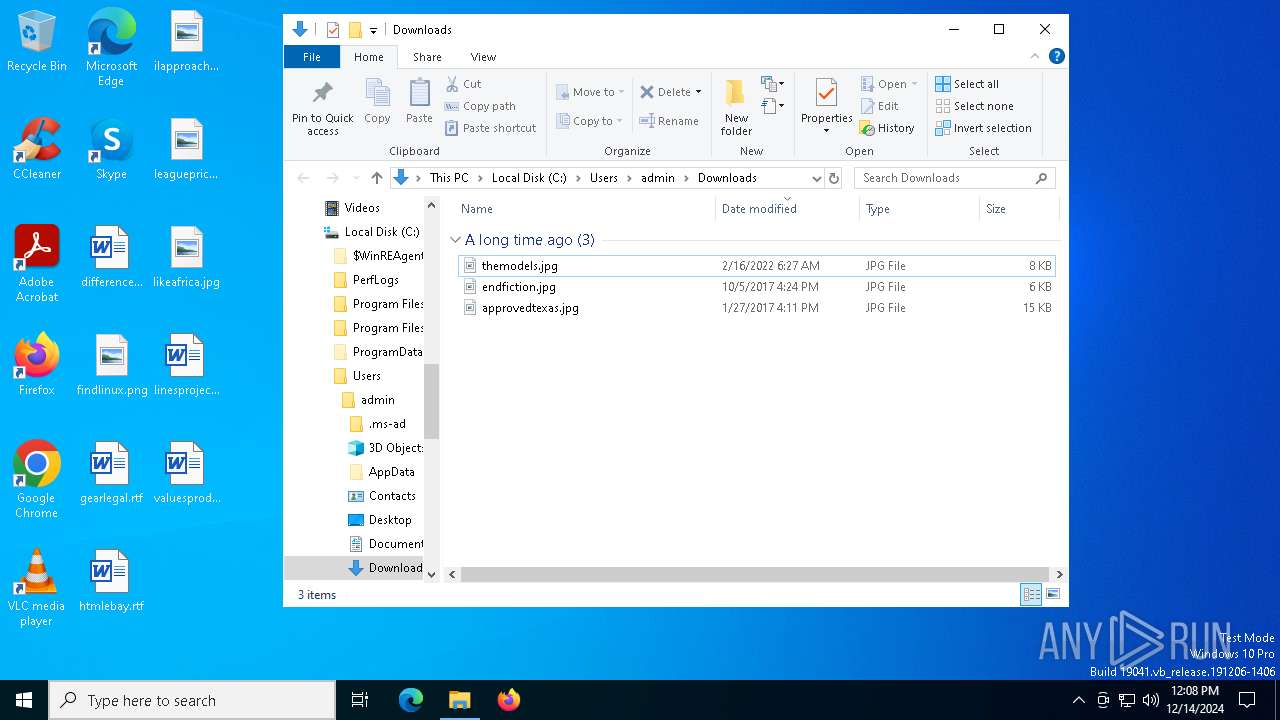
Starts CMD.EXE for self-deleting
- Xeno.exe (PID: 6176)
SUSPICIOUS
Process drops legitimate windows executable
- msedge.exe (PID: 6316)
- Xeno.exe (PID: 3988)
- msedge.exe (PID: 5340)
- Xeno.exe (PID: 6420)
- Xeno.exe (PID: 6176)
Creates file in the systems drive root
- explorer.exe (PID: 4488)
Discord domain found in command line (probably downloading payload)
- msedge.exe (PID: 5340)
Process drops python dynamic module
- Xeno.exe (PID: 3988)
- Xeno.exe (PID: 6420)
Executable content was dropped or overwritten
- Xeno.exe (PID: 3988)
- Xeno.exe (PID: 6420)
- Xeno.exe (PID: 6176)
- csc.exe (PID: 6316)
Application launched itself
- Xeno.exe (PID: 3988)
- Xeno.exe (PID: 6420)
Starts CMD.EXE for commands execution
- Xeno.exe (PID: 7316)
- Xeno.exe (PID: 6176)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 7248)
- cmd.exe (PID: 7188)
- cmd.exe (PID: 4816)
Uses WEVTUTIL.EXE to query events from a log or log file
- cmd.exe (PID: 8116)
- cmd.exe (PID: 6440)
Changes default file association
- reg.exe (PID: 836)
The process drops C-runtime libraries
- Xeno.exe (PID: 6420)
- Xeno.exe (PID: 3988)
Found strings related to reading or modifying Windows Defender settings
- Xeno.exe (PID: 7316)
- Xeno.exe (PID: 6176)
Script disables Windows Defender's IPS
- cmd.exe (PID: 6220)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6220)
- cmd.exe (PID: 6204)
- cmd.exe (PID: 6824)
- cmd.exe (PID: 7232)
- cmd.exe (PID: 5460)
- cmd.exe (PID: 2076)
- cmd.exe (PID: 6416)
- cmd.exe (PID: 3928)
- cmd.exe (PID: 1740)
Script disables Windows Defender's real-time protection
- cmd.exe (PID: 6220)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 6248)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 6204)
- cmd.exe (PID: 6824)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 4932)
- cmd.exe (PID: 7536)
Get information on the list of running processes
- cmd.exe (PID: 7212)
- cmd.exe (PID: 6744)
- cmd.exe (PID: 4708)
- Xeno.exe (PID: 6176)
Starts application with an unusual extension
- cmd.exe (PID: 7188)
- cmd.exe (PID: 7332)
- cmd.exe (PID: 6684)
- cmd.exe (PID: 7192)
- cmd.exe (PID: 5112)
- cmd.exe (PID: 7216)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 5460)
Base64-obfuscated command line is found
- cmd.exe (PID: 5460)
Uses NETSH.EXE to obtain data on the network
- cmd.exe (PID: 6320)
Uses SYSTEMINFO.EXE to read the environment
- cmd.exe (PID: 3260)
Accesses antivirus product name via WMI (SCRIPT)
- WMIC.exe (PID: 7992)
CSC.EXE is used to compile C# code
- csc.exe (PID: 6316)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 4076)
- cmd.exe (PID: 3188)
- cmd.exe (PID: 4684)
- cmd.exe (PID: 6316)
- cmd.exe (PID: 2356)
- cmd.exe (PID: 7312)
Captures screenshot (POWERSHELL)
- powershell.exe (PID: 6520)
The executable file from the user directory is run by the CMD process
- rar.exe (PID: 7176)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 6748)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 6276)
Accesses operating system name via WMI (SCRIPT)
- WMIC.exe (PID: 6524)
Accesses product unique identifier via WMI (SCRIPT)
- WMIC.exe (PID: 2744)
Uses WMIC.EXE to obtain a list of video controllers
- cmd.exe (PID: 7036)
Accesses video controller name via WMI (SCRIPT)
- WMIC.exe (PID: 8176)
Checks for external IP
- Xeno.exe (PID: 6176)
- svchost.exe (PID: 2192)
Hides command output
- cmd.exe (PID: 3420)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 3420)
Reads security settings of Internet Explorer
- SecHealthUI.exe (PID: 6740)
BASE64 encoded PowerShell command has been detected
- cmd.exe (PID: 5460)
INFO
The sample compiled with english language support
- msedge.exe (PID: 6316)
- msedge.exe (PID: 5340)
- Xeno.exe (PID: 3988)
- Xeno.exe (PID: 6420)
- Xeno.exe (PID: 6176)
Application launched itself
- msedge.exe (PID: 5340)
- msedge.exe (PID: 4244)
Executable content was dropped or overwritten
- msedge.exe (PID: 6316)
- msedge.exe (PID: 5340)
Attempting to use instant messaging service
- msedge.exe (PID: 6316)
Checks supported languages
- identity_helper.exe (PID: 8188)
- identity_helper.exe (PID: 7784)
- Xeno.exe (PID: 3988)
- Xeno.exe (PID: 7316)
- Xeno.exe (PID: 6420)
- Xeno.exe (PID: 6176)
- tree.com (PID: 6432)
- tree.com (PID: 2260)
- tree.com (PID: 7180)
- tree.com (PID: 6152)
- csc.exe (PID: 6316)
- tree.com (PID: 6940)
- cvtres.exe (PID: 6512)
- MpCmdRun.exe (PID: 3620)
- rar.exe (PID: 7176)
- SecHealthUI.exe (PID: 6740)
- tree.com (PID: 7808)
Reads the computer name
- identity_helper.exe (PID: 7784)
- identity_helper.exe (PID: 8188)
- Xeno.exe (PID: 3988)
- Xeno.exe (PID: 6420)
- Xeno.exe (PID: 6176)
- MpCmdRun.exe (PID: 3620)
- SecHealthUI.exe (PID: 6740)
Reads Environment values
- identity_helper.exe (PID: 7784)
- identity_helper.exe (PID: 8188)
Reads security settings of Internet Explorer
- explorer.exe (PID: 4488)
- ComputerDefaults.exe (PID: 6508)
- WMIC.exe (PID: 7992)
- WMIC.exe (PID: 6524)
- WMIC.exe (PID: 6344)
- WMIC.exe (PID: 2744)
- WMIC.exe (PID: 8176)
Checks proxy server information
- explorer.exe (PID: 4488)
Creates files or folders in the user directory
- explorer.exe (PID: 4488)
The process uses the downloaded file
- msedge.exe (PID: 7604)
- explorer.exe (PID: 4488)
- cmd.exe (PID: 8020)
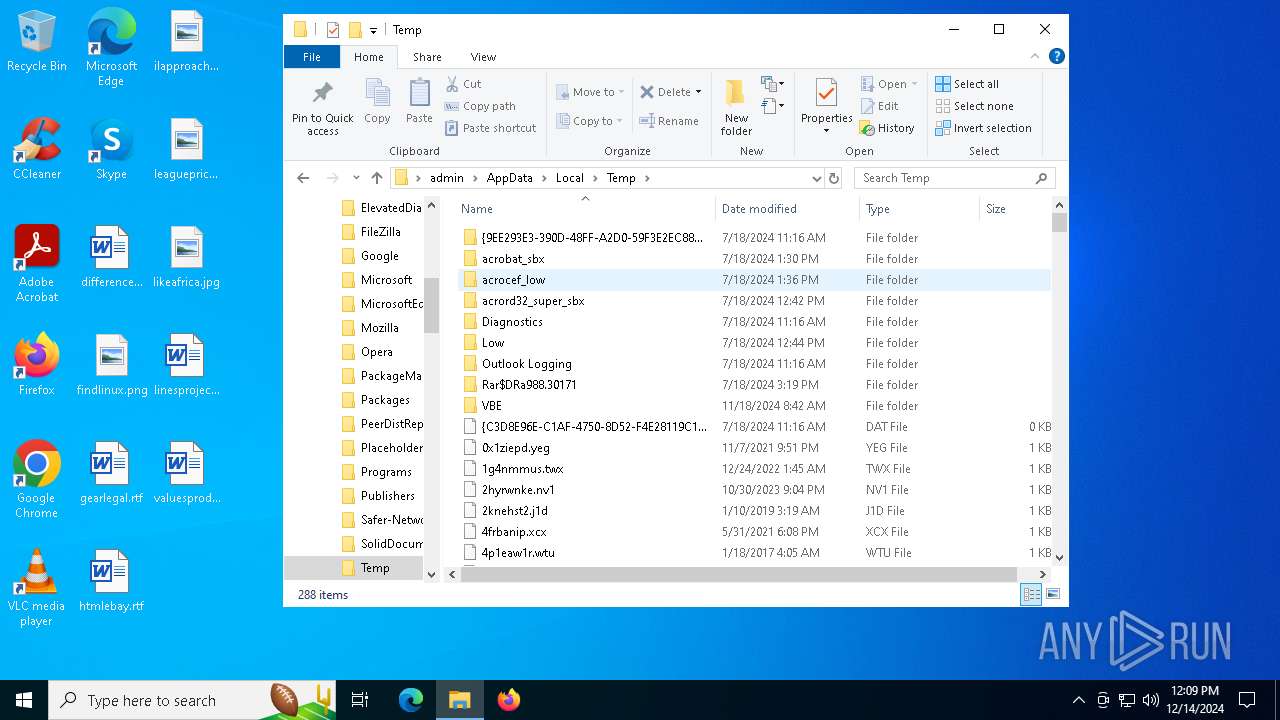
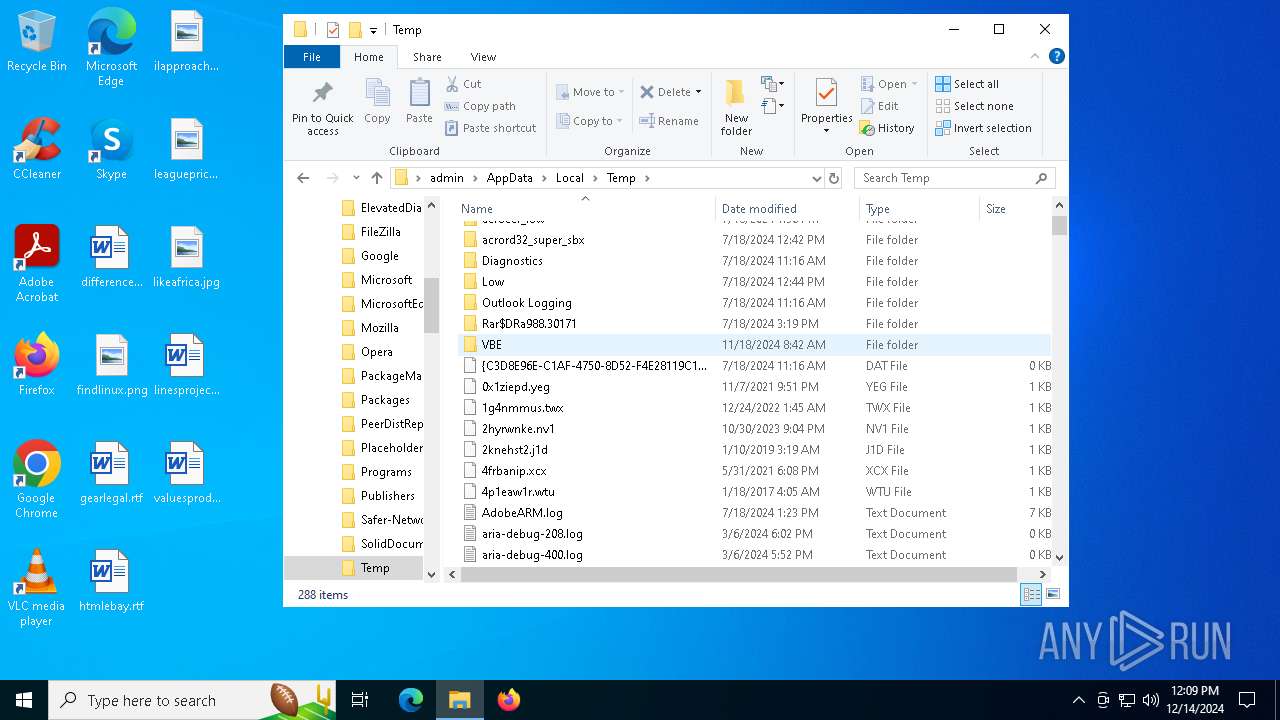
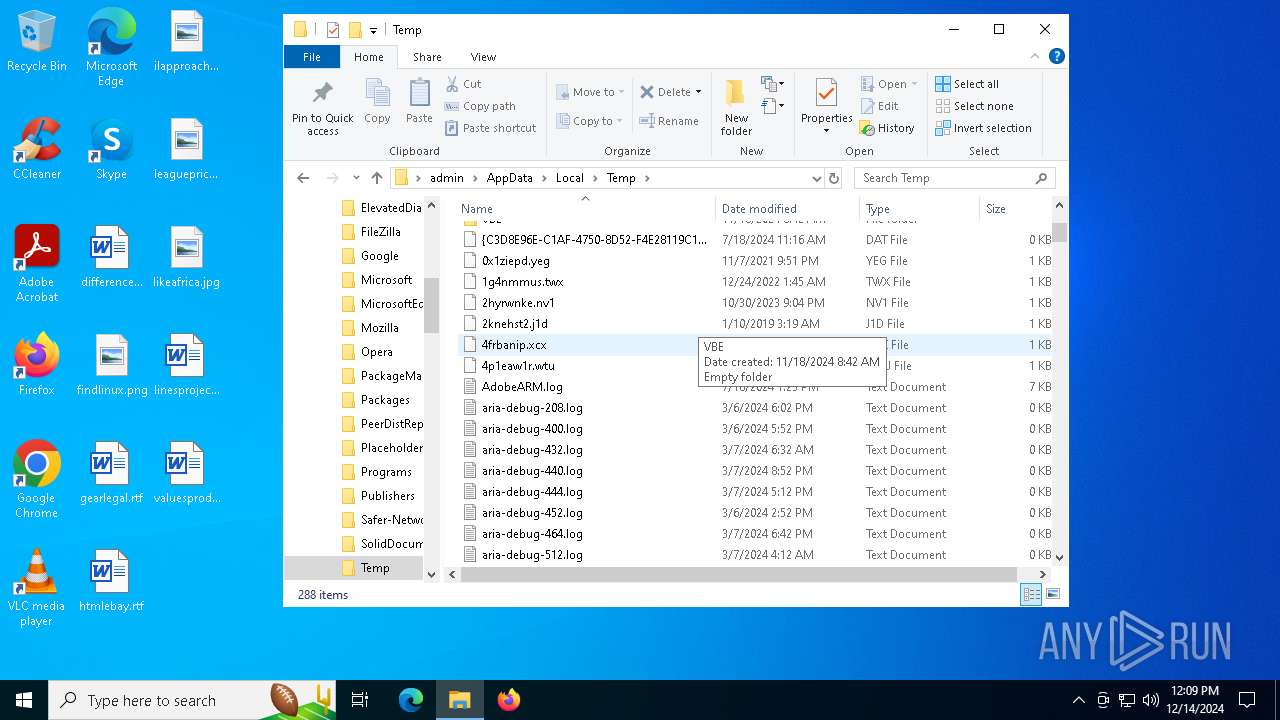
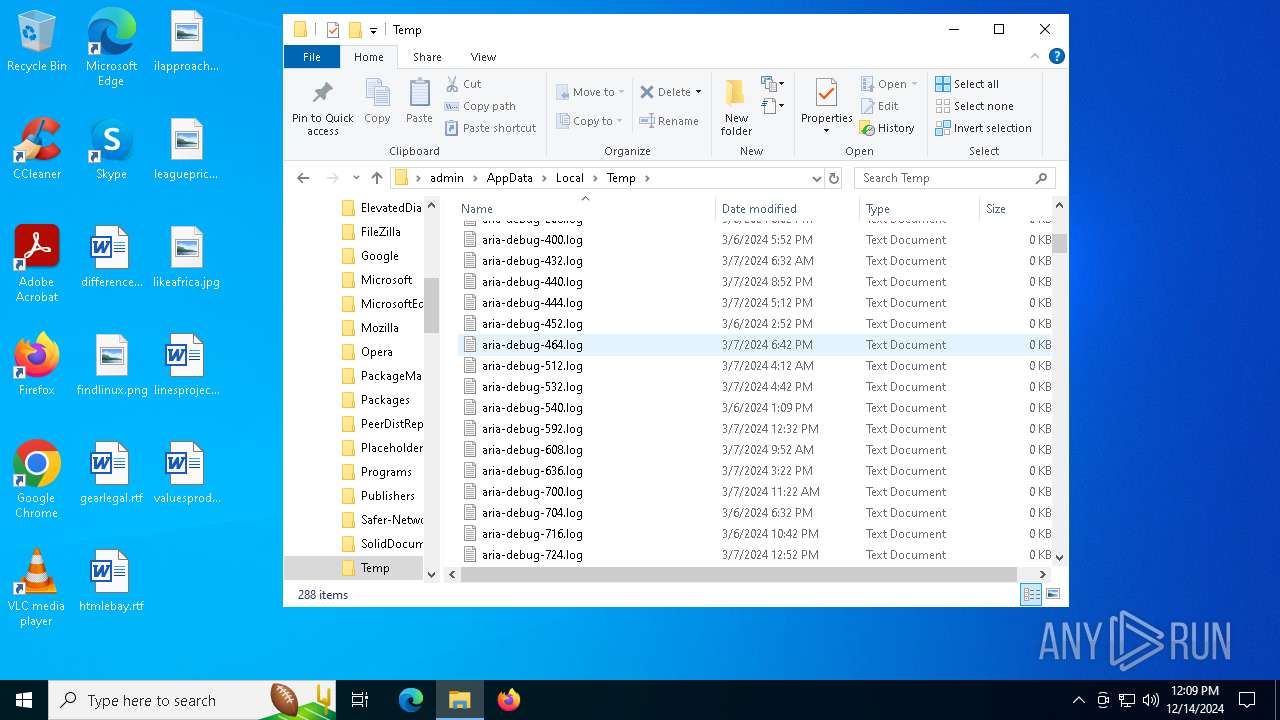
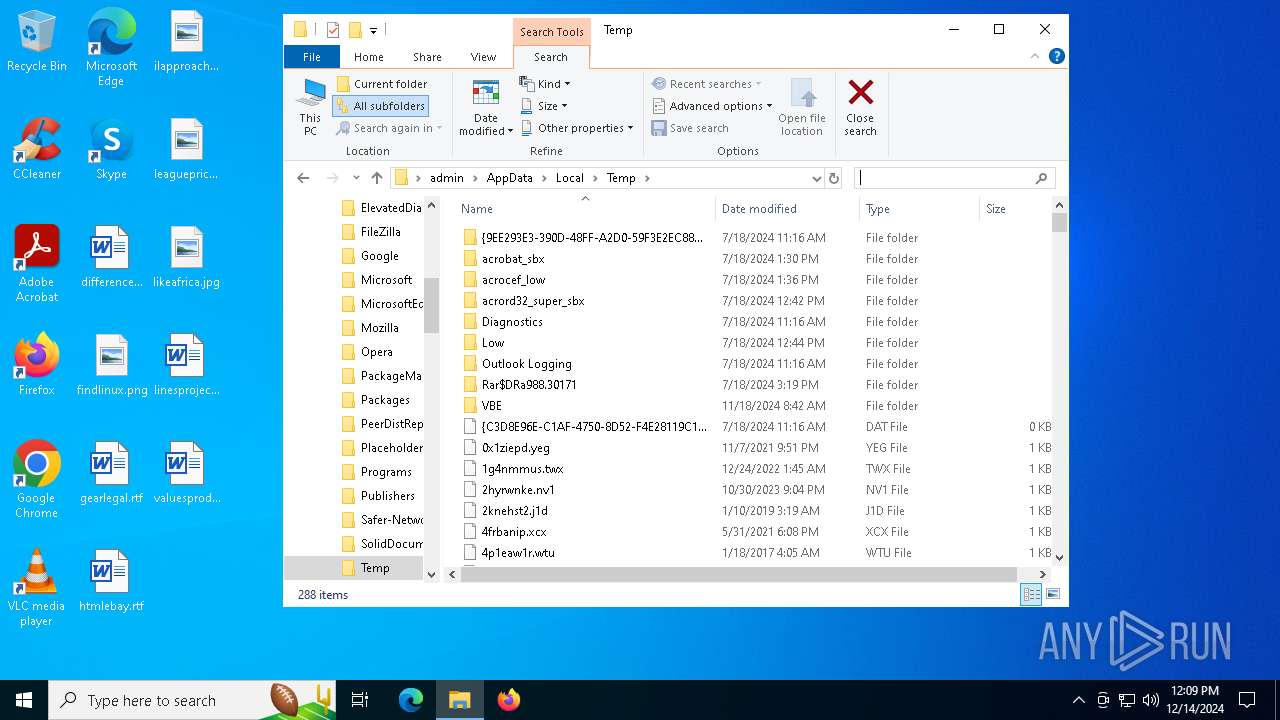
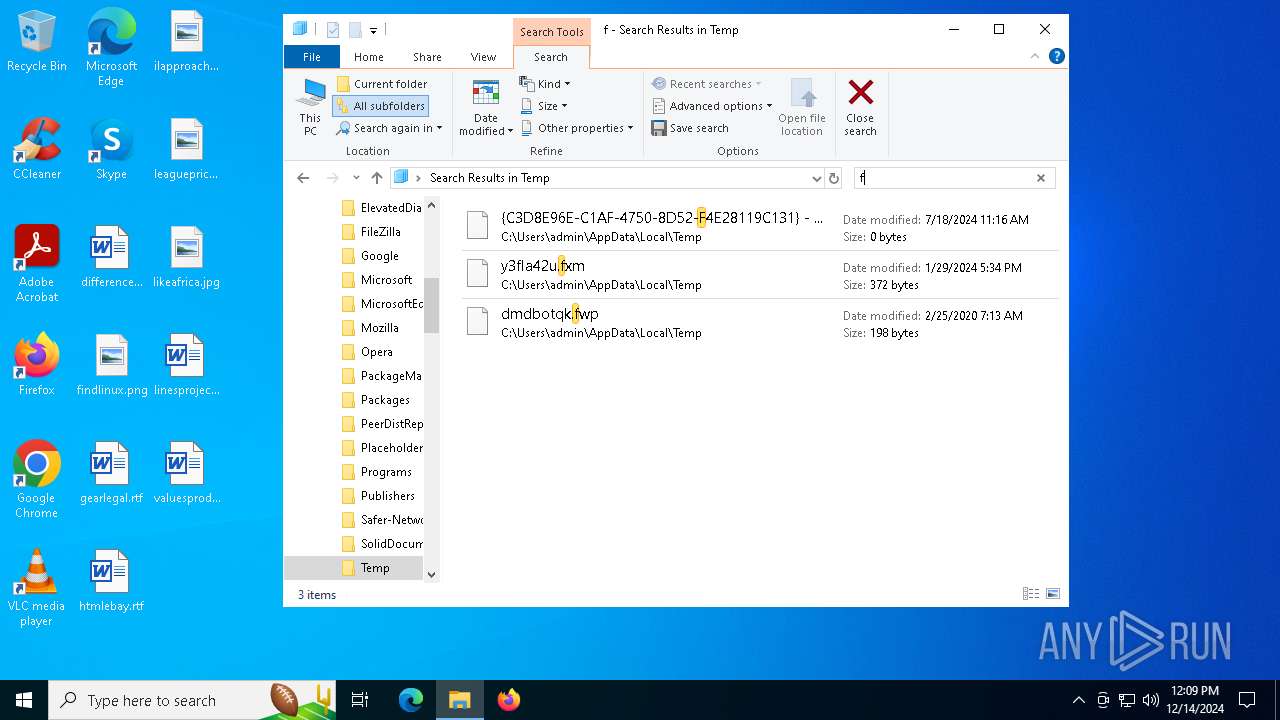
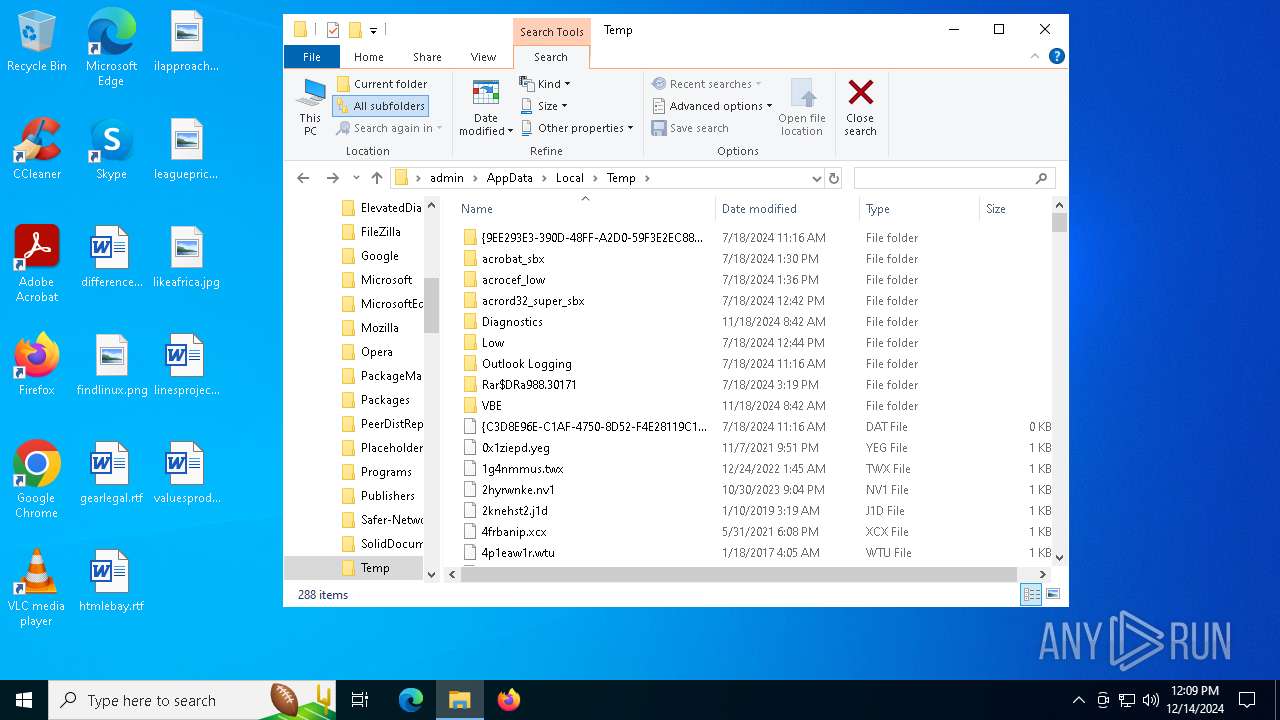
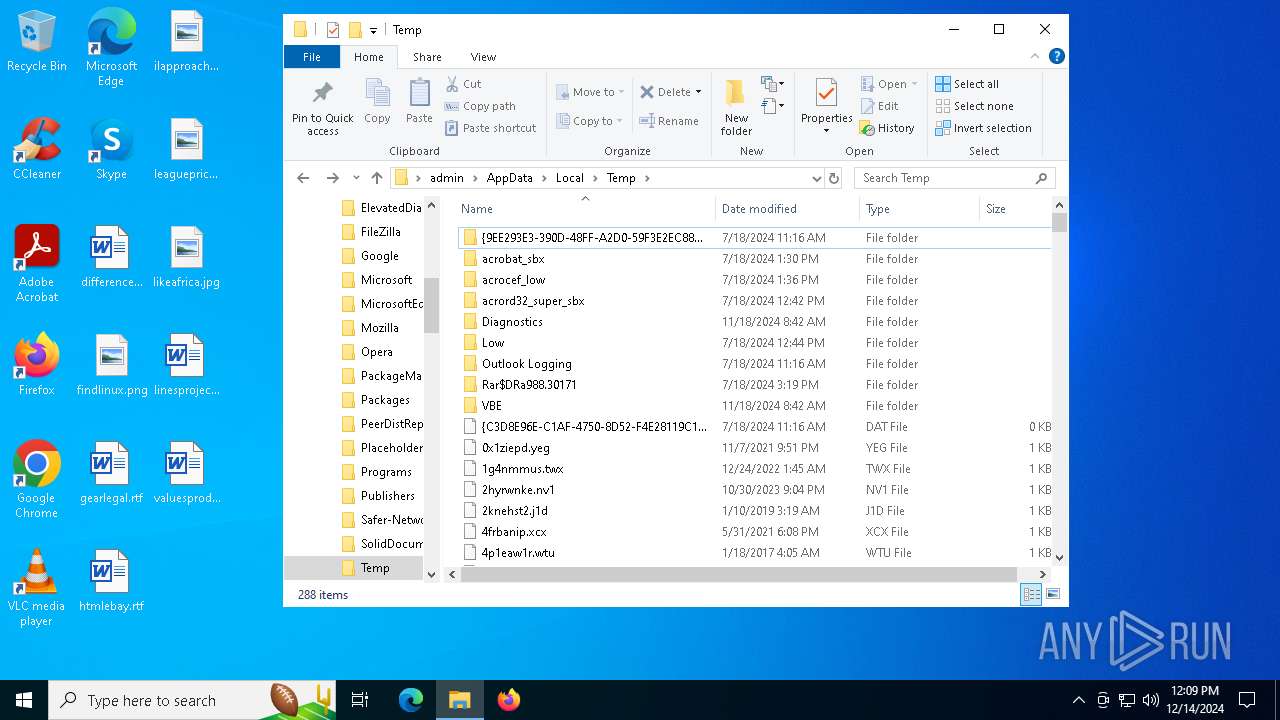
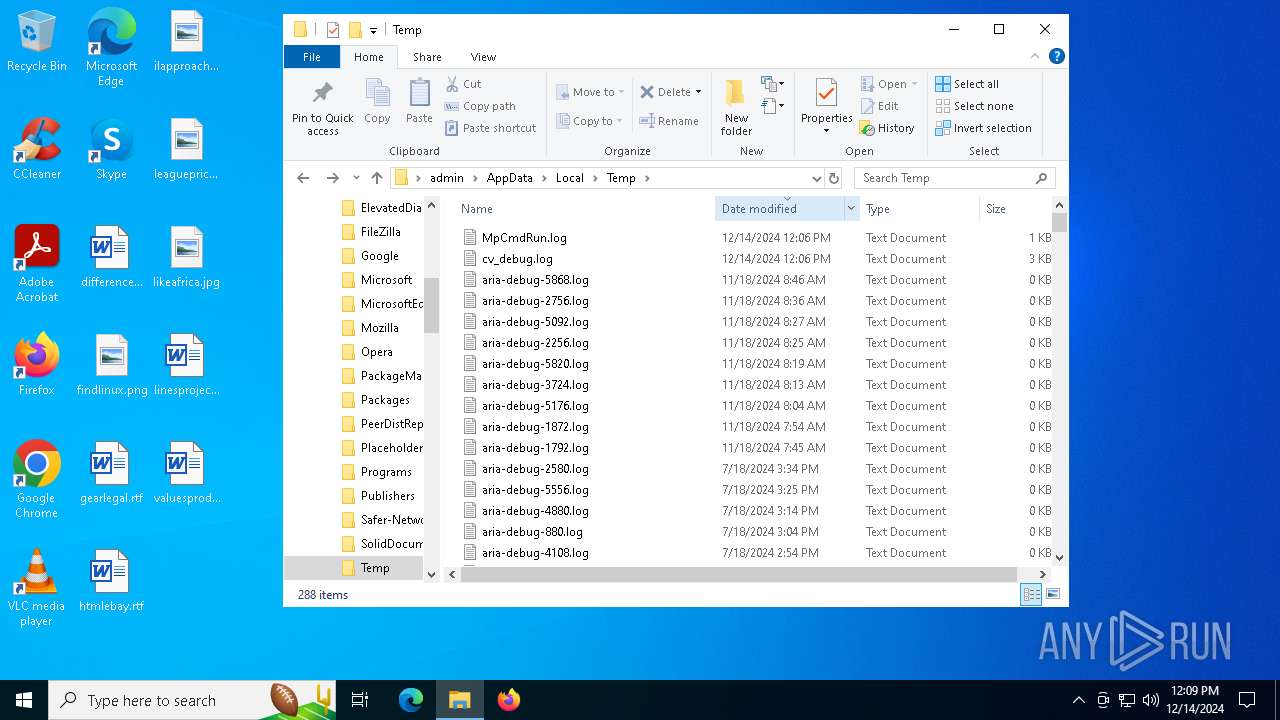
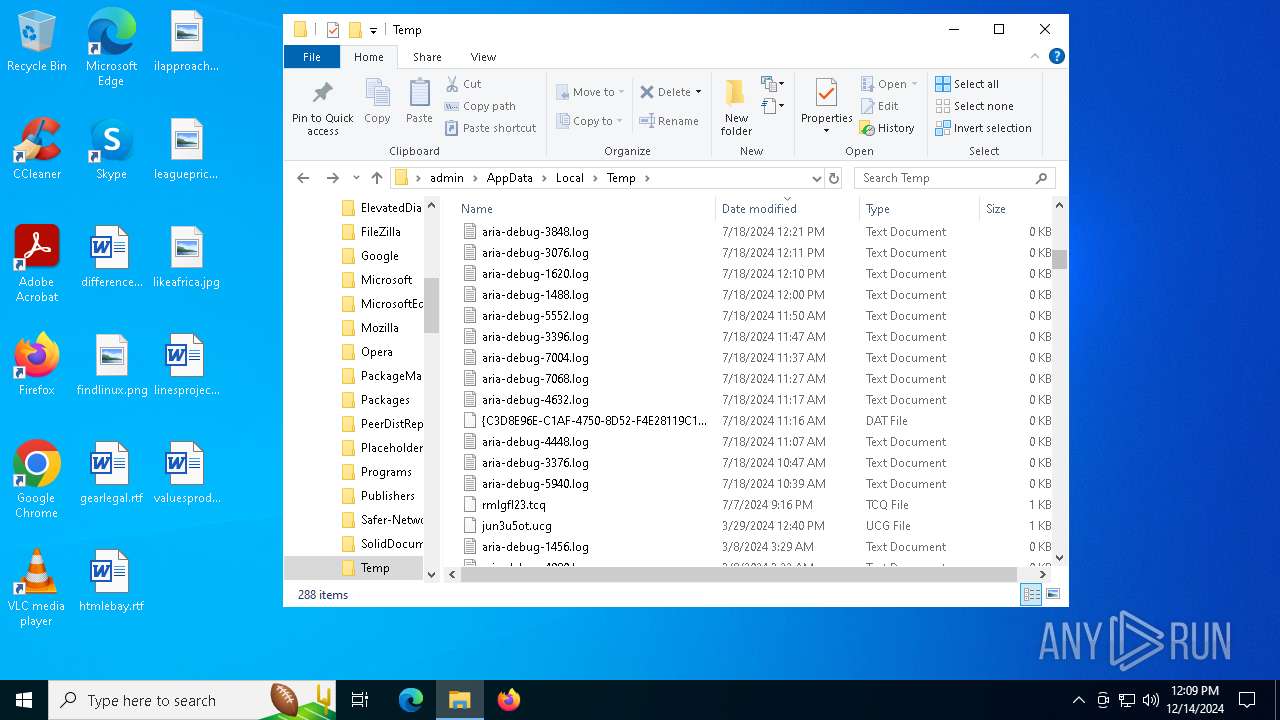
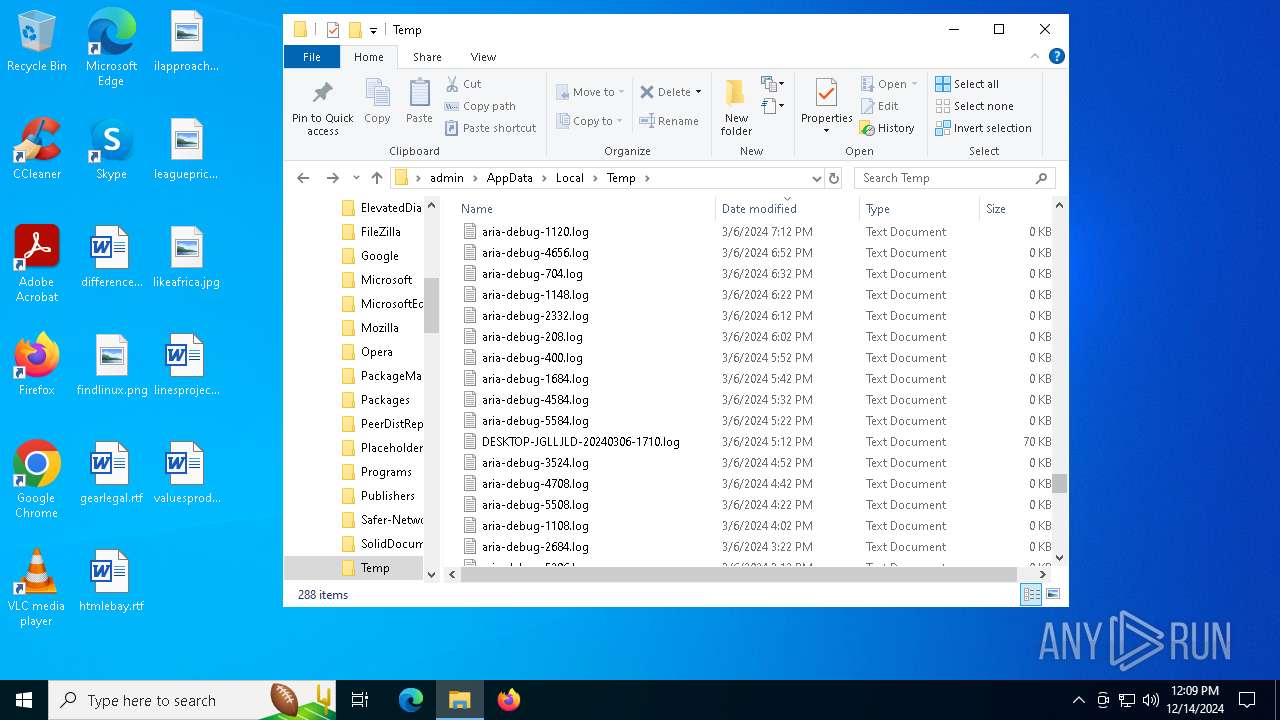
Create files in a temporary directory
- Xeno.exe (PID: 7316)
- Xeno.exe (PID: 6420)
- Xeno.exe (PID: 3988)
- Xeno.exe (PID: 6176)
- cvtres.exe (PID: 6512)
- csc.exe (PID: 6316)
- MpCmdRun.exe (PID: 3620)
- rar.exe (PID: 7176)
Reads the software policy settings
- explorer.exe (PID: 4488)
Creates files in the program directory
- Xeno.exe (PID: 6176)
The Powershell gets current clipboard
- powershell.exe (PID: 8000)
Checks the directory tree
- tree.com (PID: 6432)
- tree.com (PID: 2260)
- tree.com (PID: 7180)
- tree.com (PID: 6152)
- tree.com (PID: 7808)
- tree.com (PID: 6940)
Reads the machine GUID from the registry
- csc.exe (PID: 6316)
- rar.exe (PID: 7176)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 3608)
- powershell.exe (PID: 7548)
- powershell.exe (PID: 2744)
- powershell.exe (PID: 7696)
- powershell.exe (PID: 7244)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 3608)
- powershell.exe (PID: 2744)
- powershell.exe (PID: 7548)
Displays MAC addresses of computer network adapters
- getmac.exe (PID: 7560)
Sends debugging messages
- SecHealthUI.exe (PID: 6740)
Drops encrypted VBS script (Microsoft Script Encoder)
- explorer.exe (PID: 4488)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
314
Monitored processes
179
Malicious processes
12
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 628 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 836 | reg add hkcu\Software\Classes\ms-settings\shell\open\command /v "DelegateExecute" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1740 | C:\WINDOWS\system32\cmd.exe /c "powershell Get-ItemPropertyValue -Path 'HKLM:SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform' -Name BackupProductKeyDefault" | C:\Windows\System32\cmd.exe | — | Xeno.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2040 | tasklist /FO LIST | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2076 | C:\WINDOWS\system32\cmd.exe /c "powershell Get-ItemPropertyValue -Path HKLM:SOFTWARE\Roblox\RobloxStudioBrowser\roblox.com -Name .ROBLOSECURITY" | C:\Windows\System32\cmd.exe | — | Xeno.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2088 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2136 | powershell Get-ItemPropertyValue -Path 'HKLM:SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform' -Name BackupProductKeyDefault | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2260 | tree /A /F | C:\Windows\System32\tree.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Tree Walk Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2356 | tasklist /FO LIST | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
103 275
Read events
102 963
Write events
275
Delete events
37
Modification events
| (PID) Process: | (5340) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: E4F5B30FD0872F00 | |||
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:000000000004031E |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456A48A294F7A40804AB924005FF030B61F | |||
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:0000000000050294 |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456A48A294F7A40804AB924005FF030B61F | |||
| (PID) Process: | (5340) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: D7B9BD0FD0872F00 | |||
| (PID) Process: | (5340) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262942 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {FDF0E4E1-D85B-4319-8225-B82B3C30CEDF} | |||
| (PID) Process: | (5340) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5340) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5340) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5340) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5340) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 5E36EA0FD0872F00 | |||
Executable files
42
Suspicious files
107
Text files
127
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1352d6.TMP | — | |
MD5:— | SHA256:— | |||
| 5340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1352d6.TMP | — | |
MD5:— | SHA256:— | |||
| 5340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1352e6.TMP | — | |
MD5:— | SHA256:— | |||
| 5340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1352e6.TMP | — | |
MD5:— | SHA256:— | |||
| 5340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF135305.TMP | — | |
MD5:— | SHA256:— | |||
| 5340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
67
DNS requests
52
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6068 | svchost.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4488 | explorer.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEEj8k7RgVZSNNqfJionWlBY%3D | unknown | — | — | whitelisted |
4488 | explorer.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSdE3gf41WAic8Uh9lF92%2BIJqh5qwQUMuuSmv81lkgvKEBCcCA2kVwXheYCEDPXCKiRQFMZ4qW70zm5rW4%3D | unknown | — | — | whitelisted |
4488 | explorer.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRd0JozUYXMqqW4y4zJTrLcMCRSkAQUgTKSQSsozUbIxKLGKjkS7EipPxQCEQC%2FsVABu%2FWS1JYqd5fqc2%2Bj | unknown | — | — | whitelisted |
6176 | Xeno.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/?fields=225545 | unknown | — | — | shared |
6968 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6968 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6068 | svchost.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6068 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6316 | msedge.exe | 52.123.243.94:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5340 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6316 | msedge.exe | 162.159.129.233:443 | cdn.discordapp.com | — | — | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
cdn.discordapp.com |
| shared |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6316 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
6316 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
2192 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2192 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
6176 | Xeno.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
2192 | svchost.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
6176 | Xeno.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
6176 | Xeno.exe | A Network Trojan was detected | STEALER [ANY.RUN] BlankGrabber (SkochGrabber) Generic External IP Check |