| File name: | honeygain_app.apk |
| Full analysis: | https://app.any.run/tasks/8882d7ca-72df-413b-9897-aa6a56c1f319 |
| Verdict: | Malicious activity |
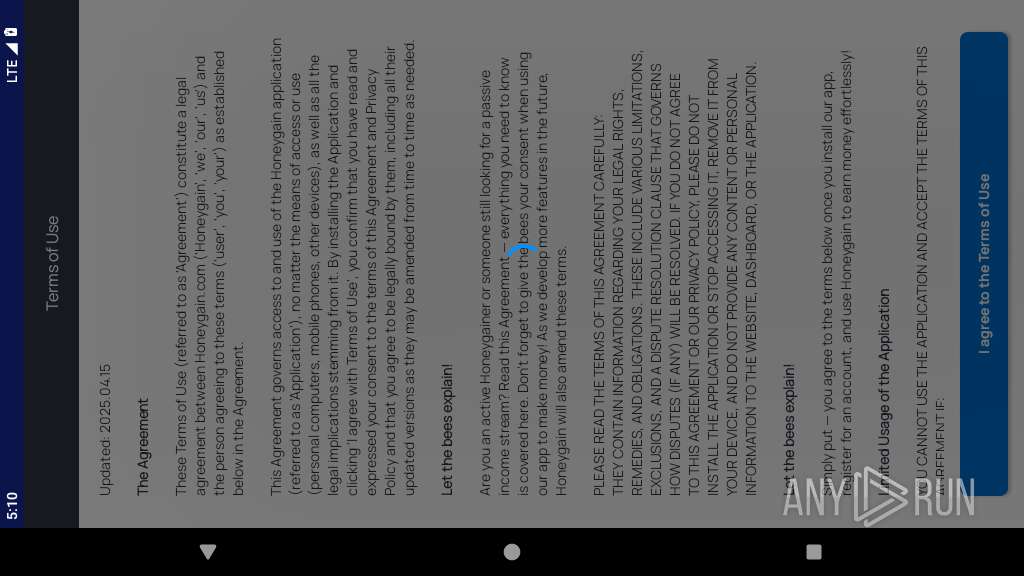
| Threats: | Adware is a form of malware that targets users with unwanted advertisements, often disrupting their browsing experience. It typically infiltrates systems through software bundling, malicious websites, or deceptive downloads. Once installed, it may track user activity, collect sensitive data, and display intrusive ads, including pop-ups or banners. Some advanced adware variants can bypass security measures and establish persistence on devices, making removal challenging. Additionally, adware can create vulnerabilities that other malware can exploit, posing a significant risk to user privacy and system security. |
| Analysis date: | June 13, 2025, 17:08:10 |
| OS: | Android 14 |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.android.package-archive |
| File info: | Android package (APK), with gradle app-metadata.properties |
| MD5: | C501CFA305DE28D4B04F8EC2B74736EC |
| SHA1: | BE8E0FE47F371E554C9F5BB055C7DA018C982755 |
| SHA256: | FAC868FC3677D62587691AC8038A321EBE8D0C2CD812A1EF745B93E598989C53 |
| SSDEEP: | 98304:abJLgsK8ubW/fC20KbnU6BL8Qh7SuxAwDU0q4sT/+Cx2ZeCeZ0iNoM9bDRobHICL:qD95JOavjV68 |
MALICIOUS
Executes system commands or scripts
- app_process64 (PID: 2255)
Hides app icon from display
- app_process64 (PID: 2255)
ADWARE has been detected (SURICATA)
- app_process64 (PID: 2255)
SUSPICIOUS
Collects data about the device's environment (JVM version)
- app_process64 (PID: 2255)
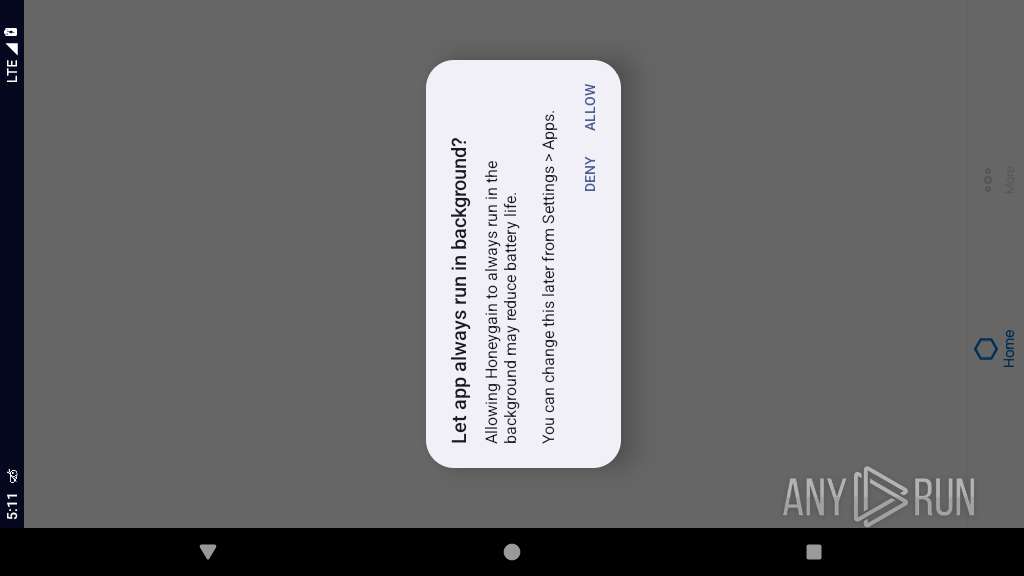
Launches a new activity
- app_process64 (PID: 2255)
Accesses system-level resources
- app_process64 (PID: 2255)
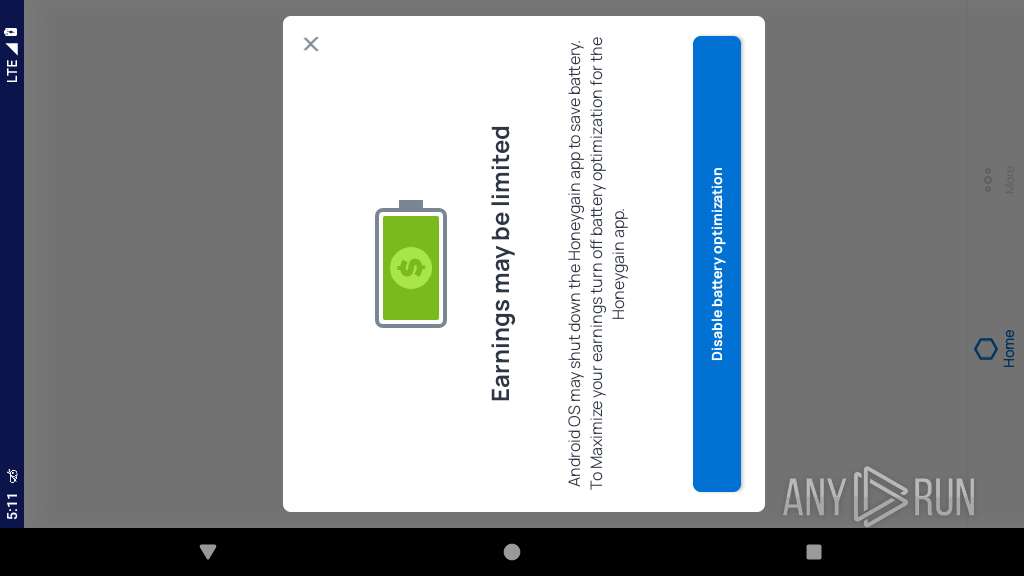
Acquires a wake lock to keep the device awake
- app_process64 (PID: 2255)
Creates a WakeLock to manage power state
- app_process64 (PID: 2255)
Establishing a connection
- app_process64 (PID: 2255)
Updates data in the storage of application settings (SharedPreferences)
- app_process64 (PID: 2255)
Retrieves the MCC and MNC of the SIM card operator
- app_process64 (PID: 2255)
Contacting a server suspected of hosting an CnC
- app_process64 (PID: 2255)
INFO
Retrieves CPU core information
- app_process64 (PID: 2255)
Dynamically inspects or modifies classes, methods, and fields at runtime
- app_process64 (PID: 2255)
Verifies whether the device is connected to the internet
- app_process64 (PID: 2255)
Returns elapsed time since boot
- app_process64 (PID: 2255)
Dynamically registers broadcast event listeners
- app_process64 (PID: 2255)
Retrieves data from storage of application settings (SharedPreferences)
- app_process64 (PID: 2255)
Stores data using SQLite database
- app_process64 (PID: 2255)
Gets file name without full path
- app_process64 (PID: 2255)
Dynamically loads a class in Java
- app_process64 (PID: 2255)
Handles throwable exceptions in the app
- app_process64 (PID: 2255)
Listens for changes in sensors
- app_process64 (PID: 2255)
Gets the display metrics associated with the device's screen
- app_process64 (PID: 2255)
Loads a native library into the application
- app_process64 (PID: 2255)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .apk | | | Android Package (62.8) |
|---|---|---|
| .jar | | | Java Archive (17.3) |
| .vym | | | VYM Mind Map (14.9) |
| .zip | | | ZIP compressed archive (4.7) |
EXIF
ZIP
| ZipRequiredVersion: | - |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1981:01:01 01:01:02 |
| ZipCRC: | 0xf9e152b4 |
| ZipCompressedSize: | 51 |
| ZipUncompressedSize: | 56 |
| ZipFileName: | META-INF/com/android/build/gradle/app-metadata.properties |
Total processes
131
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 2255 | com.android.providers.media.module | /system/bin/app_process64 | app_process64 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2355 | com.honeygain.make.money | /system/bin/app_process64 | — | app_process64 |
User: u0_a109 Integrity Level: UNKNOWN Exit code: 65280 | ||||
| 2452 | com.android.webview:webview_service | /system/bin/app_process64 | app_process64 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2479 | webview_zygote | /system/bin/app_process64 | — | app_process64 |
User: webview_zygote Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2512 | com.android.adservices.api | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2530 | com.android.webview:webview_apk | /system/bin/app_process64 | app_process64 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
197
Text files
289
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2255 | app_process64 | /data/data/com.honeygain.make.money/shared_prefs/com.google.firebase.messaging.xml | xml | |
MD5:— | SHA256:— | |||
| 2255 | app_process64 | /data/data/com.honeygain.make.money/shared_prefs/com.google.android.gms.measurement.prefs.xml | xml | |
MD5:— | SHA256:— | |||
| 2255 | app_process64 | /data/data/com.honeygain.make.money/shared_prefs/com.facebook.sdk.appEventPreferences.xml | xml | |
MD5:— | SHA256:— | |||
| 2255 | app_process64 | /data/data/com.honeygain.make.money/shared_prefs/FirebaseHeartBeatW0RFRkFVTFRd+MTo4NjY5MzI4NDQ1MjA6YW5kcm9pZDozZTJiYTQwMjY0MTNjNjhi.xml | xml | |
MD5:— | SHA256:— | |||
| 2255 | app_process64 | /data/data/com.honeygain.make.money/shared_prefs/com.facebook.sdk.USER_SETTINGS.xml | xml | |
MD5:— | SHA256:— | |||
| 2255 | app_process64 | /data/data/com.honeygain.make.money/no_backup/androidx.work.workdb-journal | binary | |
MD5:— | SHA256:— | |||
| 2255 | app_process64 | /data/data/com.honeygain.make.money/files/INSTALLATION | text | |
MD5:— | SHA256:— | |||
| 2255 | app_process64 | /data/data/com.honeygain.make.money/cache/journal.tmp | text | |
MD5:— | SHA256:— | |||
| 2255 | app_process64 | /data/data/com.honeygain.make.money/shared_prefs/com.facebook.internal.preferences.APP_GATEKEEPERS.xml | xml | |
MD5:— | SHA256:— | |||
| 2255 | app_process64 | /data/data/com.honeygain.make.money/shared_prefs/com.facebook.internal.preferences.APP_SETTINGS.xml | xml | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
64
DNS requests
46
Threats
30
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 142.250.186.131:80 | http://connectivitycheck.gstatic.com/generate_204 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
446 | mdnsd | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 216.239.35.12:123 | time.android.com | — | — | whitelisted |
— | — | 142.250.186.131:80 | connectivitycheck.gstatic.com | GOOGLE | US | whitelisted |
— | — | 216.58.206.36:443 | www.google.com | GOOGLE | US | whitelisted |
— | — | 74.125.71.81:443 | staging-remoteprovisioning.sandbox.googleapis.com | GOOGLE | US | whitelisted |
2255 | app_process64 | 157.240.0.13:443 | graph.facebook.com | FACEBOOK | US | whitelisted |
2255 | app_process64 | 104.26.13.49:443 | ff.honeygain.com | CLOUDFLARENET | US | whitelisted |
2255 | app_process64 | 104.16.248.249:443 | cloudflare-dns.com | CLOUDFLARENET | — | whitelisted |
2255 | app_process64 | 104.26.12.49:443 | ff.honeygain.com | CLOUDFLARENET | US | whitelisted |
2255 | app_process64 | 142.250.74.202:443 | firebaseinstallations.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
connectivitycheck.gstatic.com |
| whitelisted |
www.google.com |
| whitelisted |
time.android.com |
| whitelisted |
staging-remoteprovisioning.sandbox.googleapis.com |
| whitelisted |
google.com |
| whitelisted |
graph.facebook.com |
| whitelisted |
ff.honeygain.com |
| unknown |
cloudflare-dns.com |
| whitelisted |
misc.honeygain.com |
| unknown |
sentry.honeygain.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO Android Device Connectivity Check |
2255 | app_process64 | Misc activity | ET INFO Observed Cloudflare DNS over HTTPS Domain (cloudflare-dns .com in TLS SNI) |
2255 | app_process64 | Domain Observed Used for C2 Detected | ET ADWARE_PUP Observed Honeygain Domain (api .honeygain .com in TLS SNI) |
2255 | app_process64 | Domain Observed Used for C2 Detected | ET ADWARE_PUP Observed Honeygain Domain (api .honeygain .com in TLS SNI) |
2255 | app_process64 | Domain Observed Used for C2 Detected | ET ADWARE_PUP Observed Honeygain Domain (api .honeygain .com in TLS SNI) |
2255 | app_process64 | Domain Observed Used for C2 Detected | ET ADWARE_PUP Observed Honeygain Domain (api .honeygain .com in TLS SNI) |
2255 | app_process64 | Domain Observed Used for C2 Detected | ET ADWARE_PUP Observed Honeygain Domain (api .honeygain .com in TLS SNI) |
342 | netd | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2255 | app_process64 | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
2255 | app_process64 | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |