| File name: | catalog attached.doc |
| Full analysis: | https://app.any.run/tasks/acb26c66-13ec-46ae-997e-eb5a249a8e2e |
| Verdict: | Malicious activity |
| Threats: | LokiBot was developed in 2015 to steal information from a variety of applications. Despite the age, this malware is still rather popular among cybercriminals. |
| Analysis date: | December 02, 2019, 19:15:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
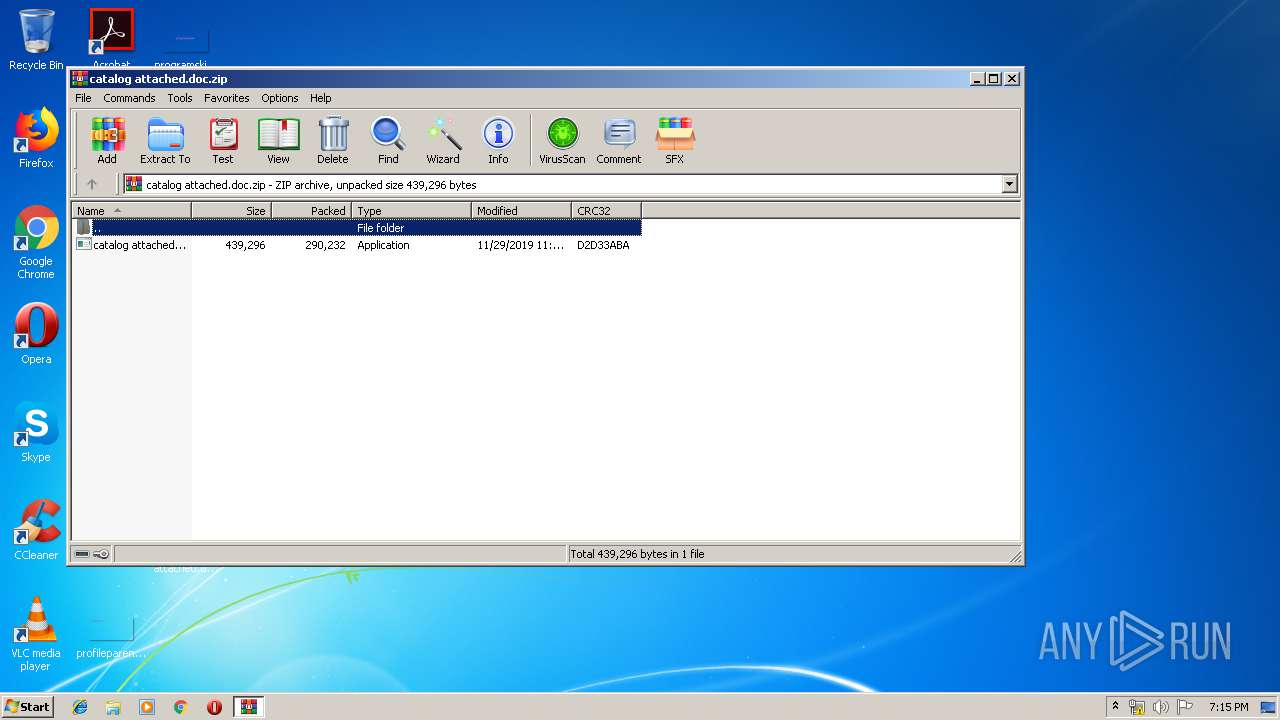
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | A7E6CAB5C4C9EB24FFC9D88EAF873CDA |
| SHA1: | 203EC509CE2212D95B5507F2307B97024BFC9C12 |
| SHA256: | FA980EAC80C07BCB59C3BEE4F83E9EB539DA811923773C6B6A24DF40ECBEEE63 |
| SSDEEP: | 6144:lvv+SFz5ik6LkKw0obI0Sb0ZW5NbVYwgPsRiKOC2EF2zc:lHtwASQI0SHzwIig2s2Y |
MALICIOUS
Application was dropped or rewritten from another process
- catalog attached.exe (PID: 3356)
- catalog attached.exe (PID: 3716)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2396)
Uses Task Scheduler to run other applications
- catalog attached.exe (PID: 3356)
LOKIBOT was detected
- catalog attached.exe (PID: 3716)
Connects to CnC server
- catalog attached.exe (PID: 3716)
Actions looks like stealing of personal data
- catalog attached.exe (PID: 3716)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4000)
- catalog attached.exe (PID: 3356)
- catalog attached.exe (PID: 3716)
Application launched itself
- catalog attached.exe (PID: 3356)
Creates files in the user directory
- catalog attached.exe (PID: 3356)
- catalog attached.exe (PID: 3716)
Loads DLL from Mozilla Firefox
- catalog attached.exe (PID: 3716)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:11:29 12:26:10 |
| ZipCRC: | 0xd2d33aba |
| ZipCompressedSize: | 290232 |
| ZipUncompressedSize: | 439296 |
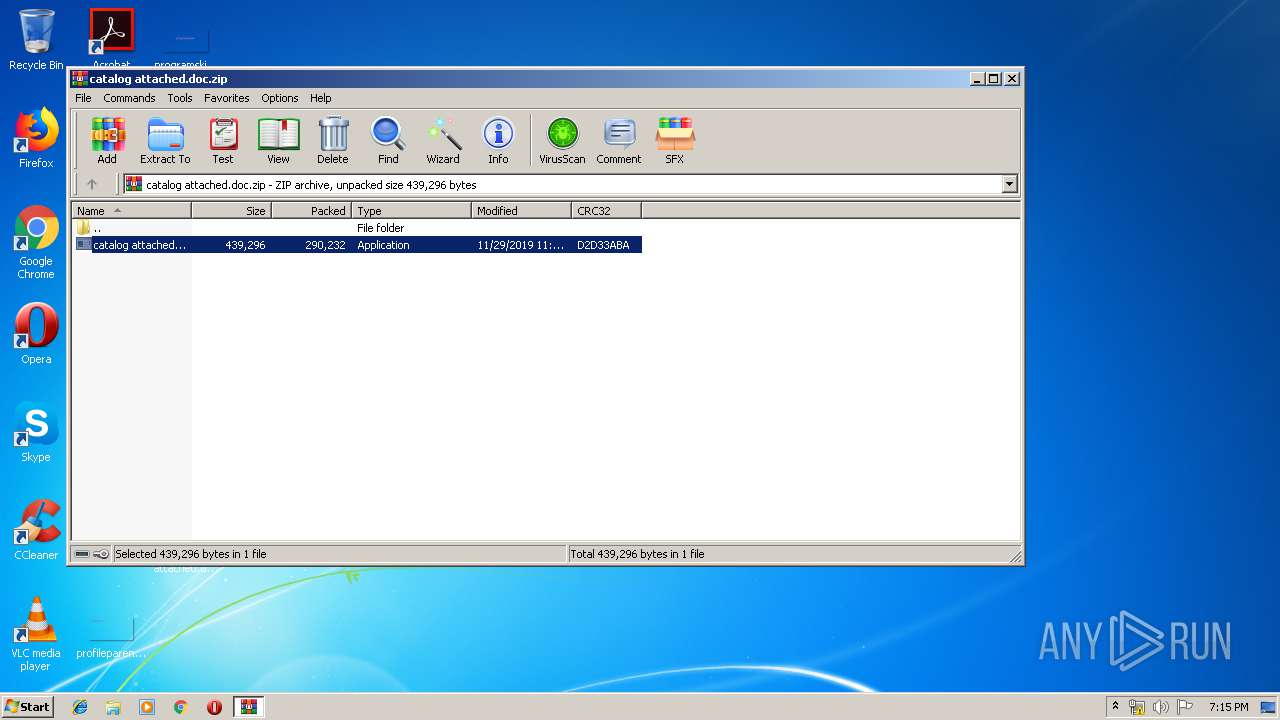
| ZipFileName: | catalog attached.exe |
Total processes
37
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2396 | "C:\Windows\System32\schtasks.exe" /Create /TN "Updates\GRmQQcwB" /XML "C:\Users\admin\AppData\Local\Temp\tmpC147.tmp" | C:\Windows\System32\schtasks.exe | — | catalog attached.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3356 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa4000.16005\catalog attached.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa4000.16005\catalog attached.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: WindowsLib Exit code: 0 Version: 5.5.5.8 Modules
| |||||||||||||||
| 3716 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa4000.16005\catalog attached.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa4000.16005\catalog attached.exe | catalog attached.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: WindowsLib Exit code: 0 Version: 5.5.5.8 Modules
| |||||||||||||||
| 4000 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\catalog attached.doc.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
557
Read events
528
Write events
29
Delete events
0
Modification events
| (PID) Process: | (4000) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (4000) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (4000) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (4000) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (4000) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\catalog attached.doc.zip | |||
| (PID) Process: | (4000) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4000) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4000) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4000) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4000) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
3
Suspicious files
0
Text files
2
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3716 | catalog attached.exe | C:\Users\admin\AppData\Roaming\F63AAA\A71D80.lck | — | |
MD5:— | SHA256:— | |||
| 3356 | catalog attached.exe | C:\Users\admin\AppData\Local\Temp\tmpC147.tmp | xml | |
MD5:— | SHA256:— | |||
| 4000 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa4000.16005\catalog attached.exe | executable | |
MD5:— | SHA256:— | |||
| 3356 | catalog attached.exe | C:\Users\admin\AppData\Roaming\GRmQQcwB.exe | executable | |
MD5:— | SHA256:— | |||
| 3716 | catalog attached.exe | C:\Users\admin\AppData\Roaming\F63AAA\A71D80.hdb | text | |
MD5:— | SHA256:— | |||
| 3716 | catalog attached.exe | C:\Users\admin\AppData\Roaming\F63AAA\A71D80.exe | executable | |
MD5:— | SHA256:— | |||
| 3716 | catalog attached.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-1302019708-1500728564-335382590-1000\0f5007522459c86e95ffcc62f32308f1_90059c37-1320-41a4-b58d-2b75a9850d2f | dbf | |
MD5:18B8CFC0185C50383AAC0A4F30A9DAC8 | SHA256:913E8CED6A447FE791954D382ABA52D490513C5D2F689B391866C7E561F89A03 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
4
DNS requests
1
Threats
26
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3716 | catalog attached.exe | POST | 404 | 8.208.8.178:80 | http://onllygoodam.com/ae2/fre.php | US | text | 15 b | malicious |
3716 | catalog attached.exe | POST | 404 | 8.208.8.178:80 | http://onllygoodam.com/ae2/fre.php | US | text | 15 b | malicious |
3716 | catalog attached.exe | POST | 404 | 8.208.8.178:80 | http://onllygoodam.com/ae2/fre.php | US | binary | 23 b | malicious |
3716 | catalog attached.exe | POST | 404 | 8.208.8.178:80 | http://onllygoodam.com/ae2/fre.php | US | binary | 23 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3716 | catalog attached.exe | 8.208.8.178:80 | onllygoodam.com | Level 3 Communications, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
onllygoodam.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3716 | catalog attached.exe | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
3716 | catalog attached.exe | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
3716 | catalog attached.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M1 |
3716 | catalog attached.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M2 |
3716 | catalog attached.exe | A Network Trojan was detected | MALWARE [PTsecurity] Loki Bot Check-in M2 |
3716 | catalog attached.exe | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
3716 | catalog attached.exe | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
3716 | catalog attached.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M1 |
3716 | catalog attached.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M2 |
3716 | catalog attached.exe | A Network Trojan was detected | MALWARE [PTsecurity] Loki Bot Check-in M2 |
4 ETPRO signatures available at the full report