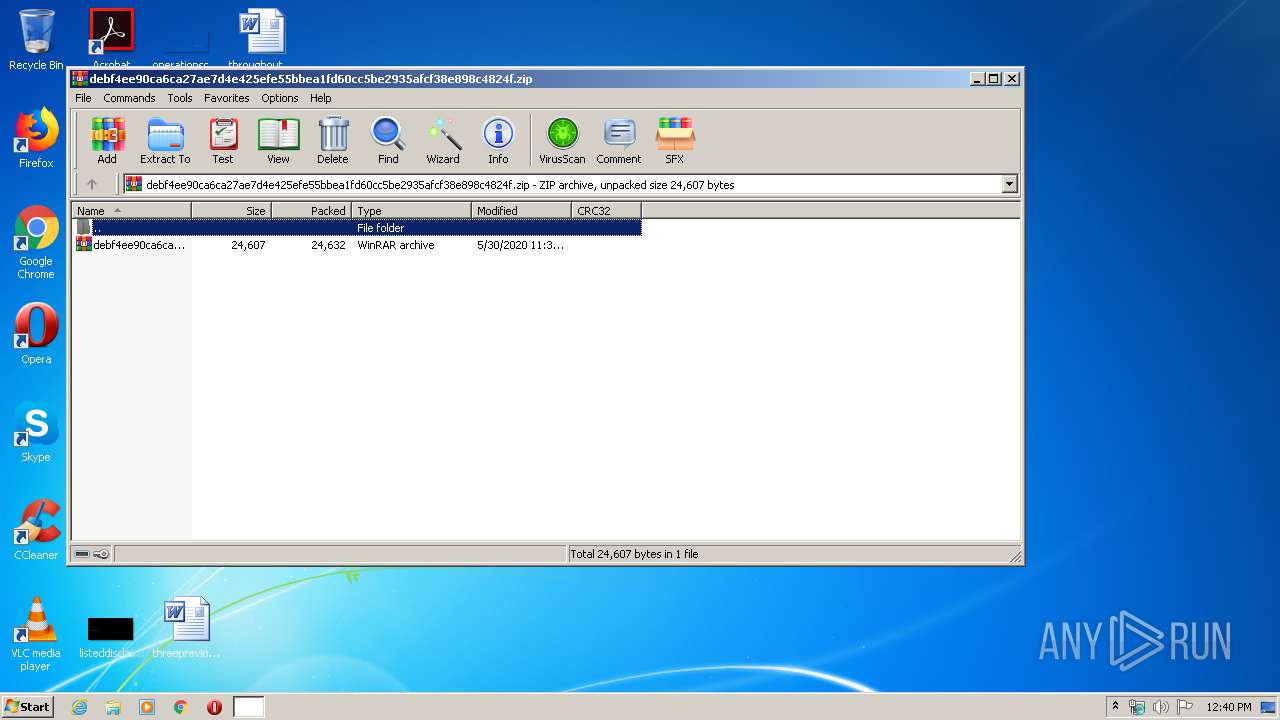
| File name: | debf4ee90ca6ca27ae7d4e425efe55bbea1fd60cc5be2935afcf38e898c4824f.zip |
| Full analysis: | https://app.any.run/tasks/522afd01-1817-4dc0-b945-3da0ed3421c1 |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | May 30, 2020, 11:39:52 |
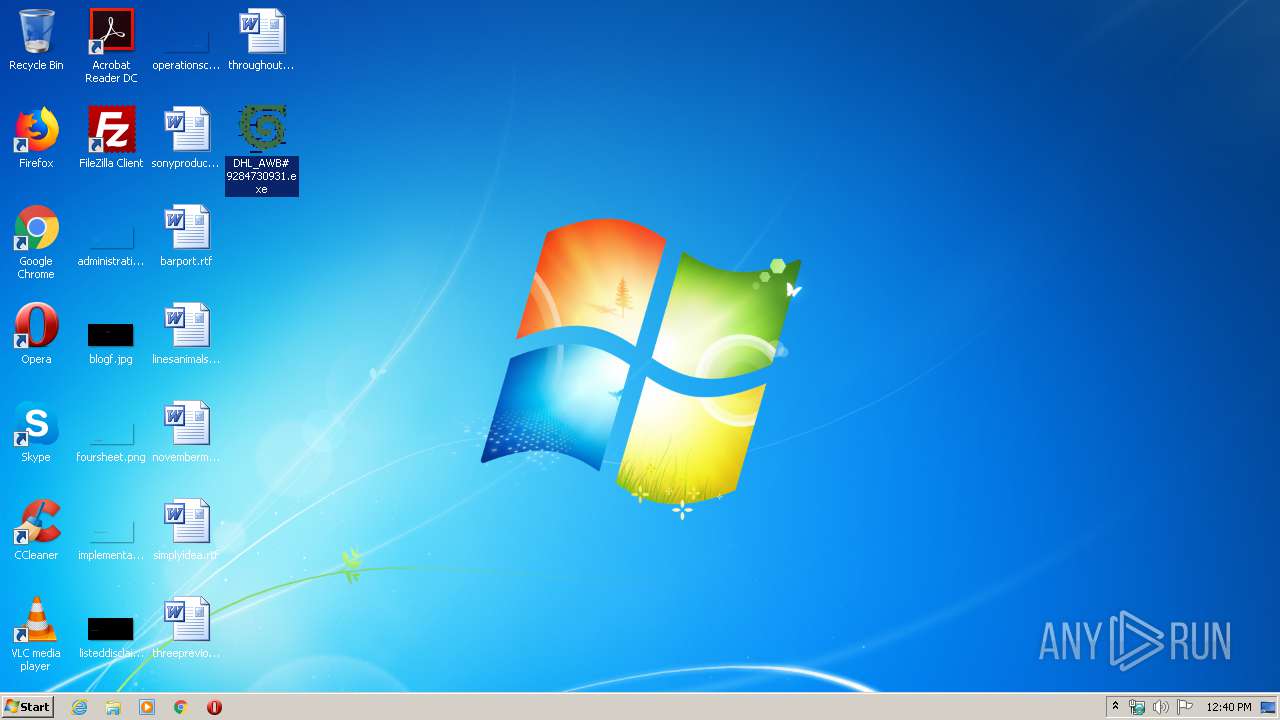
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 14CF6604341667C5FACD9F2FF10D1422 |
| SHA1: | 1D27120F7D6A1F66E4494E21F3FCE5C0C2F08D76 |
| SHA256: | FA97258B563CD4CC030B0FE1642941713F0203D7F9415AB3EBD7FB9F6821AAD3 |
| SSDEEP: | 768:GLA8sYDPAHcRL+52kmZeljl9ZVvVX2wu2BW:SsIIcRLfkrpfVswdA |
MALICIOUS
Uses SVCHOST.EXE for hidden code execution
- explorer.exe (PID: 312)
FORMBOOK was detected
- svchost.exe (PID: 2192)
- explorer.exe (PID: 312)
- Firefox.exe (PID: 948)
Connects to CnC server
- explorer.exe (PID: 312)
Application was dropped or rewritten from another process
- DHL_AWB# 9284730931.exe (PID: 1696)
- DHL_AWB# 9284730931.exe (PID: 2820)
Actions looks like stealing of personal data
- WinRAR.exe (PID: 1932)
- svchost.exe (PID: 2192)
Changes the autorun value in the registry
- svchost.exe (PID: 2192)
Stealing of credential data
- svchost.exe (PID: 2192)
Changes settings of System certificates
- DHL_AWB# 9284730931.exe (PID: 2820)
SUSPICIOUS
Application launched itself
- WinRAR.exe (PID: 1932)
- DHL_AWB# 9284730931.exe (PID: 1696)
Starts CMD.EXE for commands execution
- svchost.exe (PID: 2192)
Creates files in the user directory
- svchost.exe (PID: 2192)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2916)
Loads DLL from Mozilla Firefox
- svchost.exe (PID: 2192)
Reads Internet Cache Settings
- DHL_AWB# 9284730931.exe (PID: 2820)
Adds / modifies Windows certificates
- DHL_AWB# 9284730931.exe (PID: 2820)
INFO
Reads the hosts file
- svchost.exe (PID: 2192)
Reads settings of System Certificates
- DHL_AWB# 9284730931.exe (PID: 2820)
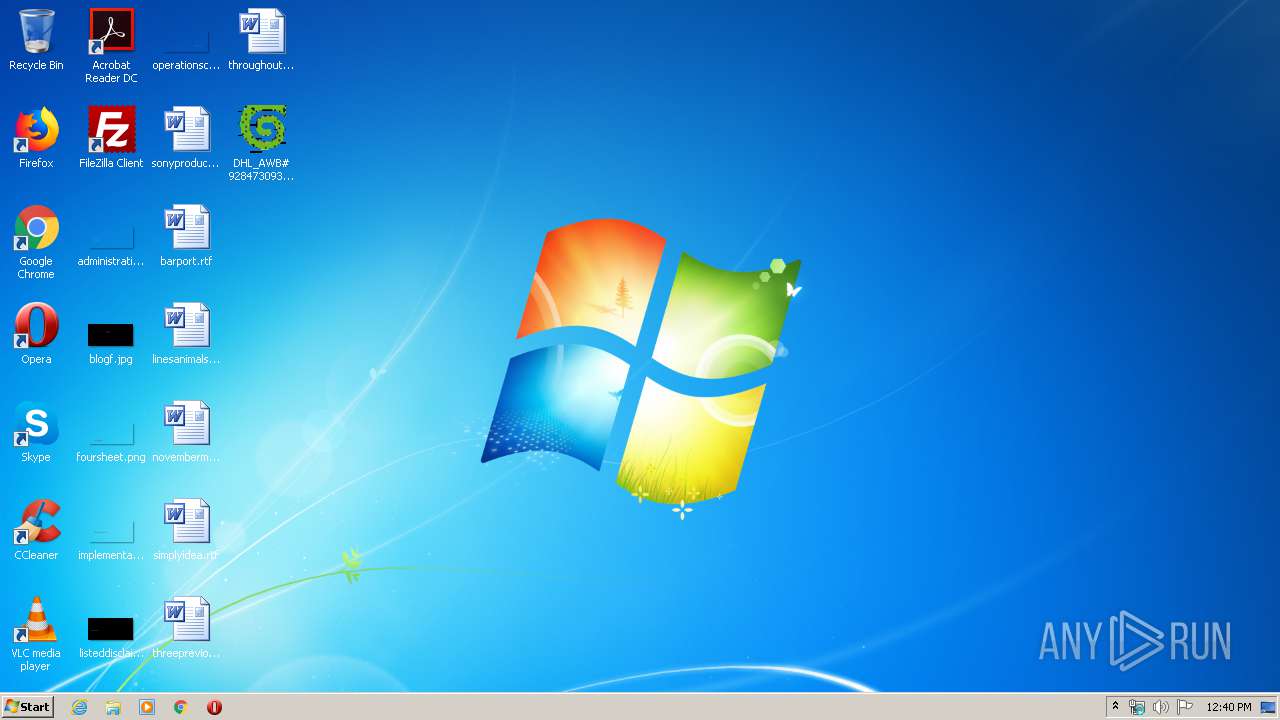
Manual execution by user
- DHL_AWB# 9284730931.exe (PID: 1696)
- svchost.exe (PID: 2192)
Creates files in the user directory
- Firefox.exe (PID: 948)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2020:05:30 11:39:08 |
| ZipCRC: | 0x9d3109de |
| ZipCompressedSize: | 24632 |
| ZipUncompressedSize: | 24607 |
| ZipFileName: | debf4ee90ca6ca27ae7d4e425efe55bbea1fd60cc5be2935afcf38e898c4824f.rar |
Total processes
44
Monitored processes
8
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 312 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 948 | "C:\Program Files\Mozilla Firefox\Firefox.exe" | C:\Program Files\Mozilla Firefox\Firefox.exe | svchost.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
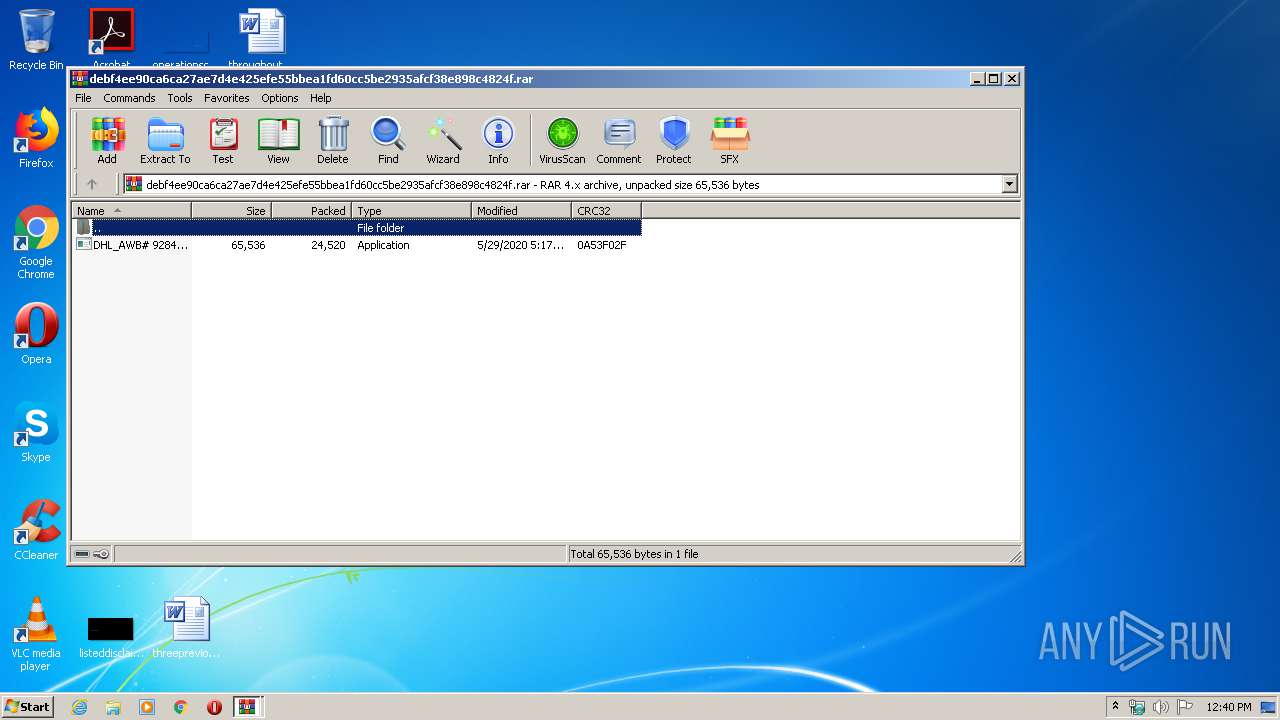
| 1696 | "C:\Users\admin\Desktop\DHL_AWB# 9284730931.exe" | C:\Users\admin\Desktop\DHL_AWB# 9284730931.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 2.02 Modules
| |||||||||||||||
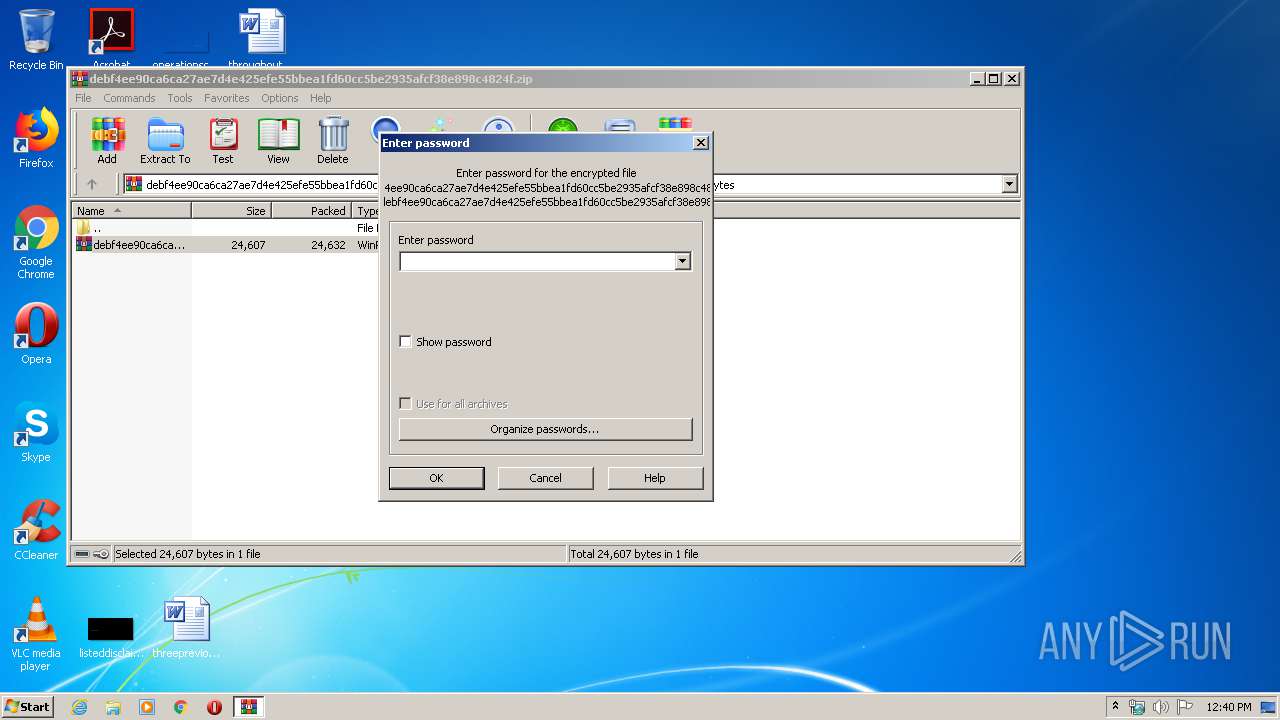
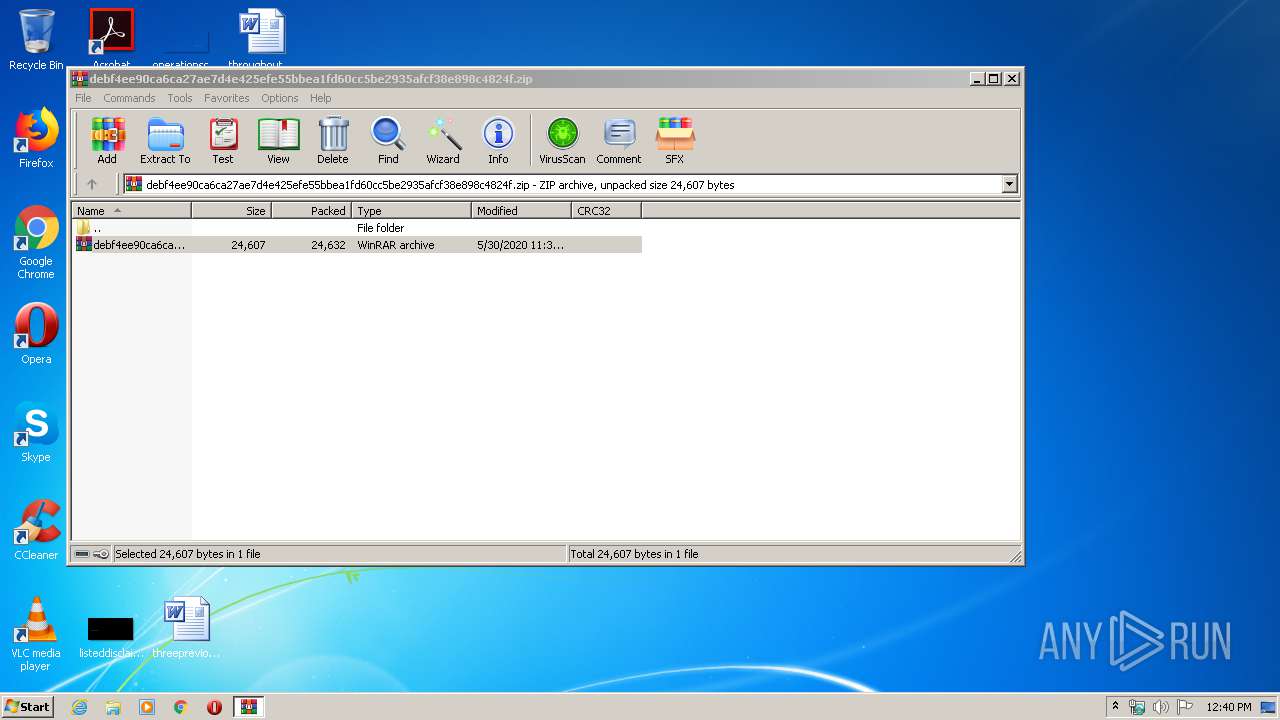
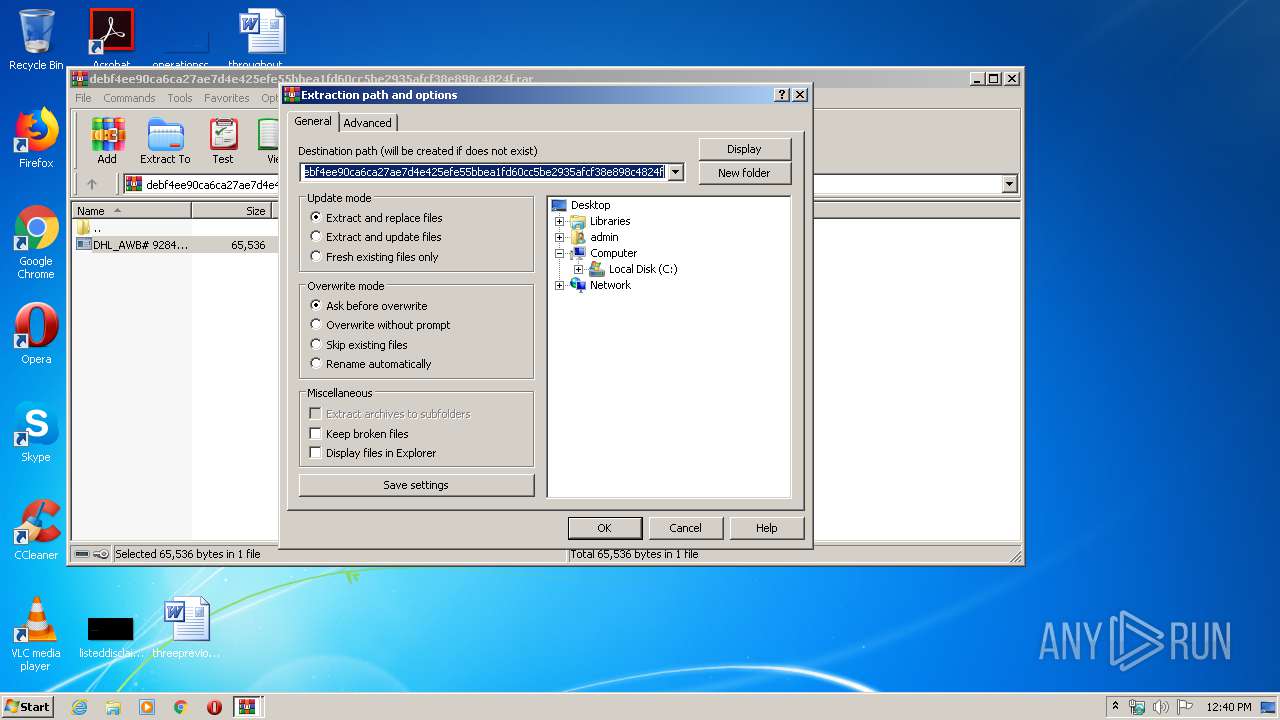
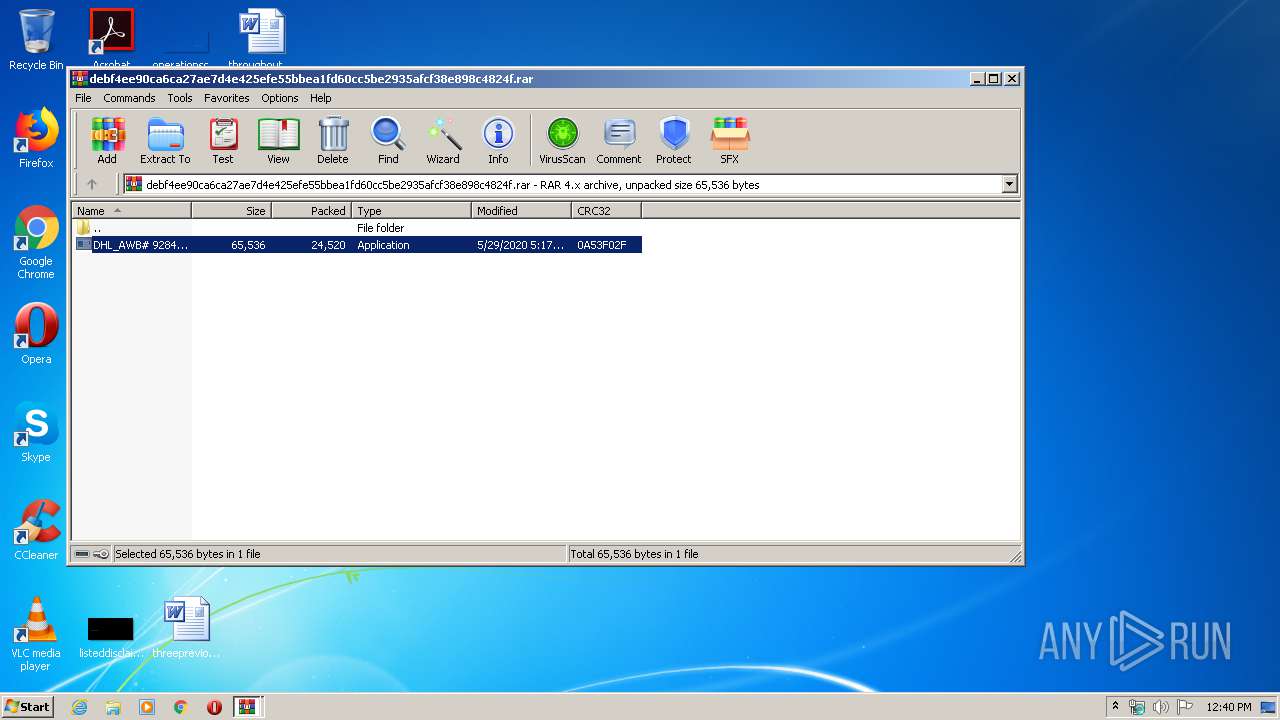
| 1932 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\debf4ee90ca6ca27ae7d4e425efe55bbea1fd60cc5be2935afcf38e898c4824f.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2192 | "C:\Windows\System32\svchost.exe" | C:\Windows\System32\svchost.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2820 | "C:\Users\admin\Desktop\DHL_AWB# 9284730931.exe" | C:\Users\admin\Desktop\DHL_AWB# 9284730931.exe | DHL_AWB# 9284730931.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 2.02 Modules
| |||||||||||||||
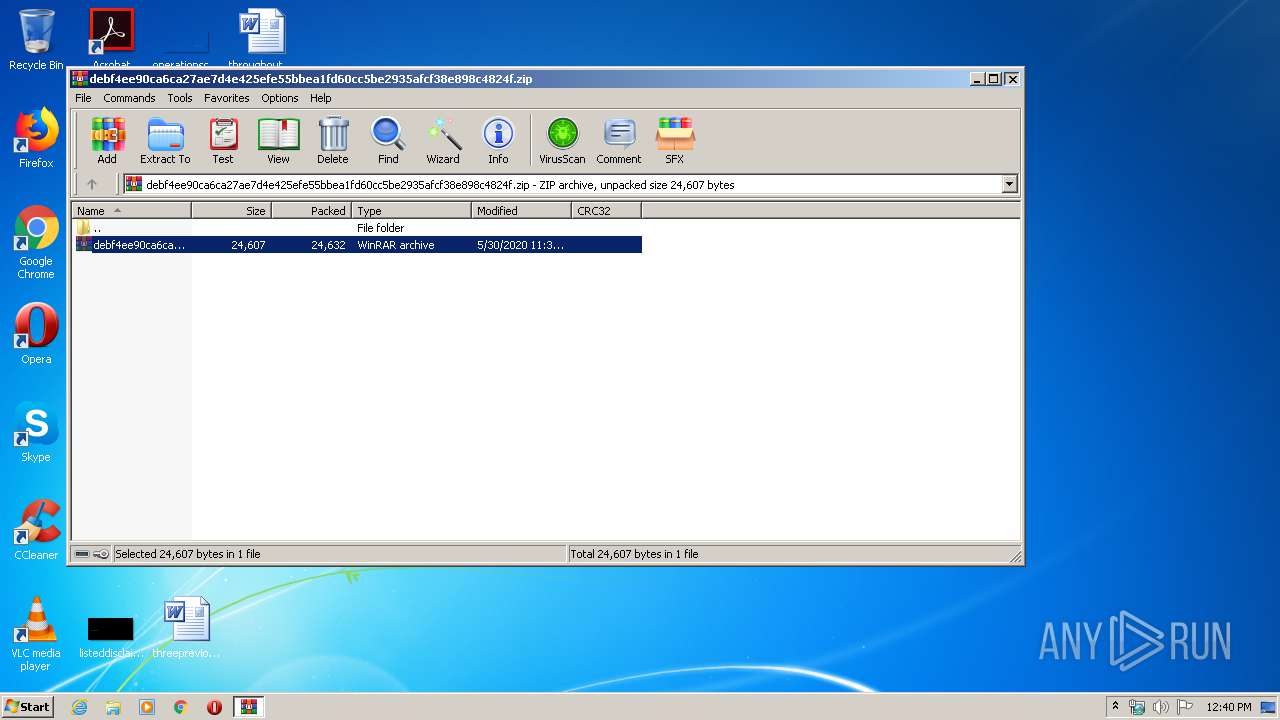
| 2916 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Rar$DIb1932.14256\debf4ee90ca6ca27ae7d4e425efe55bbea1fd60cc5be2935afcf38e898c4824f.rar | C:\Program Files\WinRAR\WinRAR.exe | WinRAR.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3144 | /c del "C:\Users\admin\Desktop\DHL_AWB# 9284730931.exe" | C:\Windows\System32\cmd.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
6 328
Read events
2 662
Write events
2 467
Delete events
1 199
Modification events
| (PID) Process: | (1932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1932) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1932) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (1932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\debf4ee90ca6ca27ae7d4e425efe55bbea1fd60cc5be2935afcf38e898c4824f.zip | |||
| (PID) Process: | (1932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (312) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | a |
Value: WinRAR.exe | |||
Executable files
1
Suspicious files
81
Text files
1
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2820 | DHL_AWB# 9284730931.exe | C:\Users\admin\AppData\Local\Temp\Cab89D6.tmp | — | |
MD5:— | SHA256:— | |||
| 2820 | DHL_AWB# 9284730931.exe | C:\Users\admin\AppData\Local\Temp\Tar89D7.tmp | — | |
MD5:— | SHA256:— | |||
| 2820 | DHL_AWB# 9284730931.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E49827401028F7A0F97B5576C77A26CB_7CE95D8DCA26FE957E7BD7D76F353B08 | der | |
MD5:— | SHA256:— | |||
| 1932 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb1932.14256\debf4ee90ca6ca27ae7d4e425efe55bbea1fd60cc5be2935afcf38e898c4824f.rar | compressed | |
MD5:— | SHA256:— | |||
| 2820 | DHL_AWB# 9284730931.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E49827401028F7A0F97B5576C77A26CB_7CE95D8DCA26FE957E7BD7D76F353B08 | binary | |
MD5:— | SHA256:— | |||
| 2192 | svchost.exe | C:\Users\admin\AppData\Roaming\JMAMR4D1\JMAlogim.jpeg | image | |
MD5:— | SHA256:— | |||
| 948 | Firefox.exe | C:\Users\admin\AppData\Roaming\JMAMR4D1\JMAlogrf.ini | binary | |
MD5:— | SHA256:— | |||
| 2192 | svchost.exe | C:\Users\admin\AppData\Roaming\JMAMR4D1\JMAlogrc.ini | binary | |
MD5:— | SHA256:— | |||
| 2916 | WinRAR.exe | C:\Users\admin\Desktop\DHL_AWB# 9284730931.exe | executable | |
MD5:DDCDC714BEDFFB59133570C3A2B7913F | SHA256:BE3E6008DDE30CB959B90A332A79931B889216A9483944DC5C0D958DEC1B8E46 | |||
| 2192 | svchost.exe | C:\Users\admin\AppData\Roaming\JMAMR4D1\JMAlogrv.ini | binary | |
MD5:BA3B6BC807D4F76794C4B81B09BB9BA5 | SHA256:6EEBF968962745B2E9DE2CA969AF7C424916D4E3FE3CC0BB9B3D414ABFCE9507 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
5
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
312 | explorer.exe | GET | — | 203.159.95.17:80 | http://www.zgmmds8.com/f23/?RLr=vXynGr9PpokEwKvpJCAzPh/5OfWF50dRGKHx+LbCEPSFsSU+I5i+AHs247TvwKjccPTDpw==&BRQl=0VvHIbaPn4fXJTG0 | TH | — | — | malicious |
2820 | DHL_AWB# 9284730931.exe | GET | 200 | 2.16.107.80:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | unknown | der | 1.37 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2820 | DHL_AWB# 9284730931.exe | 2.16.107.80:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | — | suspicious |
2820 | DHL_AWB# 9284730931.exe | 41.204.161.16:443 | qif.ac.ke | Kenya Education Network | KE | suspicious |
312 | explorer.exe | 203.159.95.17:80 | www.zgmmds8.com | — | TH | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
qif.ac.ke |
| suspicious |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
www.zgmmds8.com |
| malicious |
www.kenguy.ninja |
| unknown |
www.aroundthesix.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
312 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
1 ETPRO signatures available at the full report