| File name: | fa6b246130a460aa8915db3f56fc3735f767a5950a12d71dc3a70c400682cc41 |
| Full analysis: | https://app.any.run/tasks/179a79d7-ce58-47b6-8768-a719641c8cac |
| Verdict: | Malicious activity |
| Threats: | GuLoader is an advanced downloader written in shellcode. It’s used by criminals to distribute other malware, notably trojans, on a large scale. It’s infamous for using anti-detection and anti-analysis capabilities. |
| Analysis date: | January 10, 2025, 21:43:08 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | 6A5B8C6057DFF681139FD609FFC6B21D |
| SHA1: | B37B7A2168980B4772978A640EBF5A02F41697E6 |
| SHA256: | FA6B246130A460AA8915DB3F56FC3735F767A5950A12D71DC3A70C400682CC41 |
| SSDEEP: | 24576:tkuILYQzQ4tHX/khQ0GJLuu2sODFRrRrZQRDgQS6ZjwlxdD/g2CdaZqW7BNKTCS9:tPOYQzptHX/khQ0GJLuu2sODFRr9ZQRf |
MALICIOUS
GULOADER has been detected
- fa6b246130a460aa8915db3f56fc3735f767a5950a12d71dc3a70c400682cc41.exe (PID: 936)
Steals credentials from Web Browsers
- Bivejens.exe (PID: 5788)
Actions looks like stealing of personal data
- Bivejens.exe (PID: 5788)
SNAKEKEYLOGGER has been detected (SURICATA)
- Bivejens.exe (PID: 5788)
SUSPICIOUS
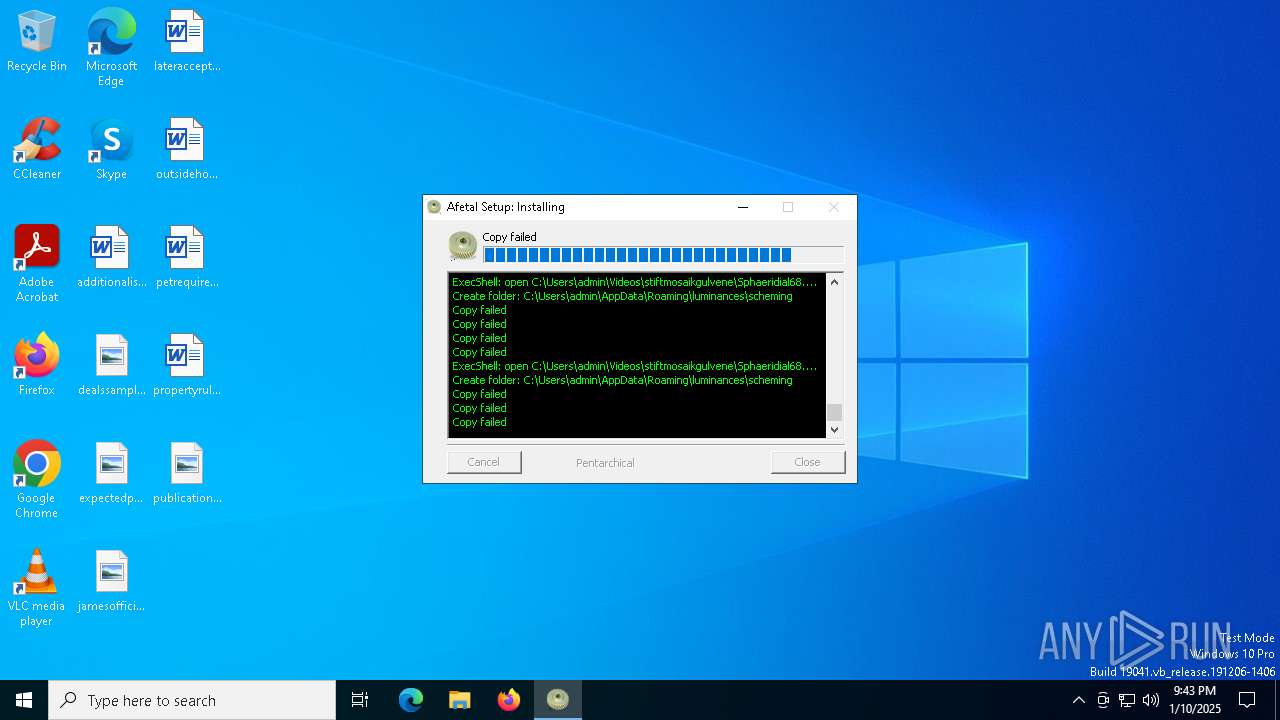
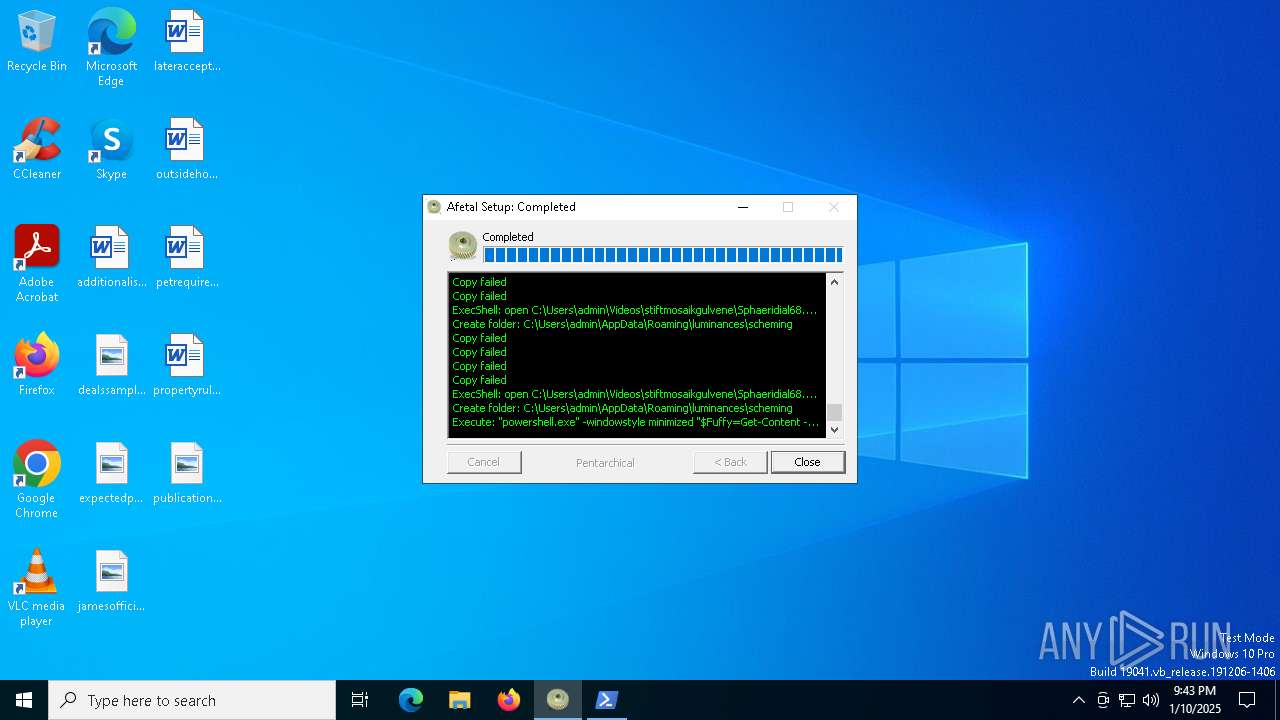
Starts POWERSHELL.EXE for commands execution
- fa6b246130a460aa8915db3f56fc3735f767a5950a12d71dc3a70c400682cc41.exe (PID: 936)
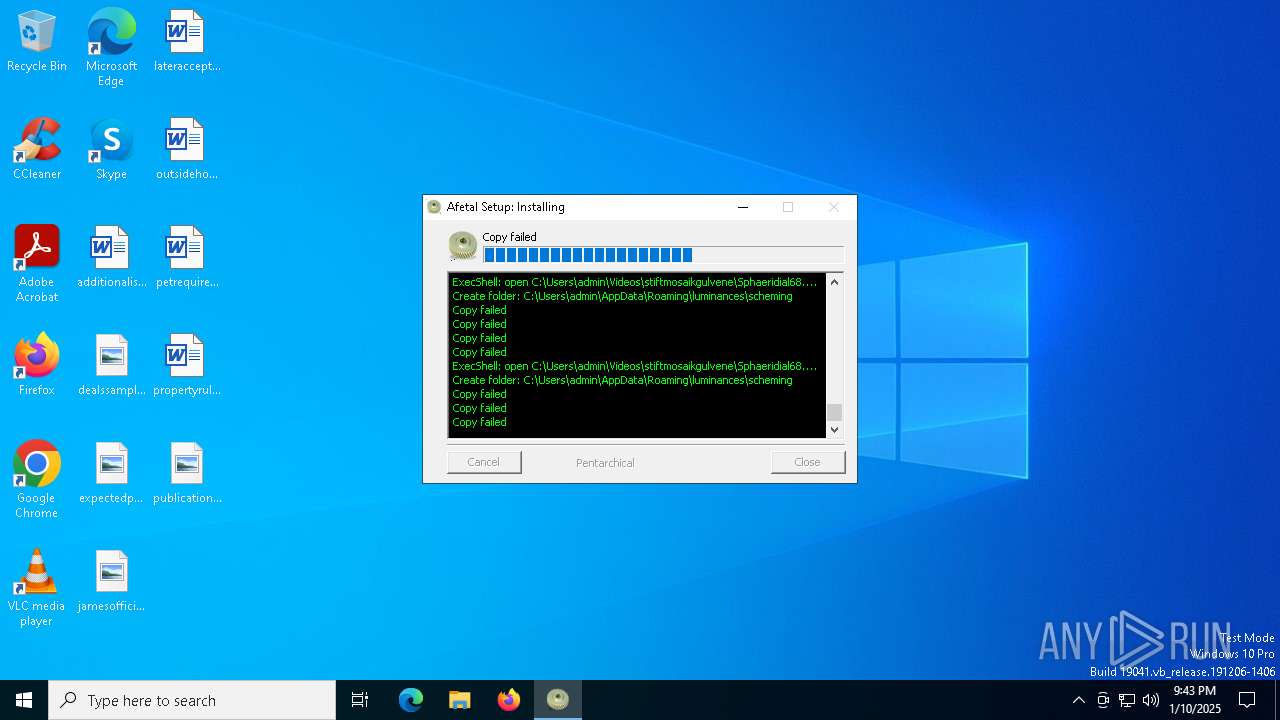
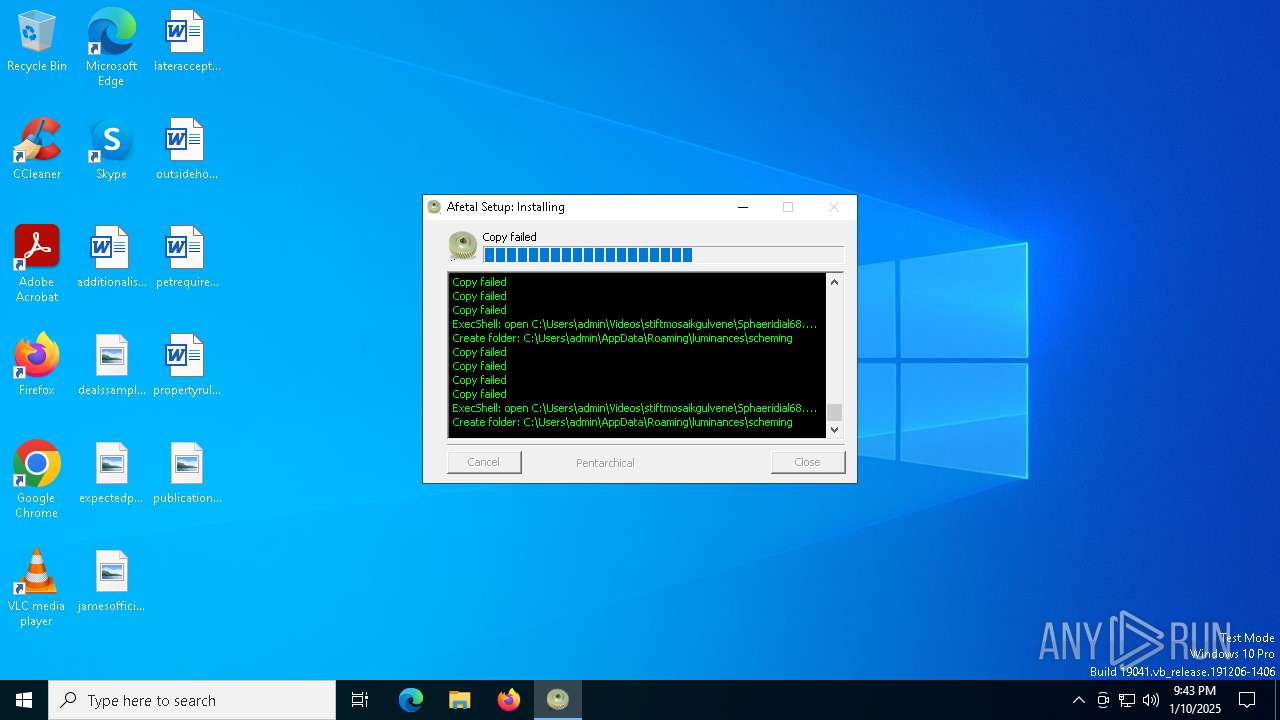
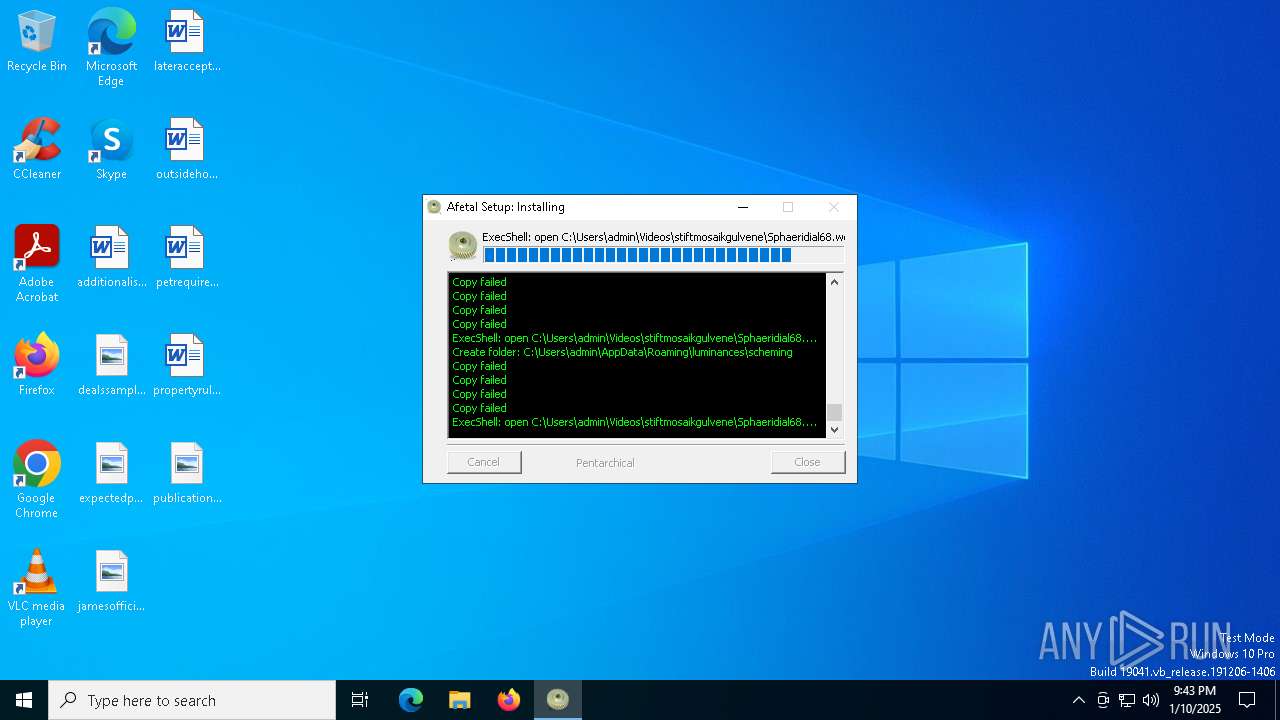
Executable content was dropped or overwritten
- powershell.exe (PID: 7116)
Checks Windows Trust Settings
- Bivejens.exe (PID: 5788)
Reads security settings of Internet Explorer
- Bivejens.exe (PID: 5788)
Checks for external IP
- svchost.exe (PID: 2192)
- Bivejens.exe (PID: 5788)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- Bivejens.exe (PID: 5788)
The process verifies whether the antivirus software is installed
- Bivejens.exe (PID: 5788)
Converts a specified value to a byte (POWERSHELL)
- powershell.exe (PID: 7116)
INFO
Create files in a temporary directory
- fa6b246130a460aa8915db3f56fc3735f767a5950a12d71dc3a70c400682cc41.exe (PID: 936)
Reads the computer name
- fa6b246130a460aa8915db3f56fc3735f767a5950a12d71dc3a70c400682cc41.exe (PID: 936)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 7116)
The sample compiled with english language support
- fa6b246130a460aa8915db3f56fc3735f767a5950a12d71dc3a70c400682cc41.exe (PID: 936)
- powershell.exe (PID: 7116)
The executable file from the user directory is run by the Powershell process
- Bivejens.exe (PID: 5788)
Reads the machine GUID from the registry
- Bivejens.exe (PID: 5788)
Reads the software policy settings
- Bivejens.exe (PID: 5788)
Checks proxy server information
- Bivejens.exe (PID: 5788)
Creates files or folders in the user directory
- Bivejens.exe (PID: 5788)
Checks supported languages
- Bivejens.exe (PID: 5788)
- fa6b246130a460aa8915db3f56fc3735f767a5950a12d71dc3a70c400682cc41.exe (PID: 936)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 7116)
Attempting to use instant messaging service
- Bivejens.exe (PID: 5788)
- svchost.exe (PID: 2192)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7116)
Gets data length (POWERSHELL)
- powershell.exe (PID: 7116)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 7116)
The process uses the downloaded file
- powershell.exe (PID: 7116)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:12:15 22:24:27+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25600 |
| InitializedDataSize: | 141824 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x3359 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.1.0.0 |
| ProductVersionNumber: | 3.1.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comments: | dusren barcarole sulcalize |
| CompanyName: | alarmsystems |
| FileDescription: | udstykningsplan uidentificerbares vrdipapircentralerne |
| FileVersion: | 3.1.0.0 |
| LegalCopyright: | dulcigenic asterix |
| LegalTrademarks: | civilisationer markild goalless |
| ProductName: | bristly sublustrously frgende |
Total processes
129
Monitored processes
5
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 936 | "C:\Users\admin\AppData\Local\Temp\fa6b246130a460aa8915db3f56fc3735f767a5950a12d71dc3a70c400682cc41.exe" | C:\Users\admin\AppData\Local\Temp\fa6b246130a460aa8915db3f56fc3735f767a5950a12d71dc3a70c400682cc41.exe | explorer.exe | ||||||||||||
User: admin Company: alarmsystems Integrity Level: MEDIUM Description: udstykningsplan uidentificerbares vrdipapircentralerne Exit code: 4294967295 Version: 3.1.0.0 Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5788 | "C:\Users\admin\AppData\Local\Temp\Bivejens.exe" | C:\Users\admin\AppData\Local\Temp\Bivejens.exe | powershell.exe | ||||||||||||
User: admin Company: alarmsystems Integrity Level: MEDIUM Description: udstykningsplan uidentificerbares vrdipapircentralerne Version: 3.1.0.0 Modules
| |||||||||||||||
| 7116 | "powershell.exe" -windowstyle minimized "$Fuffy=Get-Content -Raw 'C:\Users\admin\AppData\Local\Temp\depersonaliseredes\Thalamiflorous.Tus209';$Antigenes=$Fuffy.SubString(5130,3);.$Antigenes($Fuffy)" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | fa6b246130a460aa8915db3f56fc3735f767a5950a12d71dc3a70c400682cc41.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7132 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
9 539
Read events
9 522
Write events
17
Delete events
0
Modification events
| (PID) Process: | (936) fa6b246130a460aa8915db3f56fc3735f767a5950a12d71dc3a70c400682cc41.exe | Key: | HKEY_CURRENT_USER\skurestriber\Absee |
| Operation: | write | Name: | grandevous |
Value: %islandhood%\oveni\restaureredes.con | |||
| (PID) Process: | (5788) Bivejens.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Bivejens_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (5788) Bivejens.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Bivejens_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (5788) Bivejens.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Bivejens_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (5788) Bivejens.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Bivejens_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (5788) Bivejens.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Bivejens_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (5788) Bivejens.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Bivejens_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (5788) Bivejens.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Bivejens_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (5788) Bivejens.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Bivejens_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (5788) Bivejens.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Bivejens_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
Executable files
1
Suspicious files
14
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7116 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_sibsf34v.yjd.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7116 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_nhg1apj4.wcy.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 936 | fa6b246130a460aa8915db3f56fc3735f767a5950a12d71dc3a70c400682cc41.exe | C:\Users\admin\AppData\Local\Temp\depersonaliseredes\Ceylonteer.kae | binary | |
MD5:03ADD5EC69F2D821F4BDDF502603364B | SHA256:A8850B76F116EB91305228F5F39B2B6152927531705DE707A60FC74B86DF4003 | |||
| 936 | fa6b246130a460aa8915db3f56fc3735f767a5950a12d71dc3a70c400682cc41.exe | C:\Users\admin\AppData\Local\Temp\depersonaliseredes\udsds.aut | binary | |
MD5:152C1126D35B77FC957526436ADBEA38 | SHA256:67780594962B62DD23C55340C9AB1CD11858C15F464E8EE312A690A1759EAFD3 | |||
| 7116 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_wsj5tmpd.zhq.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5788 | Bivejens.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:92B839135741069B05829B07B6F3F3FB | SHA256:4AE12FEDBB424DA1938E2BF5B343DC175D9CDAAFD4123715BE68DDA9BB2F18C5 | |||
| 7116 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:5F62DFB53E47D6CD6715ABE772A855F8 | SHA256:C327736DF96A1BC7AC8A64CFC9935A7665EE601ACCC469BAB24E3822FA7AEFC0 | |||
| 5788 | Bivejens.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:EE5C62327FF47D2307DAE0C8FD4F17CE | SHA256:75C84F3E15E8DF1CEEB75FEFB392F1B630C174AAE4CBD03885490C80C5E32D18 | |||
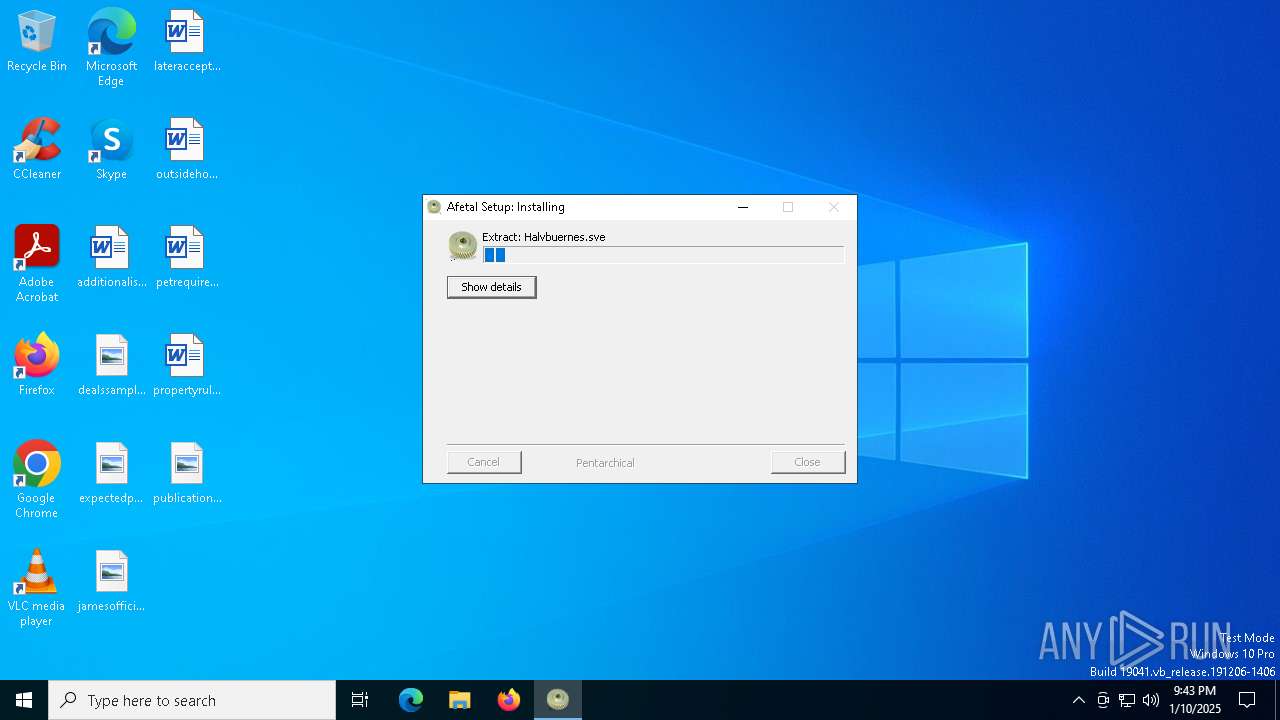
| 936 | fa6b246130a460aa8915db3f56fc3735f767a5950a12d71dc3a70c400682cc41.exe | C:\Users\admin\AppData\Local\Temp\depersonaliseredes\Halvbuernes.sve | binary | |
MD5:3EC09CE77D7046B1B0A4108EA6AAC00D | SHA256:1E5A50C09CA254DC572C08BC87F596EBF2AE2CCB09EF355BD34A1A7A2B4E1BEF | |||
| 936 | fa6b246130a460aa8915db3f56fc3735f767a5950a12d71dc3a70c400682cc41.exe | C:\Users\admin\AppData\Local\Temp\depersonaliseredes\Fleece.kar | binary | |
MD5:8A6A8A75FE9A08909B09C7242C1B0C73 | SHA256:1AAD58A3F50A3EF4E50AFCECBAF81D840F4E3F0C512BCC5844A1AEC594A06FF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
41
DNS requests
27
Threats
19
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2356 | svchost.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2356 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5788 | Bivejens.exe | GET | 200 | 172.217.16.195:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | — | — | whitelisted |
5788 | Bivejens.exe | GET | 200 | 172.217.16.195:80 | http://c.pki.goog/r/r1.crl | unknown | — | — | whitelisted |
5788 | Bivejens.exe | GET | 200 | 172.217.16.195:80 | http://o.pki.goog/wr2/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRTQtSEi8EX%2BbYUTXd8%2ByMxD3s1zQQU3hse7XkV1D43JMMhu%2Bw0OW1CsjACEQCtrC6LRgin8QlSmIIYAEvj | unknown | — | — | whitelisted |
5788 | Bivejens.exe | GET | 200 | 172.217.16.195:80 | http://o.pki.goog/wr2/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRTQtSEi8EX%2BbYUTXd8%2ByMxD3s1zQQU3hse7XkV1D43JMMhu%2Bw0OW1CsjACEQDREXAZkIcRFgn9FoWvtnQ0 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2356 | svchost.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2356 | svchost.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.23.227.215:443 | www.bing.com | Ooredoo Q.S.C. | QA | whitelisted |
1176 | svchost.exe | 20.190.159.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1076 | svchost.exe | 184.28.89.167:443 | go.microsoft.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
drive.google.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Query (checkip .dyndns .org) |
5788 | Bivejens.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup - checkip.dyndns.org |
5788 | Bivejens.exe | Device Retrieving External IP Address Detected | ET INFO 404/Snake/Matiex Keylogger Style External IP Check |
2192 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Address Lookup Domain (reallyfreegeoip .org) |
2192 | svchost.exe | Misc activity | ET INFO External IP Address Lookup Domain in DNS Lookup (reallyfreegeoip .org) |
5788 | Bivejens.exe | Misc activity | ET INFO External IP Lookup Service Domain (reallyfreegeoip .org) in TLS SNI |
5788 | Bivejens.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup - checkip.dyndns.org |
5788 | Bivejens.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup - checkip.dyndns.org |
5788 | Bivejens.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup - checkip.dyndns.org |
5788 | Bivejens.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup - checkip.dyndns.org |