| download: | /a.txt |
| Full analysis: | https://app.any.run/tasks/d7de978e-221b-4c86-9c60-8925c64d7be0 |
| Verdict: | Malicious activity |
| Threats: | Quasar is a very popular RAT in the world thanks to its code being available in open-source. This malware can be used to control the victim’s computer remotely. |
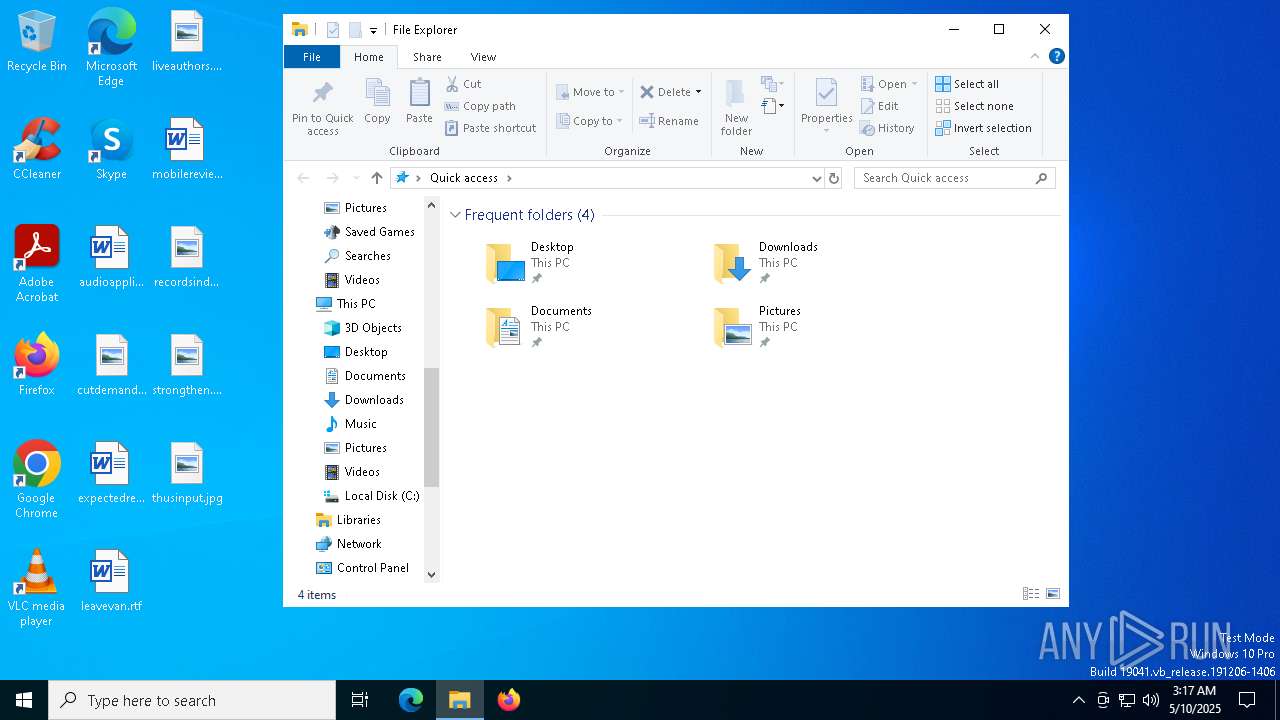
| Analysis date: | May 10, 2025, 03:15:14 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | Unicode text, UTF-8 text, with CRLF line terminators |
| MD5: | 58A7D973F891FBC97465297658DF8A09 |
| SHA1: | 017111C6D444DC3918E2A6CB5CE51BAD27531B87 |
| SHA256: | FA5F135ED7A868A15E0F79EE4CEBAD77428E8B24B99E90900F14CABEEA4F2060 |
| SSDEEP: | 48:Ye/ihbbM5oM92zKu2Gldw4bvfEQ/V3SpdfcSaFAzSGOgrHMu/mPROc59HeF:1ih/qowuN1LE5bfcSaFMSGO+F/mPEcQ |
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 3100)
- powershell.exe (PID: 1676)
- powershell.exe (PID: 6080)
- powershell.exe (PID: 1188)
Changes powershell execution policy (Bypass)
- powershell.exe (PID: 3100)
- powershell.exe (PID: 1676)
- msiexec.exe (PID: 3800)
Run PowerShell with an invisible window
- powershell.exe (PID: 6080)
Changes Windows Defender settings
- cmd.exe (PID: 1272)
- cmd.exe (PID: 4056)
- cmd.exe (PID: 5124)
Adds path to the Windows Defender exclusion list
- powershell.exe (PID: 1188)
- cmd.exe (PID: 4056)
- Launch.exe (PID: 5156)
- cmd.exe (PID: 5124)
Changes settings for sending potential threat samples to Microsoft servers
- powershell.exe (PID: 6660)
Uses Task Scheduler to autorun other applications
- cmd.exe (PID: 6944)
Starts REAGENTC.EXE to disable the Windows Recovery Environment
- ReAgentc.exe (PID: 5312)
Connects to the CnC server
- communication.exe (PID: 2840)
QUASAR has been detected (SURICATA)
- communication.exe (PID: 2840)
SUSPICIOUS
Uses ATTRIB.EXE to modify file attributes
- powershell.exe (PID: 3100)
- powershell.exe (PID: 1188)
Gets path to any of the special folders (POWERSHELL)
- powershell.exe (PID: 3100)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 3100)
Possibly malicious use of IEX has been detected
- powershell.exe (PID: 3100)
- powershell.exe (PID: 1676)
- msiexec.exe (PID: 3800)
Checks a user's role membership (POWERSHELL)
- powershell.exe (PID: 3100)
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 3100)
- powershell.exe (PID: 1676)
- msiexec.exe (PID: 3800)
- powershell.exe (PID: 6080)
- cmd.exe (PID: 1272)
- cmd.exe (PID: 4056)
- cmd.exe (PID: 5124)
- wcm.exe (PID: 3956)
Application launched itself
- powershell.exe (PID: 3100)
- powershell.exe (PID: 1676)
- powershell.exe (PID: 6080)
PowerShell delay command usage (probably sleep evasion)
- powershell.exe (PID: 6080)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 5964)
- cmd.exe (PID: 5608)
- cmd.exe (PID: 4572)
- cmd.exe (PID: 4120)
- cmd.exe (PID: 660)
- cmd.exe (PID: 3760)
- cmd.exe (PID: 2096)
- cmd.exe (PID: 4376)
- cmd.exe (PID: 1600)
- cmd.exe (PID: 5292)
- cmd.exe (PID: 4120)
- cmd.exe (PID: 5848)
- cmd.exe (PID: 4728)
- cmd.exe (PID: 6228)
- cmd.exe (PID: 1764)
- cmd.exe (PID: 900)
- cmd.exe (PID: 4944)
- cmd.exe (PID: 6512)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 6080)
- powershell.exe (PID: 1188)
- Launch.exe (PID: 5156)
- wcm.exe (PID: 3956)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 6080)
The process hides Powershell's copyright startup banner
- powershell.exe (PID: 6080)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 1244)
- msiexec.exe (PID: 3800)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 1244)
Runs shell command (SCRIPT)
- msiexec.exe (PID: 3800)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 6080)
Creates new GUID (POWERSHELL)
- powershell.exe (PID: 1188)
Found strings related to reading or modifying Windows Defender settings
- powershell.exe (PID: 1188)
- wcm.exe (PID: 3956)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 4056)
- cmd.exe (PID: 5124)
Probably fake Windows Update
- netsh.exe (PID: 3020)
- cmd.exe (PID: 5308)
Executable content was dropped or overwritten
- Launch.exe (PID: 5156)
- powershell.exe (PID: 1188)
- wcm.exe (PID: 3956)
The executable file from the user directory is run by the CMD process
- wcm.exe (PID: 3956)
- communication.exe (PID: 2840)
Windows service management via SC.EXE
- sc.exe (PID: 7152)
- sc.exe (PID: 1452)
- sc.exe (PID: 5344)
- sc.exe (PID: 5936)
- sc.exe (PID: 6744)
Stops a currently running service
- sc.exe (PID: 3800)
- sc.exe (PID: 5328)
- sc.exe (PID: 5860)
- sc.exe (PID: 6964)
- sc.exe (PID: 5520)
Uses NETSH.EXE to add a firewall rule or allowed programs
- cmd.exe (PID: 5308)
Modifies existing scheduled task
- schtasks.exe (PID: 2408)
- schtasks.exe (PID: 2268)
- schtasks.exe (PID: 5964)
- schtasks.exe (PID: 6708)
- schtasks.exe (PID: 920)
- schtasks.exe (PID: 6476)
- schtasks.exe (PID: 7000)
- schtasks.exe (PID: 3364)
Query Microsoft Defender preferences
- wcm.exe (PID: 3956)
Contacting a server suspected of hosting an CnC
- communication.exe (PID: 2840)
Checks for external IP
- svchost.exe (PID: 2196)
Connects to unusual port
- communication.exe (PID: 2840)
INFO
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 3100)
Gets or sets the time when the file was last written to (POWERSHELL)
- powershell.exe (PID: 3100)
Disables trace logs
- powershell.exe (PID: 3100)
- powershell.exe (PID: 1676)
- powershell.exe (PID: 6080)
- powershell.exe (PID: 3364)
Checks proxy server information
- powershell.exe (PID: 3100)
- powershell.exe (PID: 1676)
- powershell.exe (PID: 6080)
- slui.exe (PID: 5212)
- powershell.exe (PID: 3364)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 3100)
- powershell.exe (PID: 6660)
- powershell.exe (PID: 5624)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 3100)
Gets data length (POWERSHELL)
- powershell.exe (PID: 3100)
Reads the software policy settings
- slui.exe (PID: 3900)
- slui.exe (PID: 5212)
- msiexec.exe (PID: 1244)
Reads the computer name
- msiexec.exe (PID: 1244)
- msiexec.exe (PID: 3800)
Creates a software uninstall entry
- msiexec.exe (PID: 1244)
Executable content was dropped or overwritten
- msiexec.exe (PID: 1244)
Checks supported languages
- msiexec.exe (PID: 1244)
- msiexec.exe (PID: 3800)
Process checks computer location settings
- msiexec.exe (PID: 3800)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6660)
- powershell.exe (PID: 5624)
Potential access to remote process (Base64 Encoded 'OpenProcess')
- powershell.exe (PID: 1188)
Potential remote process memory reading (Base64 Encoded 'ReadProcessMemory')
- powershell.exe (PID: 1188)
Potential remote process memory writing (Base64 Encoded 'WriteProcessMemory')
- powershell.exe (PID: 1188)
The executable file from the user directory is run by the Powershell process
- Launch.exe (PID: 5156)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
297
Monitored processes
162
Malicious processes
13
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 240 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 444 | REG ADD "HKLM\SOFTWARE\Policies\Microsoft\Windows\WindowsUpdate\AU" /v "NoAutoUpdate" /t REG_DWORD /d 1 /f | C:\Windows\SysWOW64\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 660 | "C:\WINDOWS\system32\cmd.exe" /c reg add "HKCU\Software\Microsoft" /v "Version" /t REG_SZ /d f6247d2f2d /f | C:\Windows\SysWOW64\cmd.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 736 | reagentc /info | C:\Windows\SysWOW64\ReAgentc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Windows Recovery Agent Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 744 | REG ADD "HKLM\SOFTWARE\Policies\Microsoft\Windows\WindowsUpdate" /v "DisableWindowsUpdateAccess" /t REG_DWORD /d 1 /f | C:\Windows\SysWOW64\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 776 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 788 | reg add "HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Recovery" /v "Rollback" /t REG_DWORD /d 0 /f | C:\Windows\SysWOW64\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 788 | "C:\Windows\SysWOW64\cmd.exe" /c "sc stop WaaSMedicSvc" | C:\Windows\SysWOW64\cmd.exe | — | wcm.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1062 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 840 | "C:\Windows\SysWOW64\cmd.exe" /c "schtasks /Change /TN "Microsoft\Windows\WindowsUpdate\Scheduled Start" /Disable" | C:\Windows\SysWOW64\cmd.exe | — | wcm.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 900 | "C:\Windows\SysWOW64\cmd.exe" /c "REG ADD "HKLM\SOFTWARE\Policies\Microsoft\Windows\WindowsUpdate\AU" /v "NoAutoUpdate" /t REG_DWORD /d 1 /f" | C:\Windows\SysWOW64\cmd.exe | — | wcm.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
64 352
Read events
64 100
Write events
174
Delete events
78
Modification events
| (PID) Process: | (6080) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\PowerShell\1\ShellIds\Microsoft.PowerShell |
| Operation: | write | Name: | ExecutionPolicy |
Value: Bypass | |||
| (PID) Process: | (2332) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft |
| Operation: | write | Name: | App |
Value: crypto | |||
| (PID) Process: | (5056) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft |
| Operation: | write | Name: | Application |
Value: Yes | |||
| (PID) Process: | (1244) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1244) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1244) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1244) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1244) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: DC040000C6A8DD195AC1DB01 | |||
| (PID) Process: | (1244) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 469EC4D63FDFFA04E236C0FB170A5FCE960D5391918EFFC3600FE5E28DE6A16B | |||
| (PID) Process: | (1244) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
Executable files
5
Suspicious files
27
Text files
36
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
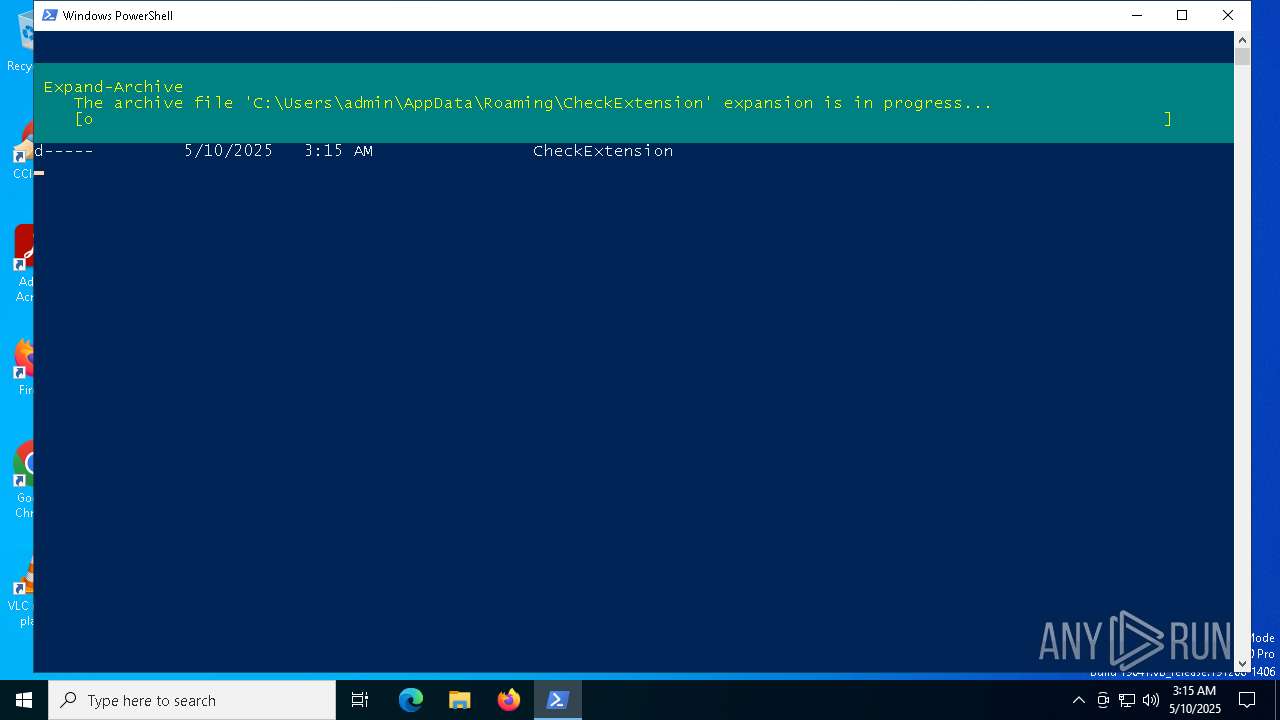
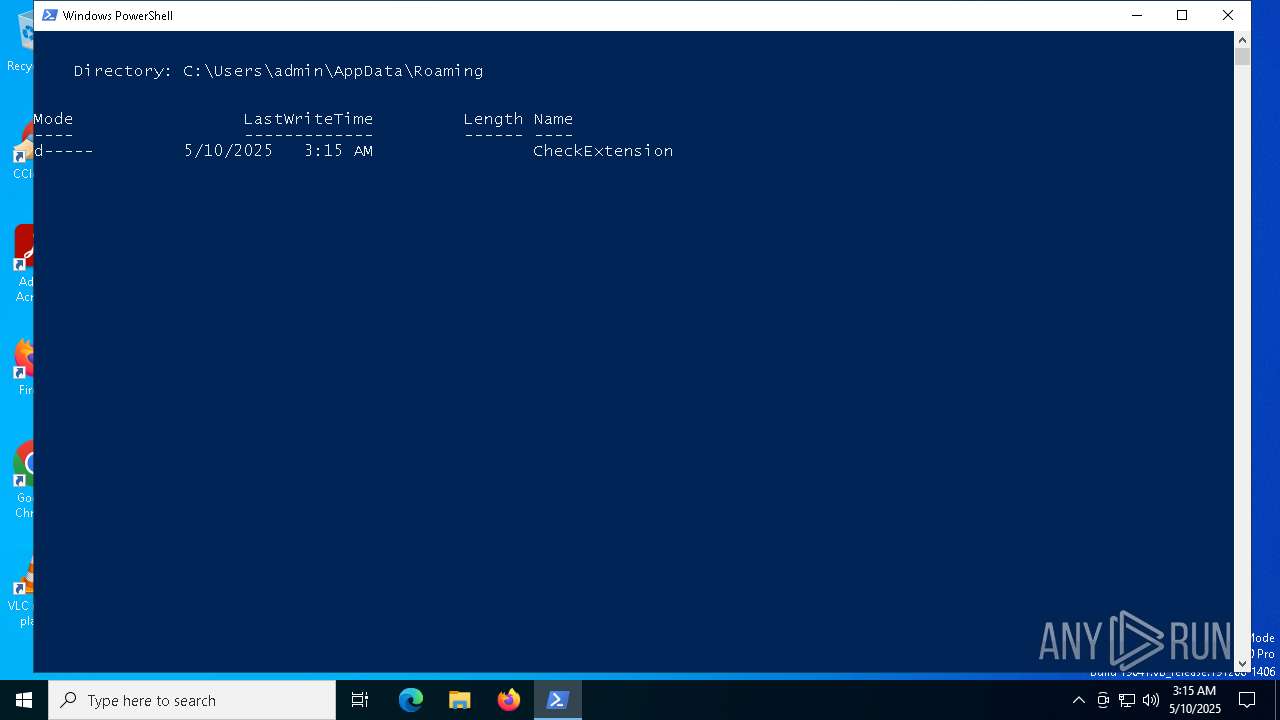
| 3100 | powershell.exe | C:\Users\admin\AppData\Roaming\CheckExtension\h.js | — | |
MD5:— | SHA256:— | |||
| 3100 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF10b901.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 3100 | powershell.exe | C:\Users\admin\AppData\Roaming\CheckExtension\manifest.json | binary | |
MD5:6FA1FEE1DF920D495850CD243D3C8838 | SHA256:A87D9892AB2130894081A8AE2C3B948E14812ADEC93CC194D9B8A3F5CCDAFABA | |||
| 3100 | powershell.exe | C:\Users\admin\AppData\Roaming\CheckExtension\invisible.png | binary | |
MD5:A13C7FB9DD0F88E3F9245A4F7DFD20CD | SHA256:44665F38BF2BB4650925EF4C7B28DCA22ABB3C36DBA6BEAF244FDA0B49D5879E | |||
| 3100 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_psoq2jth.3p3.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3100 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\7HNR3LP0FQFAKLTM03LB.temp | binary | |
MD5:F2204848F88032740B374709C37405D6 | SHA256:1F90FDFFF4B2333EFE14A27CA9D2F2A78AC6606B9FF0C40511D71C4796DC942A | |||
| 3100 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:F2204848F88032740B374709C37405D6 | SHA256:1F90FDFFF4B2333EFE14A27CA9D2F2A78AC6606B9FF0C40511D71C4796DC942A | |||
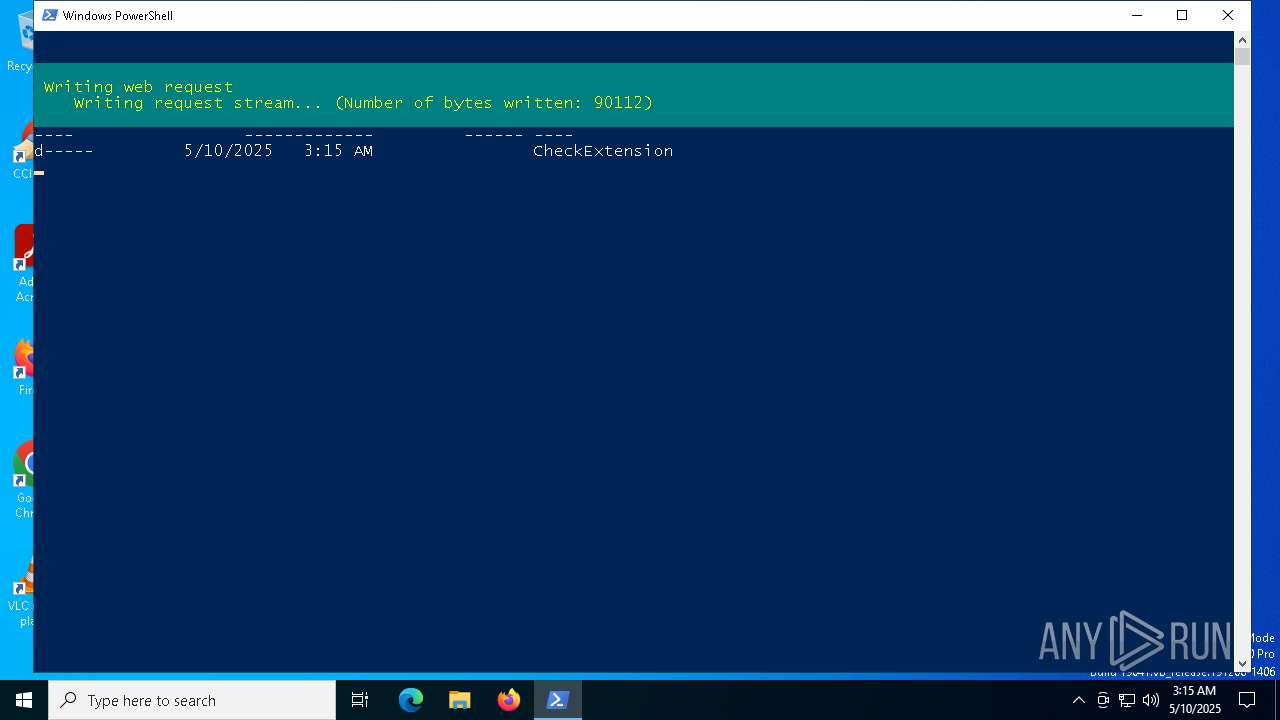
| 3100 | powershell.exe | C:\Users\admin\AppData\Local\Temp\extension.zip | compressed | |
MD5:D27B34A314E362B6AB34F765A114F61F | SHA256:234BD31617000B0665244164371028F870711241B9C70FA38DDA03BC449274DE | |||
| 3100 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_wm5ikr0i.x0z.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3100 | powershell.exe | C:\Users\admin\AppData\Roaming\CheckExtension\content.js | text | |
MD5:B29E93B5CC3387AAFF9B57477ED96B68 | SHA256:136B821F69EAC70BA81B12C5C08A418D73178F8FD1C1882DEFE5CC67E5ADE7BB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
90
DNS requests
26
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 868 b | whitelisted |
6512 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
6512 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 407 b | whitelisted |
— | — | GET | 200 | 23.216.77.31:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.216.77.31:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 40.126.31.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
3100 | powershell.exe | 66.29.153.87:443 | solidity.bot | NAMECHEAP-NET | US | unknown |
2112 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
solidity.bot |
| unknown |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET INFO External IP Lookup Domain in DNS Lookup (ipwho .is) |
2840 | communication.exe | Domain Observed Used for C2 Detected | ET MALWARE Generic AsyncRAT/zgRAT Style SSL Cert |
2840 | communication.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Malicious SSL Cert (Quasar CnC) |
2840 | communication.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] QuasarRAT Successful Connection (GCM_SHA384) |