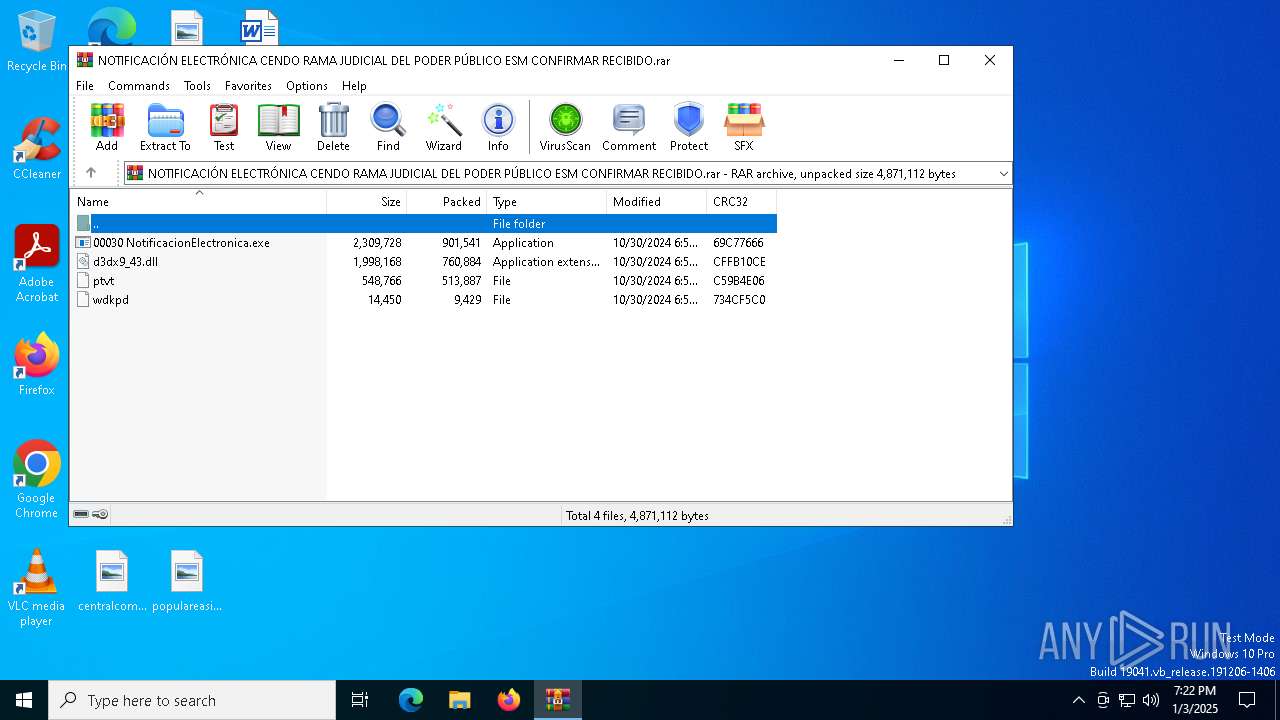
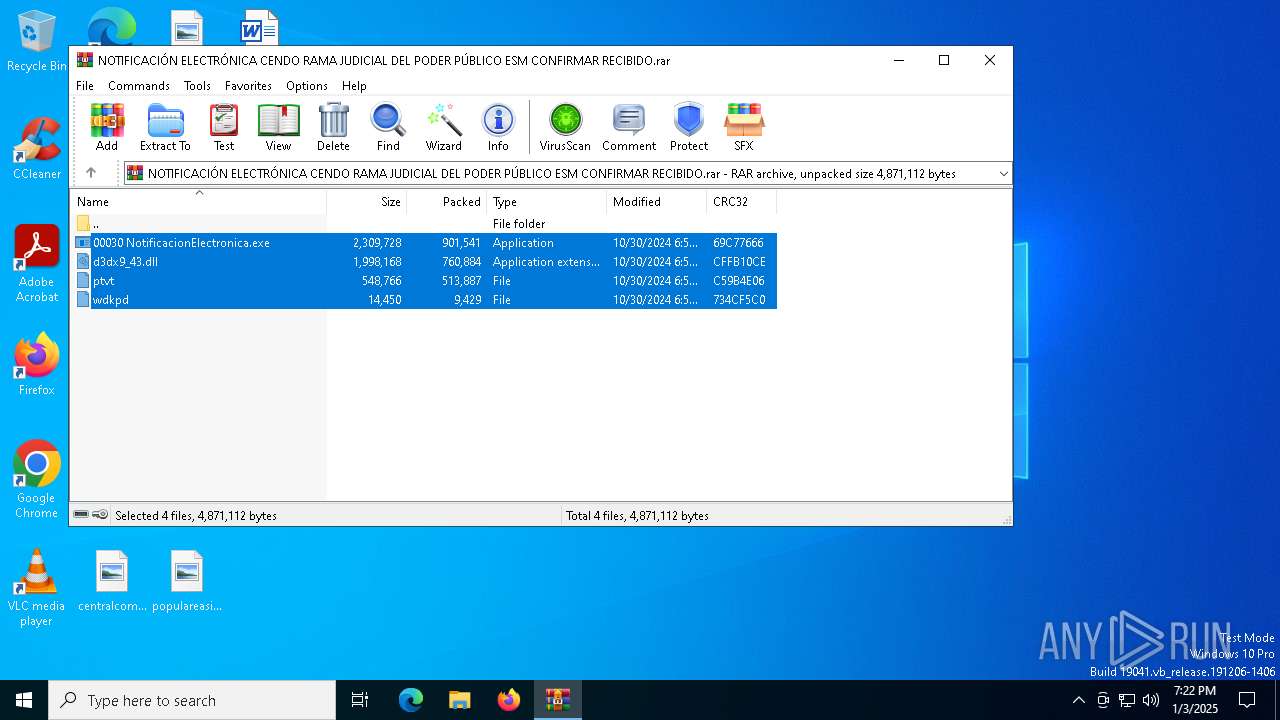
| File name: | NOTIFICACIÓN ELECTRÓNICA CENDO RAMA JUDICIAL DEL PODER PÚBLICO ESM CONFIRMAR RECIBIDO.rar |
| Full analysis: | https://app.any.run/tasks/a011154e-2028-40fc-a1c6-418d5e09f91d |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | January 03, 2025, 19:22:37 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 811866D4C0BCD902DFA2D7889C4D3E63 |
| SHA1: | 9734AB27CAC44A576F9C48545BF27FF63D210861 |
| SHA256: | FA4543923DAE10BCF173BCAB1A8218AA0B1699980235F91DB04F9FC7480CCCE2 |
| SSDEEP: | 98304:8A/Rp/wbRWEaqRv7G8aemPRNdb6UJmIx1mZIxN3iA65FsKsIVsE+eoZnmqbPHHiy:LcC |
MALICIOUS
Generic archive extractor
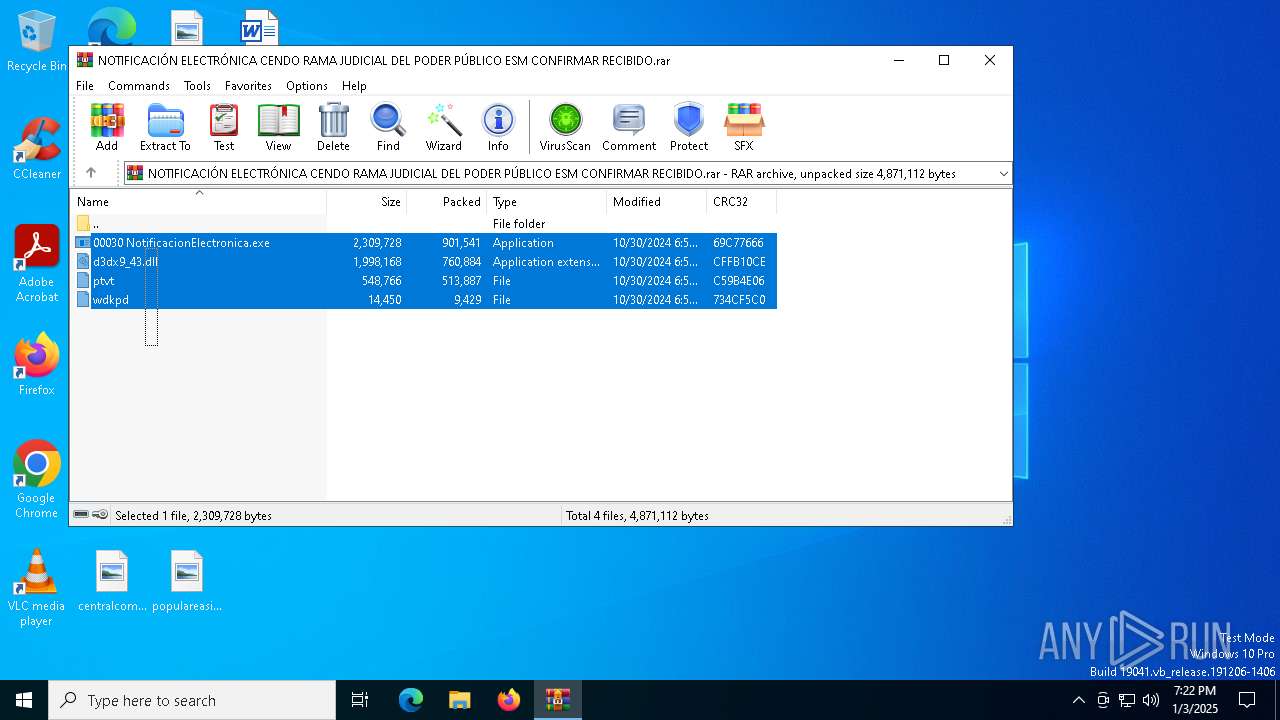
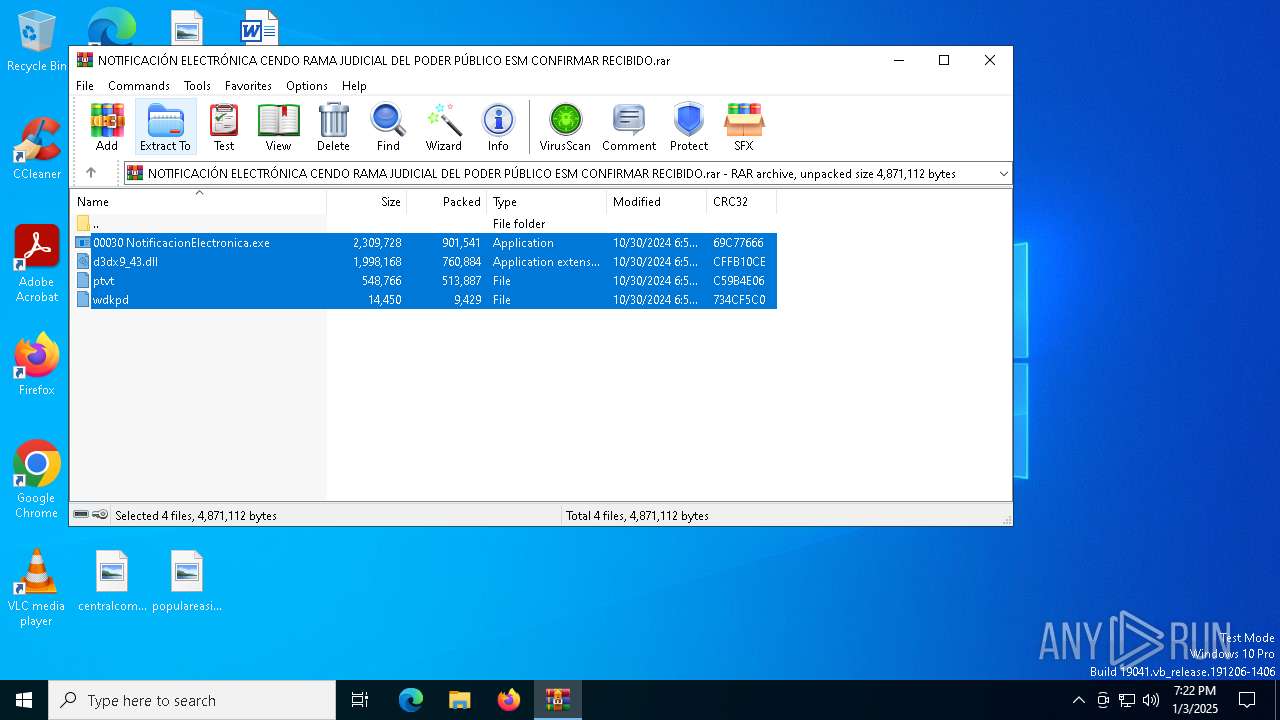
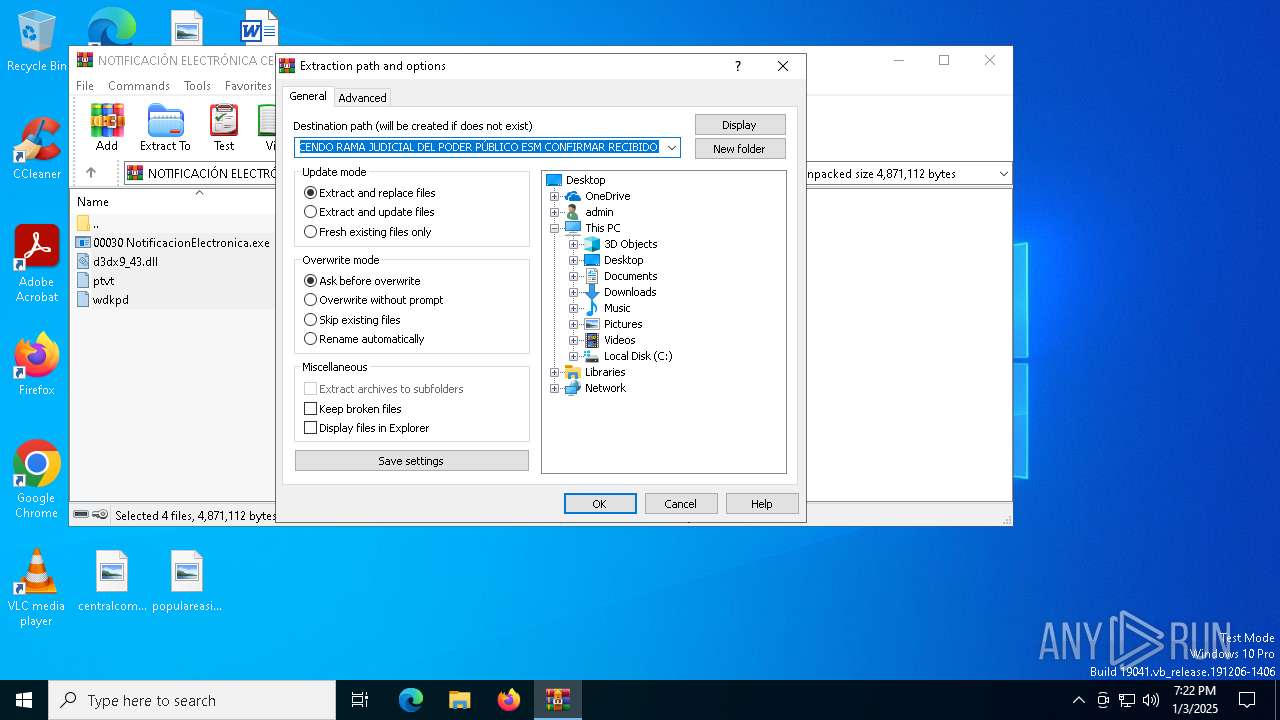
- WinRAR.exe (PID: 6628)
Executing a file with an untrusted certificate
- 00030 NotificacionElectronica.exe (PID: 3552)
ASYNCRAT has been detected (MUTEX)
- MSBuild.exe (PID: 1488)
HIJACKLOADER has been detected (YARA)
- 00030 NotificacionElectronica.exe (PID: 3552)
ASYNCRAT has been detected (YARA)
- MSBuild.exe (PID: 1488)
SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 6628)
- 00030 NotificacionElectronica.exe (PID: 3552)
Executable content was dropped or overwritten
- 00030 NotificacionElectronica.exe (PID: 3552)
Starts CMD.EXE for commands execution
- 00030 NotificacionElectronica.exe (PID: 3552)
Connects to unusual port
- MSBuild.exe (PID: 1488)
INFO
Creates files or folders in the user directory
- 00030 NotificacionElectronica.exe (PID: 3552)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6628)
The sample compiled with english language support
- WinRAR.exe (PID: 6628)
- 00030 NotificacionElectronica.exe (PID: 3552)
The process uses the downloaded file
- WinRAR.exe (PID: 6628)
Reads the computer name
- 00030 NotificacionElectronica.exe (PID: 3552)
- MSBuild.exe (PID: 1488)
Manual execution by a user
- 00030 NotificacionElectronica.exe (PID: 3552)
Checks supported languages
- 00030 NotificacionElectronica.exe (PID: 3552)
- MSBuild.exe (PID: 1488)
Create files in a temporary directory
- 00030 NotificacionElectronica.exe (PID: 3552)
Reads the machine GUID from the registry
- MSBuild.exe (PID: 1488)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 9429 |
| UncompressedSize: | 14450 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | wdkpd |
Total processes
131
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1488 | C:\WINDOWS\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSBuild.exe Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3552 | "C:\Users\admin\Desktop\00030 NotificacionElectronica.exe" | C:\Users\admin\Desktop\00030 NotificacionElectronica.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 3732 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5404 | C:\WINDOWS\SysWOW64\cmd.exe | C:\Windows\SysWOW64\cmd.exe | — | 00030 NotificacionElectronica.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6628 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\NOTIFICACIÓN ELECTRÓNICA CENDO RAMA JUDICIAL DEL PODER PÚBLICO ESM CONFIRMAR RECIBIDO.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
3 054
Read events
3 020
Write events
21
Delete events
13
Modification events
| (PID) Process: | (6628) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6628) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6628) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6628) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\NOTIFICACIÓN ELECTRÓNICA CENDO RAMA JUDICIAL DEL PODER PÚBLICO ESM CONFIRMAR RECIBIDO.rar | |||
| (PID) Process: | (6628) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6628) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6628) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6628) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6628) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (6628) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
Executable files
3
Suspicious files
6
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5404 | cmd.exe | C:\Users\admin\AppData\Local\Temp\gicakwobrptob | — | |
MD5:— | SHA256:— | |||
| 6628 | WinRAR.exe | C:\Users\admin\Desktop\ptvt | binary | |
MD5:51B6BC457D591A9B73608BE306B05A43 | SHA256:D901710C189D6D486BBE6ECF9EF0C3B1C16B675A2A7C279F7E858585E9B397FE | |||
| 6628 | WinRAR.exe | C:\Users\admin\Desktop\00030 NotificacionElectronica.exe | executable | |
MD5:D9530ECEE42ACCCFD3871672A511BC9E | SHA256:81E04F9A131534ACC0E9DE08718C062D3D74C80C7F168EC7E699CD4B2BD0F280 | |||
| 6628 | WinRAR.exe | C:\Users\admin\Desktop\d3dx9_43.dll | executable | |
MD5:D87DE826CA653D3BFE426337EADC0EE3 | SHA256:6F0B9E1F52998E21DB8B5A07305D93E699E9E766C0D04403F436E2551946701E | |||
| 6628 | WinRAR.exe | C:\Users\admin\Desktop\wdkpd | binary | |
MD5:7082BA2B15A6F4DDC06A8E0C54C5CC81 | SHA256:358301CE5A8C665C353460DDE15B7FDA2F979BD9AB5D49C0CC9F2F495828A362 | |||
| 3552 | 00030 NotificacionElectronica.exe | C:\Users\admin\AppData\Roaming\ClientWizard\d3dx9_43.dll | executable | |
MD5:D87DE826CA653D3BFE426337EADC0EE3 | SHA256:6F0B9E1F52998E21DB8B5A07305D93E699E9E766C0D04403F436E2551946701E | |||
| 3552 | 00030 NotificacionElectronica.exe | C:\Users\admin\AppData\Roaming\ClientWizard\wdkpd | binary | |
MD5:7082BA2B15A6F4DDC06A8E0C54C5CC81 | SHA256:358301CE5A8C665C353460DDE15B7FDA2F979BD9AB5D49C0CC9F2F495828A362 | |||
| 3552 | 00030 NotificacionElectronica.exe | C:\Users\admin\AppData\Local\Temp\14049e25 | binary | |
MD5:99BF764F539749D03DC56DA294E97CD5 | SHA256:26D2D742CD5732E1C41A6566F69C984612F9E8BBD13E024765DF27100BCCB598 | |||
| 3552 | 00030 NotificacionElectronica.exe | C:\Users\admin\AppData\Roaming\ClientWizard\ptvt | binary | |
MD5:51B6BC457D591A9B73608BE306B05A43 | SHA256:D901710C189D6D486BBE6ECF9EF0C3B1C16B675A2A7C279F7E858585E9B397FE | |||
| 5404 | cmd.exe | C:\Users\admin\AppData\Local\Temp\sihdnv | binary | |
MD5:911370296A1147D7A64AC90514B0D7A5 | SHA256:B29F1DE1B73EF6DE7F43035D8BEA49431666A6991F0606BD41184AF21E0DB5A3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
80
DNS requests
23
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.35:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.230.103:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.230.103:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5992 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5992 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6380 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
640 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.164.35:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 184.30.230.103:80 | www.microsoft.com | AKAMAI-AS | US | unknown |
4712 | MoUsoCoreWorker.exe | 184.30.230.103:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
5064 | SearchApp.exe | 2.23.227.221:443 | www.bing.com | Ooredoo Q.S.C. | QA | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1176 | svchost.exe | 40.126.31.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
2192 | svchost.exe | Potentially Bad Traffic | ET INFO DYNAMIC_DNS Query to a *.duckdns .org Domain |
2192 | svchost.exe | Potentially Bad Traffic | ET INFO DYNAMIC_DNS Query to a *.duckdns .org Domain |
2192 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
2192 | svchost.exe | Potentially Bad Traffic | ET INFO DYNAMIC_DNS Query to a *.duckdns .org Domain |
2192 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
2192 | svchost.exe | Potentially Bad Traffic | ET INFO DYNAMIC_DNS Query to a *.duckdns .org Domain |
2192 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
2192 | svchost.exe | Potentially Bad Traffic | ET INFO DYNAMIC_DNS Query to a *.duckdns .org Domain |
2192 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |