| File name: | 1.exe |
| Full analysis: | https://app.any.run/tasks/90d95551-04be-4d60-86ed-071b9243ffe7 |
| Verdict: | Malicious activity |
| Threats: | Phorpiex is a malicious software that has been a significant threat in the cybersecurity landscape since 2016. It is a modular malware known for its ability to maintain an extensive botnet. Unlike other botnets, Phorpiex does not concentrate on DDoS attacks. Instead, it has been involved in numerous large-scale spam email campaigns and the distribution of other malicious payloads, such as LockBit. |
| Analysis date: | August 13, 2019, 23:16:21 |
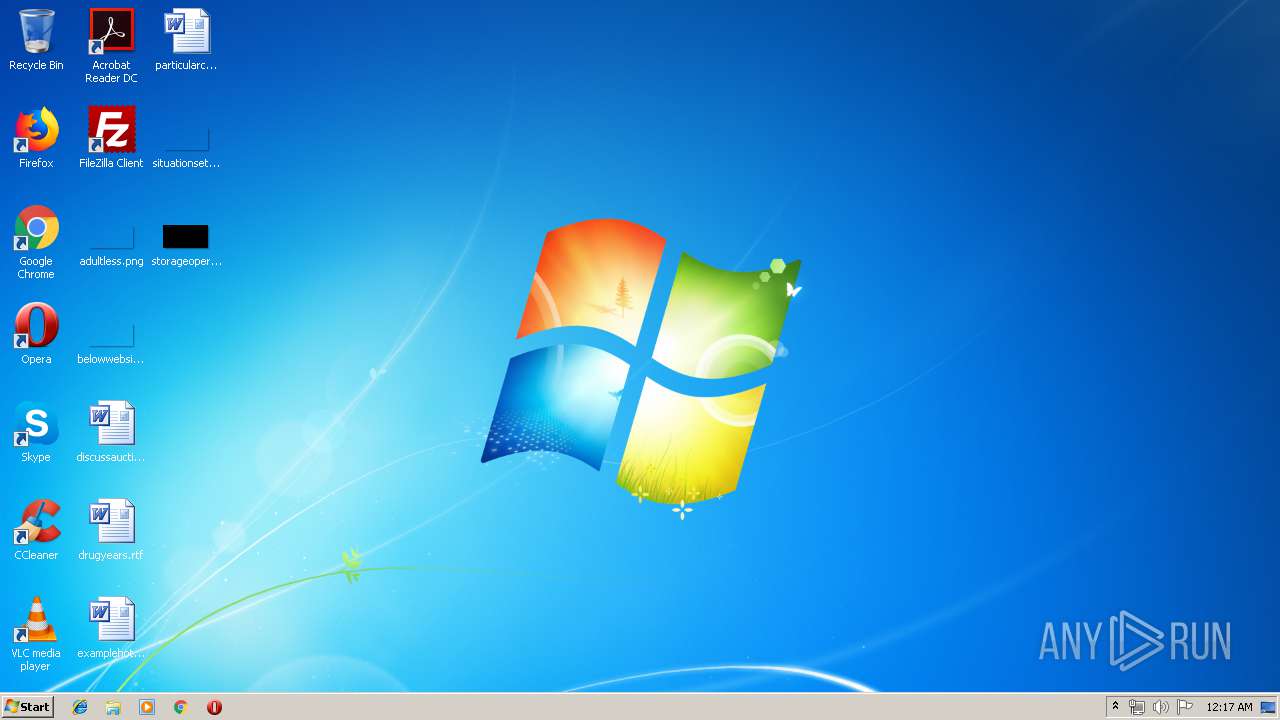
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | F8DCF54AA841455DB600FD9DD5243727 |
| SHA1: | CC8EE6BD6E7001852CEAE25A515FDCB91023A4E5 |
| SHA256: | FA2993F2455971244350178008CC671FB739B53D79B594C80E69047421CE1666 |
| SSDEEP: | 6144:BMlvS0cEcZcfiInOJA8YHmlGwdHHQbLRpprgzPd7zqxUcr:BMZHcESFInAAvGlGAApuzwxt |
MALICIOUS
Changes the autorun value in the registry
- 1.exe (PID: 2956)
- 38720.exe (PID: 2468)
Disables Windows Defender
- sysmudt.exe (PID: 2584)
- sysrtvo.exe (PID: 3260)
Changes Security Center notification settings
- sysmudt.exe (PID: 2584)
- sysrtvo.exe (PID: 3260)
Disables Windows System Restore
- sysmudt.exe (PID: 2584)
- sysrtvo.exe (PID: 3260)
PHORPIEX was detected
- sysmudt.exe (PID: 2584)
- sysrtvo.exe (PID: 3260)
Application was dropped or rewritten from another process
- 38720.exe (PID: 2468)
- sysrtvo.exe (PID: 3260)
- 39495.exe (PID: 3320)
- 29433.exe (PID: 724)
- 10506.exe (PID: 2148)
Connects to CnC server
- sysmudt.exe (PID: 2584)
SUSPICIOUS
Starts itself from another location
- 1.exe (PID: 2956)
- 38720.exe (PID: 2468)
- sysrtvo.exe (PID: 3260)
Creates files in the user directory
- sysmudt.exe (PID: 2584)
- 29433.exe (PID: 724)
Executable content was dropped or overwritten
- sysmudt.exe (PID: 2584)
- 1.exe (PID: 2956)
- 38720.exe (PID: 2468)
- sysrtvo.exe (PID: 3260)
- 29433.exe (PID: 724)
Connects to SMTP port
- 10506.exe (PID: 2148)
Creates files in the program directory
- 29433.exe (PID: 724)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:06:29 16:48:37+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 159744 |
| InitializedDataSize: | 143360 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa3e9 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.9.9.2 |
| ProductVersionNumber: | 4.9.9.2 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Bloodshed Software |
| FileDescription: | Dev-C++ IDE |
| FileVersion: | 4.9.9.2 |
| InternalName: | devcpp.exe |
| LegalCopyright: | Copyright Bloodshed Software |
| LegalTrademarks: | - |
| OriginalFileName: | devcpp.exe |
| ProductName: | Dev-C++ |
| ProductVersion: | 5 |
| Comments: | Under the GNU General Public License |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 29-Jun-2016 14:48:37 |
| Detected languages: |
|
| CompanyName: | Bloodshed Software |
| FileDescription: | Dev-C++ IDE |
| FileVersion: | 4.9.9.2 |
| InternalName: | devcpp.exe |
| LegalCopyright: | Copyright Bloodshed Software |
| LegalTrademarks: | - |
| OriginalFilename: | devcpp.exe |
| ProductName: | Dev-C++ |
| ProductVersion: | 5 |
| Comments: | Under the GNU General Public License |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 29-Jun-2016 14:48:37 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000260BF | 0x00027000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.48674 |
.rdata | 0x00028000 | 0x0000A4AA | 0x0000B000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.48539 |
.data | 0x00033000 | 0x0000CD1C | 0x0000A000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.23584 |
.rsrc | 0x00040000 | 0x00004C56 | 0x00005000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.5061 |
.reloc | 0x00045000 | 0x0001D7BE | 0x0001E000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 4.646 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.4167 | 852 | UNKNOWN | English - United States | RT_VERSION |
7 | 2.7403 | 202 | UNKNOWN | UNKNOWN | RT_STRING |
9 | 1.7593 | 62 | UNKNOWN | UNKNOWN | RT_STRING |
31 | 3.02695 | 308 | UNKNOWN | Hebrew - Israel | RT_CURSOR |
32 | 2.74274 | 180 | UNKNOWN | Hebrew - Israel | RT_CURSOR |
34 | 6.96696 | 3240 | UNKNOWN | English - United States | RT_ICON |
100 | 3.23533 | 356 | UNKNOWN | UNKNOWN | RT_DIALOG |
128 | 2.86383 | 18 | UNKNOWN | UNKNOWN | UNKNOWN |
2049 | 2.4724 | 132 | UNKNOWN | UNKNOWN | RT_STRING |
3585 | 2.10121 | 72 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
OLEPRO32.DLL |
SHELL32.dll |
USER32.dll |
WINSPOOL.DRV |
comdlg32.dll |
Total processes
39
Monitored processes
7
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 724 | C:\Users\admin\AppData\Local\Temp\29433.exe | C:\Users\admin\AppData\Local\Temp\29433.exe | sysrtvo.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: MFC-Anwendung Elliptic Button Demo Exit code: 0 Version: 2, 0, 0, 0 Modules
| |||||||||||||||
| 2148 | C:\Users\admin\AppData\Local\Temp\10506.exe | C:\Users\admin\AppData\Local\Temp\10506.exe | sysrtvo.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: MFC-Anwendung Elliptic Button Demo Exit code: 0 Version: 2, 0, 0, 0 Modules
| |||||||||||||||
| 2468 | C:\Users\admin\AppData\Local\Temp\38720.exe | C:\Users\admin\AppData\Local\Temp\38720.exe | sysmudt.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: MFC-Anwendung Elliptic Button Demo Exit code: 0 Version: 2, 0, 0, 0 Modules
| |||||||||||||||
| 2584 | C:\Users\admin\105827982\sysmudt.exe | C:\Users\admin\105827982\sysmudt.exe | 1.exe | ||||||||||||
User: admin Company: Bloodshed Software Integrity Level: MEDIUM Description: Dev-C++ IDE Exit code: 0 Version: 4.9.9.2 Modules
| |||||||||||||||
| 2956 | "C:\Users\admin\AppData\Local\Temp\1.exe" | C:\Users\admin\AppData\Local\Temp\1.exe | explorer.exe | ||||||||||||
User: admin Company: Bloodshed Software Integrity Level: MEDIUM Description: Dev-C++ IDE Exit code: 0 Version: 4.9.9.2 Modules
| |||||||||||||||
| 3260 | C:\Users\admin\1929216923\sysrtvo.exe | C:\Users\admin\1929216923\sysrtvo.exe | 38720.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: MFC-Anwendung Elliptic Button Demo Exit code: 0 Version: 2, 0, 0, 0 Modules
| |||||||||||||||
| 3320 | C:\Users\admin\AppData\Local\Temp\39495.exe | C:\Users\admin\AppData\Local\Temp\39495.exe | — | sysrtvo.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: MFC-Anwendung Elliptic Button Demo Exit code: 0 Version: 2, 0, 0, 0 Modules
| |||||||||||||||
Total events
116
Read events
52
Write events
64
Delete events
0
Modification events
| (PID) Process: | (2956) 1.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Microsoft Windows Driver |
Value: C:\Users\admin\105827982\sysmudt.exe | |||
| (PID) Process: | (2956) 1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Microsoft Windows Driver |
Value: C:\Users\admin\105827982\sysmudt.exe | |||
| (PID) Process: | (2584) sysmudt.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender |
| Operation: | write | Name: | DisableAntiSpyware |
Value: 1 | |||
| (PID) Process: | (2584) sysmudt.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-time Protection |
| Operation: | write | Name: | DisableScanOnRealtimeEnable |
Value: 1 | |||
| (PID) Process: | (2584) sysmudt.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-time Protection |
| Operation: | write | Name: | DisableOnAccessProtection |
Value: 1 | |||
| (PID) Process: | (2584) sysmudt.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-time Protection |
| Operation: | write | Name: | DisableBehaviorMonitoring |
Value: 1 | |||
| (PID) Process: | (2584) sysmudt.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center |
| Operation: | write | Name: | AntiVirusOverride |
Value: 1 | |||
| (PID) Process: | (2584) sysmudt.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center |
| Operation: | write | Name: | UpdatesOverride |
Value: 1 | |||
| (PID) Process: | (2584) sysmudt.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center |
| Operation: | write | Name: | FirewallOverride |
Value: 1 | |||
| (PID) Process: | (2584) sysmudt.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center |
| Operation: | write | Name: | AntiVirusDisableNotify |
Value: 1 | |||
Executable files
11
Suspicious files
10
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2584 | sysmudt.exe | C:\Users\admin\AppData\Local\Temp\38720.exe | binary | |
MD5:— | SHA256:— | |||
| 2584 | sysmudt.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\1[1] | binary | |
MD5:— | SHA256:— | |||
| 3260 | sysrtvo.exe | C:\Users\admin\AppData\Local\Temp\39495.exe | binary | |
MD5:— | SHA256:— | |||
| 3260 | sysrtvo.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\2[1] | binary | |
MD5:— | SHA256:— | |||
| 3260 | sysrtvo.exe | C:\Users\admin\AppData\Local\Temp\15962.exe | binary | |
MD5:— | SHA256:— | |||
| 2468 | 38720.exe | C:\Users\admin\1929216923\sysrtvo.exe | executable | |
MD5:— | SHA256:— | |||
| 3260 | sysrtvo.exe | C:\Users\admin\AppData\Local\Temp\29433.exe | binary | |
MD5:— | SHA256:— | |||
| 2956 | 1.exe | C:\Users\admin\105827982\sysmudt.exe | executable | |
MD5:— | SHA256:— | |||
| 3260 | sysrtvo.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\3[1] | binary | |
MD5:— | SHA256:— | |||
| 3260 | sysrtvo.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\5[1] | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
12
DNS requests
84
Threats
52
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2584 | sysmudt.exe | GET | 200 | 185.176.27.132:80 | http://185.176.27.132/t.php?new=1 | GB | — | — | malicious |
2584 | sysmudt.exe | GET | 200 | 193.32.161.73:80 | http://193.32.161.73/t.php?new=1 | unknown | — | — | malicious |
2584 | sysmudt.exe | GET | — | 185.176.27.132:80 | http://185.176.27.132/1 | GB | — | — | malicious |
3260 | sysrtvo.exe | GET | 304 | 185.176.27.132:80 | http://185.176.27.132/1 | GB | — | — | malicious |
3260 | sysrtvo.exe | GET | — | 185.176.27.132:80 | http://185.176.27.132/3 | GB | — | — | malicious |
3260 | sysrtvo.exe | GET | — | 185.176.27.132:80 | http://185.176.27.132/2 | GB | — | — | malicious |
3260 | sysrtvo.exe | GET | — | 185.176.27.132:80 | http://185.176.27.132/5 | GB | — | — | malicious |
2584 | sysmudt.exe | GET | 200 | 185.176.27.132:80 | http://185.176.27.132/1 | GB | binary | 424 Kb | malicious |
3260 | sysrtvo.exe | GET | 200 | 185.176.27.132:80 | http://185.176.27.132/2 | GB | binary | 1.85 Mb | malicious |
3260 | sysrtvo.exe | GET | 200 | 185.176.27.132:80 | http://185.176.27.132/3 | GB | binary | 364 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2584 | sysmudt.exe | 208.100.26.251:80 | urusurofhsorhfuuhl.cc | Steadfast | US | suspicious |
2584 | sysmudt.exe | 185.176.27.132:80 | — | — | GB | malicious |
2584 | sysmudt.exe | 35.225.160.245:80 | aeifaeifhutuhuhusl.cc | — | US | malicious |
2584 | sysmudt.exe | 193.32.161.73:80 | — | — | — | malicious |
3260 | sysrtvo.exe | 185.176.27.132:80 | — | — | GB | malicious |
3260 | sysrtvo.exe | 208.100.26.251:80 | urusurofhsorhfuuhl.cc | Steadfast | US | suspicious |
2148 | 10506.exe | 67.195.228.94:25 | mta7.am0.yahoodns.net | Yahoo | US | unknown |
3260 | sysrtvo.exe | 35.225.160.245:80 | aeifaeifhutuhuhusl.cc | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
urusurofhsorhfuuhk.su |
| malicious |
aeifaeifhutuhuhusk.su |
| unknown |
rzhsudhugugfugugsk.su |
| unknown |
bfagzzezgaegzgfaik.su |
| unknown |
eaeuafhuaegfugeudk.su |
| unknown |
aeufuaehfiuehfuhfk.su |
| malicious |
daedagheauehfuuhfk.su |
| unknown |
aeoughaoheguaoehdk.su |
| unknown |
eguaheoghouughahsk.su |
| unknown |
huaeokaefoaeguaehk.su |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1064 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
2584 | sysmudt.exe | Misc Attack | ET DROP Dshield Block Listed Source group 1 |
1064 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
1064 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
1064 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
1064 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
1064 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
1064 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
1064 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
1064 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
4 ETPRO signatures available at the full report