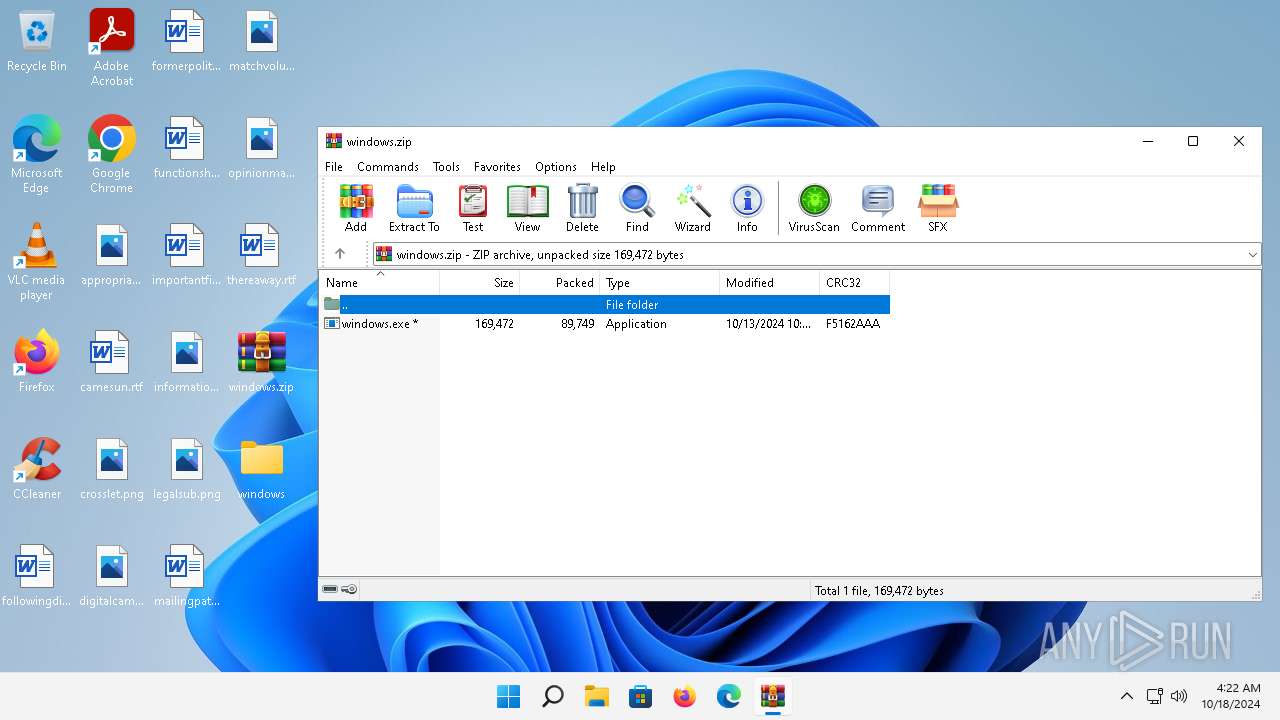
| File name: | windows.zip |
| Full analysis: | https://app.any.run/tasks/480976b7-568a-47e0-9e56-62d7bd8caf06 |
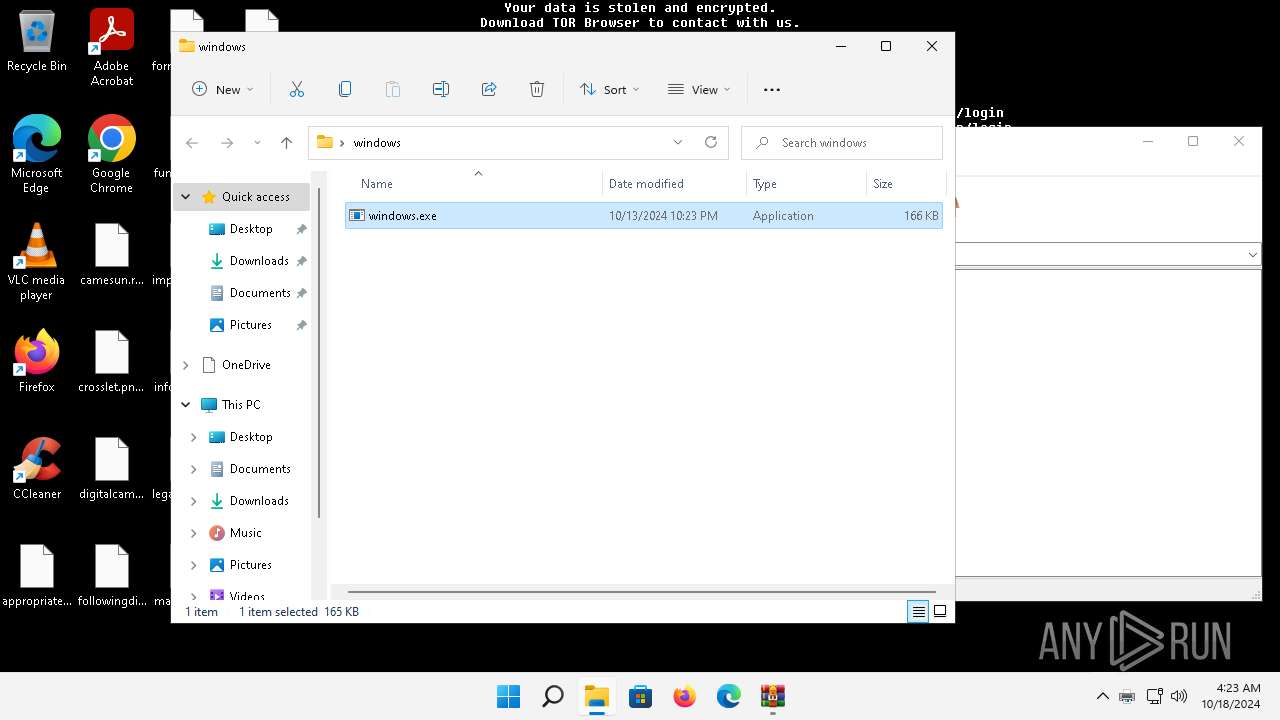
| Verdict: | Malicious activity |
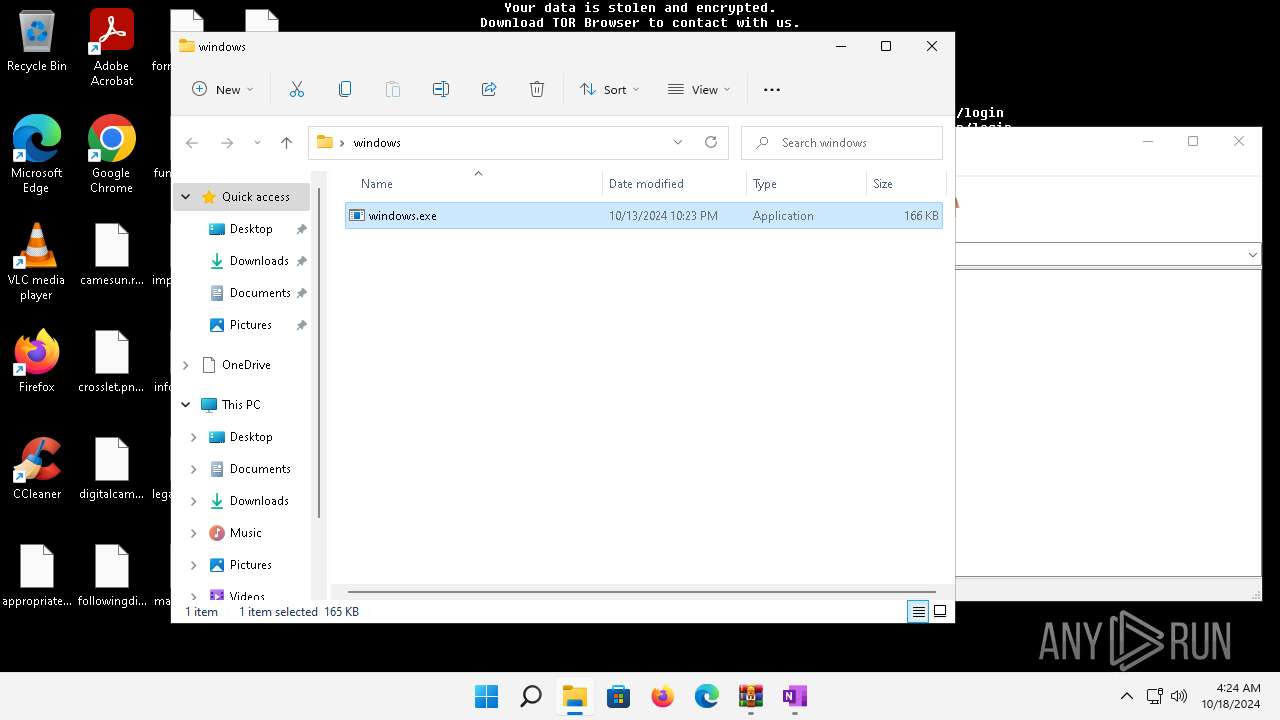
| Threats: | Lynx is a double extortion ransomware: attackers encrypt important and sensitive data and demand a ransom for decryption simultaneously threatening to publish or sell the data. Active since mid-2024. Among techniques are terminating processes and services, privilege escalation, deleting shadow copies. Distribution by phishing, malvertising, exploiting vulnerabilities. |
| Analysis date: | October 18, 2024, 04:22:20 |
| OS: | Windows 11 Professional (build: 22000, 64 bit) |
| Tags: | |
| Indicators: | |
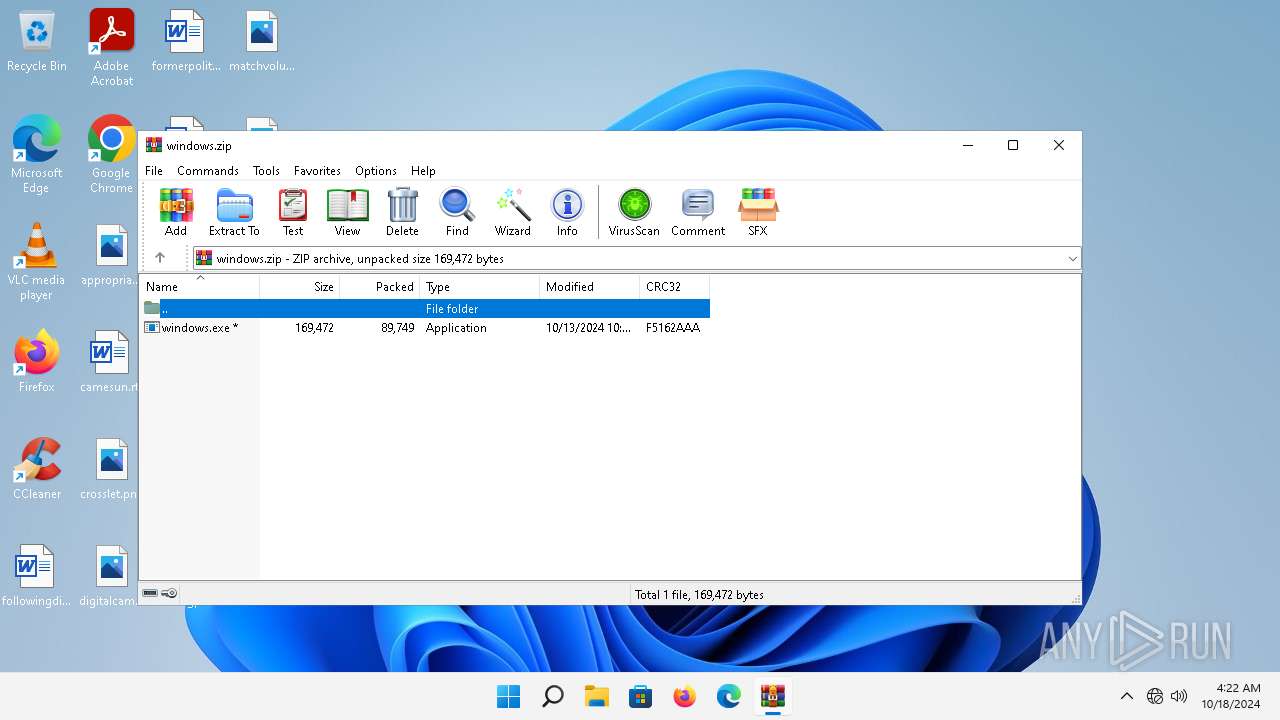
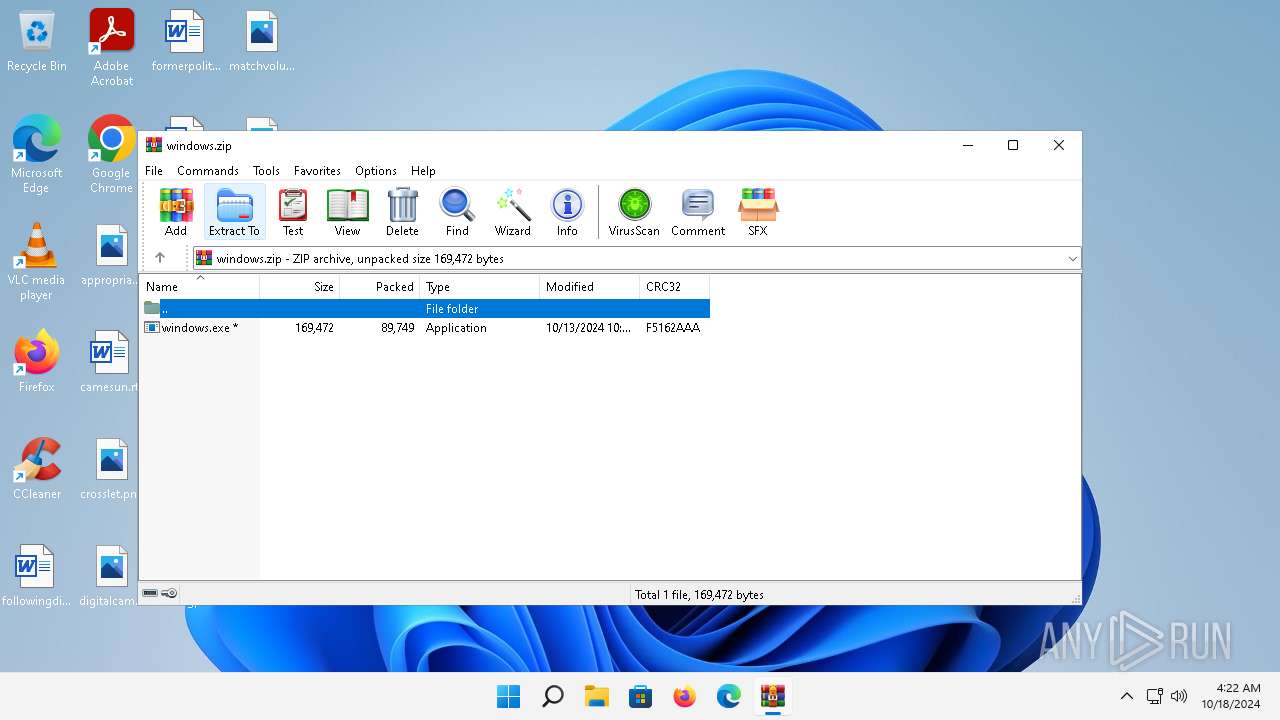
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 6CECEBC76EFD45FCFA7CFBEC5F383150 |
| SHA1: | AA6808022D241E61C0571B428763D5AD8CA81918 |
| SHA256: | F9BB467DDBC18ABA13667ABE99D2289D7C799C289AAE1158E8F7460531BD56B7 |
| SSDEEP: | 1536:cclte73+M7XLPAG1YDcsh7Knp+LTM+XIlE5dzWPxn6MPei9fAiE7RVjrU8odc:BlEDpb9YGALTtYlvxnMi4iAzjrFl |
MALICIOUS
LYNX has been detected
- windows.exe (PID: 4400)
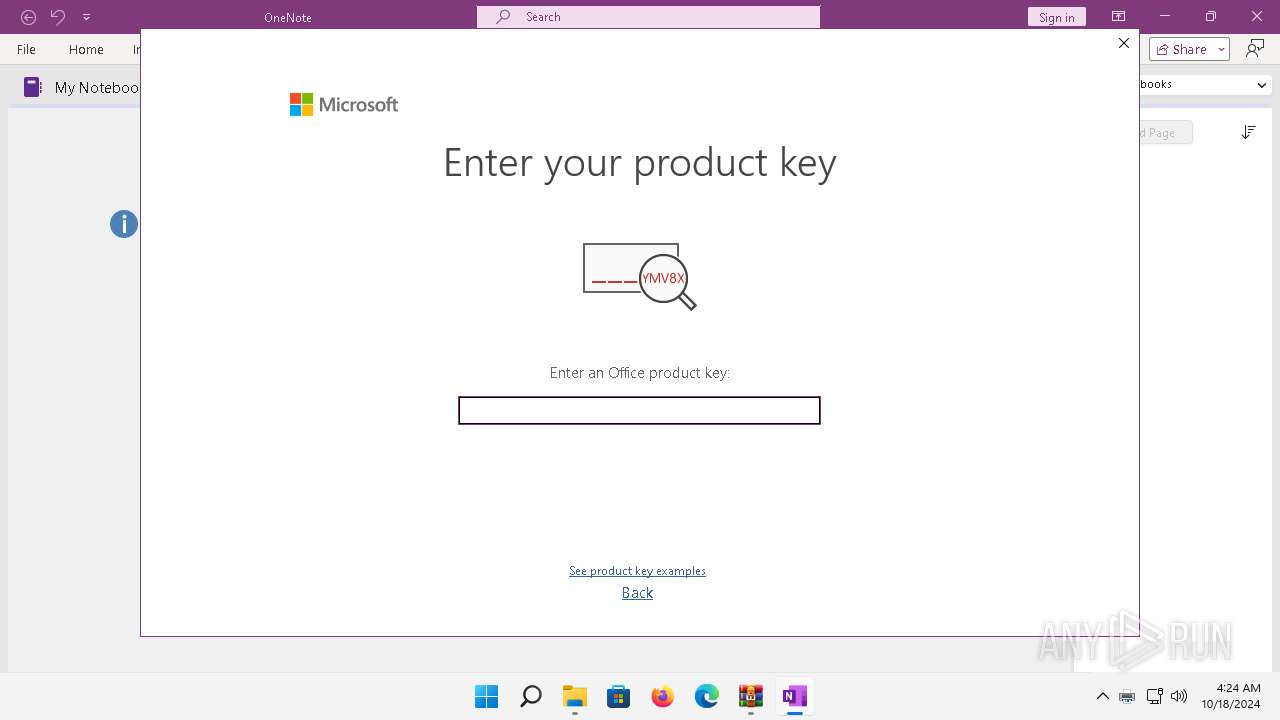
- ONENOTE.EXE (PID: 10708)
Renames files like ransomware
- windows.exe (PID: 4400)
Scans artifacts that could help determine the target
- ONENOTE.EXE (PID: 10708)
SUSPICIOUS
Creates file in the systems drive root
- windows.exe (PID: 4400)
Reads the Internet Settings
- printfilterpipelinesvc.exe (PID: 10512)
- ONENOTE.EXE (PID: 10708)
Changes the desktop background image
- windows.exe (PID: 4400)
Executes as Windows Service
- FXSSVC.exe (PID: 10632)
Reads security settings of Internet Explorer
- ONENOTE.EXE (PID: 10708)
Reads settings of System Certificates
- ONENOTE.EXE (PID: 10708)
Reads the date of Windows installation
- ONENOTE.EXE (PID: 10708)
Checks Windows Trust Settings
- ONENOTE.EXE (PID: 10708)
INFO
Reads the computer name
- windows.exe (PID: 4400)
- ONENOTE.EXE (PID: 10708)
Checks supported languages
- windows.exe (PID: 4400)
- ONENOTE.EXE (PID: 10708)
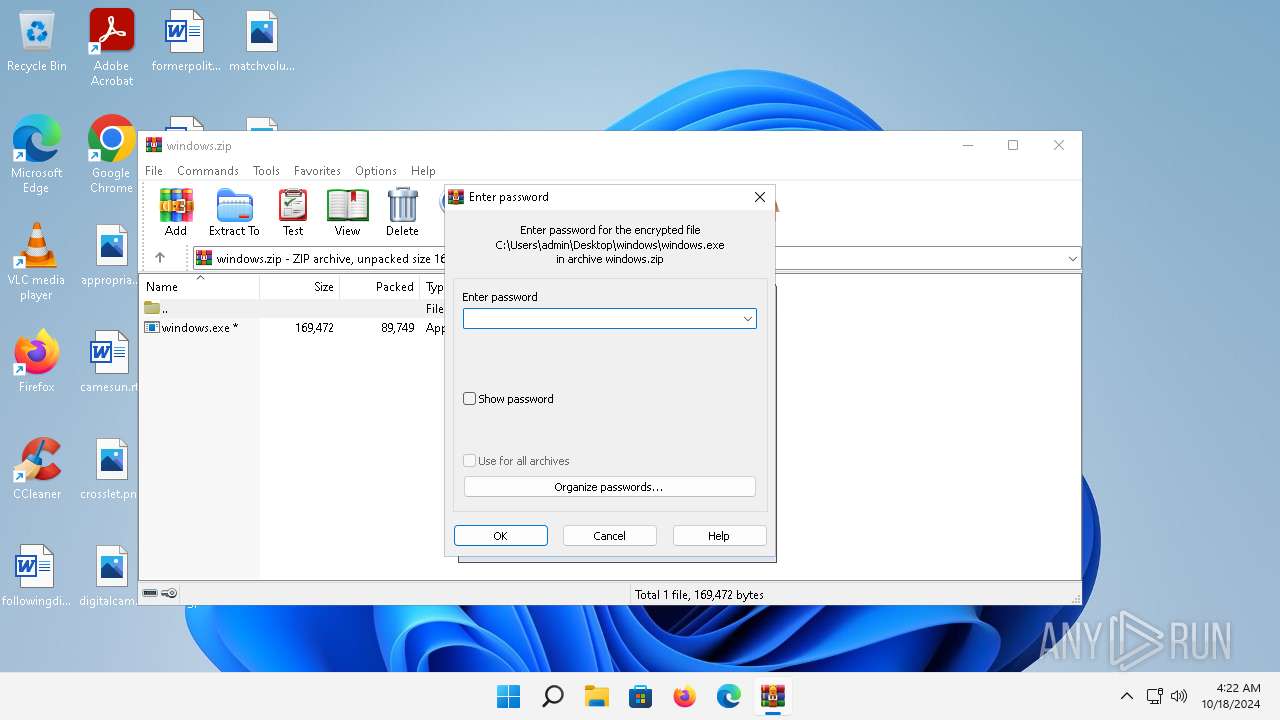
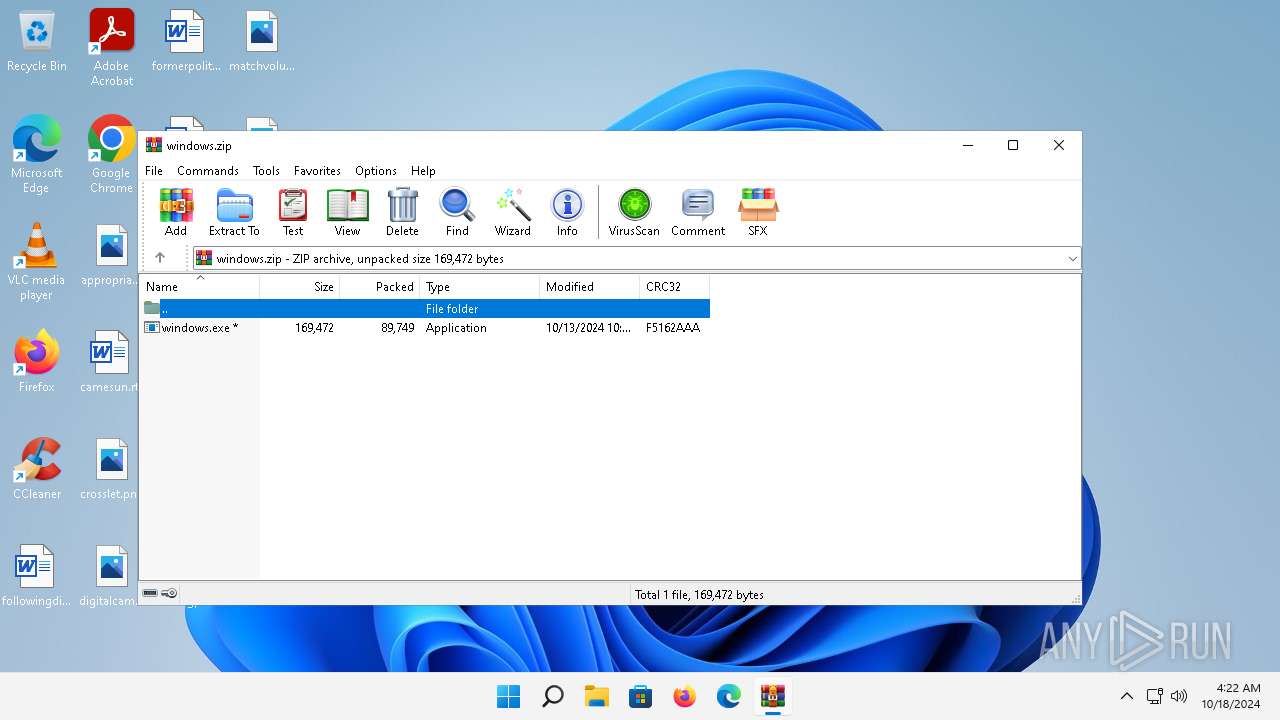
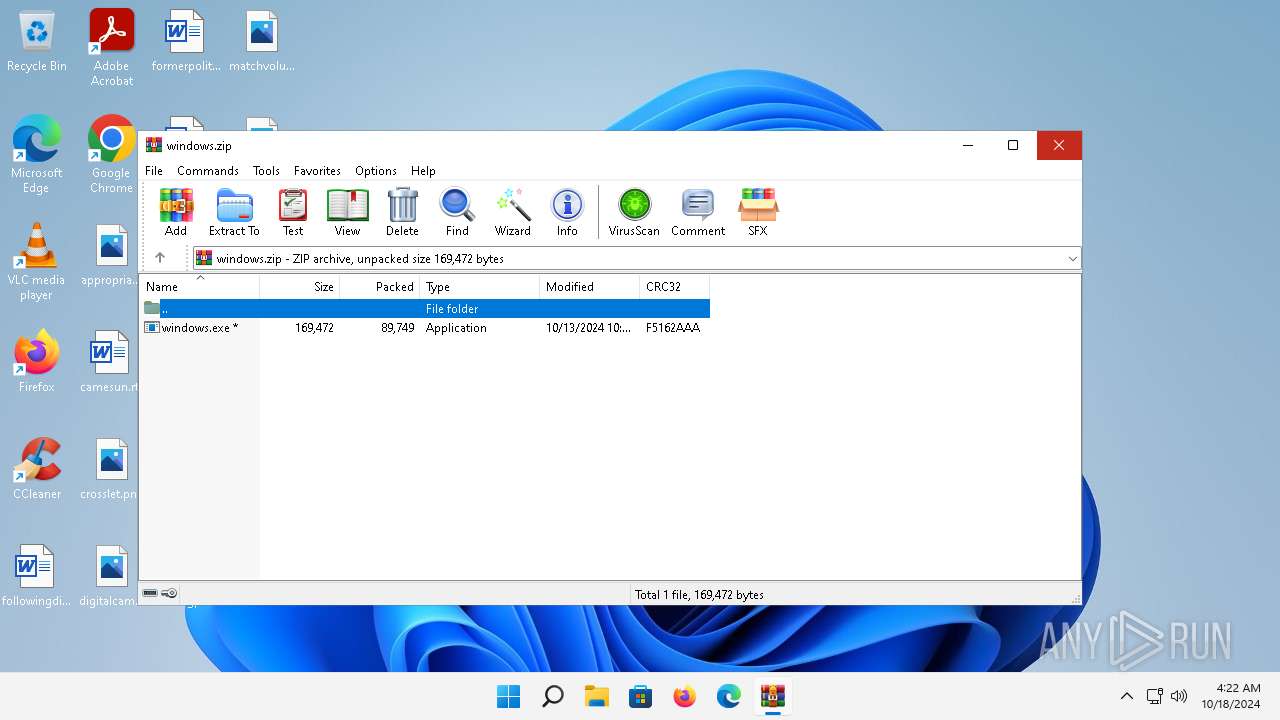
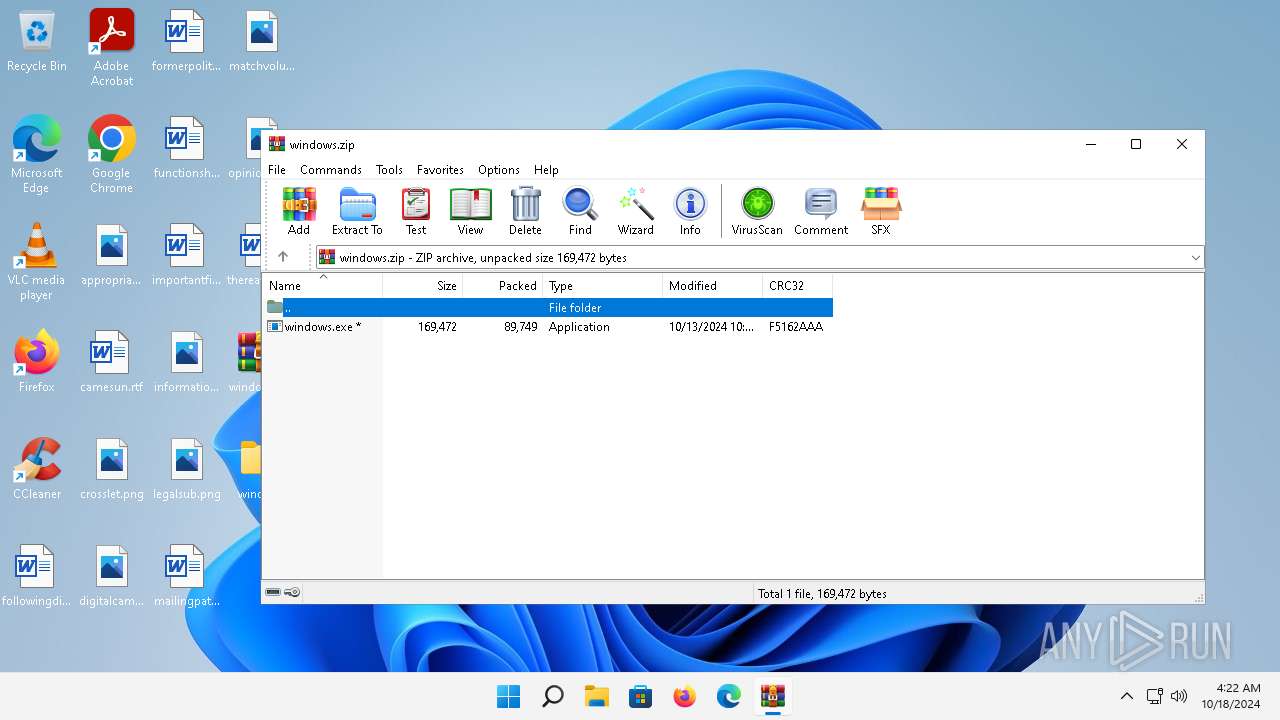
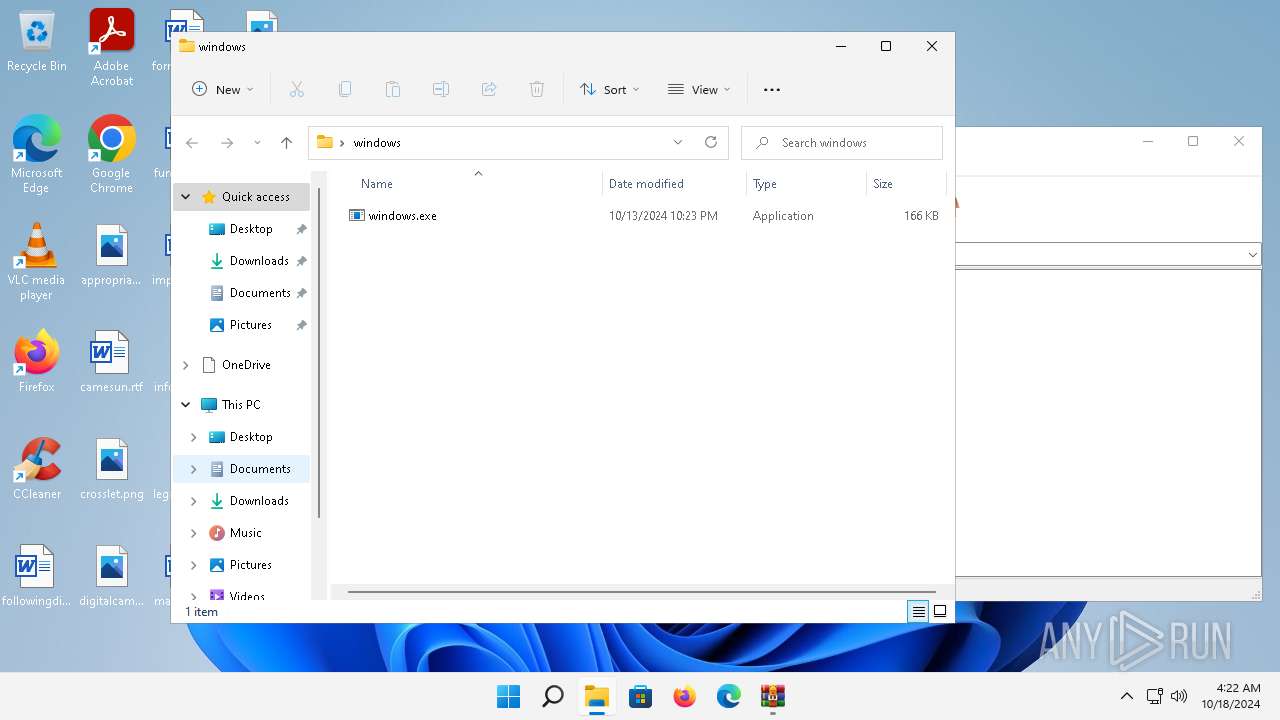
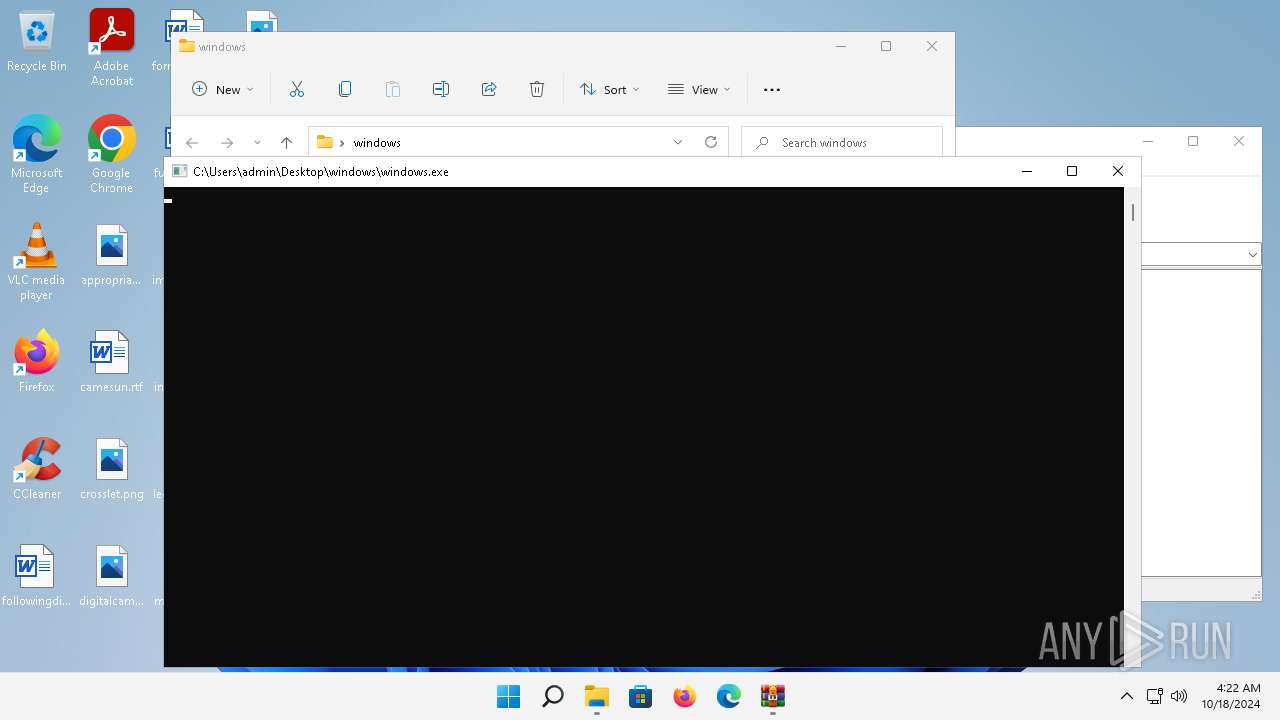
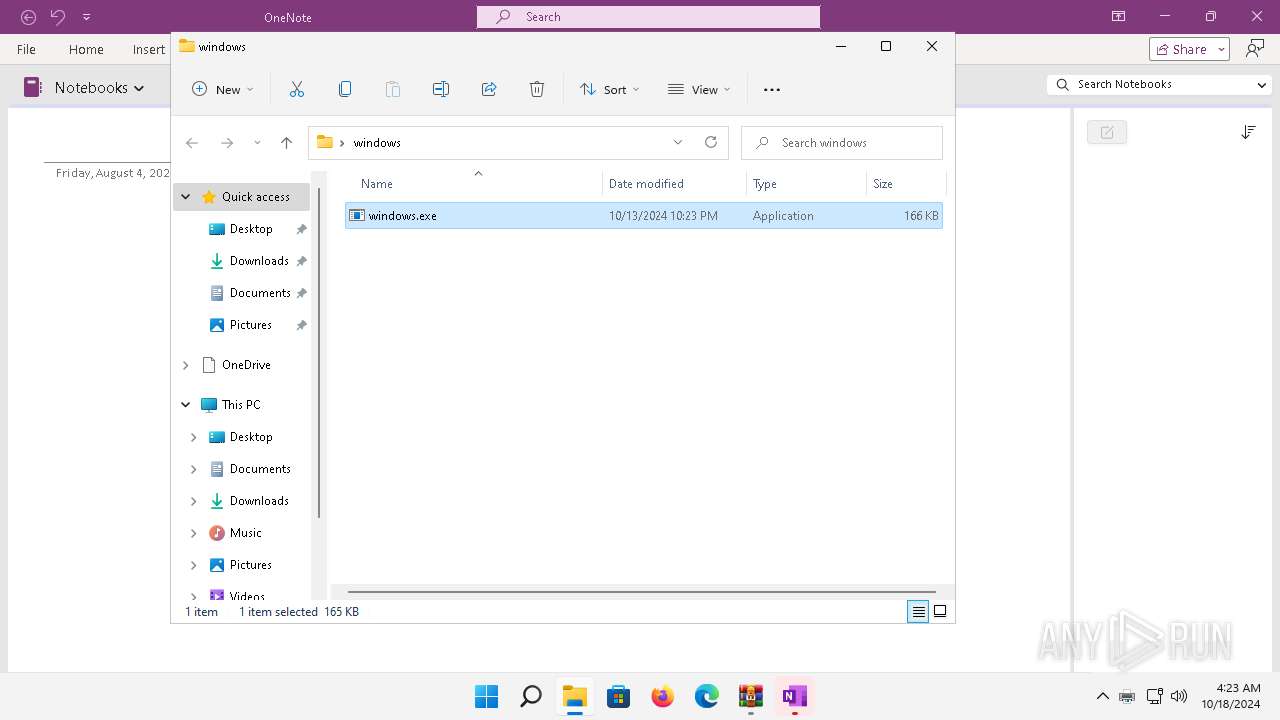
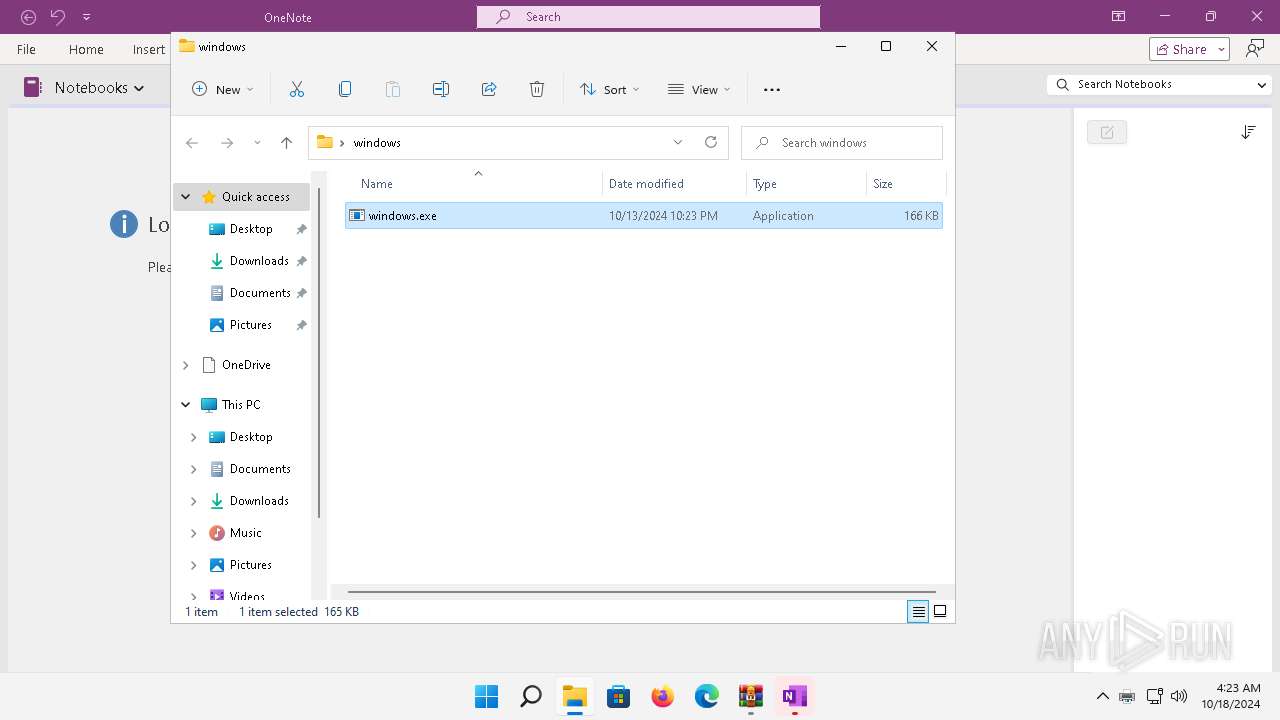
Manual execution by a user
- windows.exe (PID: 4400)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2364)
The process uses the downloaded file
- WinRAR.exe (PID: 2364)
Creates files in the program directory
- windows.exe (PID: 4400)
- FXSSVC.exe (PID: 10632)
Reads the machine GUID from the registry
- windows.exe (PID: 4400)
- ONENOTE.EXE (PID: 10708)
Create files in a temporary directory
- windows.exe (PID: 4400)
- ONENOTE.EXE (PID: 10708)
Creates files or folders in the user directory
- windows.exe (PID: 4400)
- printfilterpipelinesvc.exe (PID: 10512)
- ONENOTE.EXE (PID: 10708)
Reads security settings of Internet Explorer
- printfilterpipelinesvc.exe (PID: 10512)
Disables trace logs
- FXSSVC.exe (PID: 10632)
Reads Microsoft Office registry keys
- ONENOTE.EXE (PID: 10708)
Reads Environment values
- ONENOTE.EXE (PID: 10708)
Checks proxy server information
- ONENOTE.EXE (PID: 10708)
Reads the software policy settings
- ONENOTE.EXE (PID: 10708)
Reads CPU info
- ONENOTE.EXE (PID: 10708)
Reads product name
- ONENOTE.EXE (PID: 10708)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:10:13 15:23:30 |
| ZipCRC: | 0xf5162aaa |
| ZipCompressedSize: | 89749 |
| ZipUncompressedSize: | 169472 |
| ZipFileName: | windows.exe |
Total processes
123
Monitored processes
8
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
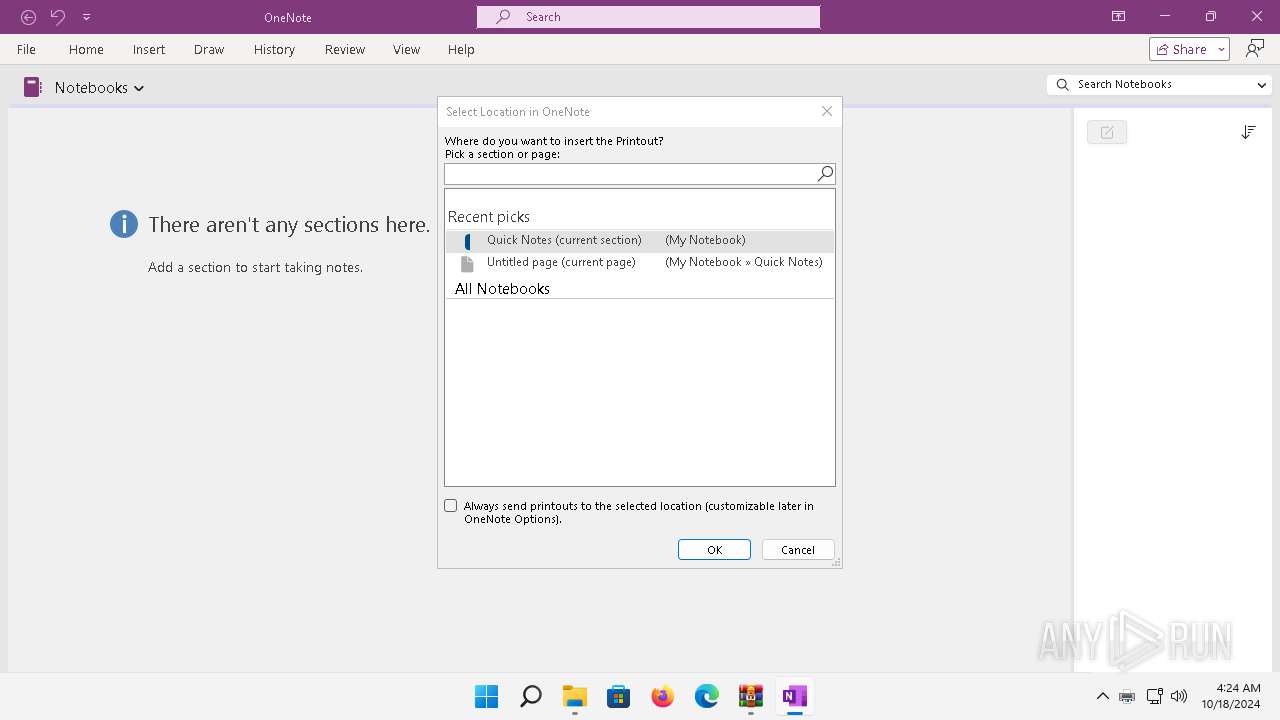
| 1588 | /tsr | C:\Program Files\Microsoft Office\root\Office16\ONENOTEM.EXE | — | ONENOTE.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Send to OneNote Tool Version: 16.0.16626.20134 Modules
| |||||||||||||||
| 1636 | \??\C:\Windows\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | windows.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
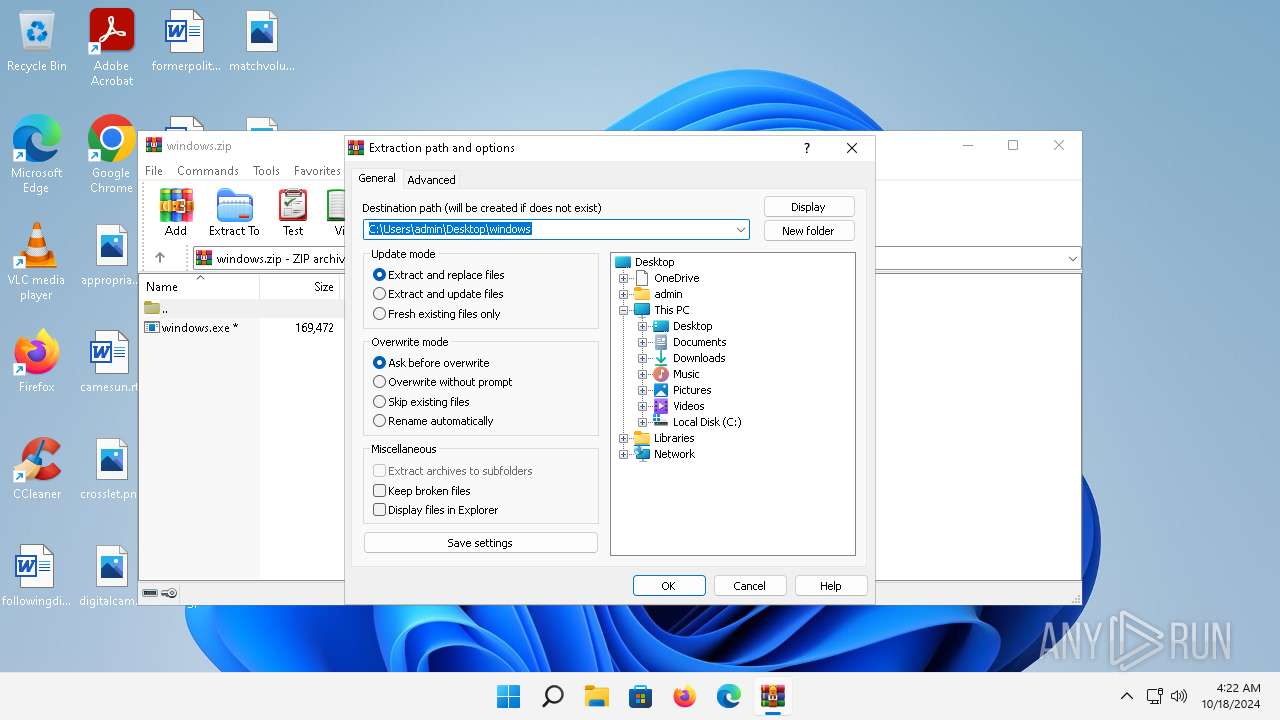
| 2364 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\windows.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 4400 | "C:\Users\admin\Desktop\windows\windows.exe" | C:\Users\admin\Desktop\windows\windows.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 5056 | C:\Windows\System32\rundll32.exe C:\Windows\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 10512 | C:\Windows\system32\printfilterpipelinesvc.exe -Embedding | C:\Windows\System32\printfilterpipelinesvc.exe | — | svchost.exe | |||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Print Filter Pipeline Host Exit code: 0 Version: 10.0.22000.653 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 10632 | C:\Windows\system32\fxssvc.exe | C:\Windows\System32\FXSSVC.exe | — | services.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Fax Service Version: 10.0.22000.795 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 10708 | /insertdoc "C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\{E5AAB9A9-B4D0-4721-AD51-DB1D713EE593}.xps" 133736990068350000 | C:\Program Files\Microsoft Office\root\Office16\ONENOTE.EXE | printfilterpipelinesvc.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft OneNote Version: 16.0.16626.20134 Modules
| |||||||||||||||
Total events
15 785
Read events
15 581
Write events
191
Delete events
13
Modification events
| (PID) Process: | (2364) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | VerInfo |
Value: 005B0500D962CB551521DB01 | |||
| (PID) Process: | (2364) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2364) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2364) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\windows.zip | |||
| (PID) Process: | (2364) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2364) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2364) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2364) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2364) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\windows | |||
| (PID) Process: | (2364) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
2
Suspicious files
1 007
Text files
506
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2364 | WinRAR.exe | C:\Users\admin\AppData\Roaming\WinRAR\version.dat | binary | |
MD5:51FB42B8184FFF99A1F7B5CE6711906B | SHA256:57905F52B585B9D883F358DB9763C541A1A5A05811E02945D3356838324C81E9 | |||
| 4400 | windows.exe | C:\ProgramData\Adobe\ARM\{291AA914-A987-4CE9-BD63-0C0A92D435E5}\README.txt | text | |
MD5:6B28FE0629ADBB6F11208259FAA88489 | SHA256:F3AD1045E0BE113922B41045C87003F864C0E79844B71CBB383ED4287C905FFB | |||
| 4400 | windows.exe | C:\ProgramData\Adobe\README.txt | text | |
MD5:6B28FE0629ADBB6F11208259FAA88489 | SHA256:F3AD1045E0BE113922B41045C87003F864C0E79844B71CBB383ED4287C905FFB | |||
| 4400 | windows.exe | C:\ProgramData\Adobe\ARM\Acrobat_22.003.20314\README.txt | text | |
MD5:6B28FE0629ADBB6F11208259FAA88489 | SHA256:F3AD1045E0BE113922B41045C87003F864C0E79844B71CBB383ED4287C905FFB | |||
| 4400 | windows.exe | C:\Users\admin\AppData\Local\VirtualStore\README.txt | text | |
MD5:6B28FE0629ADBB6F11208259FAA88489 | SHA256:F3AD1045E0BE113922B41045C87003F864C0E79844B71CBB383ED4287C905FFB | |||
| 4400 | windows.exe | C:\Users\admin\AppData\Local\VirtualStore\ProgramData\Microsoft\ClickToRun\MachineData\Catalog\Packages\{9AC08E99-230B-47E8-9721-4577B7F124EA}\{1A8308C7-90D1-4200-B16E-646F163A08E8}\Manifest.xml | — | |
MD5:— | SHA256:— | |||
| 4400 | windows.exe | C:\Users\admin\AppData\Local\VirtualStore\ProgramData\Microsoft\README.txt | text | |
MD5:6B28FE0629ADBB6F11208259FAA88489 | SHA256:F3AD1045E0BE113922B41045C87003F864C0E79844B71CBB383ED4287C905FFB | |||
| 4400 | windows.exe | C:\ProgramData\Adobe\Temp\README.txt | text | |
MD5:6B28FE0629ADBB6F11208259FAA88489 | SHA256:F3AD1045E0BE113922B41045C87003F864C0E79844B71CBB383ED4287C905FFB | |||
| 4400 | windows.exe | C:\Users\admin\AppData\Local\VirtualStore\ProgramData\Microsoft\AppV\Setup\README.txt | text | |
MD5:6B28FE0629ADBB6F11208259FAA88489 | SHA256:F3AD1045E0BE113922B41045C87003F864C0E79844B71CBB383ED4287C905FFB | |||
| 4400 | windows.exe | C:\ProgramData\README.txt | text | |
MD5:6B28FE0629ADBB6F11208259FAA88489 | SHA256:F3AD1045E0BE113922B41045C87003F864C0E79844B71CBB383ED4287C905FFB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
50
DNS requests
39
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5060 | smartscreen.exe | GET | 304 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?d10e63853eea6c1a | unknown | — | — | whitelisted |
5060 | smartscreen.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5060 | smartscreen.exe | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBTkdQGdwyPiJnQdbEA5B5X5BZZGLgQUO3DRU%2Bl2JZ1gqMpmD8abrm9UFmoCEzMAgi58WZZ1Doub1SAAAACCLnw%3D | unknown | — | — | whitelisted |
6208 | firefox.exe | POST | 200 | 2.16.202.121:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
6208 | firefox.exe | POST | 200 | 2.16.202.121:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
6208 | firefox.exe | POST | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/ | unknown | — | — | whitelisted |
1140 | svchost.exe | GET | 304 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?6d709d11b7687aa8 | unknown | — | — | whitelisted |
1088 | svchost.exe | POST | 403 | 184.28.89.167:80 | http://go.microsoft.com/fwlink/?LinkID=252669&clcid=0x409 | unknown | — | — | whitelisted |
1088 | svchost.exe | POST | 403 | 184.28.89.167:80 | http://go.microsoft.com/fwlink/?LinkID=252669&clcid=0x409 | unknown | — | — | whitelisted |
1140 | svchost.exe | GET | 304 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?2e9603725ad2c005 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 52.109.32.97:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5552 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1296 | svchost.exe | 2.16.164.35:80 | — | Akamai International B.V. | NL | unknown |
5060 | smartscreen.exe | 48.209.180.244:443 | checkappexec.microsoft.com | — | US | whitelisted |
5060 | smartscreen.exe | 199.232.214.172:80 | ctldl.windowsupdate.com | FASTLY | US | whitelisted |
5060 | smartscreen.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
5060 | smartscreen.exe | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 34.149.100.209:443 | firefox.settings.services.mozilla.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
officeclient.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
checkappexec.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
firefox.settings.services.mozilla.com |
| whitelisted |
incoming.telemetry.mozilla.org |
| whitelisted |
telemetry-incoming.r53-2.services.mozilla.com |
| whitelisted |
prod.remote-settings.prod.webservices.mozgcp.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1296 | svchost.exe | Misc activity | ET INFO Microsoft Connection Test |