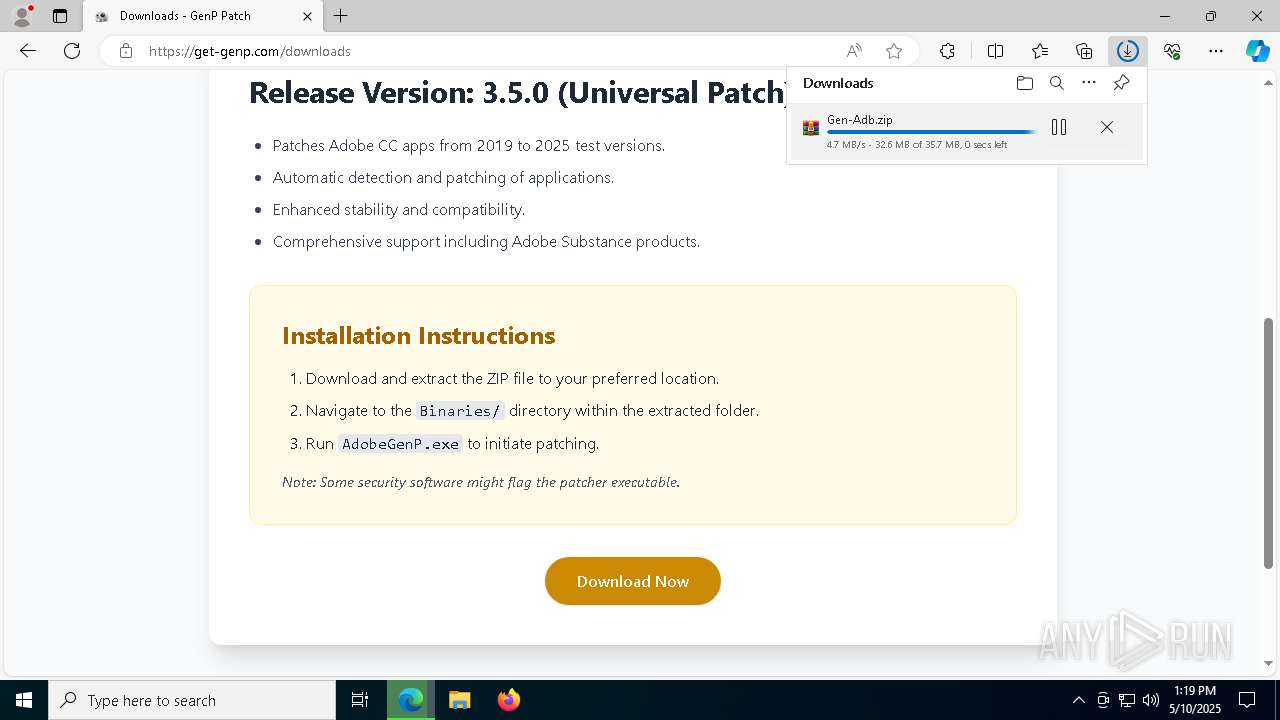
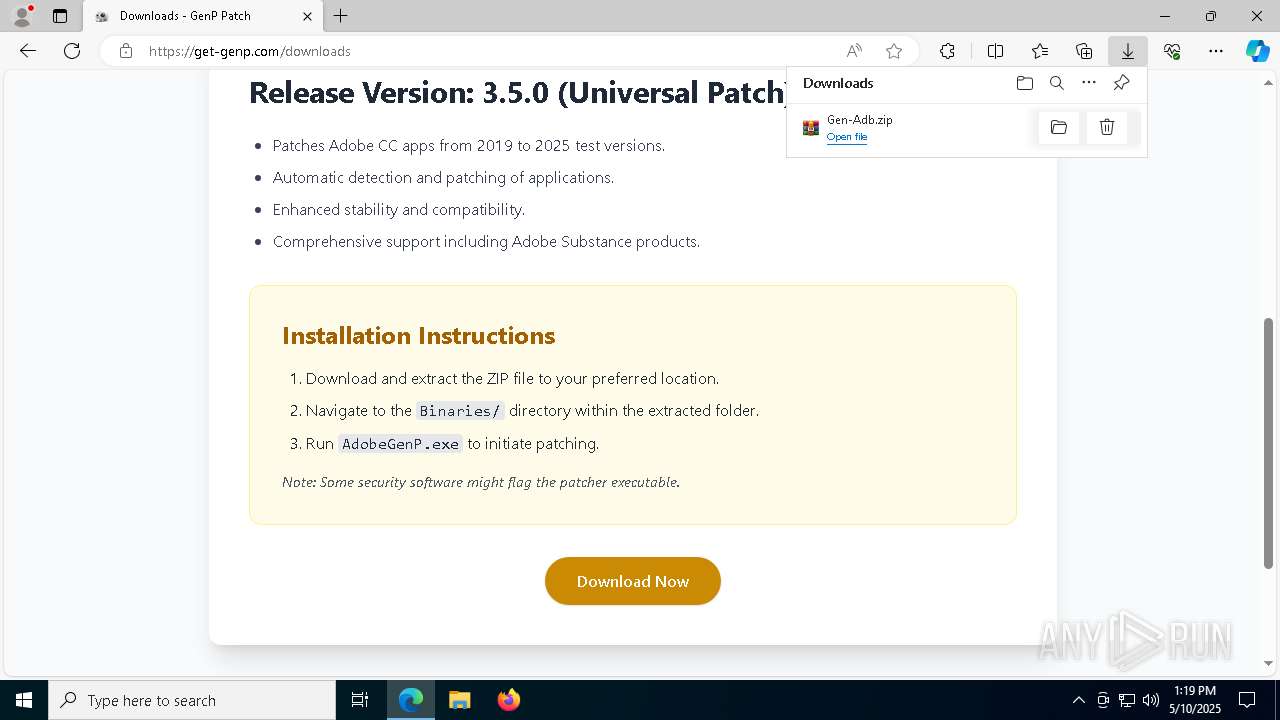
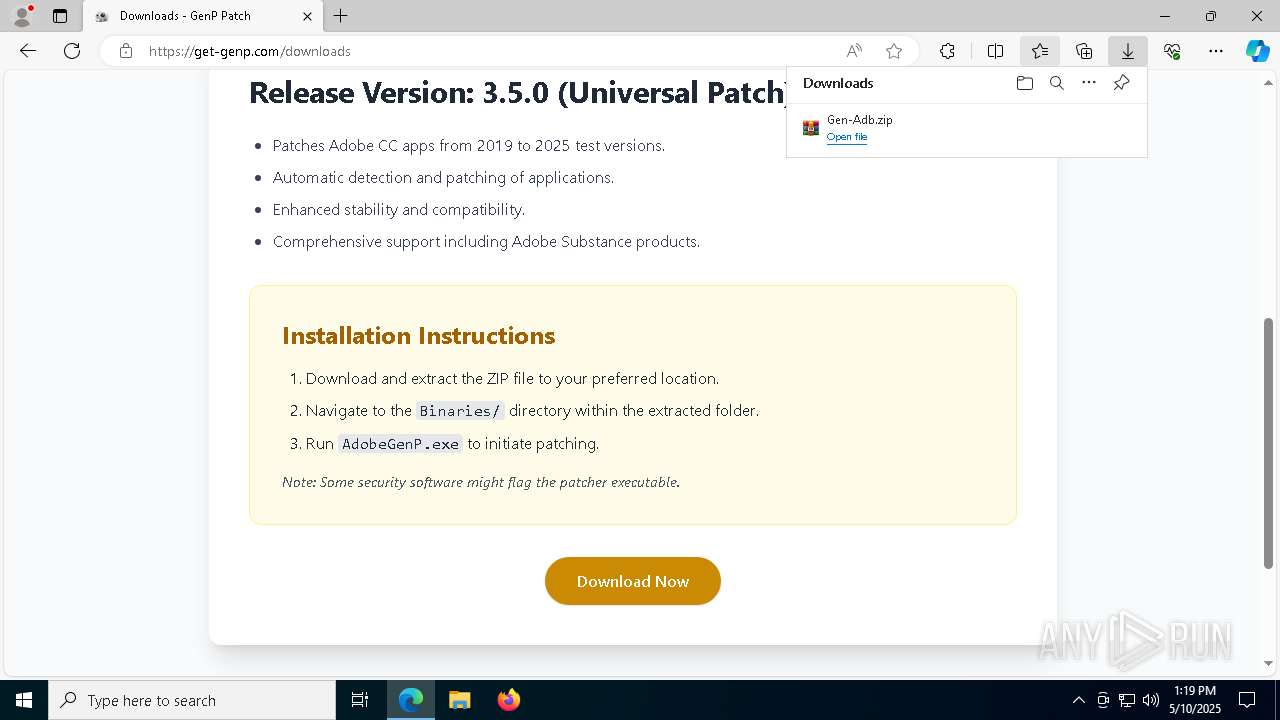
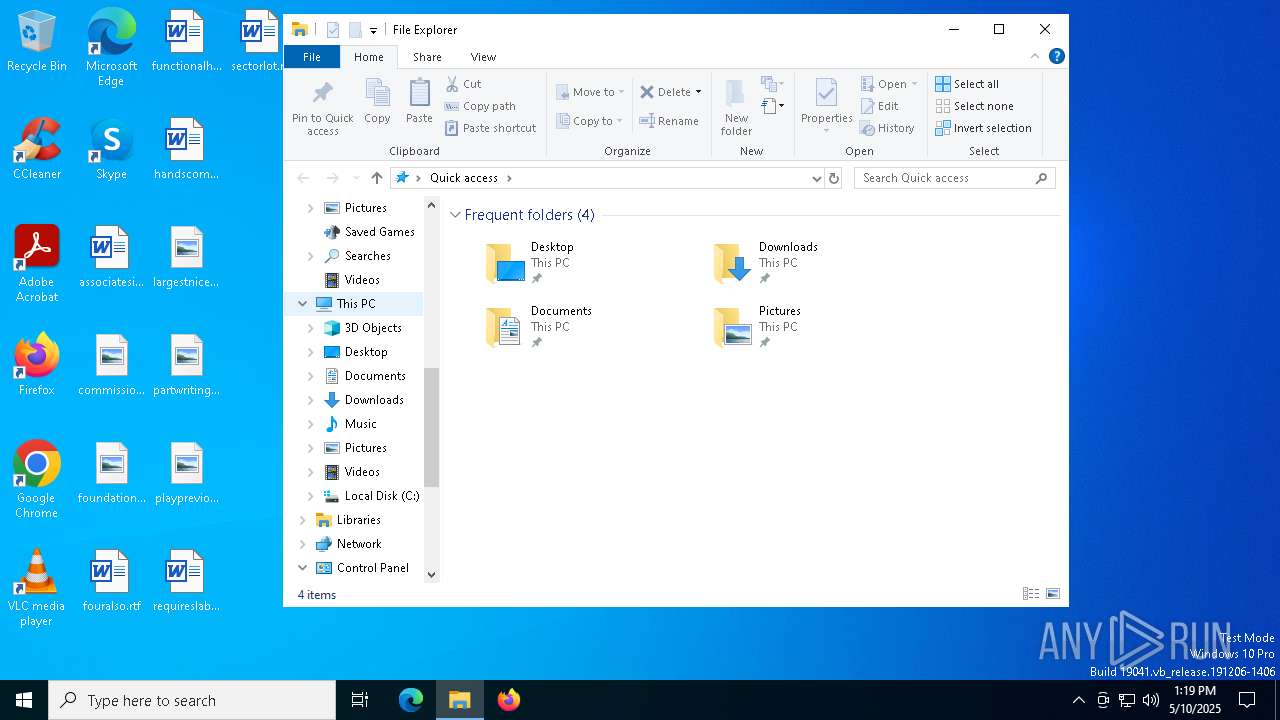
| URL: | https://get-genp.com/ |
| Full analysis: | https://app.any.run/tasks/48e94f52-9a15-42b0-8bca-97487716b6cb |
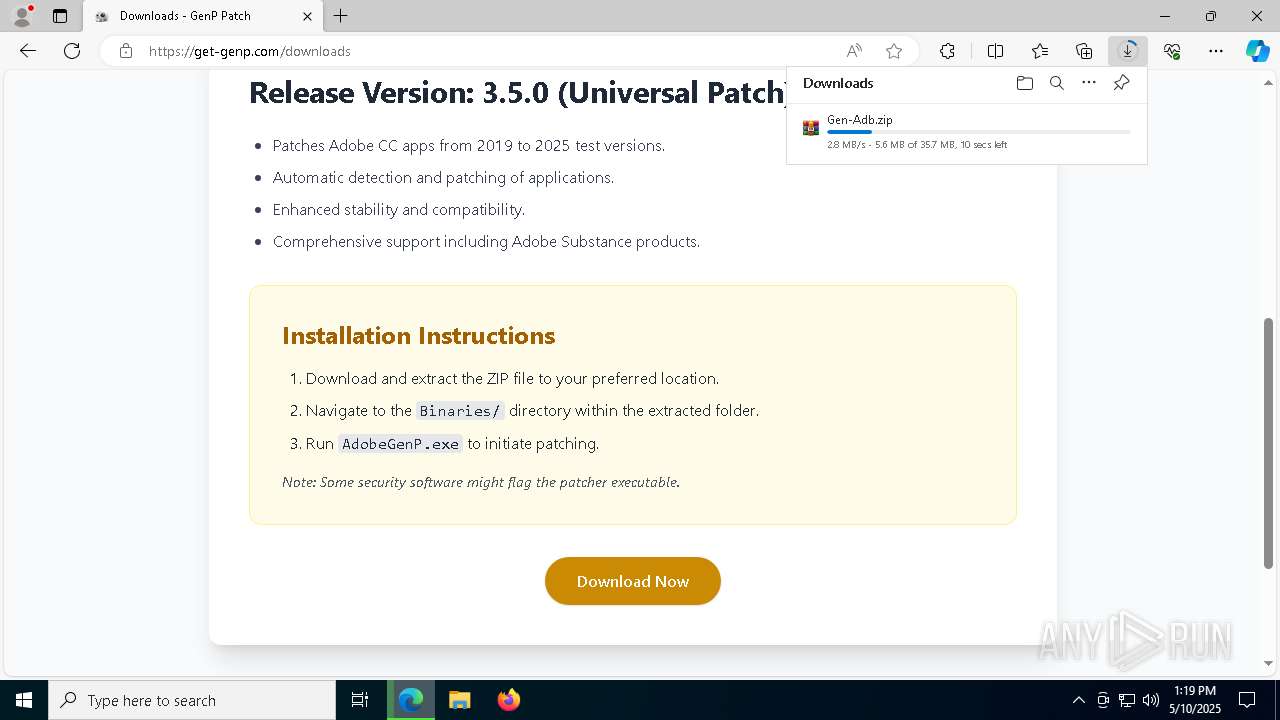
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | May 10, 2025, 13:18:59 |
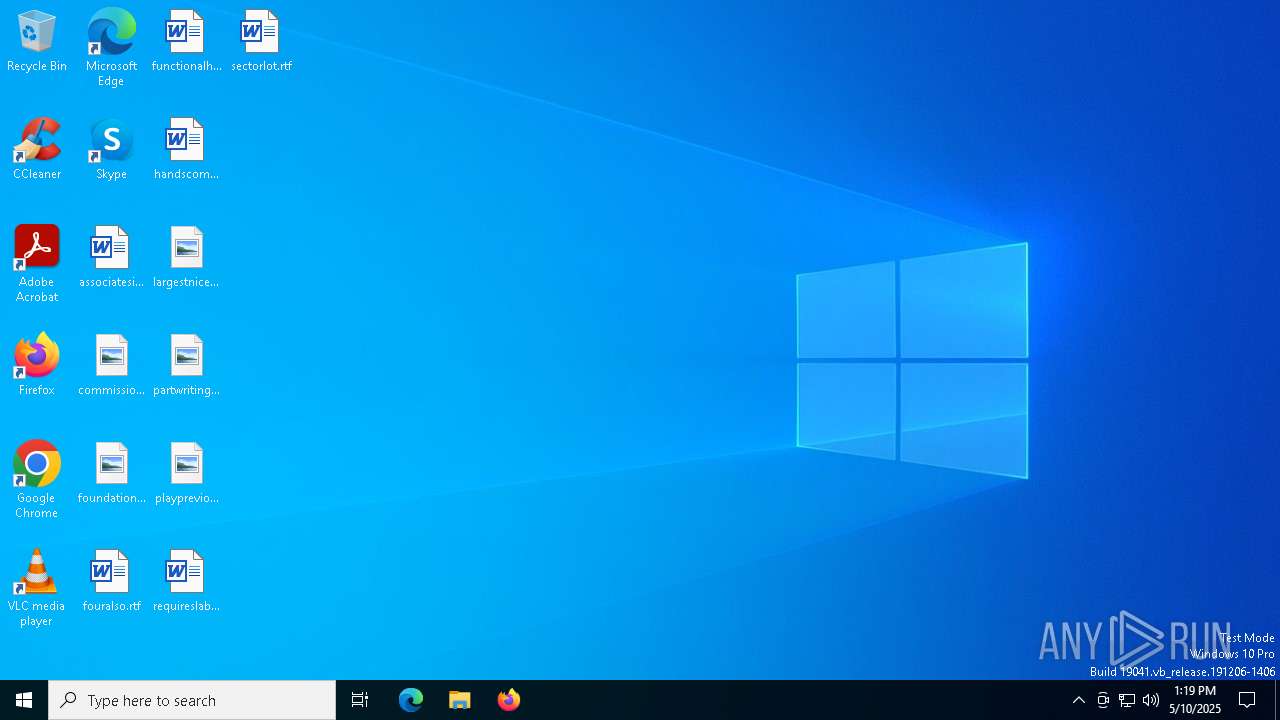
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
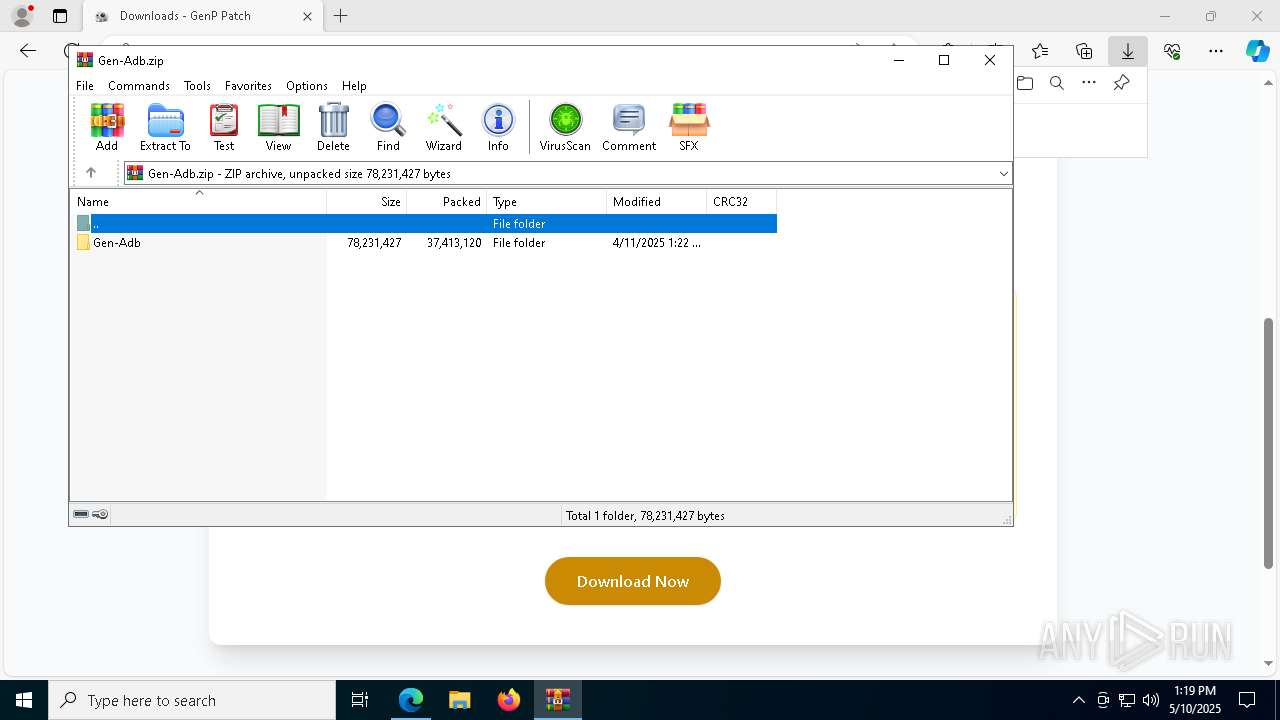
| MD5: | ABDCB203445E6298EAC830C0FF2EBC48 |
| SHA1: | 89E7F357FD98DB9D9F27688C6D7888024EC6AC4C |
| SHA256: | F9B2A5B9AB317ABBFA296E74F40B227E9283A89DE4E1E6D7DBED30C2FDD3CAEA |
| SSDEEP: | 3:N8hSLQG:2oLP |
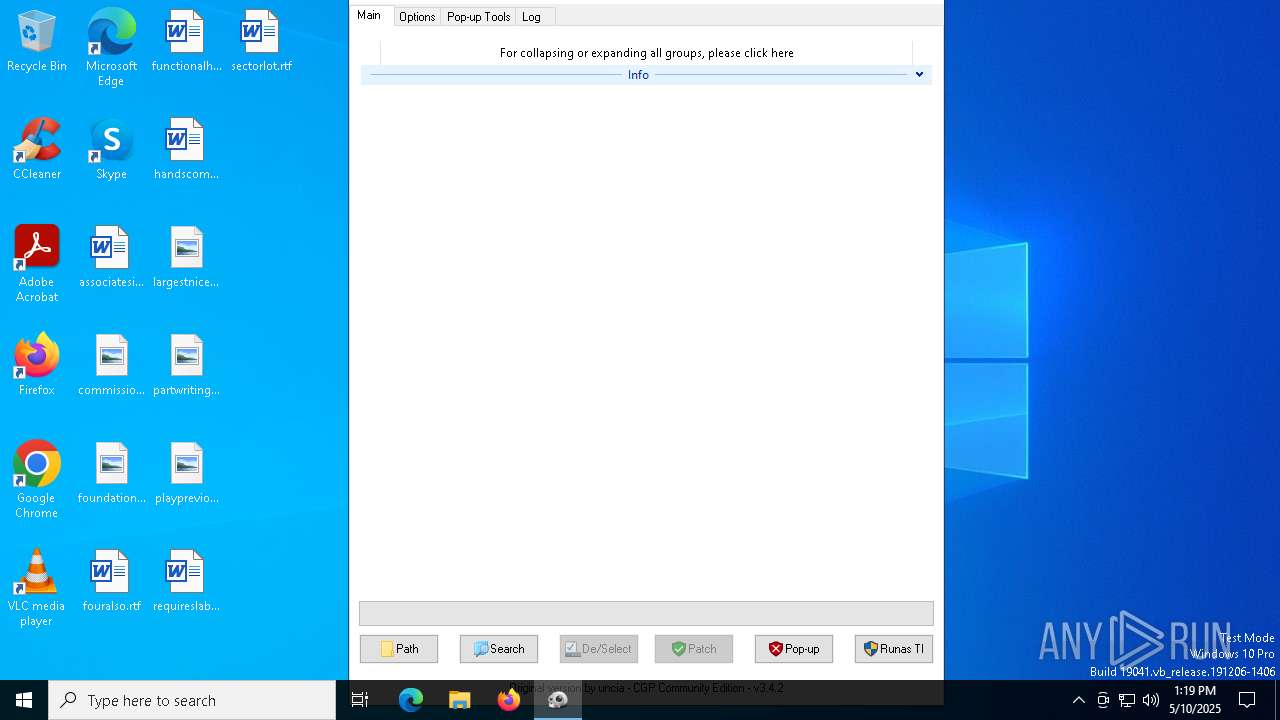
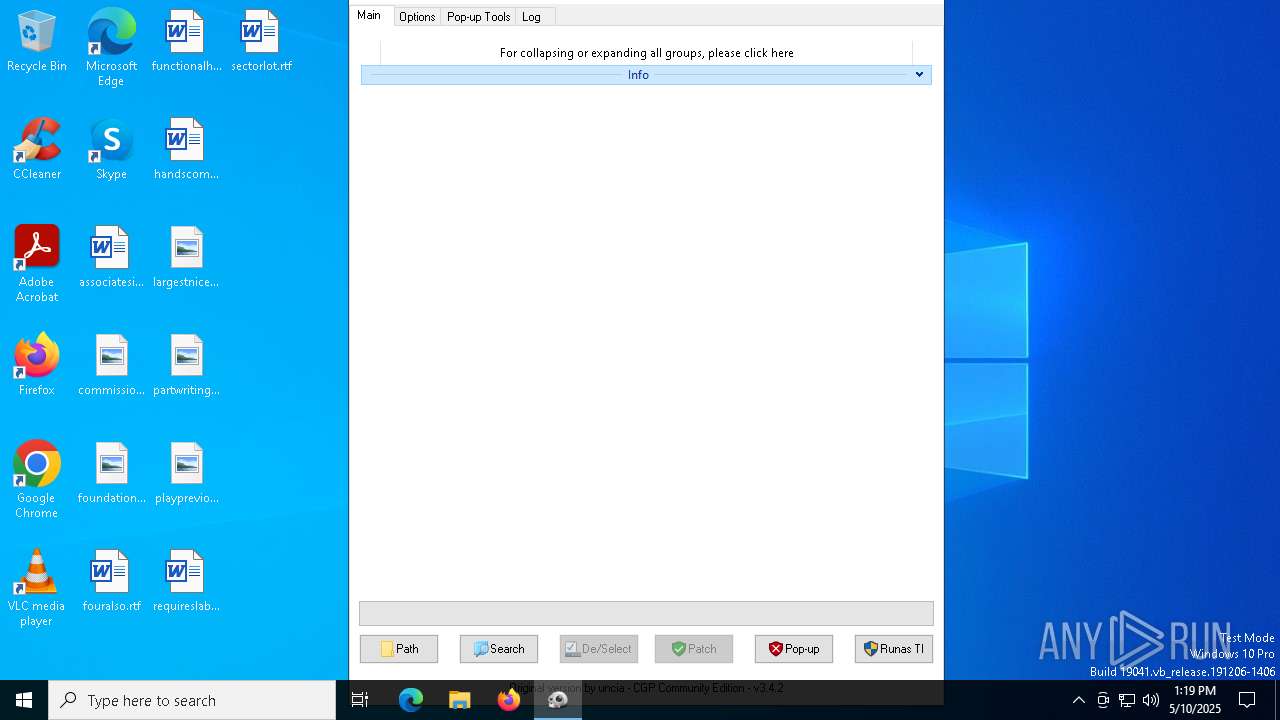
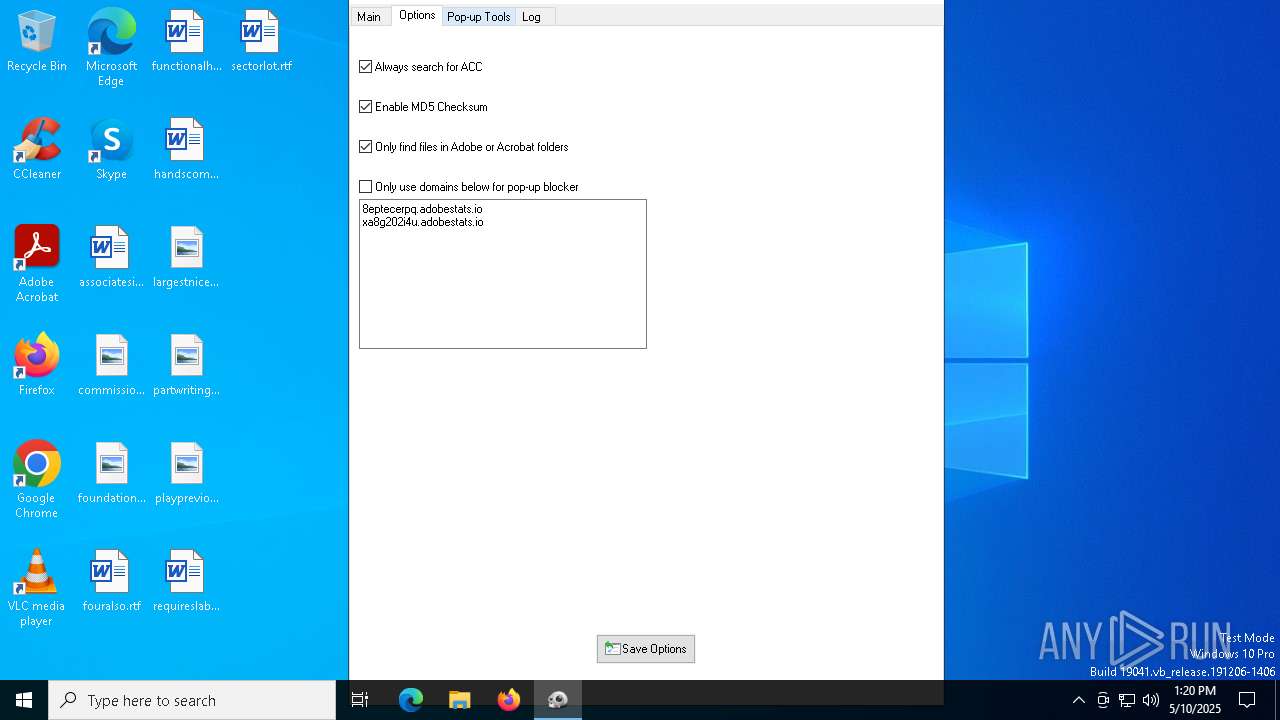
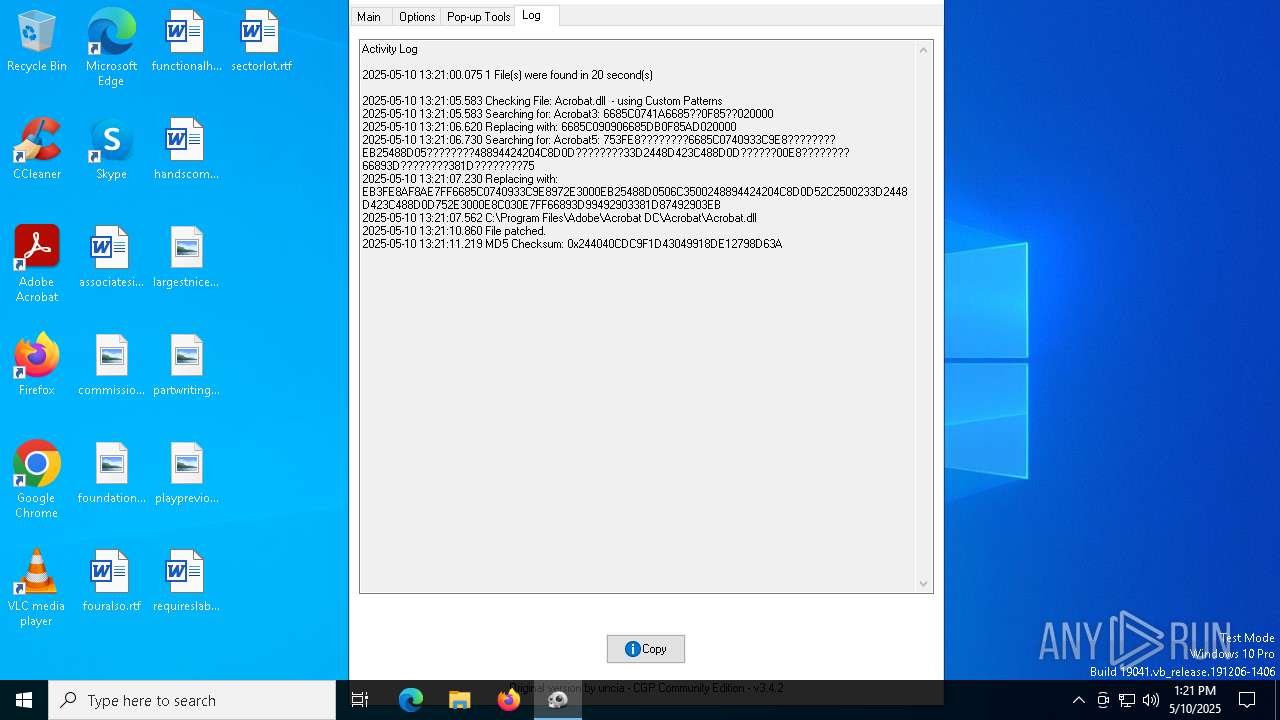
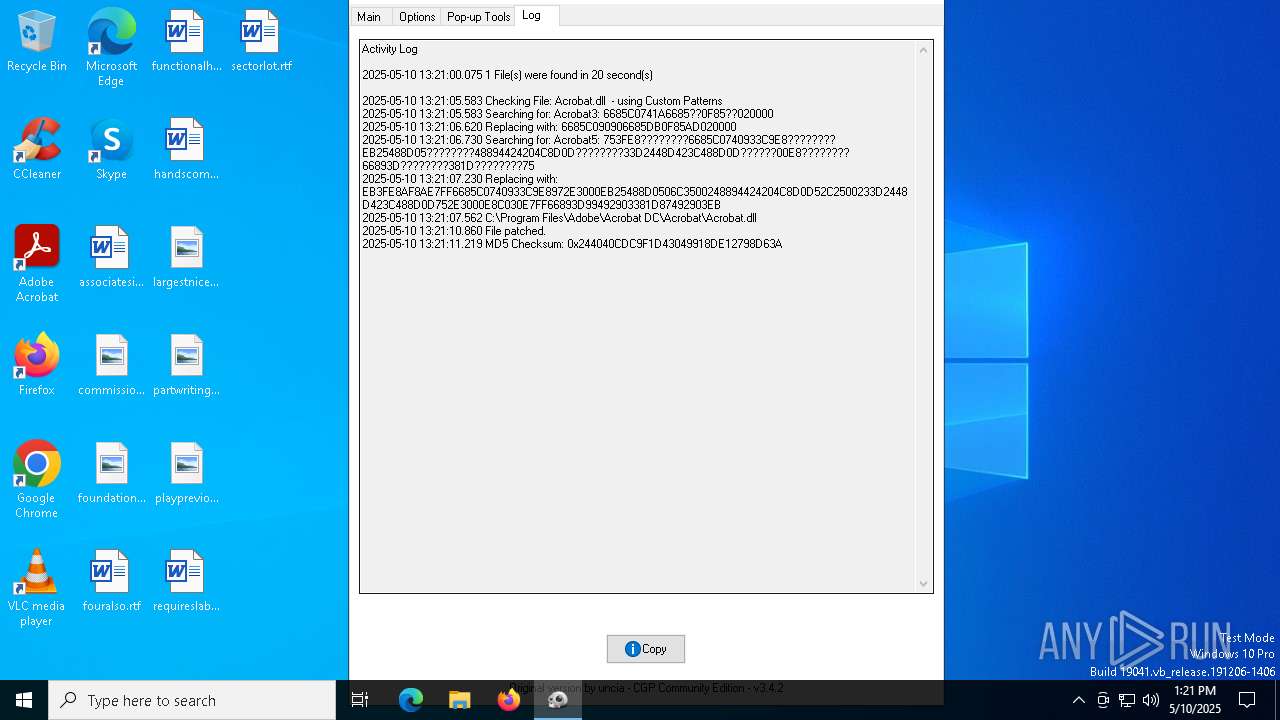
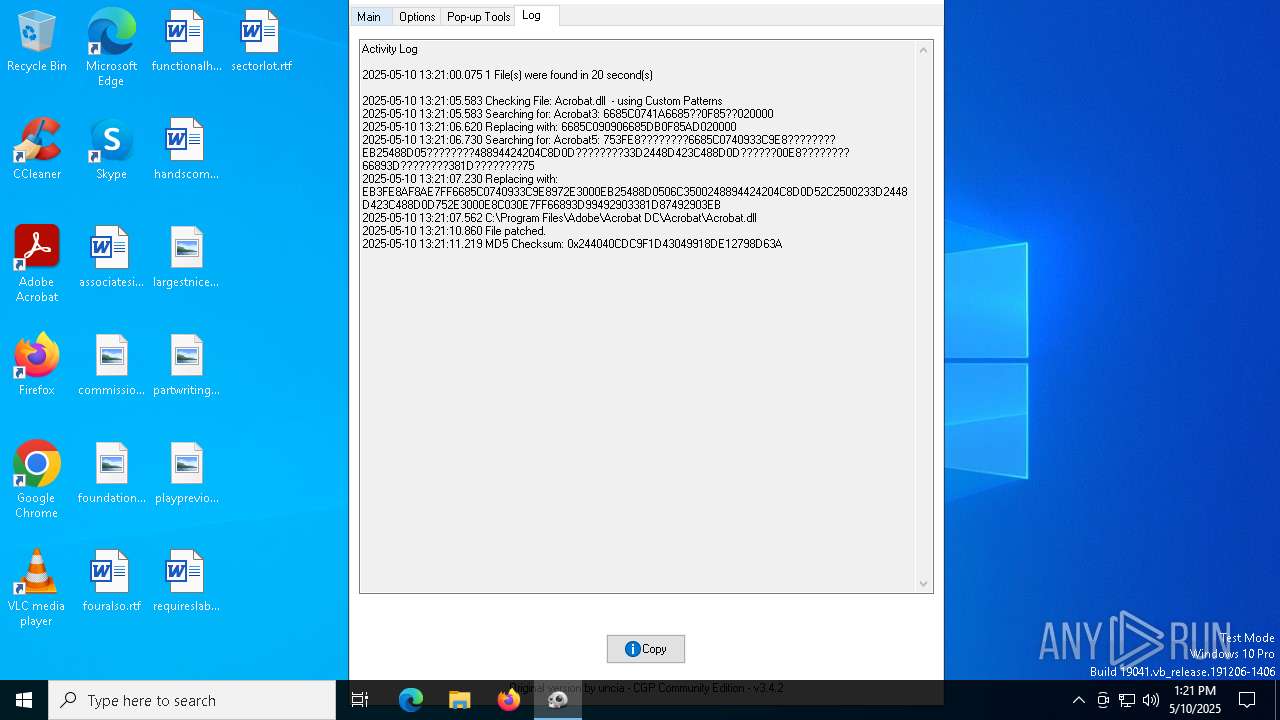
MALICIOUS
Uses Task Scheduler to autorun other applications
- cmd.exe (PID: 7376)
Run PowerShell with an invisible window
- powershell.exe (PID: 8112)
Bypass execution policy to execute commands
- powershell.exe (PID: 8112)
- powershell.exe (PID: 7656)
- powershell.exe (PID: 3192)
Changes powershell execution policy (Bypass)
- wscript.exe (PID: 7780)
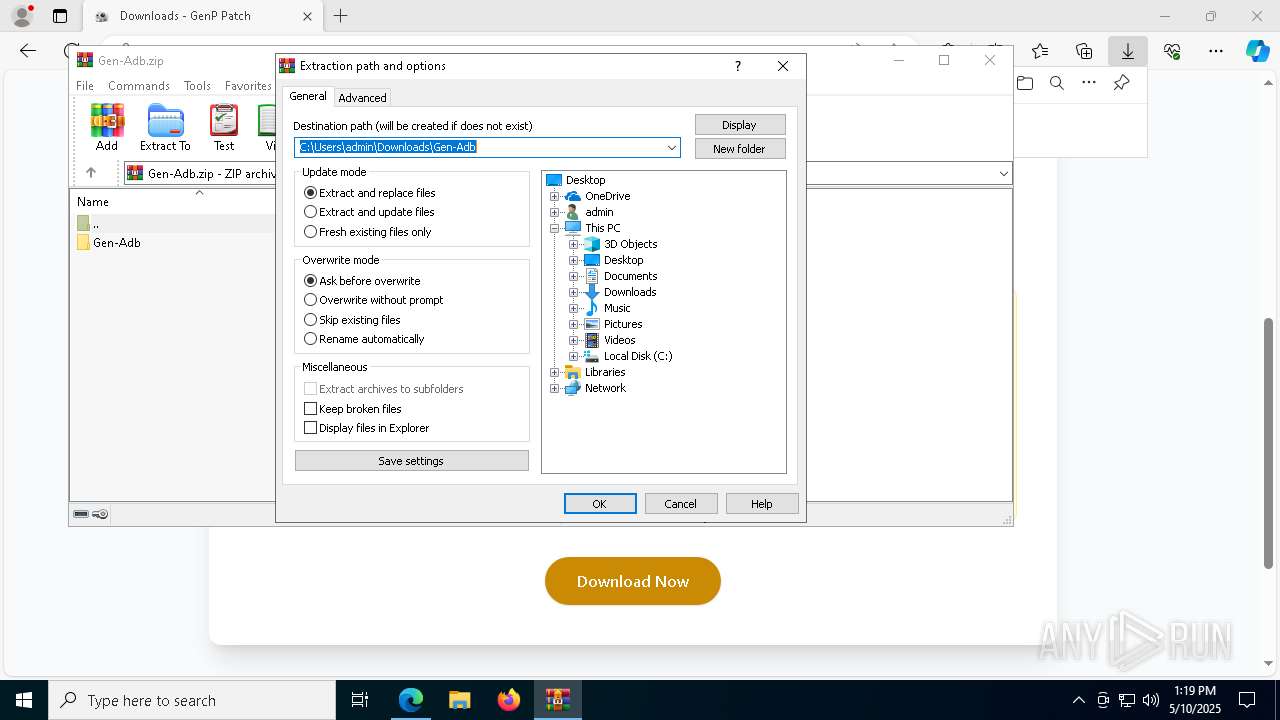
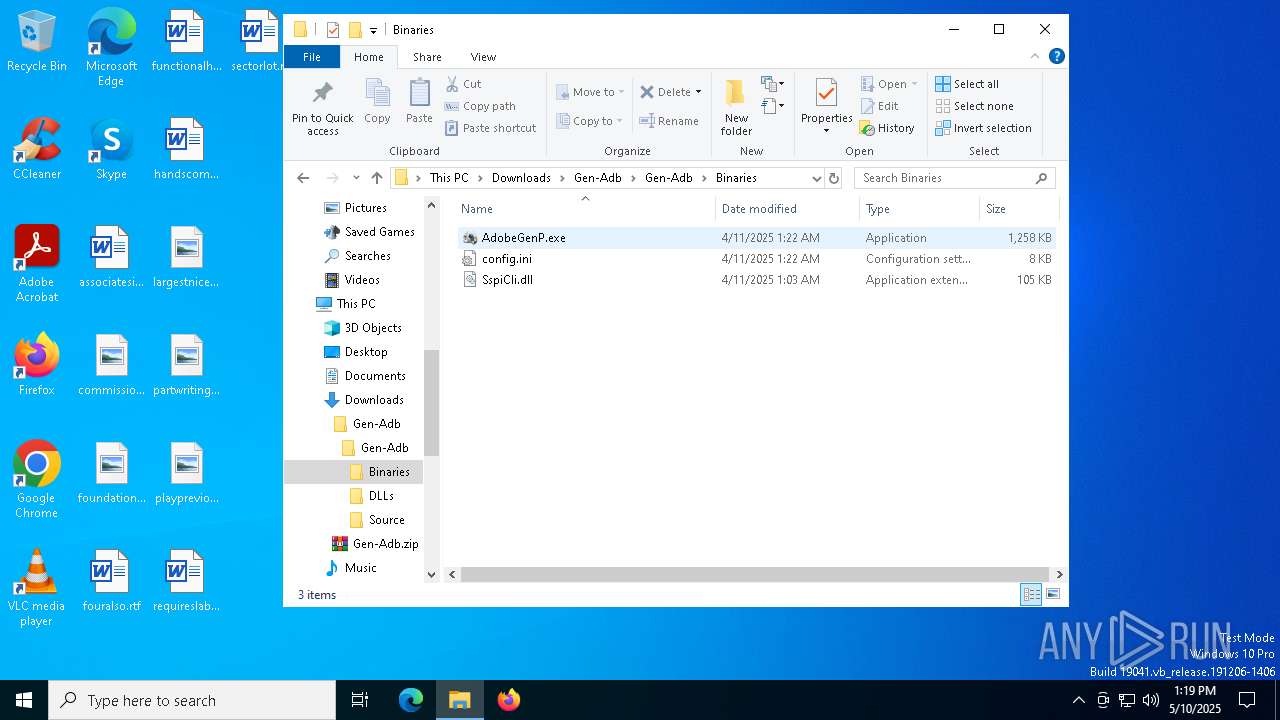
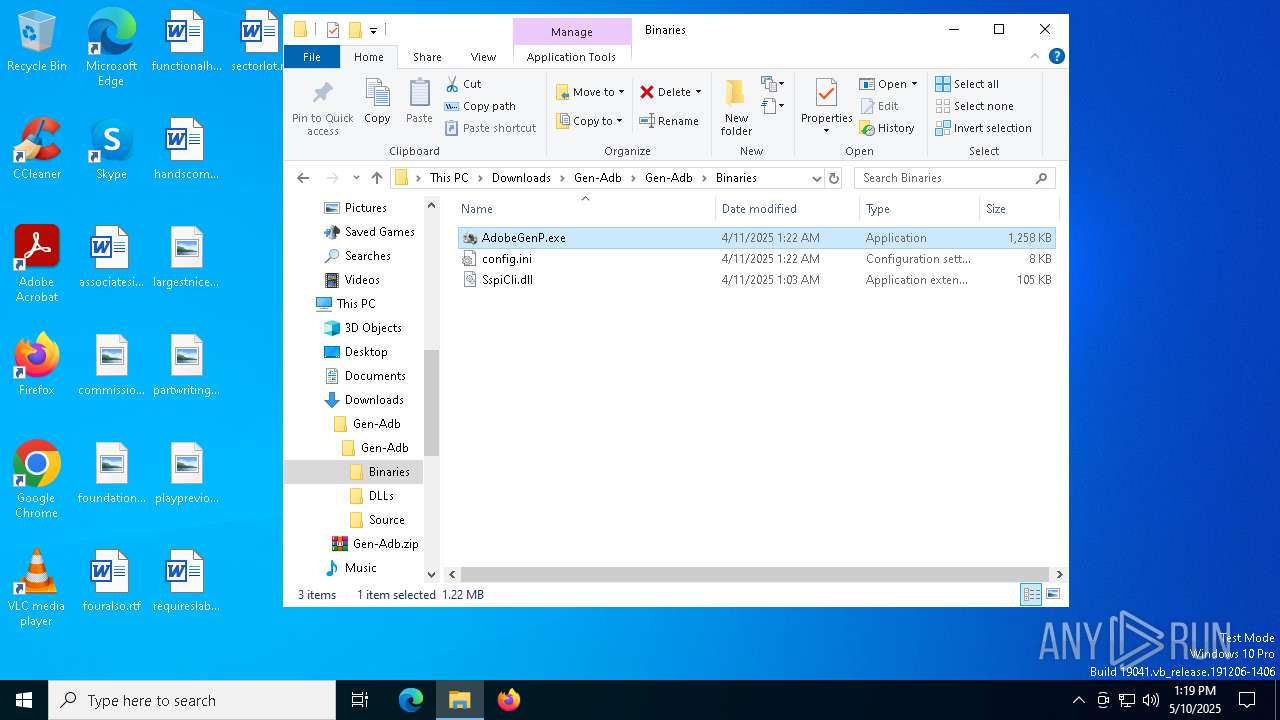
- AdobeGenP.exe (PID: 7532)
Adds path to the Windows Defender exclusion list
- python.exe (PID: 1096)
Changes Windows Defender settings
- python.exe (PID: 1096)
Vulnerable driver has been detected
- python.exe (PID: 1096)
- tar.exe (PID: 7540)
XMRIG has been detected
- python.exe (PID: 1096)
XMRig has been detected
- xmrig.exe (PID: 8040)
MINER has been detected (SURICATA)
- xmrig.exe (PID: 8040)
Connects to the CnC server
- xmrig.exe (PID: 8040)
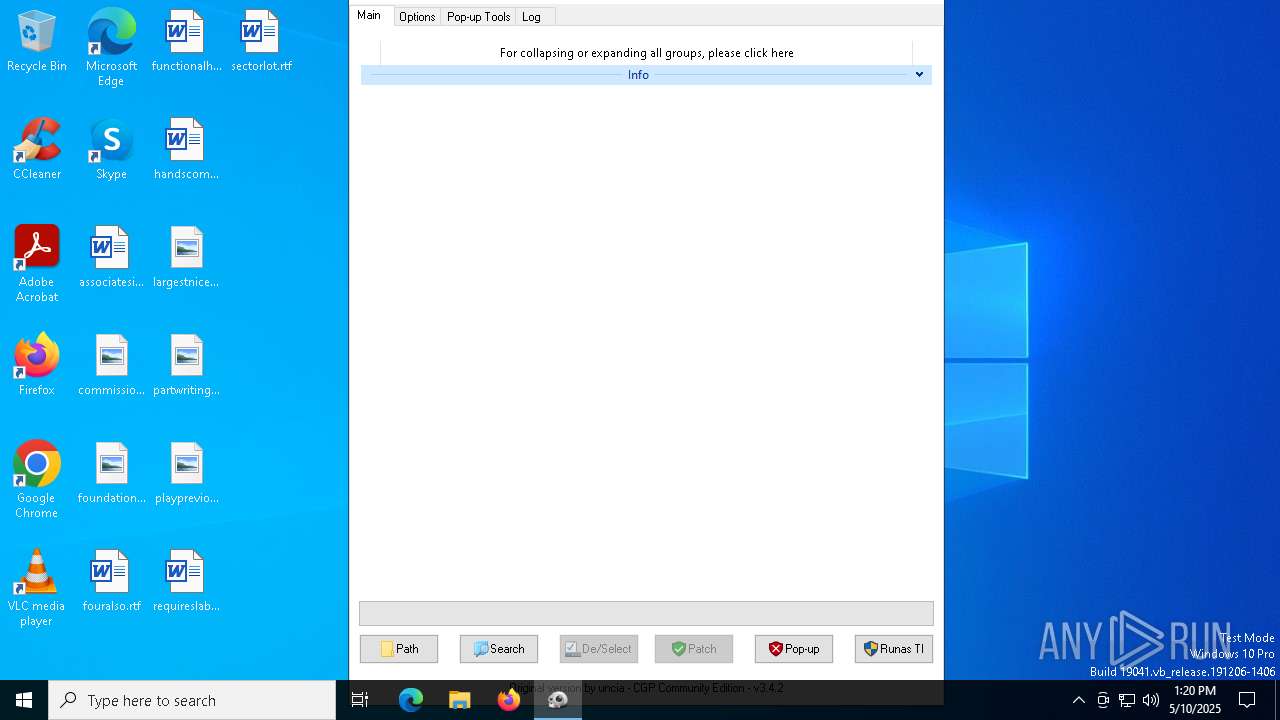
SUSPICIOUS
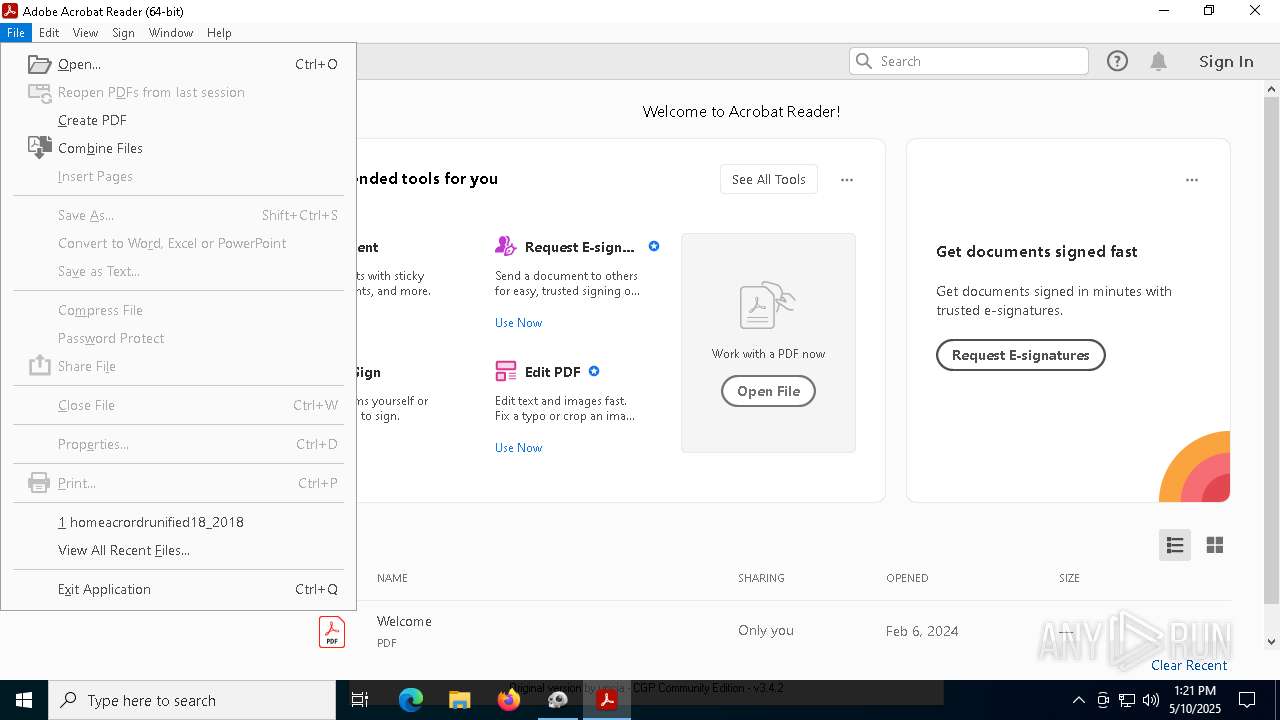
Starts CMD.EXE for commands execution
- AdobeGenP.exe (PID: 7532)
- python.exe (PID: 1096)
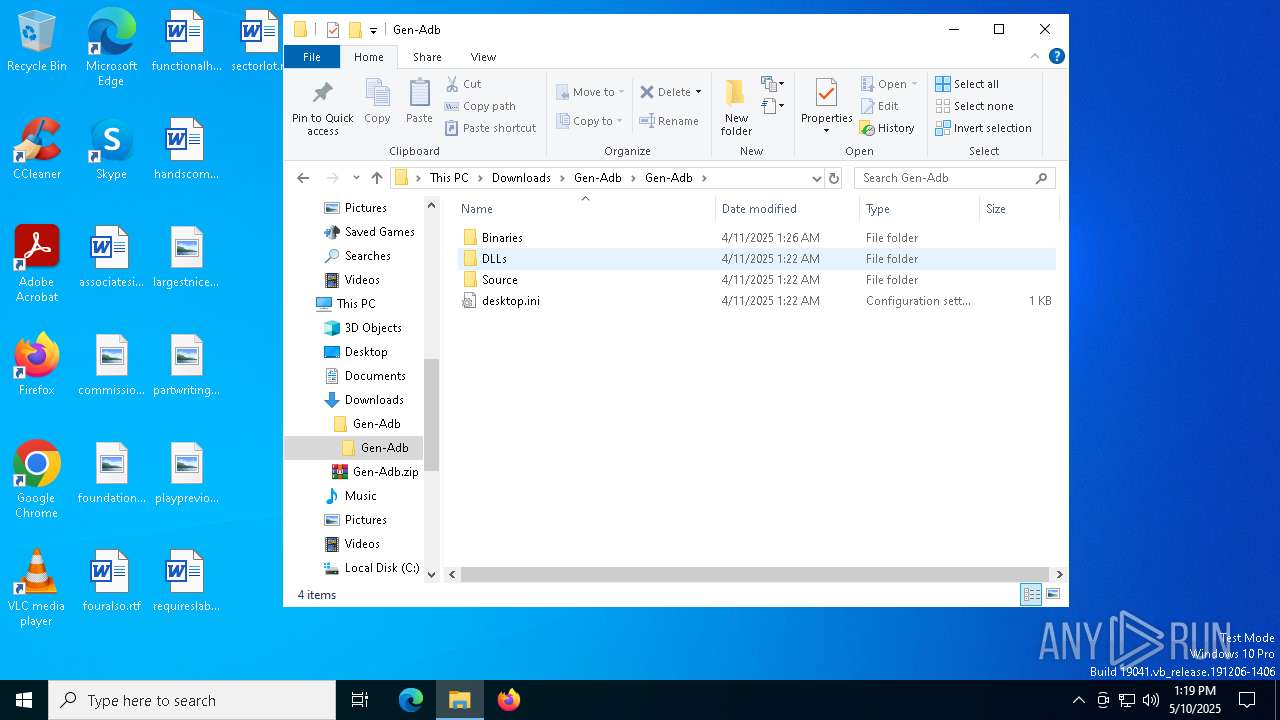
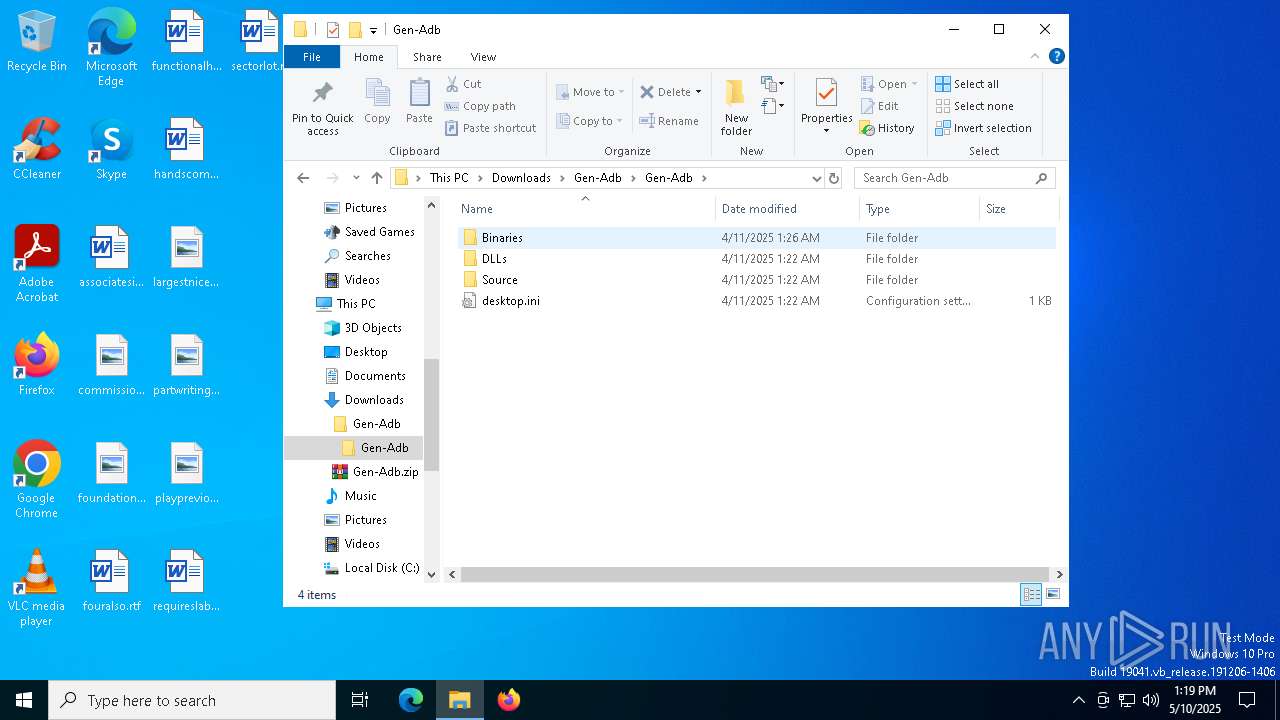
Write to the desktop.ini file (may be used to cloak folders)
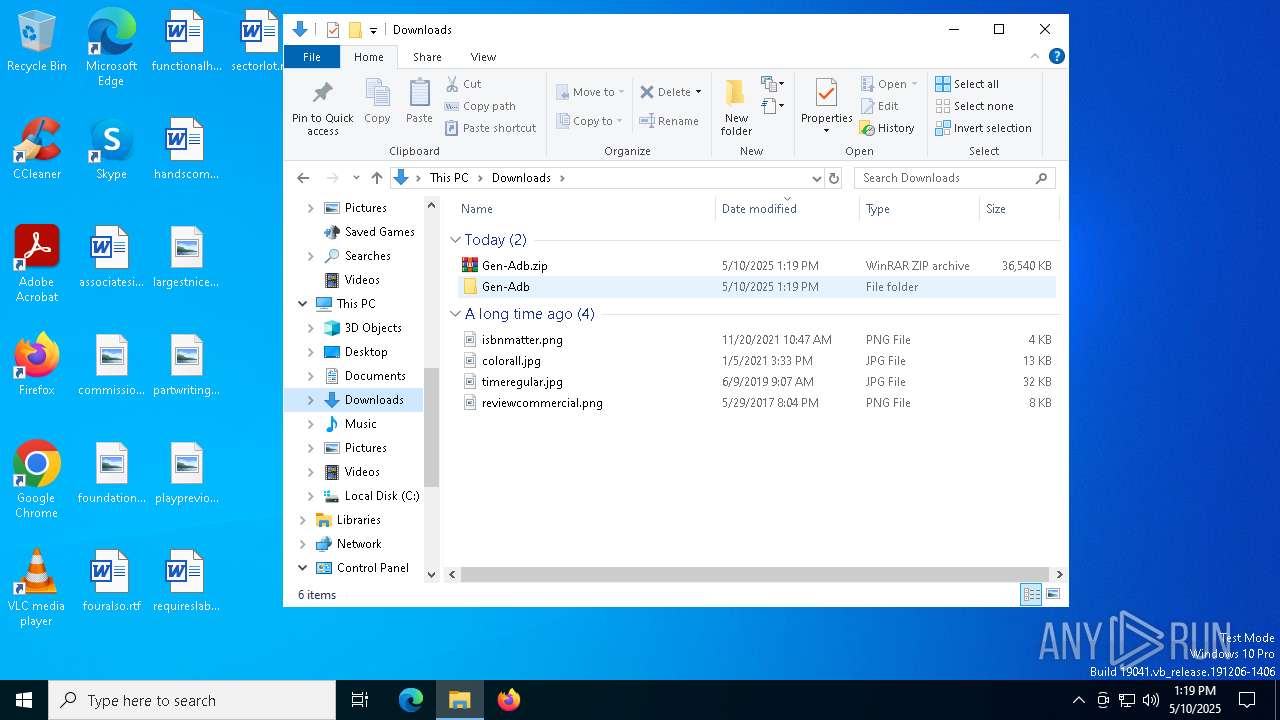
- WinRAR.exe (PID: 7892)
Execution of CURL command
- AdobeGenP.exe (PID: 7532)
The process executes via Task Scheduler
- wscript.exe (PID: 7780)
Executable content was dropped or overwritten
- tar.exe (PID: 7720)
- tar.exe (PID: 4212)
- tar.exe (PID: 960)
- tar.exe (PID: 7540)
Process drops python dynamic module
- tar.exe (PID: 7720)
- tar.exe (PID: 4212)
- tar.exe (PID: 960)
Process drops legitimate windows executable
- tar.exe (PID: 7720)
- tar.exe (PID: 4212)
The process drops C-runtime libraries
- tar.exe (PID: 7720)
- tar.exe (PID: 4212)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 7780)
- python.exe (PID: 1096)
- AdobeGenP.exe (PID: 7532)
The process bypasses the loading of PowerShell profile settings
- wscript.exe (PID: 7780)
Runs shell command (SCRIPT)
- wscript.exe (PID: 7780)
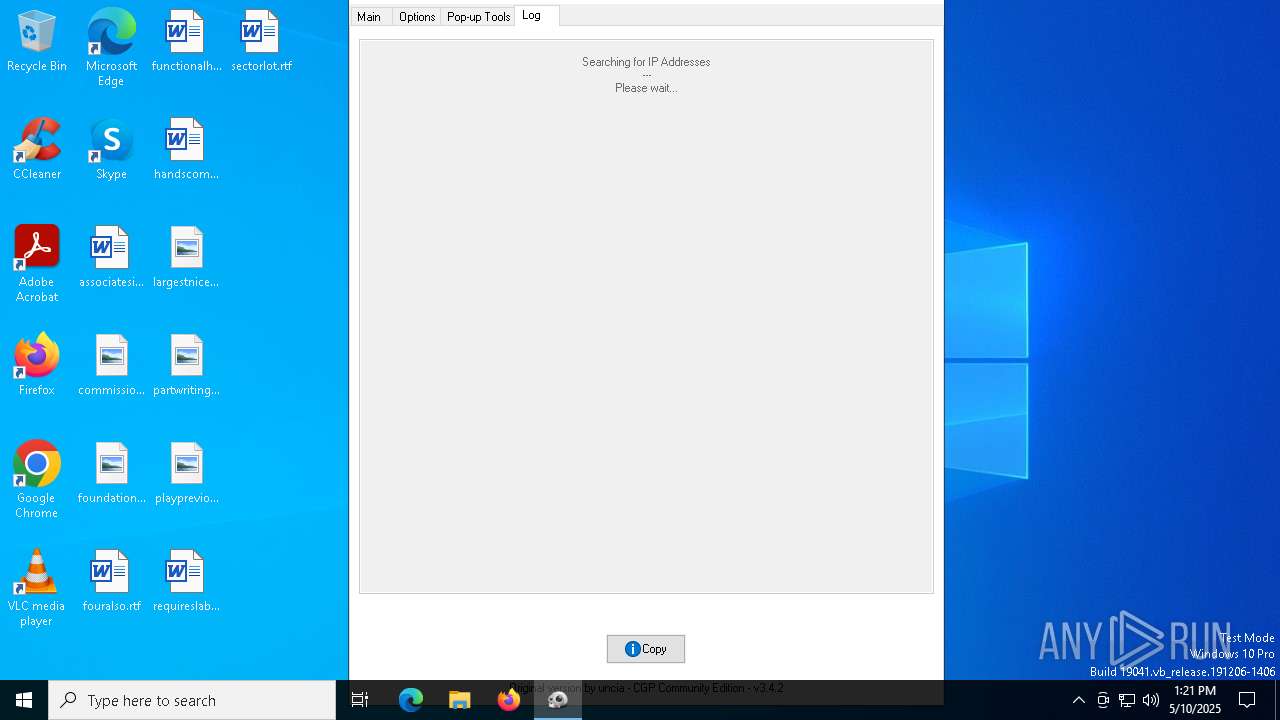
Checks for external IP
- svchost.exe (PID: 2196)
- python.exe (PID: 1096)
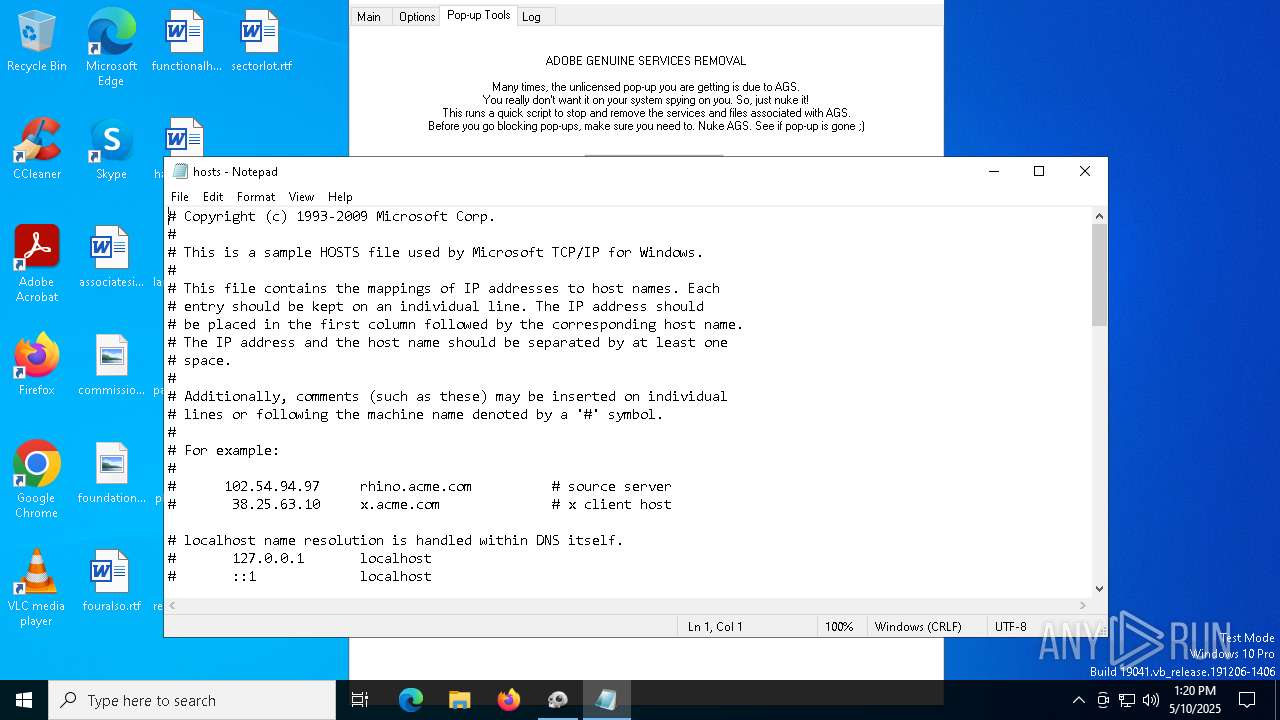
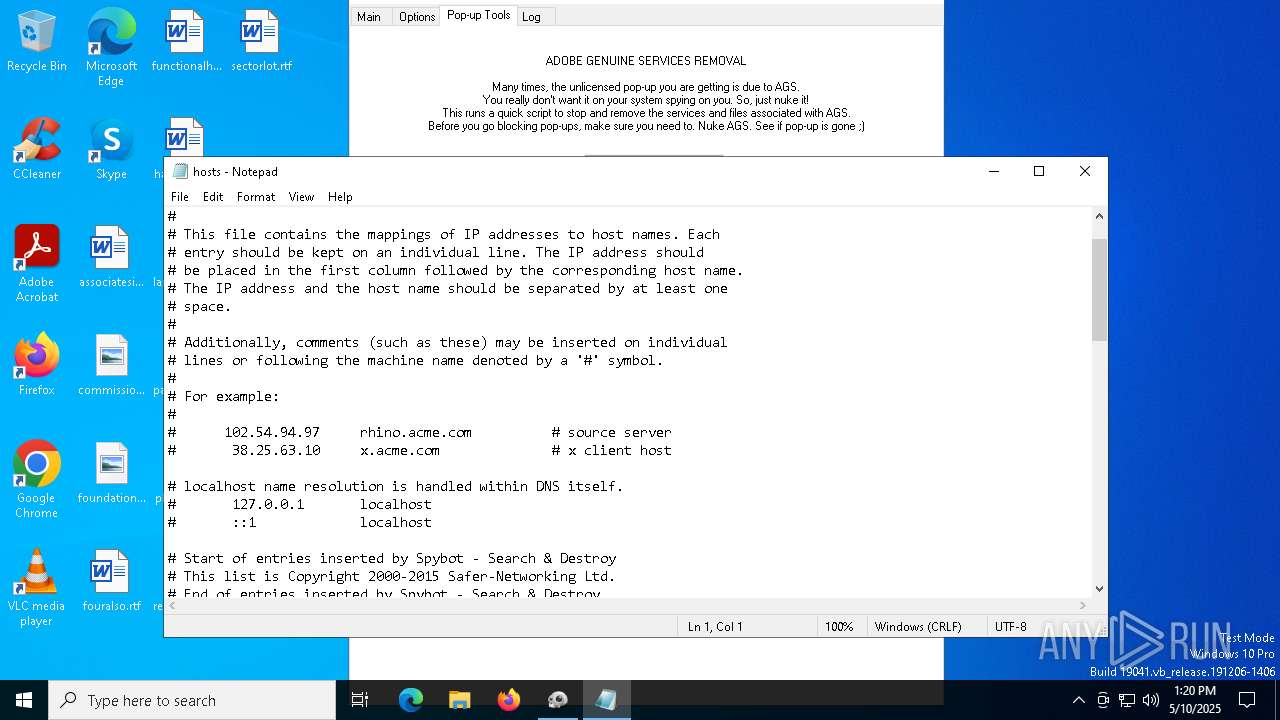
Start notepad (likely ransomware note)
- AdobeGenP.exe (PID: 7532)
Query Microsoft Defender preferences
- python.exe (PID: 1096)
Script adds exclusion path to Windows Defender
- python.exe (PID: 1096)
Drops a system driver (possible attempt to evade defenses)
- tar.exe (PID: 7540)
Potential Corporate Privacy Violation
- xmrig.exe (PID: 8040)
Connects to unusual port
- xmrig.exe (PID: 8040)
Found IP address in command line
- powershell.exe (PID: 7656)
- powershell.exe (PID: 3192)
Removes files via Powershell
- powershell.exe (PID: 3192)
Probably obfuscated PowerShell command line is found
- AdobeGenP.exe (PID: 7532)
Manipulates environment variables
- powershell.exe (PID: 3192)
ADOBEGENP mutex has been found
- AdobeGenP.exe (PID: 7532)
INFO
Application launched itself
- msedge.exe (PID: 6808)
- msedge.exe (PID: 1568)
- Acrobat.exe (PID: 7256)
Checks supported languages
- identity_helper.exe (PID: 7900)
- identity_helper.exe (PID: 7604)
- curl.exe (PID: 7280)
- tar.exe (PID: 7720)
- python.exe (PID: 1096)
- AdobeGenP.exe (PID: 7532)
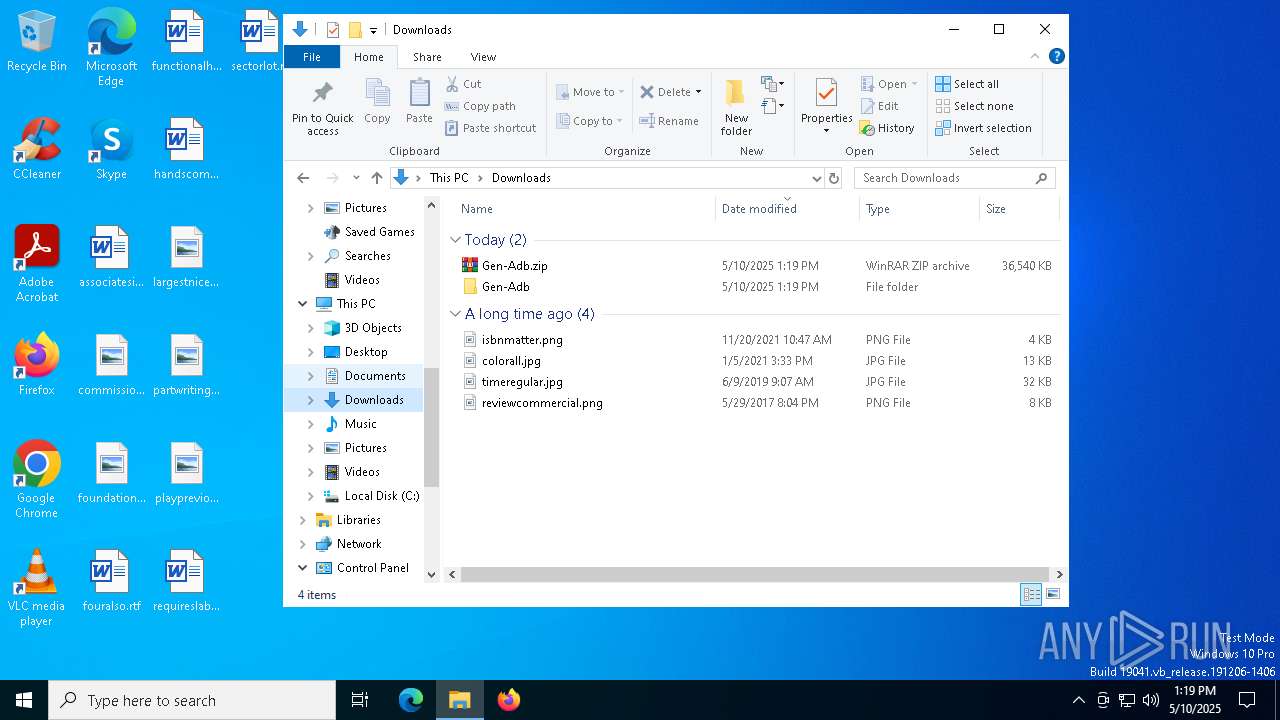
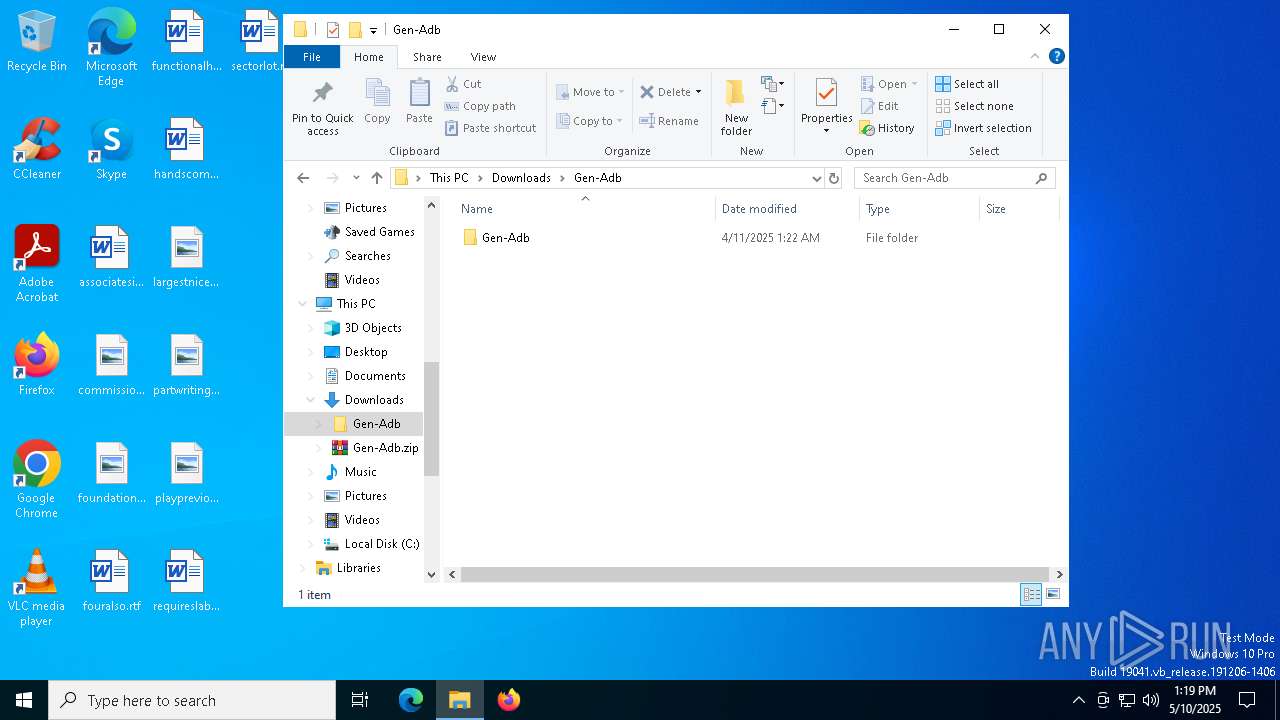
Creates a new folder
- cmd.exe (PID: 4784)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6808)
Reads the computer name
- identity_helper.exe (PID: 7900)
- identity_helper.exe (PID: 7604)
- curl.exe (PID: 7280)
- AdobeGenP.exe (PID: 7532)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7892)
Reads Environment values
- identity_helper.exe (PID: 7900)
- identity_helper.exe (PID: 7604)
The sample compiled with english language support
- WinRAR.exe (PID: 7892)
- tar.exe (PID: 7720)
- tar.exe (PID: 4212)
- tar.exe (PID: 960)
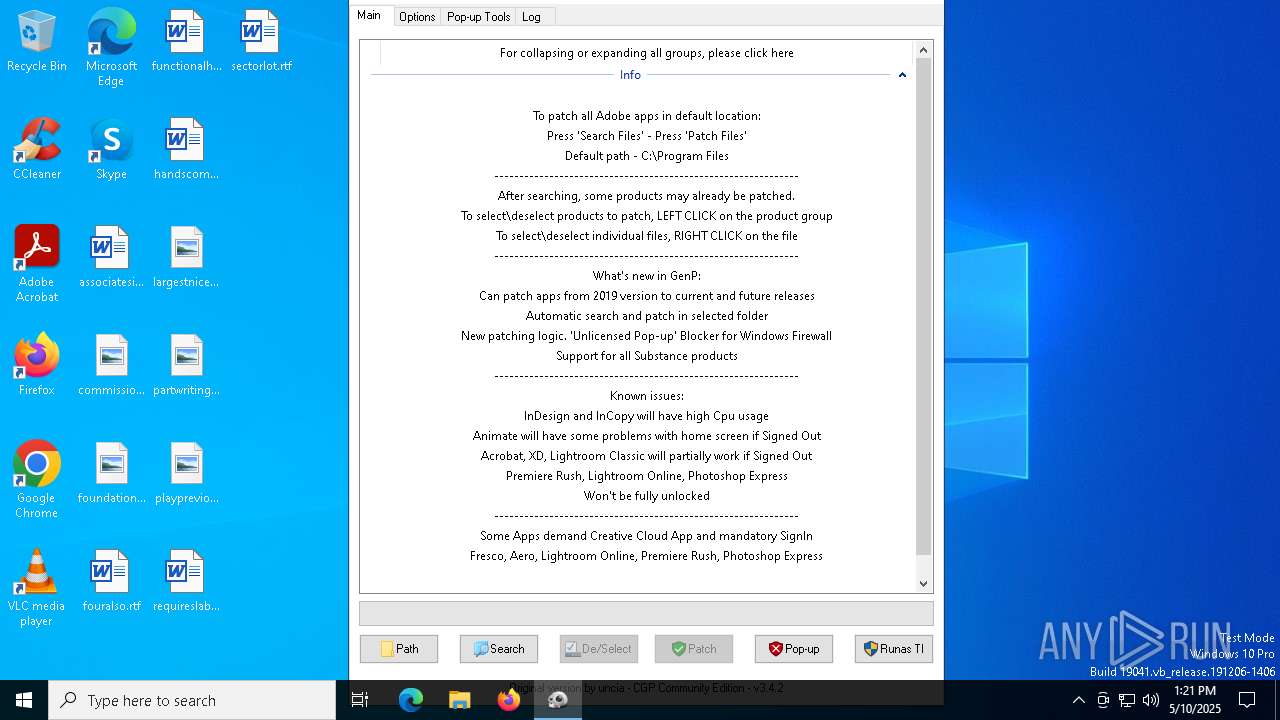
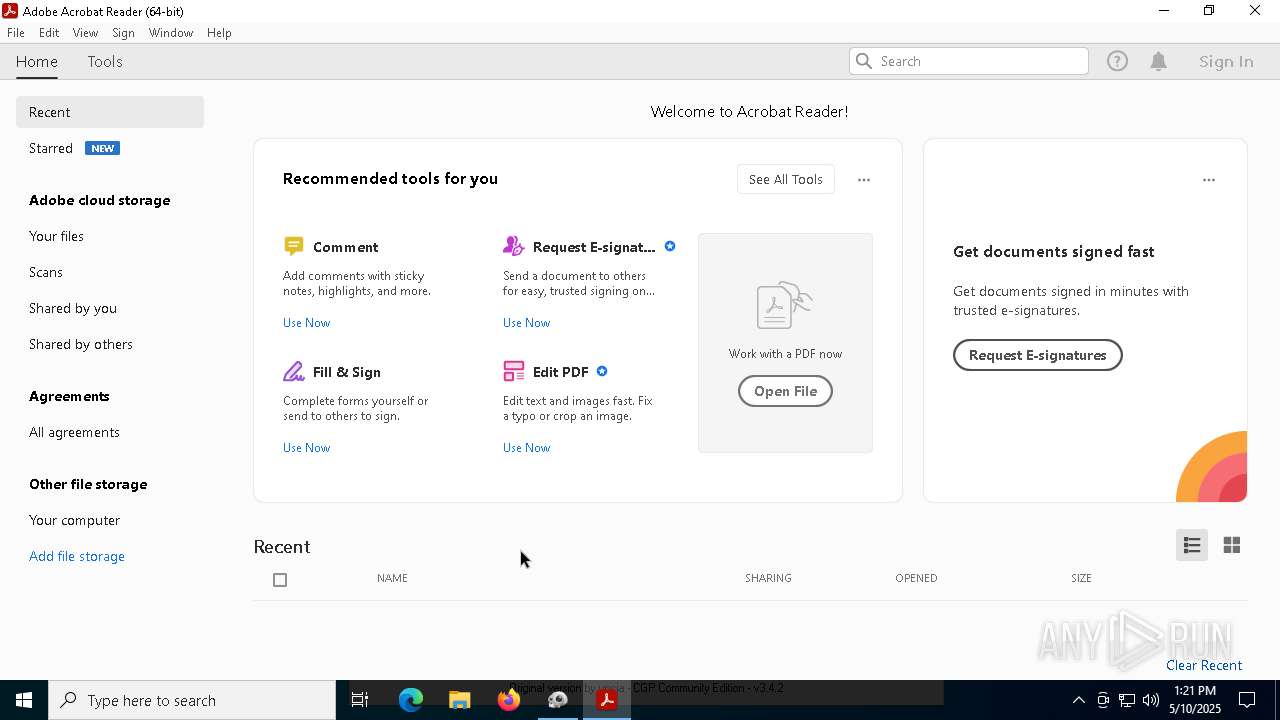
Manual execution by a user
- AdobeGenP.exe (PID: 7456)
- AdobeGenP.exe (PID: 7532)
- Acrobat.exe (PID: 7256)
Reads mouse settings
- AdobeGenP.exe (PID: 7532)
Execution of CURL command
- cmd.exe (PID: 7216)
Python executable
- python.exe (PID: 1096)
Checks operating system version
- python.exe (PID: 1096)
The sample compiled with japanese language support
- python.exe (PID: 1096)
- tar.exe (PID: 7540)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
234
Monitored processes
101
Malicious processes
6
Suspicious processes
4
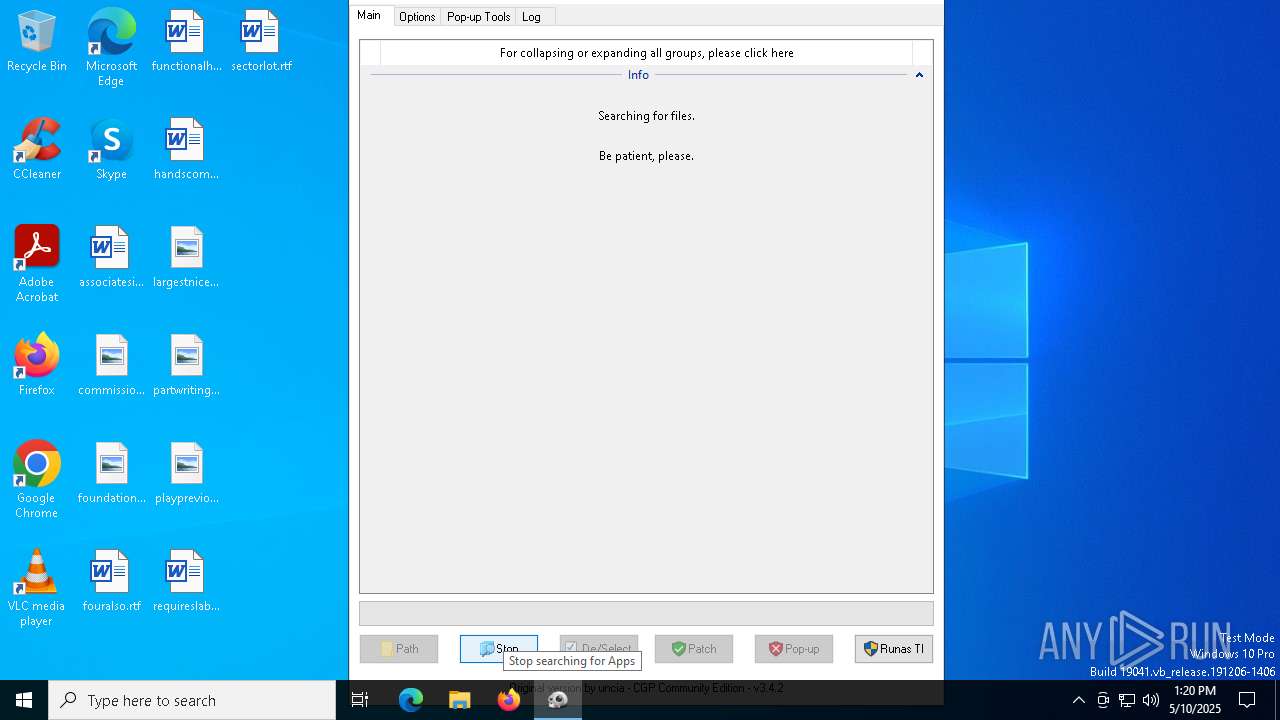
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x1c0,0x1e0,0x298,0x1e4,0x2a0,0x7ffc88225fd8,0x7ffc88225fe4,0x7ffc88225ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 780 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 904 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6652 --field-trial-handle=2356,i,10192358573623739259,11552641864673109238,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 960 | tar -xf nig.zip | C:\Windows\System32\tar.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: bsdtar archive tool Version: 3.5.2 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1096 | "C:\Windows\SystemHealth\Update\python.exe" .\SysMon.py | C:\Windows\SystemHealth\Update\python.exe | powershell.exe | ||||||||||||
User: admin Company: Python Software Foundation Integrity Level: HIGH Description: Python Version: 3.11.0 Modules
| |||||||||||||||
| 1388 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=1640 --field-trial-handle=2232,i,7435471158569699540,12476152952066708911,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1568 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1628 | C:\WINDOWS\system32\cmd.exe /c tar -xf getthem.zip | C:\Windows\System32\cmd.exe | — | python.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1672 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=6100 --field-trial-handle=2356,i,10192358573623739259,11552641864673109238,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1760 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6388 --field-trial-handle=2356,i,10192358573623739259,11552641864673109238,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
51 980
Read events
51 778
Write events
181
Delete events
21
Modification events
| (PID) Process: | (6808) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: E1D5DB355E932F00 | |||
| (PID) Process: | (6808) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 6AB3E3355E932F00 | |||
| (PID) Process: | (6808) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328466 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {B3ABC5D0-CA7B-4B00-B5E0-94E535887756} | |||
| (PID) Process: | (6808) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328466 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E083F31D-9A80-424A-85A6-79837F806446} | |||
| (PID) Process: | (6808) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6808) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6808) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6808) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6808) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328466 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {833928CC-C48F-448F-979E-5EAA8CC8B5D7} | |||
| (PID) Process: | (6808) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: D10C3F365E932F00 | |||
Executable files
218
Suspicious files
1 767
Text files
1 905
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10ba3a.TMP | — | |
MD5:— | SHA256:— | |||
| 6808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10ba49.TMP | — | |
MD5:— | SHA256:— | |||
| 6808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10ba49.TMP | — | |
MD5:— | SHA256:— | |||
| 6808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10ba49.TMP | — | |
MD5:— | SHA256:— | |||
| 6808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10ba59.TMP | — | |
MD5:— | SHA256:— | |||
| 6808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
78
DNS requests
4 486
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5344 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5344 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7280 | curl.exe | GET | 200 | 172.67.206.1:8080 | http://micro-economics.net:8080/downloadables/Update.zip | unknown | — | — | unknown |
7236 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0bff3331-8429-4575-9b2b-a689321198ed?P1=1747389042&P2=404&P3=2&P4=ls%2bJJ%2boSOFVp2O4D2WnQIXdskCt4B2G7avSrwTrtySSTO2XUfmrd3hc4MkpDt9x9OpZpsWHIwRnkvXIYxELTXg%3d%3d | unknown | — | — | whitelisted |
7236 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0bff3331-8429-4575-9b2b-a689321198ed?P1=1747389042&P2=404&P3=2&P4=ls%2bJJ%2boSOFVp2O4D2WnQIXdskCt4B2G7avSrwTrtySSTO2XUfmrd3hc4MkpDt9x9OpZpsWHIwRnkvXIYxELTXg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
6808 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7320 | msedge.exe | 104.21.48.1:443 | get-genp.com | — | — | unknown |
7320 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
get-genp.com |
| unknown |
business.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7320 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7320 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
1096 | python.exe | Device Retrieving External IP Address Detected | ET INFO Possible External IP Lookup Domain Observed in SNI (ipinfo. io) |
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ipinfo .io) |
2196 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
1096 | python.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
8040 | xmrig.exe | Potential Corporate Privacy Violation | ET INFO Cryptocurrency Miner Checkin |
8040 | xmrig.exe | Potential Corporate Privacy Violation | ET INFO Cryptocurrency Miner Checkin |