| File name: | BTG.exe |
| Full analysis: | https://app.any.run/tasks/4b715d63-2653-4ef0-af2e-870309a7749b |
| Verdict: | Malicious activity |
| Threats: | RedLine Stealer is a malicious program that collects users’ confidential data from browsers, systems, and installed software. It also infects operating systems with other malware. |
| Analysis date: | September 05, 2023, 13:04:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | C190C8F963520C2F26EFCDFE49C24E16 |
| SHA1: | 8137E915CD53E31E6DAC573615C56374F26FF401 |
| SHA256: | F944A07BF87FAD81F1070E3334876B7C7566991D06BD69478E2B8A9CA1BF3169 |
| SSDEEP: | 24576:kbWxJMFmKXbhpvGg6qpxPL9bSUjHD2b23:7EXbhpvGOtRjj2b2 |
MALICIOUS
Unusual connection from system programs
- vbc.exe (PID: 2380)
Connects to the CnC server
- vbc.exe (PID: 2380)
Steals credentials from Web Browsers
- vbc.exe (PID: 2380)
REDLINE was detected
- vbc.exe (PID: 2380)
REDLINE detected by memory dumps
- vbc.exe (PID: 2380)
Actions looks like stealing of personal data
- vbc.exe (PID: 2380)
SUSPICIOUS
The process executes VB scripts
- BTG.exe (PID: 2968)
Reads browser cookies
- vbc.exe (PID: 2380)
Searches for installed software
- vbc.exe (PID: 2380)
Reads the Internet Settings
- vbc.exe (PID: 2380)
INFO
Checks supported languages
- BTG.exe (PID: 2968)
- vbc.exe (PID: 2380)
Reads the computer name
- vbc.exe (PID: 2380)
Reads Environment values
- vbc.exe (PID: 2380)
Reads product name
- vbc.exe (PID: 2380)
Reads the machine GUID from the registry
- vbc.exe (PID: 2380)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
RedLine
(PID) Process(2380) vbc.exe
C2 (1)94.142.138.4:80
Botnet@nmrzv88
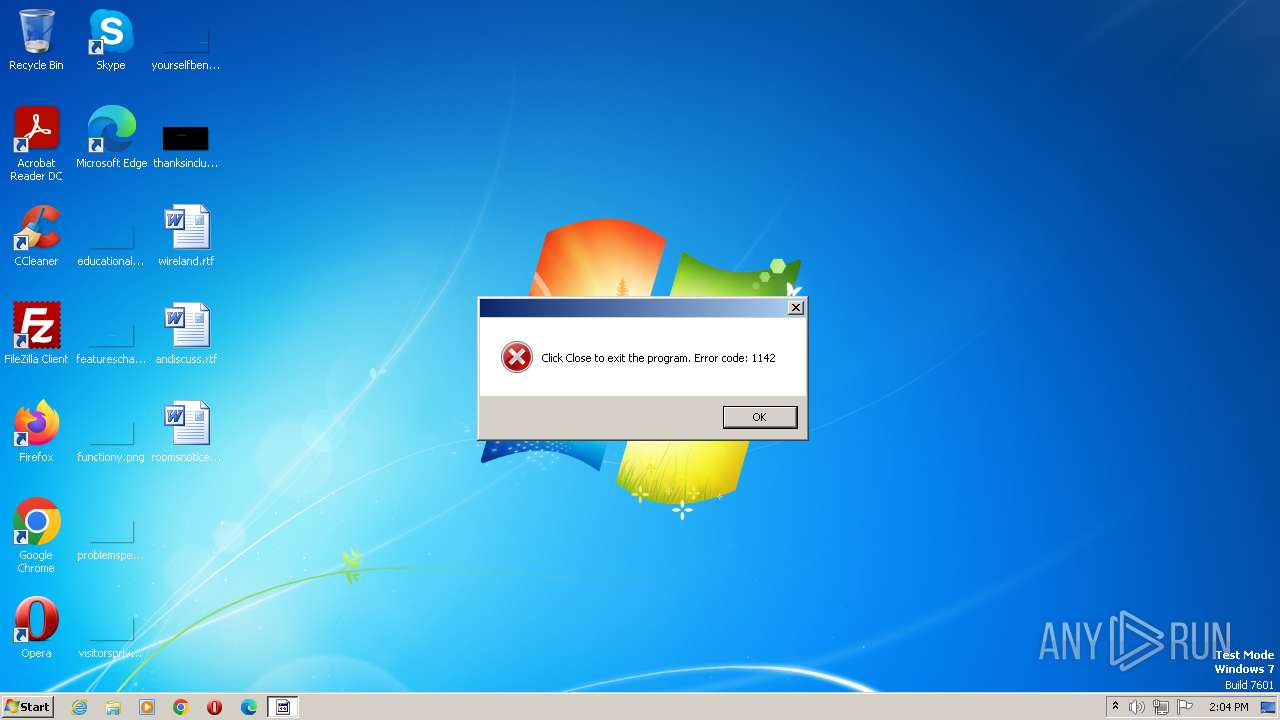
Err_msgClick Close to exit the program. Error code: 1142
Auth_valueff2294eb8c32446e92144d9b8a702d93
US (12)
net.tcp://
/
localhost
ff2294eb8c32446e92144d9b8a702d93
Authorization
ns1
DDs/Bjg5NB0gEwYVITBBXSoOCw4=
EihbBxYDFVYjPSRS
El0WAyxfFgM9SzsZDUEgCgEjVB4ZNwYDES4nVA0+FggNOz8bP1cmESE8WhQnNS8dDkoKCDdBTAY/MAMeDjsrQzgKWFk=
Consumedly
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 6 |
| EntryPoint: | 0x11ea |
| UninitializedDataSize: | - |
| InitializedDataSize: | 385024 |
| CodeSize: | 728064 |
| LinkerVersion: | 14.32 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, 32-bit |
| TimeStamp: | 2023:09:05 12:43:01+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Sep-2023 12:43:01 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 11 |
| Time date stamp: | 05-Sep-2023 12:43:01 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000B1B5A | 0x000B1C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.72556 |
.rdata | 0x000B3000 | 0x0001BF31 | 0x0001C000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.08465 |
.data | 0x000CF000 | 0x00039FC0 | 0x00038000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.27478 |
.idata | 0x00109000 | 0x00001313 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.79772 |
.tls | 0x0010B000 | 0x00000309 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0111738 |
.00cfg | 0x0010C000 | 0x0000010E | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.110557 |
.rsrc | 0x0010D000 | 0x0000043C | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.14297 |
.reloc | 0x0010E000 | 0x00005F47 | 0x00006000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.09676 |
.snake | 0x0011A000 | 0x00002710 | 0x00002800 | IMAGE_SCN_MEM_READ, IMAGE_SCN_TYPE_COPY | 0.0201847 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
Imports
KERNEL32.dll |
USER32.dll |
Total processes
36
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2380 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\vbc.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\vbc.exe | BTG.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 12.0.51209.34209 Modules
RedLine(PID) Process(2380) vbc.exe C2 (1)94.142.138.4:80 Botnet@nmrzv88 Err_msgClick Close to exit the program. Error code: 1142 Auth_valueff2294eb8c32446e92144d9b8a702d93 US (12) net.tcp:// / localhost ff2294eb8c32446e92144d9b8a702d93 Authorization ns1 DDs/Bjg5NB0gEwYVITBBXSoOCw4= EihbBxYDFVYjPSRS El0WAyxfFgM9SzsZDUEgCgEjVB4ZNwYDES4nVA0+FggNOz8bP1cmESE8WhQnNS8dDkoKCDdBTAY/MAMeDjsrQzgKWFk= Consumedly | |||||||||||||||
| 2968 | "C:\Users\admin\AppData\Local\Temp\BTG.exe" | C:\Users\admin\AppData\Local\Temp\BTG.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
1 381
Read events
1 381
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
1
Threats
10
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2380 | vbc.exe | 94.142.138.4:80 | — | Network Management Ltd | RU | malicious |
3284 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2380 | vbc.exe | 172.67.75.172:443 | api.ip.sb | CLOUDFLARENET | US | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.ip.sb |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2380 | vbc.exe | Potentially Bad Traffic | ET INFO Microsoft net.tcp Connection Initialization Activity |
2380 | vbc.exe | A Network Trojan was detected | ET MALWARE Redline Stealer TCP CnC Activity |
2380 | vbc.exe | A Network Trojan was detected | ET MALWARE [ANY.RUN] RedLine Stealer Related (MC-NMF Authorization) |
2380 | vbc.exe | A Network Trojan was detected | ET MALWARE Redline Stealer TCP CnC - Id1Response |
2380 | vbc.exe | A Network Trojan was detected | ET MALWARE Redline Stealer TCP CnC - Id1Response |
2380 | vbc.exe | A Network Trojan was detected | ET MALWARE Redline Stealer TCP CnC Activity |
2380 | vbc.exe | Successful Credential Theft Detected | SUSPICIOUS [ANY.RUN] Clear Text Password Exfiltration Atempt |
2380 | vbc.exe | Successful Credential Theft Detected | SUSPICIOUS [ANY.RUN] Clear Text Password Exfiltration Atempt |
2380 | vbc.exe | A Network Trojan was detected | ET MALWARE Redline Stealer TCP CnC Activity |
1 ETPRO signatures available at the full report