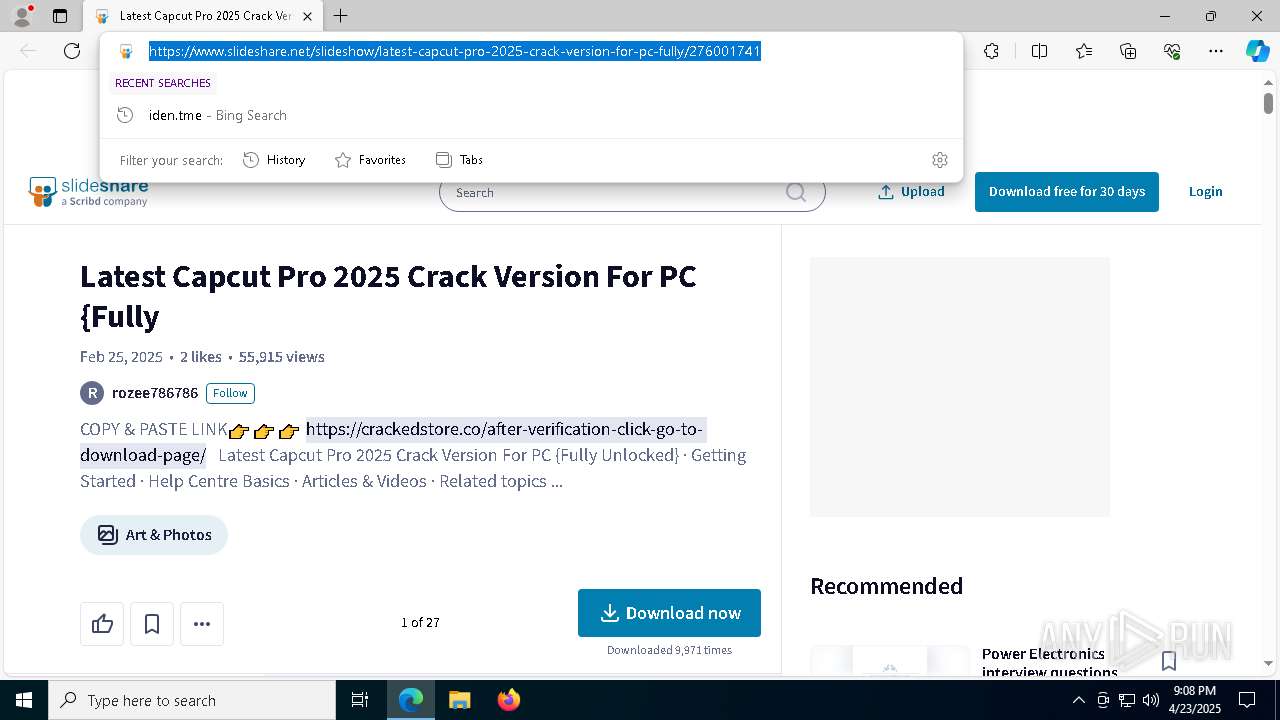
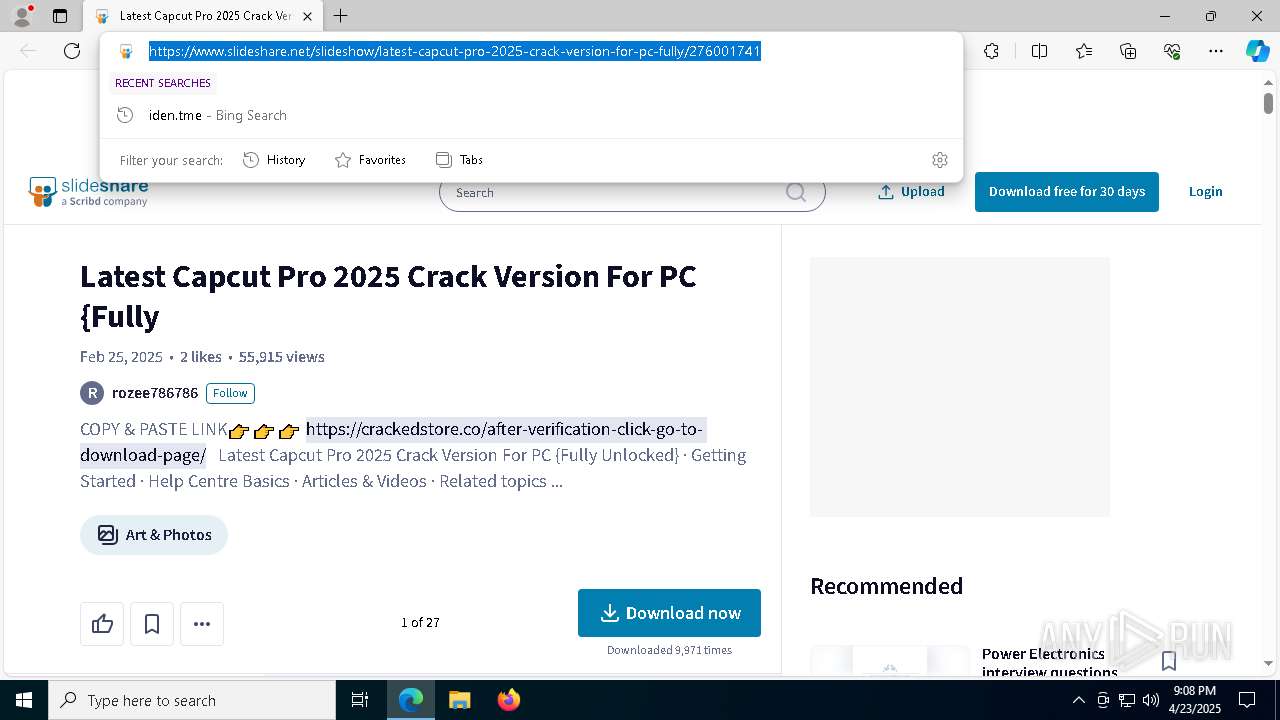
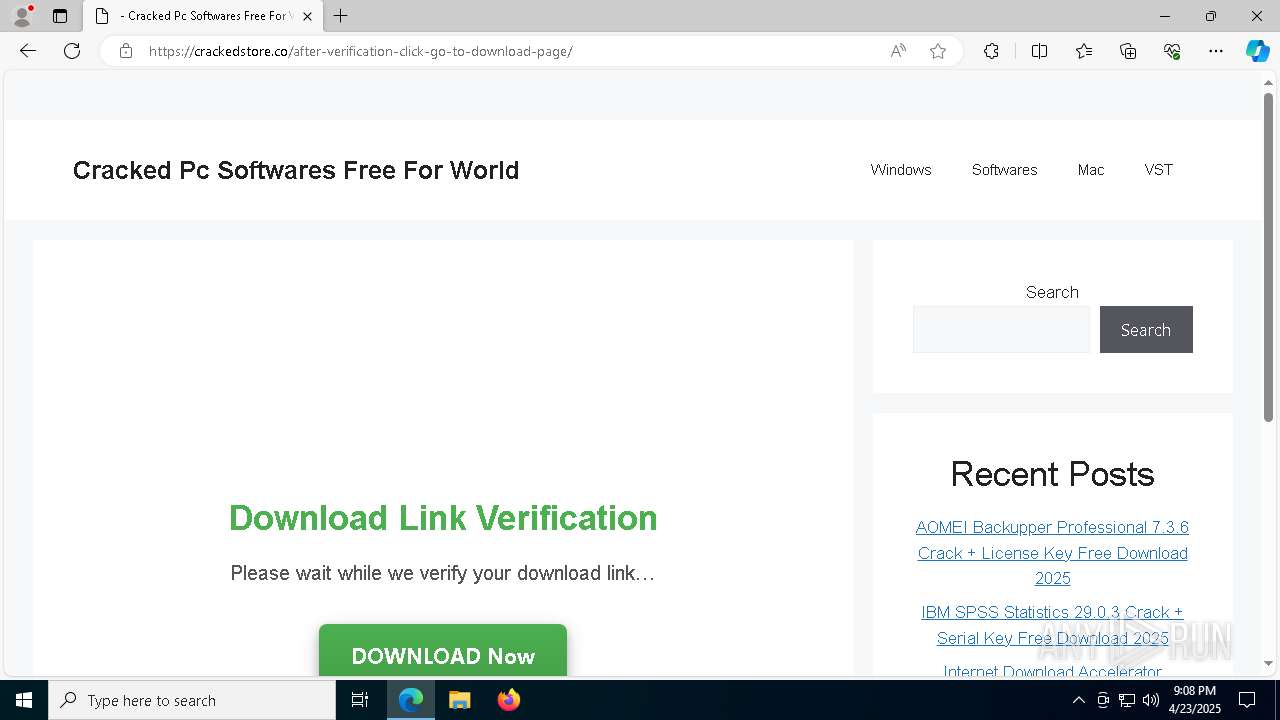
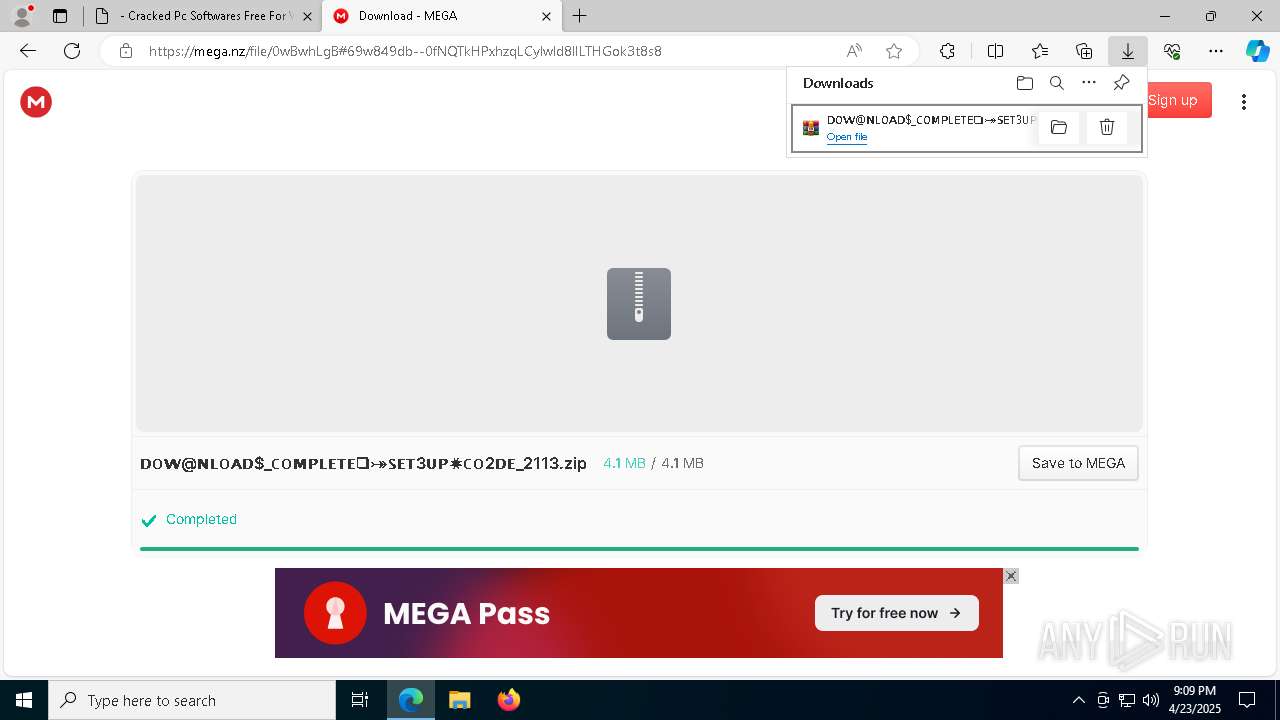
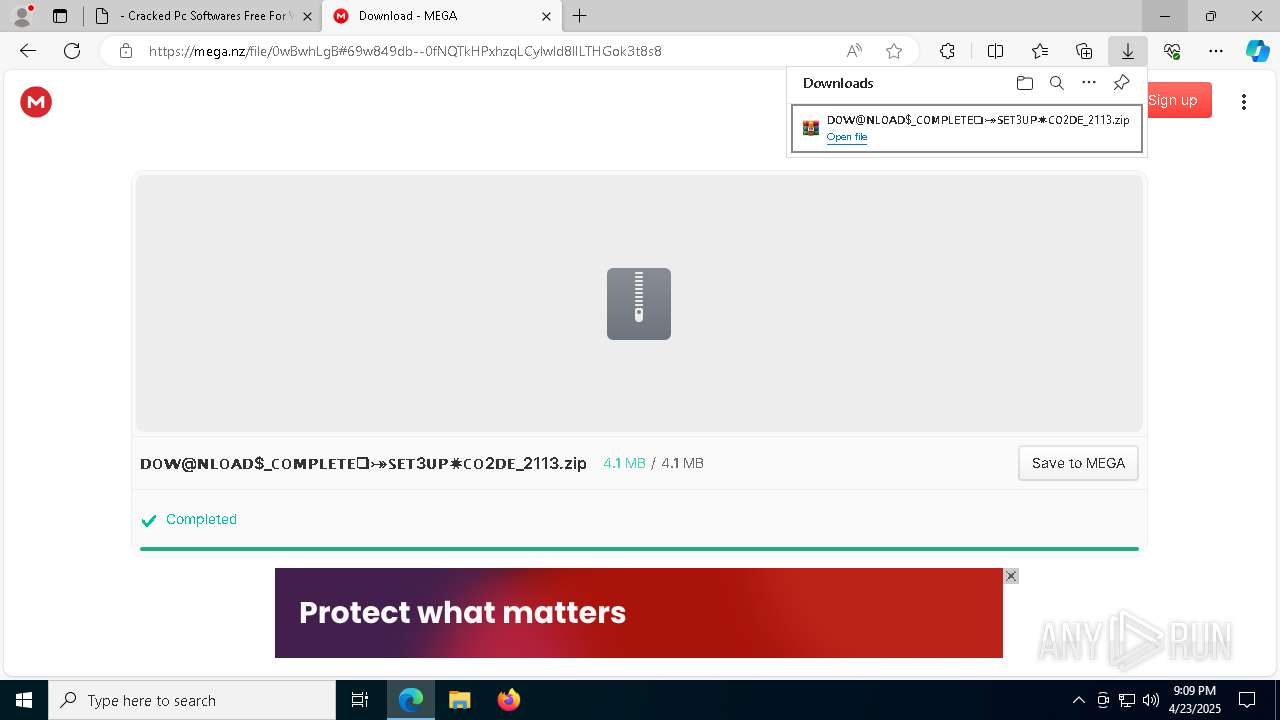
| URL: | https://www.slideshare.net/slideshow/latest-capcut-pro-2025-crack-version-for-pc-fully/276001741 |
| Full analysis: | https://app.any.run/tasks/aabc1f56-ba31-4427-9f4a-f8ee5764c644 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | April 23, 2025, 21:08:24 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | DDC24619F2EDE0A6B4CA5BB267421DE3 |
| SHA1: | 78FB73A28983B81DC79167626142F776E89DFA13 |
| SHA256: | F91BE5F7DE381488097E3DAF33D849B95A8EA8F786B9E874B98EF648F9343F32 |
| SSDEEP: | 3:N8DSL9A/EzOAAWCnadQOPbK8DKSccT/O:2OL9A79adbPVXE |
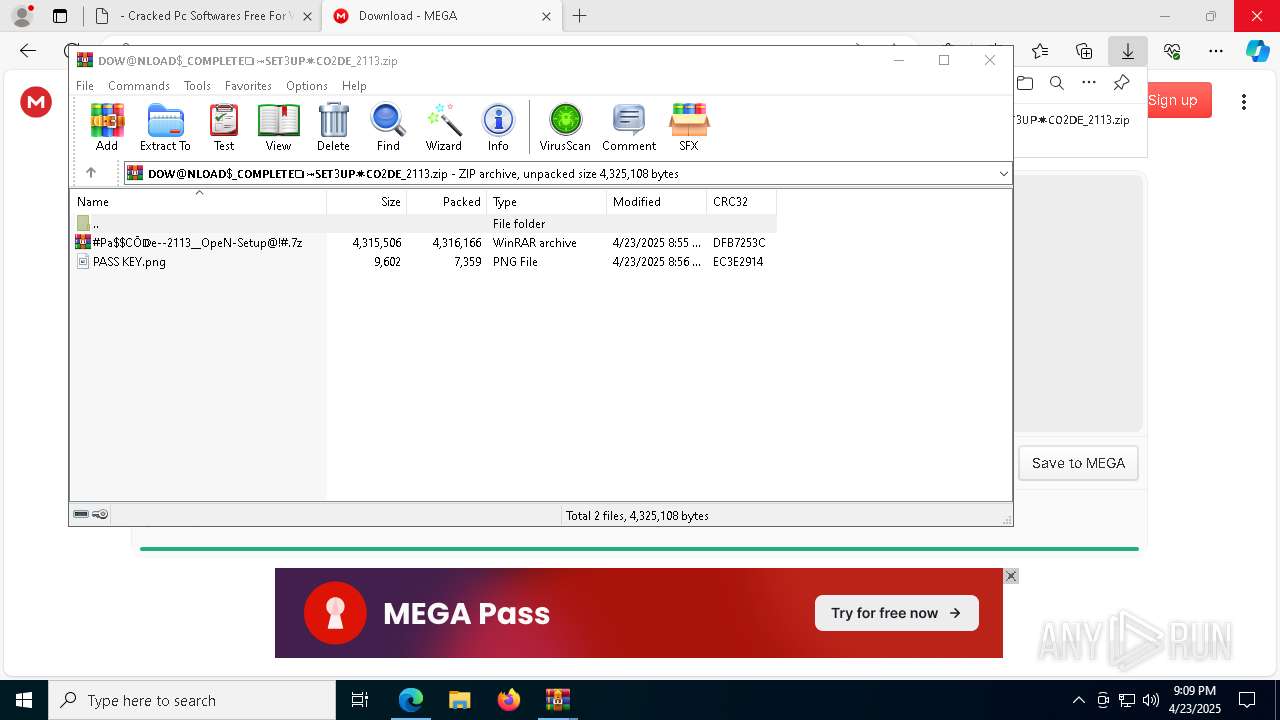
MALICIOUS
PHISHING has been detected (SURICATA)
- msedge.exe (PID: 7580)
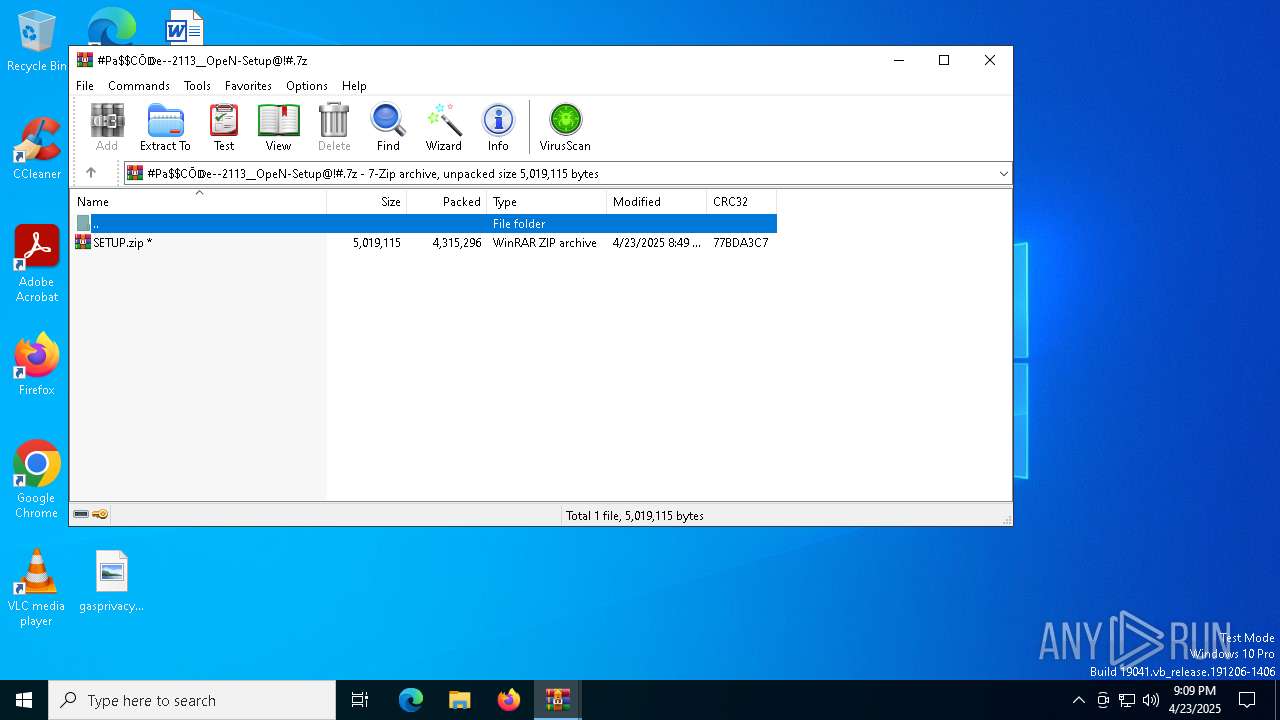
Executing a file with an untrusted certificate
- setup.exe (PID: 5680)
- 5RYIYM13DDNUP4HW4QVK3QMJARCV.exe (PID: 2616)
LUMMA mutex has been found
- setup.exe (PID: 5680)
Actions looks like stealing of personal data
- setup.exe (PID: 5680)
Changes the autorun value in the registry
- reg.exe (PID: 5136)
Steals credentials from Web Browsers
- setup.exe (PID: 5680)
SUSPICIOUS
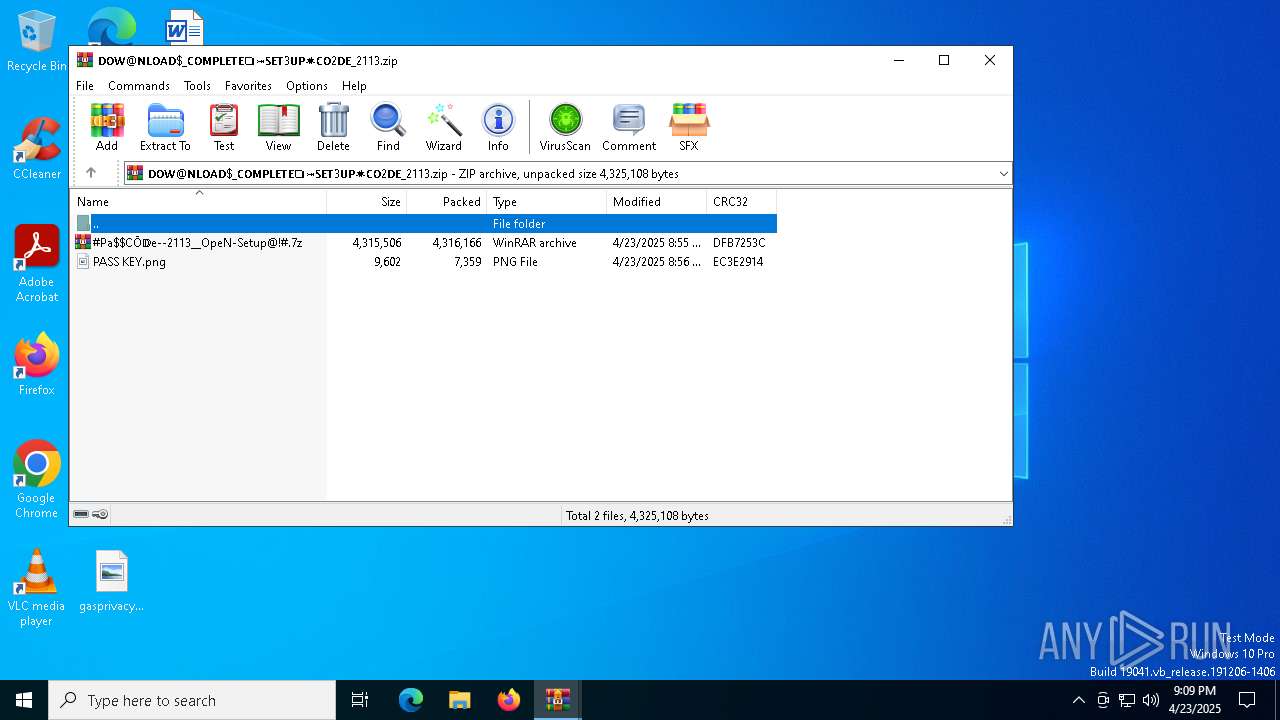
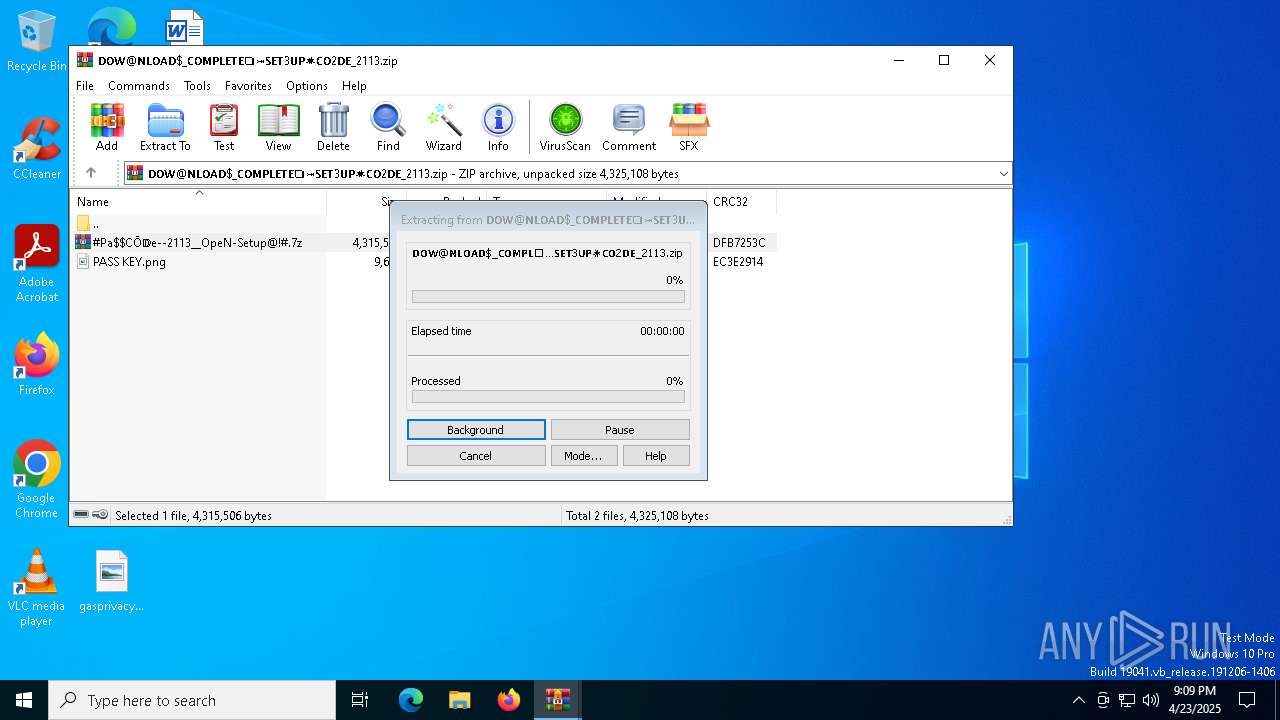
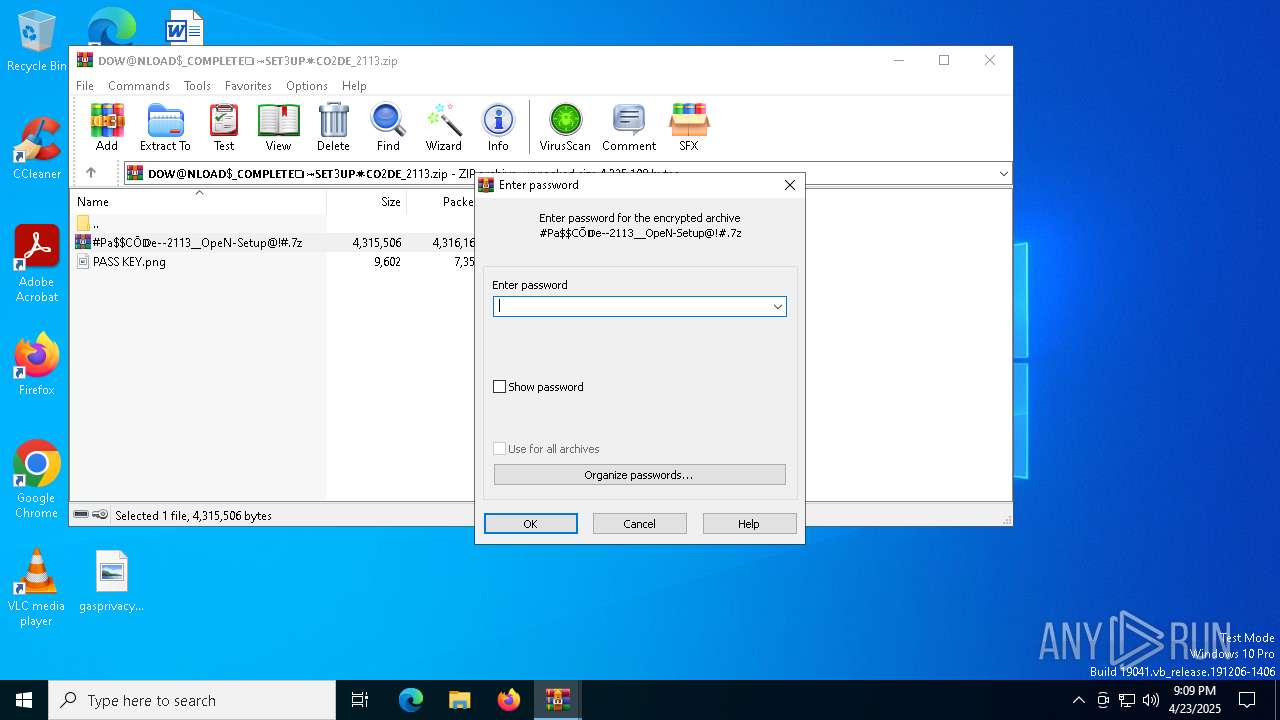
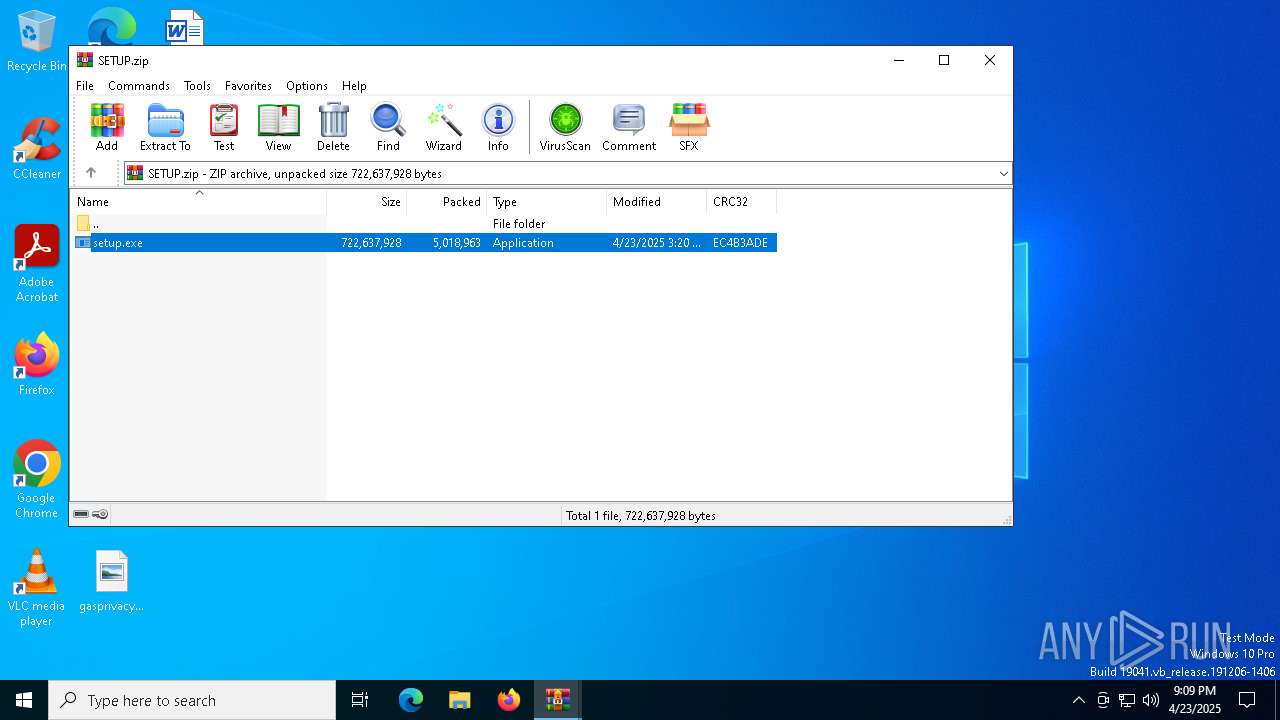
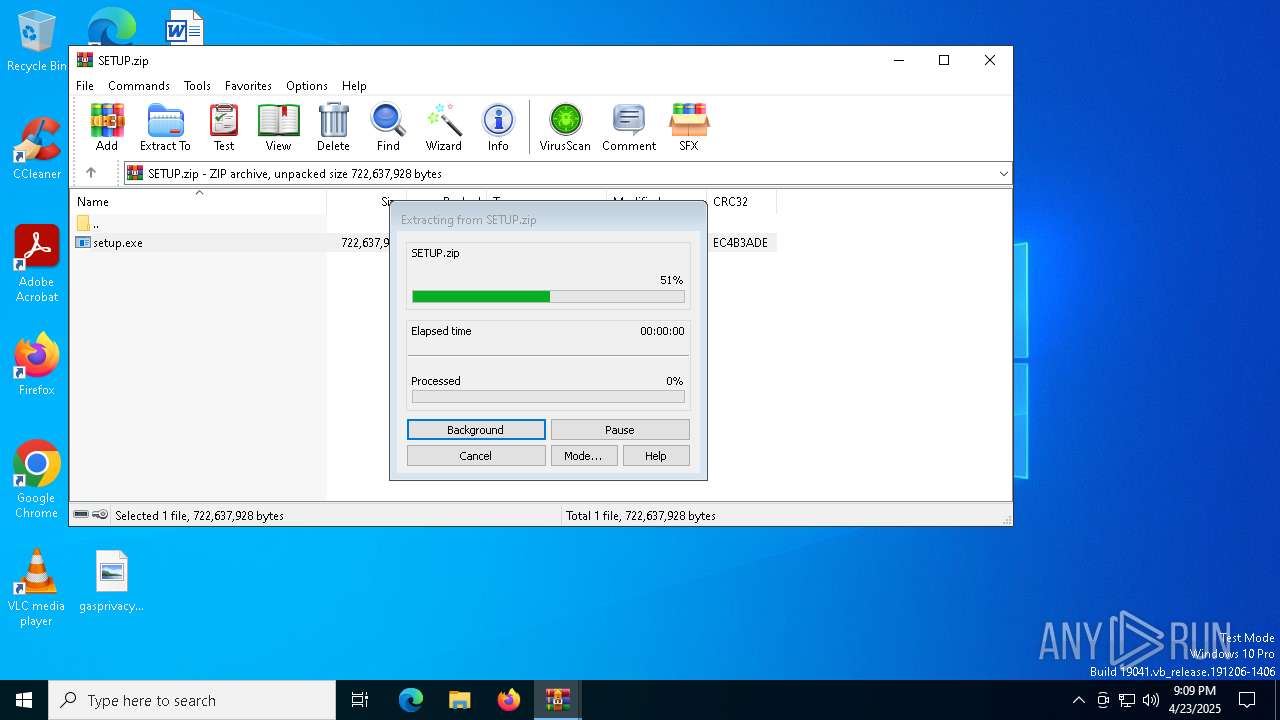
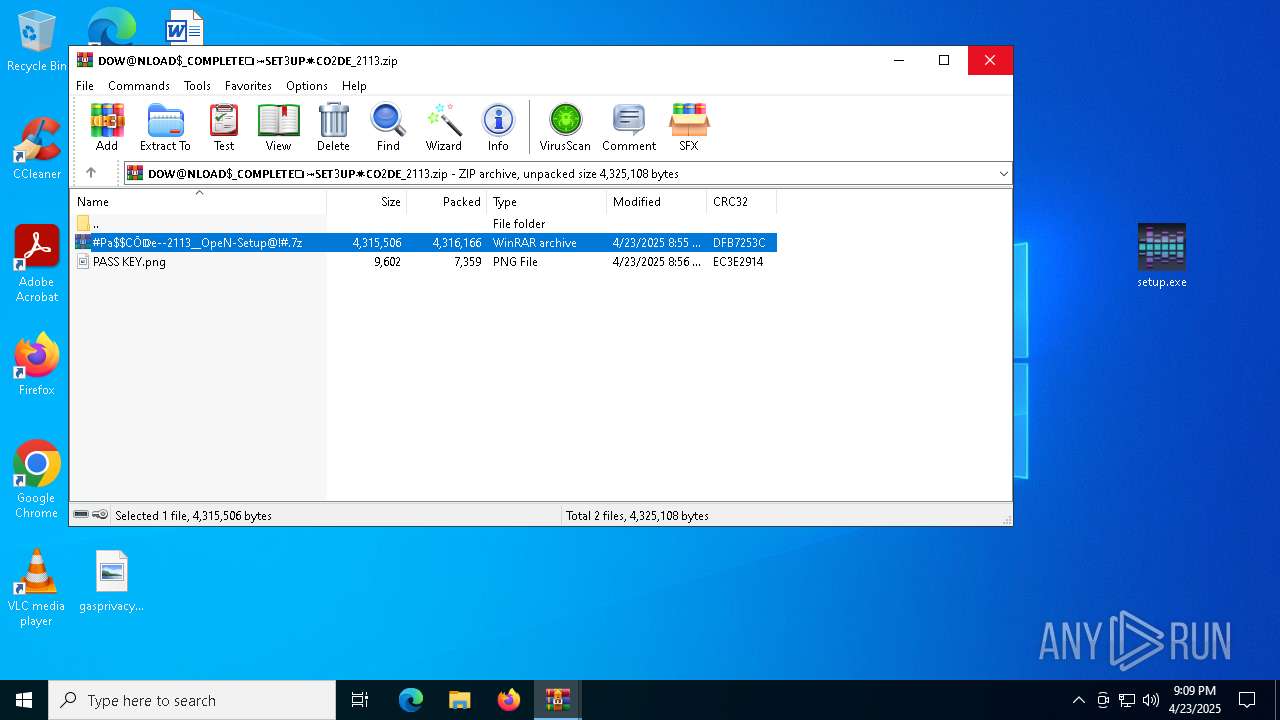
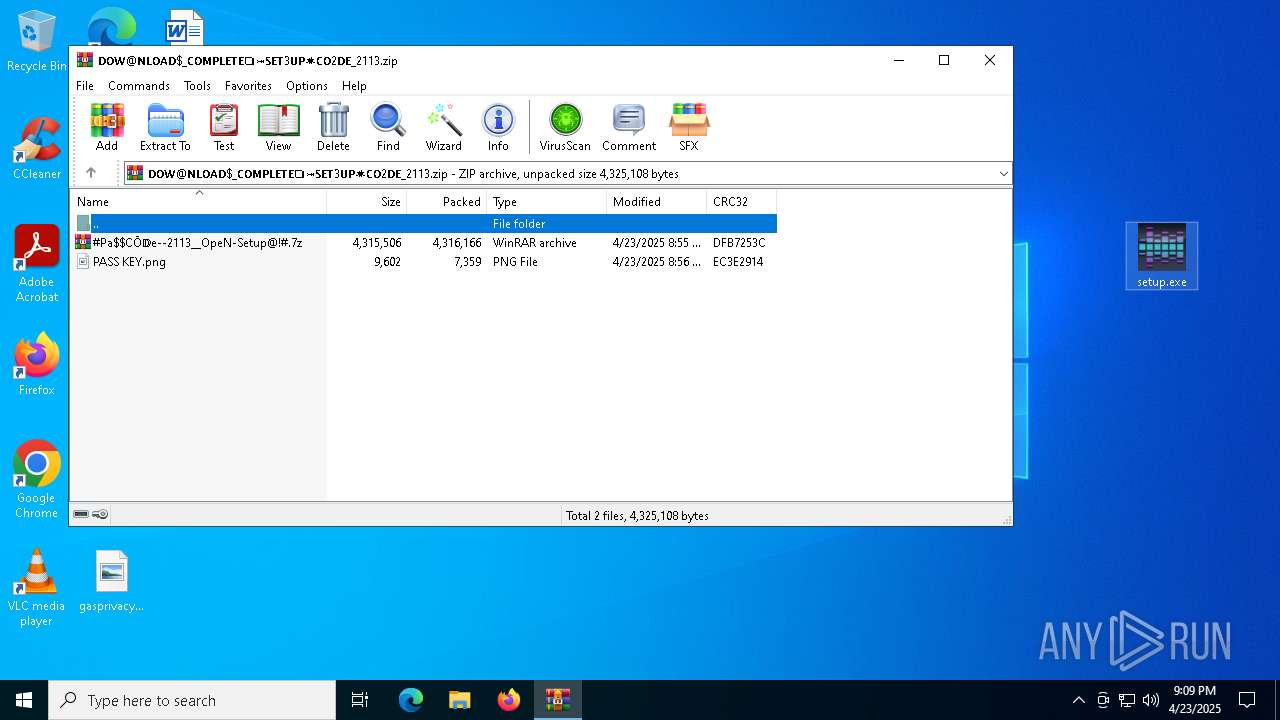
Application launched itself
- WinRAR.exe (PID: 8284)
- WinRAR.exe (PID: 9072)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 8284)
- WinRAR.exe (PID: 9072)
There is functionality for VM detection antiVM strings (YARA)
- setup.exe (PID: 5680)
Starts CMD.EXE for commands execution
- 5RYIYM13DDNUP4HW4QVK3QMJARCV.exe (PID: 2616)
Searches for installed software
- setup.exe (PID: 5680)
Executable content was dropped or overwritten
- setup.exe (PID: 5680)
- 5RYIYM13DDNUP4HW4QVK3QMJARCV.exe (PID: 2616)
There is functionality for taking screenshot (YARA)
- 5RYIYM13DDNUP4HW4QVK3QMJARCV.exe (PID: 2616)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 7052)
Connects to unusual port
- 5RYIYM13DDNUP4HW4QVK3QMJARCV.exe (PID: 2616)
INFO
Reads the computer name
- identity_helper.exe (PID: 1660)
- identity_helper.exe (PID: 9132)
- 5RYIYM13DDNUP4HW4QVK3QMJARCV.exe (PID: 2616)
- setup.exe (PID: 5680)
Reads Environment values
- identity_helper.exe (PID: 1660)
- identity_helper.exe (PID: 9132)
Application launched itself
- msedge.exe (PID: 7340)
- msedge.exe (PID: 8524)
Checks supported languages
- identity_helper.exe (PID: 1660)
- identity_helper.exe (PID: 9132)
- setup.exe (PID: 5680)
- 5RYIYM13DDNUP4HW4QVK3QMJARCV.exe (PID: 2616)
Reads Microsoft Office registry keys
- msedge.exe (PID: 7340)
Reads the software policy settings
- slui.exe (PID: 8144)
- setup.exe (PID: 5680)
- 5RYIYM13DDNUP4HW4QVK3QMJARCV.exe (PID: 2616)
- slui.exe (PID: 4920)
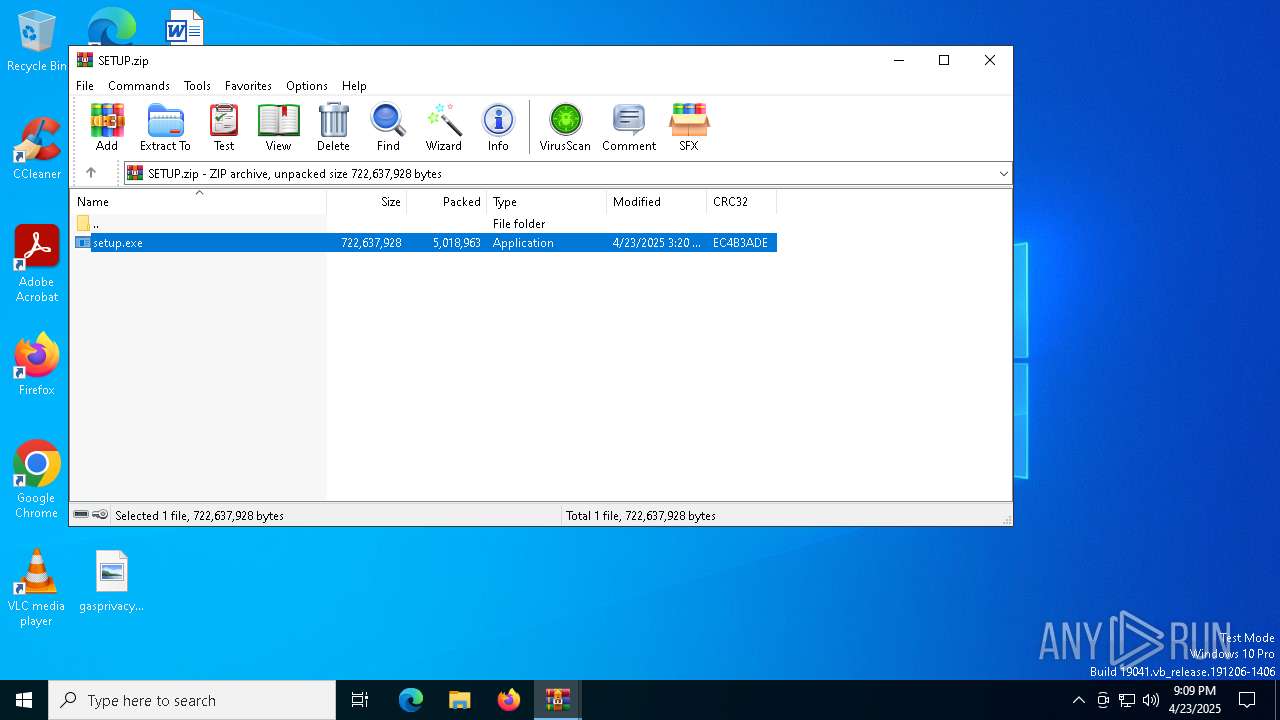
Manual execution by a user
- setup.exe (PID: 5680)
Compiled with Borland Delphi (YARA)
- 5RYIYM13DDNUP4HW4QVK3QMJARCV.exe (PID: 2616)
The sample compiled with english language support
- setup.exe (PID: 5680)
- 5RYIYM13DDNUP4HW4QVK3QMJARCV.exe (PID: 2616)
Create files in a temporary directory
- setup.exe (PID: 5680)
Creates files in the program directory
- 5RYIYM13DDNUP4HW4QVK3QMJARCV.exe (PID: 2616)
Drops encrypted JS script (Microsoft Script Encoder)
- 5RYIYM13DDNUP4HW4QVK3QMJARCV.exe (PID: 2616)
Checks proxy server information
- slui.exe (PID: 4920)
Reads the machine GUID from the registry
- 5RYIYM13DDNUP4HW4QVK3QMJARCV.exe (PID: 2616)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
228
Monitored processes
91
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 668 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5764 --field-trial-handle=2396,i,5658225951746871912,569744655510921117,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 728 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5256 --field-trial-handle=2424,i,10695800079951640387,126782153170539802,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 812 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5756 --field-trial-handle=2396,i,5658225951746871912,569744655510921117,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1052 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=19 --mojo-platform-channel-handle=6032 --field-trial-handle=2396,i,5658225951746871912,569744655510921117,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1072 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=1724 --field-trial-handle=2424,i,10695800079951640387,126782153170539802,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1660 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6292 --field-trial-handle=2396,i,5658225951746871912,569744655510921117,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1672 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=23 --mojo-platform-channel-handle=5716 --field-trial-handle=2396,i,5658225951746871912,569744655510921117,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1852 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2420 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4708 --field-trial-handle=2424,i,10695800079951640387,126782153170539802,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2564 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.slideshare.net/slideshow/latest-capcut-pro-2025-crack-version-for-pc-fully/276001741" | C:\Program Files\Internet Explorer\iexplore.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
20 808
Read events
20 660
Write events
130
Delete events
18
Modification events
| (PID) Process: | (2564) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2564) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2564) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2564) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2564) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2564) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (7340) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7340) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7340) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7340) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
26
Suspicious files
538
Text files
196
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10becd.TMP | — | |
MD5:— | SHA256:— | |||
| 7340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10bebe.TMP | — | |
MD5:— | SHA256:— | |||
| 7340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10becd.TMP | — | |
MD5:— | SHA256:— | |||
| 7340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10beed.TMP | — | |
MD5:— | SHA256:— | |||
| 7340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10bf5a.TMP | — | |
MD5:— | SHA256:— | |||
| 7340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
37
TCP/UDP connections
188
DNS requests
205
Threats
26
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7360 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7360 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6576 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1745626152&P2=404&P3=2&P4=me%2f%2bfnhZTw12y%2boQY1%2f2uueMXt4QKCMKd6UR4Q9jx7XOxTE%2fvEnp66ydkHQL3AdbZVeEShM%2bR94BoTwIS5ET3g%3d%3d | unknown | — | — | whitelisted |
6576 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1745626152&P2=404&P3=2&P4=me%2f%2bfnhZTw12y%2boQY1%2f2uueMXt4QKCMKd6UR4Q9jx7XOxTE%2fvEnp66ydkHQL3AdbZVeEShM%2bR94BoTwIS5ET3g%3d%3d | unknown | — | — | whitelisted |
6576 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1745626152&P2=404&P3=2&P4=me%2f%2bfnhZTw12y%2boQY1%2f2uueMXt4QKCMKd6UR4Q9jx7XOxTE%2fvEnp66ydkHQL3AdbZVeEShM%2bR94BoTwIS5ET3g%3d%3d | unknown | — | — | whitelisted |
6576 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1745626152&P2=404&P3=2&P4=me%2f%2bfnhZTw12y%2boQY1%2f2uueMXt4QKCMKd6UR4Q9jx7XOxTE%2fvEnp66ydkHQL3AdbZVeEShM%2bR94BoTwIS5ET3g%3d%3d | unknown | — | — | whitelisted |
6576 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1745626152&P2=404&P3=2&P4=me%2f%2bfnhZTw12y%2boQY1%2f2uueMXt4QKCMKd6UR4Q9jx7XOxTE%2fvEnp66ydkHQL3AdbZVeEShM%2bR94BoTwIS5ET3g%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4424 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
7340 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7580 | msedge.exe | 104.18.20.206:443 | a.pub.network | — | — | whitelisted |
7580 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7580 | msedge.exe | 151.101.130.152:443 | www.slideshare.net | — | — | whitelisted |
7580 | msedge.exe | 142.250.181.232:443 | www.googletagmanager.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.slideshare.net |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7580 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7580 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
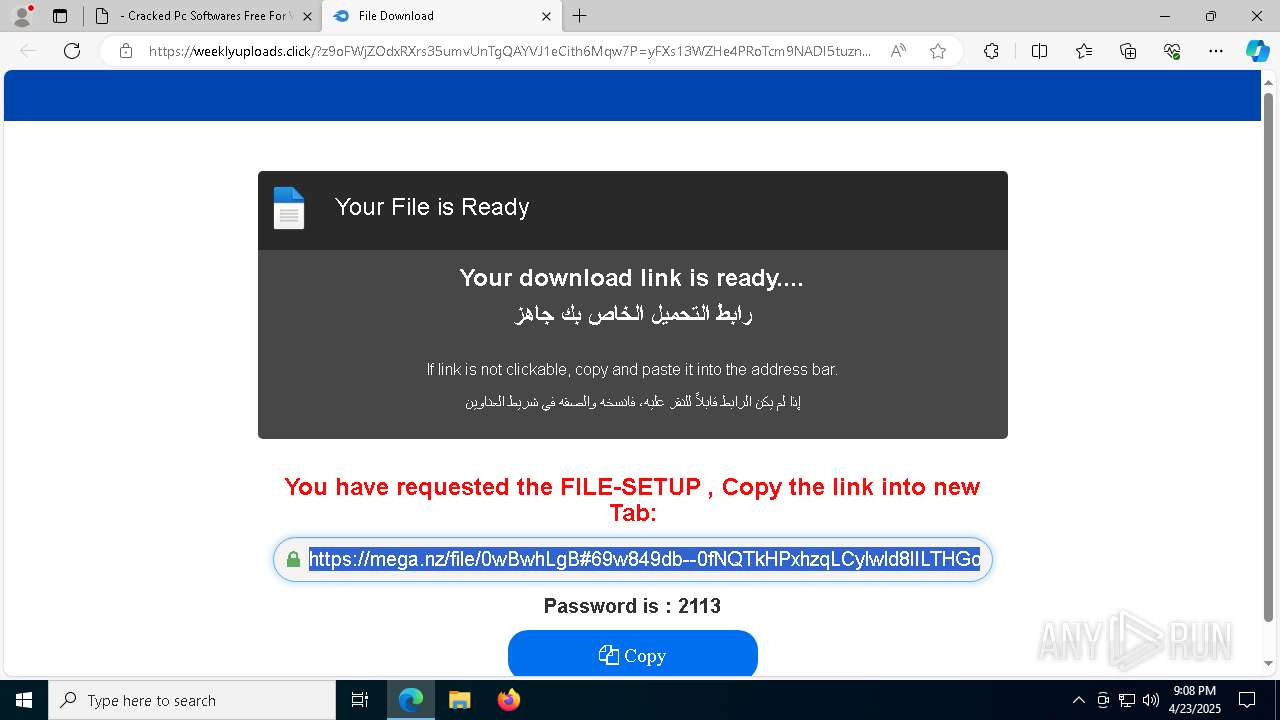
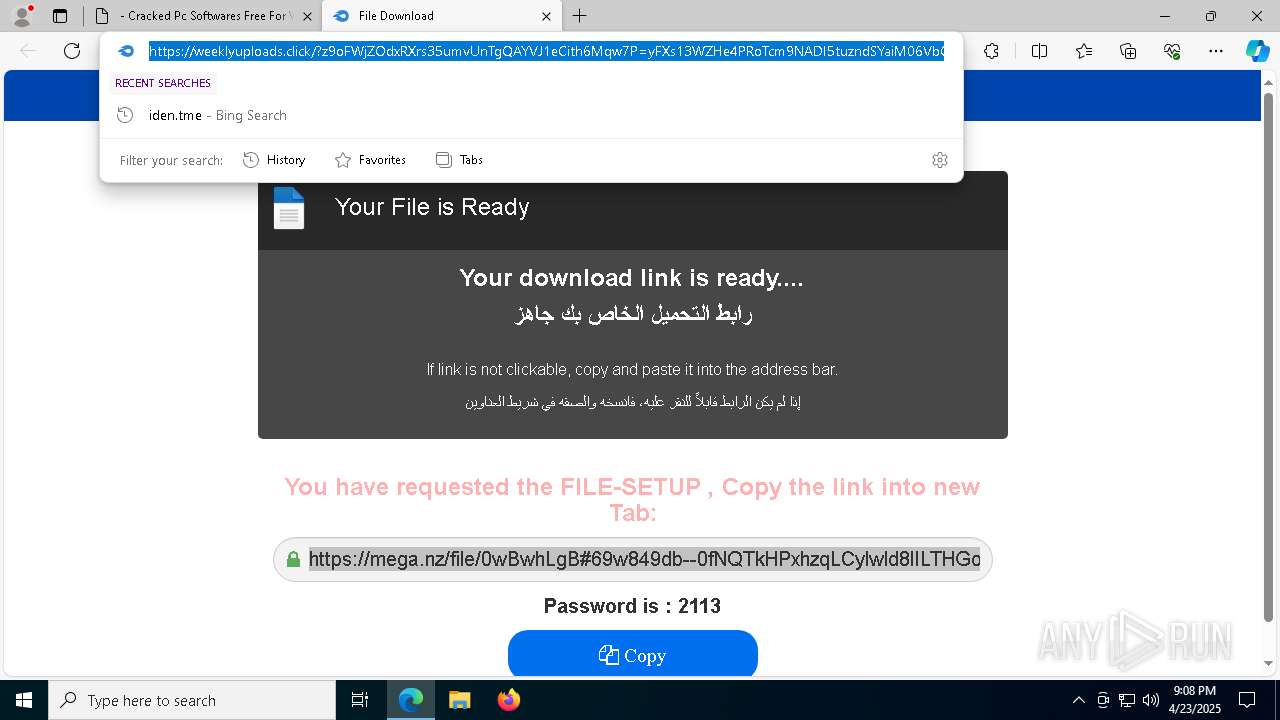
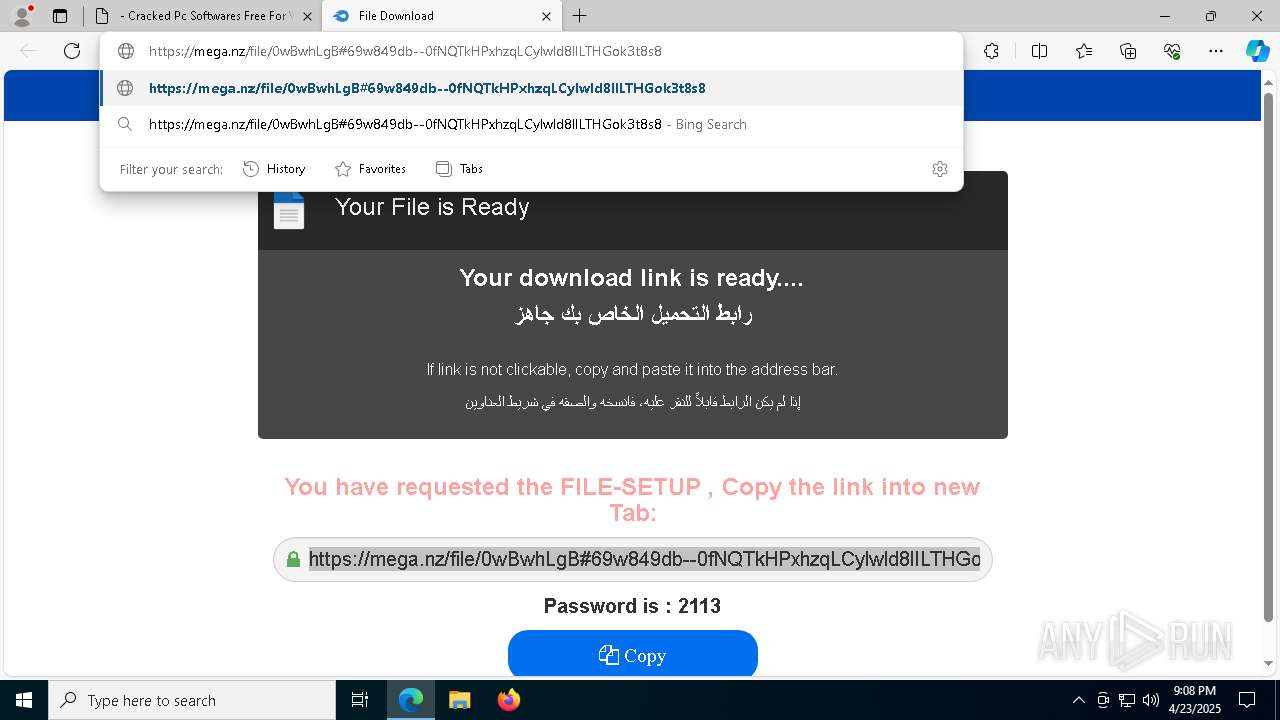
7580 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing domain by CrossDomain (weeklyuploads .click) |
7580 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing domain by CrossDomain (weeklyuploads .click) |
7580 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing domain by CrossDomain (weeklyuploads .click) |
7580 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing domain by CrossDomain (weeklyuploads .click) |
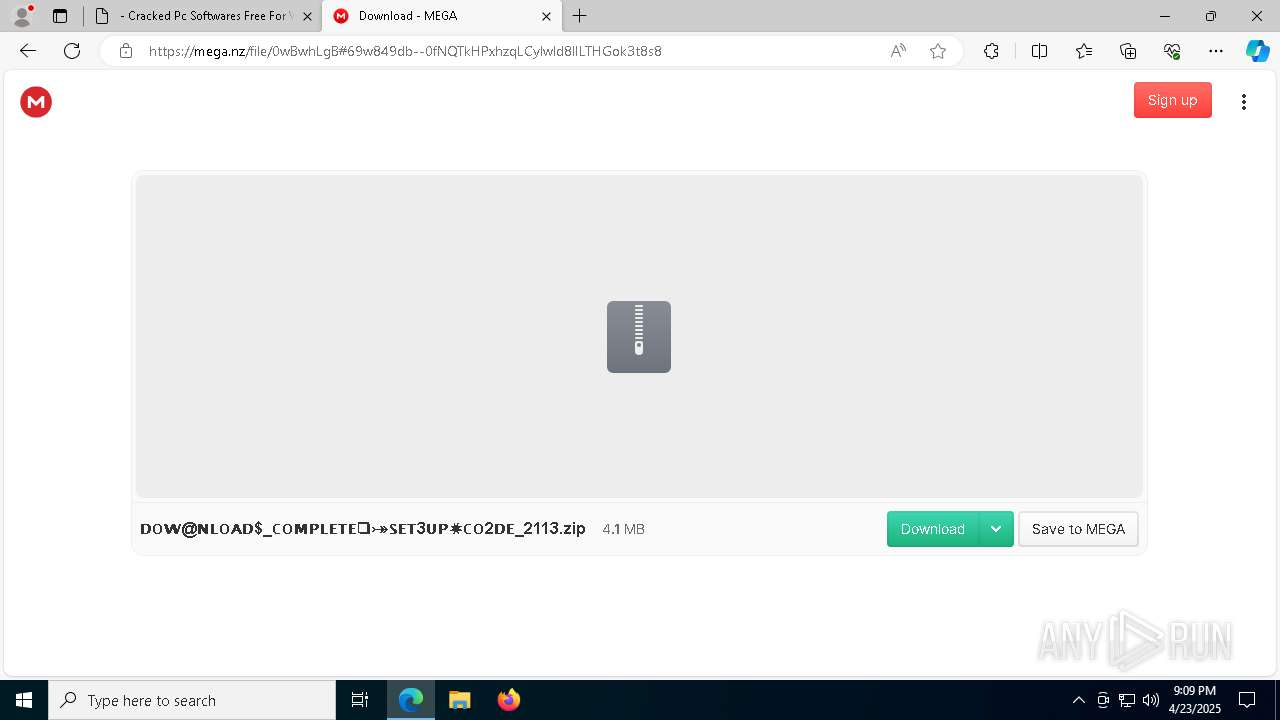
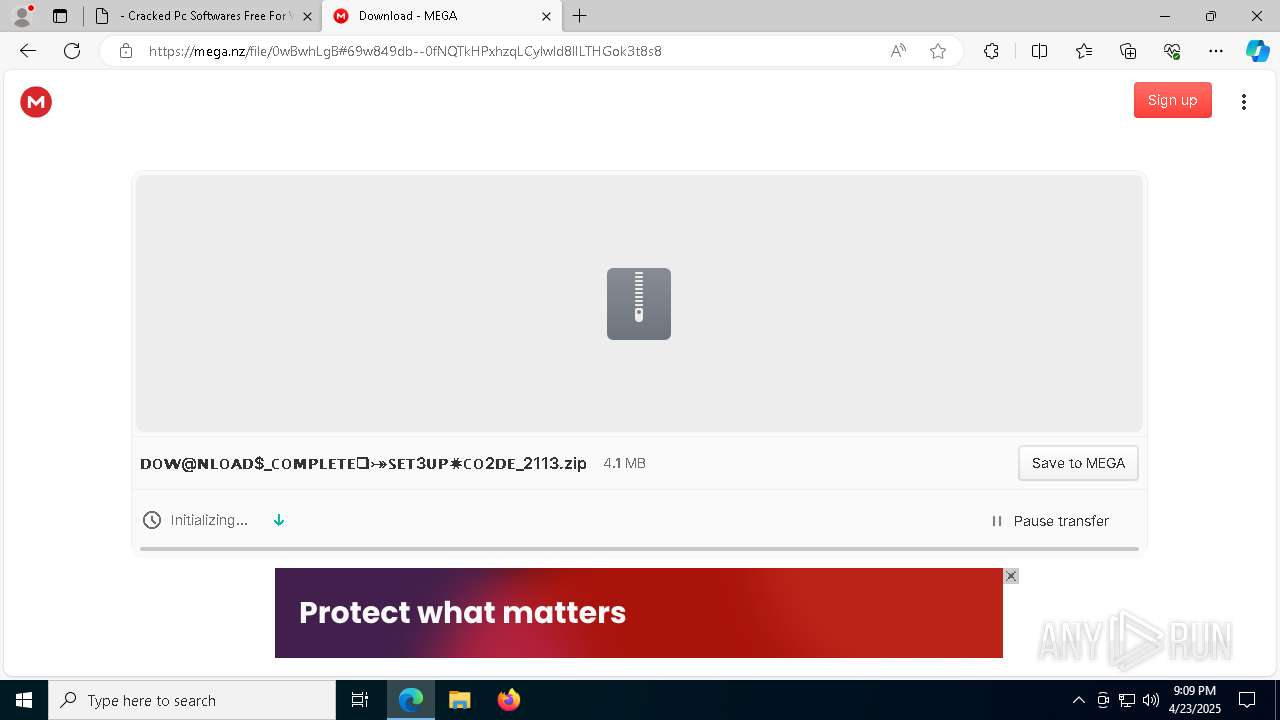
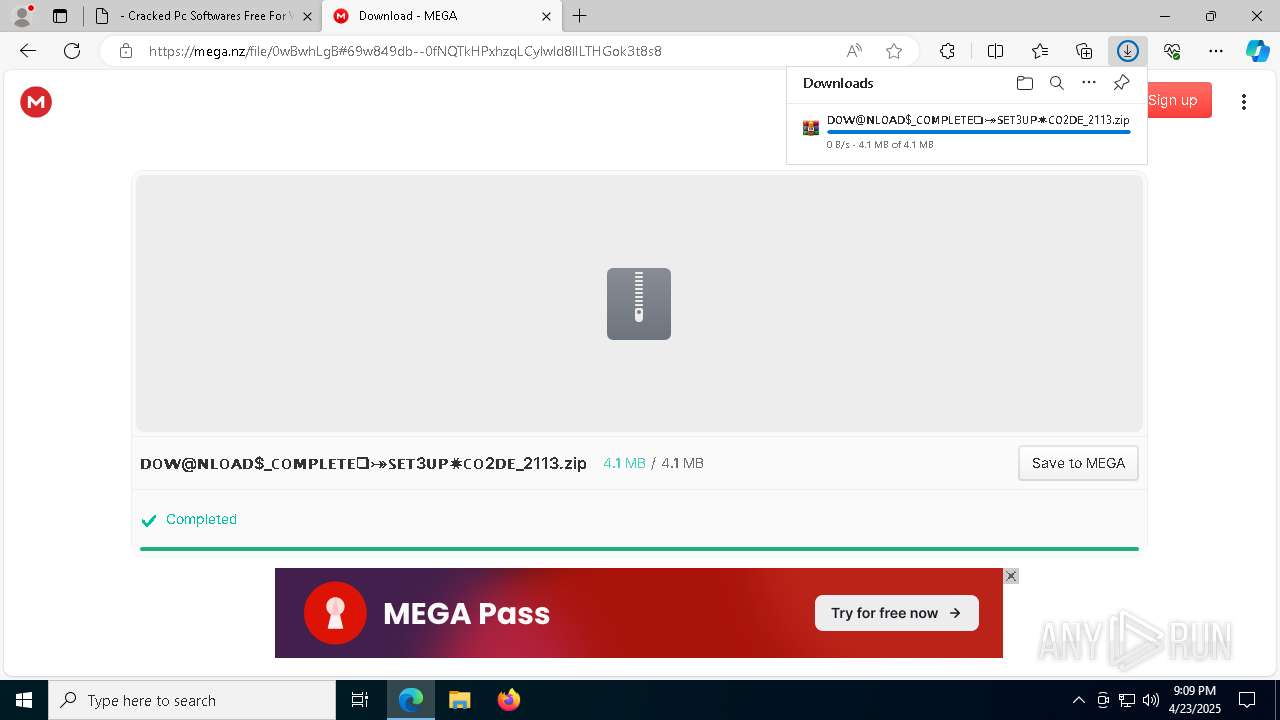
7580 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
7580 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
7580 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
7580 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |