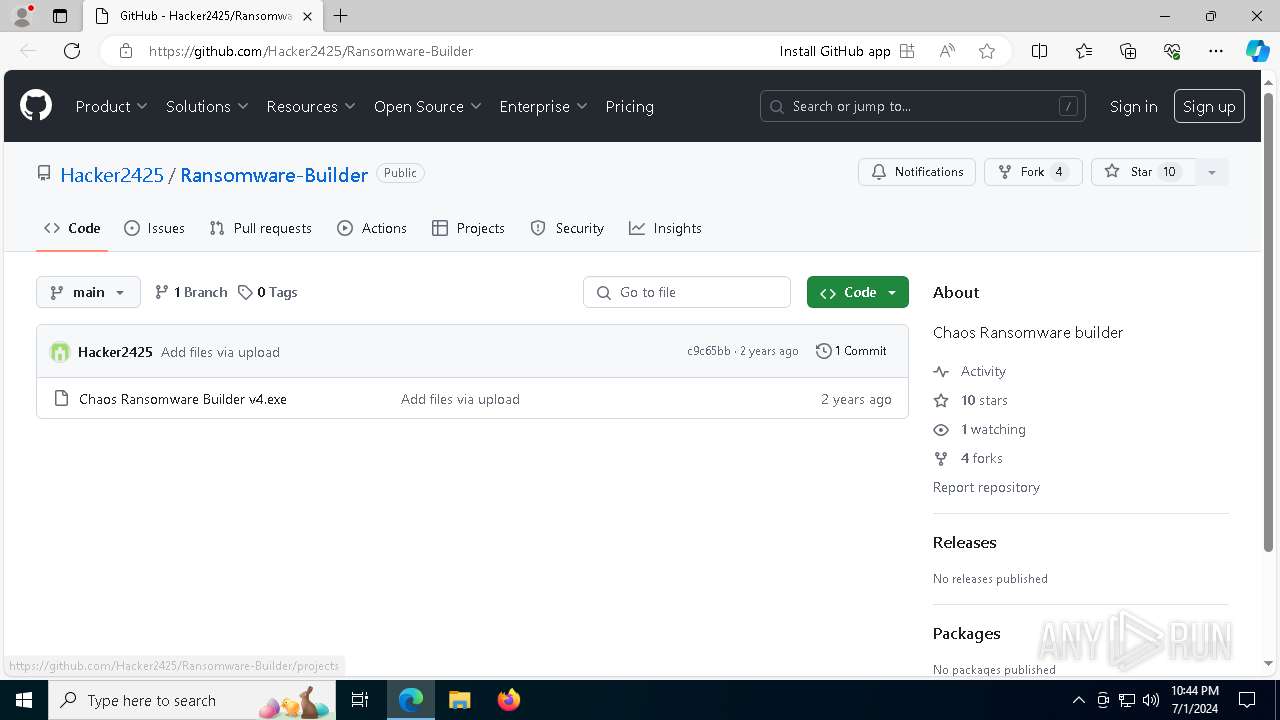
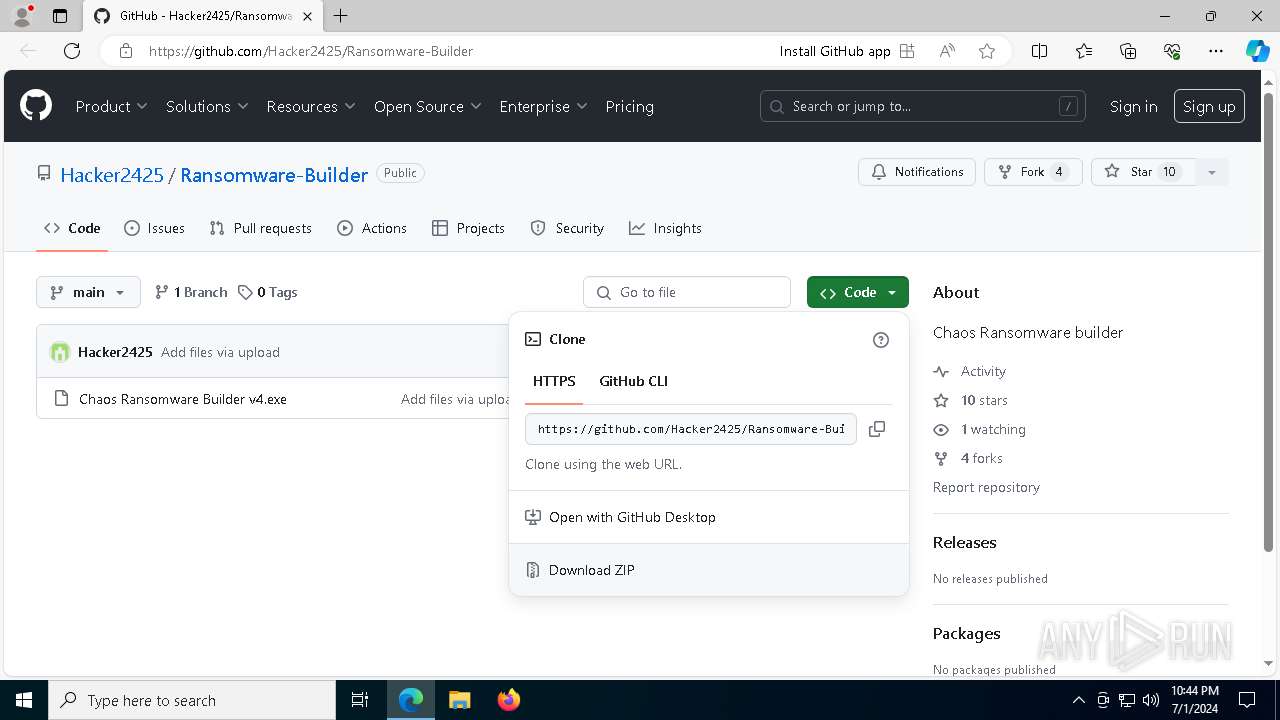
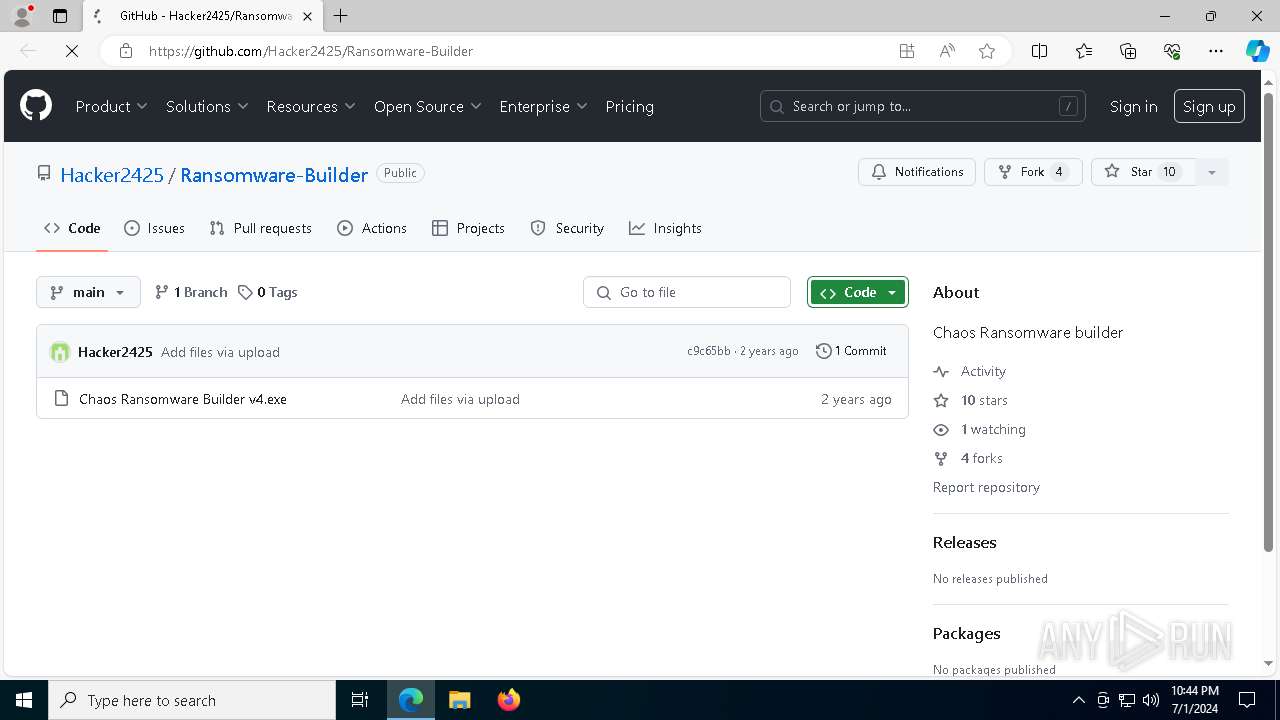
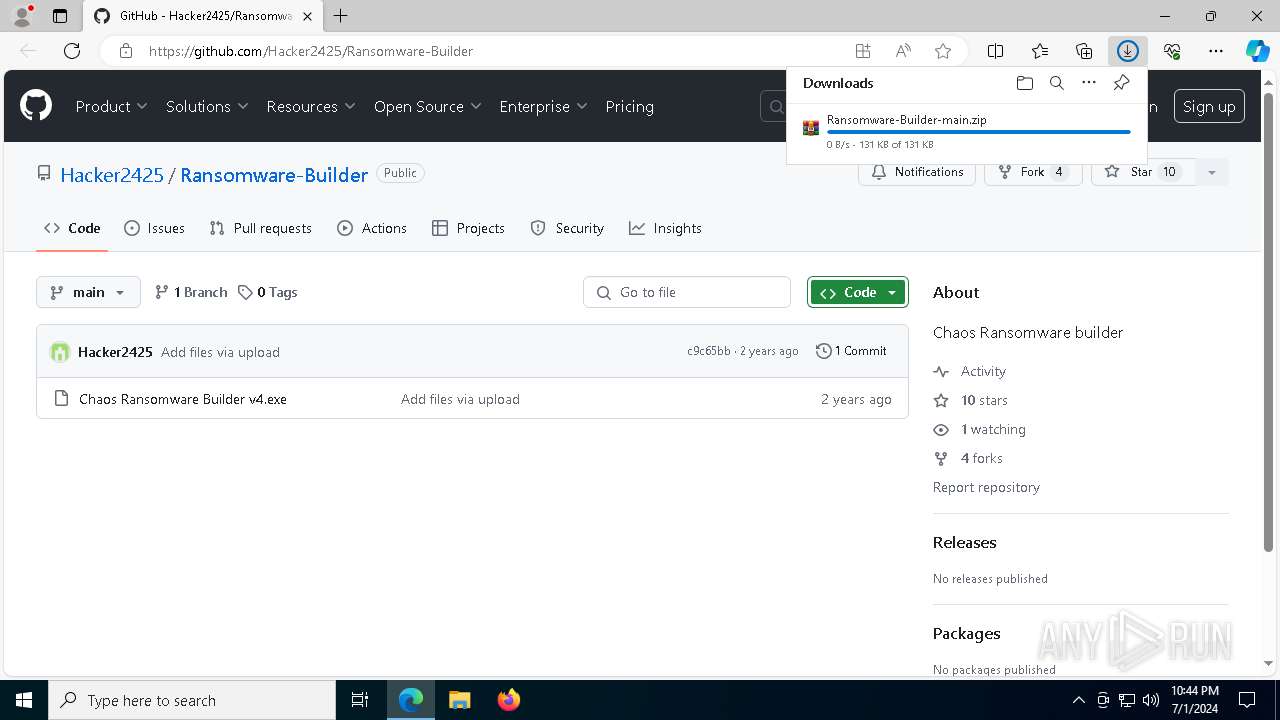
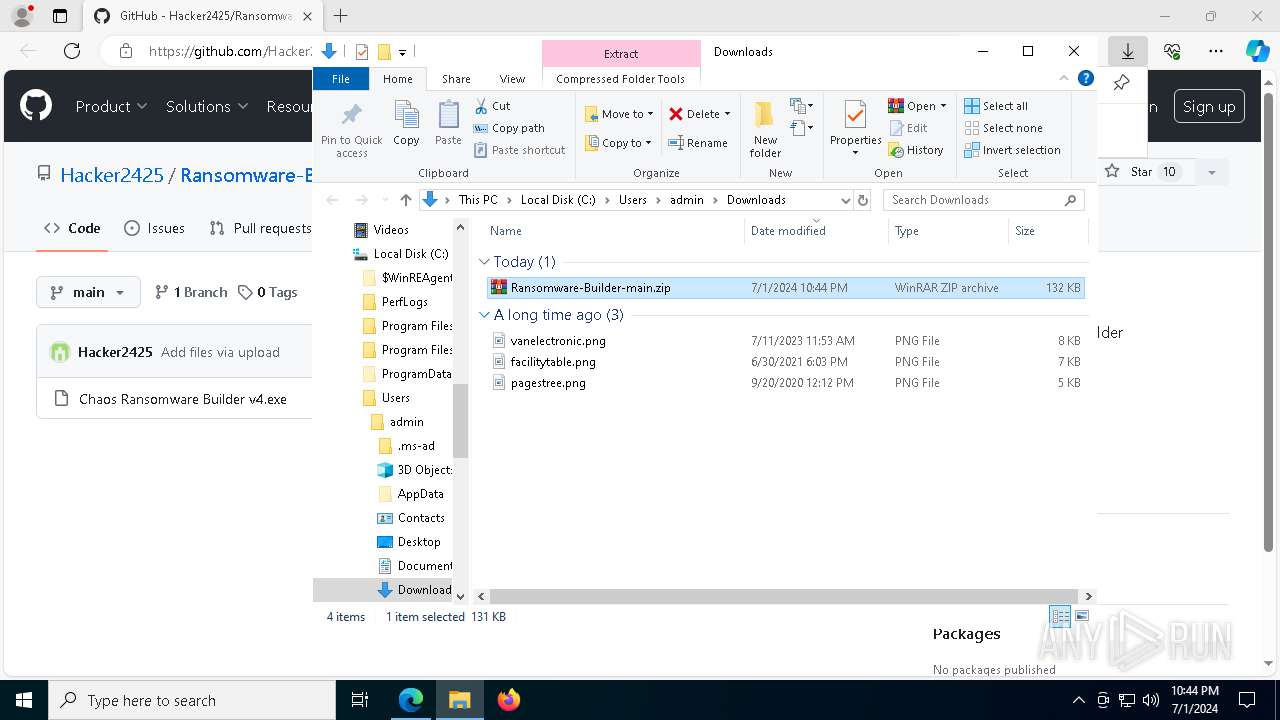
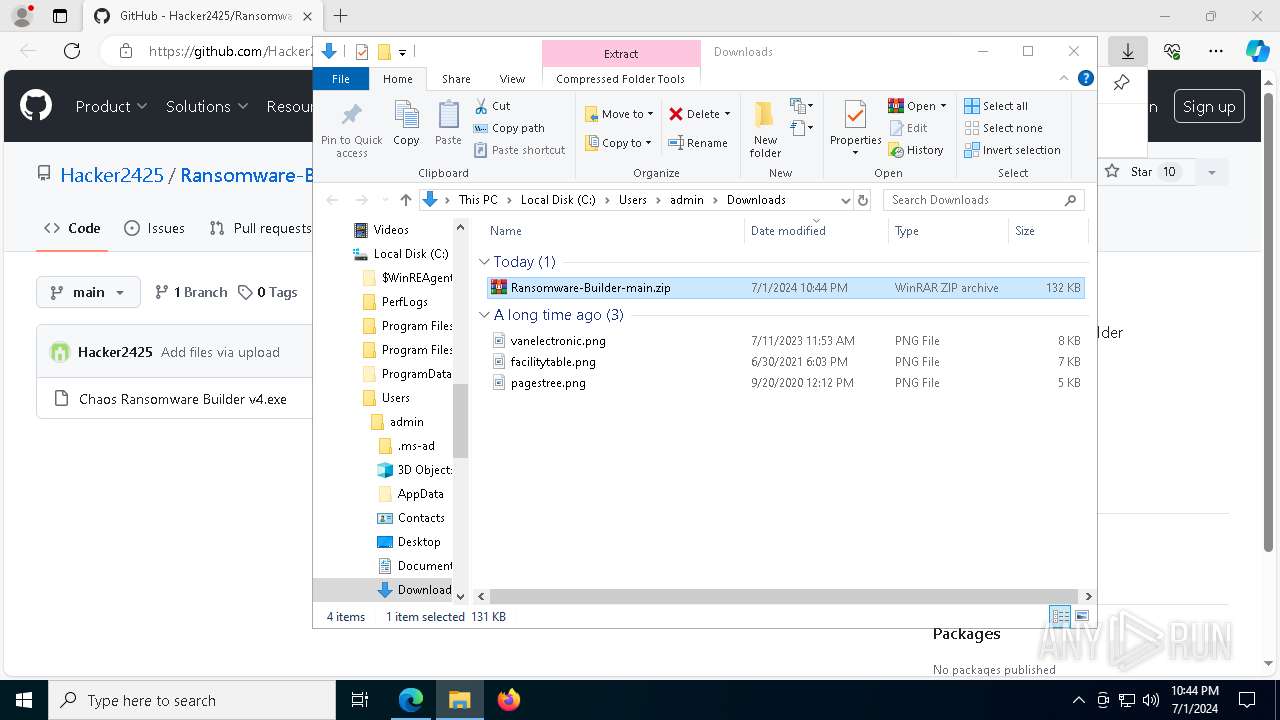
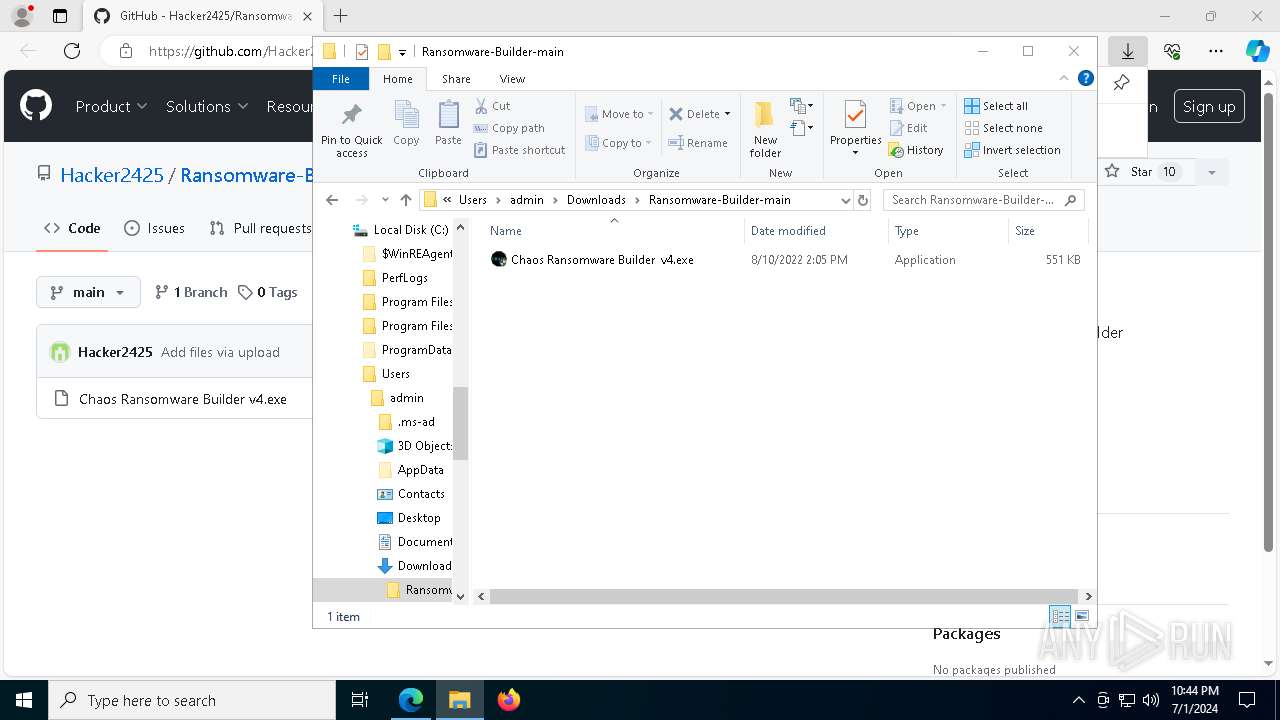
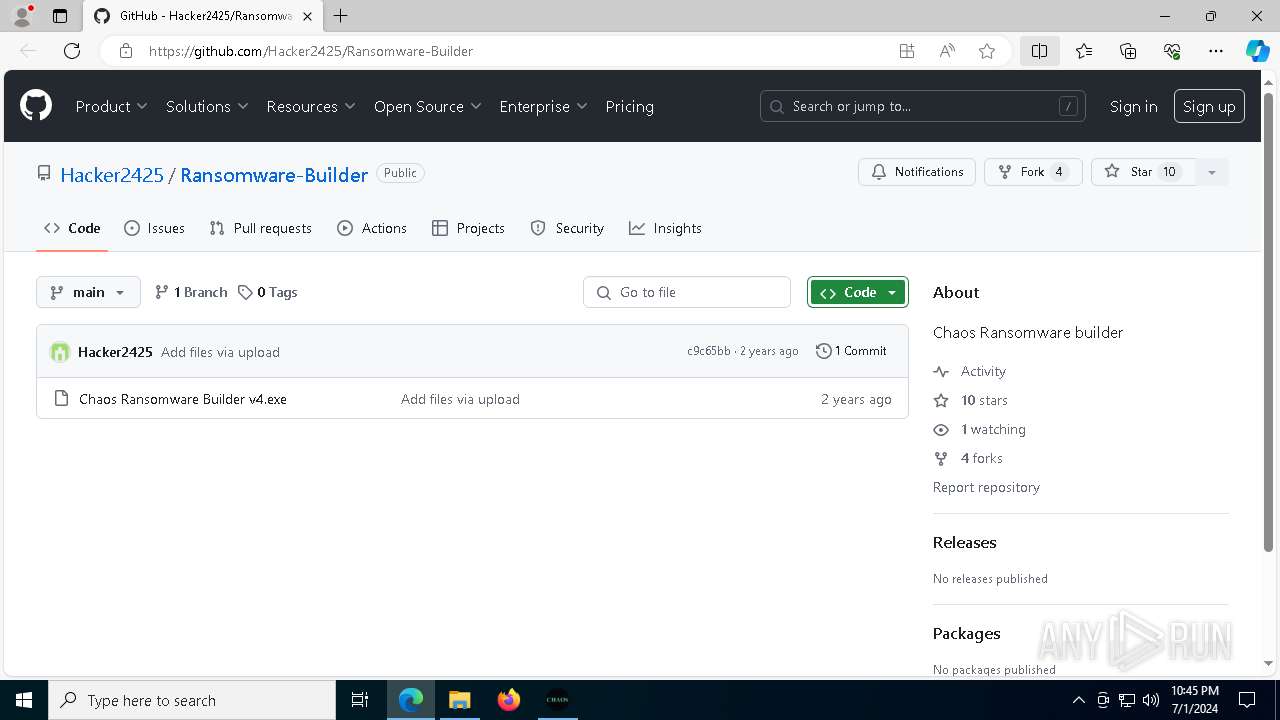
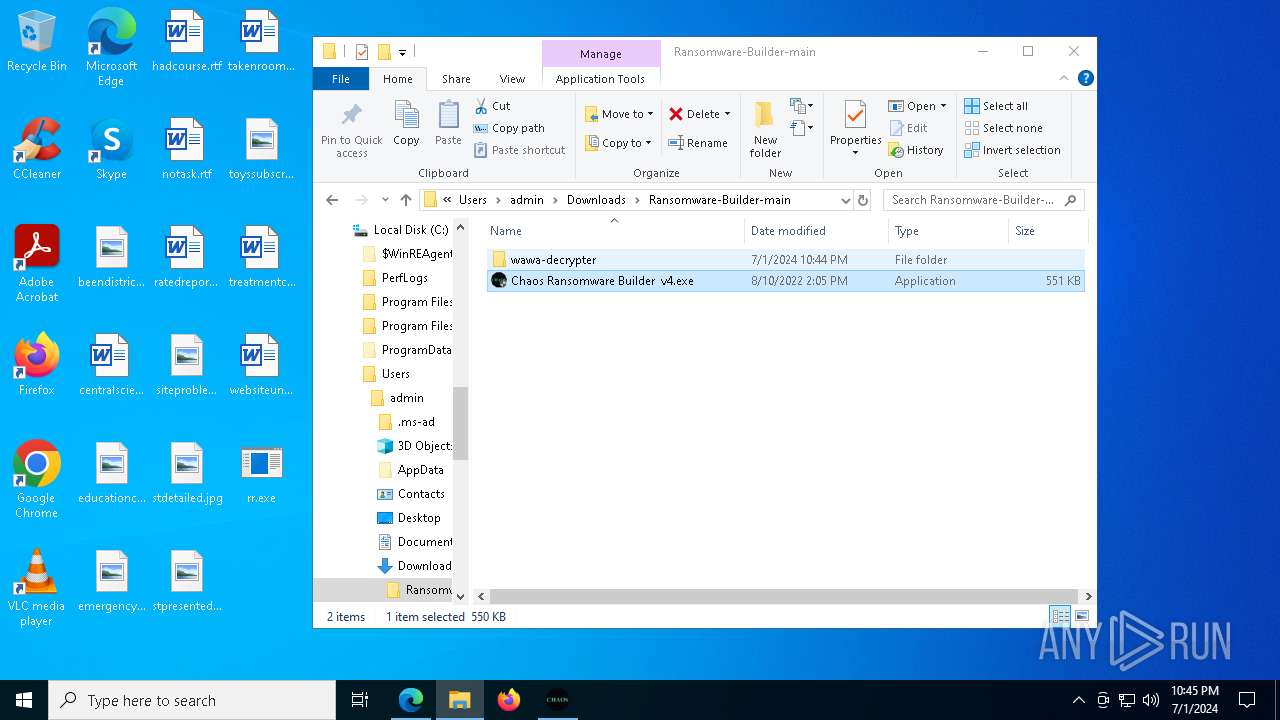
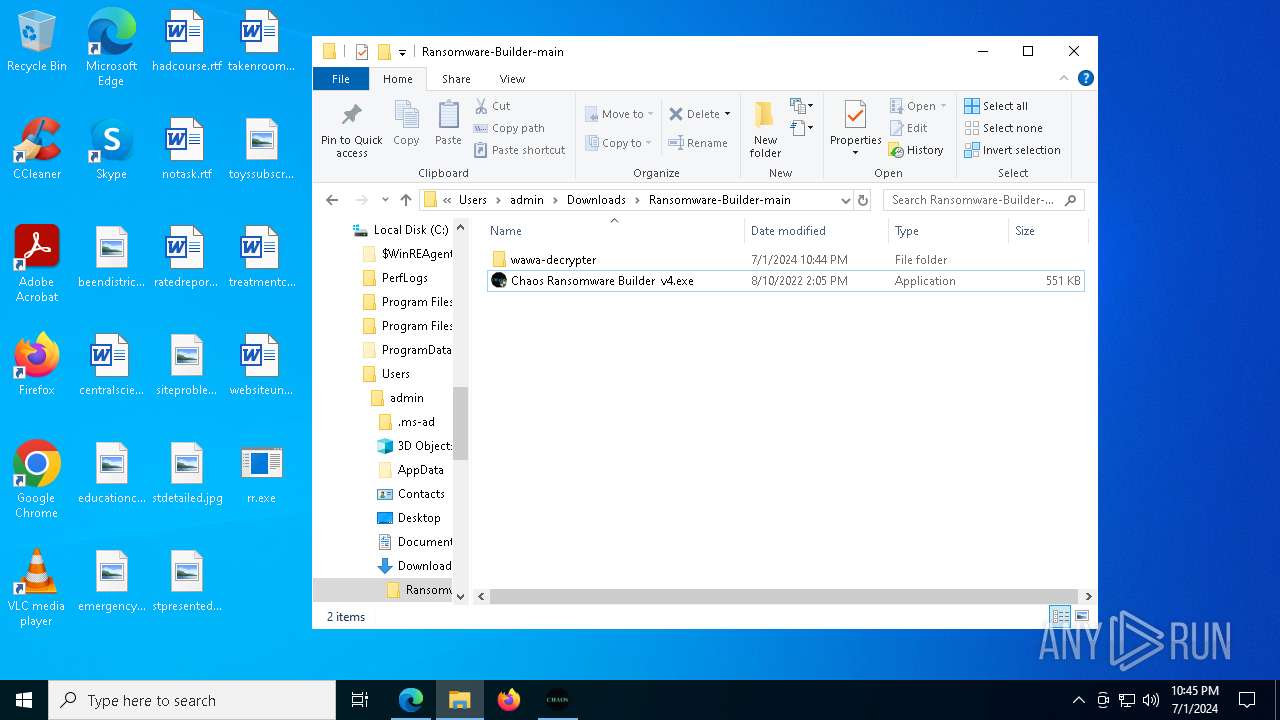
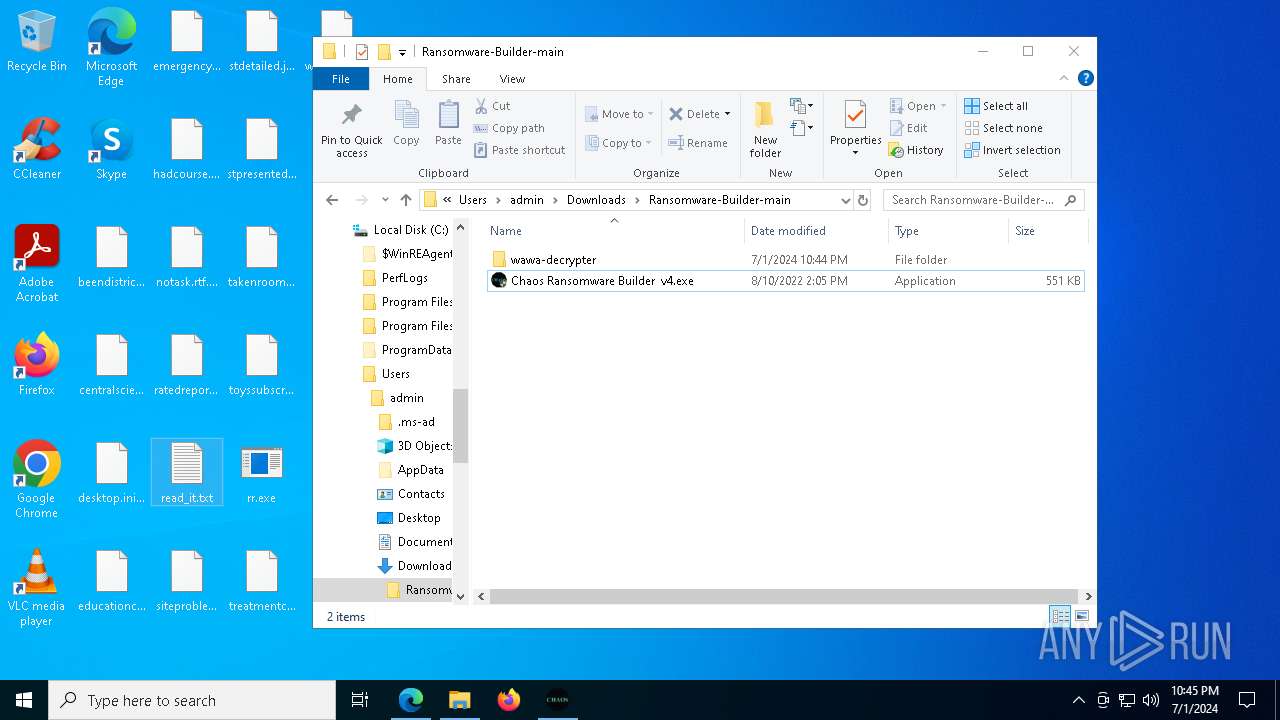
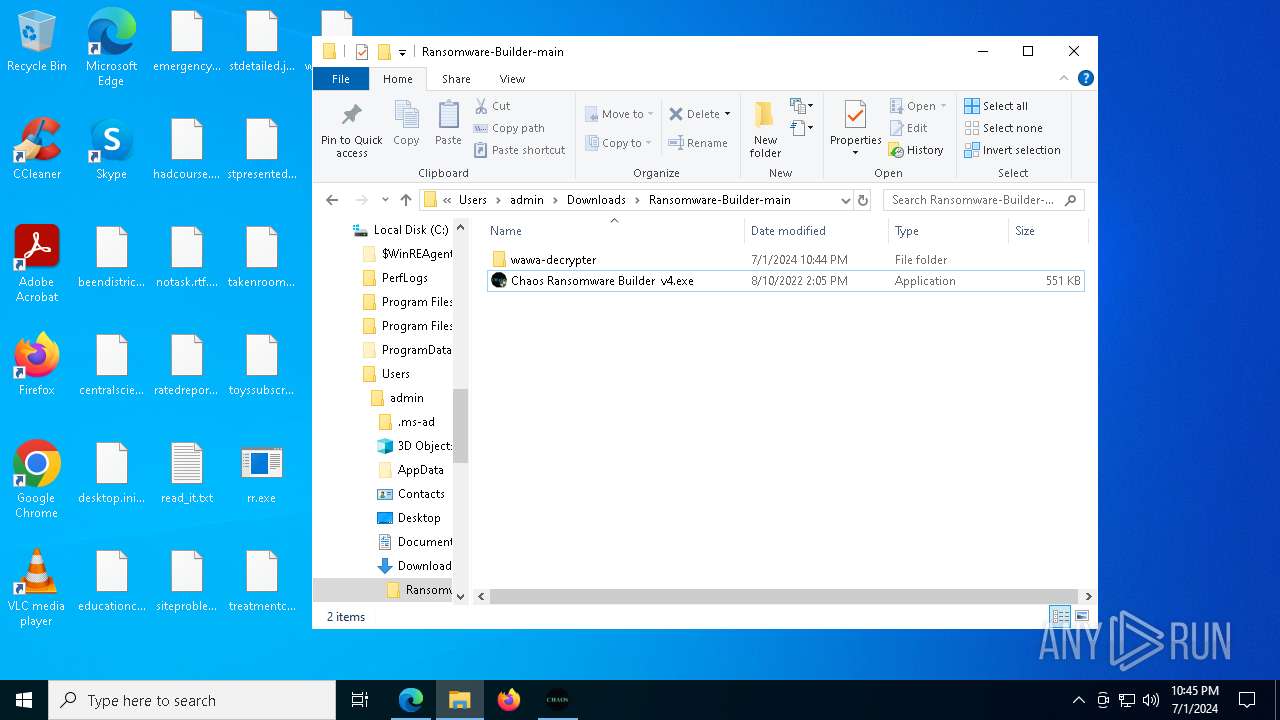
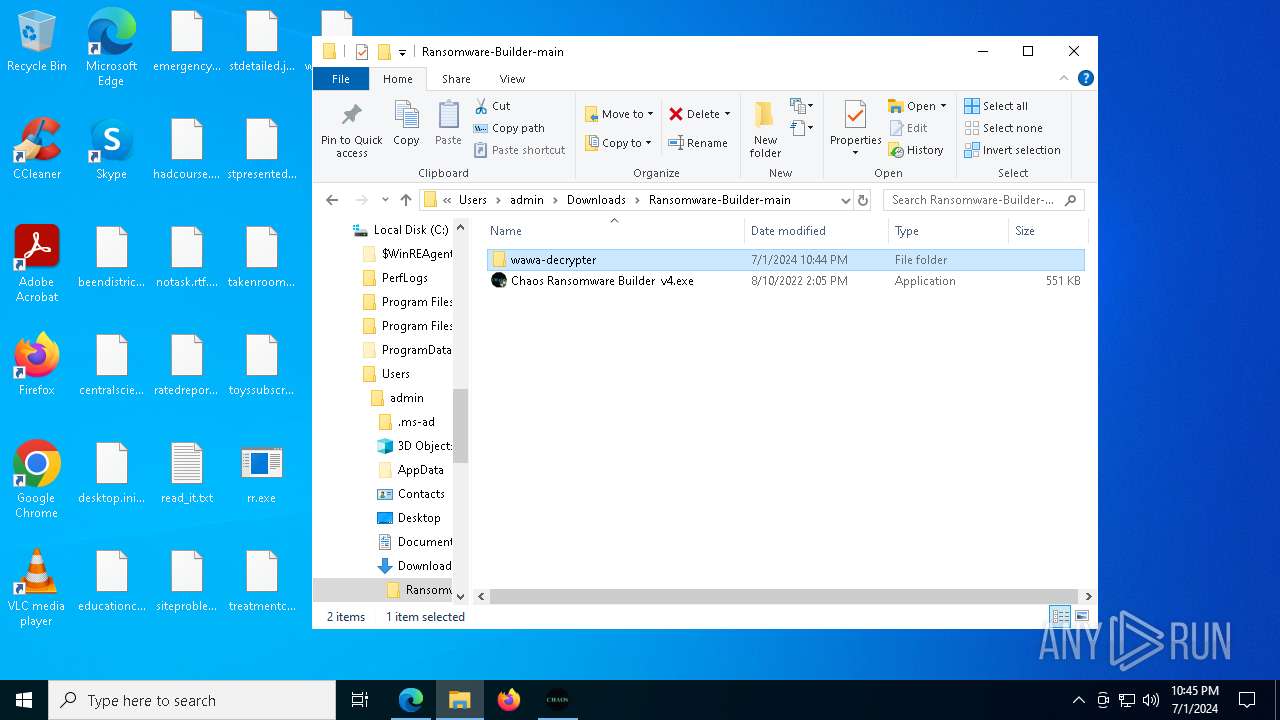
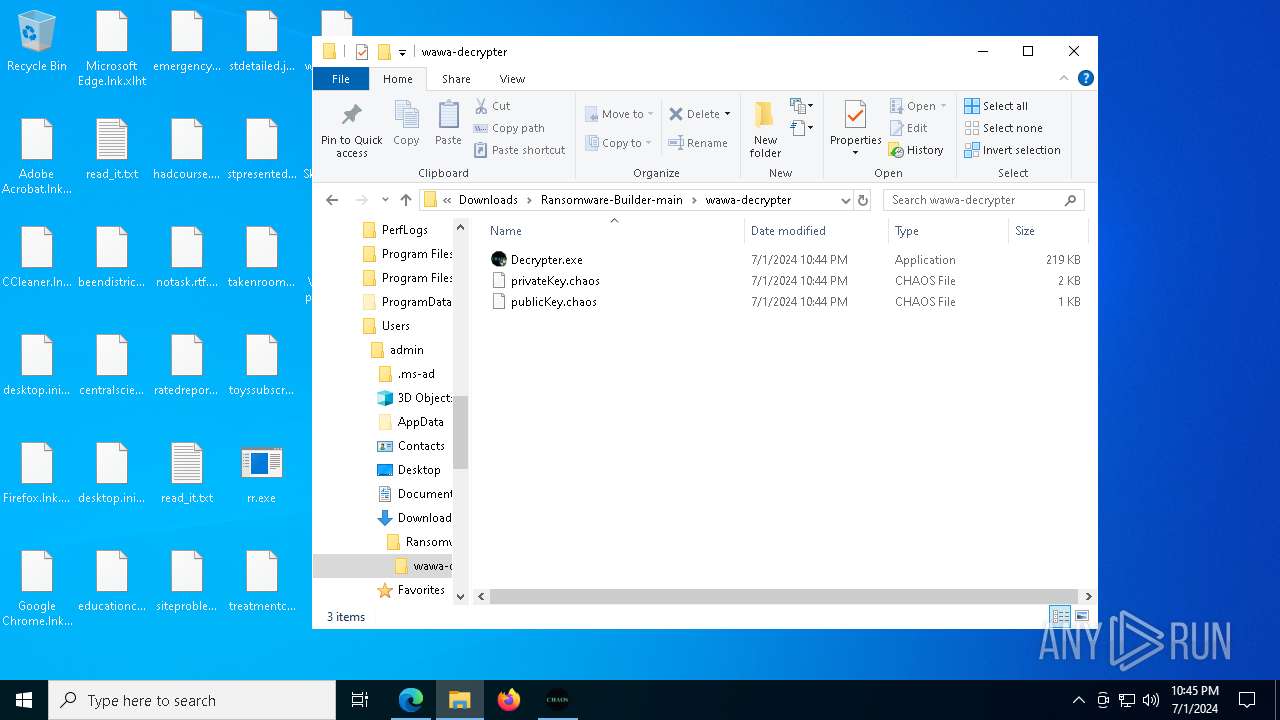
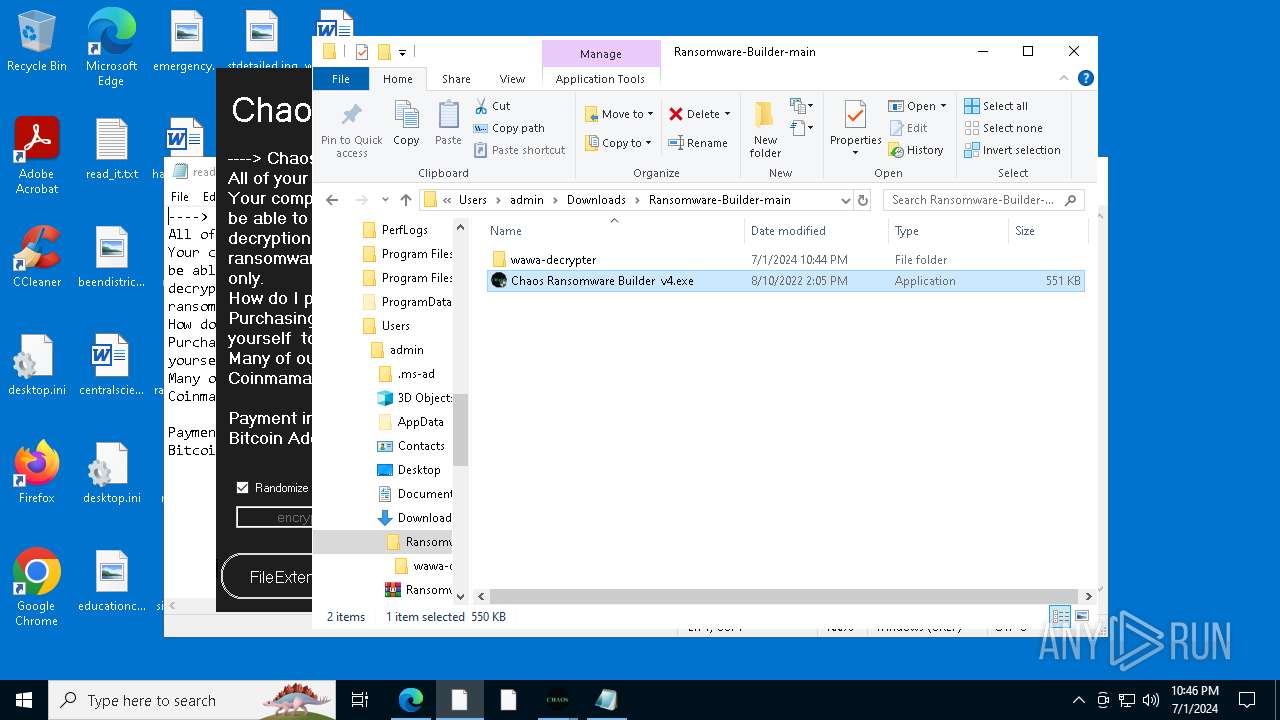
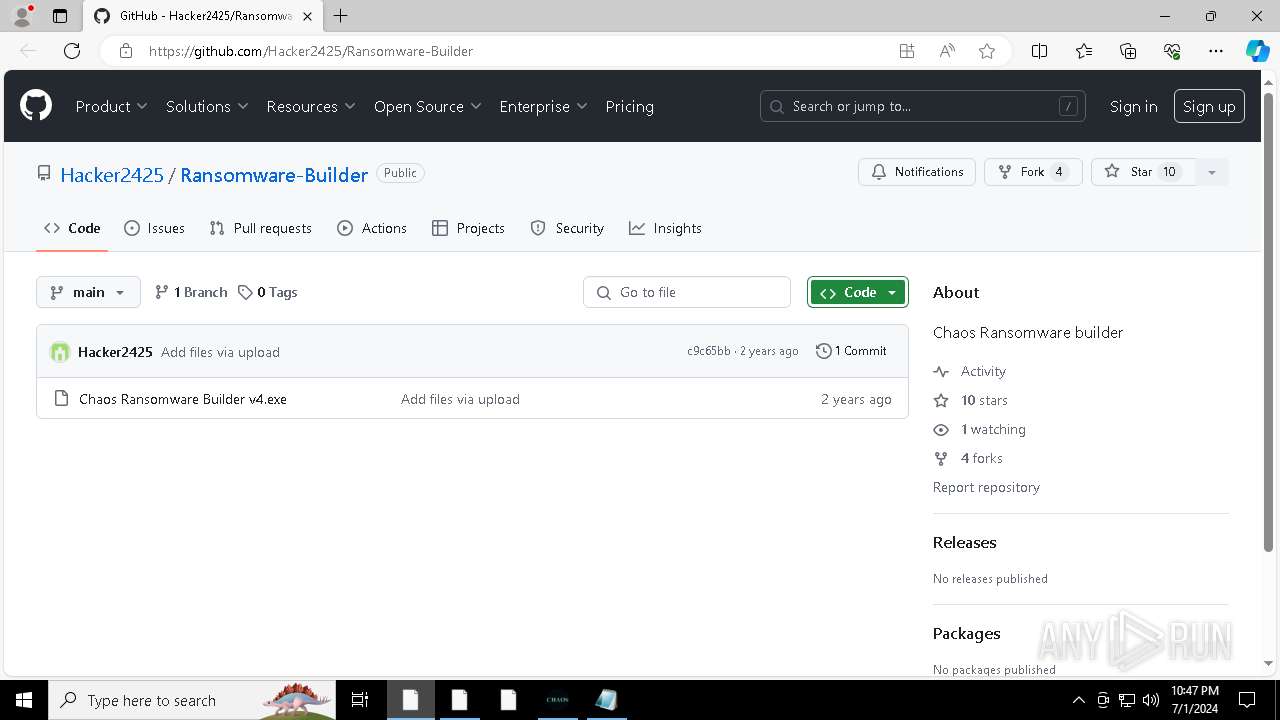
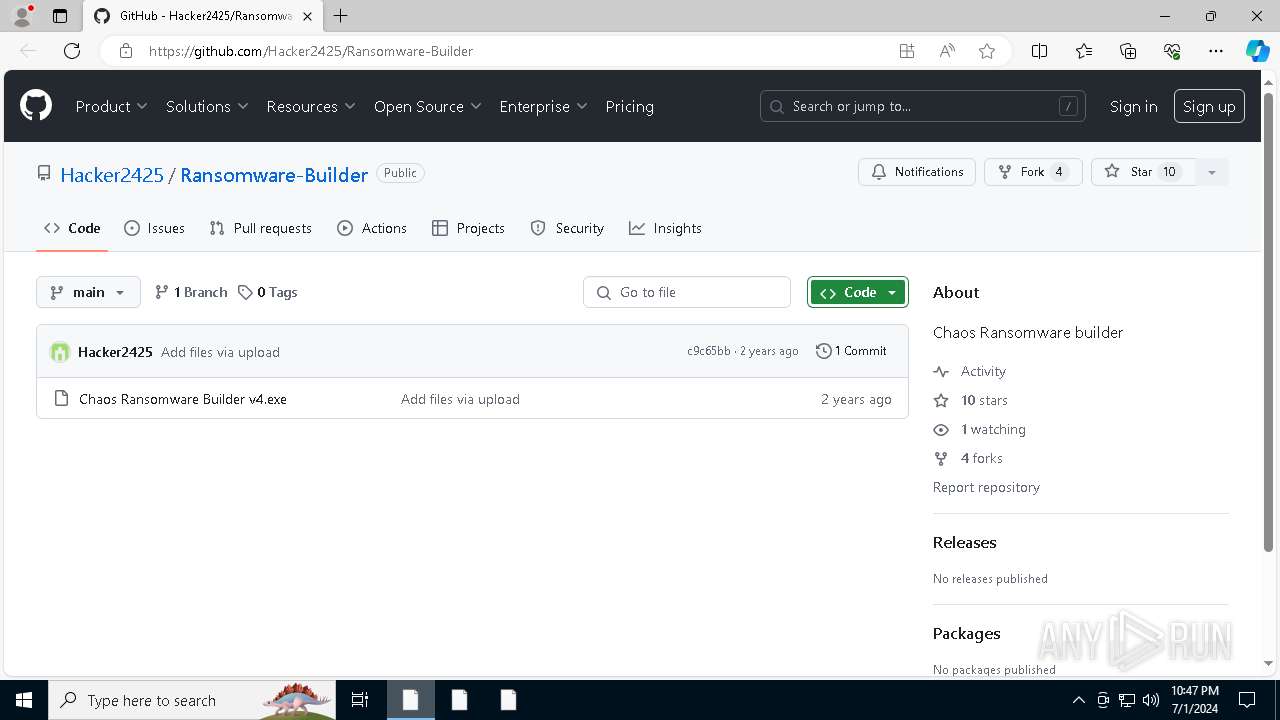
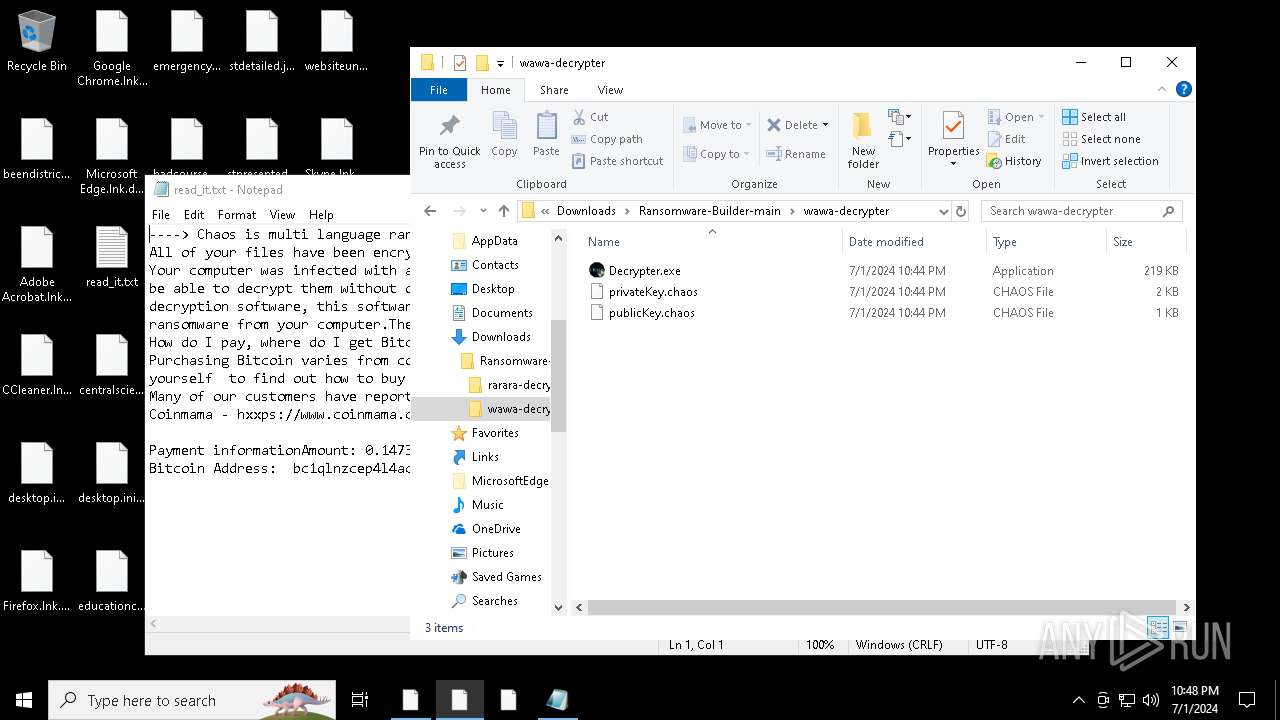
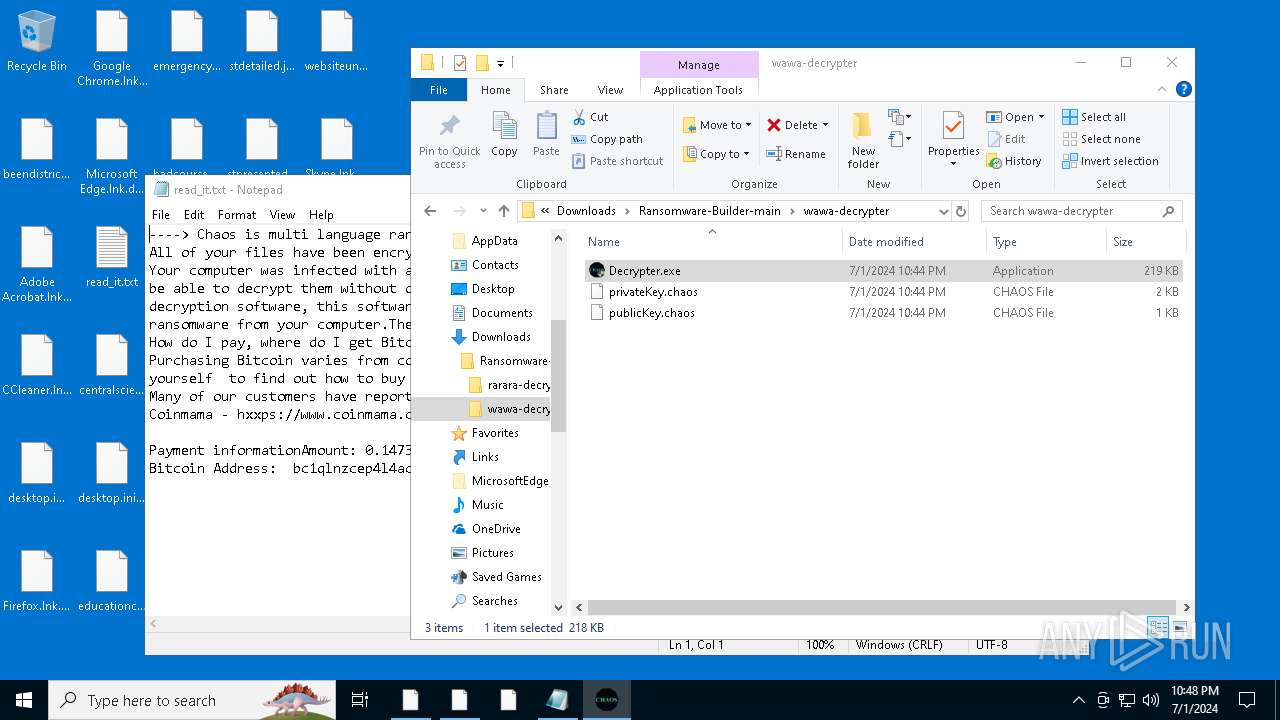
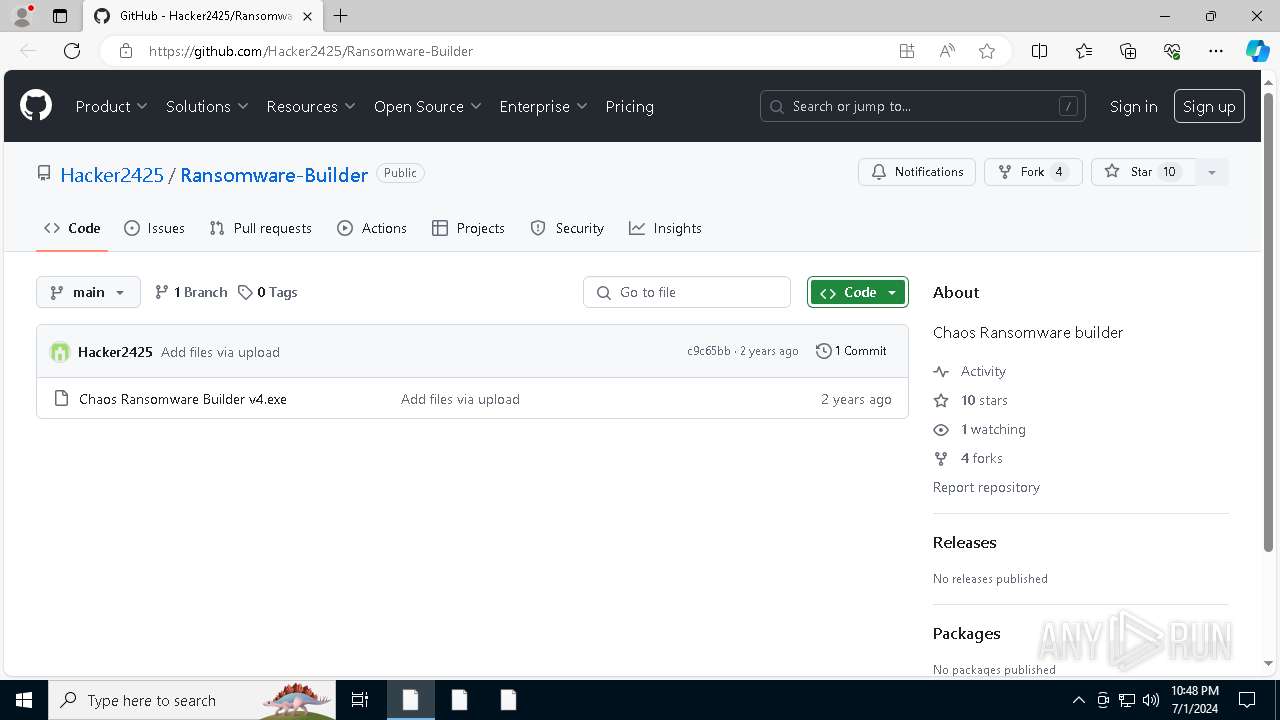
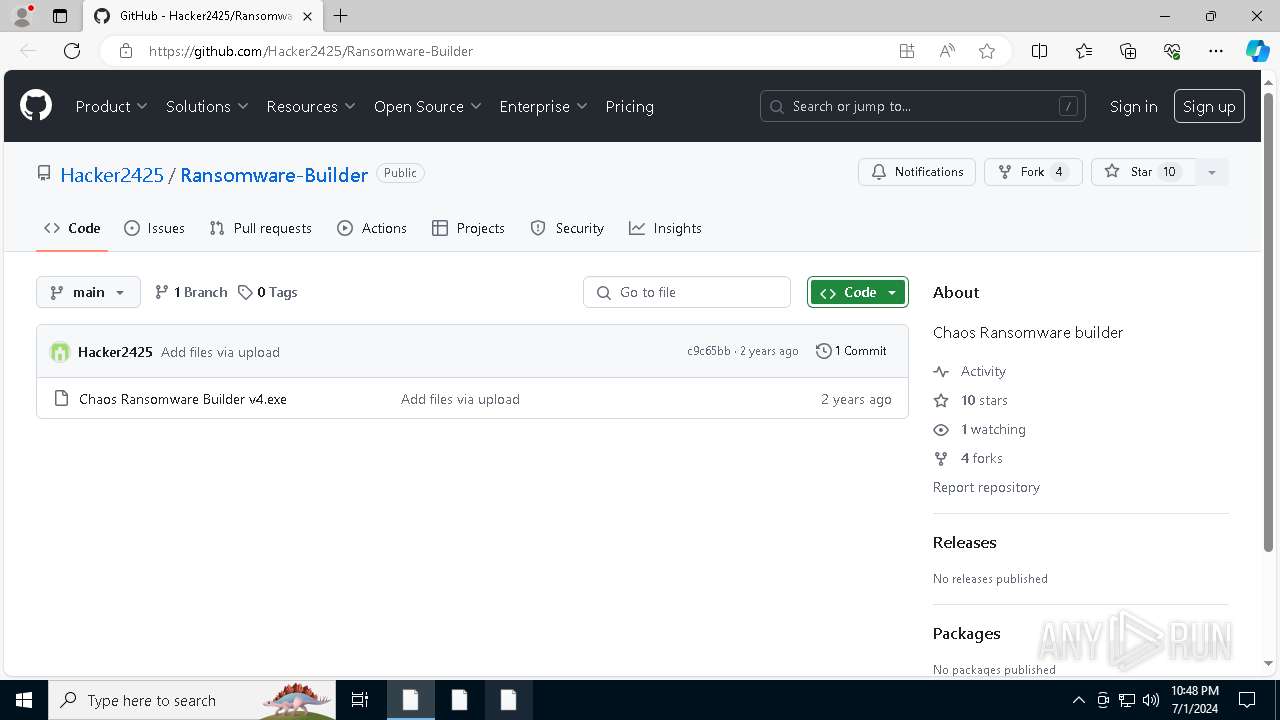
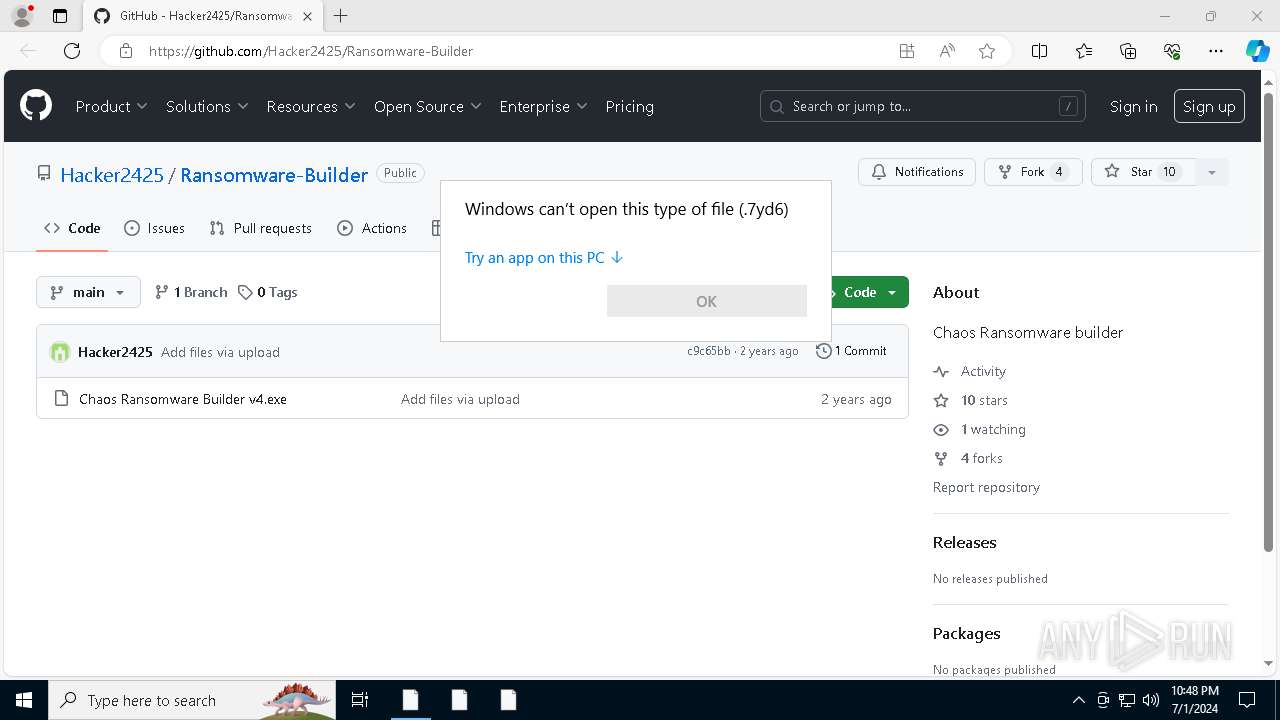
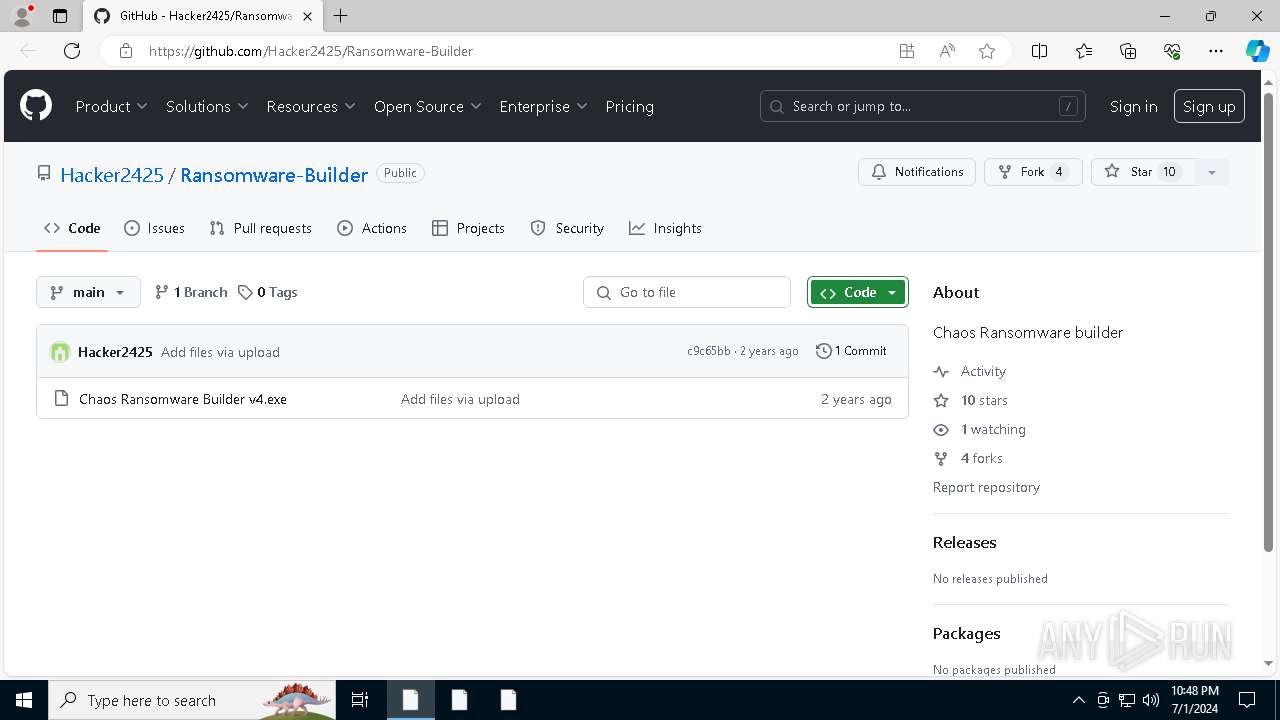
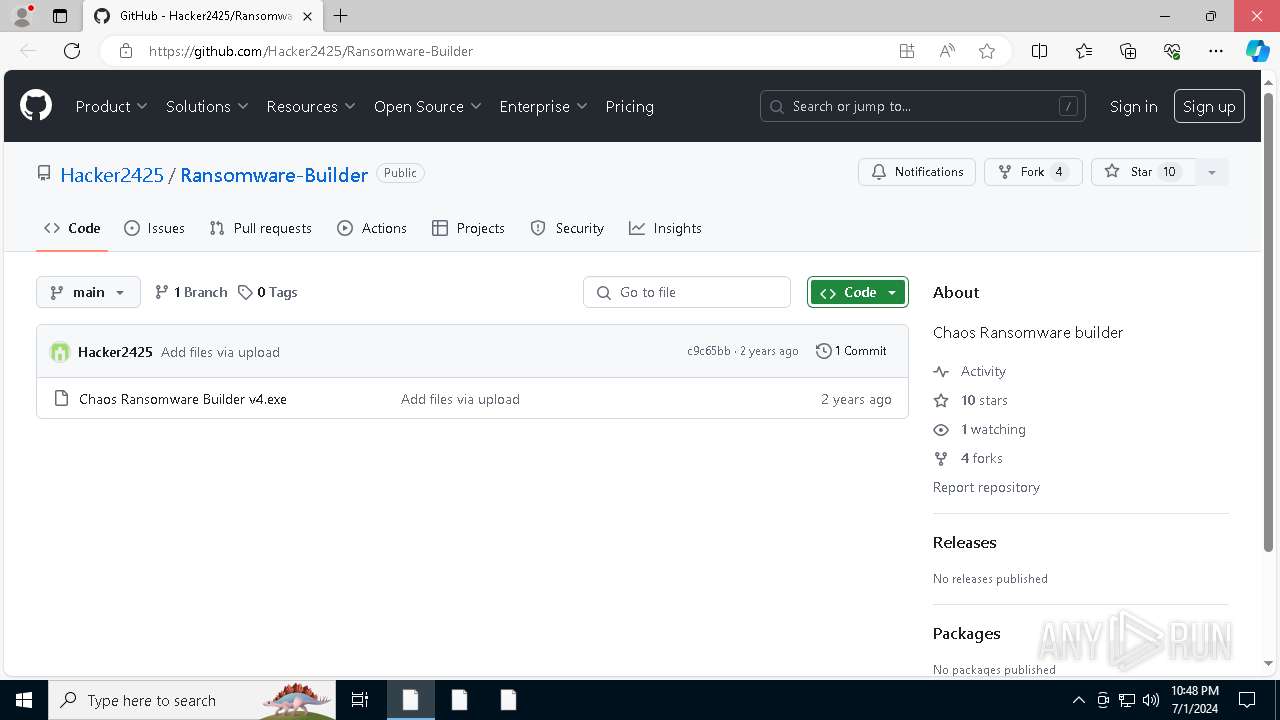
| URL: | https://github.com/Hacker2425/Ransomware-Builder.git |
| Full analysis: | https://app.any.run/tasks/2d5d32e6-8e2a-4736-9d05-d70837592fde |
| Verdict: | Malicious activity |
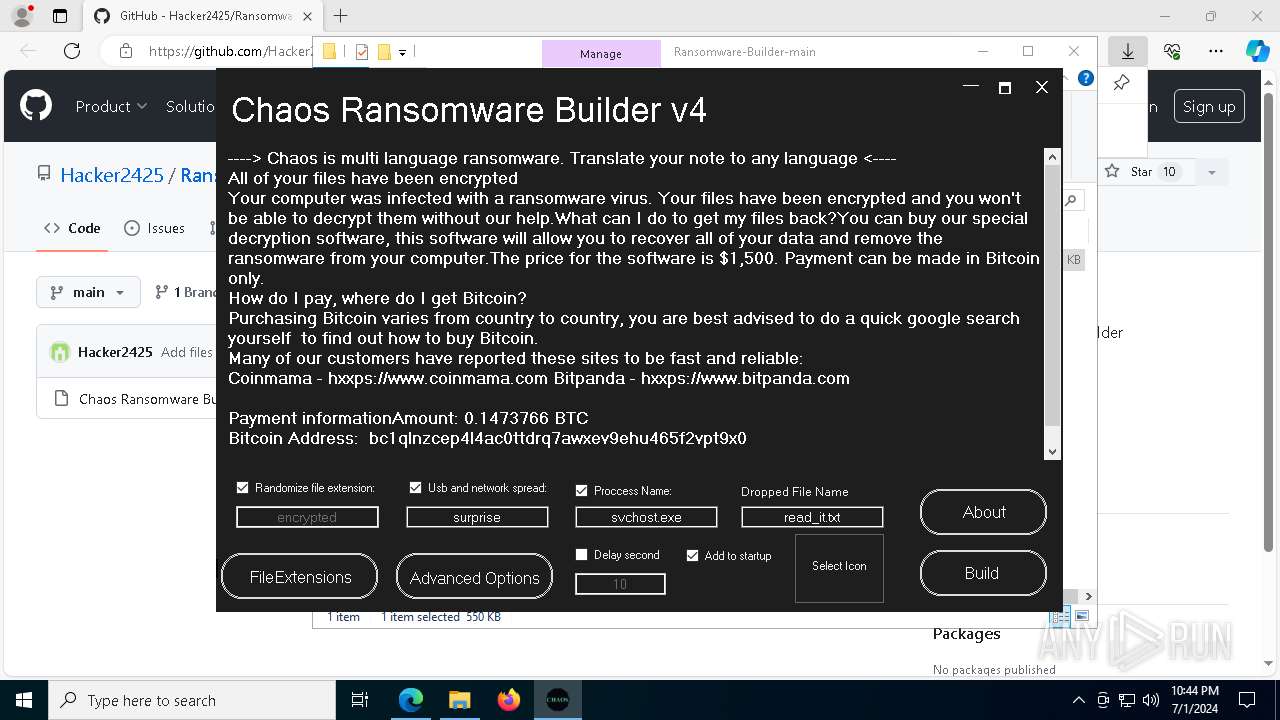
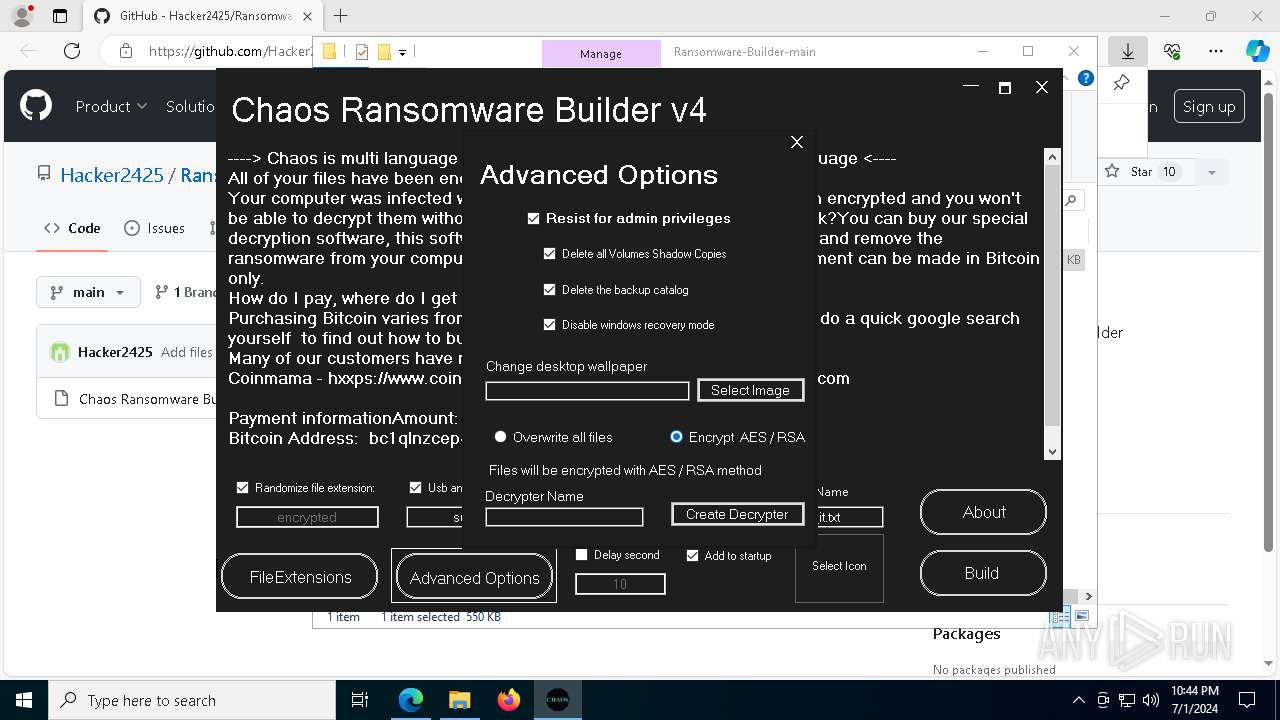
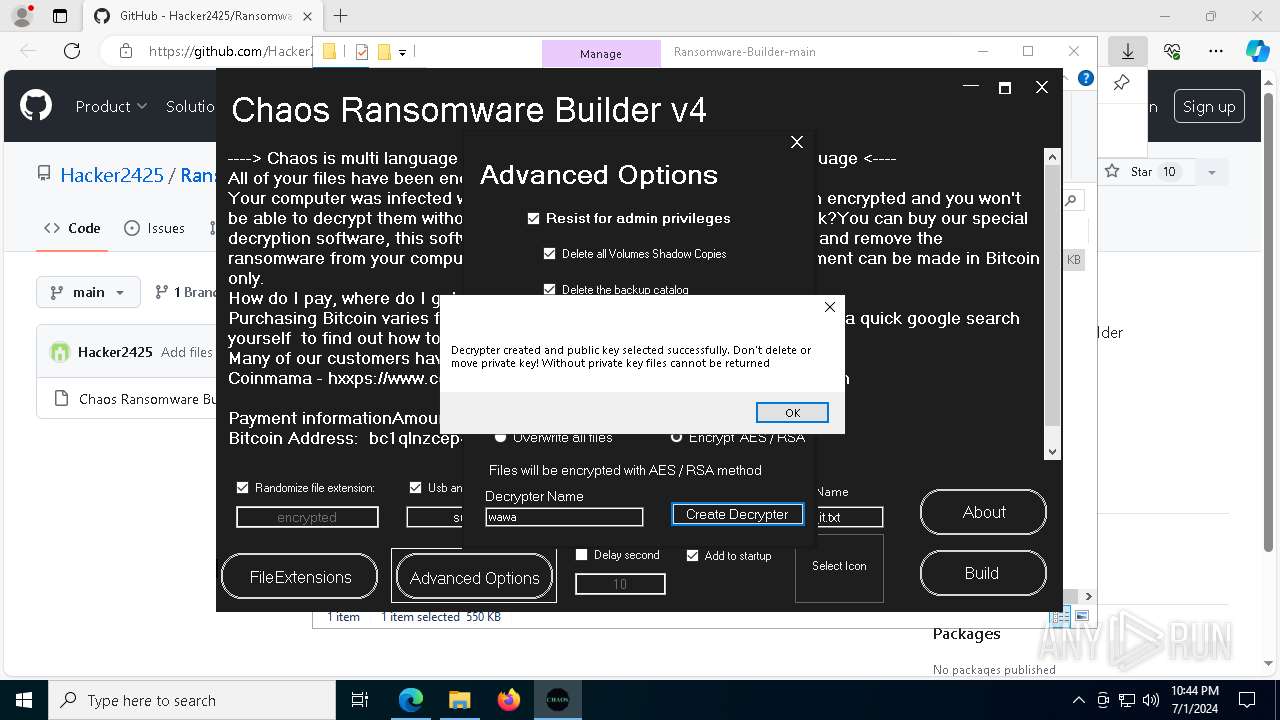
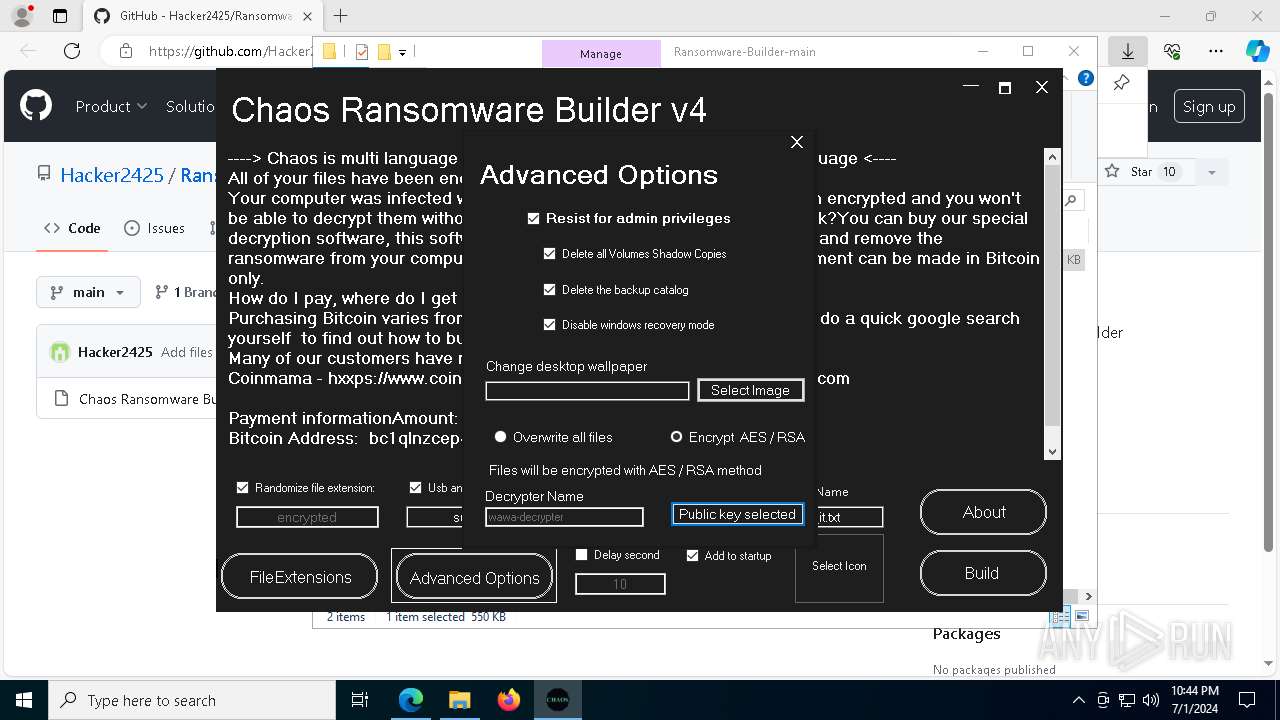
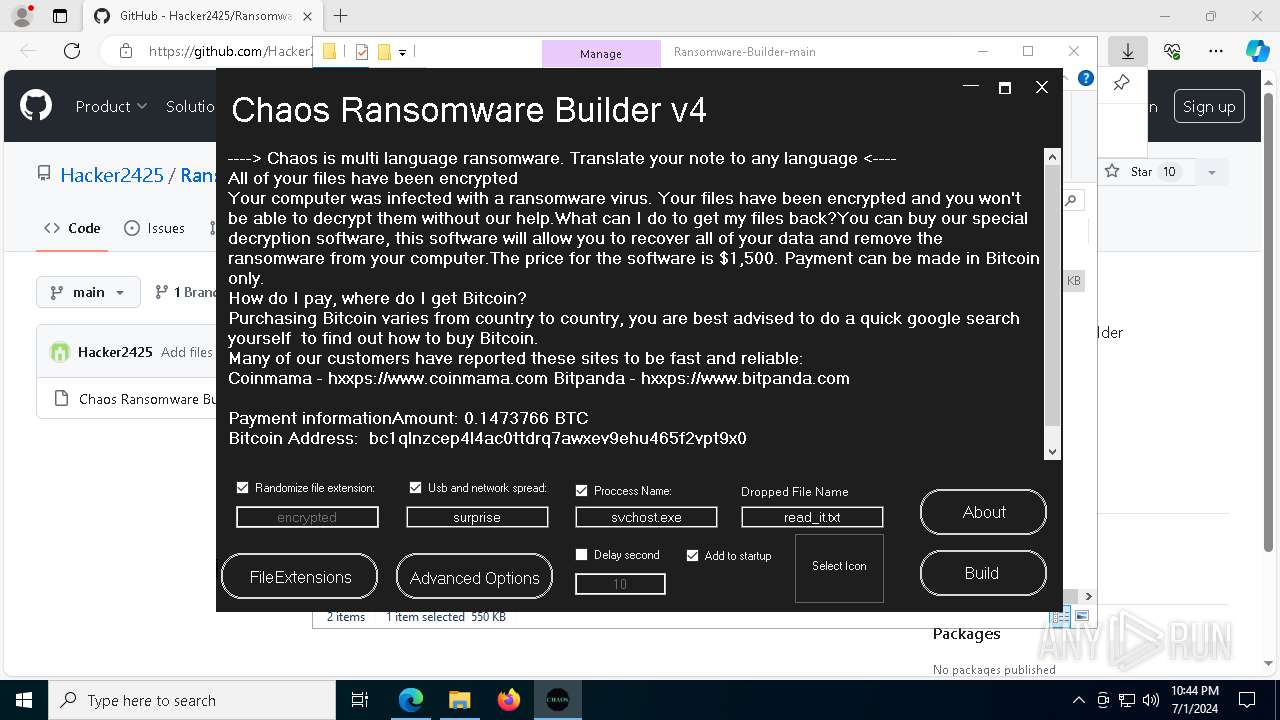
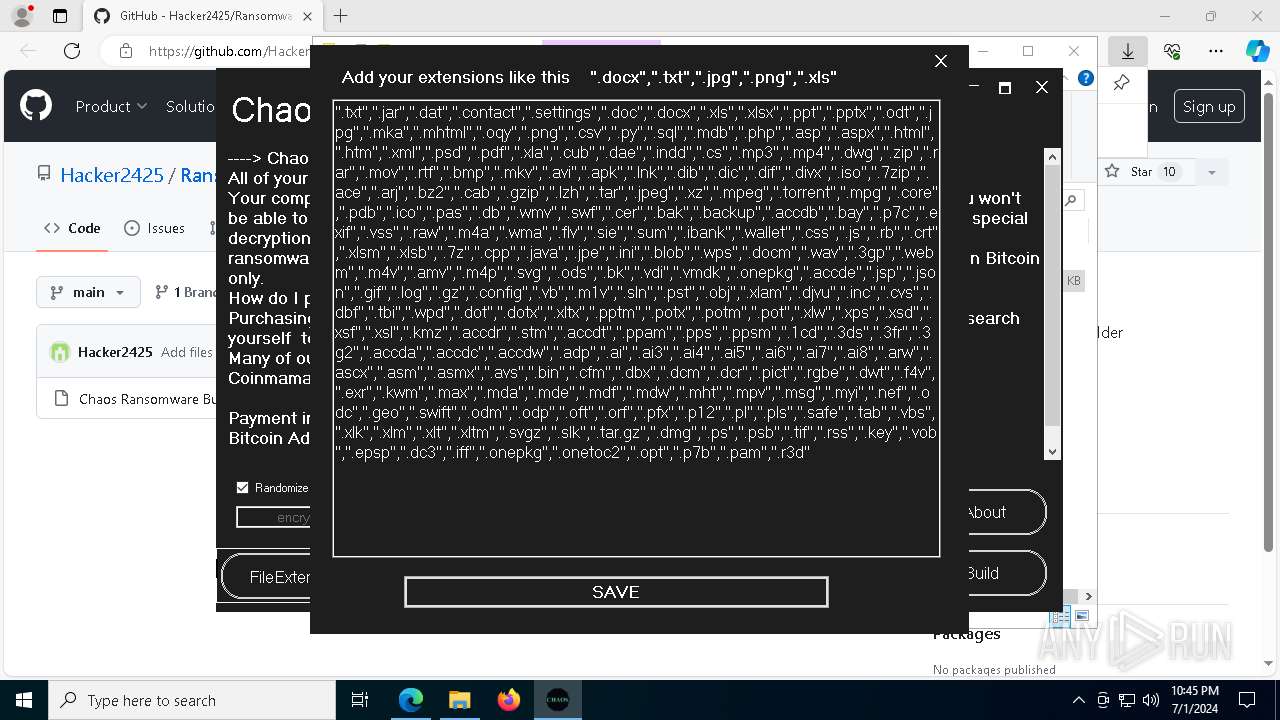
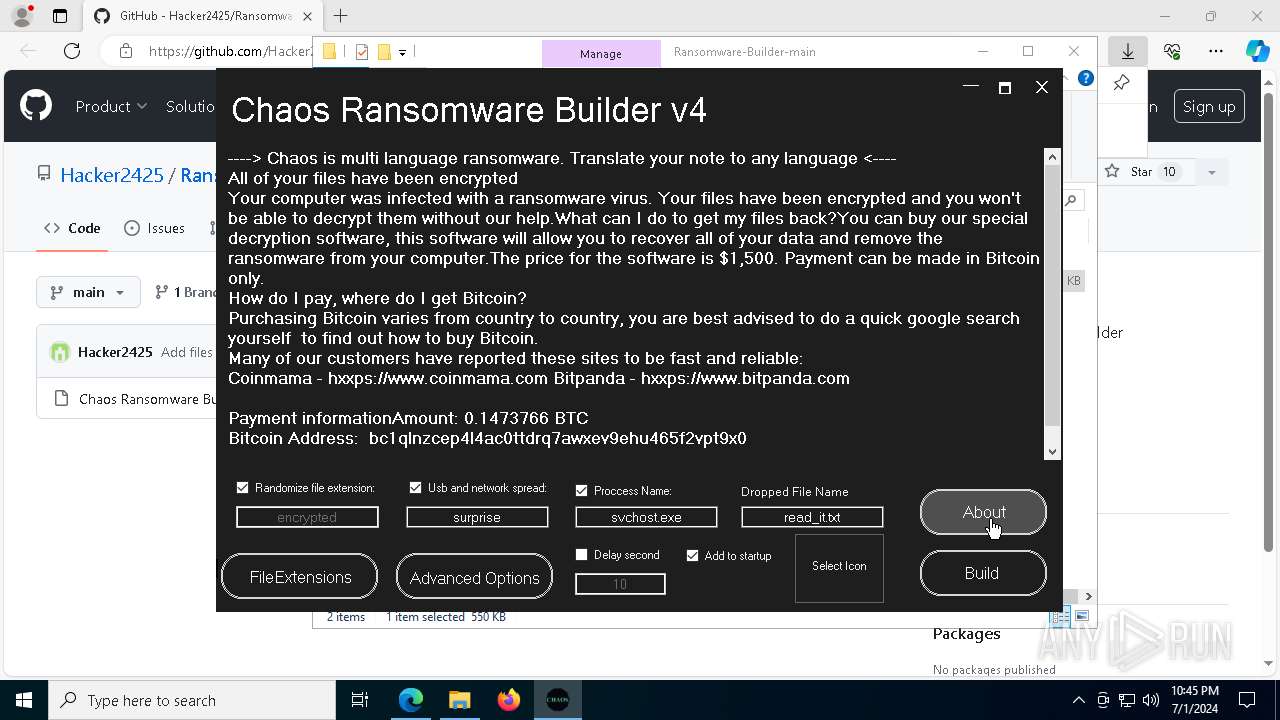
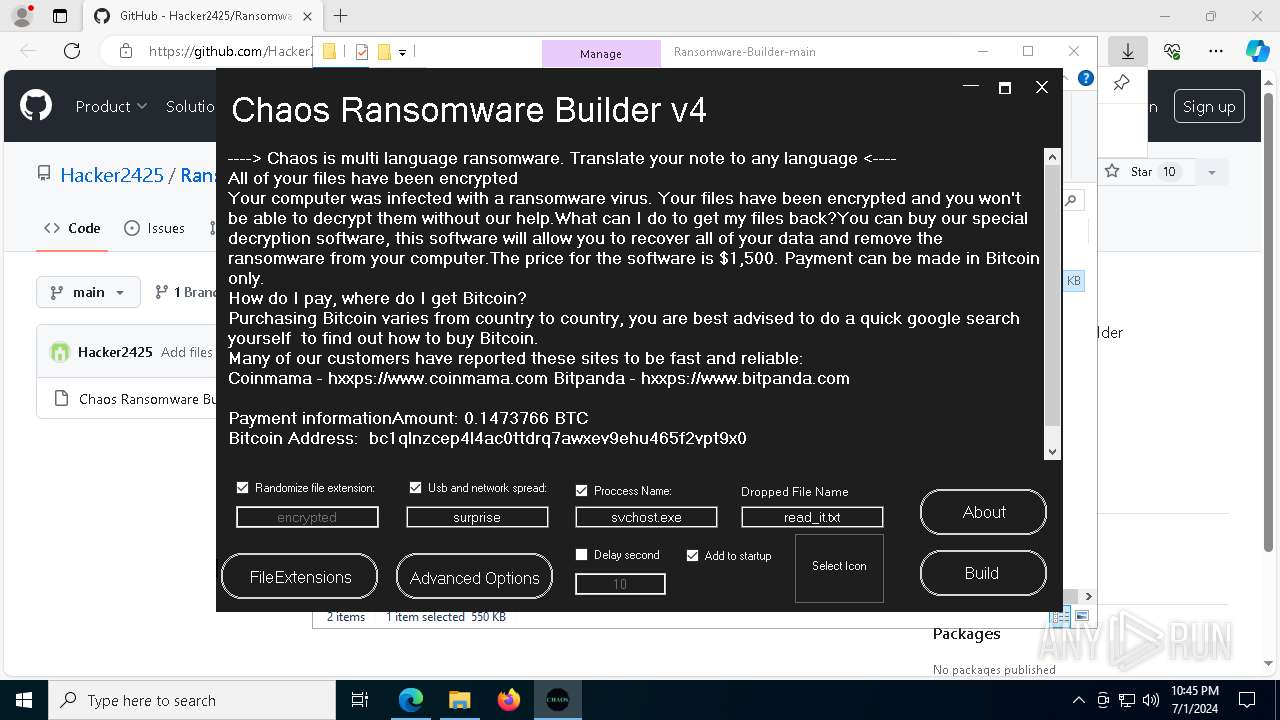
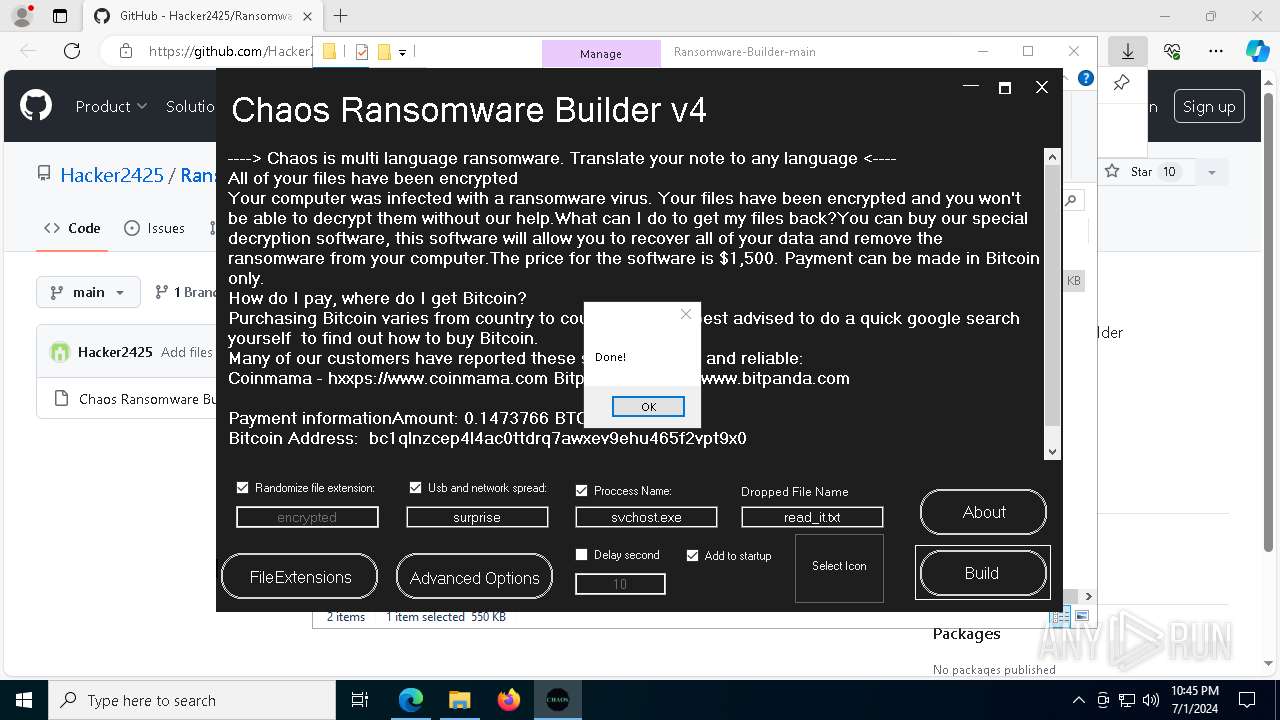
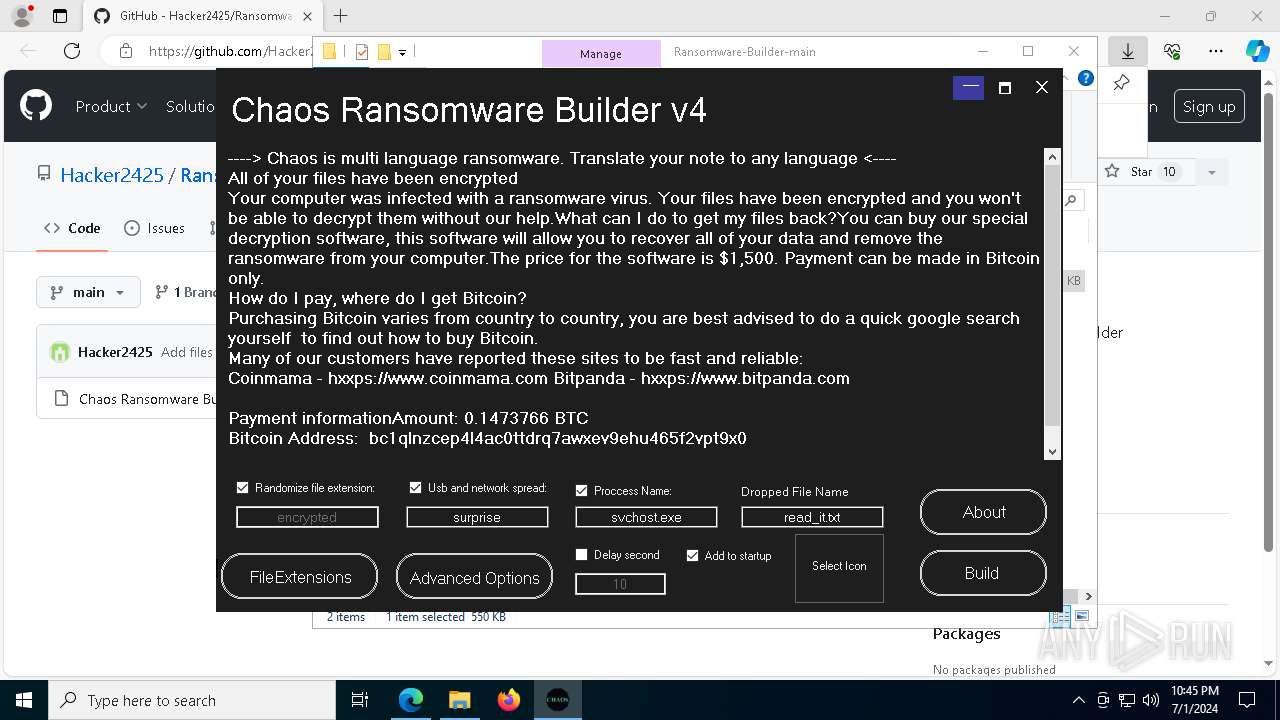
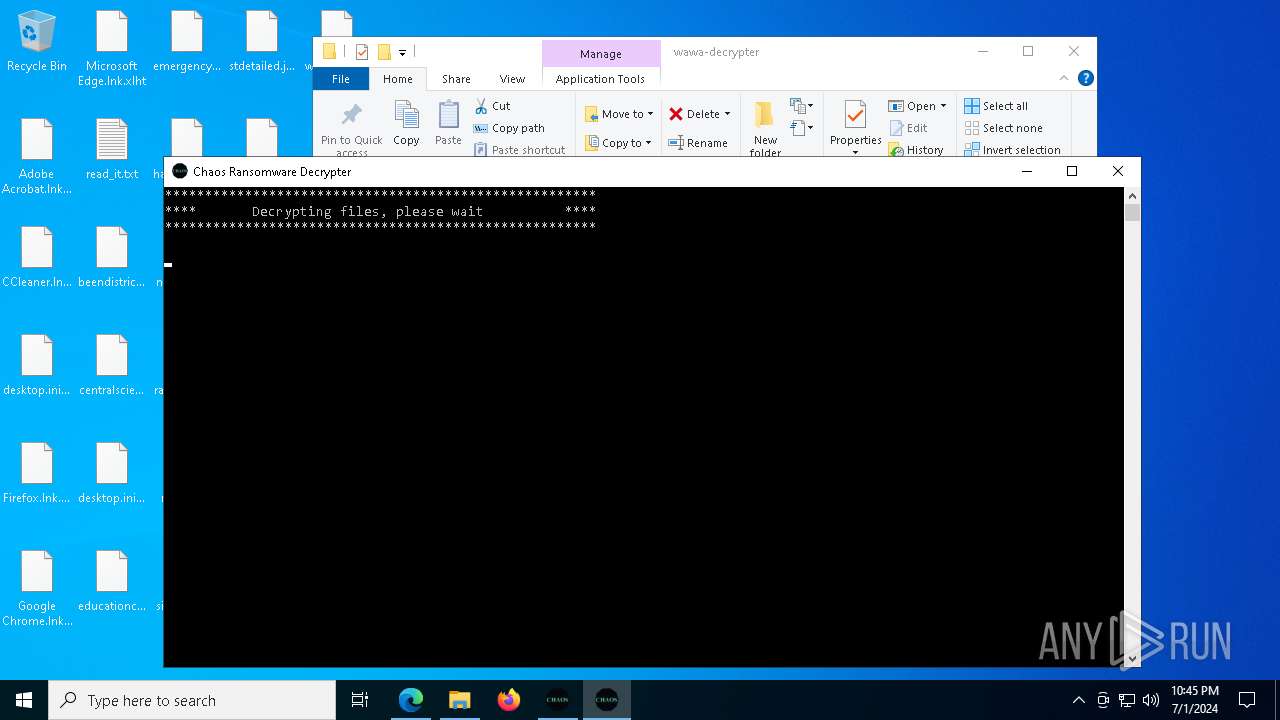
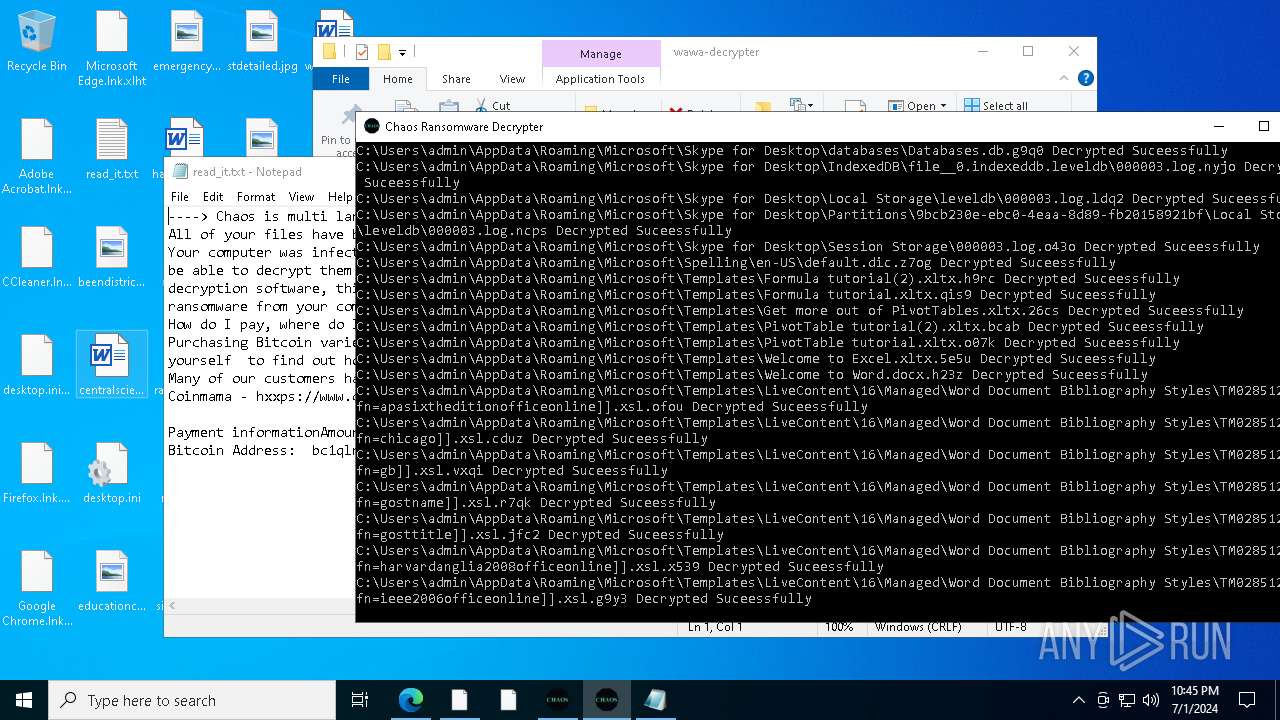
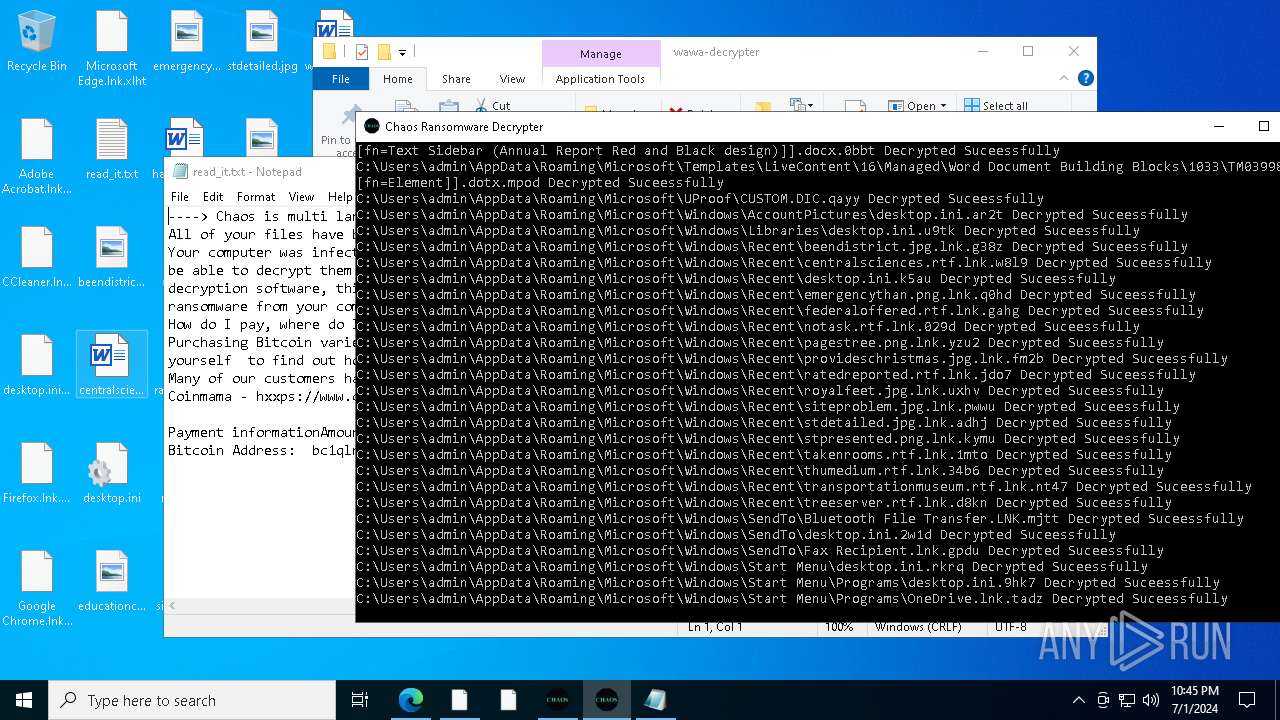
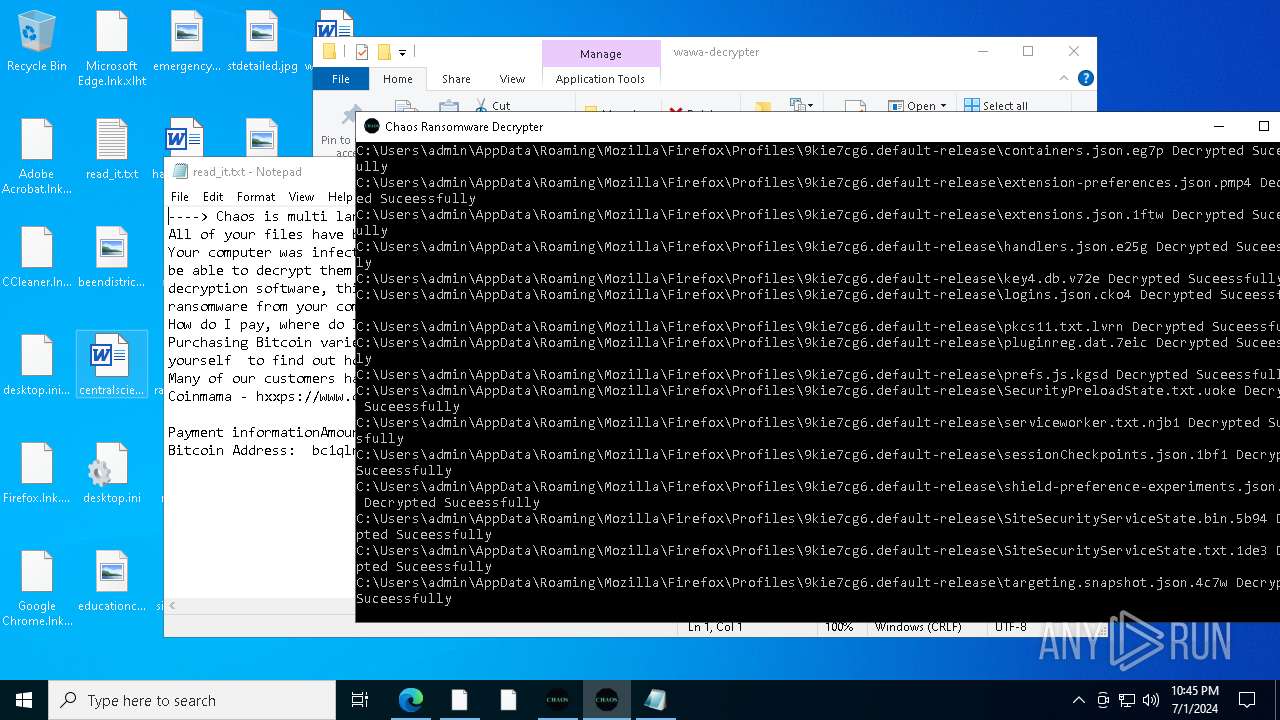
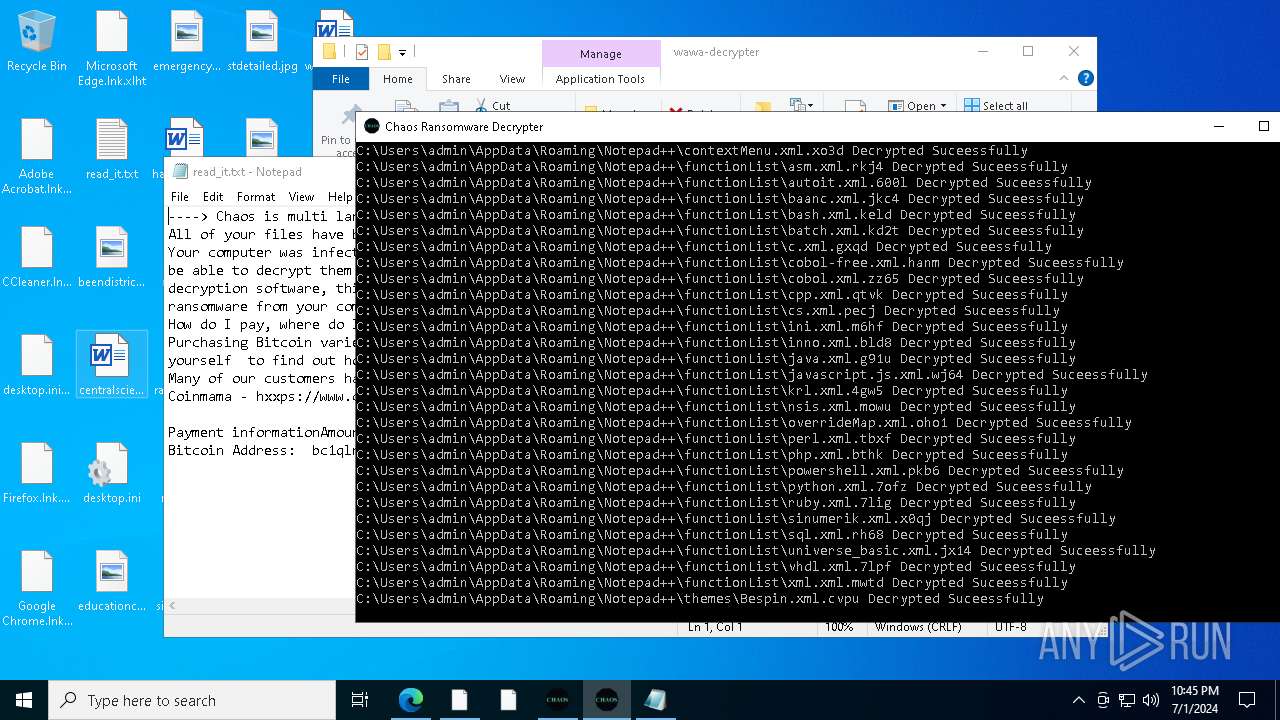
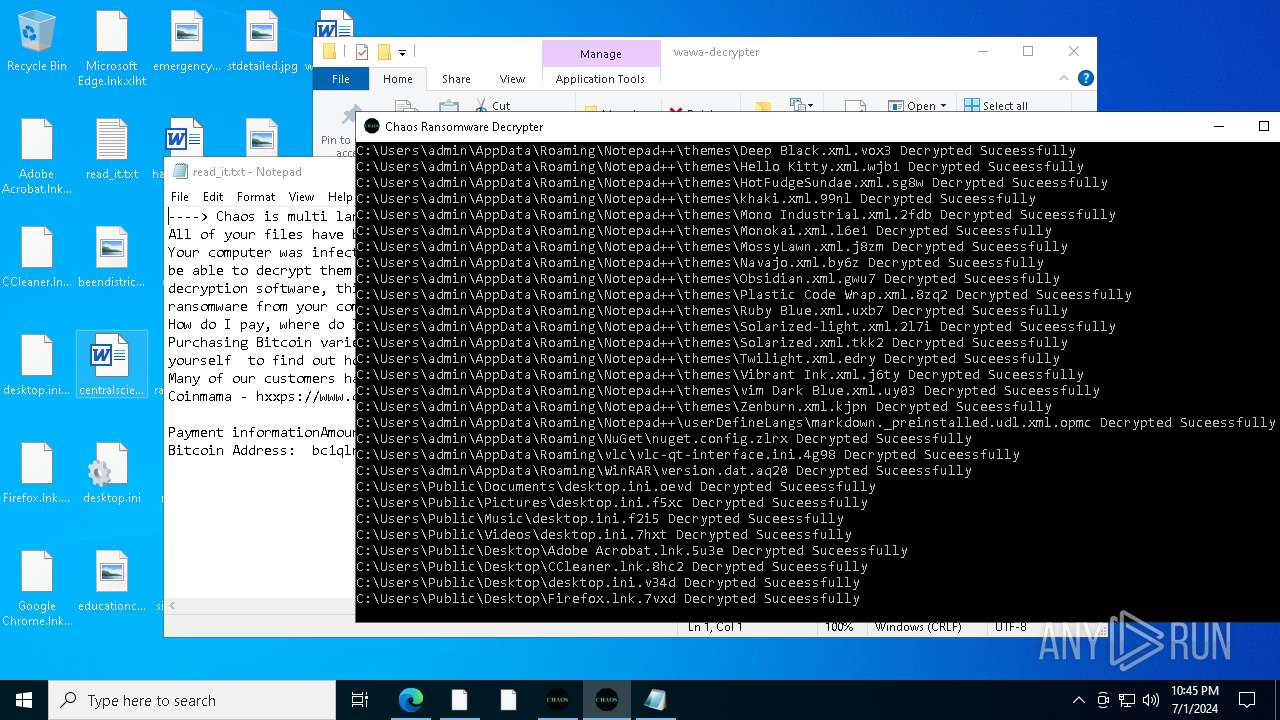
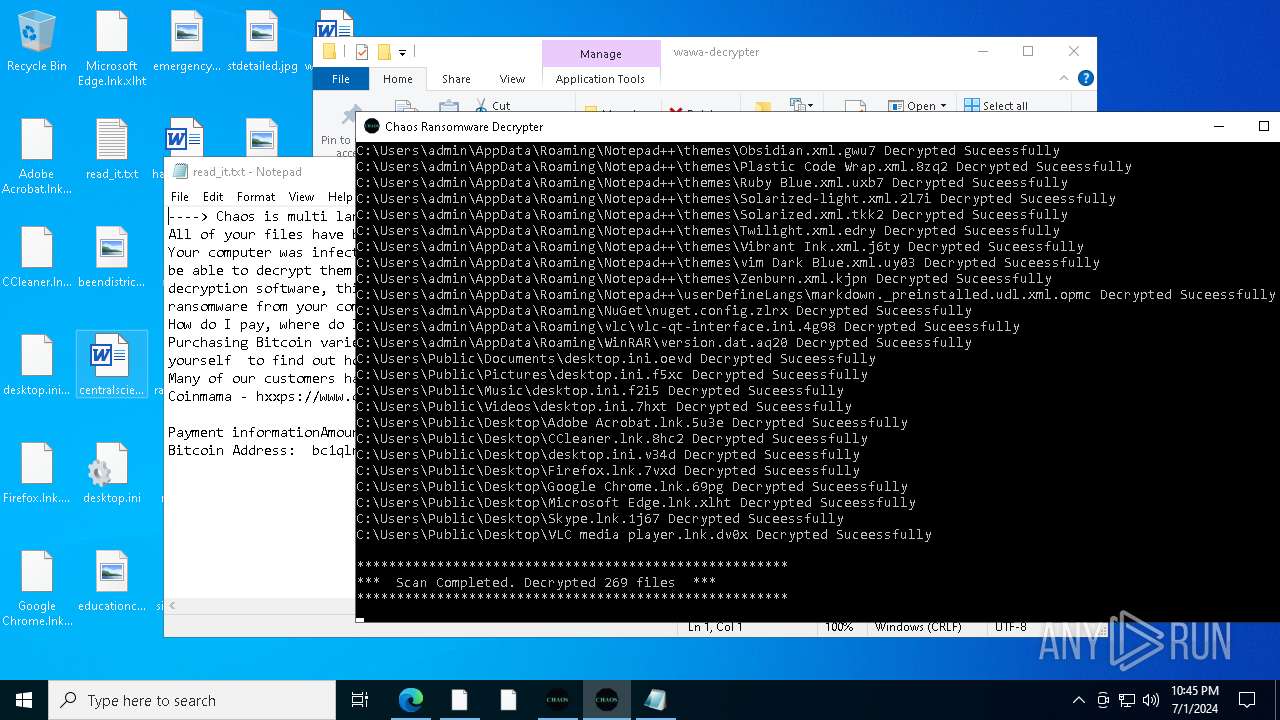
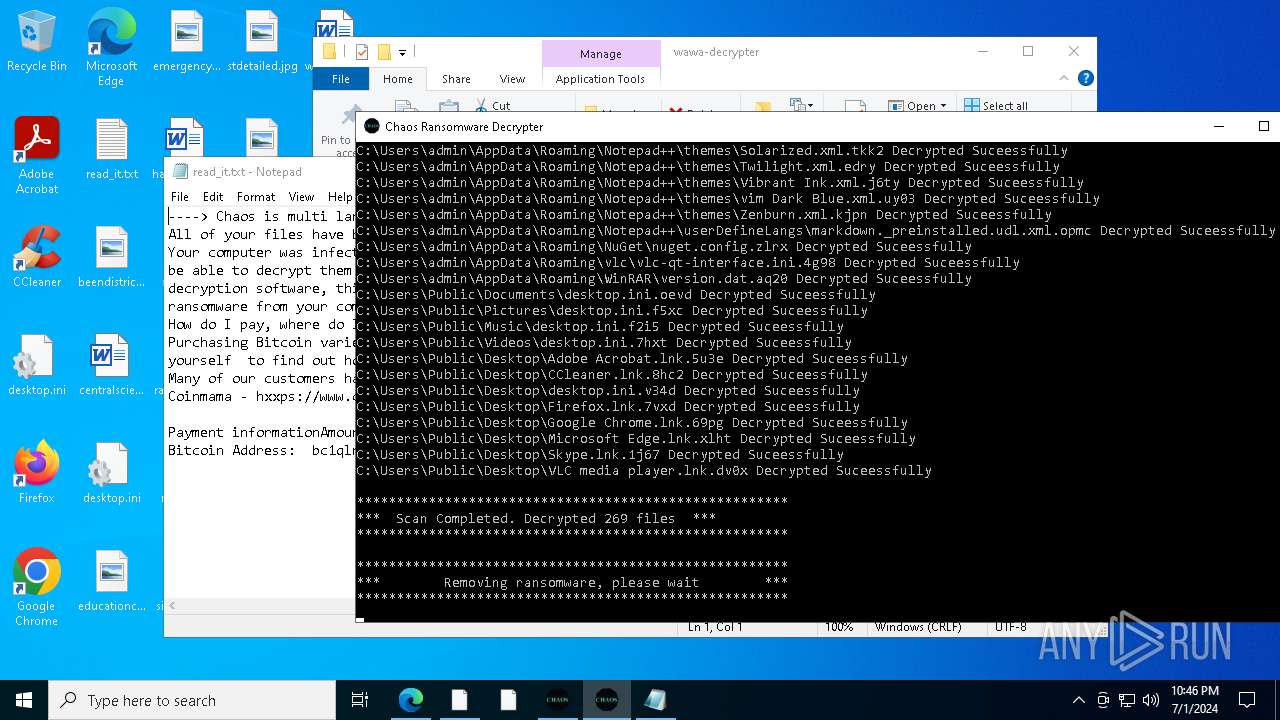
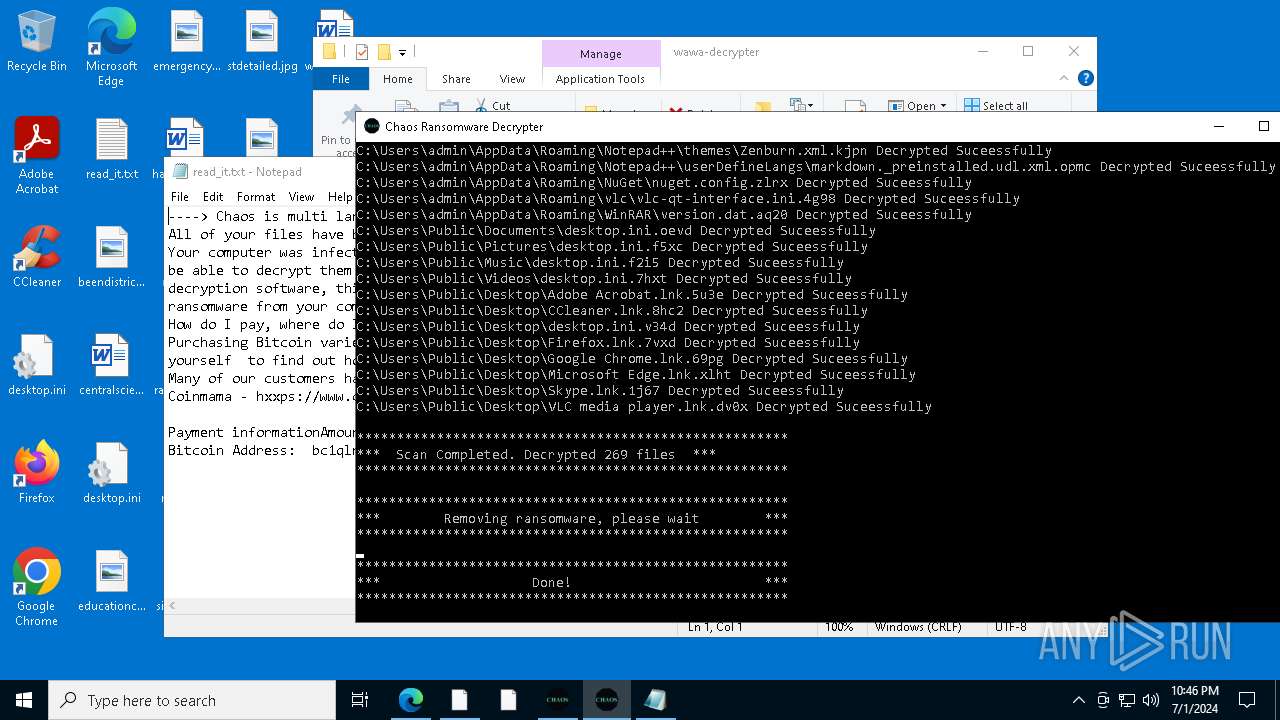
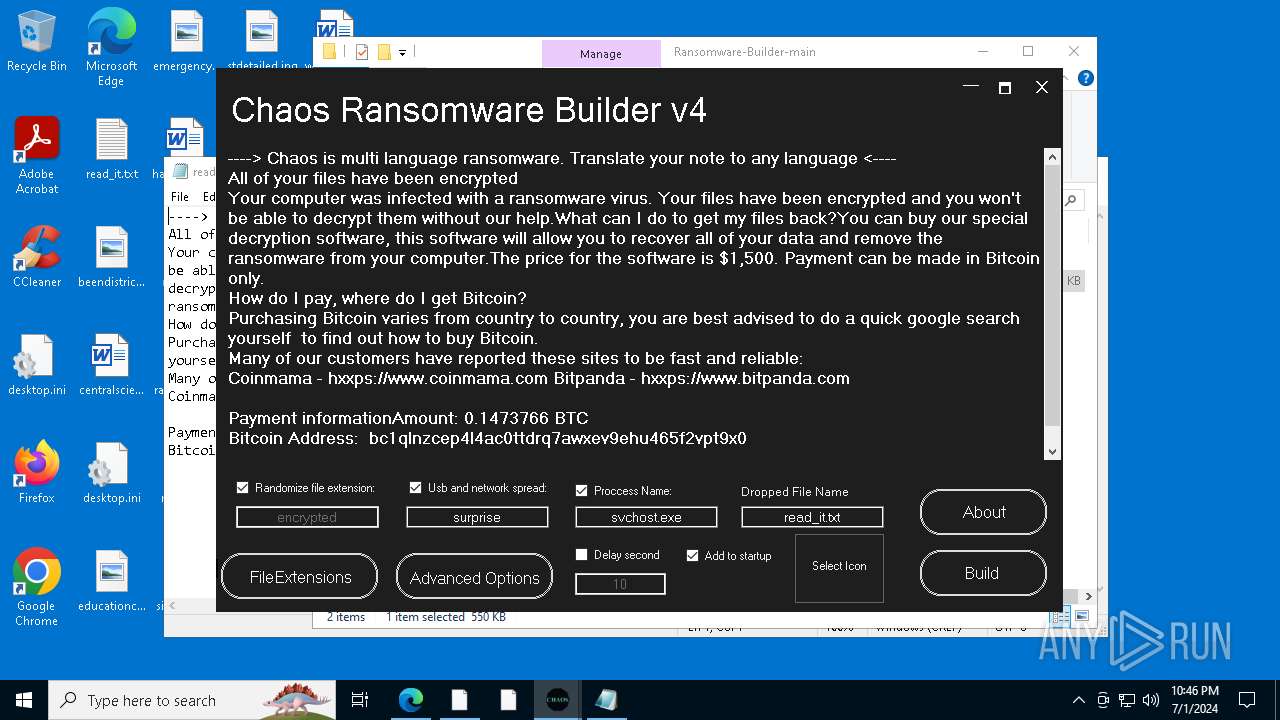
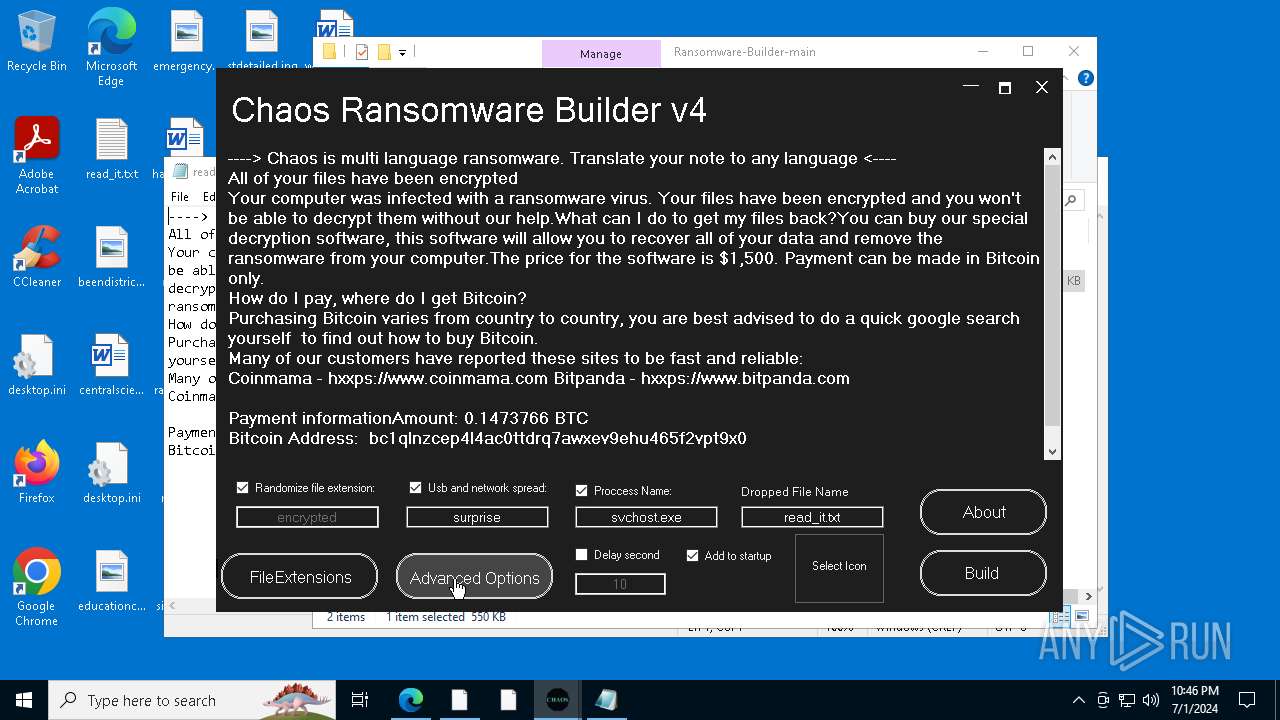
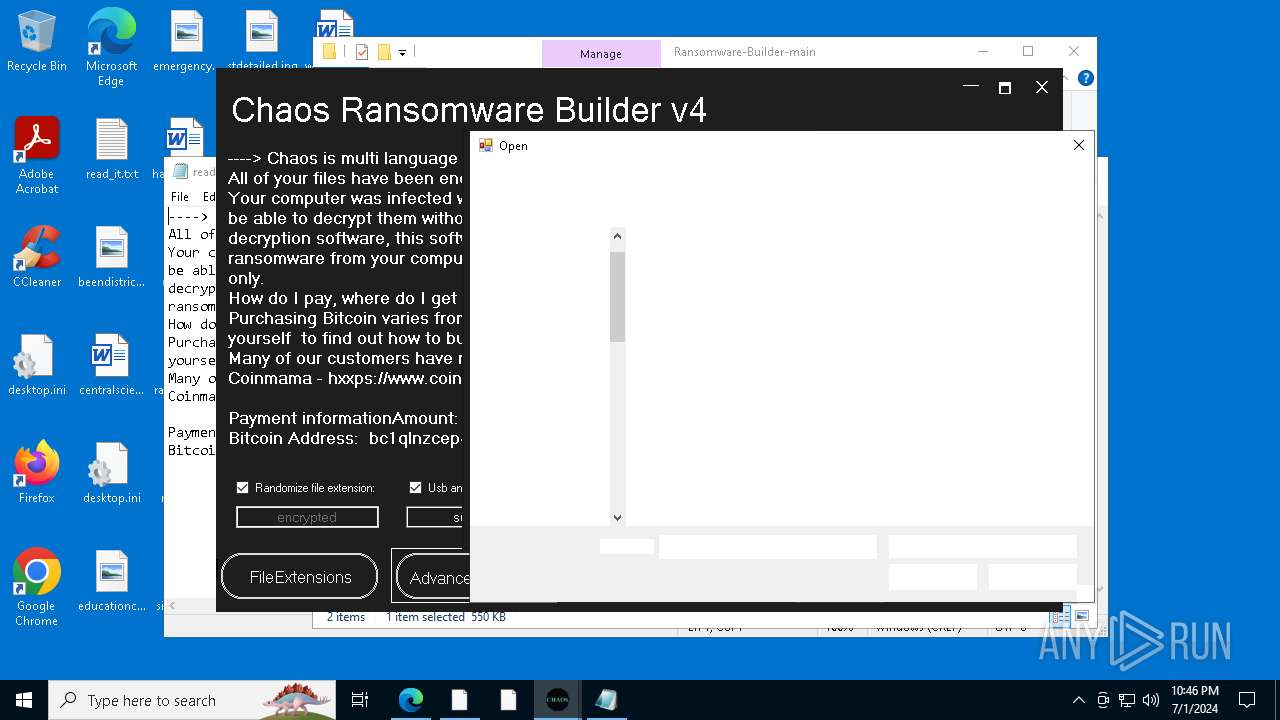
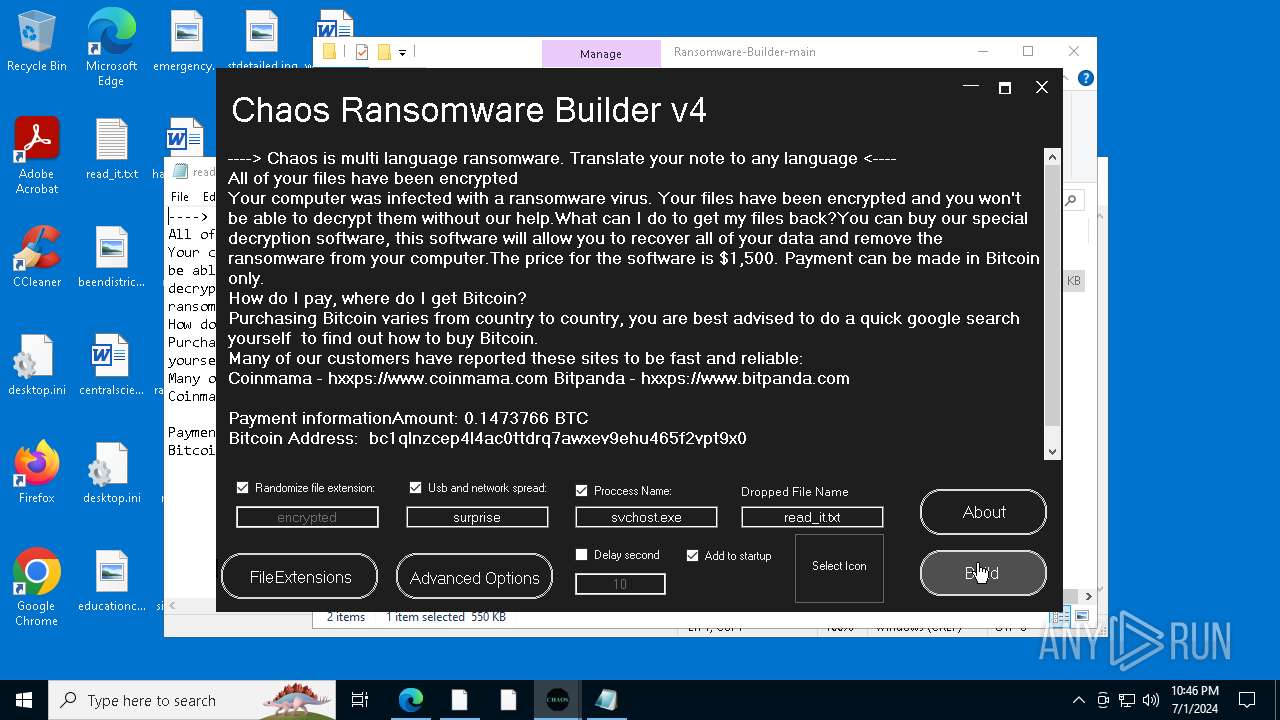
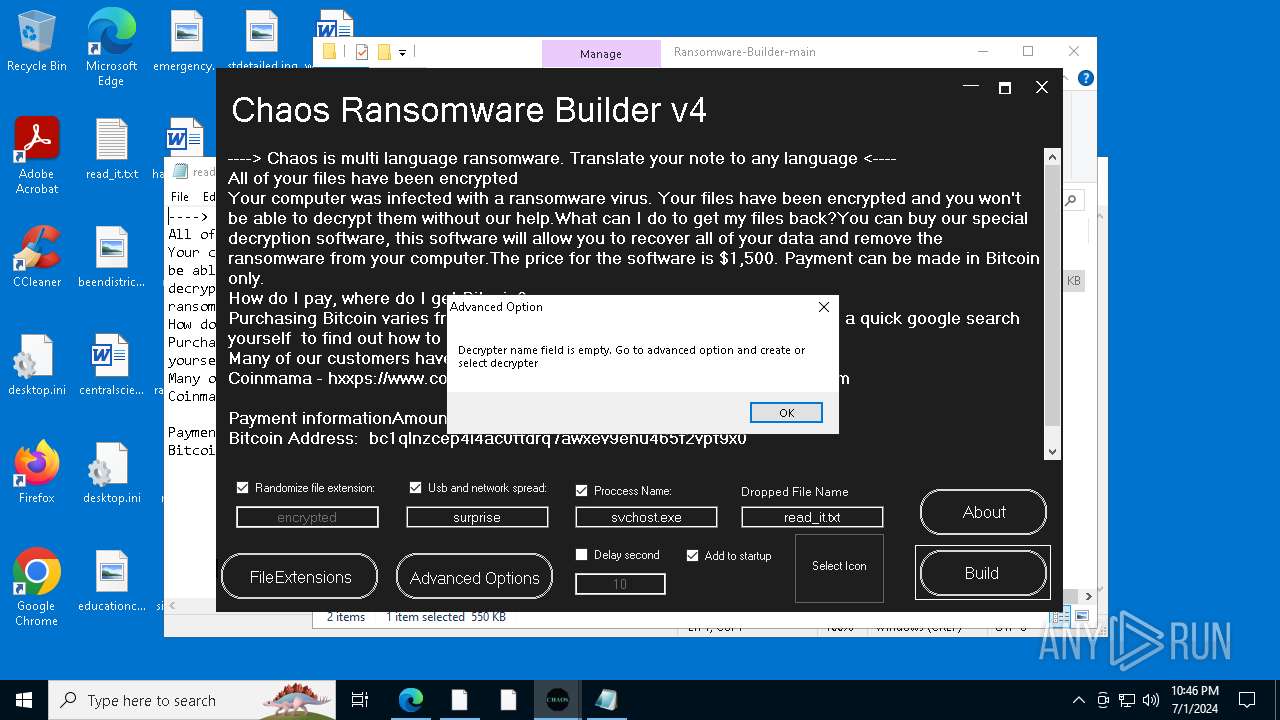
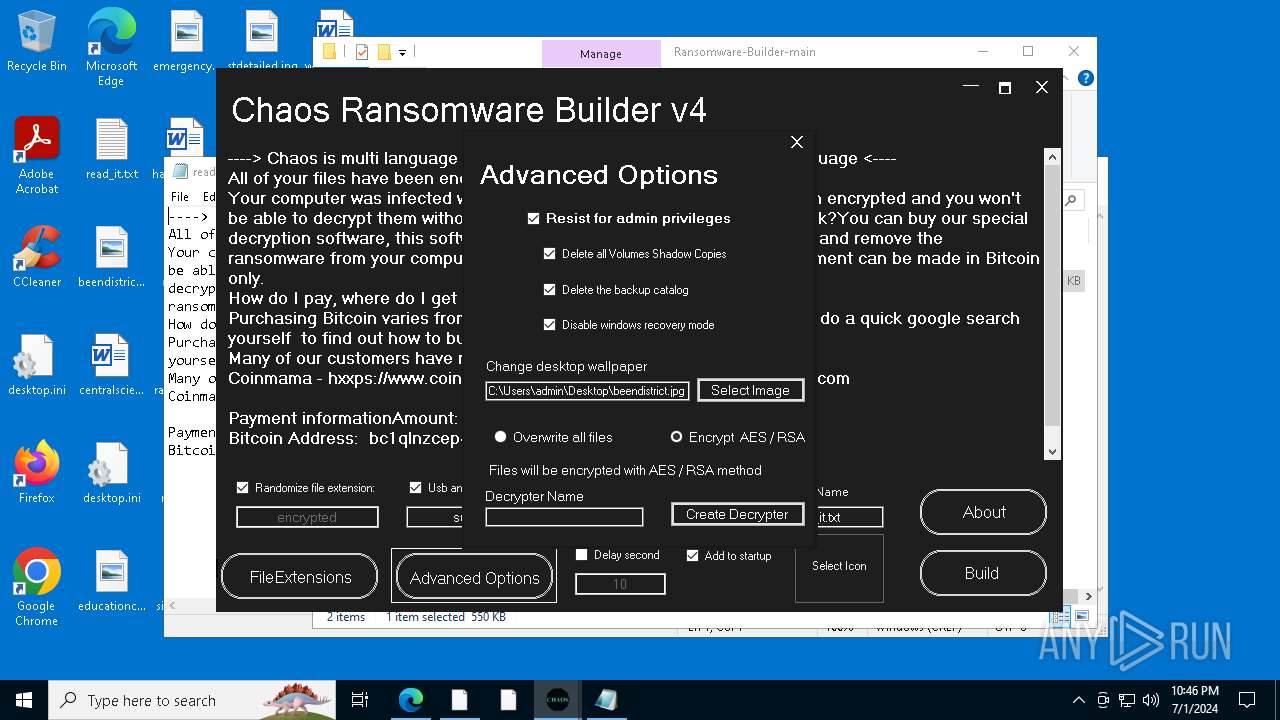
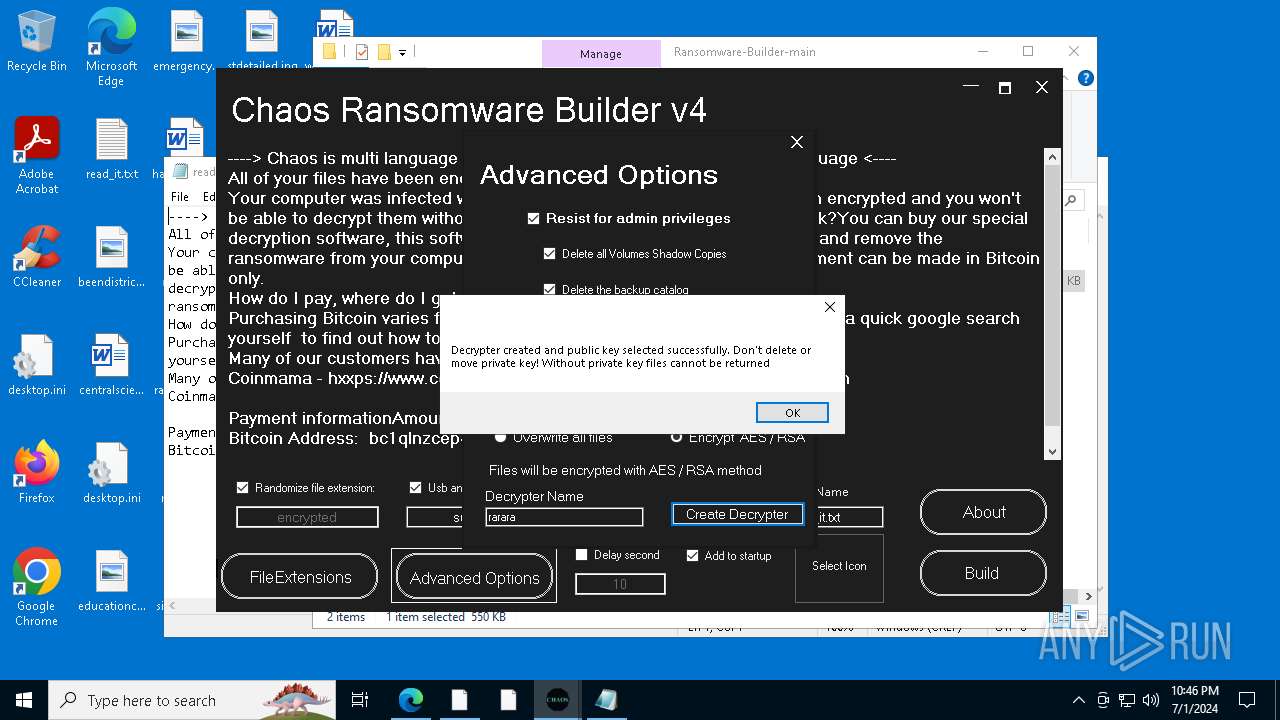
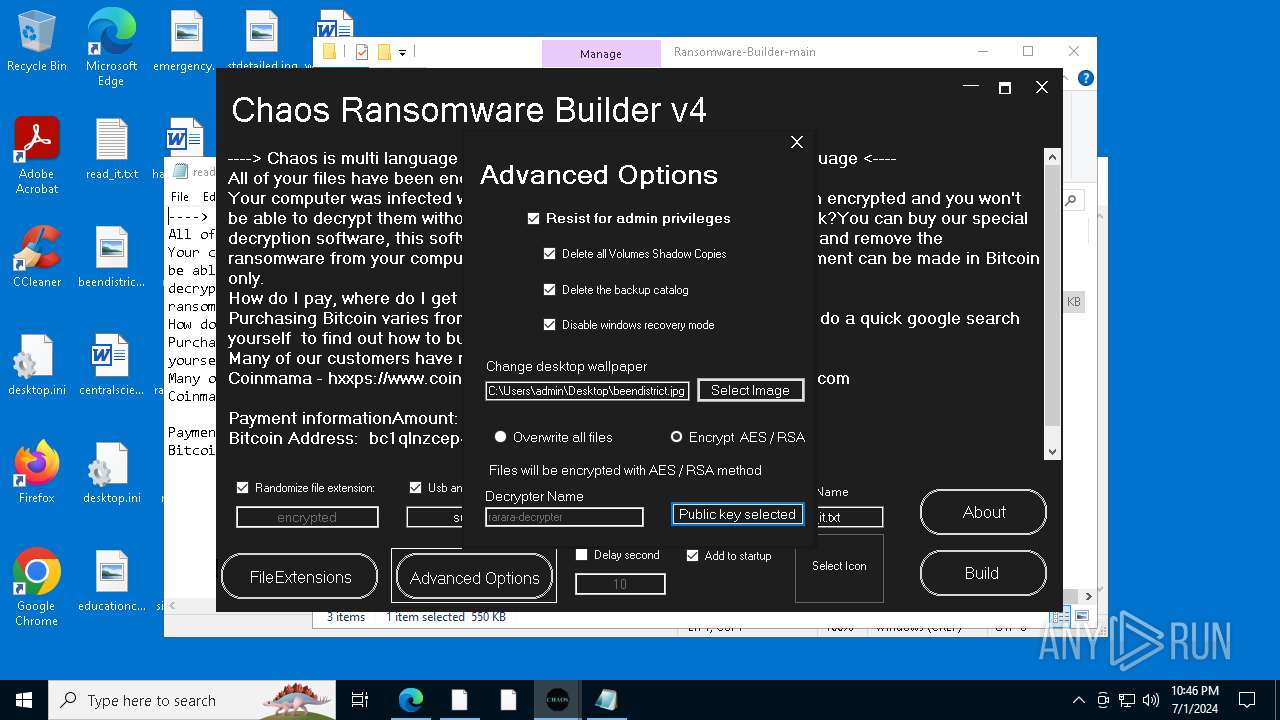
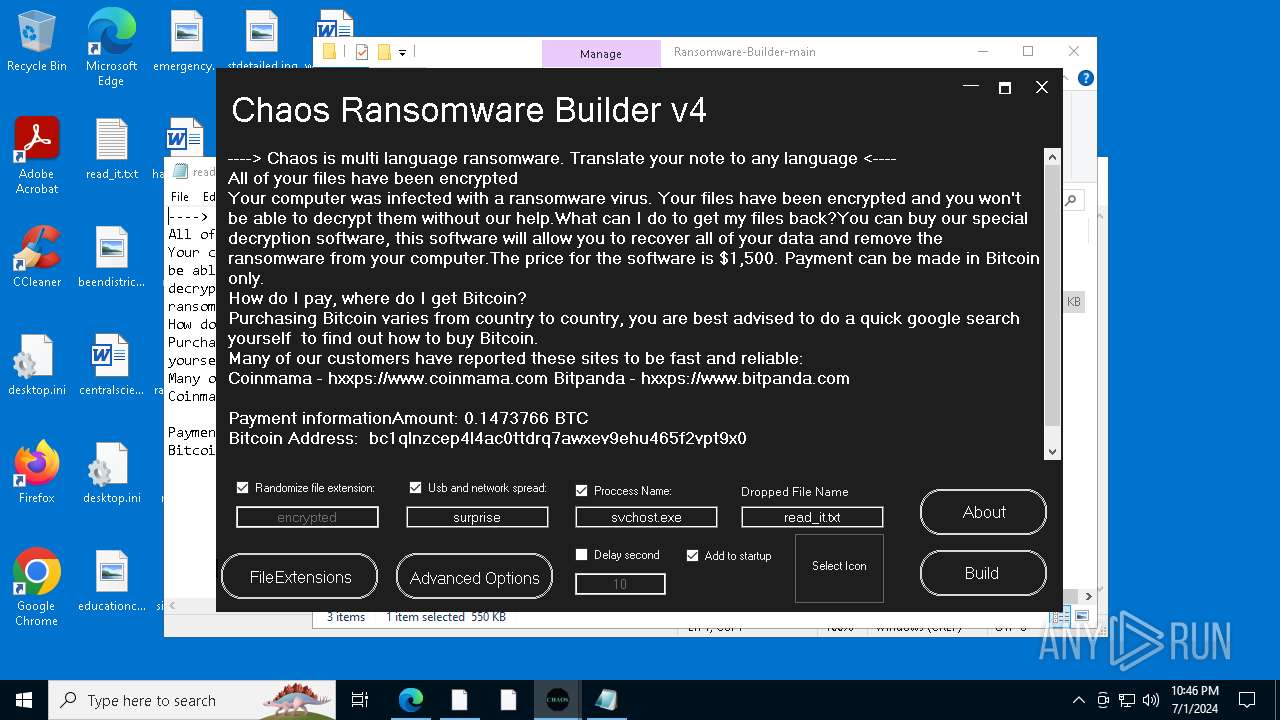
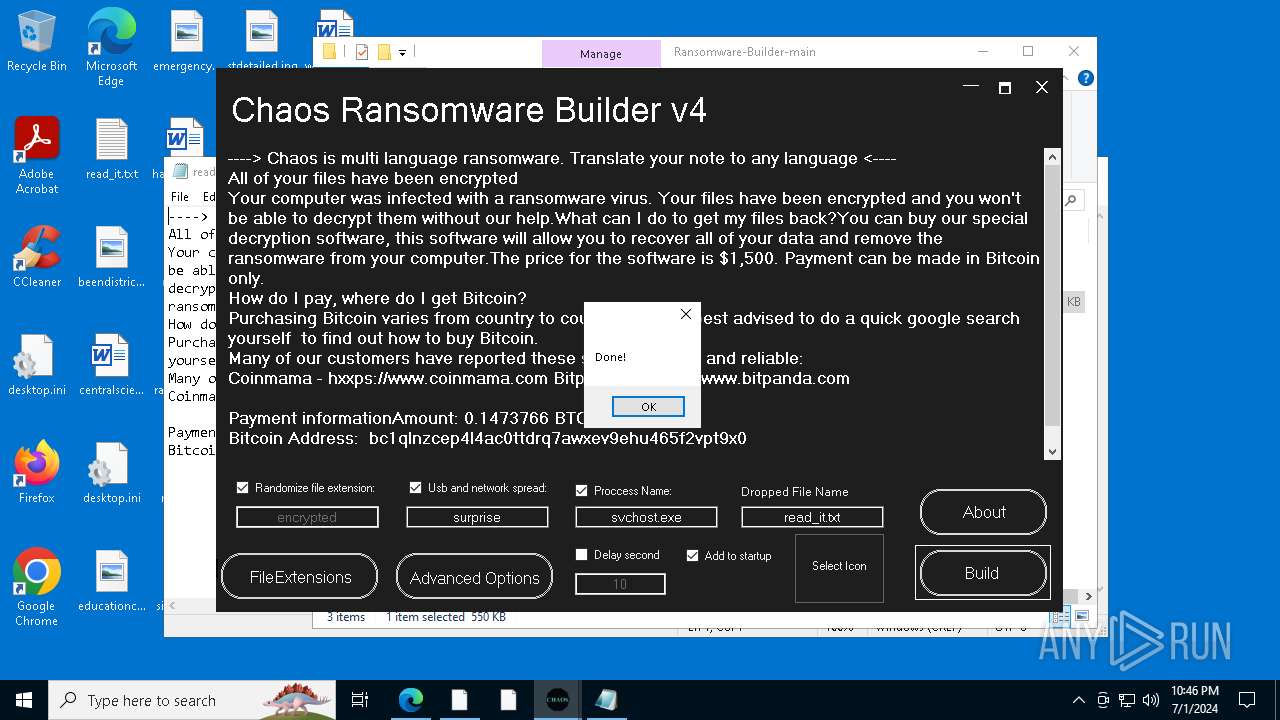
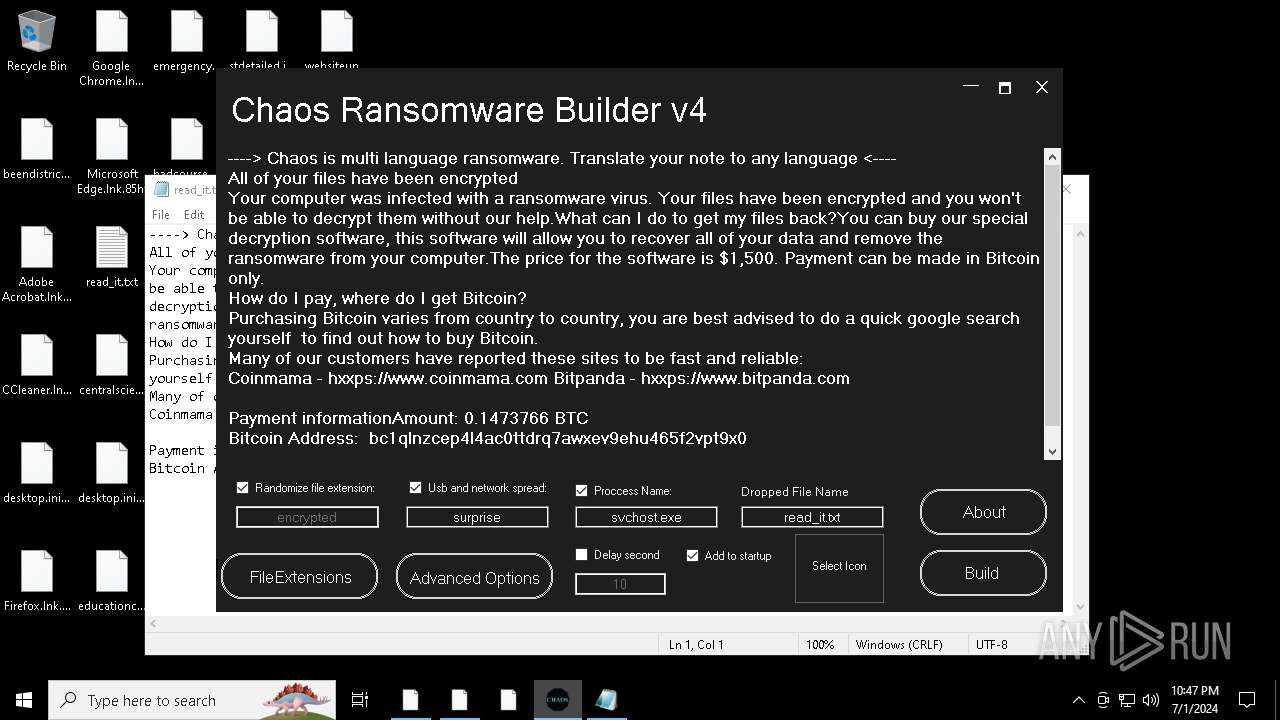
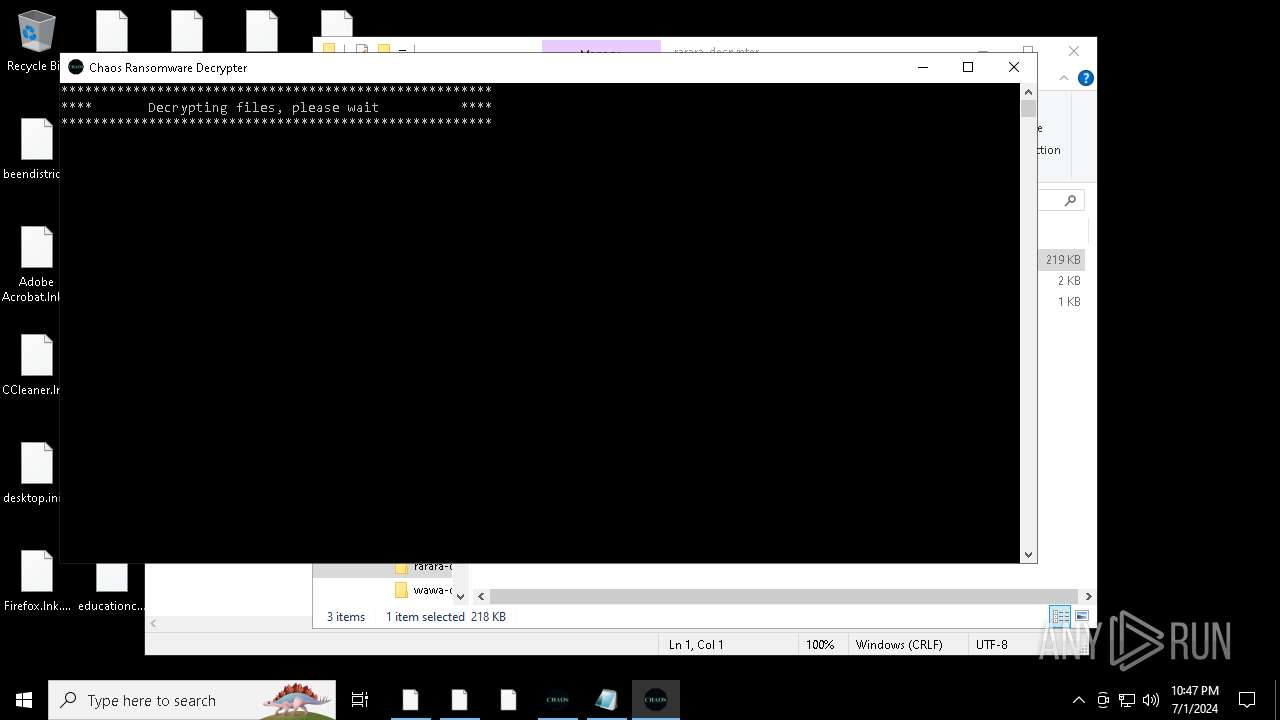
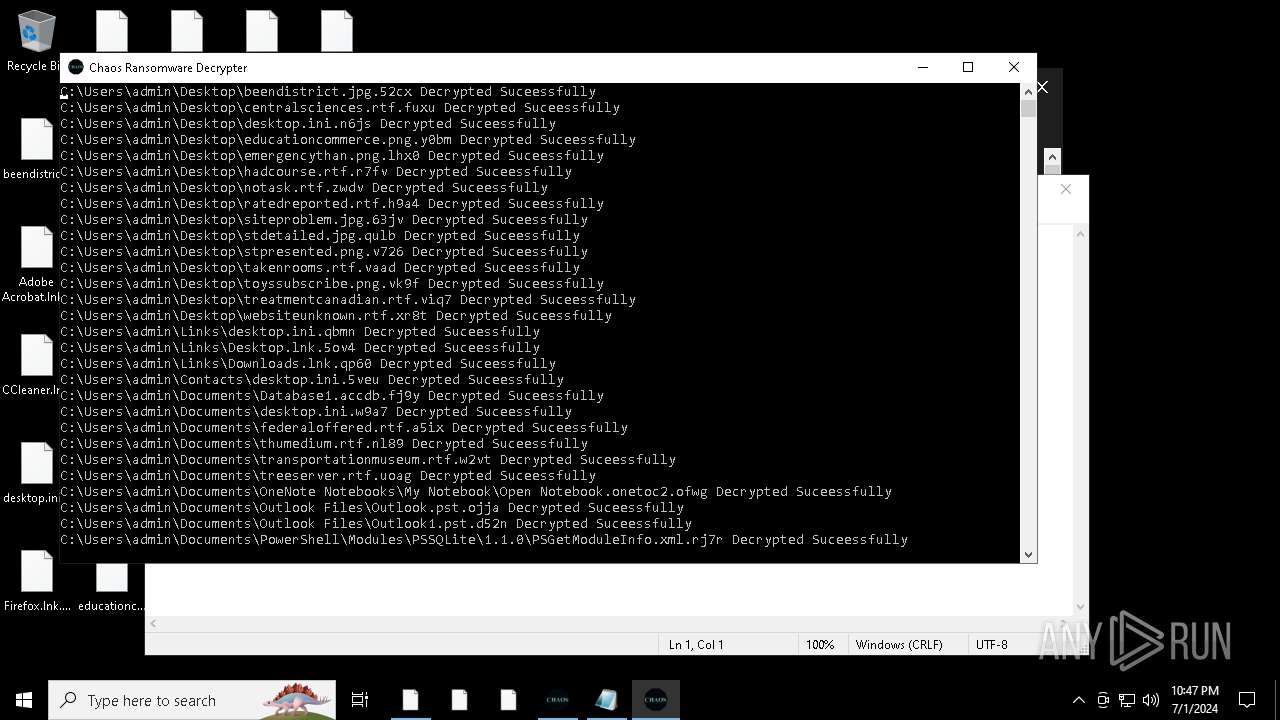
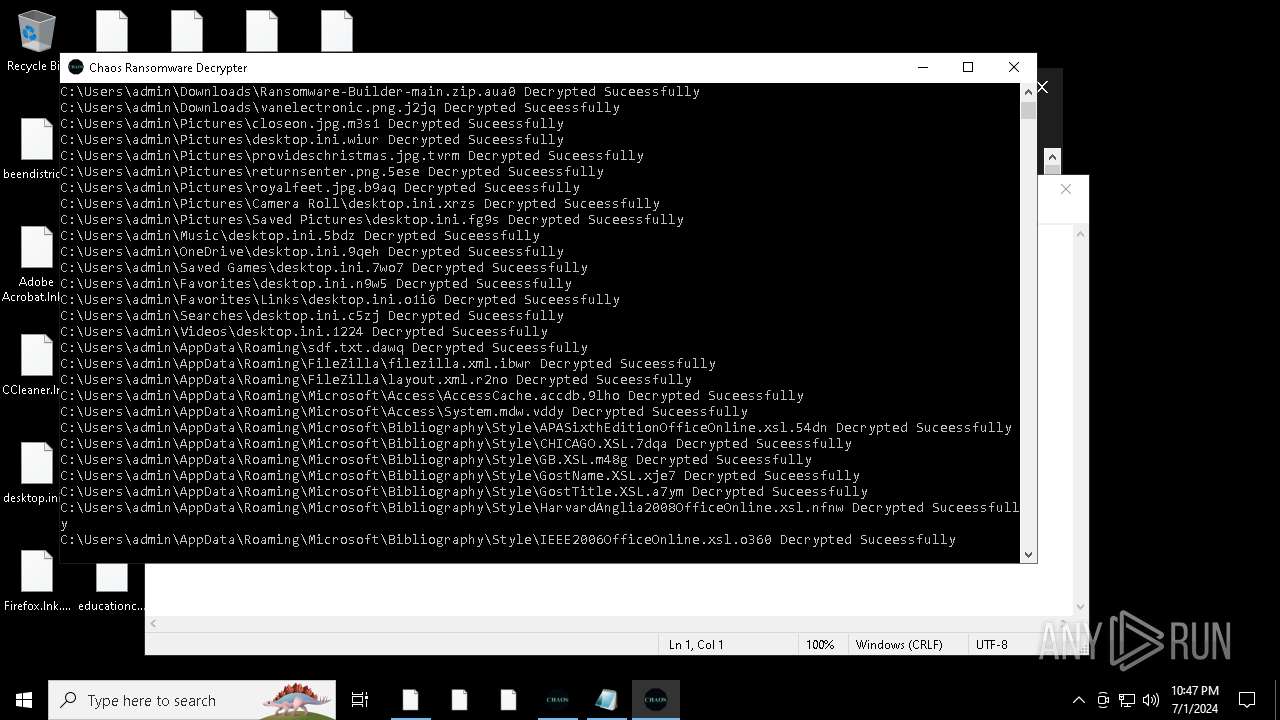
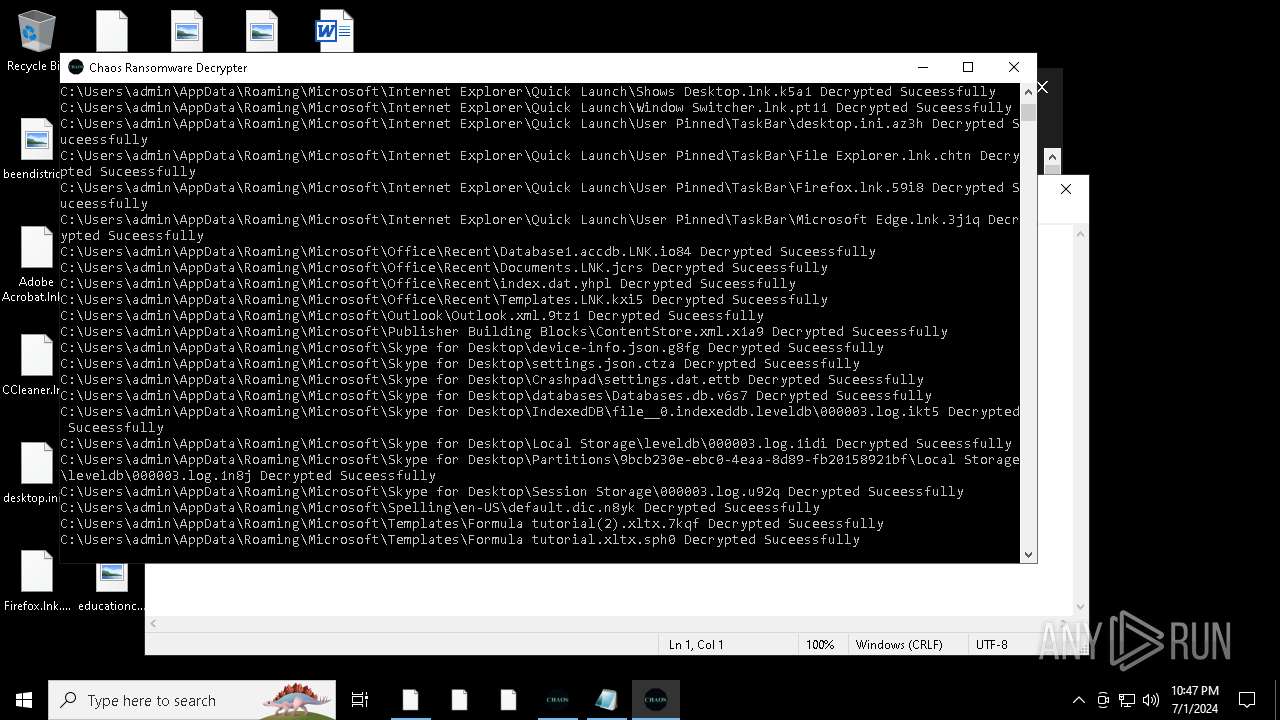
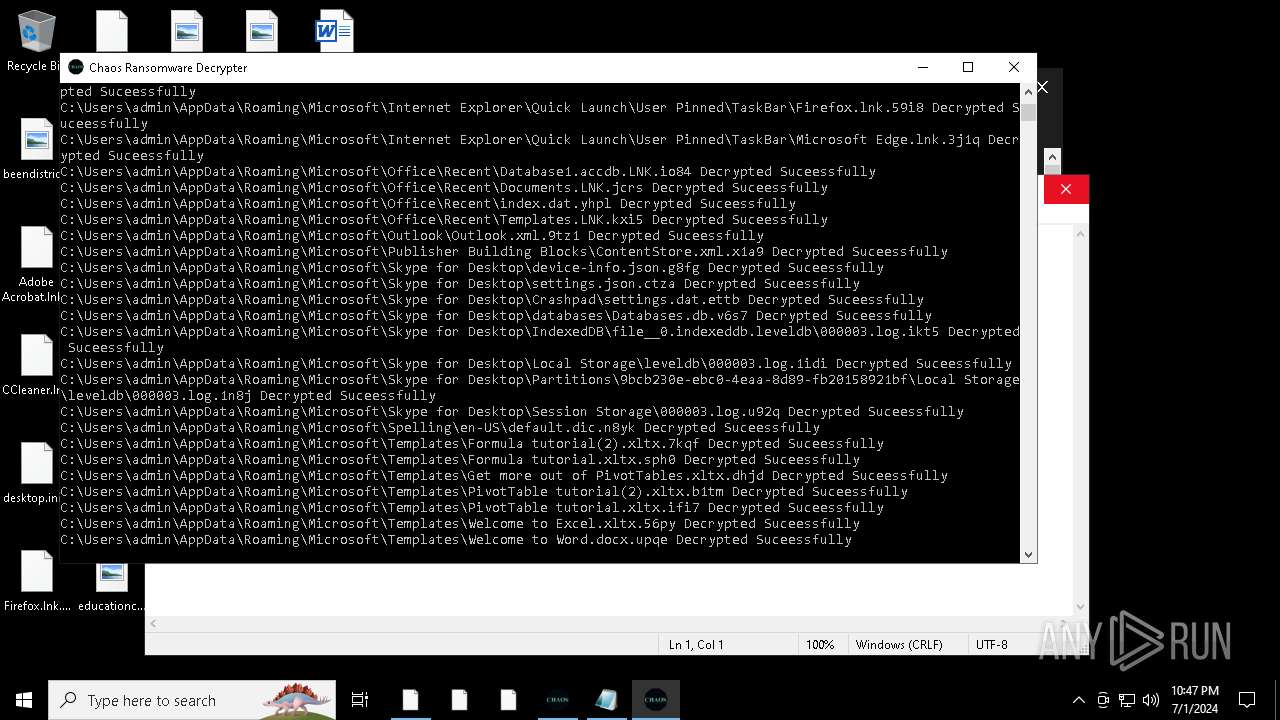
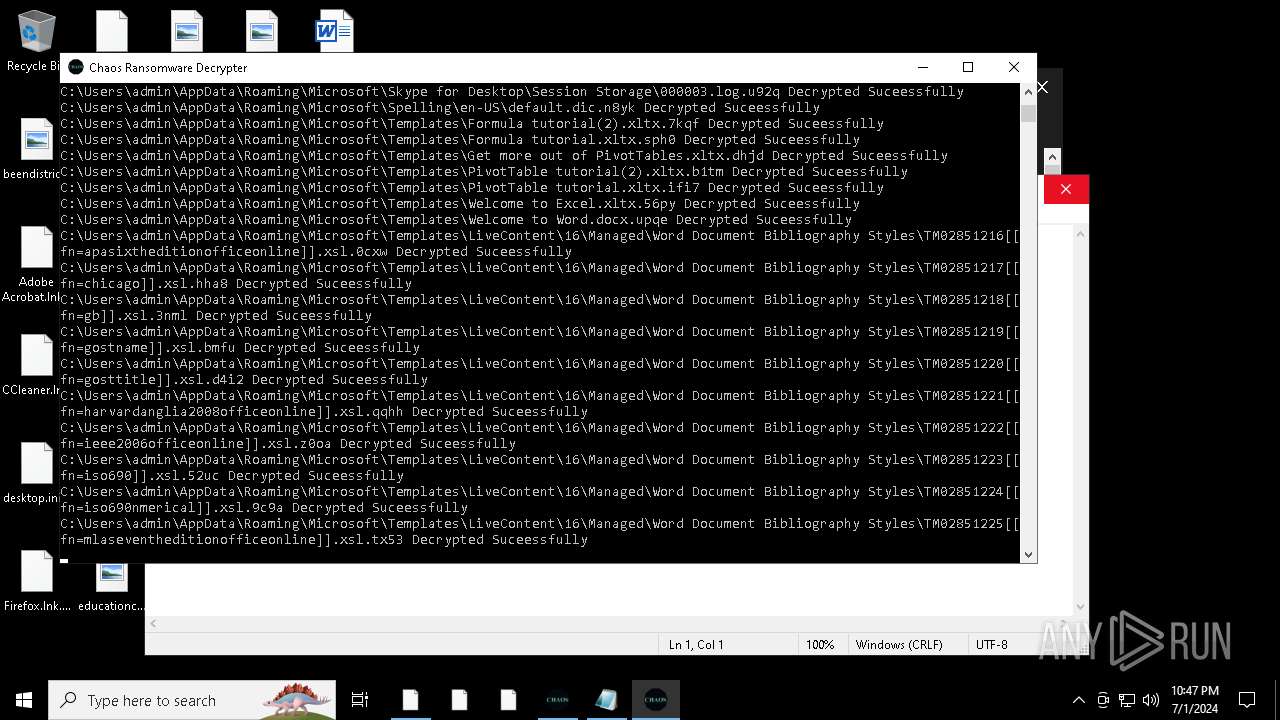
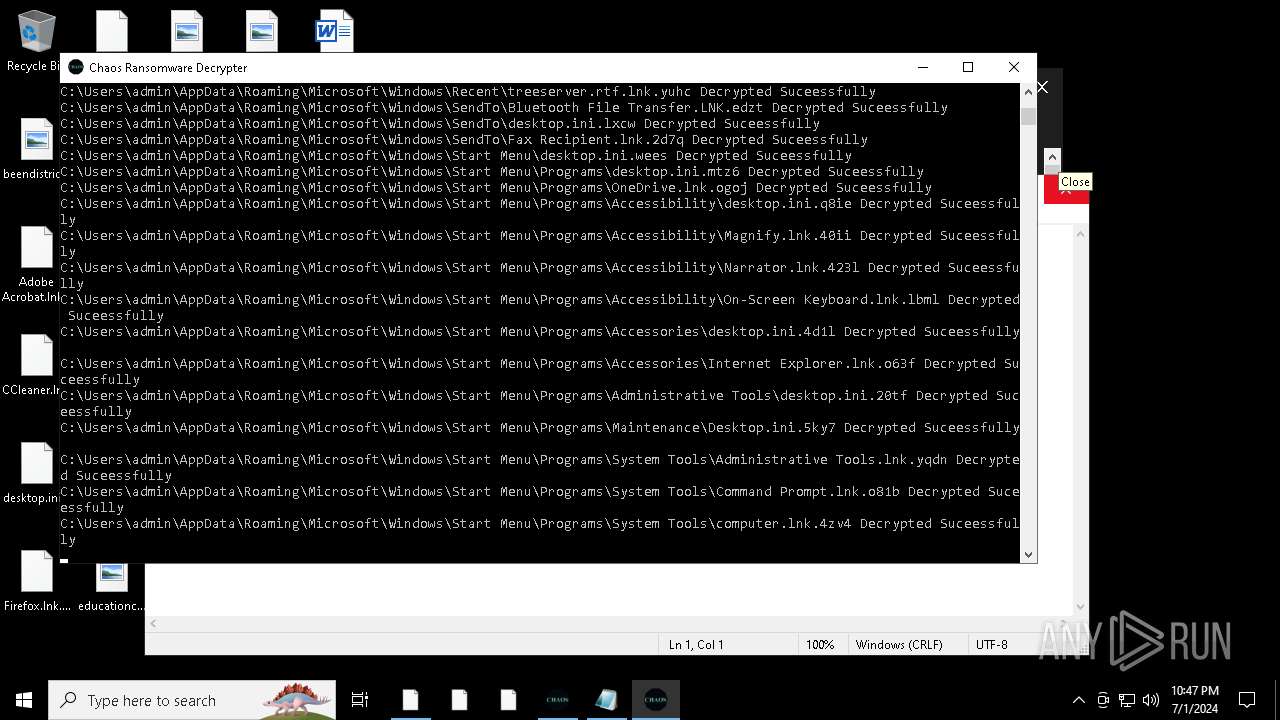
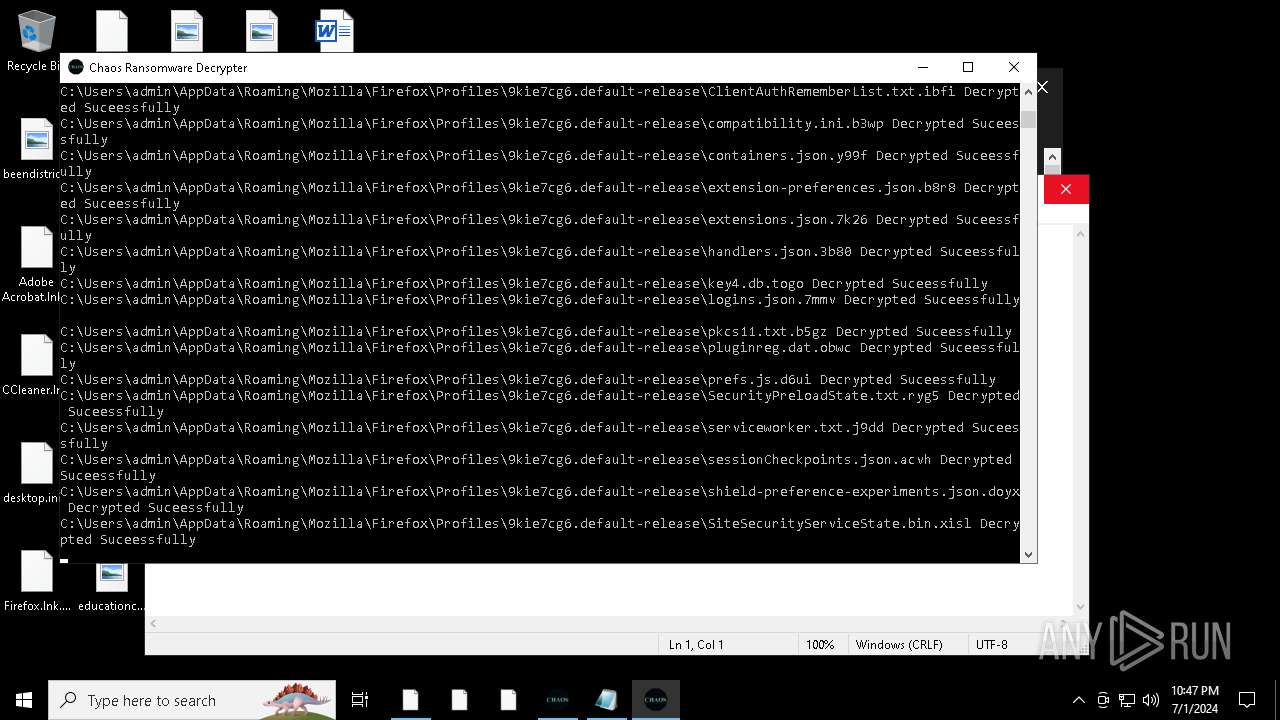
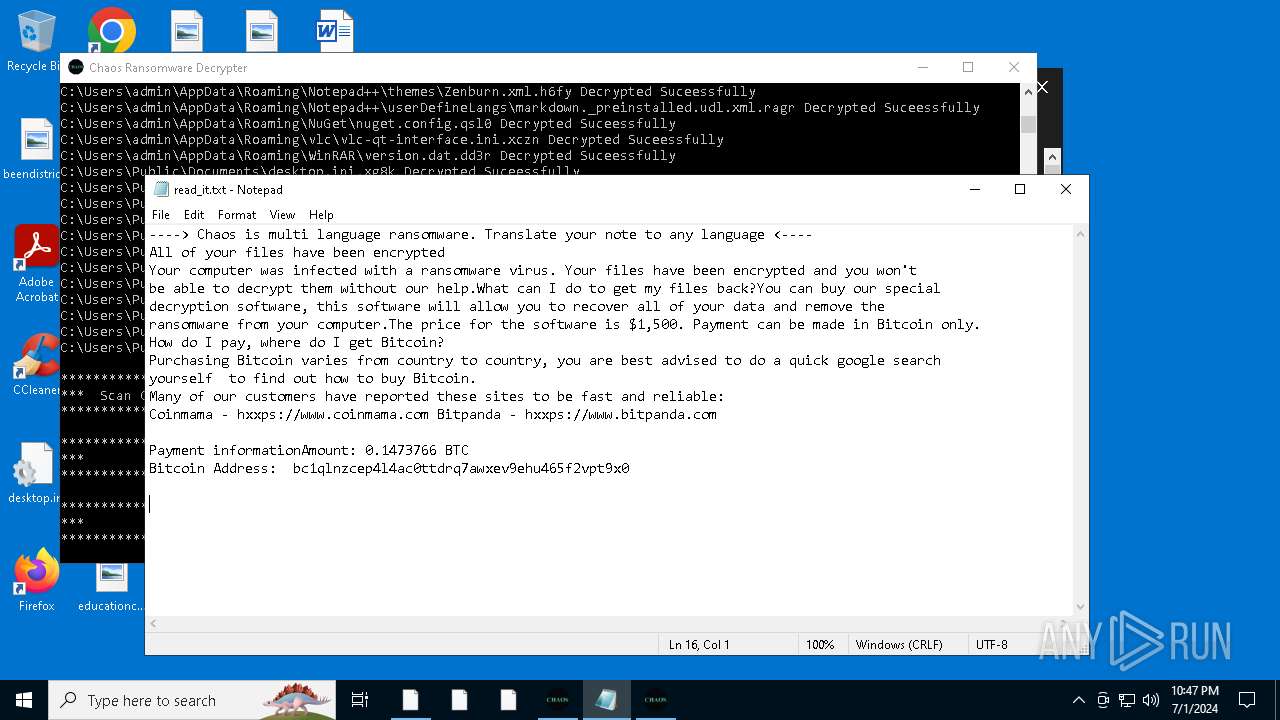
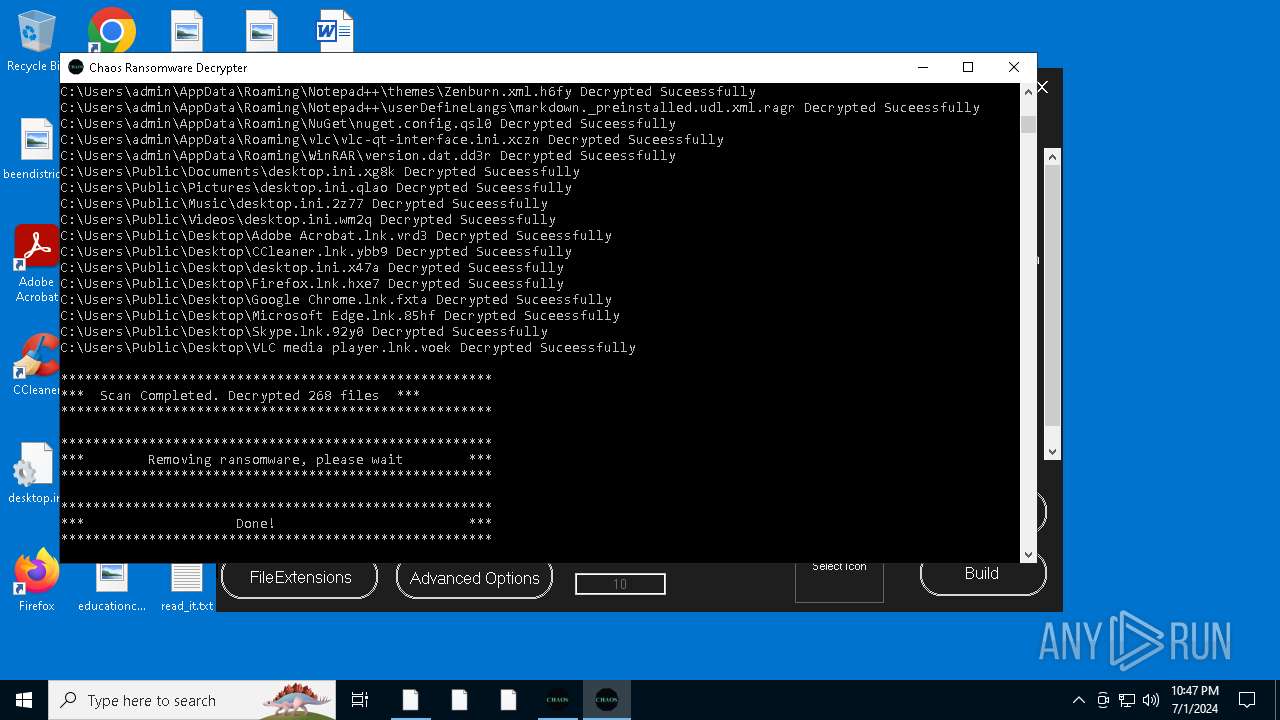
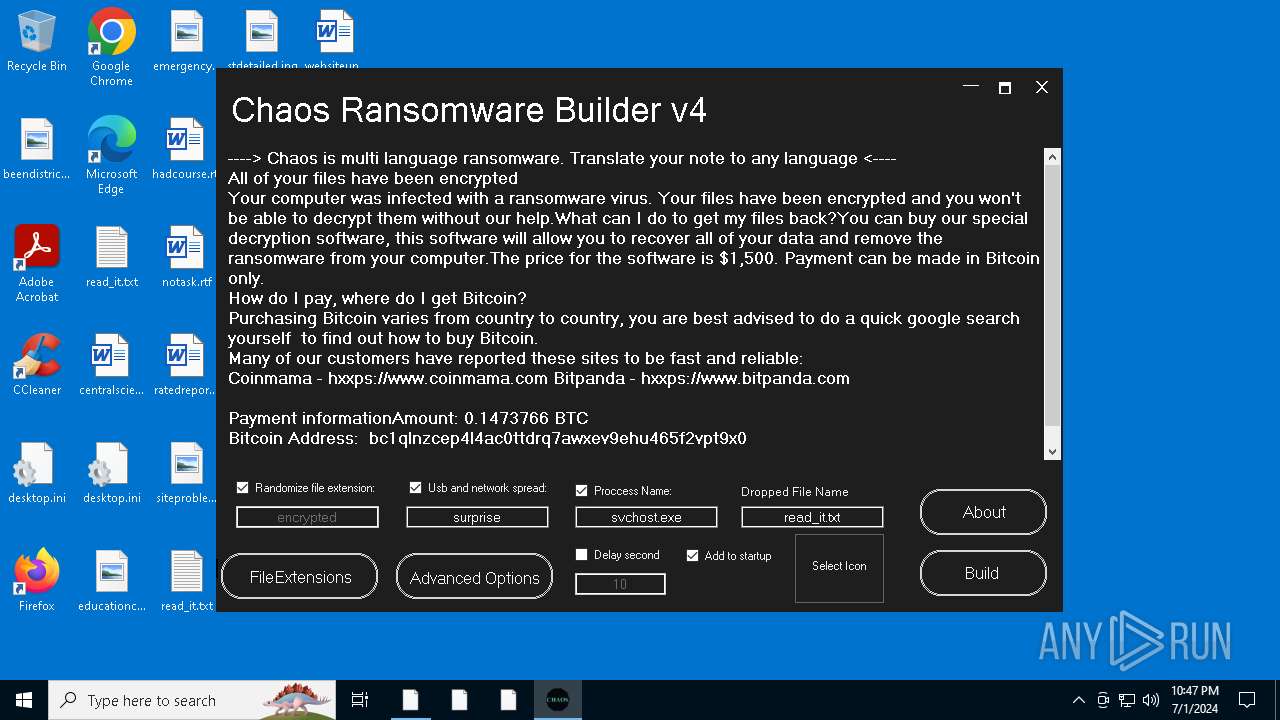
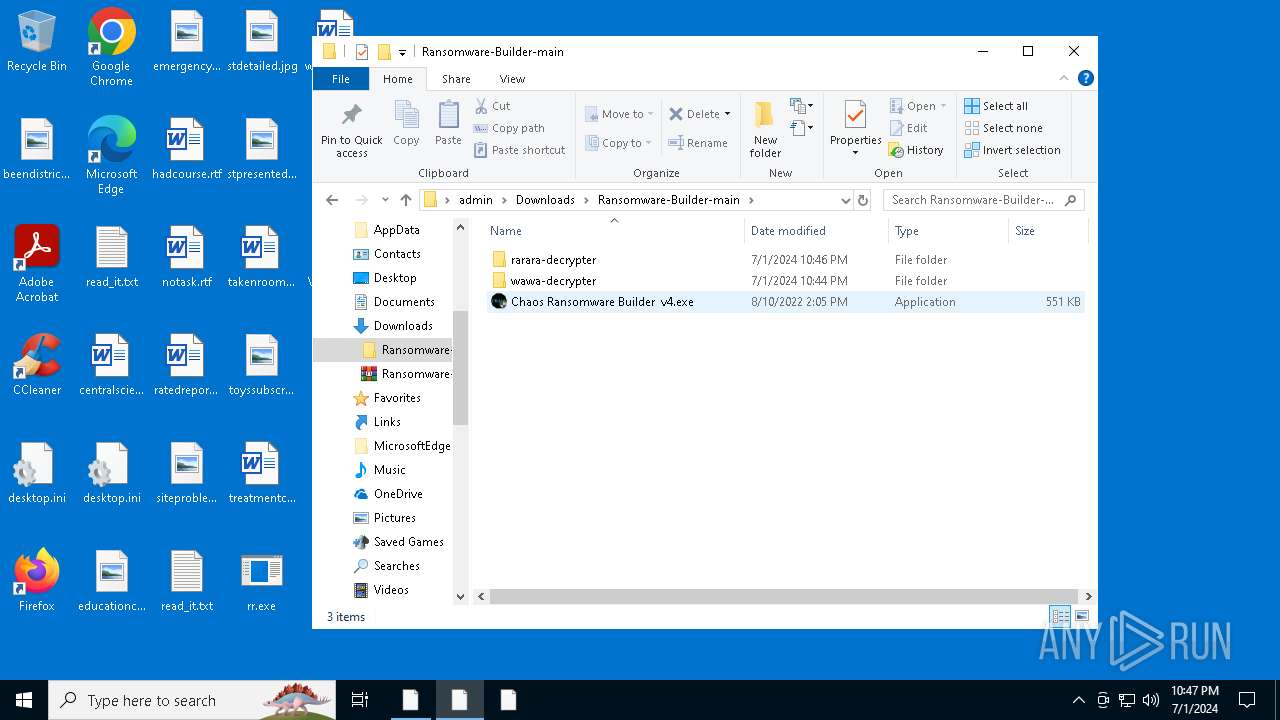
| Threats: | Chaos ransomware is a malware family known for its destructive capabilities and diverse variants. It first appeared in 2021 as a ransomware builder and later acted as a wiper. Unlike most ransomware strains that encrypt data to extort payment, early Chaos variants permanently corrupted files, while later versions adopted more conventional encryption techniques. |
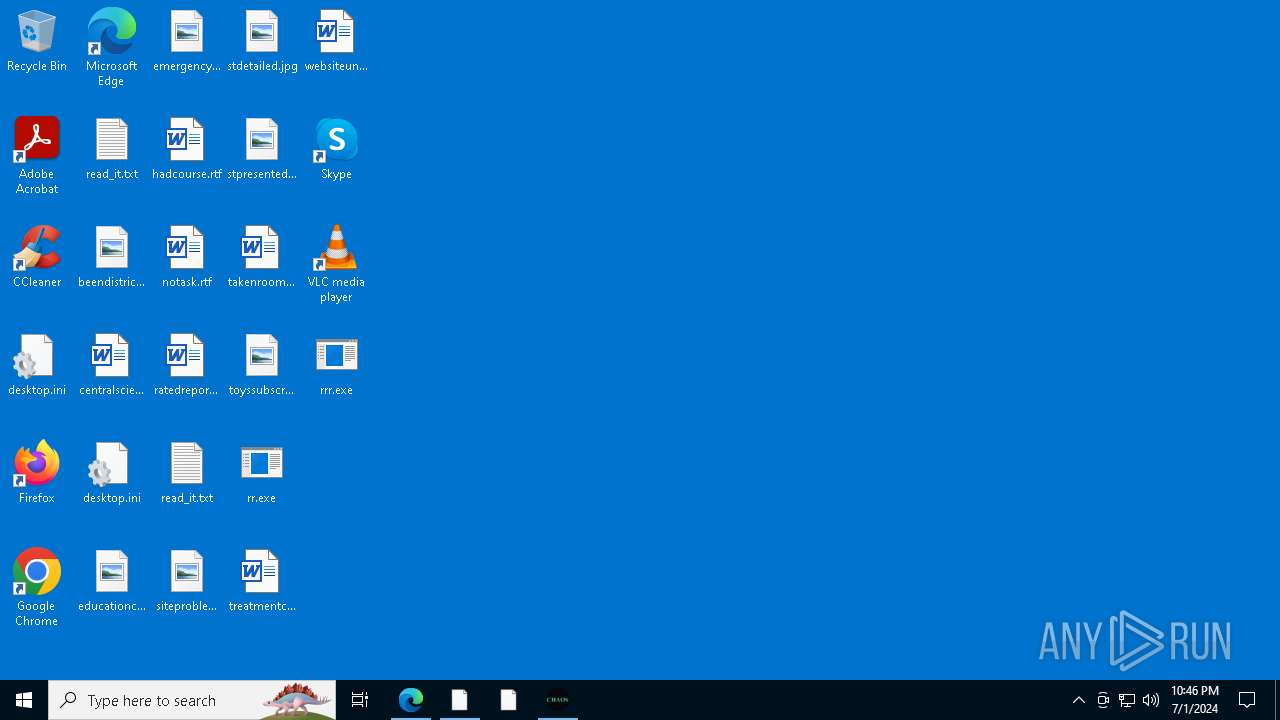
| Analysis date: | July 01, 2024, 22:43:57 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | B89B4B4E3AA771DD4EE4CCAFCAD02403 |
| SHA1: | 4B75D218A2704B5DD21D09AED7197795F715C442 |
| SHA256: | F8FA15042632899D957B930F15D0E5CE6AD4AABDDB89E4D4B091C9219684FFA7 |
| SSDEEP: | 3:N8tEdRZf1znJBAbp:2uFfhnAp |
MALICIOUS
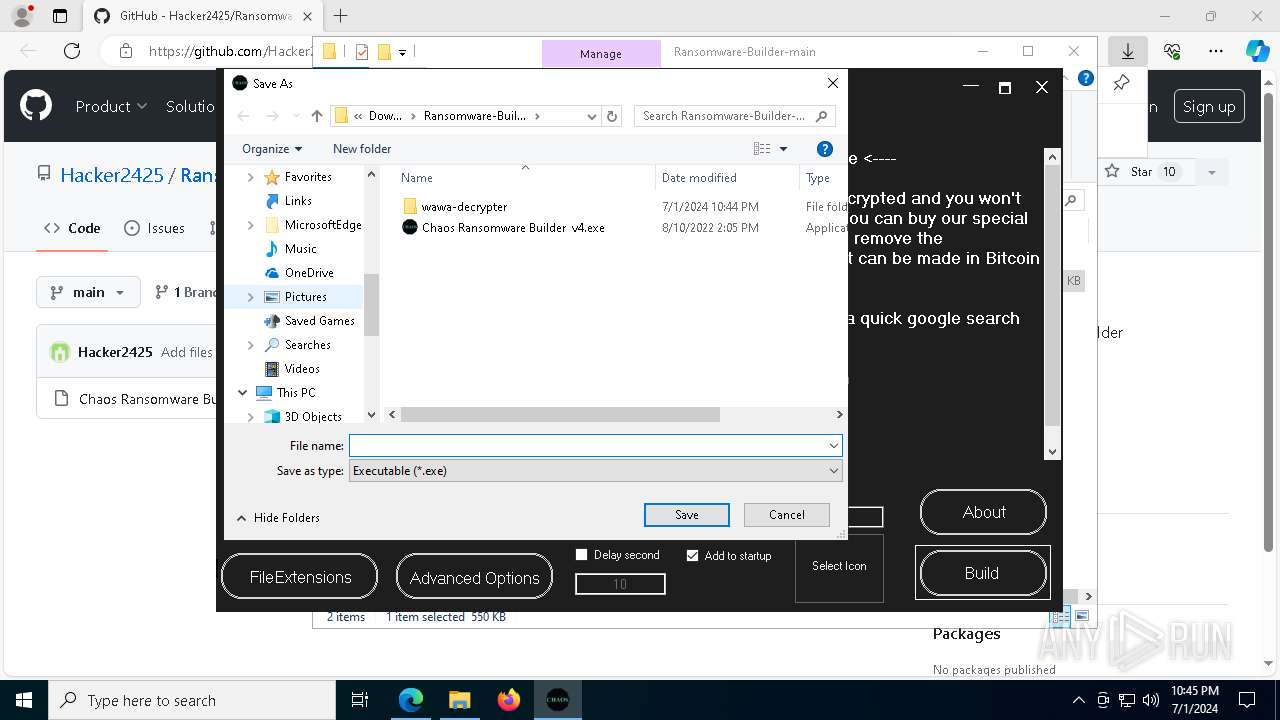
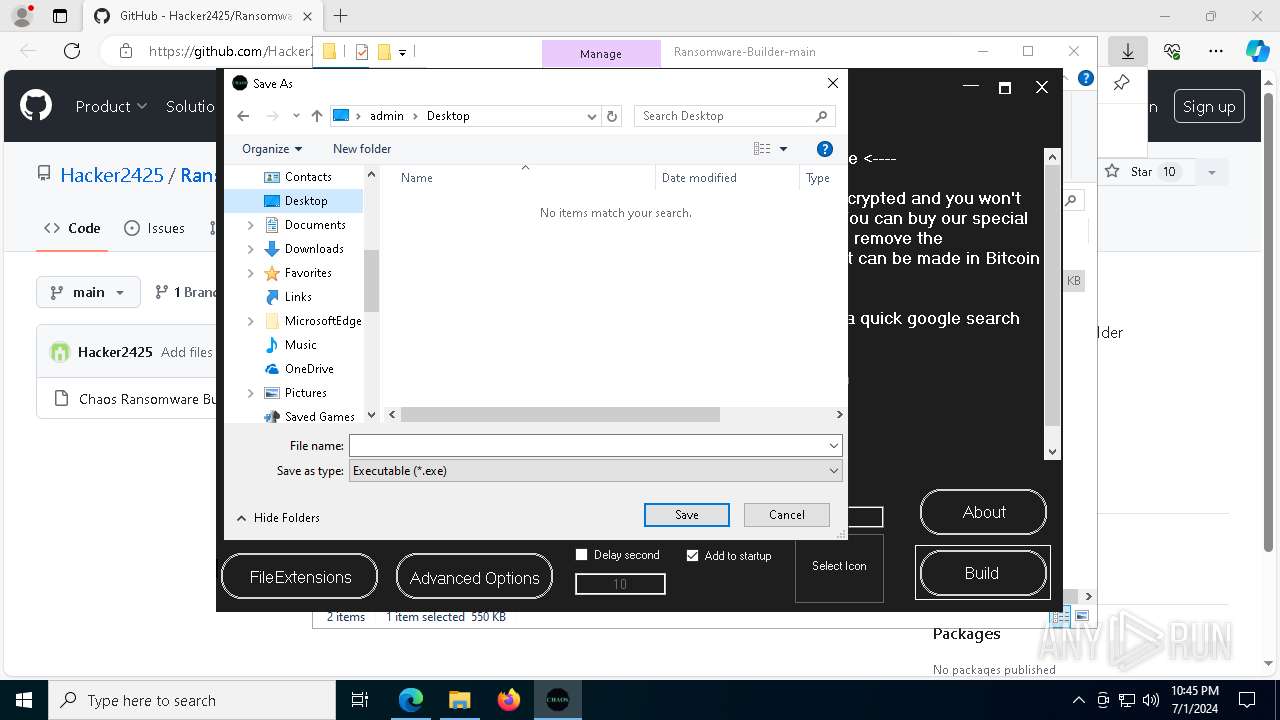
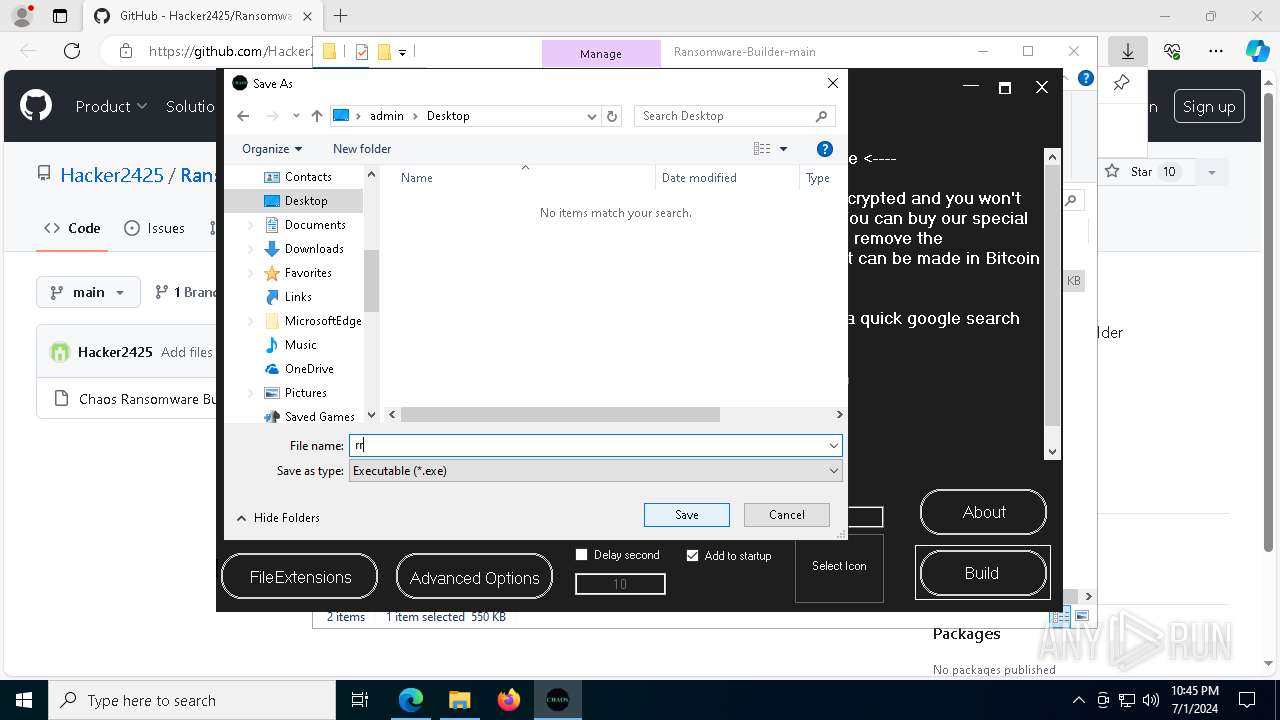
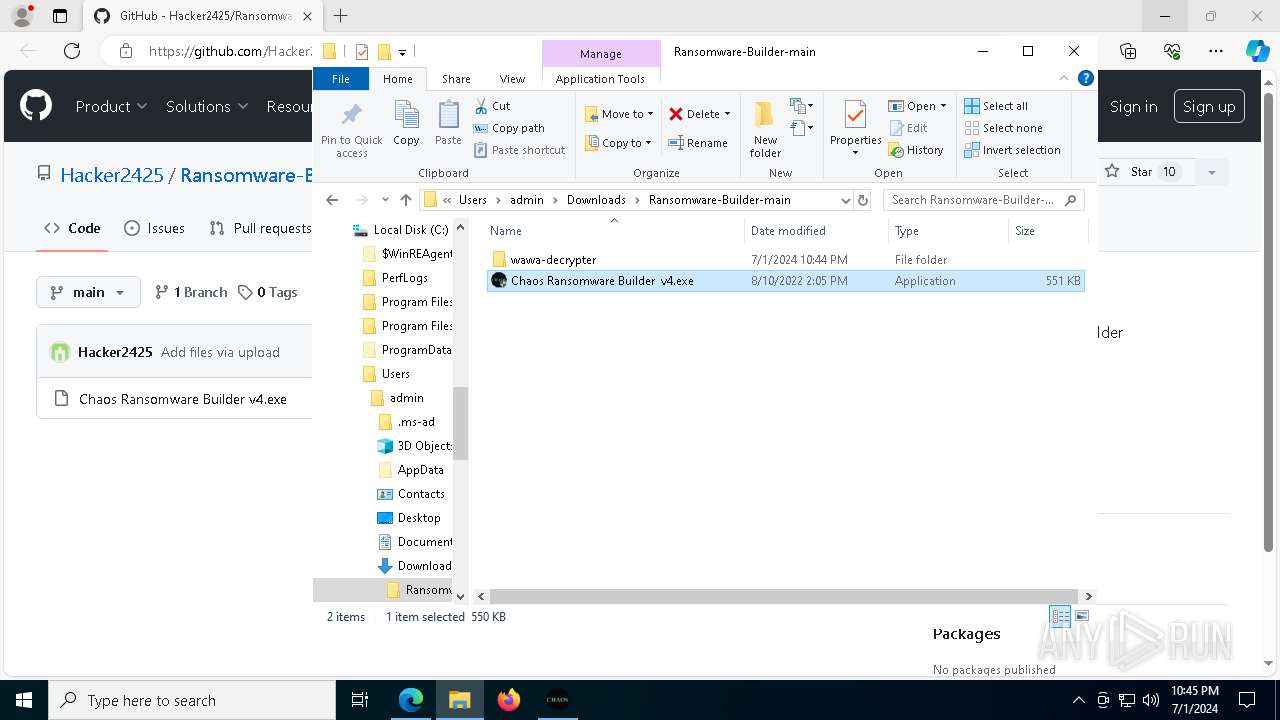
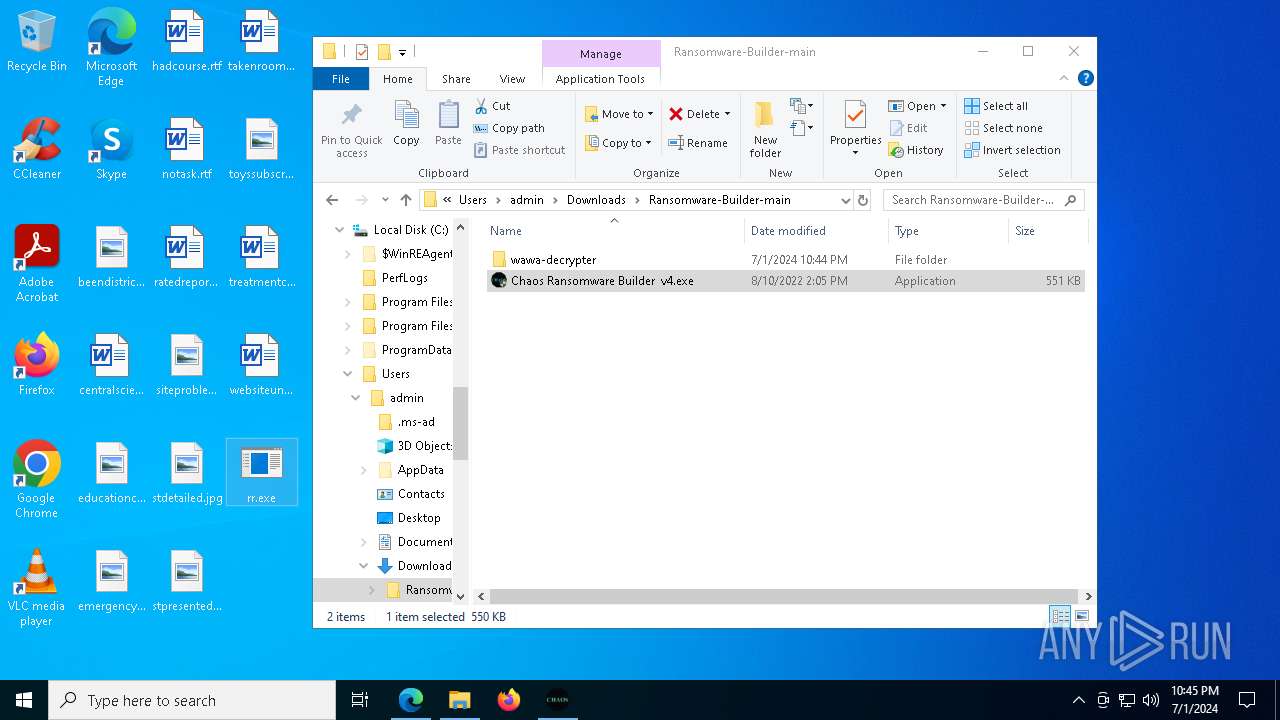
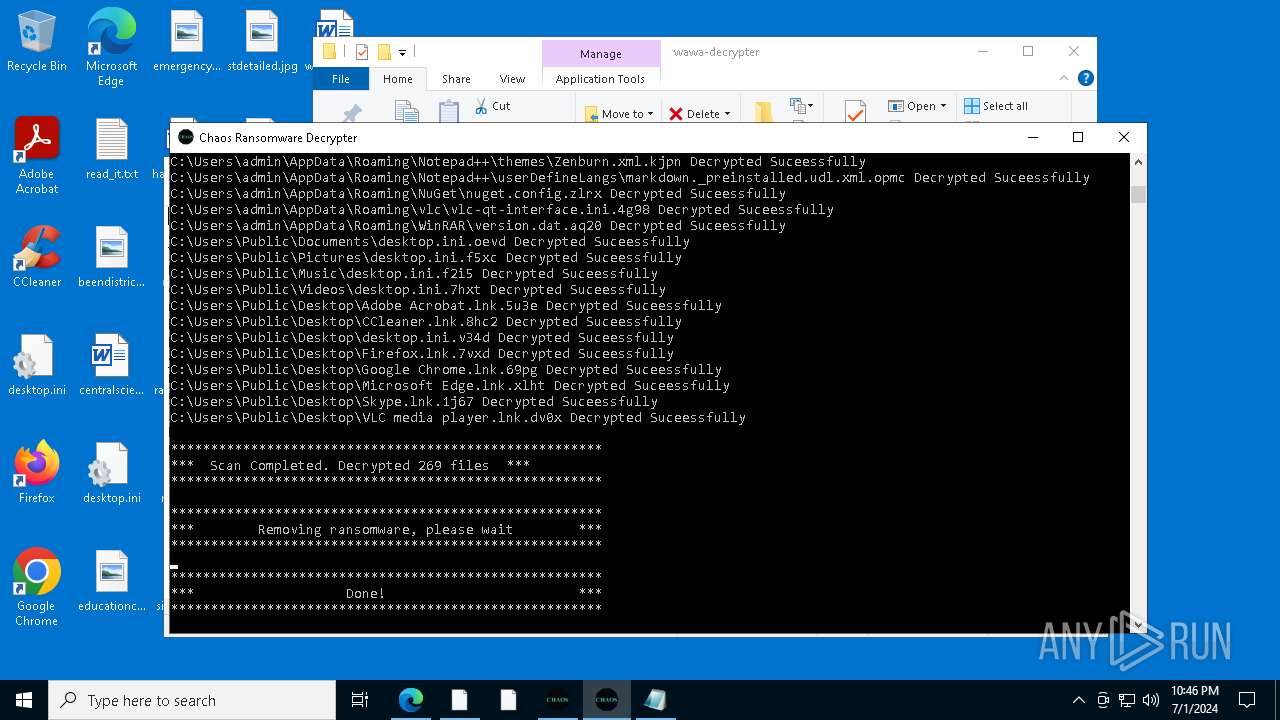
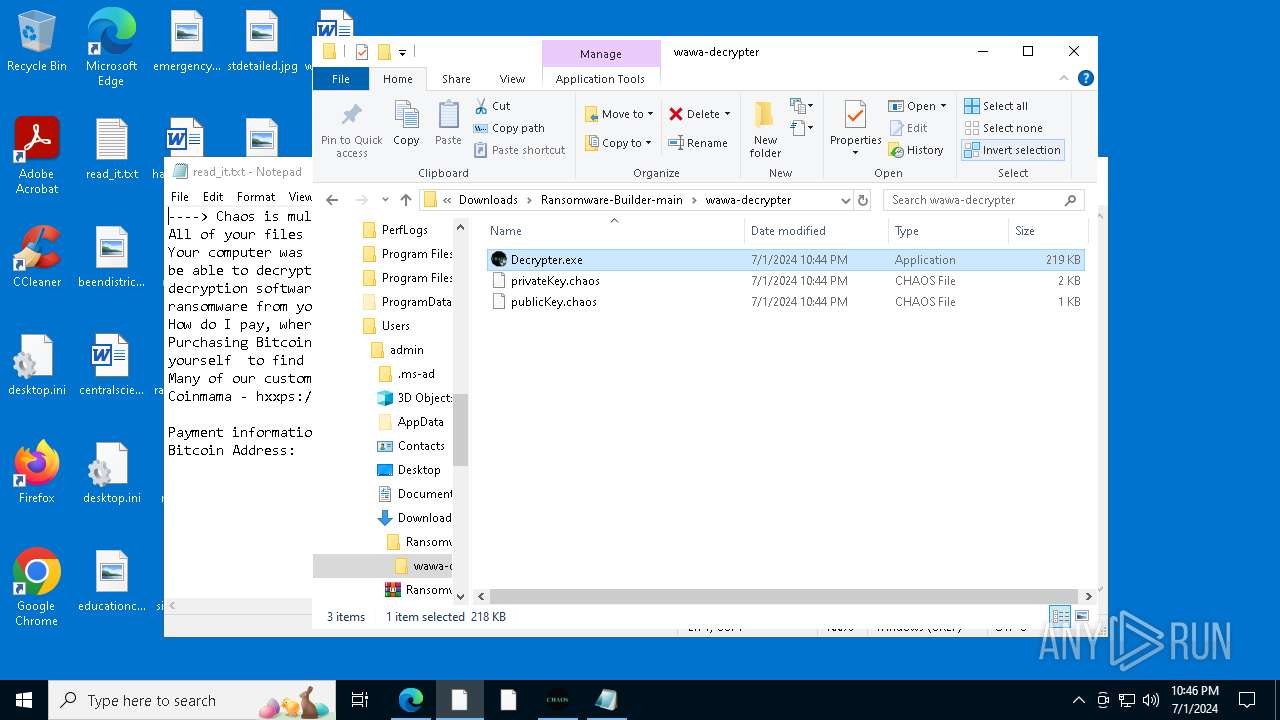
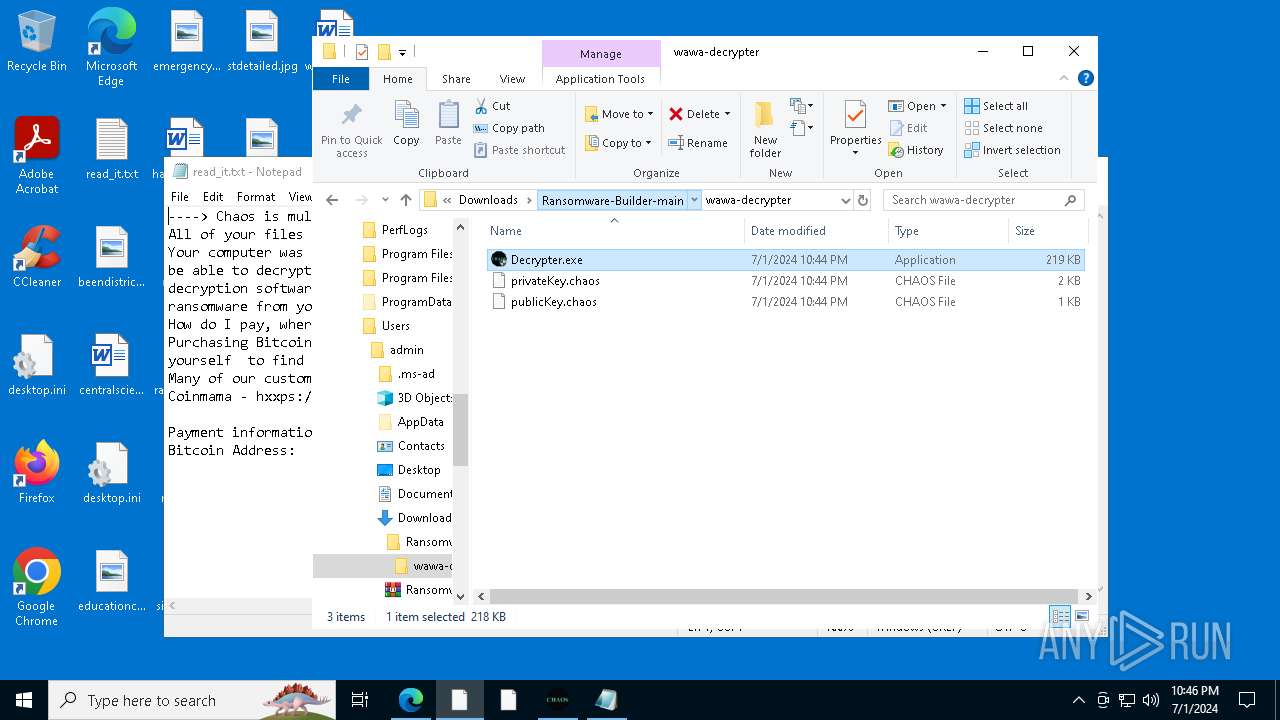
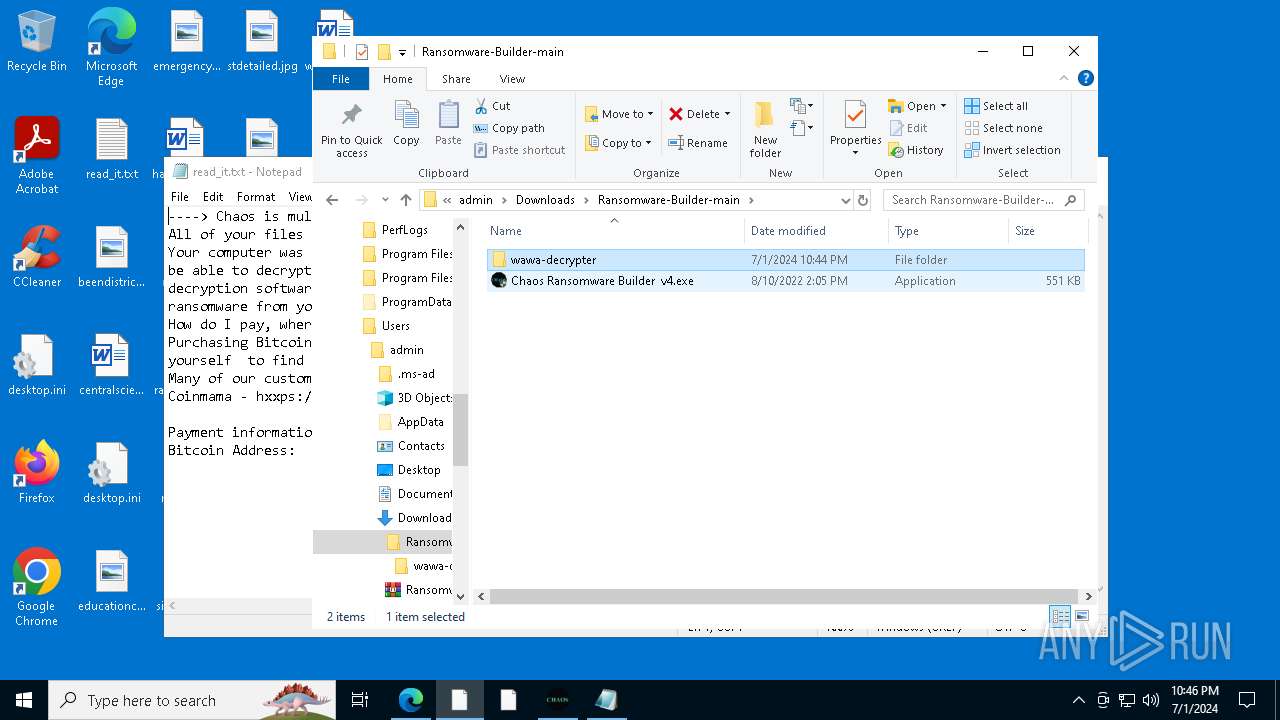
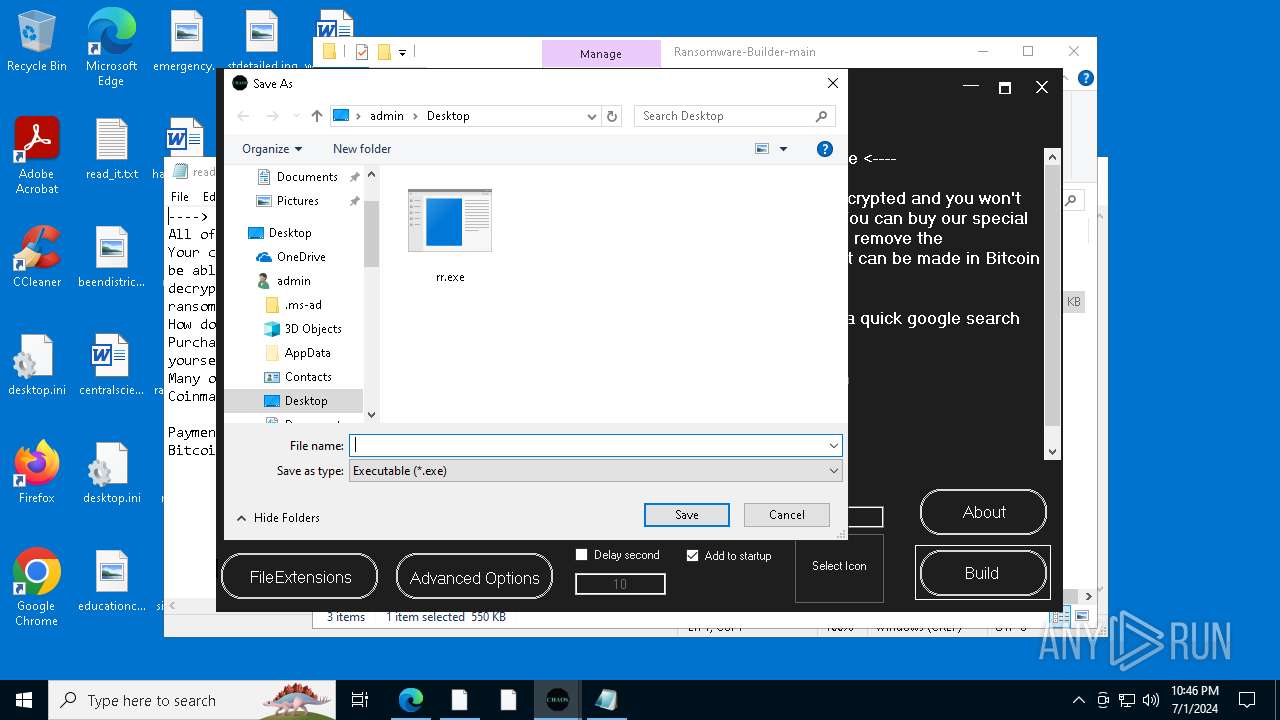
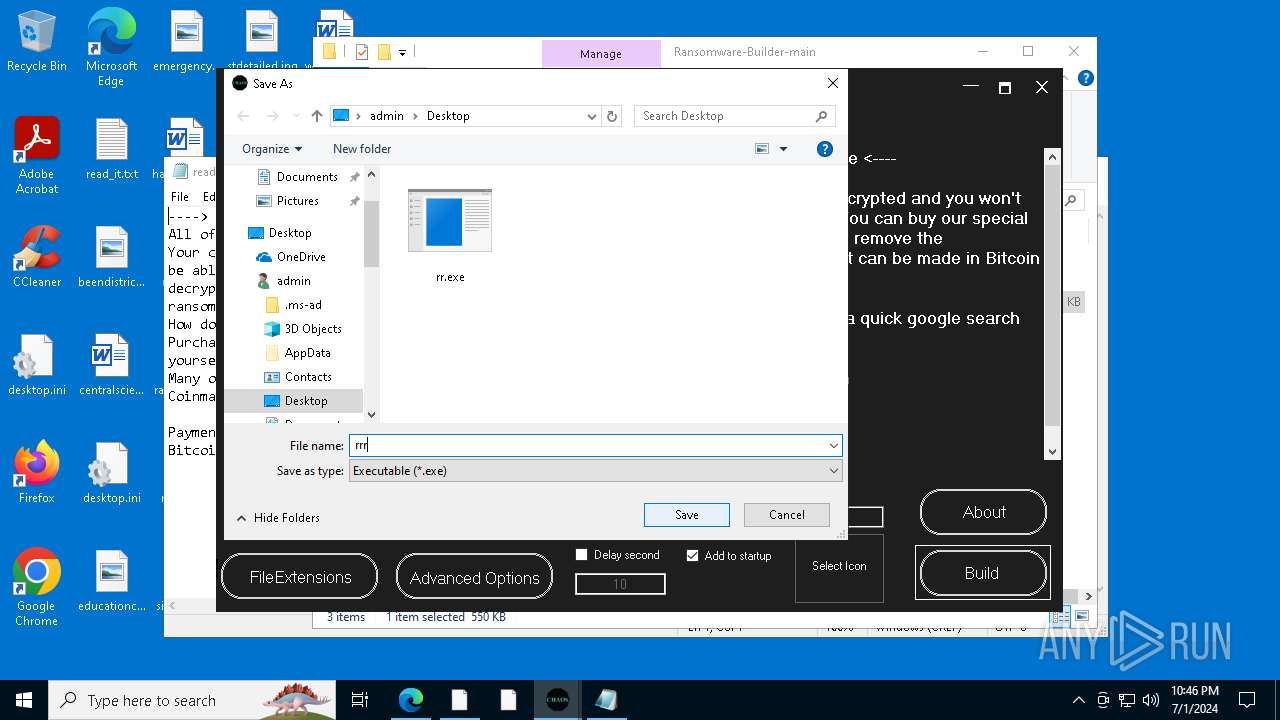
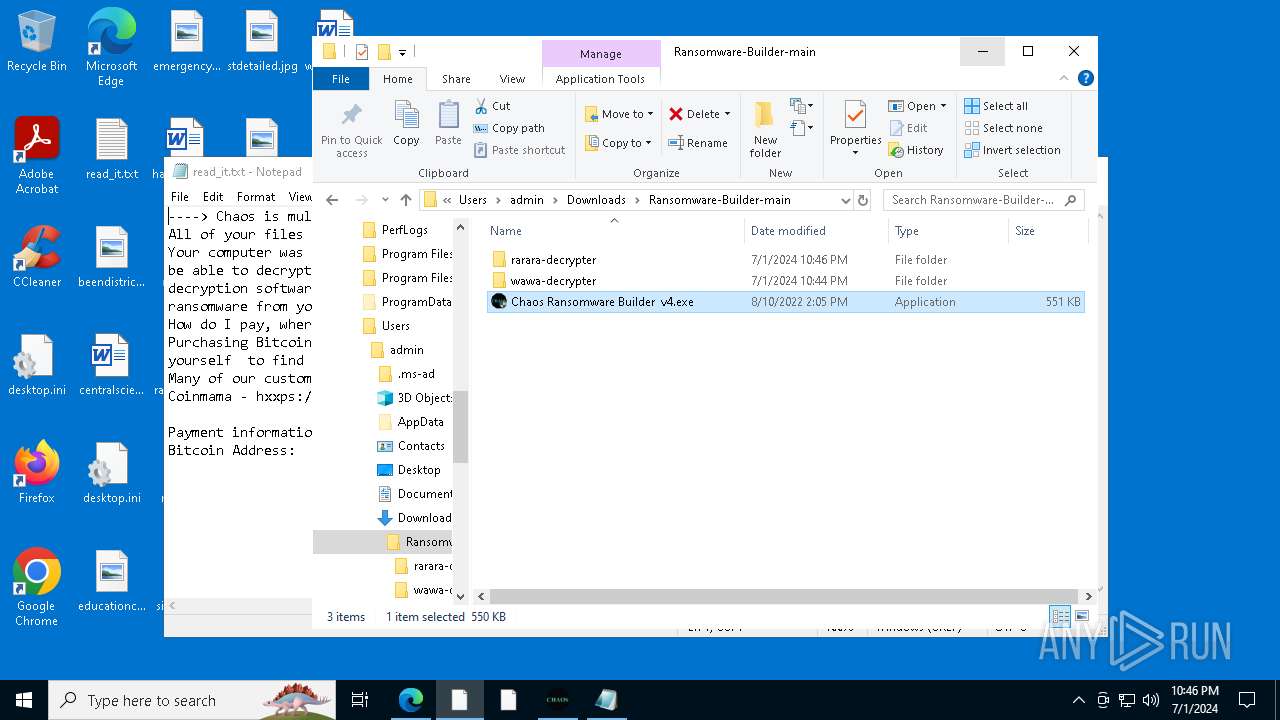
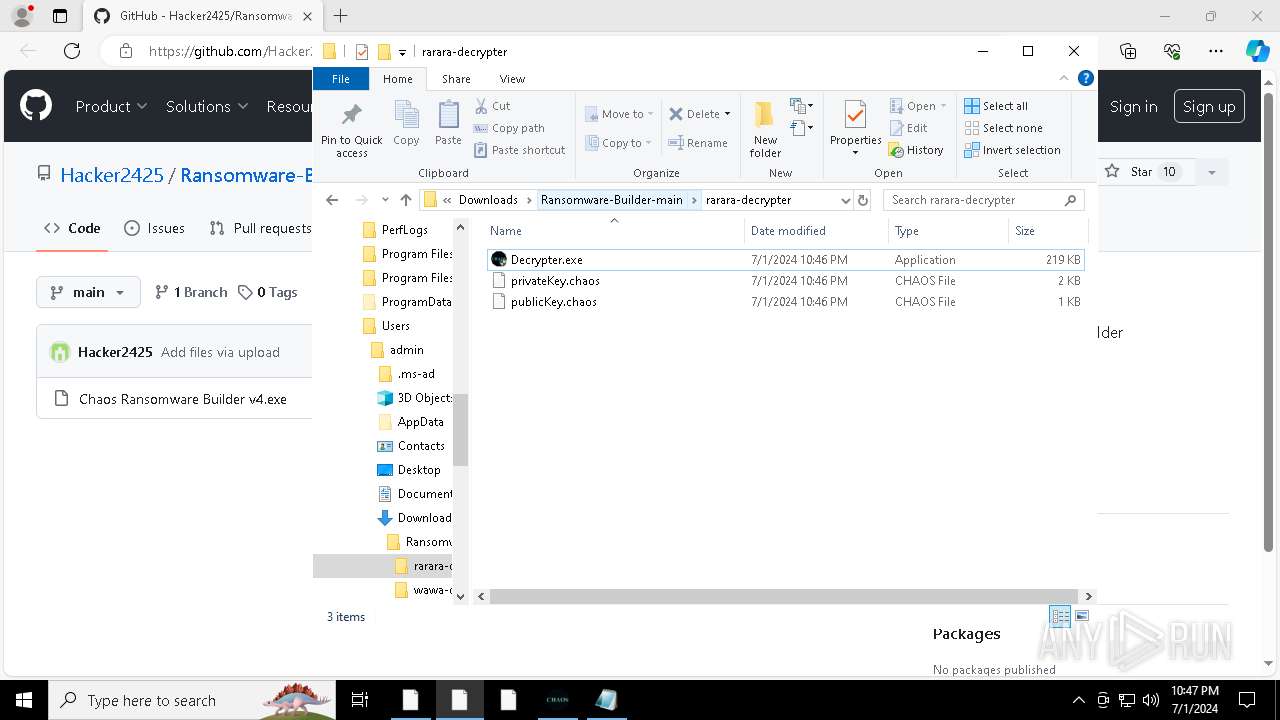
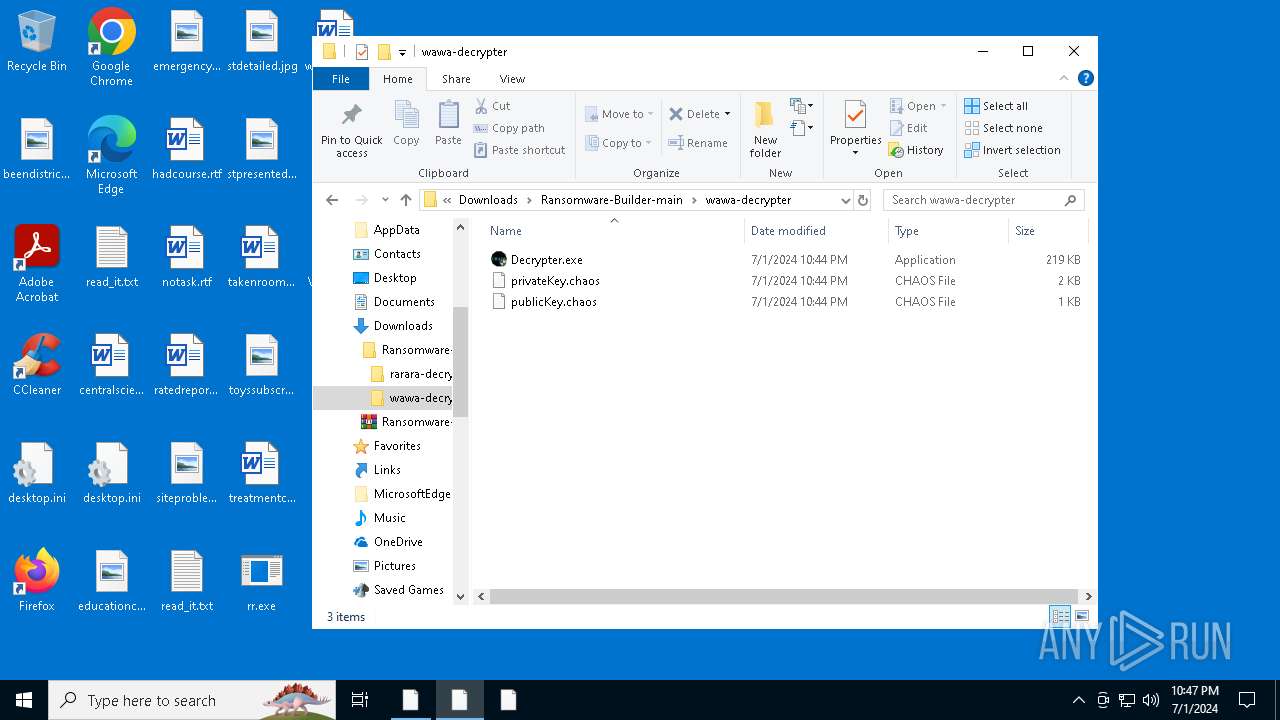
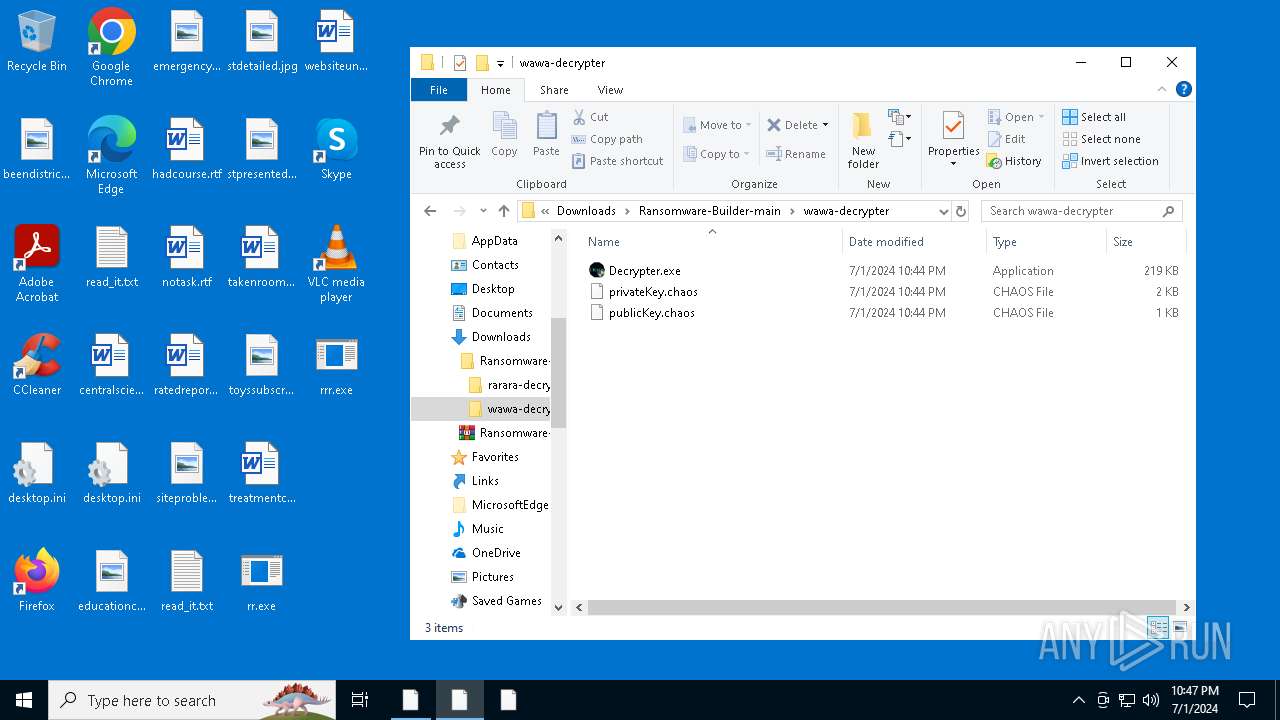
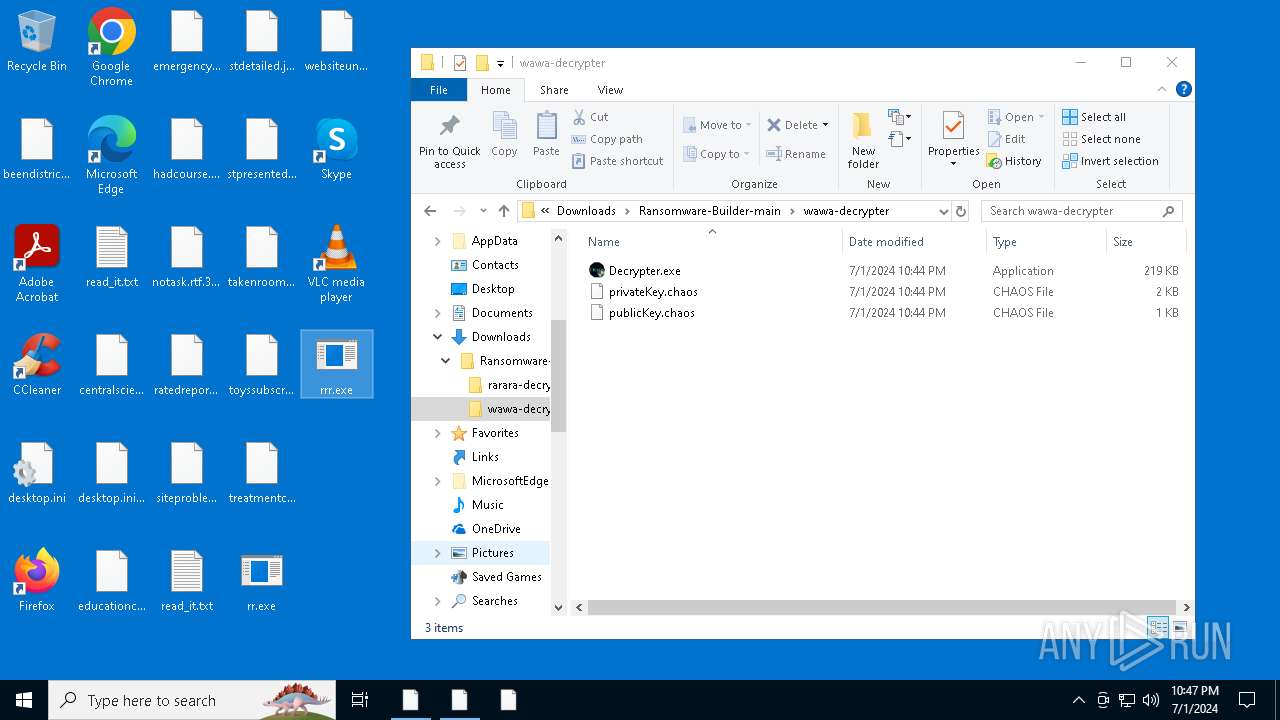
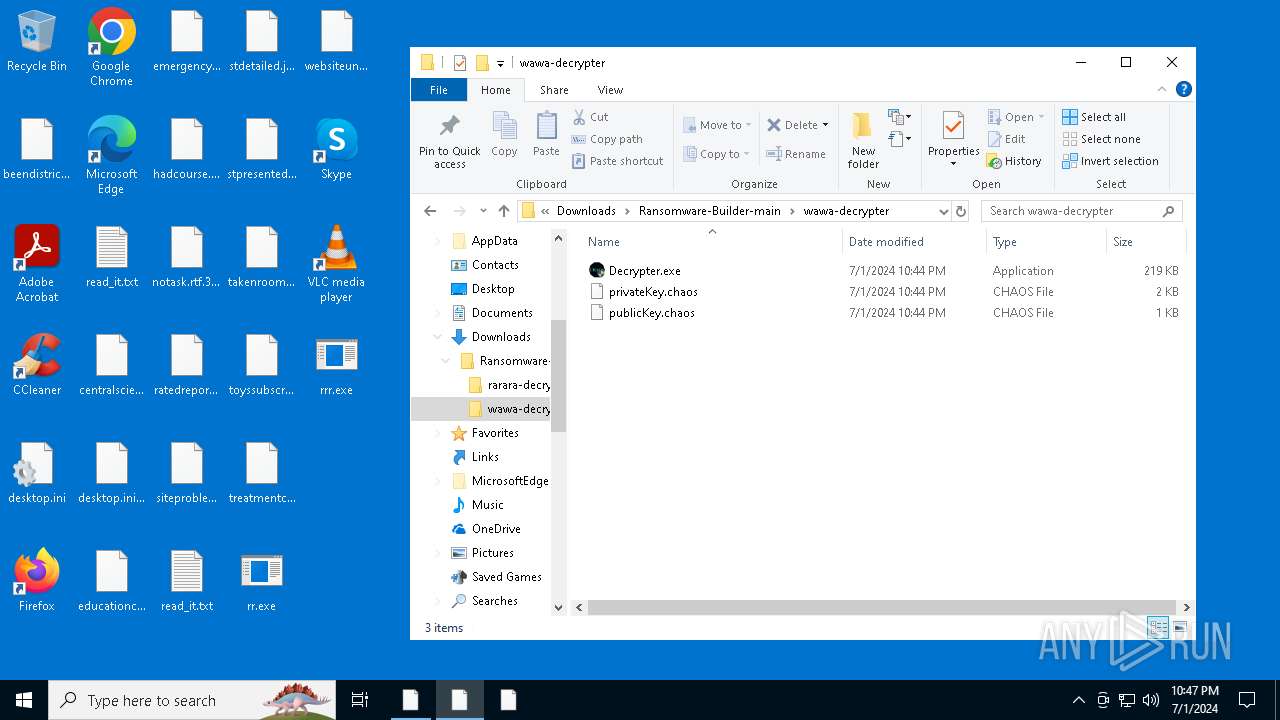
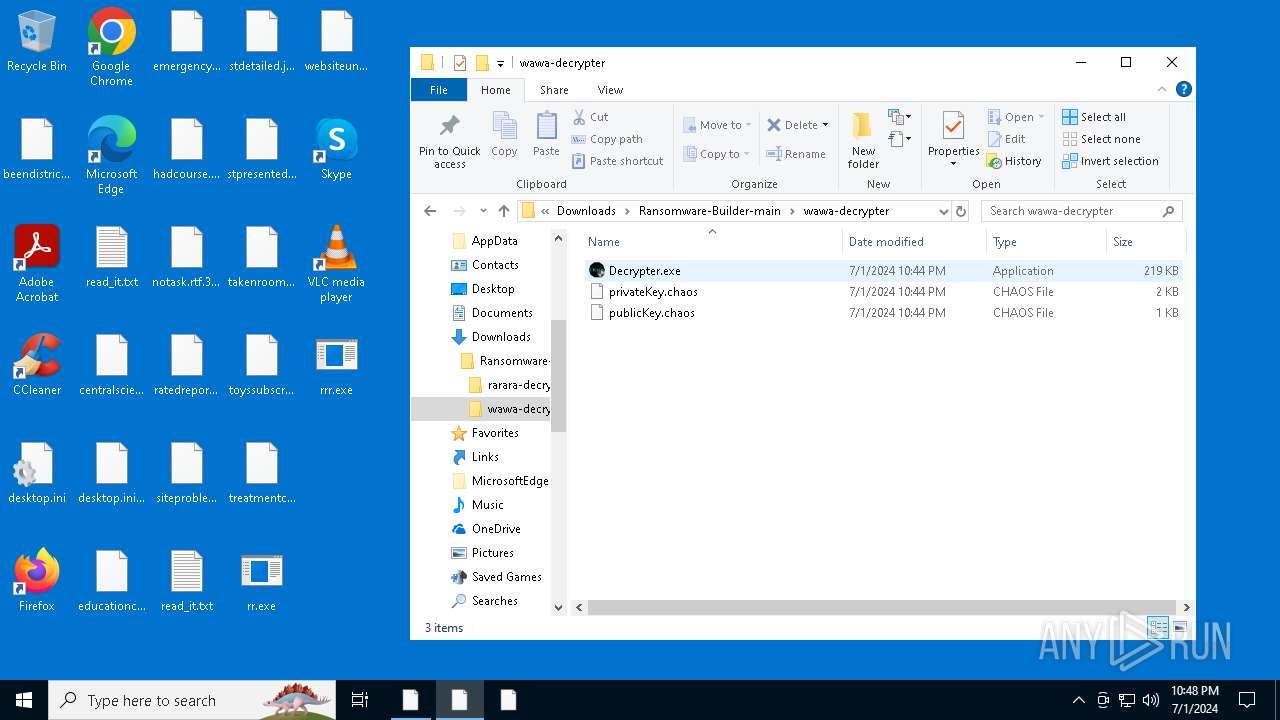
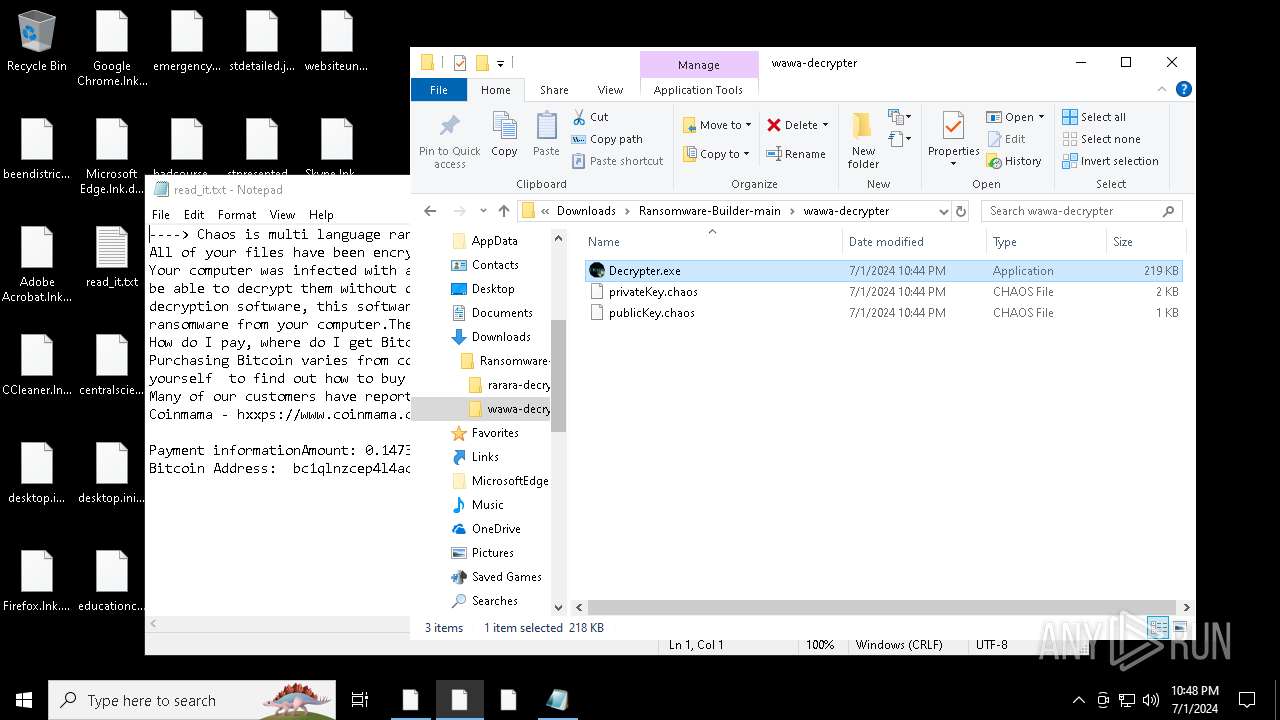
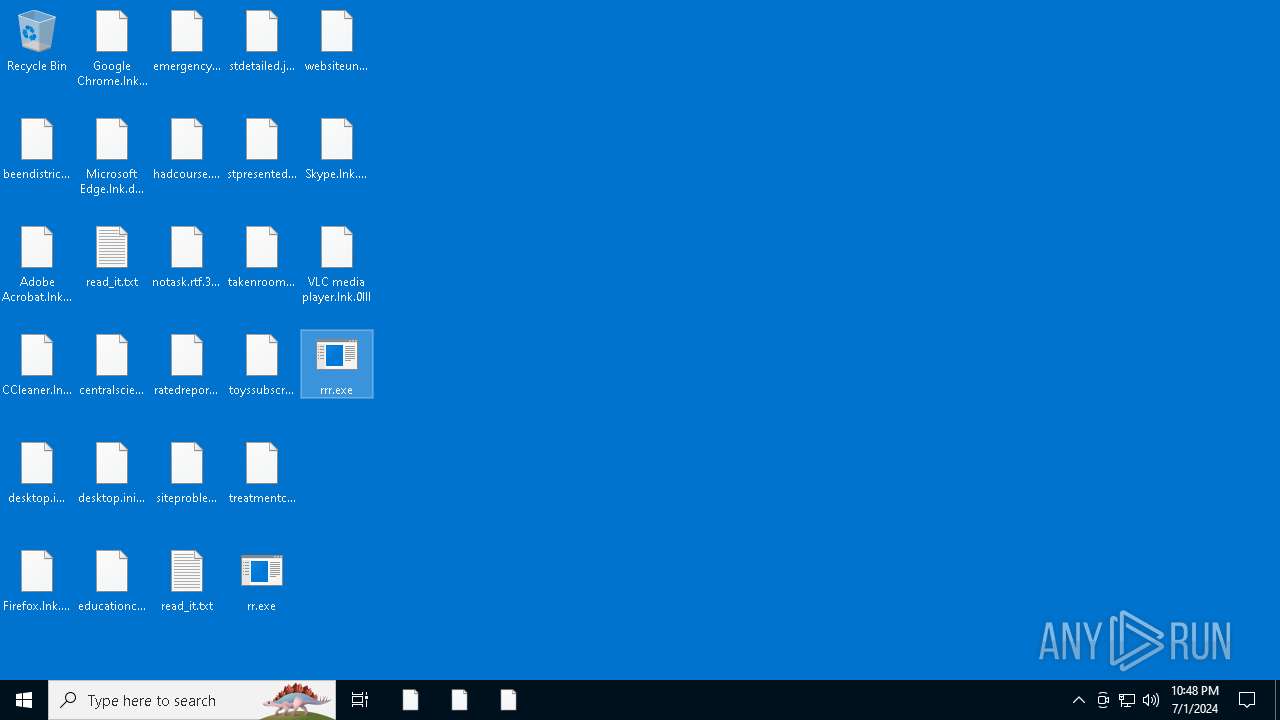
Drops the executable file immediately after the start
- csc.exe (PID: 3964)
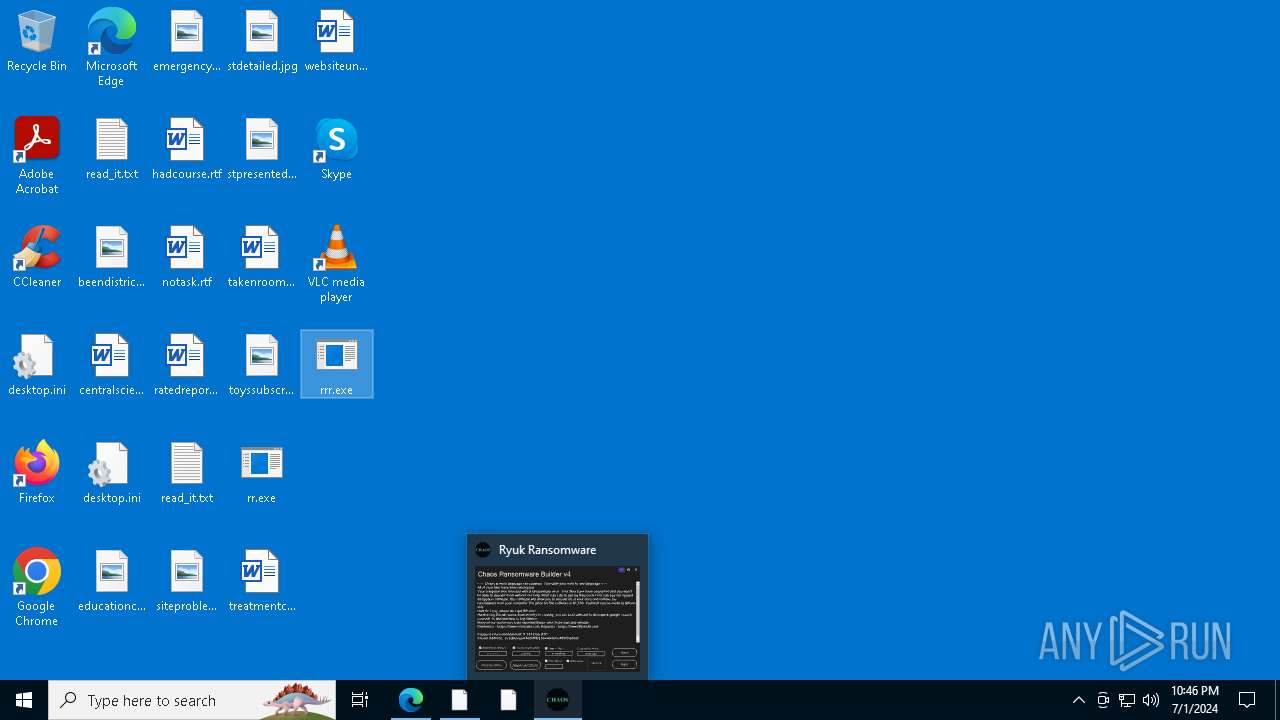
- Chaos Ransomware Builder v4.exe (PID: 6648)
- rr.exe (PID: 4812)
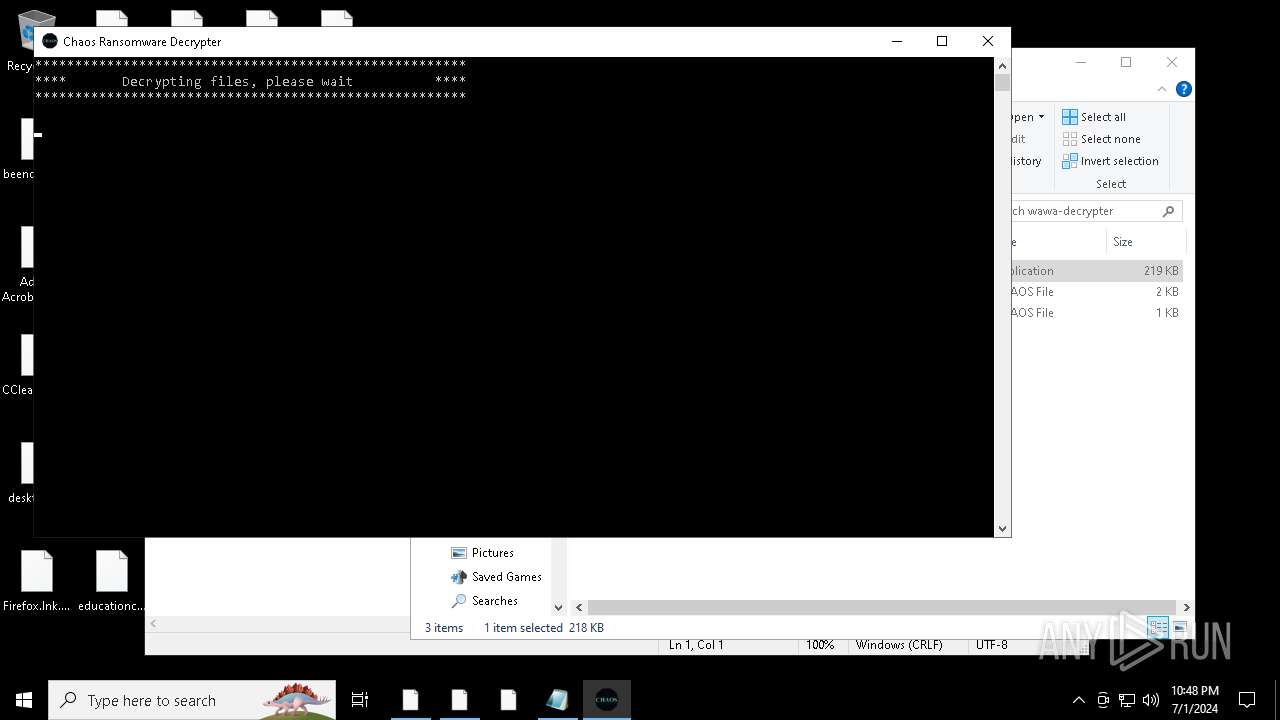
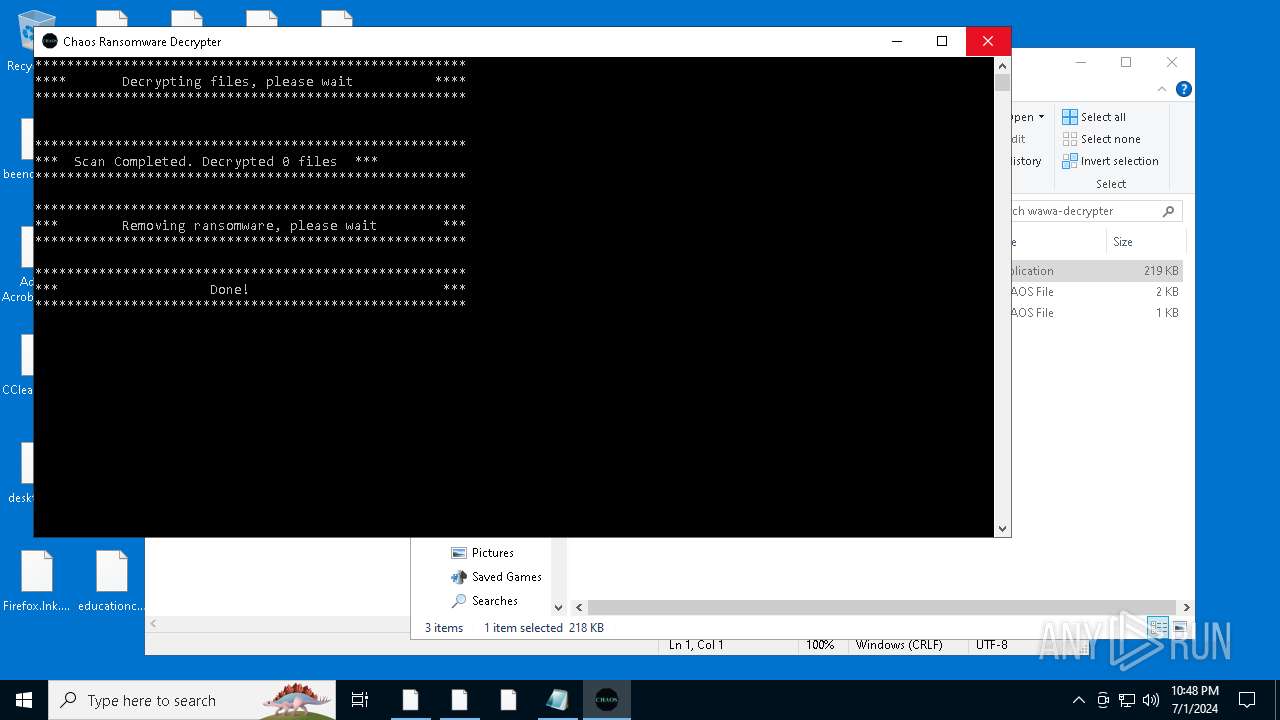
- Decrypter.exe (PID: 2916)
- Chaos Ransomware Builder v4.exe (PID: 7076)
- csc.exe (PID: 4524)
- rrr.exe (PID: 2392)
- Decrypter.exe (PID: 6976)
- rrr.exe (PID: 332)
Create files in the Startup directory
- svchost.exe (PID: 6248)
- svchost.exe (PID: 6692)
- svchost.exe (PID: 2612)
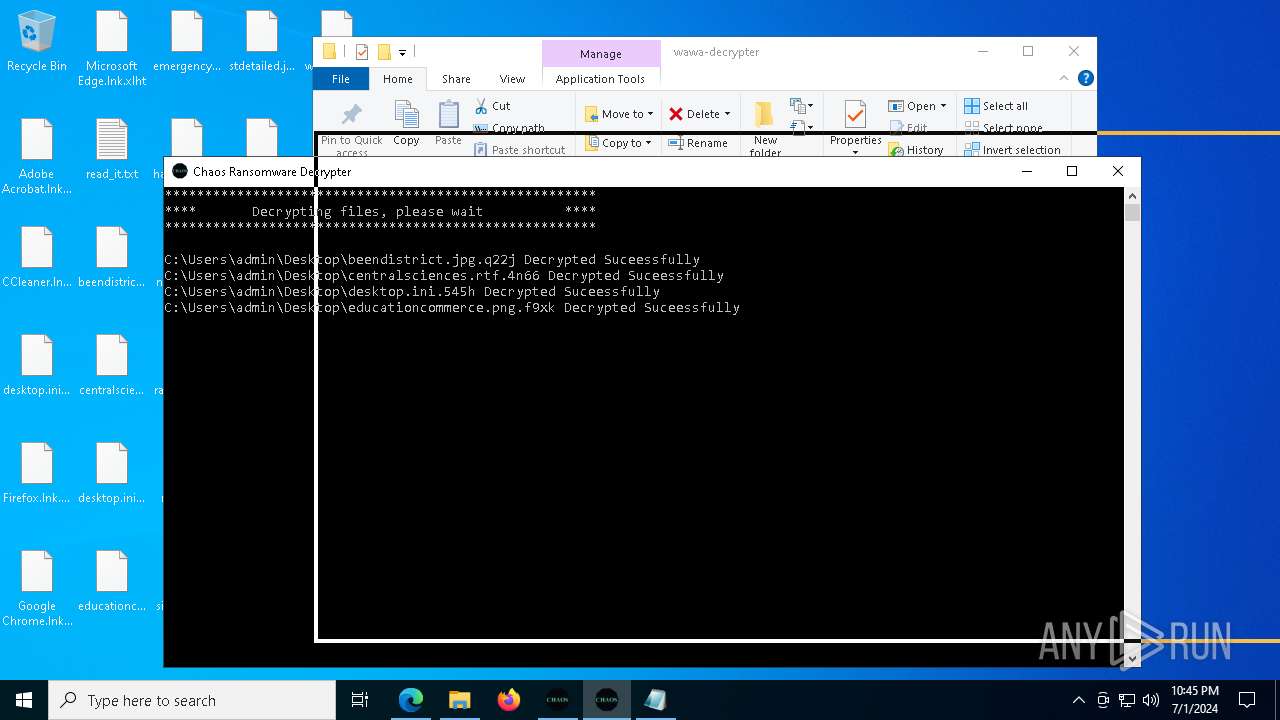
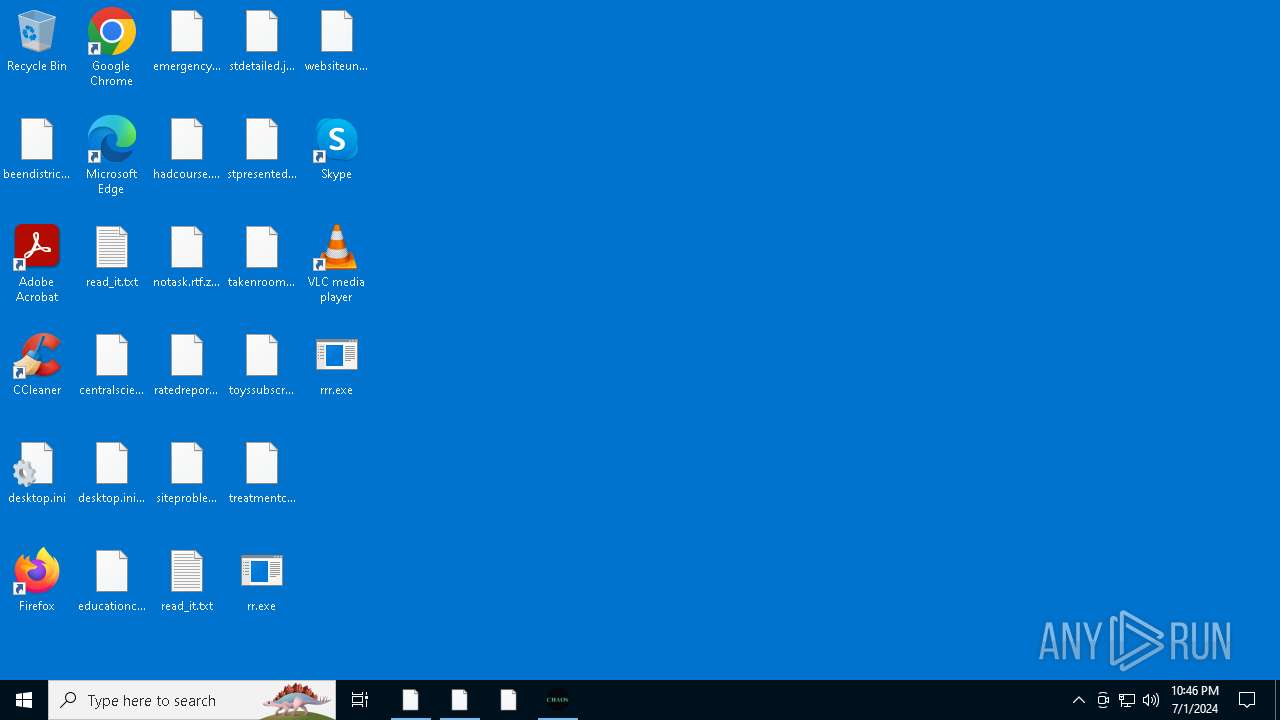
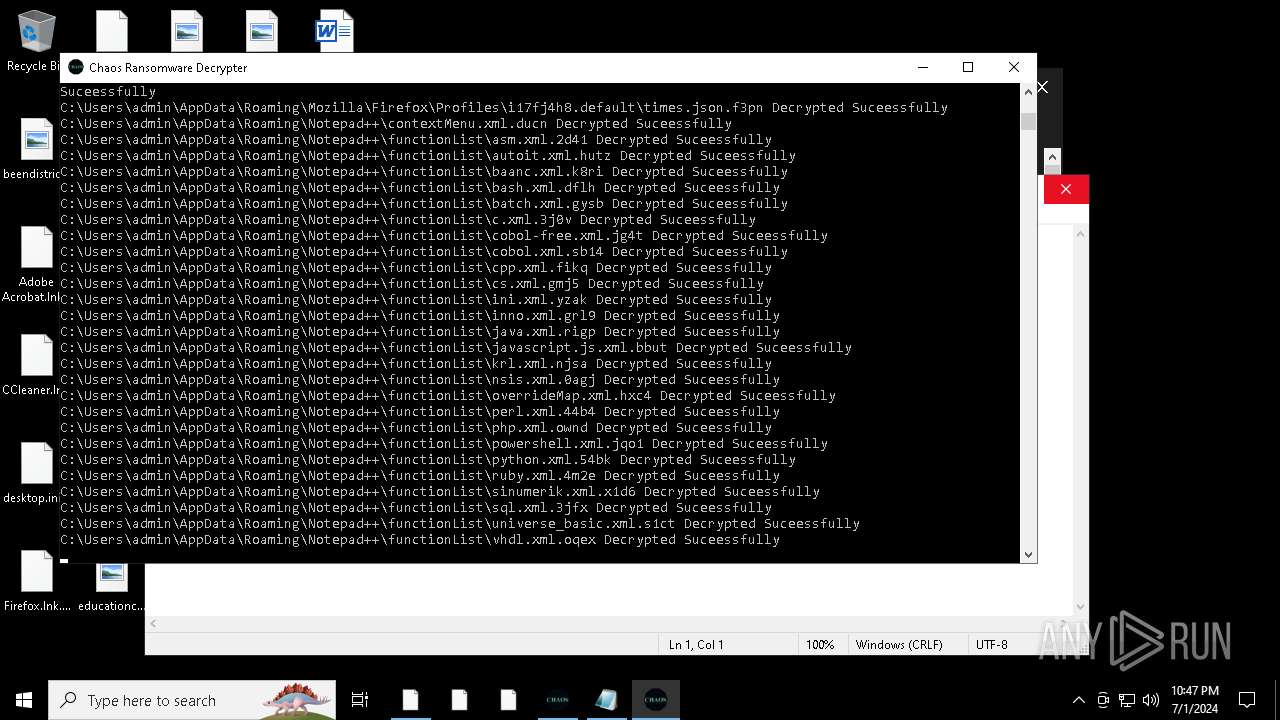
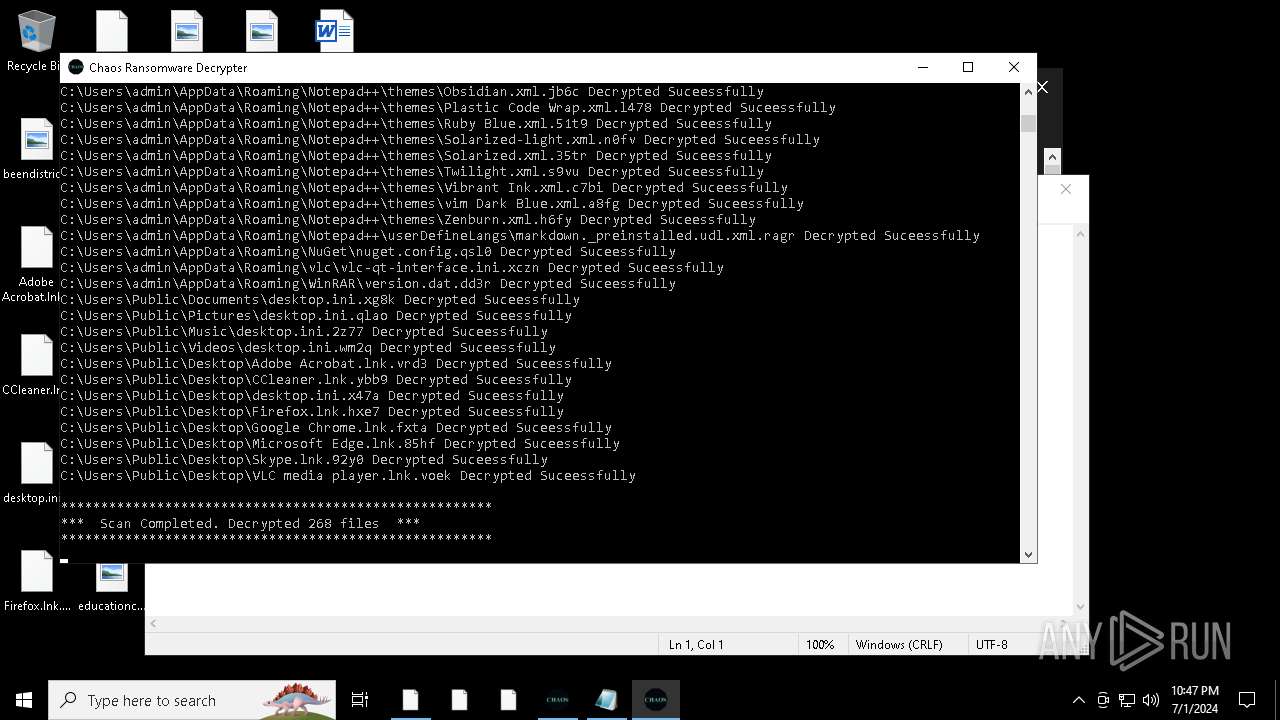
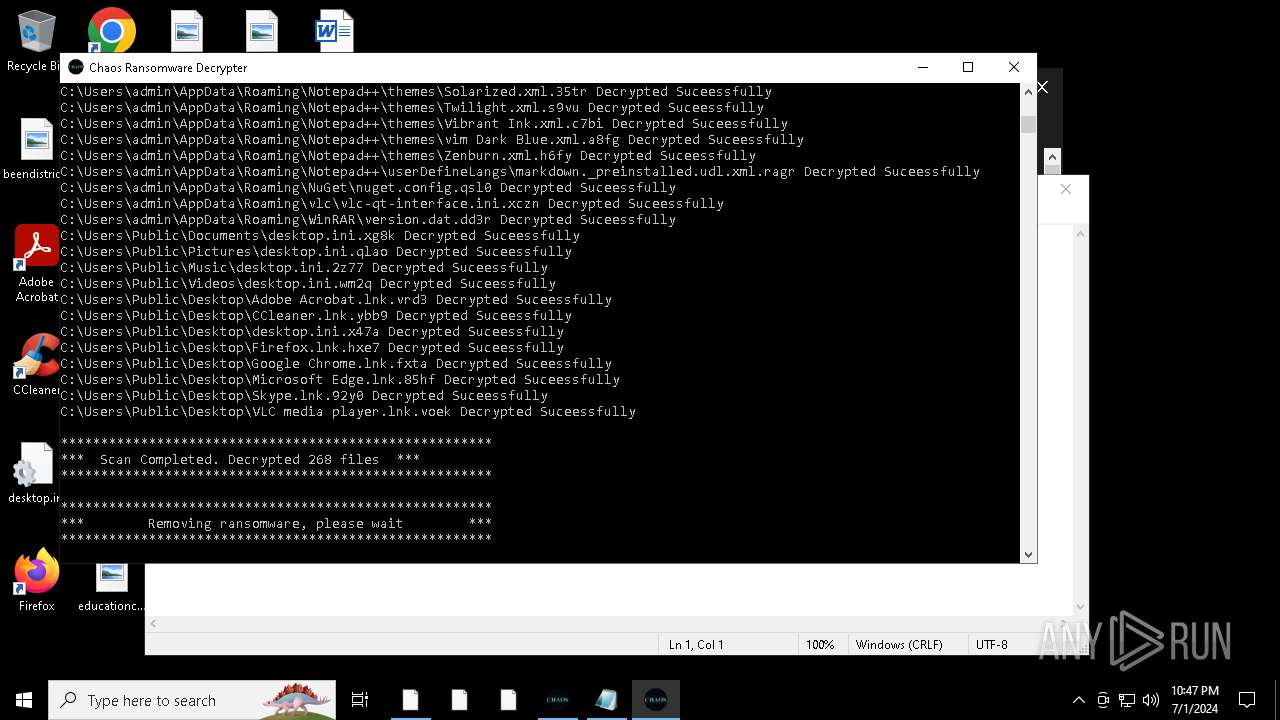
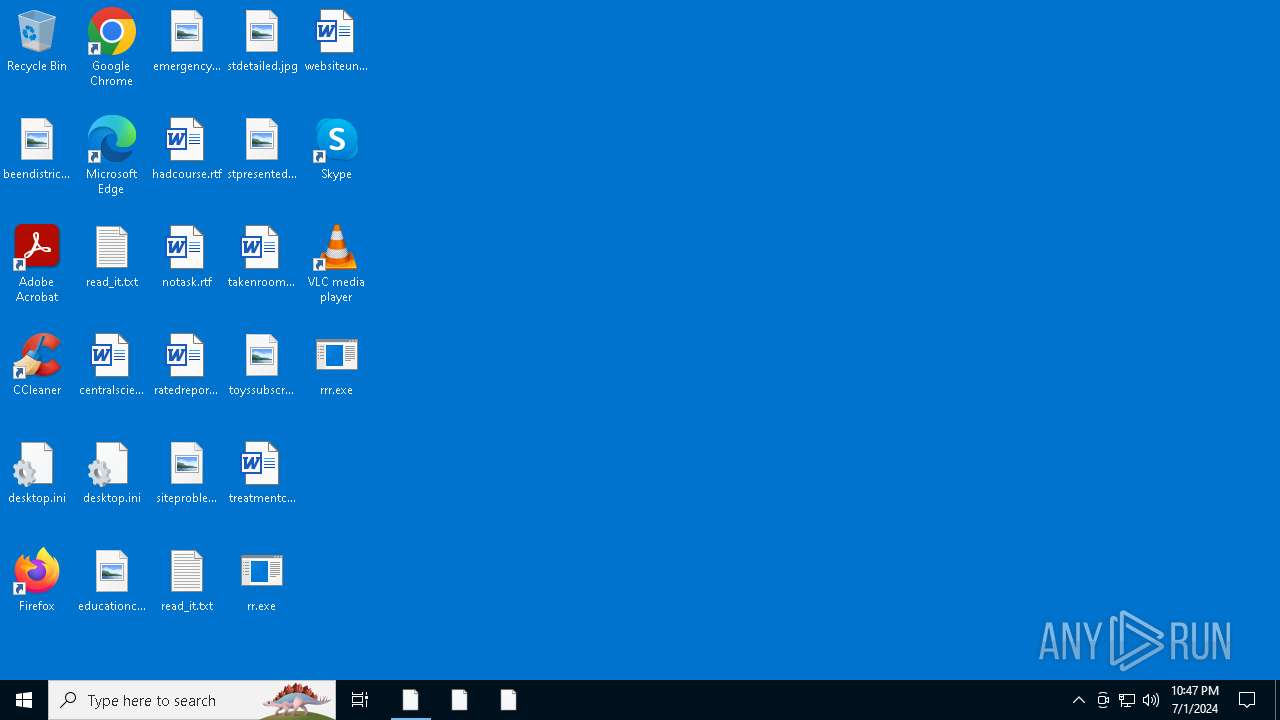
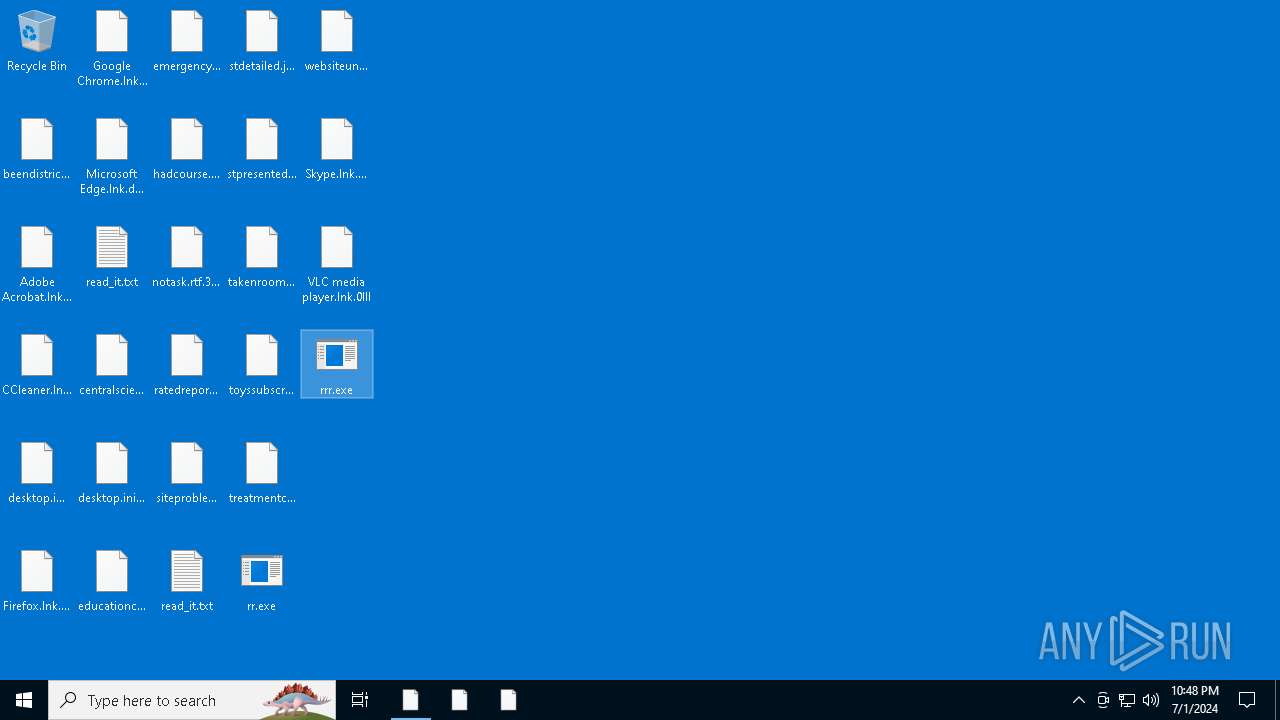
Renames files like ransomware
- svchost.exe (PID: 6248)
- svchost.exe (PID: 6692)
- svchost.exe (PID: 2612)
CHAOS has been detected (YARA)
- Chaos Ransomware Builder v4.exe (PID: 6648)
- svchost.exe (PID: 6692)
- svchost.exe (PID: 2612)
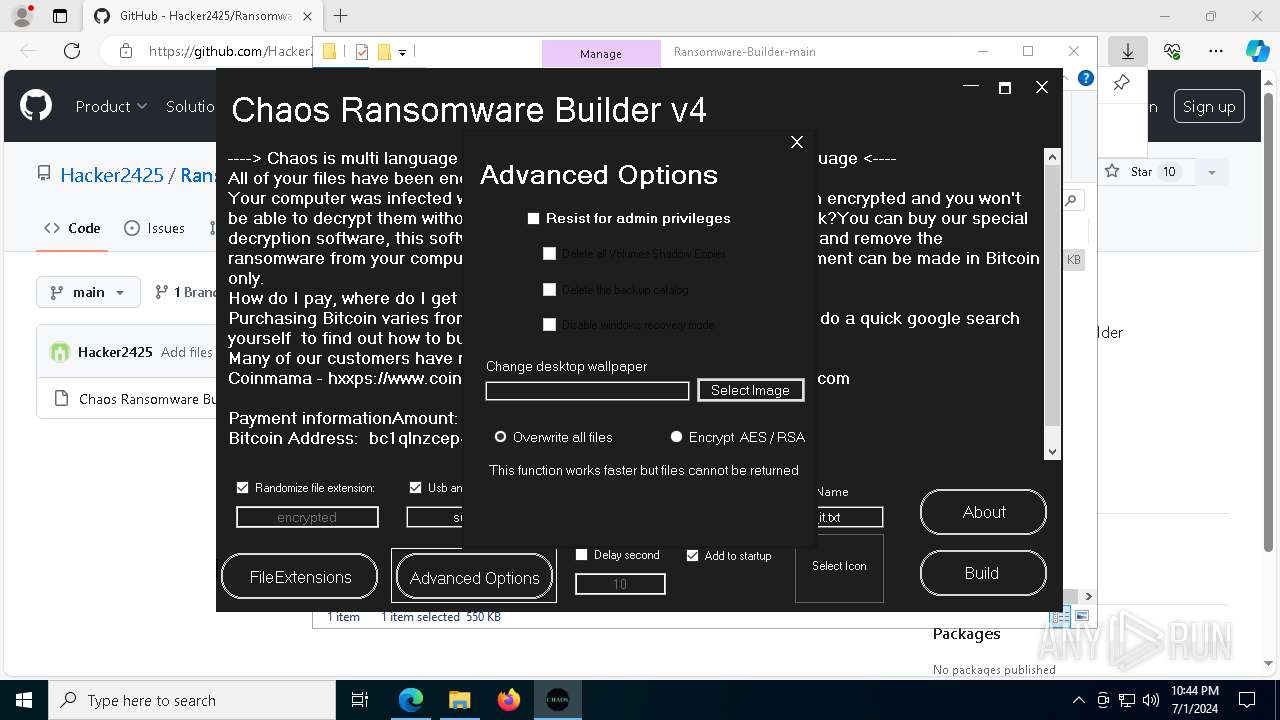
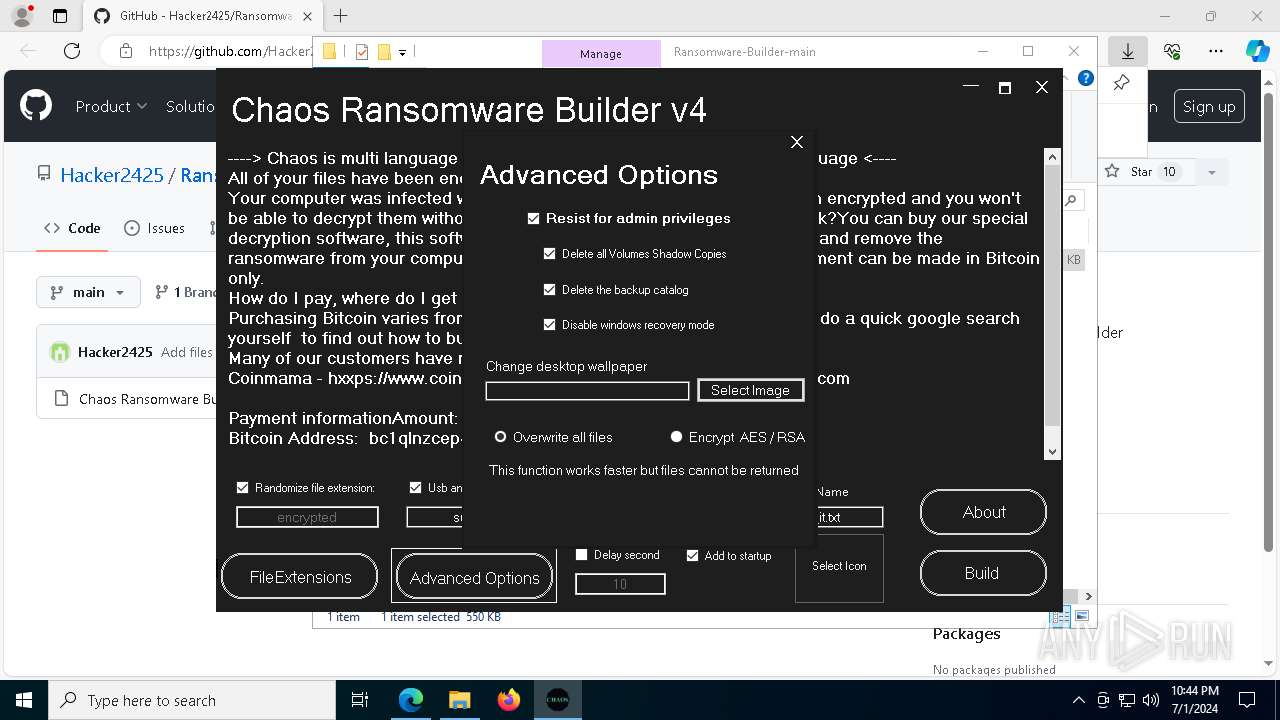
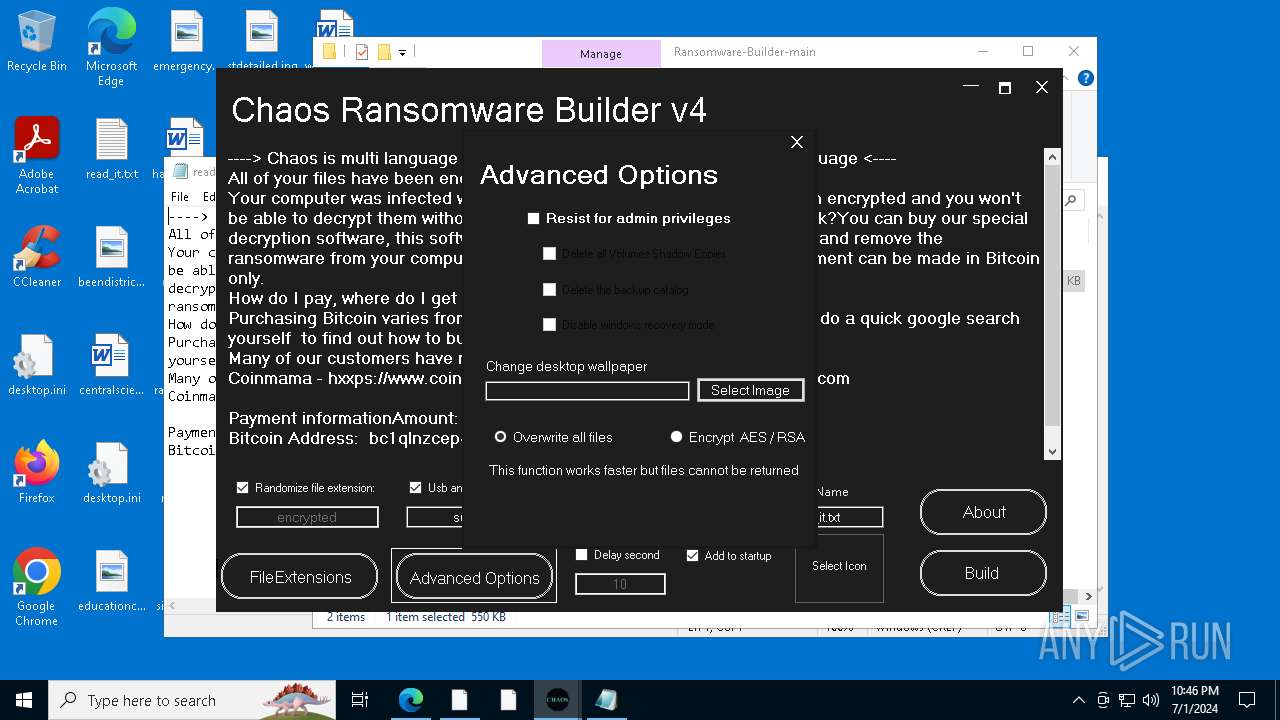
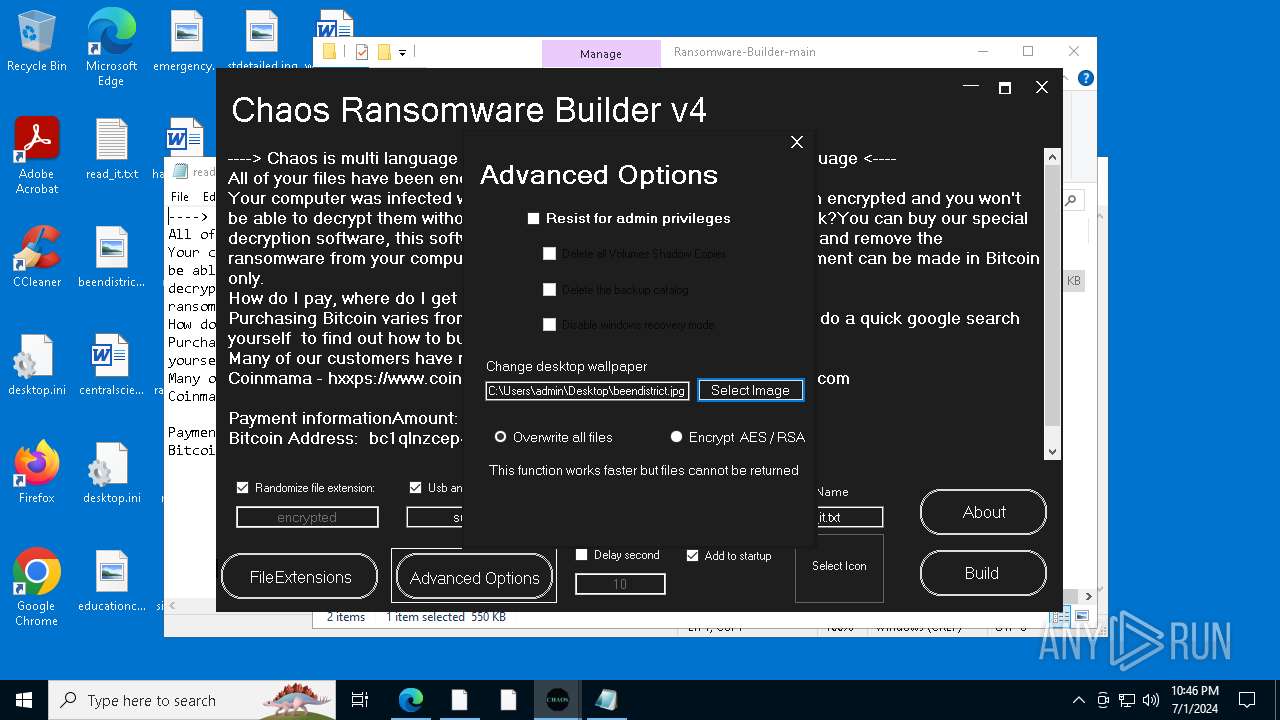
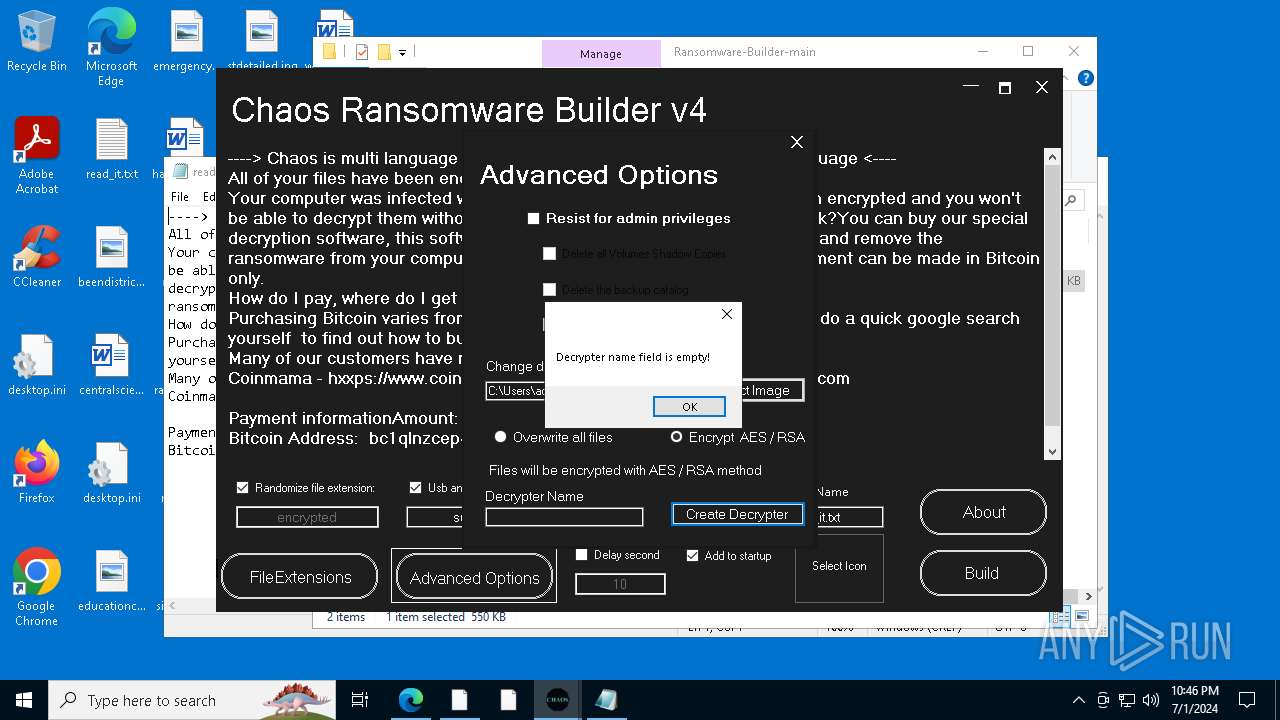
Deletes shadow copies
- cmd.exe (PID: 6888)
- cmd.exe (PID: 4796)
- cmd.exe (PID: 6520)
- cmd.exe (PID: 6232)
- cmd.exe (PID: 6520)
- cmd.exe (PID: 7088)
Using BCDEDIT.EXE to modify recovery options
- cmd.exe (PID: 3800)
- cmd.exe (PID: 3748)
- cmd.exe (PID: 4756)
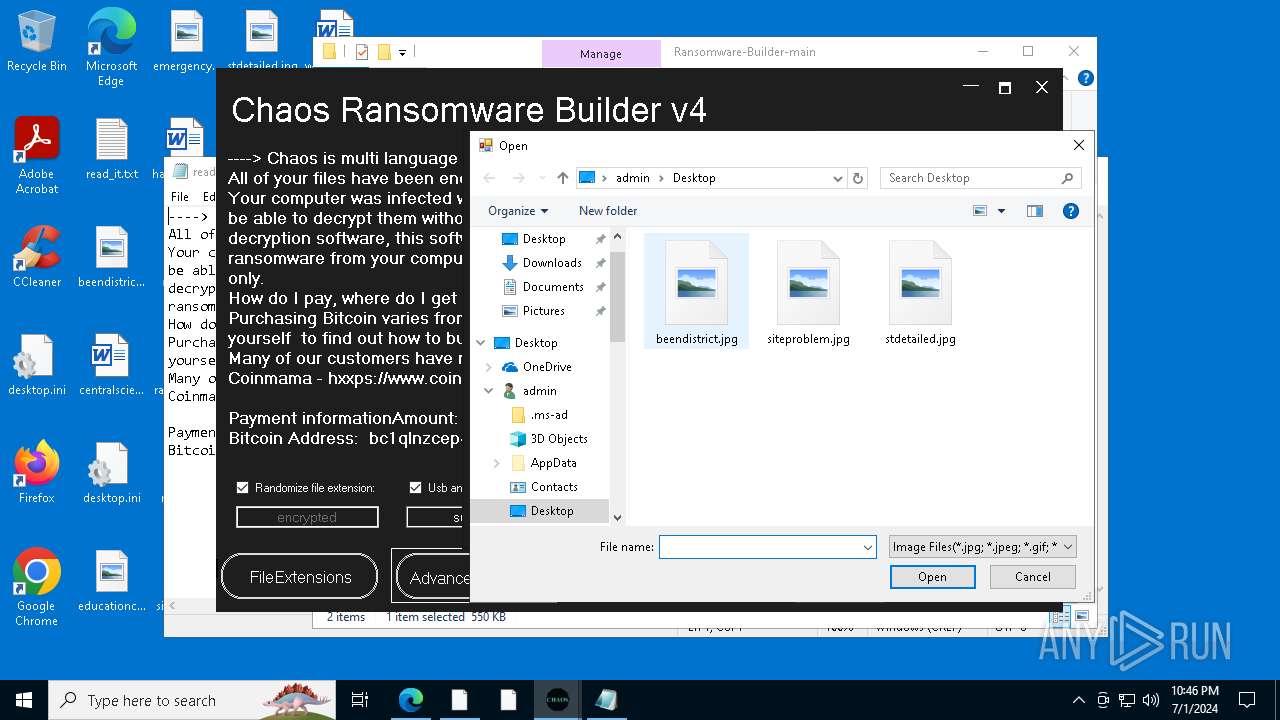
Drops known malicious image
- Decrypter.exe (PID: 2916)
- Decrypter.exe (PID: 6976)
Steals credentials from Web Browsers
- Decrypter.exe (PID: 2916)
- Decrypter.exe (PID: 6976)
- Decrypter.exe (PID: 5252)
Actions looks like stealing of personal data
- svchost.exe (PID: 6248)
- svchost.exe (PID: 6692)
- Decrypter.exe (PID: 2916)
- Decrypter.exe (PID: 6976)
- svchost.exe (PID: 2612)
- Decrypter.exe (PID: 5252)
SUSPICIOUS
Reads security settings of Internet Explorer
- Chaos Ransomware Builder v4.exe (PID: 6648)
- rr.exe (PID: 4812)
- svchost.exe (PID: 6248)
- Chaos Ransomware Builder v4.exe (PID: 7076)
- rrr.exe (PID: 2392)
- svchost.exe (PID: 6692)
- rrr.exe (PID: 332)
- svchost.exe (PID: 2612)
Executable content was dropped or overwritten
- Chaos Ransomware Builder v4.exe (PID: 6648)
- csc.exe (PID: 3964)
- rr.exe (PID: 4812)
- Chaos Ransomware Builder v4.exe (PID: 7076)
- csc.exe (PID: 4524)
- rrr.exe (PID: 2392)
- rrr.exe (PID: 332)
The process creates files with name similar to system file names
- rr.exe (PID: 4812)
- rrr.exe (PID: 2392)
- rrr.exe (PID: 332)
Reads the date of Windows installation
- rr.exe (PID: 4812)
- svchost.exe (PID: 6248)
- rrr.exe (PID: 2392)
- svchost.exe (PID: 6692)
- svchost.exe (PID: 2612)
- rrr.exe (PID: 332)
Starts itself from another location
- rr.exe (PID: 4812)
- rrr.exe (PID: 2392)
- rrr.exe (PID: 332)
Write to the desktop.ini file (may be used to cloak folders)
- svchost.exe (PID: 6248)
Executes as Windows Service
- VSSVC.exe (PID: 5040)
- vds.exe (PID: 2992)
- wbengine.exe (PID: 5504)
Starts CMD.EXE for commands execution
- svchost.exe (PID: 6248)
- svchost.exe (PID: 6692)
- svchost.exe (PID: 2612)
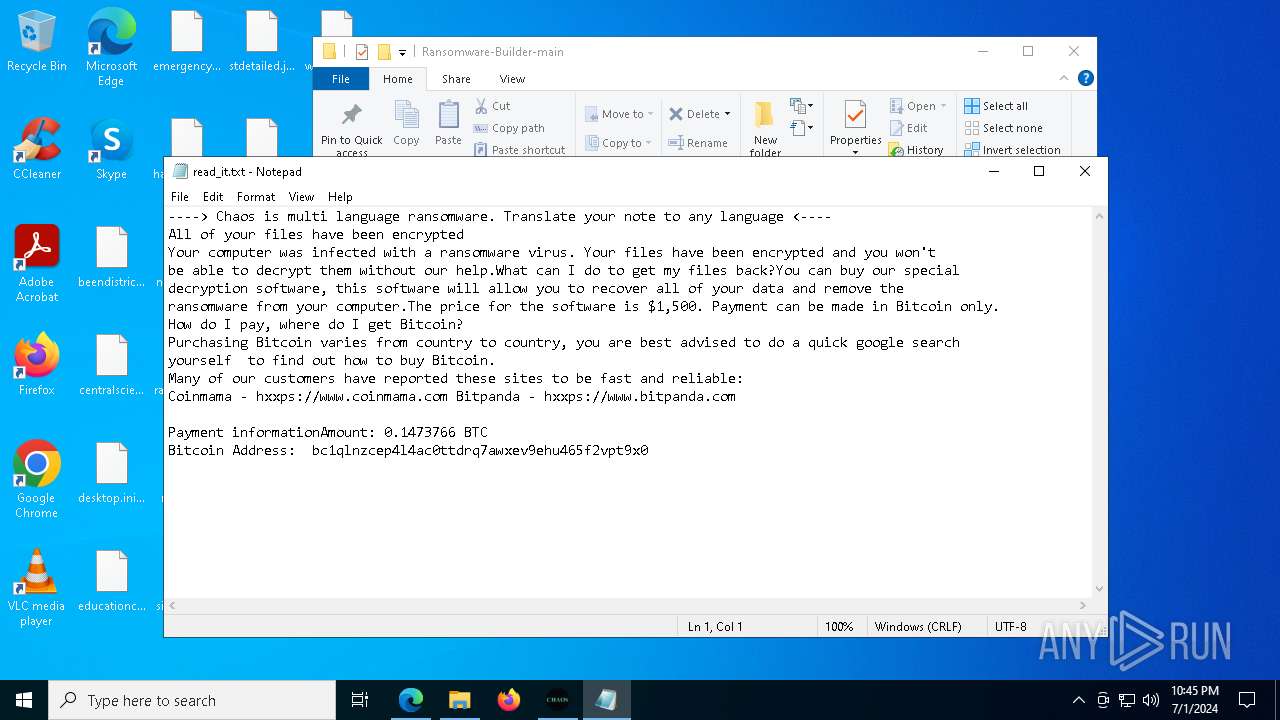
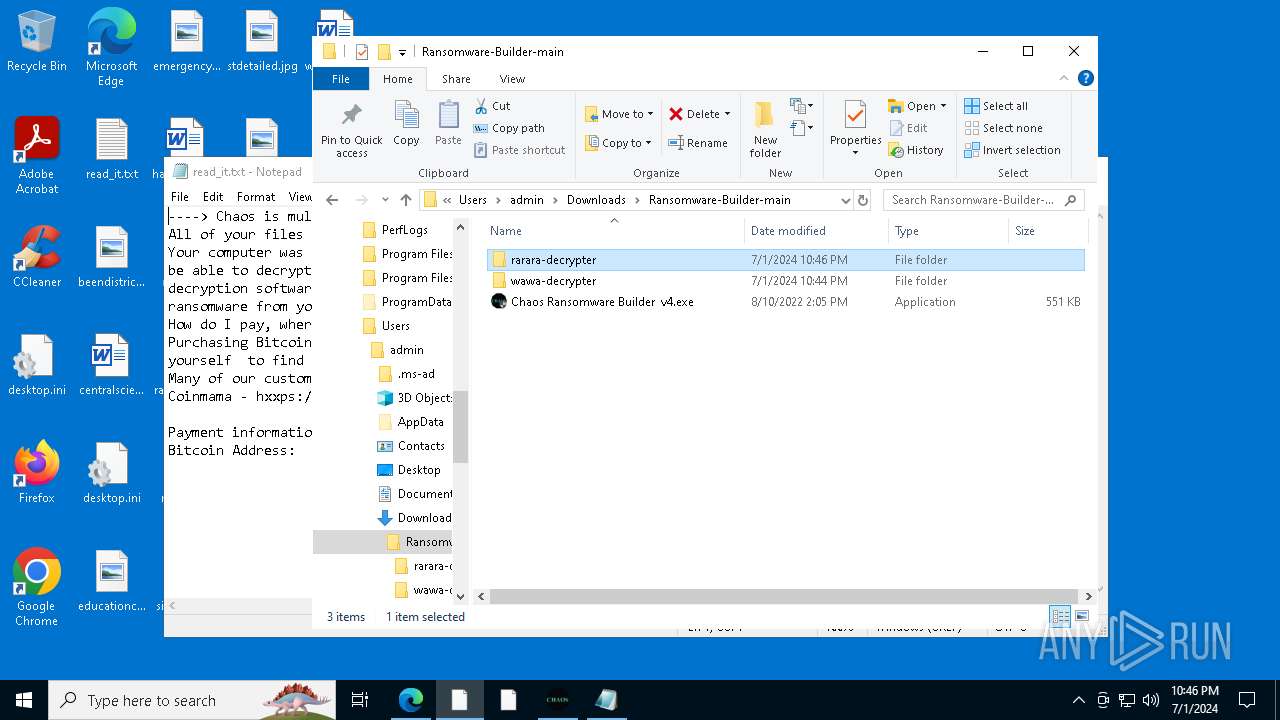
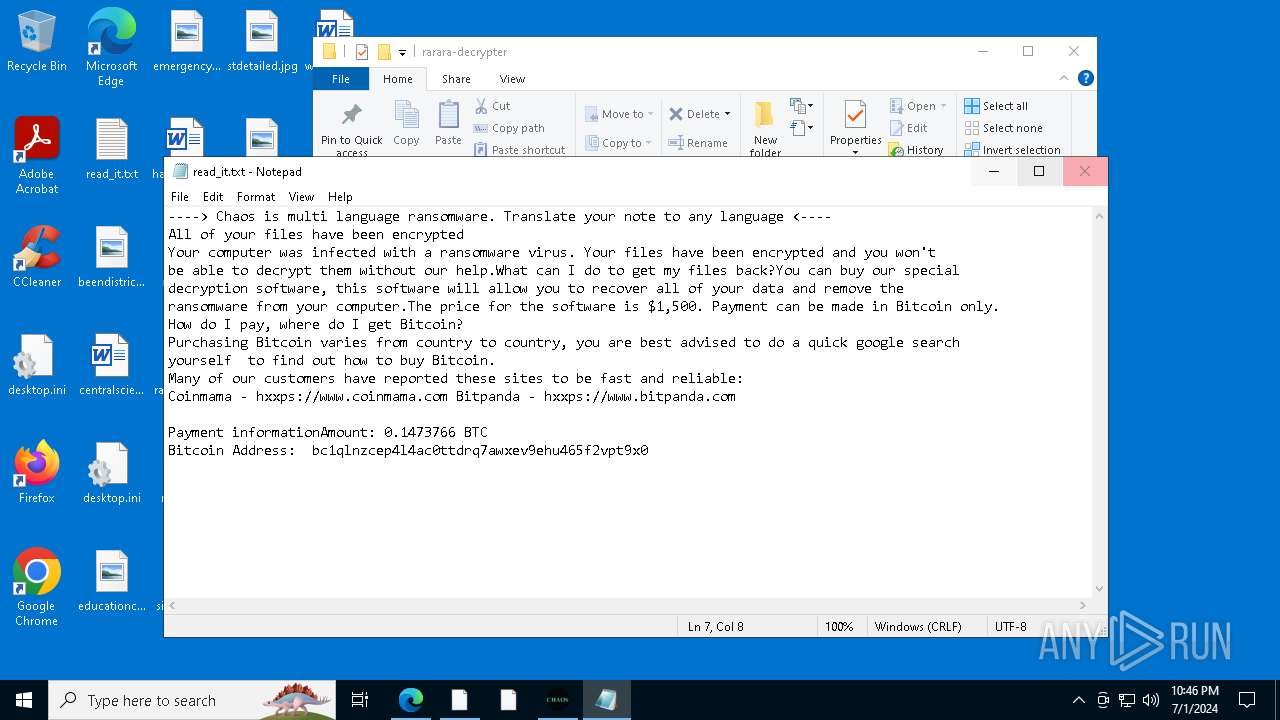
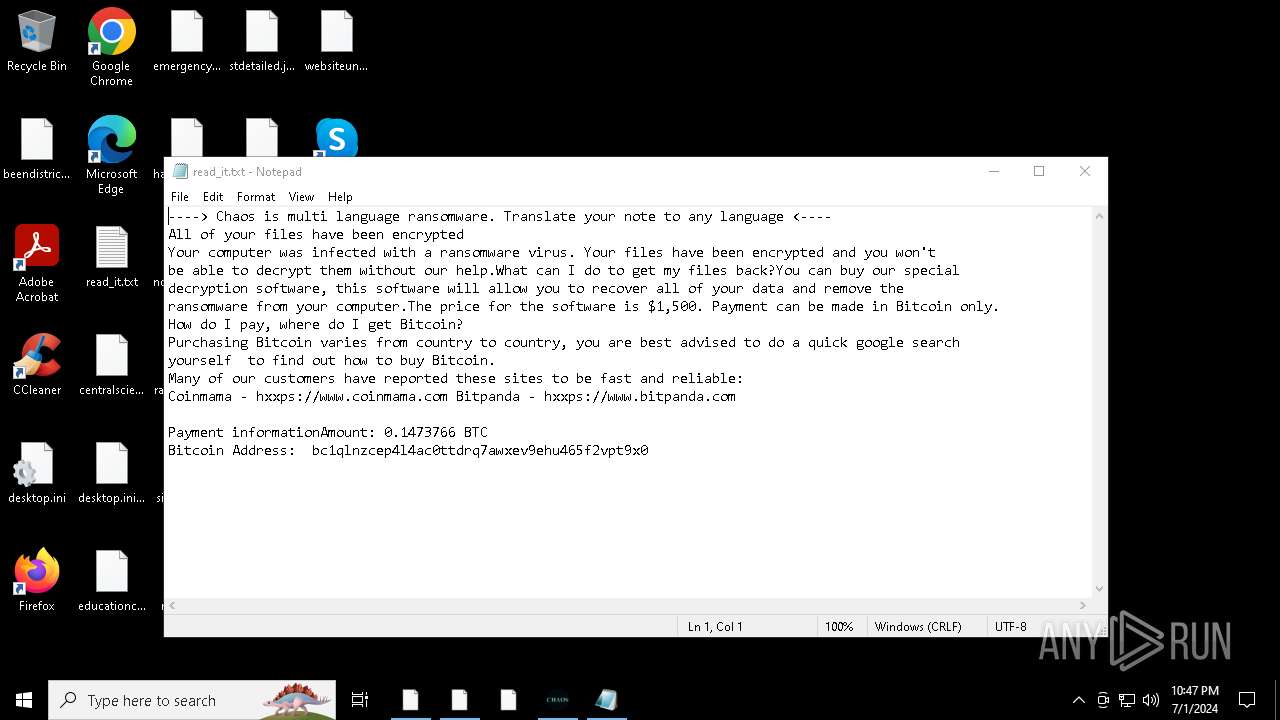
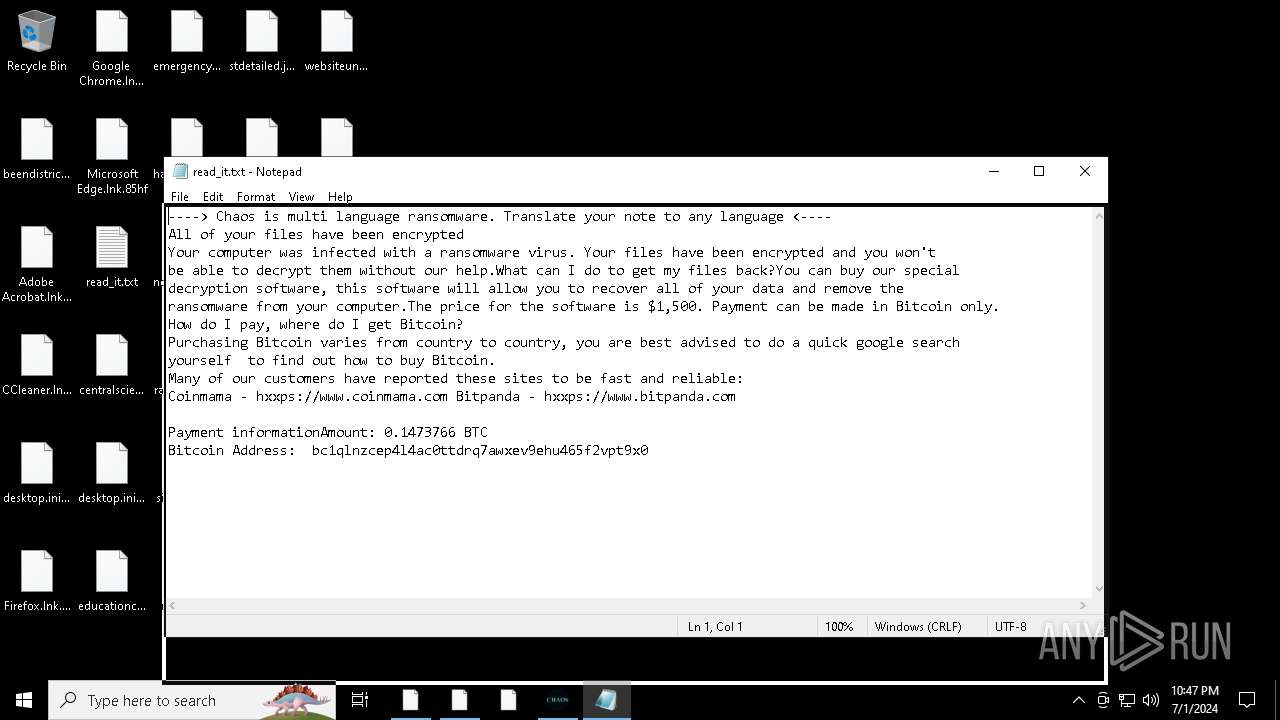
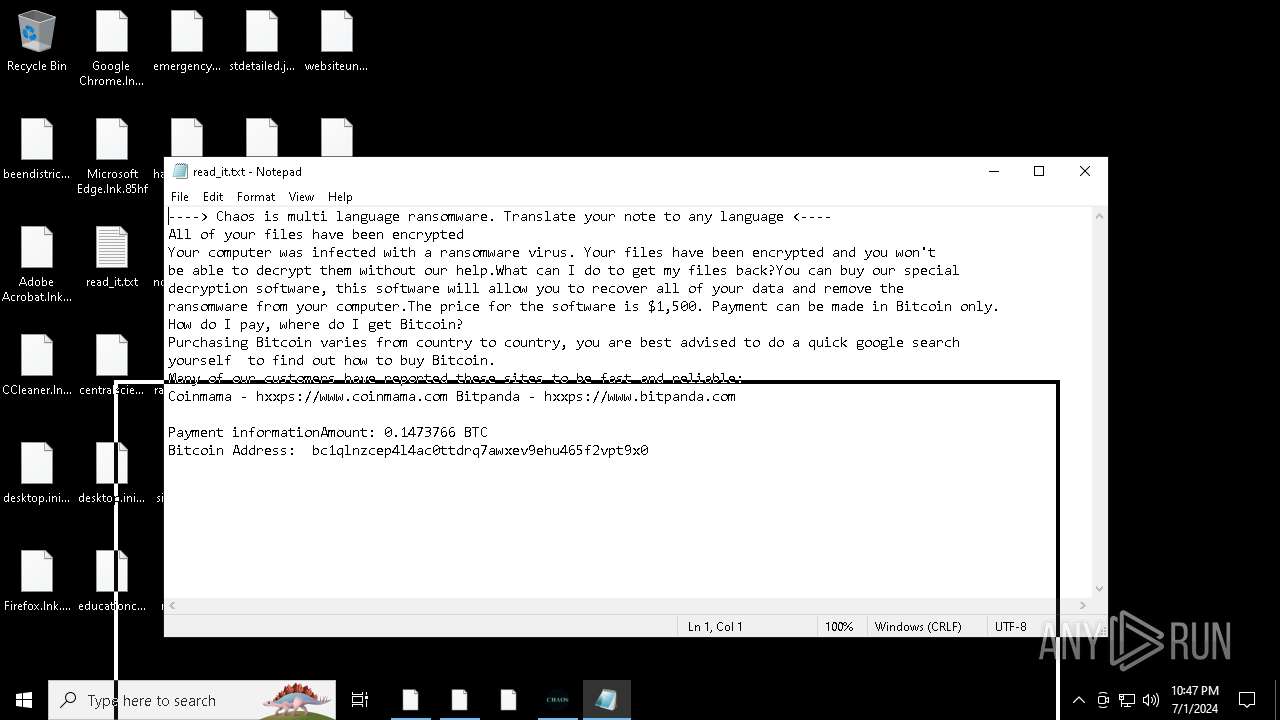
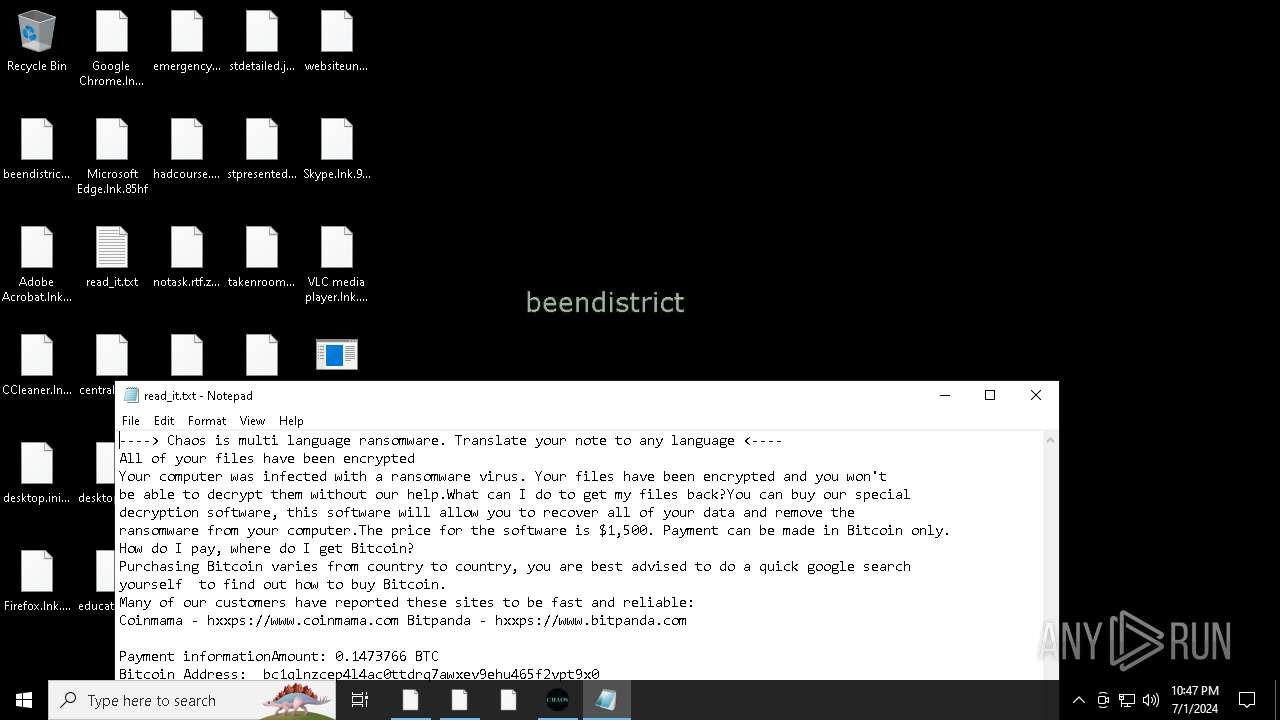
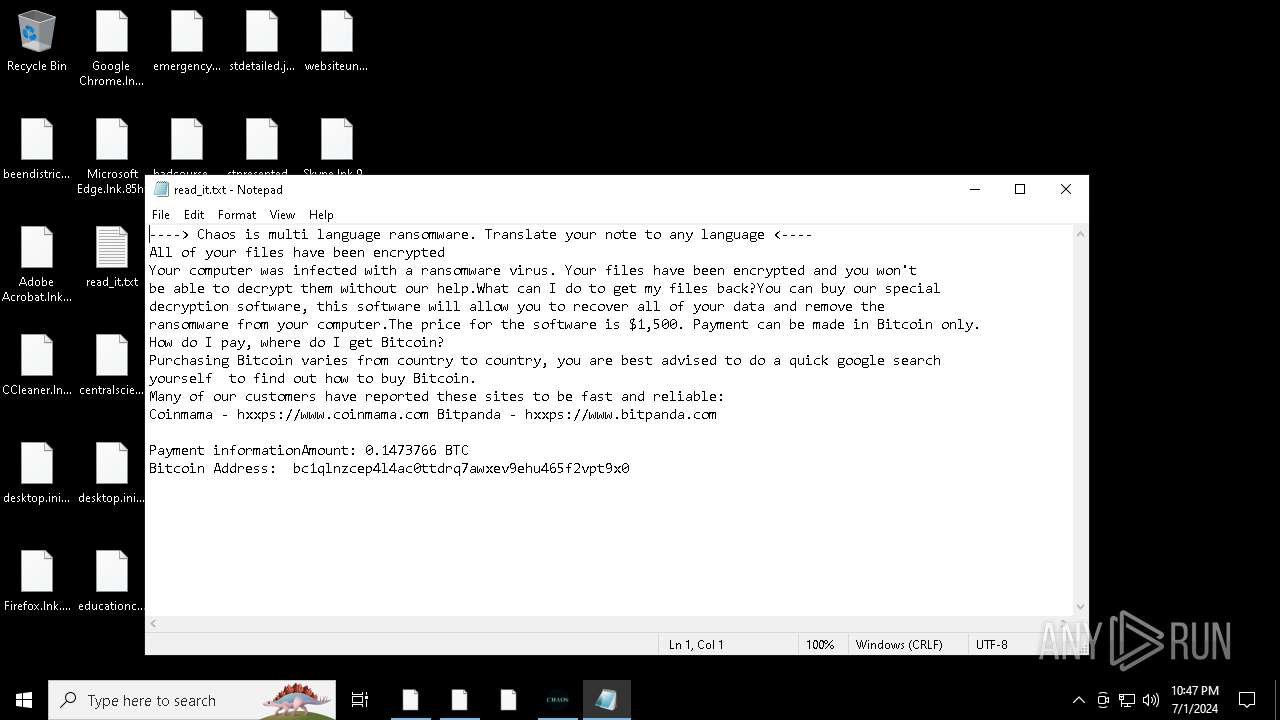
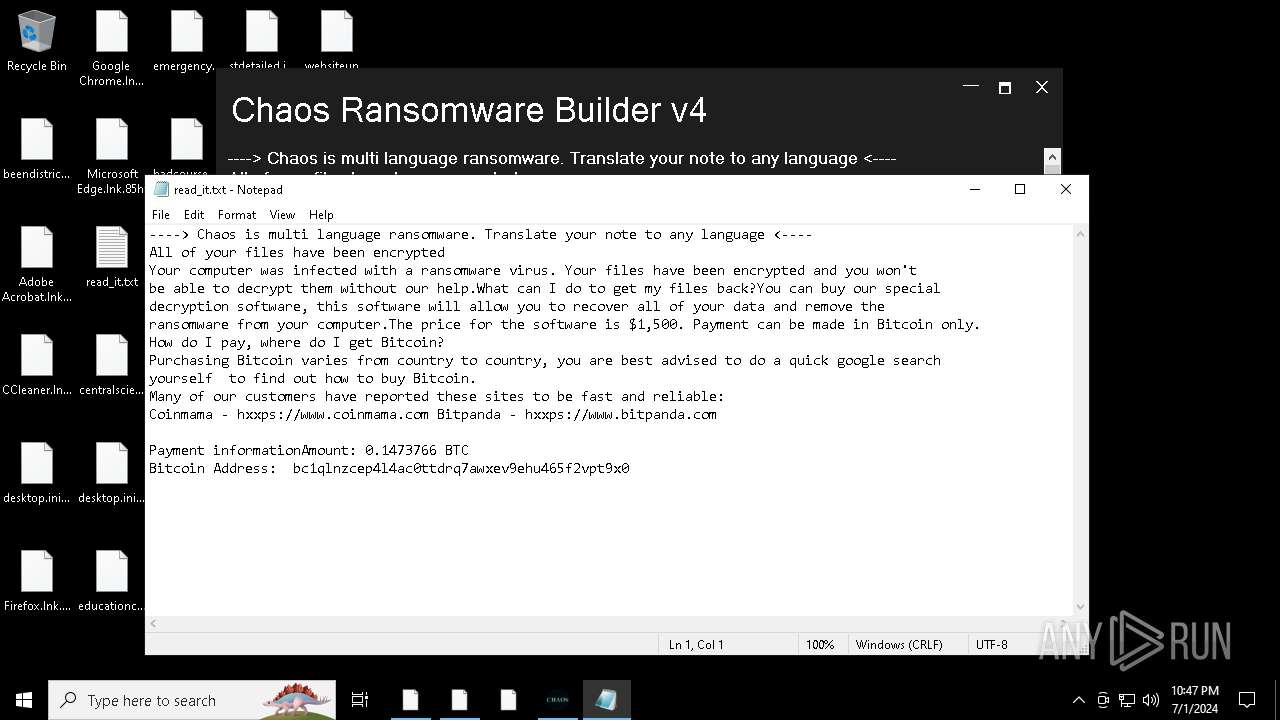
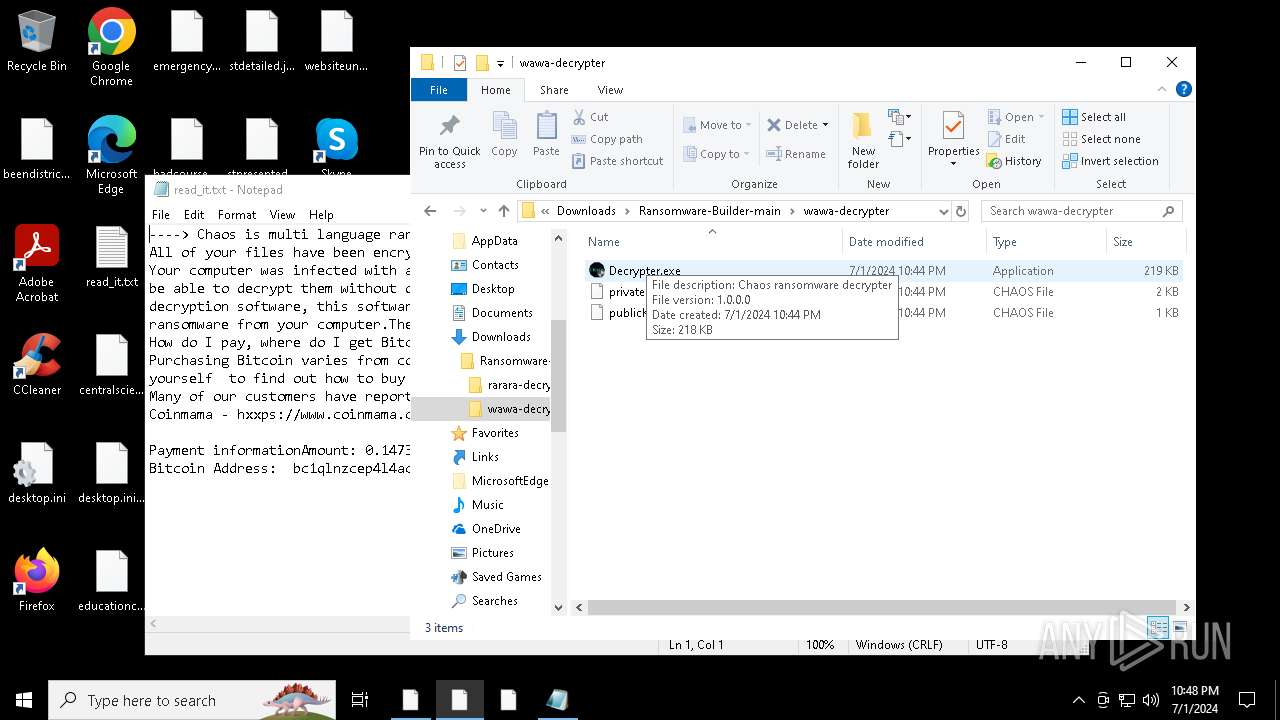
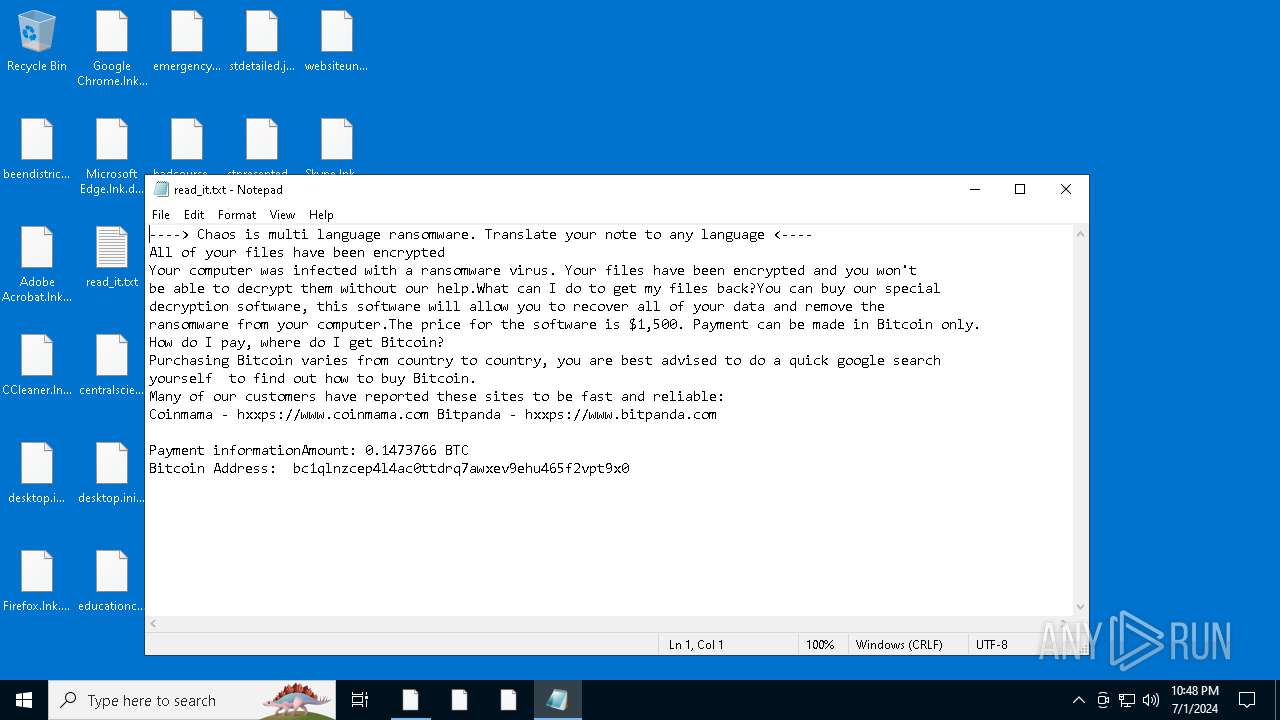
Start notepad (likely ransomware note)
- svchost.exe (PID: 6248)
- svchost.exe (PID: 6692)
- svchost.exe (PID: 2612)
INFO
Drops the executable file immediately after the start
- msedge.exe (PID: 3104)
- msedge.exe (PID: 368)
- WinRAR.exe (PID: 6676)
- msedge.exe (PID: 2132)
Checks supported languages
- identity_helper.exe (PID: 6532)
- Chaos Ransomware Builder v4.exe (PID: 6648)
- cvtres.exe (PID: 4756)
- csc.exe (PID: 3964)
- rr.exe (PID: 4812)
- svchost.exe (PID: 6248)
- Decrypter.exe (PID: 2916)
- Chaos Ransomware Builder v4.exe (PID: 7076)
- csc.exe (PID: 4524)
- cvtres.exe (PID: 916)
- rrr.exe (PID: 2392)
- svchost.exe (PID: 6692)
- TextInputHost.exe (PID: 360)
- Decrypter.exe (PID: 6976)
- rrr.exe (PID: 332)
- svchost.exe (PID: 2612)
- Decrypter.exe (PID: 5252)
- identity_helper.exe (PID: 3844)
Reads Microsoft Office registry keys
- msedge.exe (PID: 3104)
- svchost.exe (PID: 6248)
- svchost.exe (PID: 6692)
- svchost.exe (PID: 2612)
- OpenWith.exe (PID: 764)
- msedge.exe (PID: 7108)
- OpenWith.exe (PID: 6584)
Reads the computer name
- identity_helper.exe (PID: 6532)
- Chaos Ransomware Builder v4.exe (PID: 6648)
- rr.exe (PID: 4812)
- svchost.exe (PID: 6248)
- Decrypter.exe (PID: 2916)
- Chaos Ransomware Builder v4.exe (PID: 7076)
- rrr.exe (PID: 2392)
- svchost.exe (PID: 6692)
- TextInputHost.exe (PID: 360)
- Decrypter.exe (PID: 6976)
- rrr.exe (PID: 332)
- svchost.exe (PID: 2612)
- Decrypter.exe (PID: 5252)
- identity_helper.exe (PID: 3844)
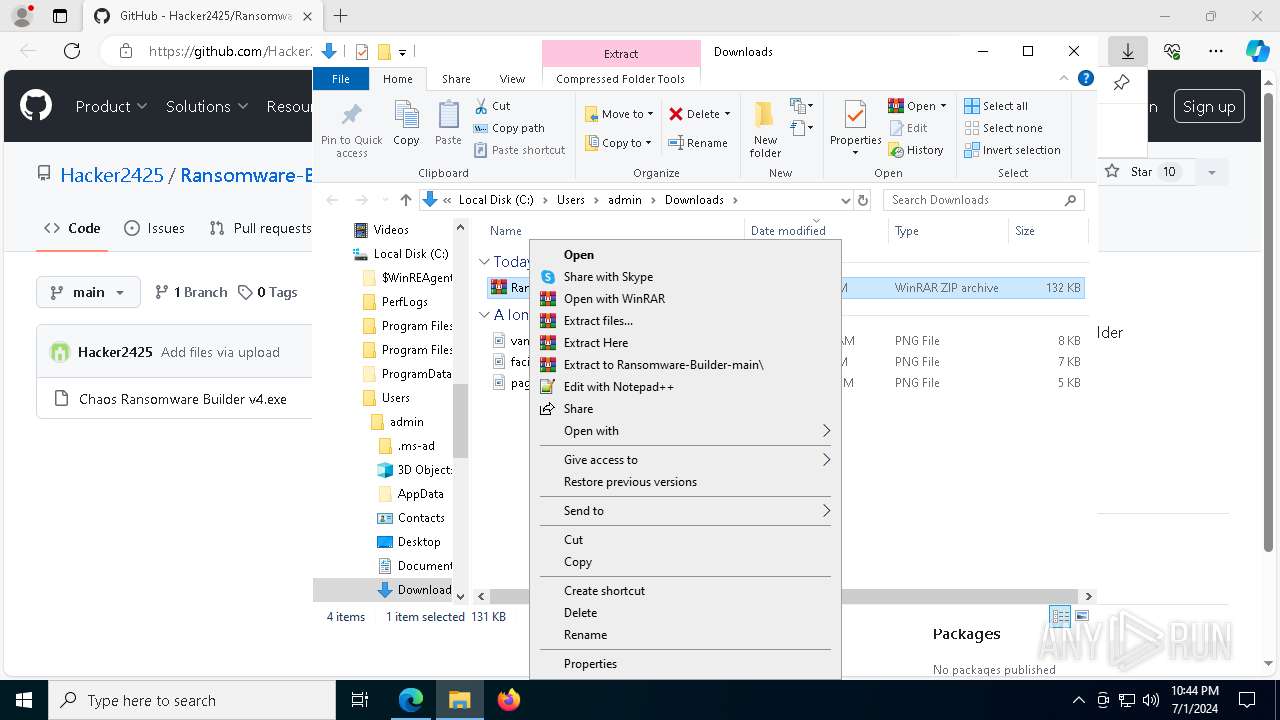
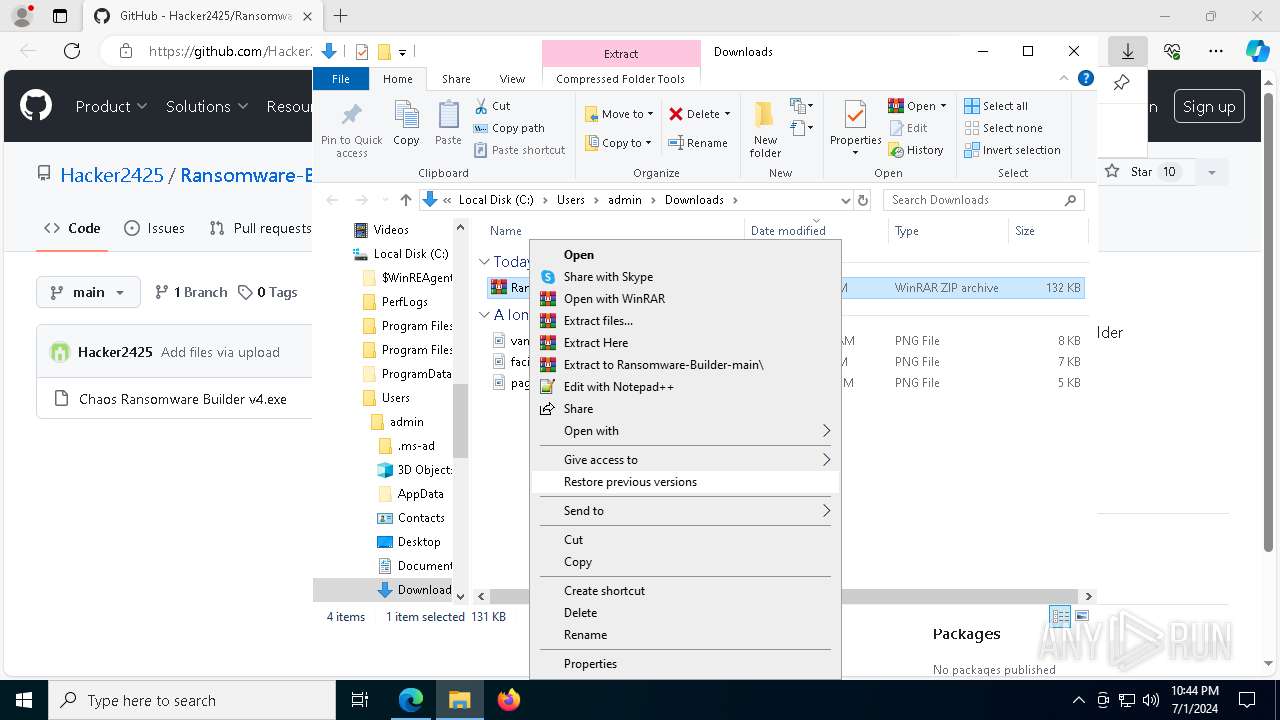
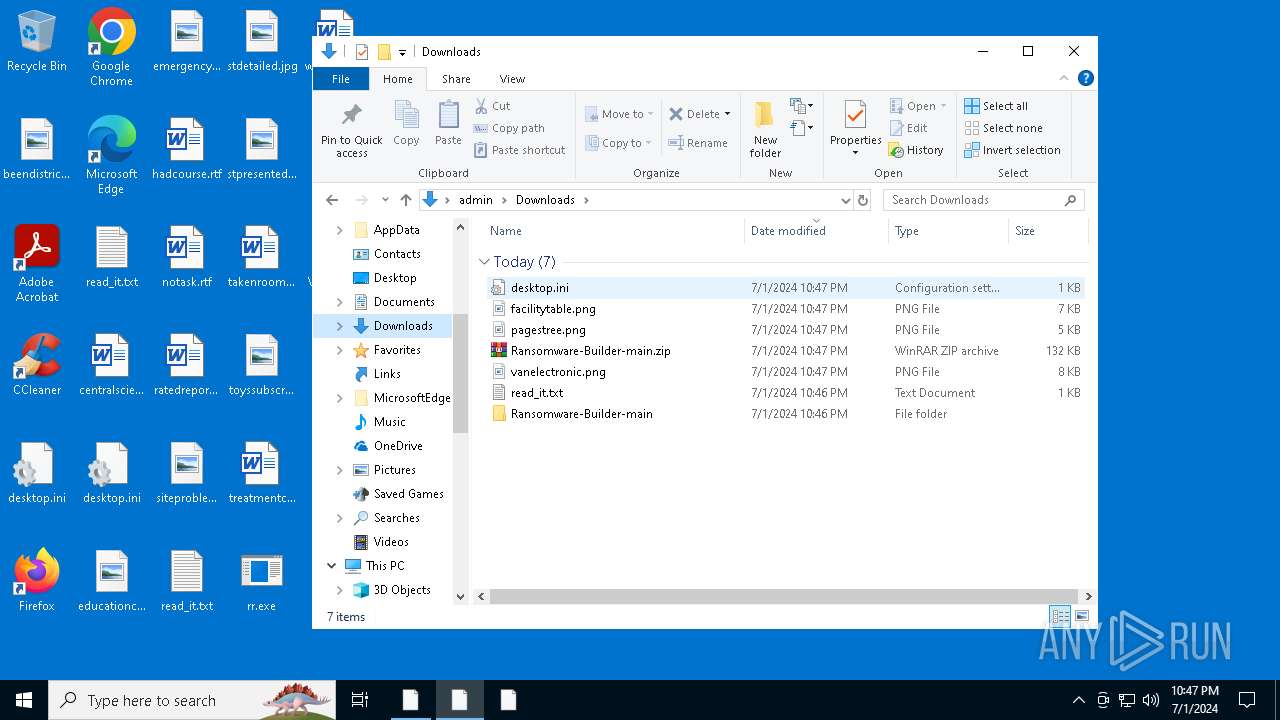
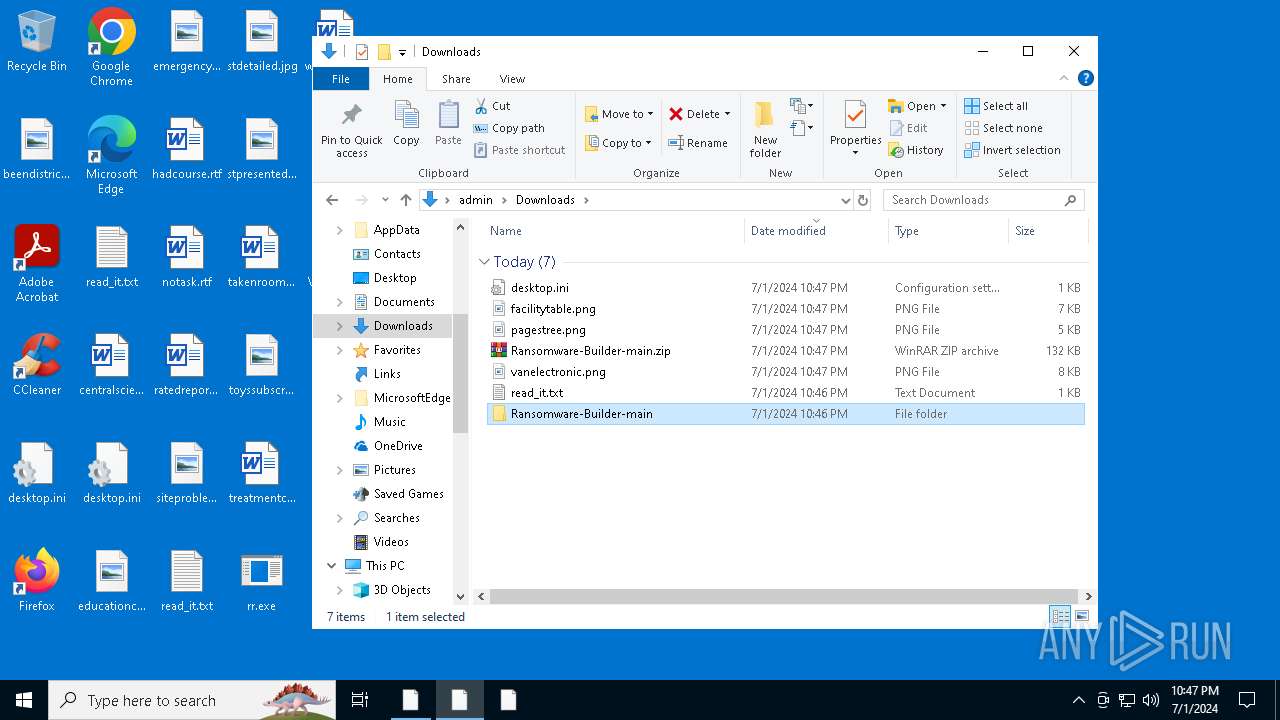
The process uses the downloaded file
- msedge.exe (PID: 3716)
- WinRAR.exe (PID: 6676)
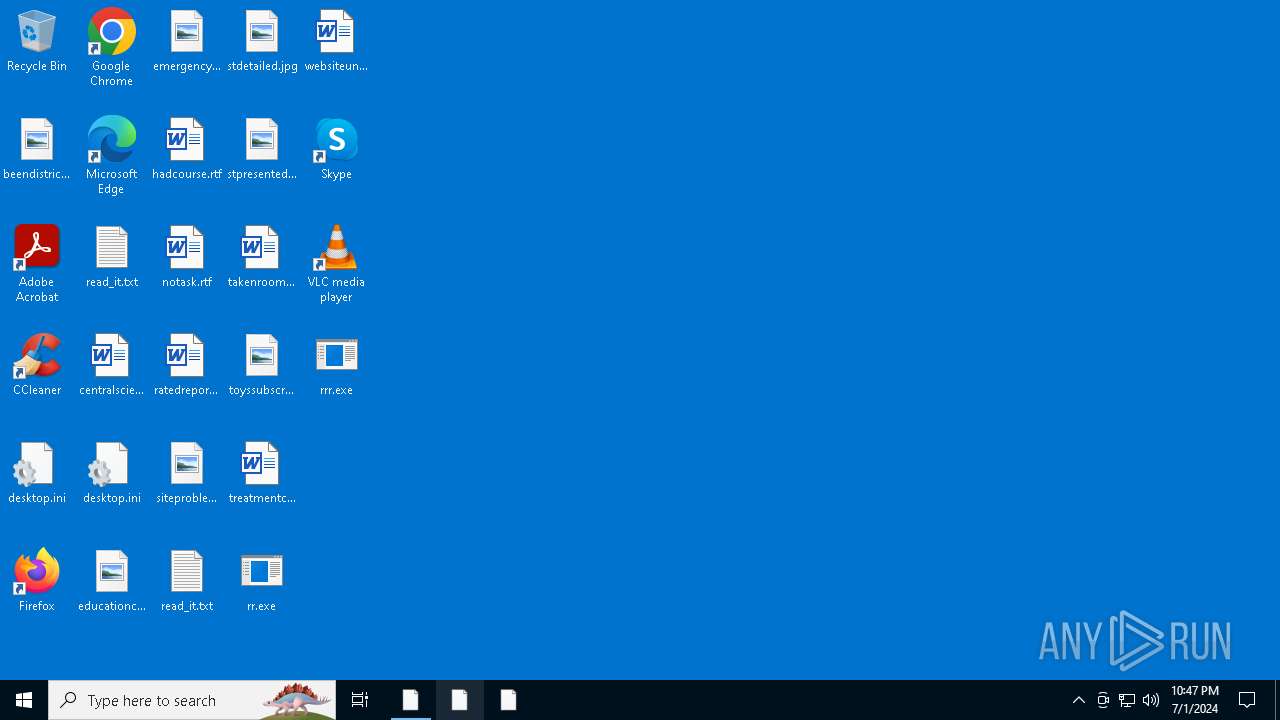
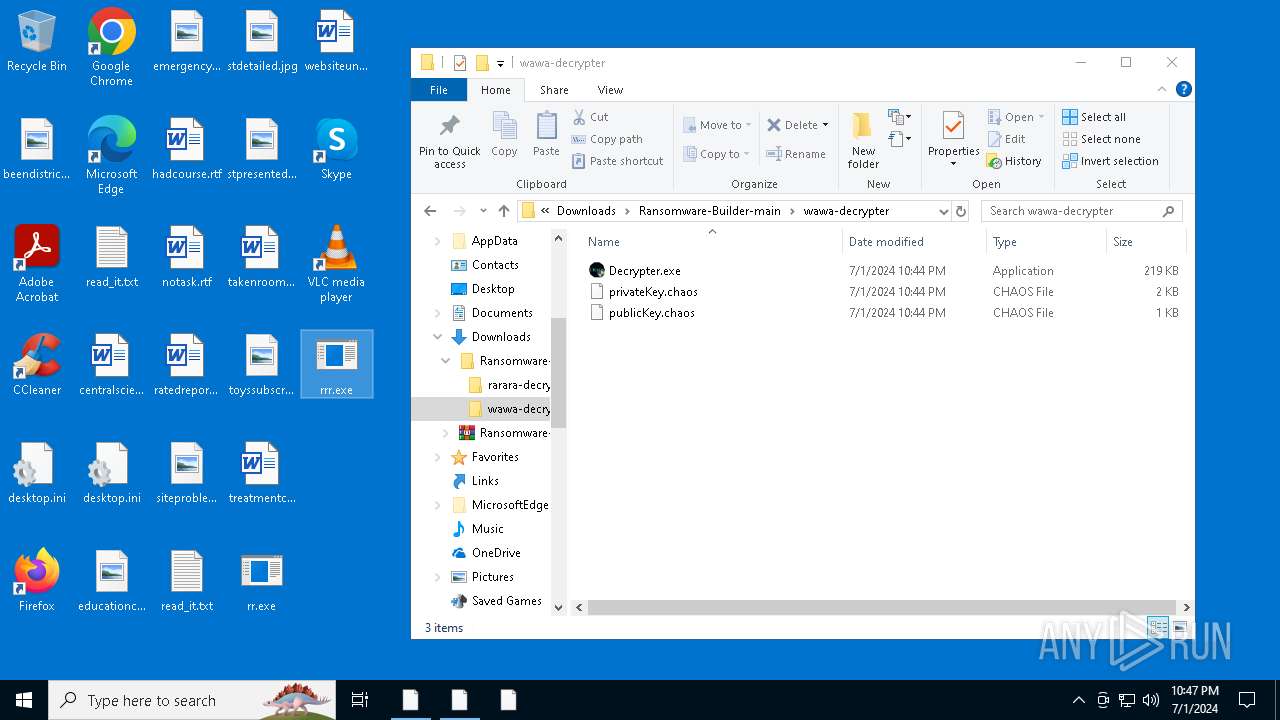
Manual execution by a user
- WinRAR.exe (PID: 6676)
- Chaos Ransomware Builder v4.exe (PID: 6692)
- Chaos Ransomware Builder v4.exe (PID: 6648)
- rr.exe (PID: 4812)
- notepad.exe (PID: 6964)
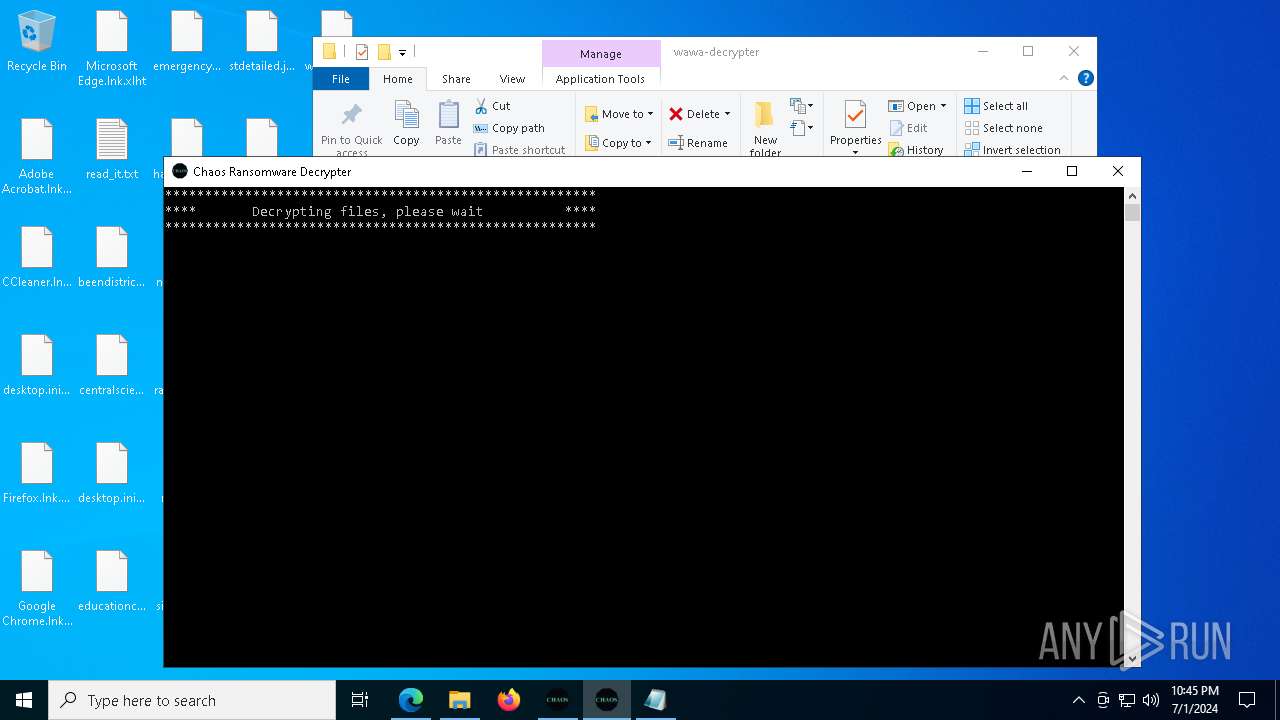
- Decrypter.exe (PID: 2916)
- Decrypter.exe (PID: 1224)
- Chaos Ransomware Builder v4.exe (PID: 6100)
- Chaos Ransomware Builder v4.exe (PID: 7076)
- rrr.exe (PID: 2392)
- Decrypter.exe (PID: 5268)
- rrr.exe (PID: 332)
- Decrypter.exe (PID: 6976)
- Decrypter.exe (PID: 5252)
- Decrypter.exe (PID: 6340)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6676)
Reads the machine GUID from the registry
- Chaos Ransomware Builder v4.exe (PID: 6648)
- csc.exe (PID: 3964)
- svchost.exe (PID: 6248)
- Decrypter.exe (PID: 2916)
- Chaos Ransomware Builder v4.exe (PID: 7076)
- csc.exe (PID: 4524)
- svchost.exe (PID: 6692)
- Decrypter.exe (PID: 6976)
- svchost.exe (PID: 2612)
- Decrypter.exe (PID: 5252)
Application launched itself
- msedge.exe (PID: 3104)
- msedge.exe (PID: 7108)
Create files in a temporary directory
- Chaos Ransomware Builder v4.exe (PID: 6648)
- cvtres.exe (PID: 4756)
- Decrypter.exe (PID: 2916)
- Chaos Ransomware Builder v4.exe (PID: 7076)
- cvtres.exe (PID: 916)
- svchost.exe (PID: 6692)
- Decrypter.exe (PID: 6976)
- svchost.exe (PID: 2612)
- Decrypter.exe (PID: 5252)
Creates files or folders in the user directory
- rr.exe (PID: 4812)
- svchost.exe (PID: 6248)
- Chaos Ransomware Builder v4.exe (PID: 7076)
- rrr.exe (PID: 2392)
- svchost.exe (PID: 6692)
- svchost.exe (PID: 2612)
- rrr.exe (PID: 332)
Process checks computer location settings
- rr.exe (PID: 4812)
- svchost.exe (PID: 6248)
- rrr.exe (PID: 2392)
- svchost.exe (PID: 6692)
- rrr.exe (PID: 332)
- svchost.exe (PID: 2612)
Reads security settings of Internet Explorer
- notepad.exe (PID: 6964)
- WMIC.exe (PID: 6764)
- notepad.exe (PID: 6604)
- WMIC.exe (PID: 6460)
- notepad.exe (PID: 6992)
- notepad.exe (PID: 436)
- WMIC.exe (PID: 6704)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
292
Monitored processes
137
Malicious processes
19
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 332 | "C:\Users\admin\Desktop\rrr.exe" | C:\Users\admin\Desktop\rrr.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 1 Version: 0.0.0.0 Modules
| |||||||||||||||
| 360 | "C:\WINDOWS\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe" -ServerName:InputApp.AppXjd5de1g66v206tj52m9d0dtpppx4cgpn.mca | C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Version: 123.26505.0.0 Modules
| |||||||||||||||
| 368 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2556 --field-trial-handle=2356,i,9611547076405390961,12824625942390455224,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 436 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Roaming\read_it.txt | C:\Windows\System32\notepad.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 692 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=3496 --field-trial-handle=2356,i,9611547076405390961,12824625942390455224,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 692 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4900 --field-trial-handle=2404,i,5640986907290347022,18090546265715522385,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 764 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\Windows\System32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 916 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 916 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES32BB.tmp" "c:\Users\admin\Desktop\CSCE187B687C10C44369716C21369C9BD6.TMP" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.32.31326.0 Modules
| |||||||||||||||
| 1224 | "C:\Users\admin\Downloads\Ransomware-Builder-main\wawa-decrypter\Decrypter.exe" | C:\Users\admin\Downloads\Ransomware-Builder-main\wawa-decrypter\Decrypter.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Chaos ransomware decrypter Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
81 784
Read events
81 231
Write events
472
Delete events
81
Modification events
| (PID) Process: | (3104) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3104) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3104) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3104) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3104) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3104) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3104) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3104) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
| (PID) Process: | (3104) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3104) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | urlstats |
Value: 0 | |||
Executable files
23
Suspicious files
628
Text files
1 660
Unknown types
36
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3104 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1ad7d3.TMP | — | |
MD5:— | SHA256:— | |||
| 3104 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1ad7d3.TMP | — | |
MD5:— | SHA256:— | |||
| 3104 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1ad7d3.TMP | — | |
MD5:— | SHA256:— | |||
| 3104 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1ad7d3.TMP | — | |
MD5:— | SHA256:— | |||
| 3104 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3104 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3104 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3104 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3104 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1ad7f2.TMP | — | |
MD5:— | SHA256:— | |||
| 3104 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
47
TCP/UDP connections
121
DNS requests
88
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6312 | svchost.exe | GET | 206 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/aad09a72-80db-4ffe-81ce-9b317e7d891b?P1=1720161624&P2=404&P3=2&P4=mP6C8kjmGwECnjdD%2f95LRi6MoG842Nx6g7271rL1Q2nZ64mcEvX%2bAJbjUKoCwaqxCTqPx8JeurLikJB3GER8Wg%3d%3d | unknown | — | — | unknown |
6312 | svchost.exe | GET | 206 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/aad09a72-80db-4ffe-81ce-9b317e7d891b?P1=1720161624&P2=404&P3=2&P4=mP6C8kjmGwECnjdD%2f95LRi6MoG842Nx6g7271rL1Q2nZ64mcEvX%2bAJbjUKoCwaqxCTqPx8JeurLikJB3GER8Wg%3d%3d | unknown | — | — | unknown |
6312 | svchost.exe | GET | 206 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/aad09a72-80db-4ffe-81ce-9b317e7d891b?P1=1720161624&P2=404&P3=2&P4=mP6C8kjmGwECnjdD%2f95LRi6MoG842Nx6g7271rL1Q2nZ64mcEvX%2bAJbjUKoCwaqxCTqPx8JeurLikJB3GER8Wg%3d%3d | unknown | — | — | unknown |
6312 | svchost.exe | GET | 206 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/aad09a72-80db-4ffe-81ce-9b317e7d891b?P1=1720161624&P2=404&P3=2&P4=mP6C8kjmGwECnjdD%2f95LRi6MoG842Nx6g7271rL1Q2nZ64mcEvX%2bAJbjUKoCwaqxCTqPx8JeurLikJB3GER8Wg%3d%3d | unknown | — | — | unknown |
1544 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
3040 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | unknown |
6808 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | unknown |
6928 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | unknown |
6312 | svchost.exe | HEAD | 200 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/aad09a72-80db-4ffe-81ce-9b317e7d891b?P1=1720161624&P2=404&P3=2&P4=mP6C8kjmGwECnjdD%2f95LRi6MoG842Nx6g7271rL1Q2nZ64mcEvX%2bAJbjUKoCwaqxCTqPx8JeurLikJB3GER8Wg%3d%3d | unknown | — | — | unknown |
6500 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3560 | RUXIMICS.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
5784 | MoUsoCoreWorker.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
368 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
3104 | msedge.exe | 239.255.255.250:1900 | — | — | — | unknown |
368 | msedge.exe | 140.82.121.3:443 | github.com | GITHUB | US | unknown |
368 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
368 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
368 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.edge.skype.com |
| whitelisted |
github.com |
| shared |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| unknown |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
github.githubassets.com |
| whitelisted |
avatars.githubusercontent.com |
| whitelisted |
www.bing.com |
| whitelisted |
user-images.githubusercontent.com |
| whitelisted |
Threats
Process | Message |
|---|---|
wbadmin.exe | Invalid parameter passed to C runtime function.
|
wbadmin.exe | Invalid parameter passed to C runtime function.
|
wbadmin.exe | Invalid parameter passed to C runtime function.
|