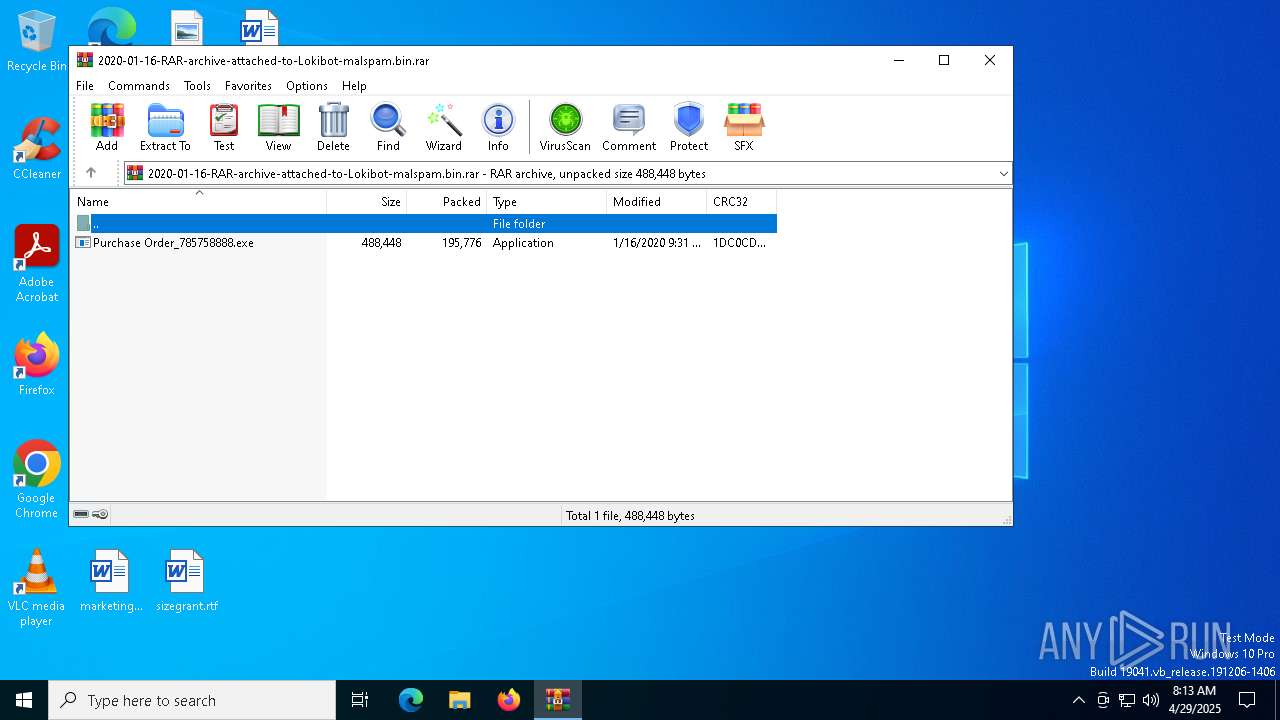
| File name: | 2020-01-16-RAR-archive-attached-to-Lokibot-malspam.bin |
| Full analysis: | https://app.any.run/tasks/287a1020-c878-4864-882d-a526f5cb97a3 |
| Verdict: | Malicious activity |
| Threats: | LokiBot was developed in 2015 to steal information from a variety of applications. Despite the age, this malware is still rather popular among cybercriminals. |
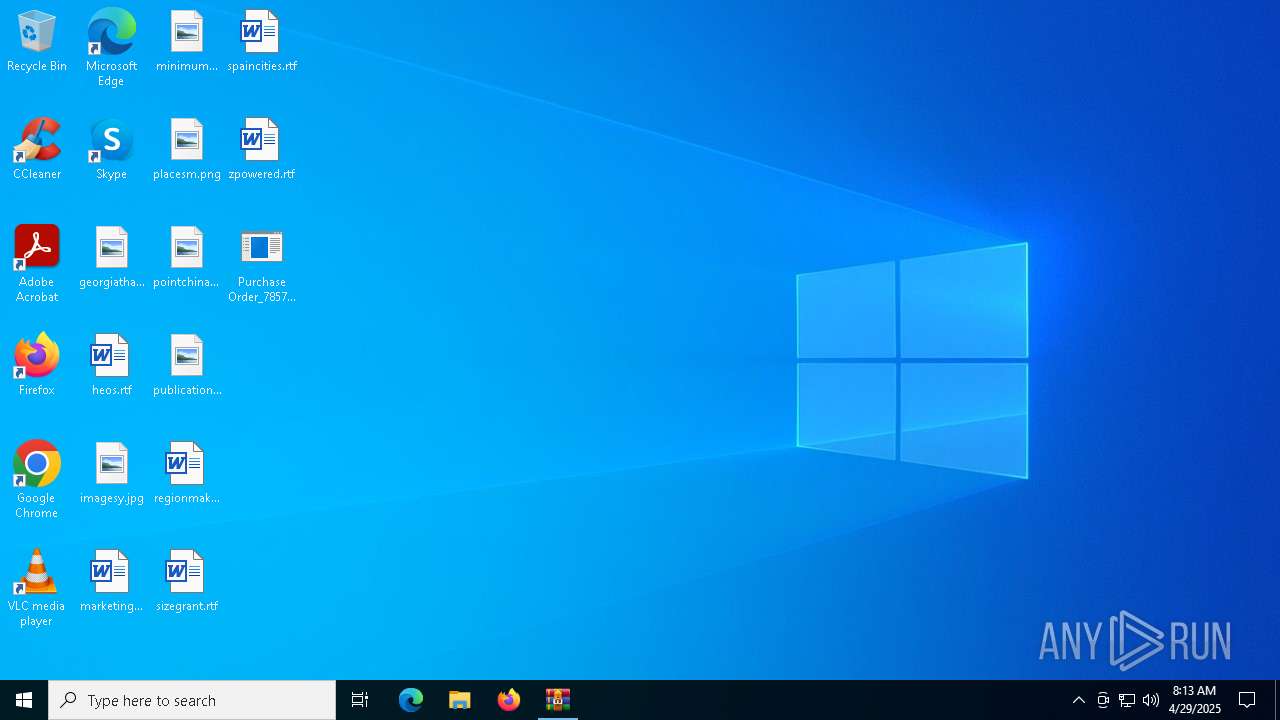
| Analysis date: | April 29, 2025, 08:12:57 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 90C4A56B9806E2DD30965DA4E72113AF |
| SHA1: | 9F2648385CCF1E21D75E6009E6E973F5AF5E6C75 |
| SHA256: | F8D477D295B0436DD0C156AB77EFBCAC4262ACD0B37FC17F08EA1E8E1BE4F444 |
| SSDEEP: | 6144:e9cPyh4dPDtgP6VwoVr5cyrZ6oi9X+b0RbyMMOGStR:DddPD+mwk5bEdwUpMKD |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 2100)
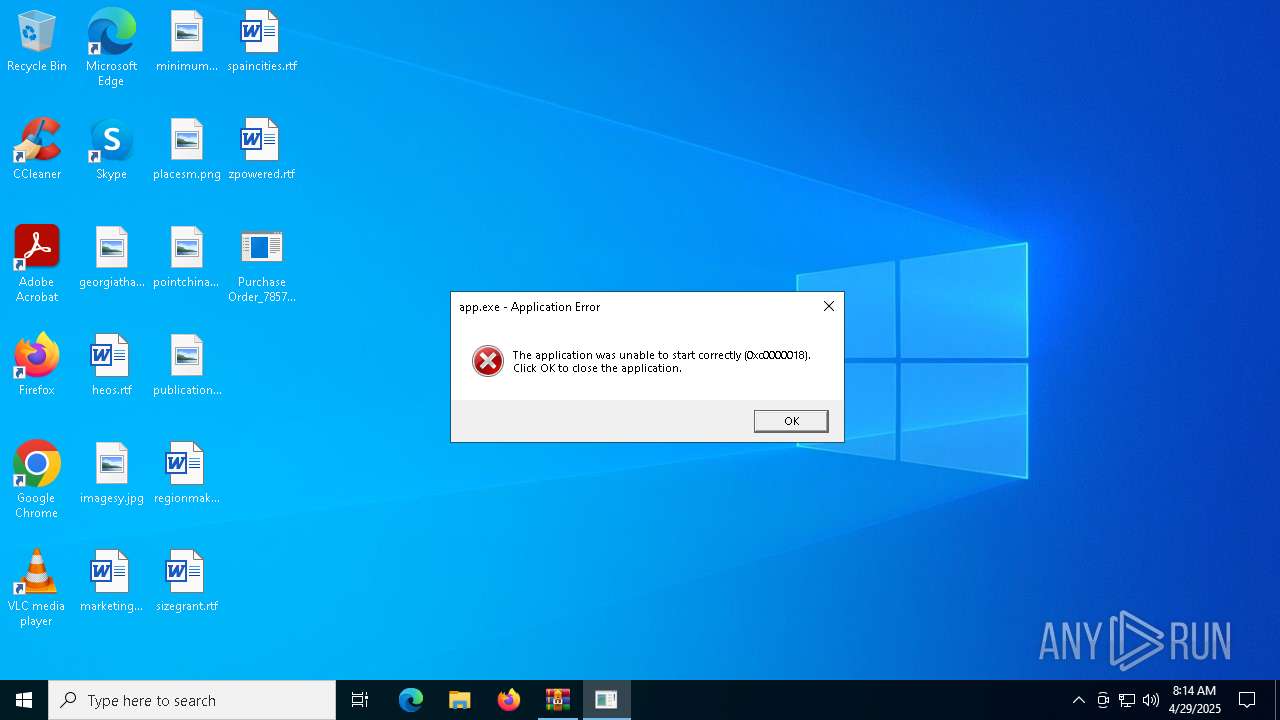
Changes the autorun value in the registry
- app.exe (PID: 1388)
XORed URL has been found (YARA)
- app.exe (PID: 6960)
LOKIBOT has been detected (YARA)
- app.exe (PID: 6960)
SUSPICIOUS
Reads security settings of Internet Explorer
- Purchase Order_785758888.exe (PID: 208)
- app.exe (PID: 1388)
Executable content was dropped or overwritten
- cmd.exe (PID: 6192)
Starts CMD.EXE for commands execution
- Purchase Order_785758888.exe (PID: 208)
The executable file from the user directory is run by the CMD process
- app.exe (PID: 1388)
Application launched itself
- app.exe (PID: 1388)
INFO
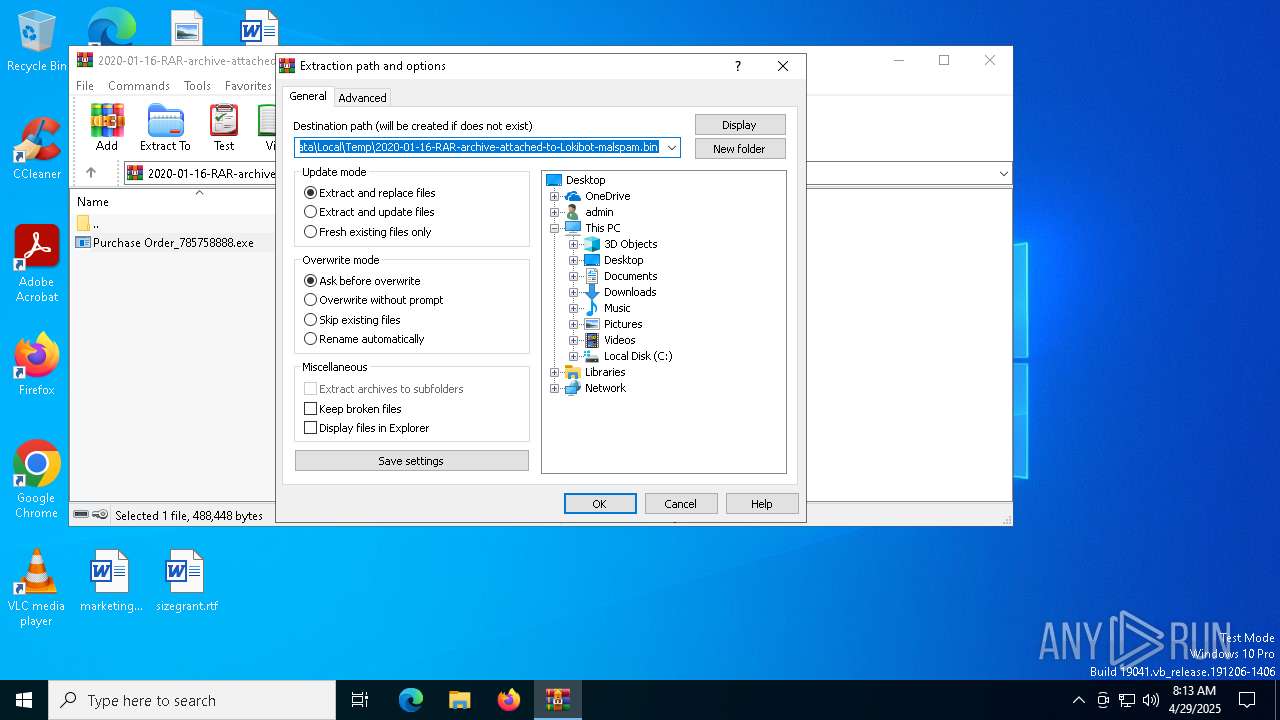
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2100)
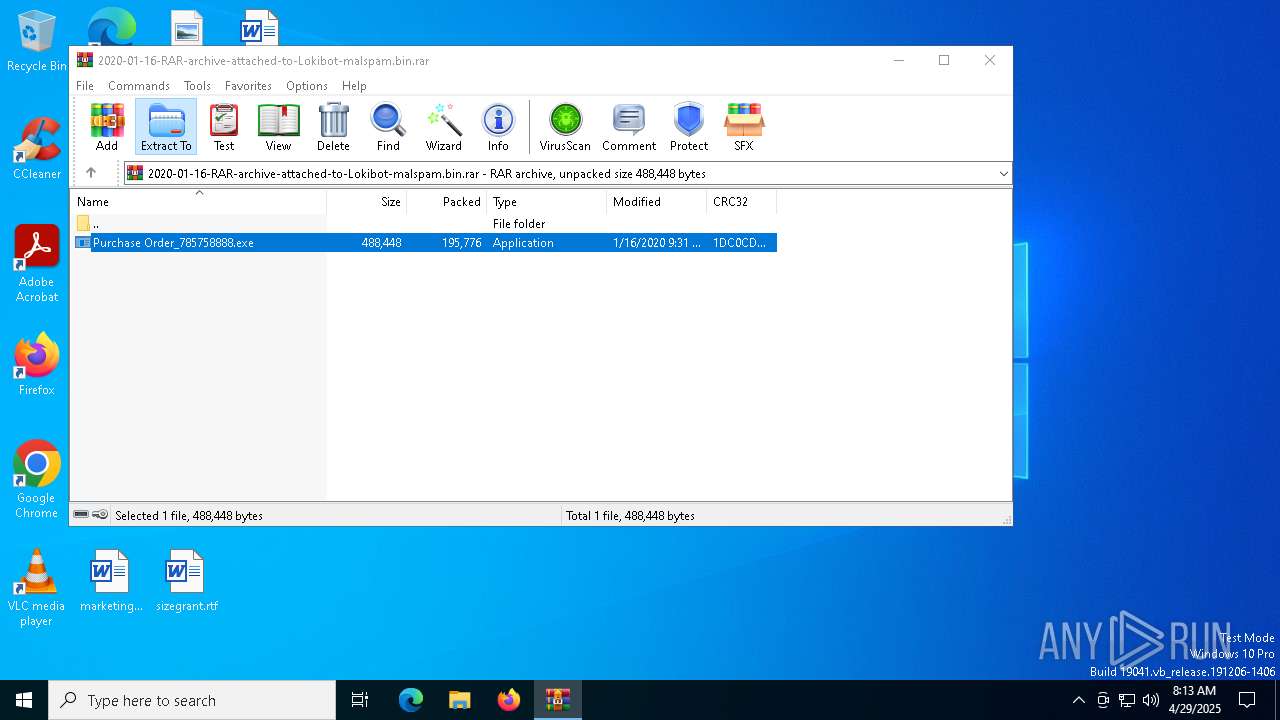
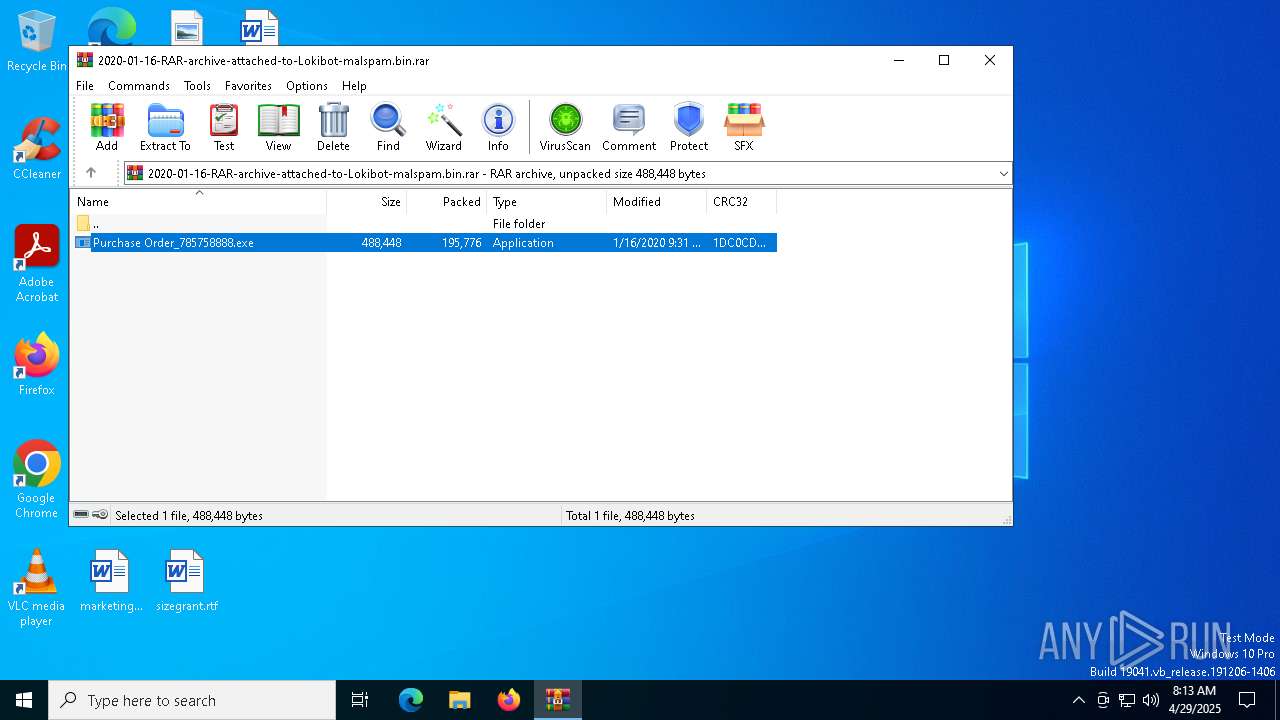
Manual execution by a user
- Purchase Order_785758888.exe (PID: 208)
Checks supported languages
- Purchase Order_785758888.exe (PID: 208)
- app.exe (PID: 1388)
Reads the computer name
- Purchase Order_785758888.exe (PID: 208)
- app.exe (PID: 1388)
Reads the machine GUID from the registry
- Purchase Order_785758888.exe (PID: 208)
- app.exe (PID: 1388)
Process checks computer location settings
- Purchase Order_785758888.exe (PID: 208)
Reads the software policy settings
- slui.exe (PID: 6988)
- slui.exe (PID: 6640)
Checks proxy server information
- slui.exe (PID: 6640)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
xor-url
(PID) Process(6960) app.exe
Decrypted-URLs (1)http://himkon.ga/amaswitch/fre.php
LokiBot
(PID) Process(6960) app.exe
C2http://himkon.ga/amaswitch/fre.php
Decoys (4)kbfvzoboss.bid/alien/fre.php
alphastand.trade/alien/fre.php
alphastand.win/alien/fre.php
alphastand.top/alien/fre.php
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 195776 |
| UncompressedSize: | 488448 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | Purchase Order_785758888.exe |
Total processes
144
Monitored processes
11
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | "C:\Users\admin\Desktop\Purchase Order_785758888.exe" | C:\Users\admin\Desktop\Purchase Order_785758888.exe | — | explorer.exe | |||||||||||
User: admin Company: y}6KF8m%4$Rwo7?D3T Integrity Level: MEDIUM Description: Hn5+x2$F-zM7tE3 Exit code: 0 Version: 9.14.18.23 Modules
| |||||||||||||||
| 1184 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1388 | "C:\Users\admin\Documents\app.exe" | C:\Users\admin\Documents\app.exe | cmd.exe | ||||||||||||
User: admin Company: y}6KF8m%4$Rwo7?D3T Integrity Level: MEDIUM Description: Hn5+x2$F-zM7tE3 Exit code: 0 Version: 9.14.18.23 Modules
| |||||||||||||||
| 1912 | "C:\Windows\System32\cmd.exe" /c, "C:\Users\admin\Documents\app.exe" | C:\Windows\SysWOW64\cmd.exe | — | Purchase Order_785758888.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2100 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\2020-01-16-RAR-archive-attached-to-Lokibot-malspam.bin.rar | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 2136 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5260 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6192 | "C:\Windows\System32\cmd.exe" /c copy "C:\Users\admin\Desktop\Purchase Order_785758888.exe" "C:\Users\admin\Documents\app.exe" | C:\Windows\SysWOW64\cmd.exe | Purchase Order_785758888.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6640 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6960 | "C:\Users\admin\Documents\app.exe" | C:\Users\admin\Documents\app.exe | app.exe | ||||||||||||
User: admin Company: y}6KF8m%4$Rwo7?D3T Integrity Level: MEDIUM Description: Hn5+x2$F-zM7tE3 Exit code: 3221225496 Version: 9.14.18.23 Modules
xor-url(PID) Process(6960) app.exe Decrypted-URLs (1)http://himkon.ga/amaswitch/fre.php LokiBot(PID) Process(6960) app.exe C2http://himkon.ga/amaswitch/fre.php Decoys (4)kbfvzoboss.bid/alien/fre.php alphastand.trade/alien/fre.php alphastand.win/alien/fre.php alphastand.top/alien/fre.php | |||||||||||||||
Total events
9 568
Read events
9 543
Write events
12
Delete events
13
Modification events
| (PID) Process: | (2100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (2100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\2020-01-16-RAR-archive-attached-to-Lokibot-malspam.bin.rar | |||
| (PID) Process: | (2100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (2100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
Executable files
2
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6192 | cmd.exe | C:\Users\admin\Documents\app.exe | executable | |
MD5:809605E1089B9A8652F3E381852E93BC | SHA256:5C4699B94F18589AC3C81E2C498567458AF02EE5954FA9CC0BCA4C6886782157 | |||
| 2100 | WinRAR.exe | C:\Users\admin\Desktop\Purchase Order_785758888.exe | executable | |
MD5:809605E1089B9A8652F3E381852E93BC | SHA256:5C4699B94F18589AC3C81E2C498567458AF02EE5954FA9CC0BCA4C6886782157 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
39
DNS requests
20
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 20.190.160.128:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2112 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5968 | SIHClient.exe | 4.175.87.197:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5968 | SIHClient.exe | 20.3.187.198:443 | fe3cr.delivery.mp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6988 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
198.187.3.20.in-addr.arpa |
| unknown |
d.4.1.9.1.6.7.1.0.0.0.0.0.0.0.0.1.0.0.9.0.0.1.f.1.1.1.0.1.0.a.2.ip6.arpa |
| unknown |
nexusrules.officeapps.live.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |