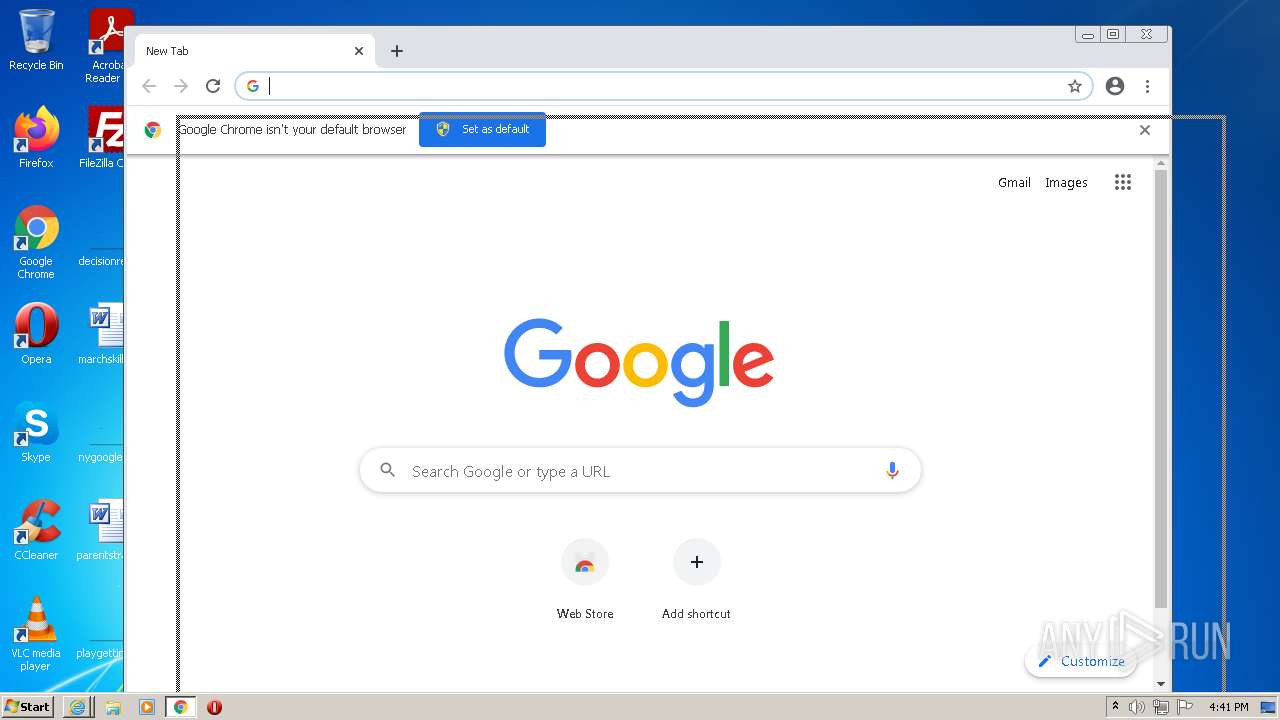
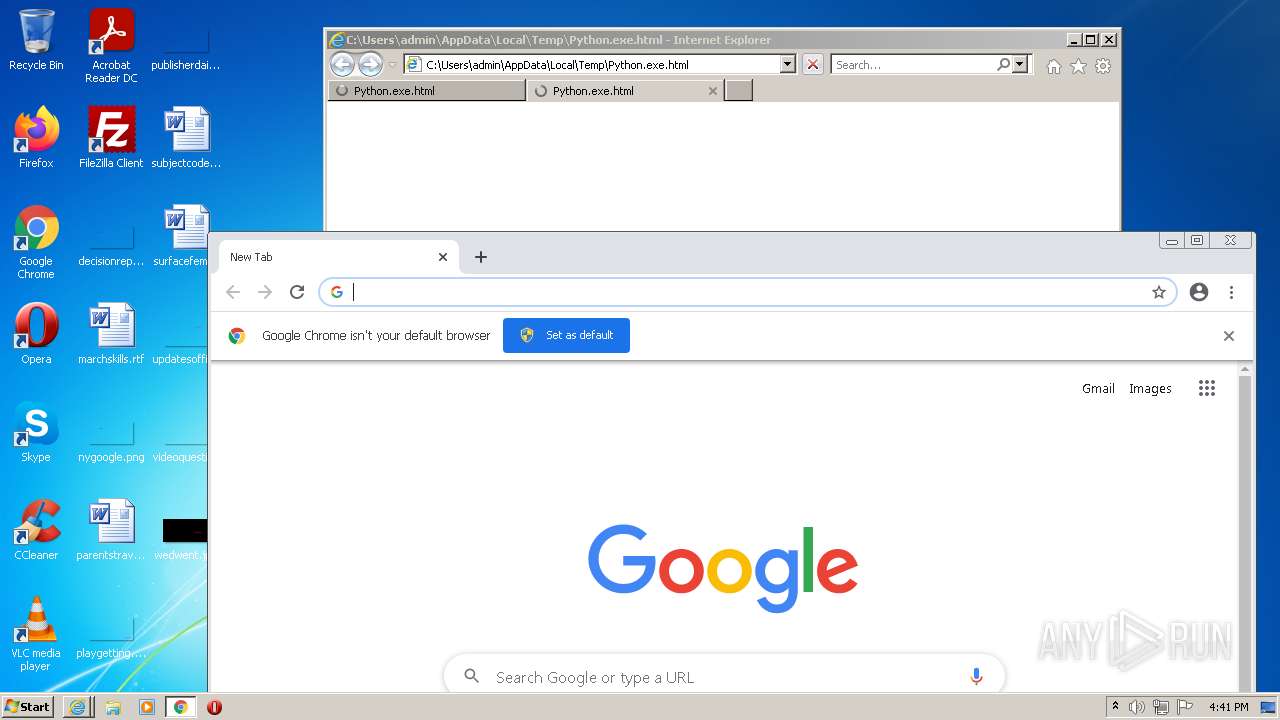
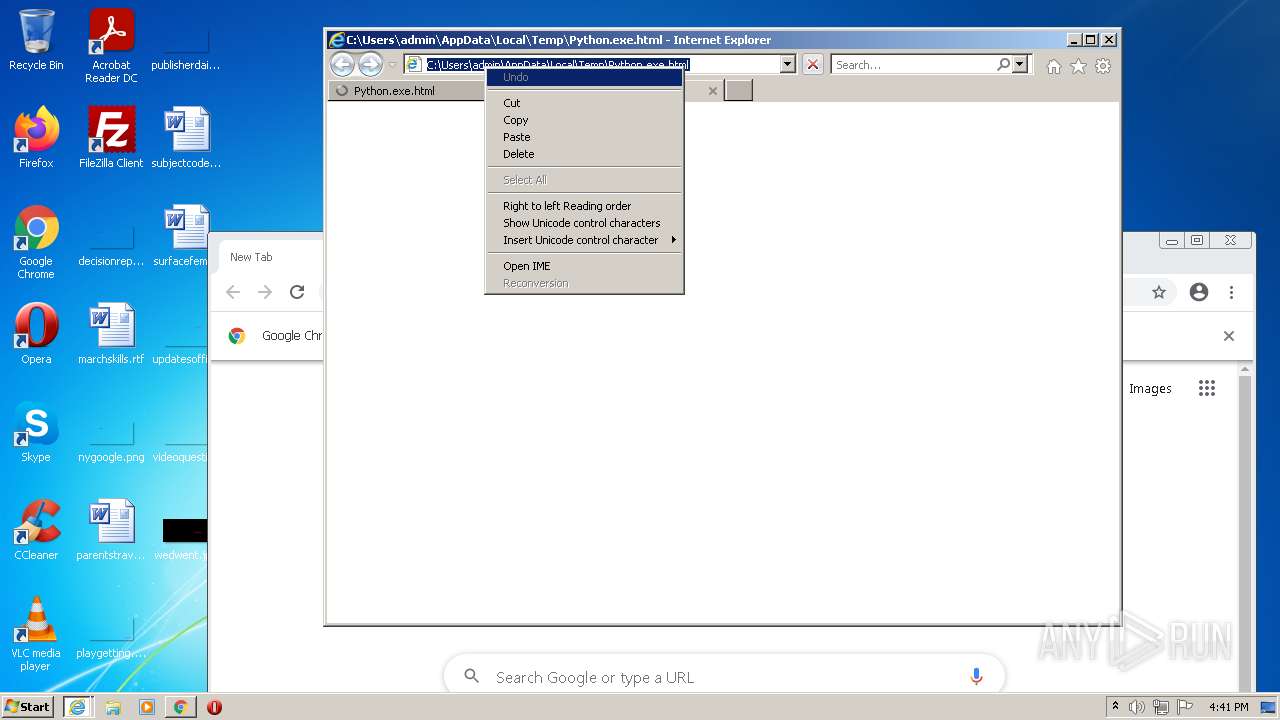
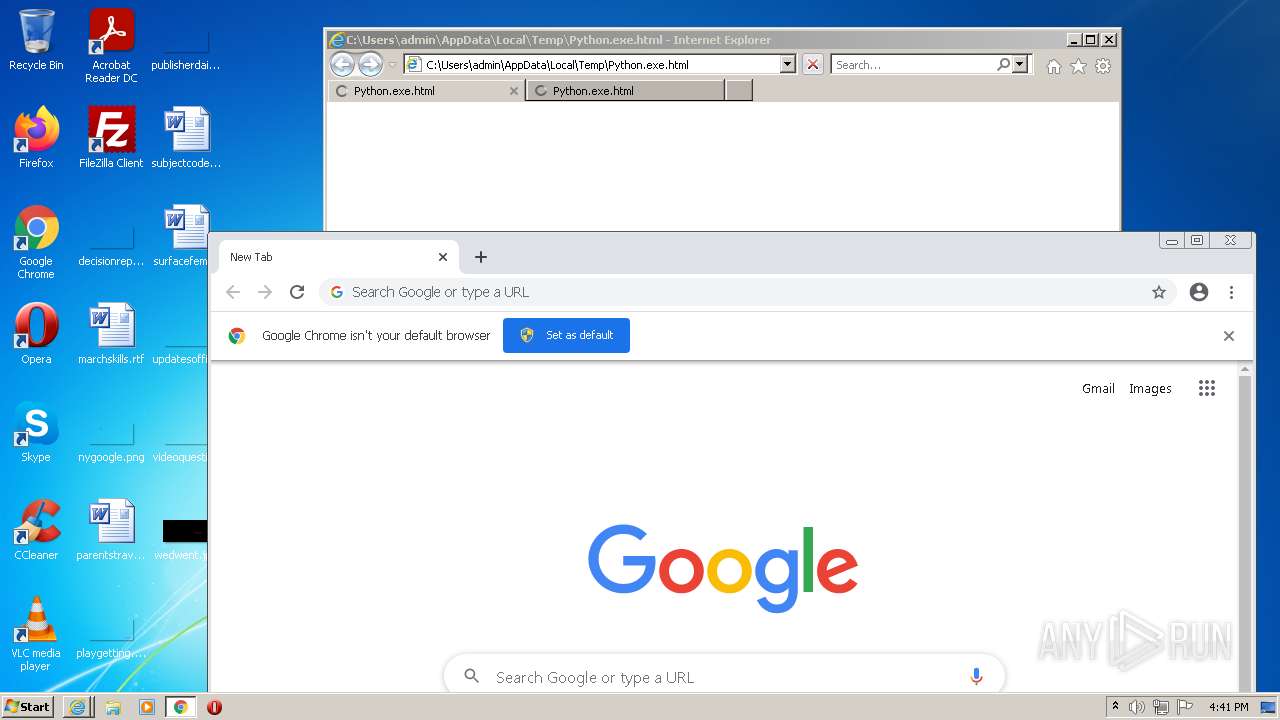
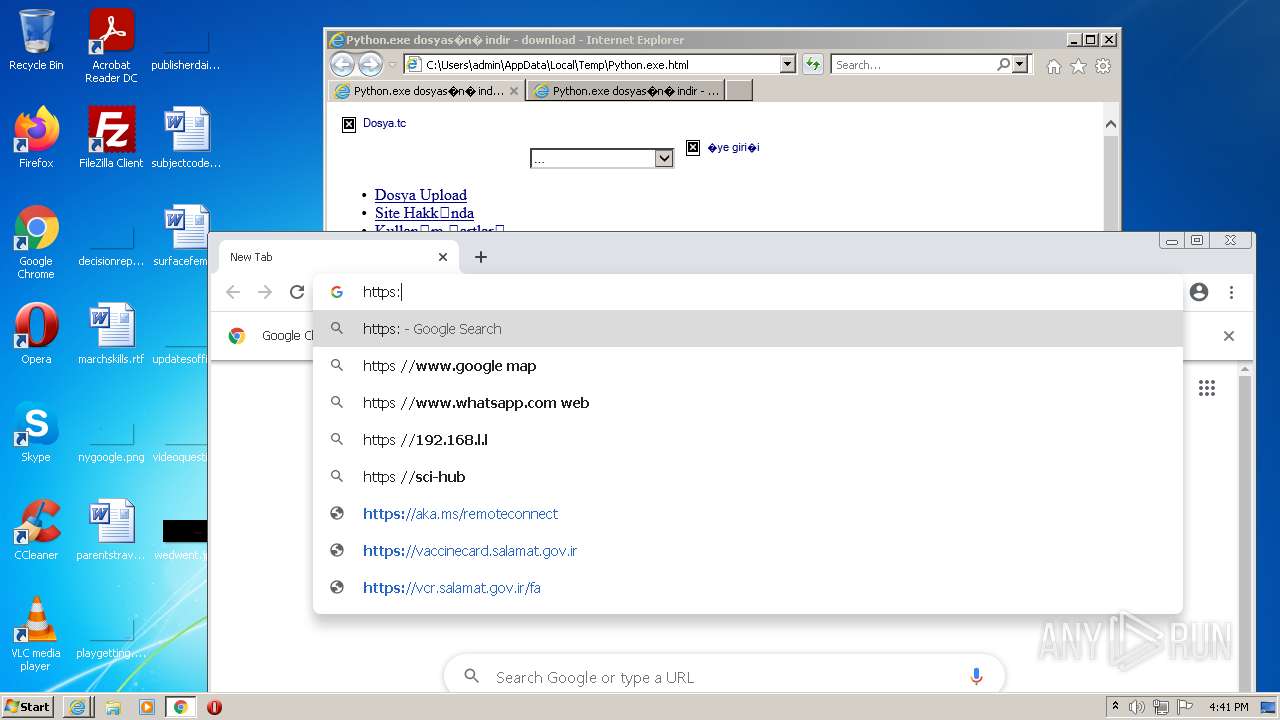
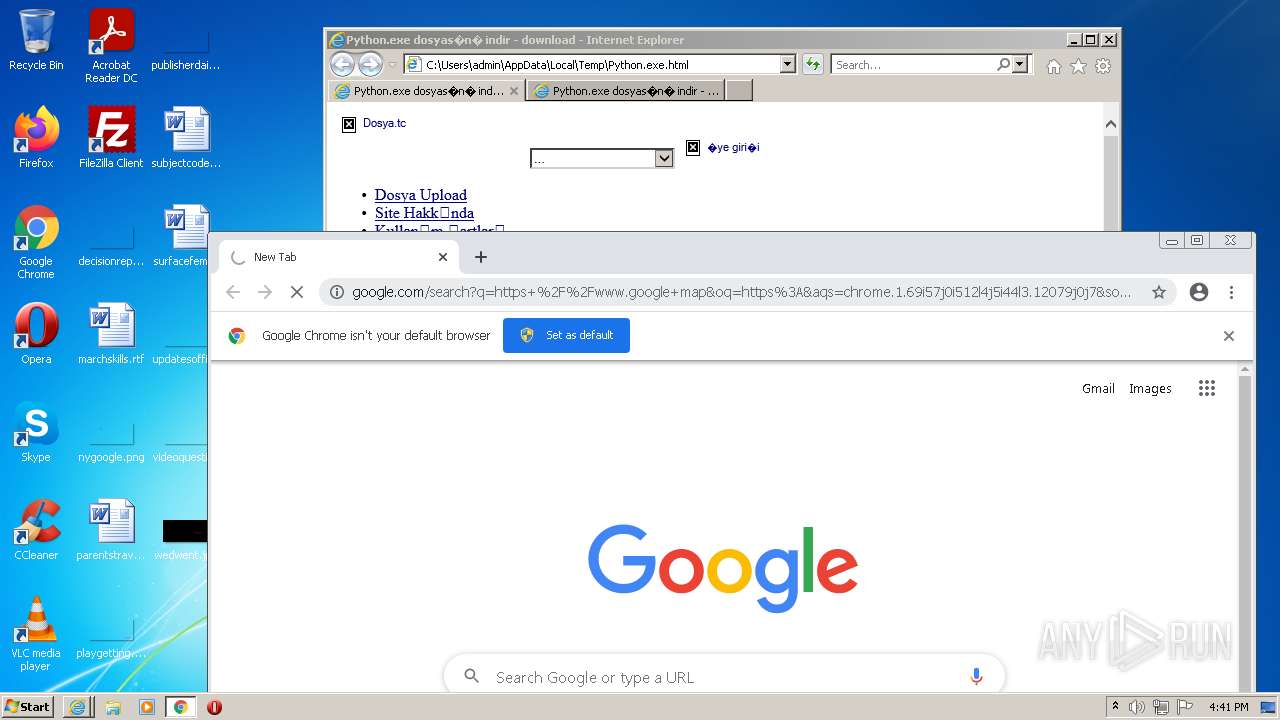
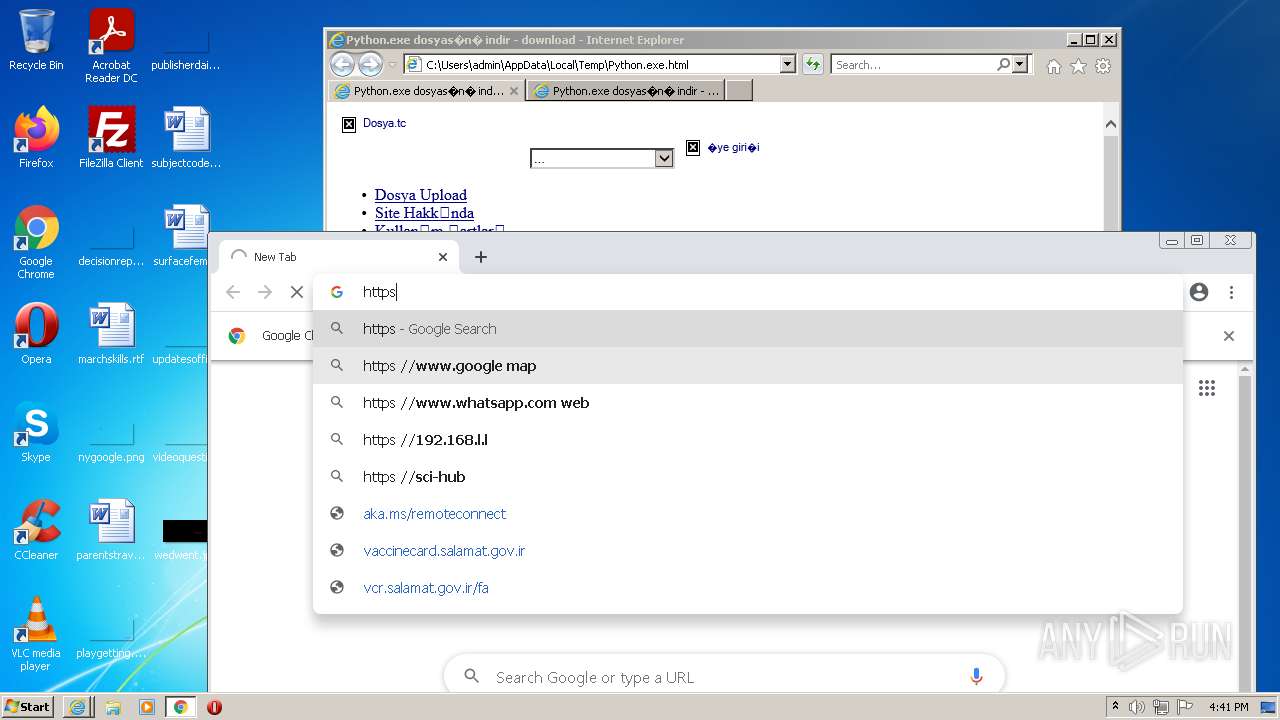
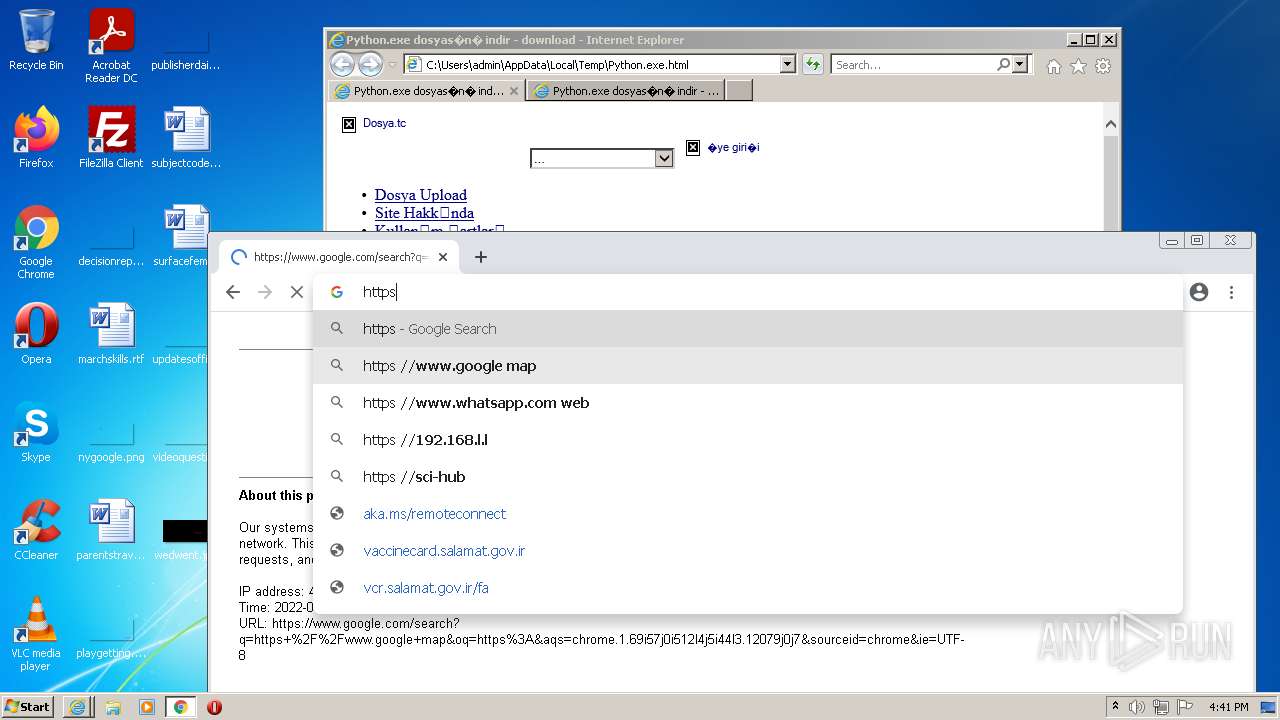
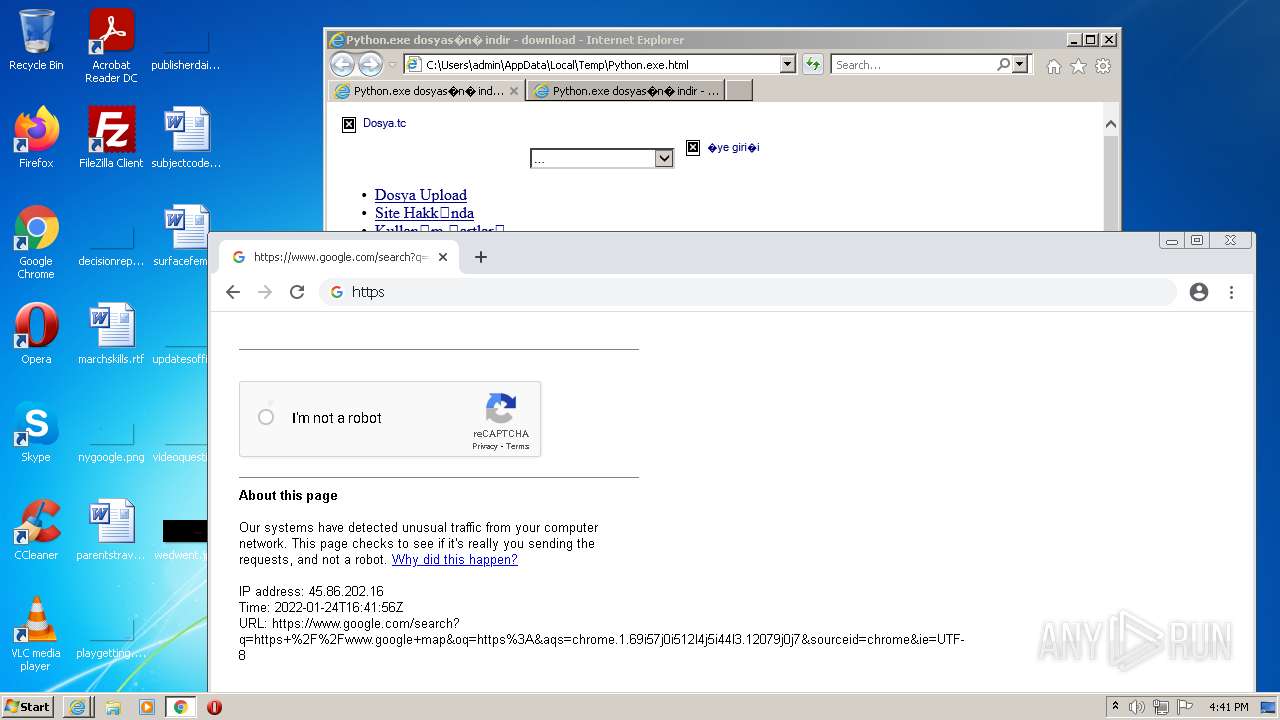
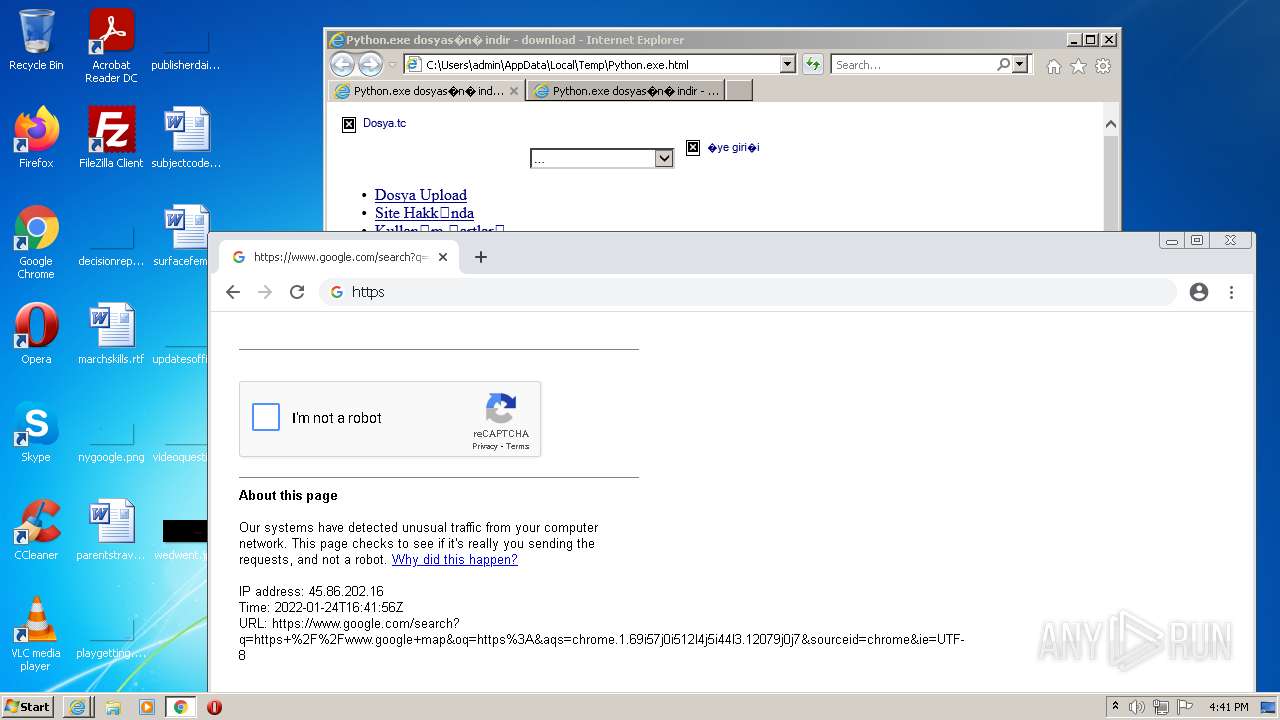
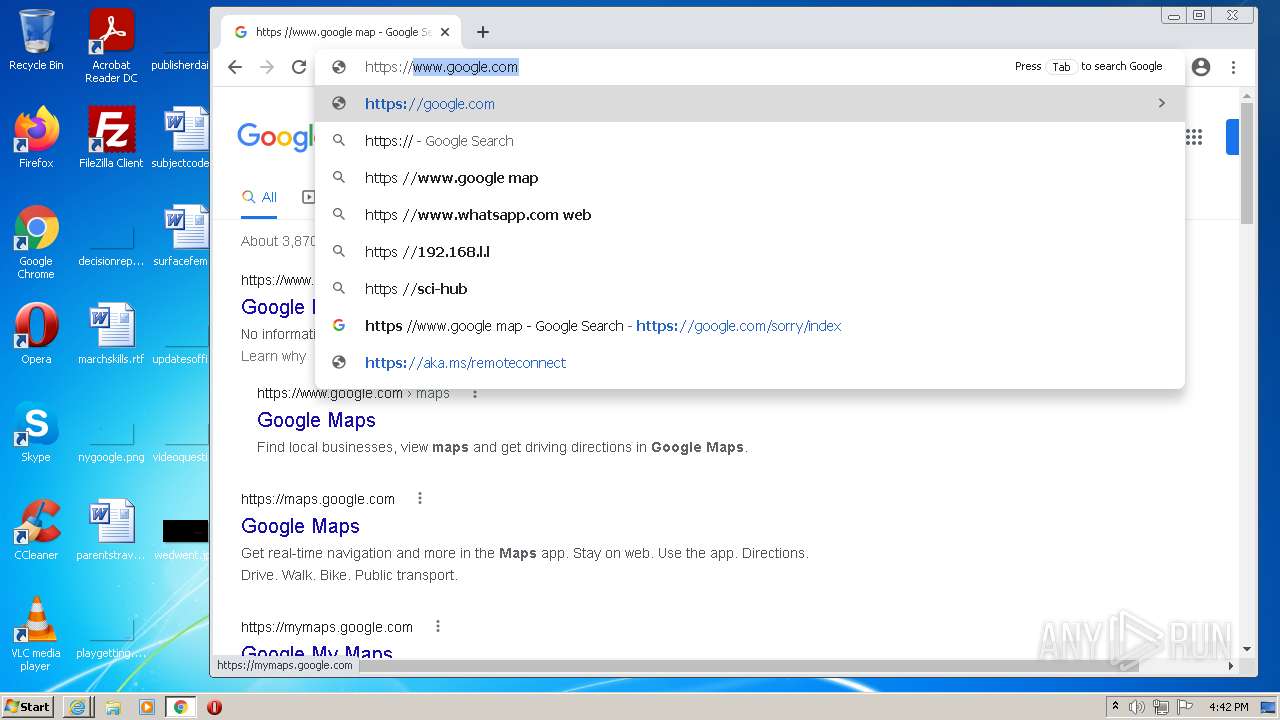
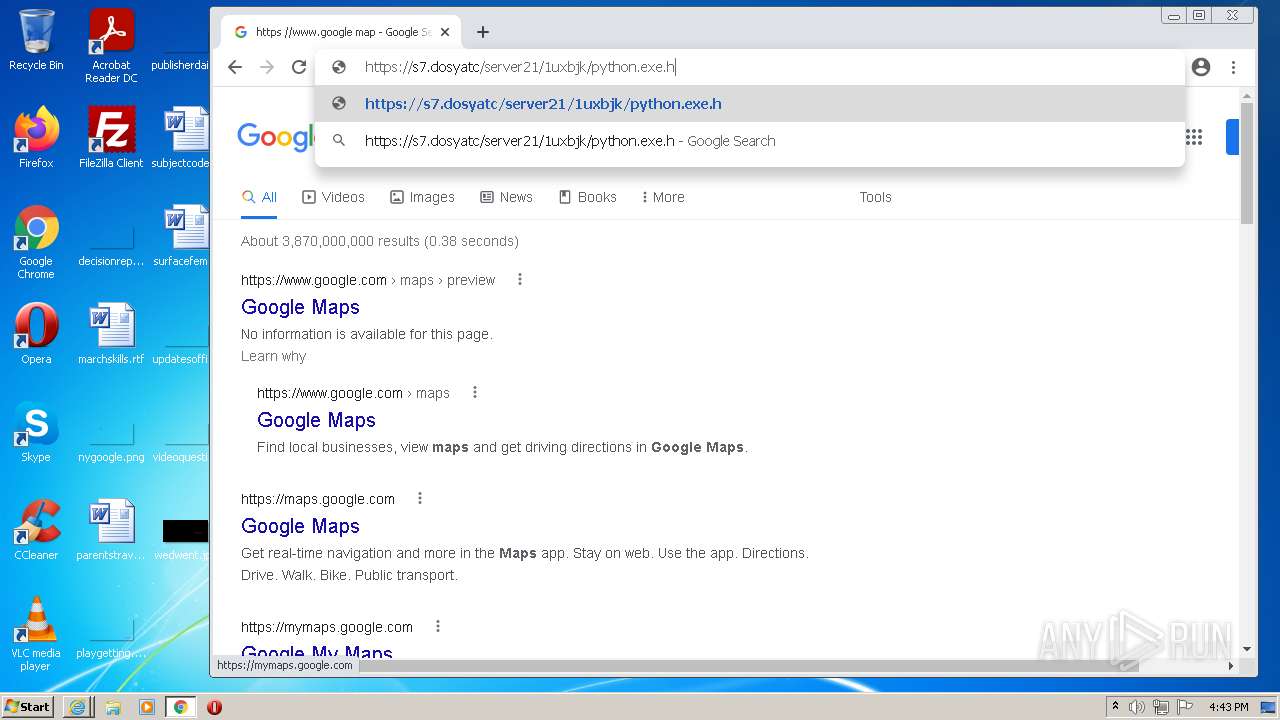
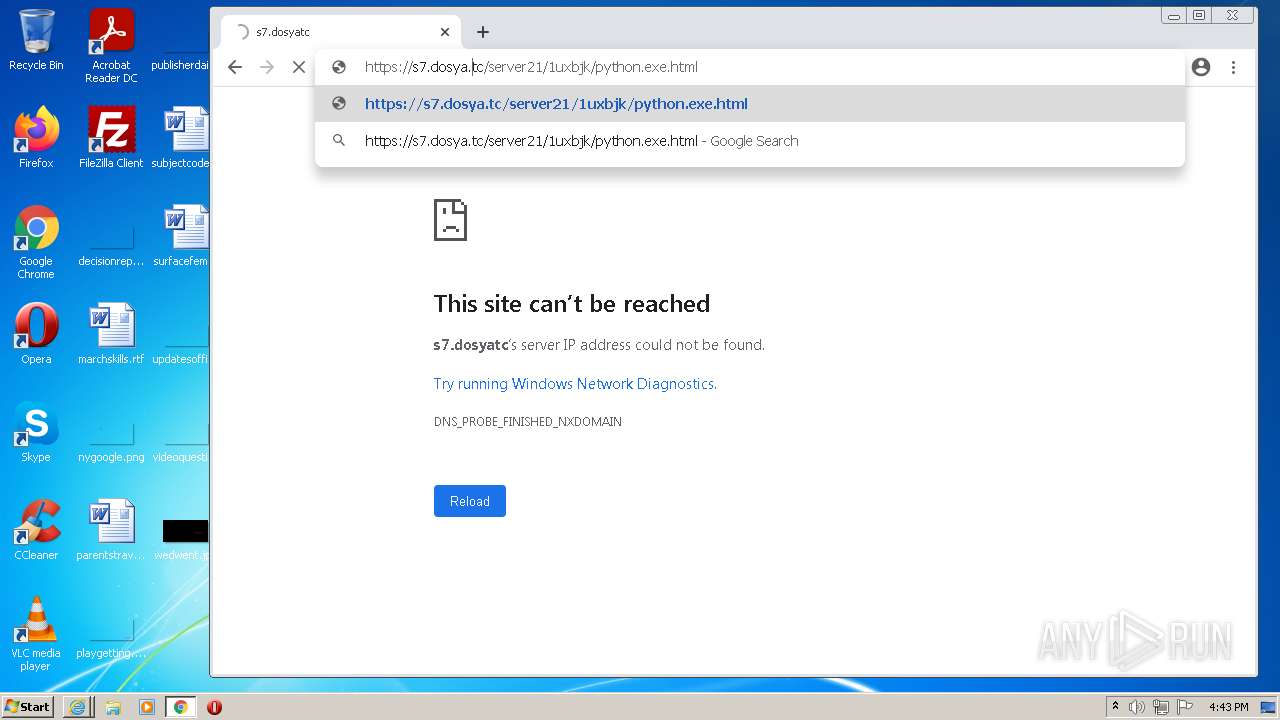
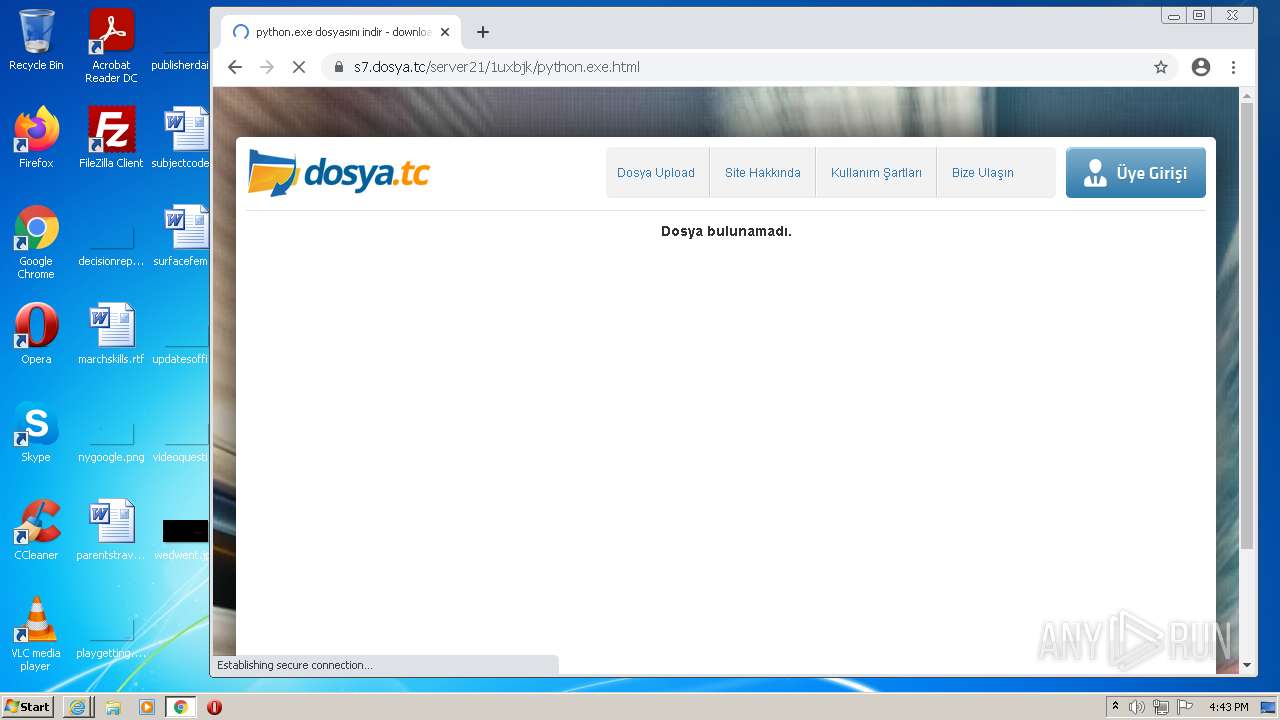
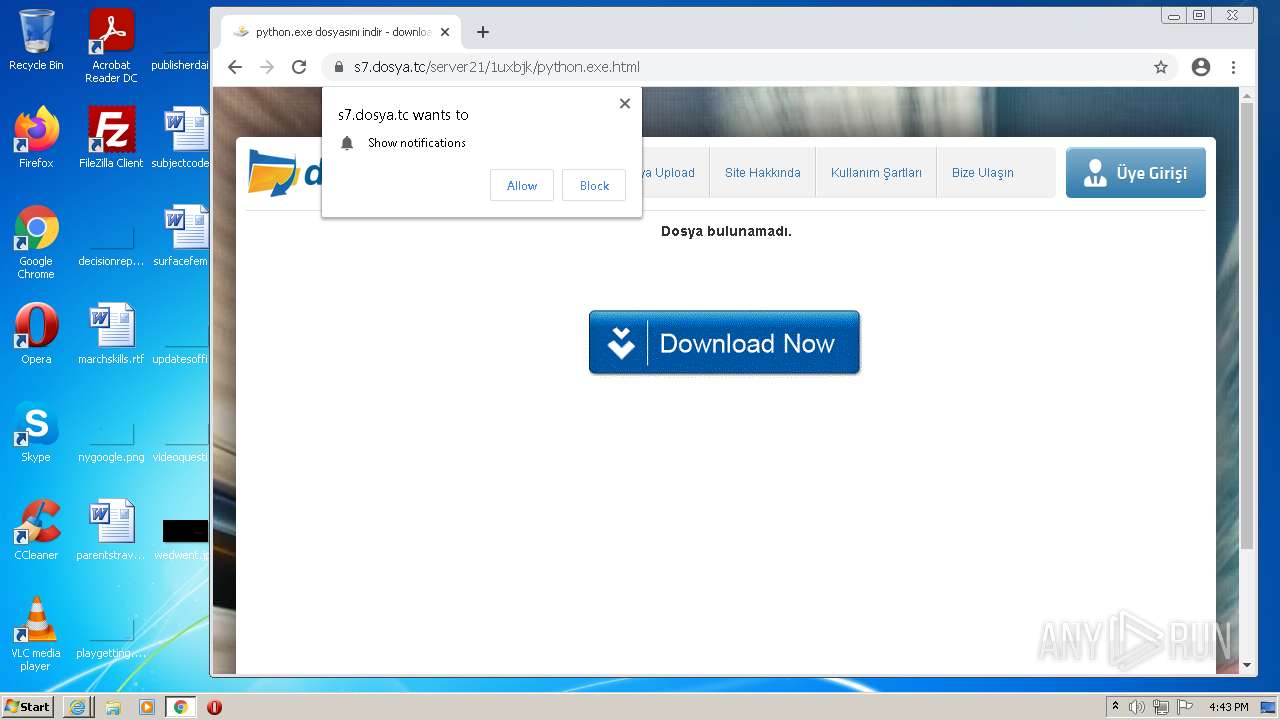
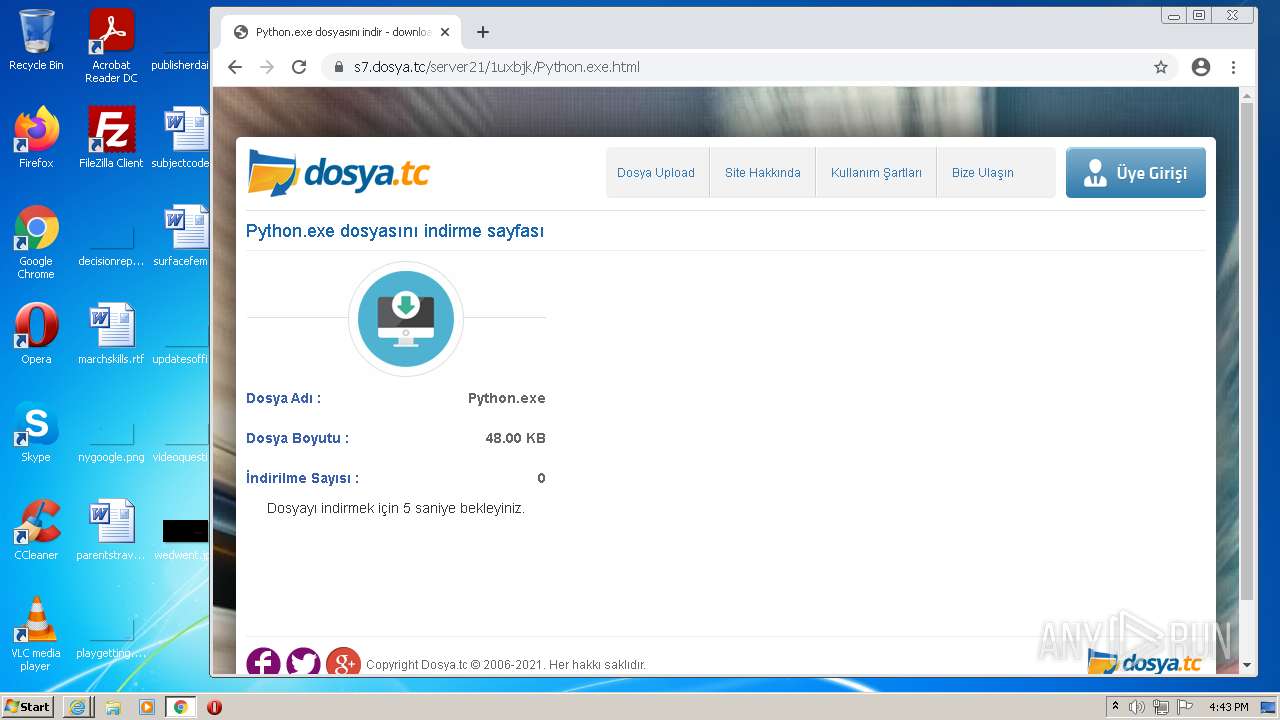
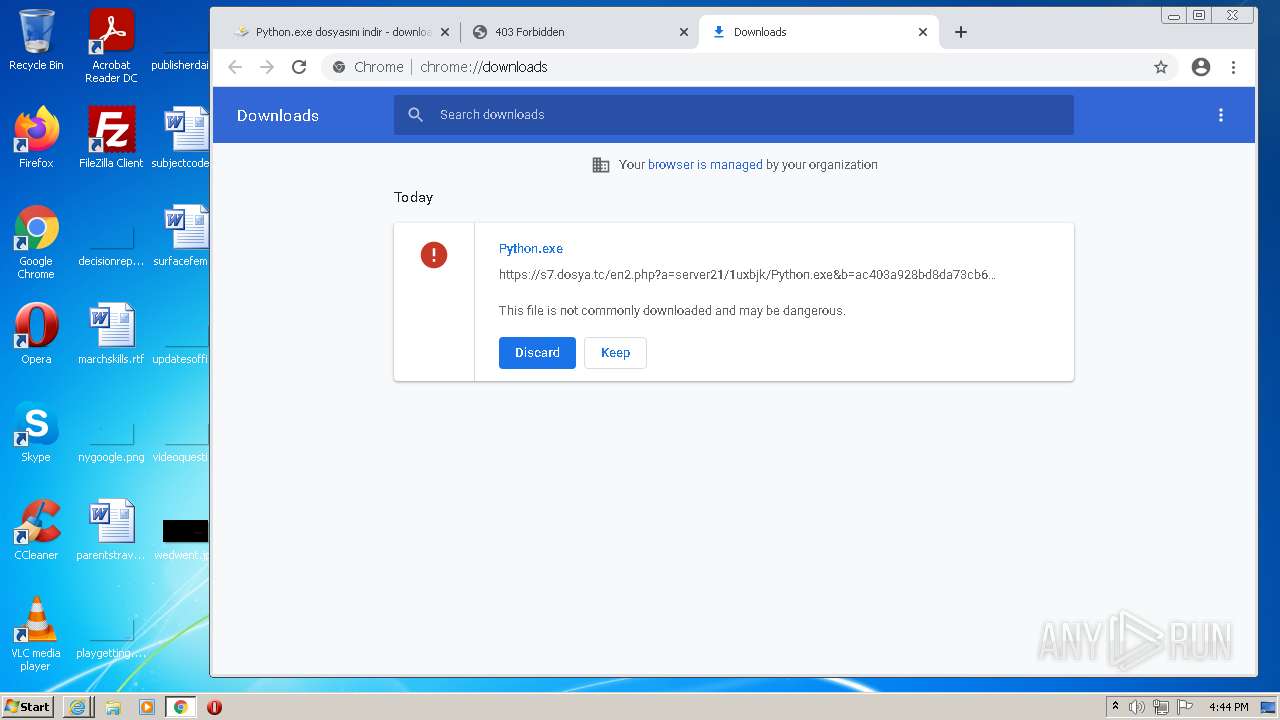
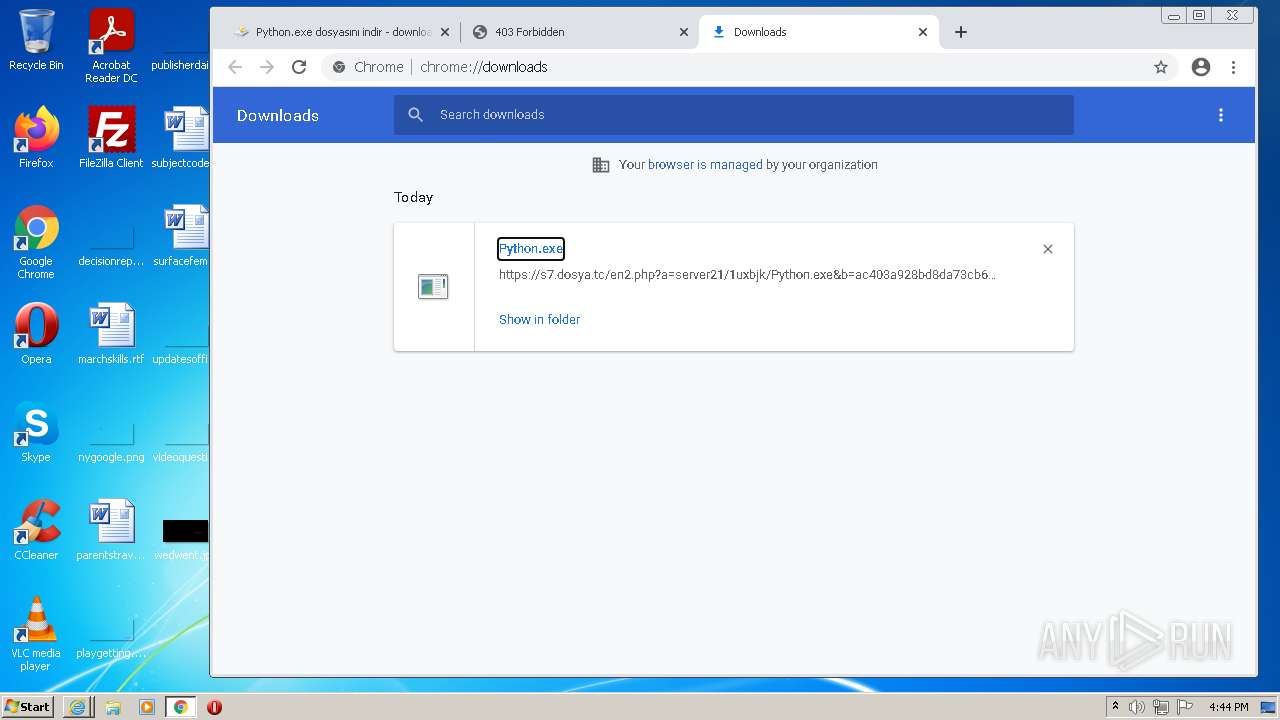
| download: | Python.exe.html |
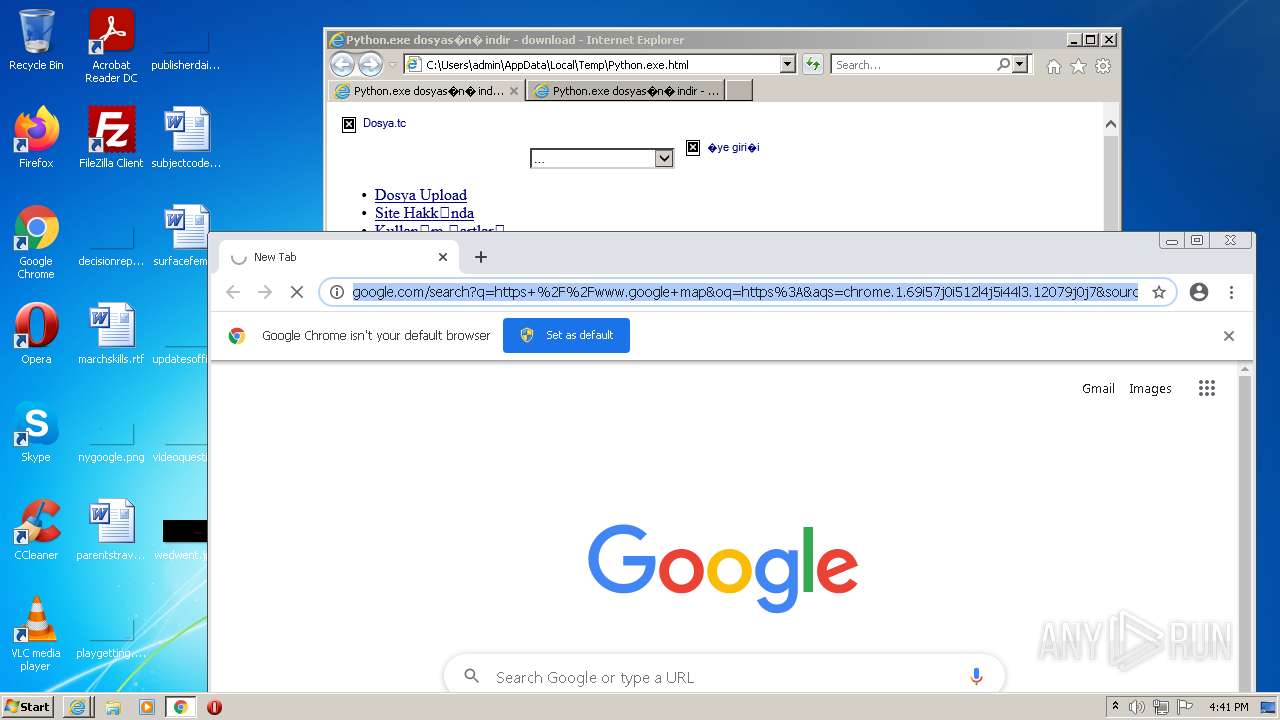
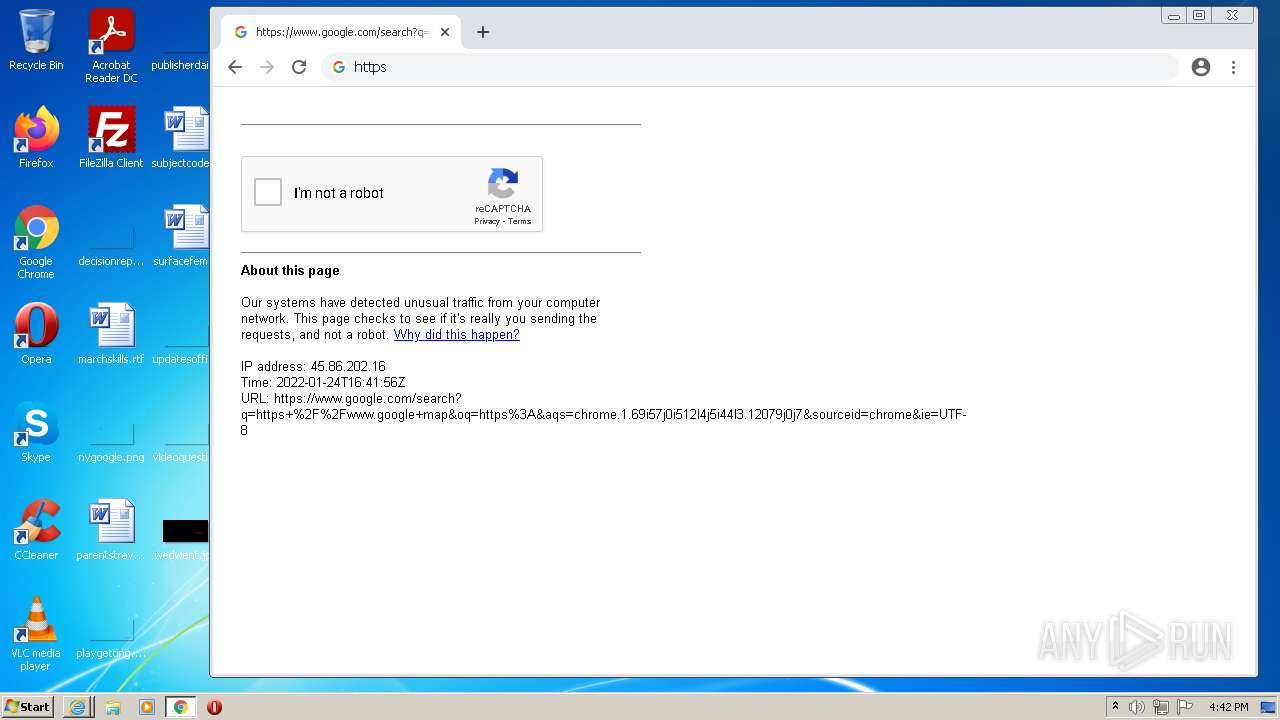
| Full analysis: | https://app.any.run/tasks/5e39decc-9ff7-4e0d-b7a5-fdd25fdef863 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | January 24, 2022, 16:40:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ISO-8859 text |
| MD5: | BF8C3C13CC2FD07CF94BC670A9FC23C0 |
| SHA1: | 7FDA1AAF4EE2CF1B4F9C0EF11B9FC33744CA0A7F |
| SHA256: | F888EBF60AB9B7735F8C0448FDEE926619E5E9527A269C18A1CC843158D57D85 |
| SSDEEP: | 96:yDCaSzQKLqLVNVU7HFwfiQV+E/52EOZGNTk0byrXsy62kR:yD2zQlhrqo3OZGe0eXen |
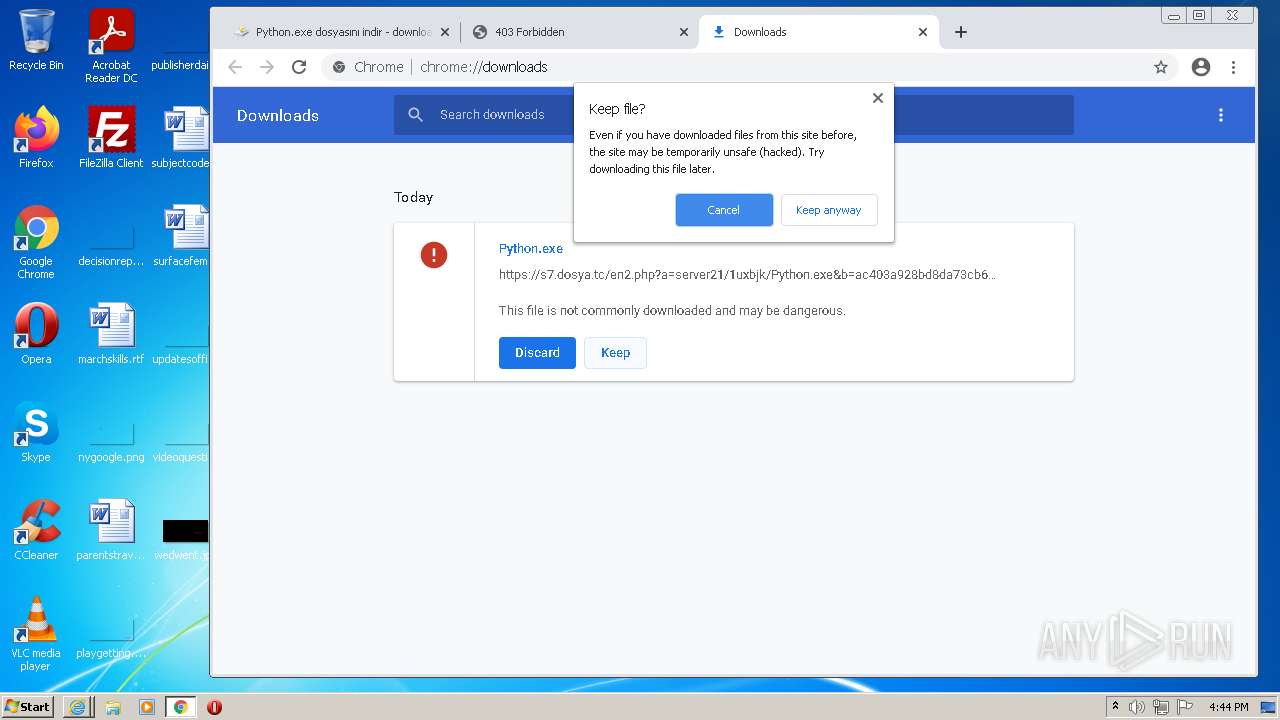
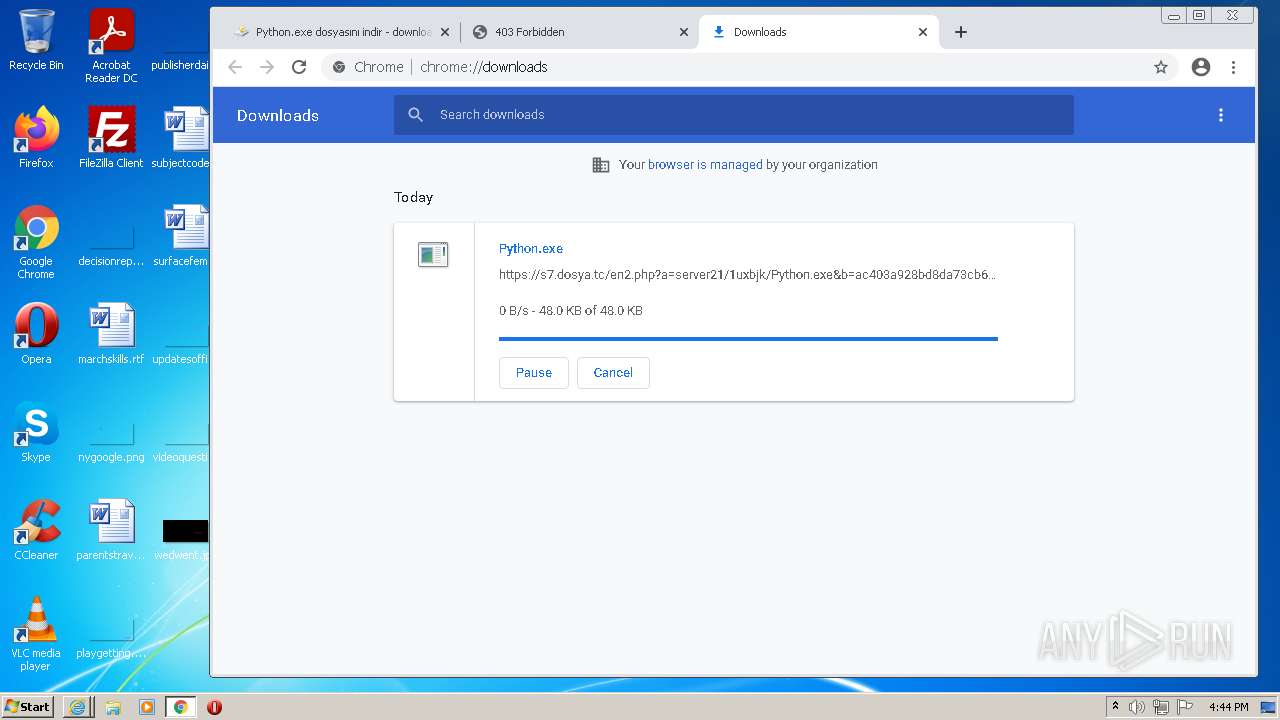
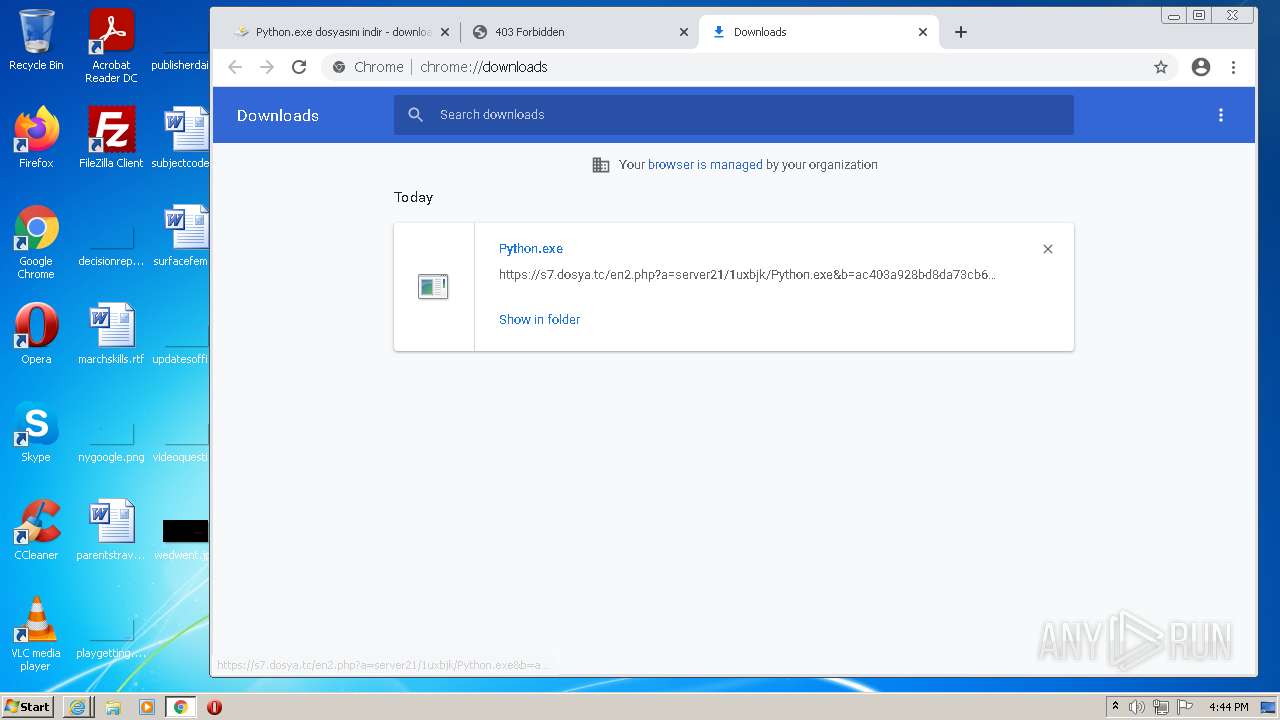
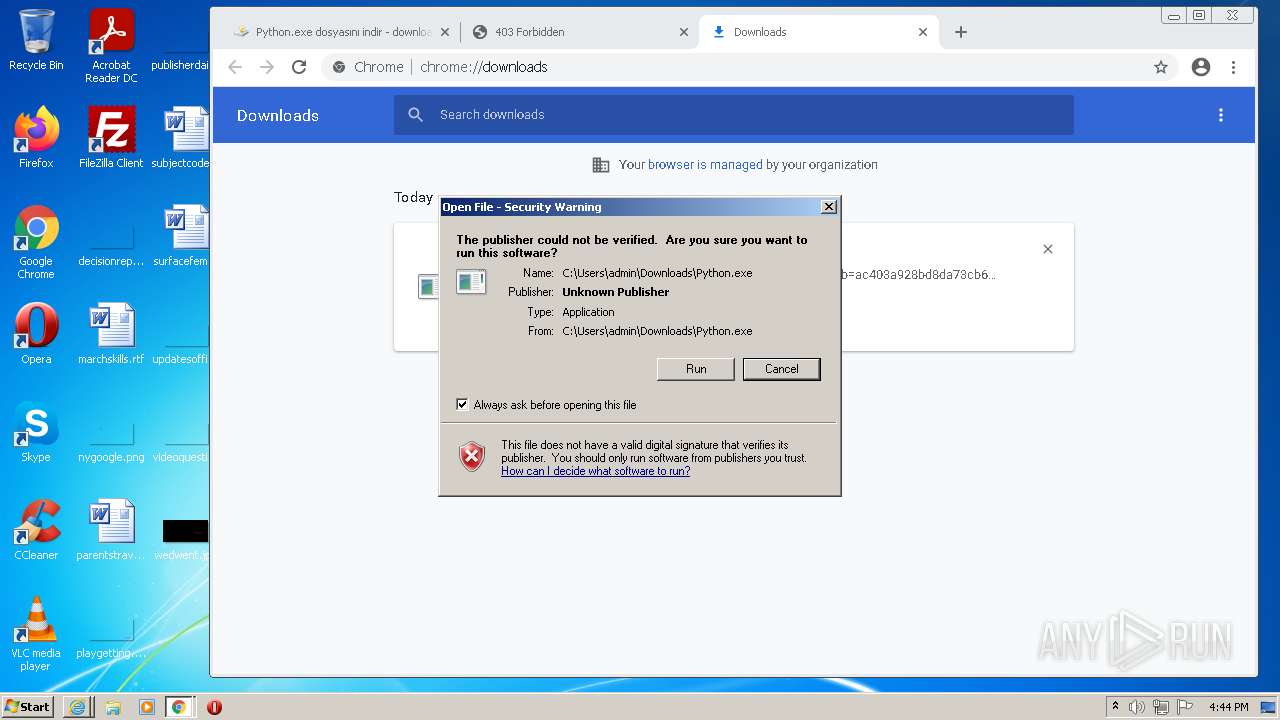
MALICIOUS
Application was dropped or rewritten from another process
- Python.exe (PID: 2128)
- python-3.7.1.exe (PID: 2572)
Steals credentials from Web Browsers
- python-3.7.1.exe (PID: 2572)
ASYNCRAT was detected
- python-3.7.1.exe (PID: 2572)
Changes the autorun value in the registry
- Python.exe (PID: 2128)
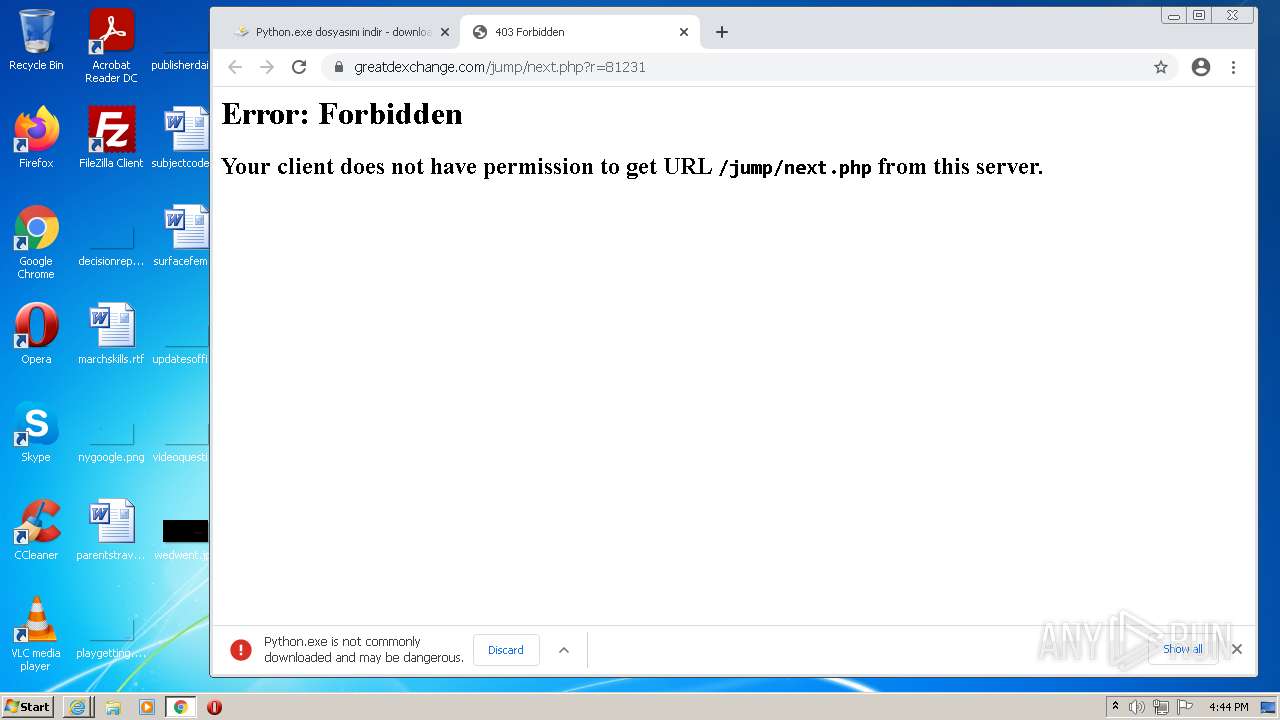
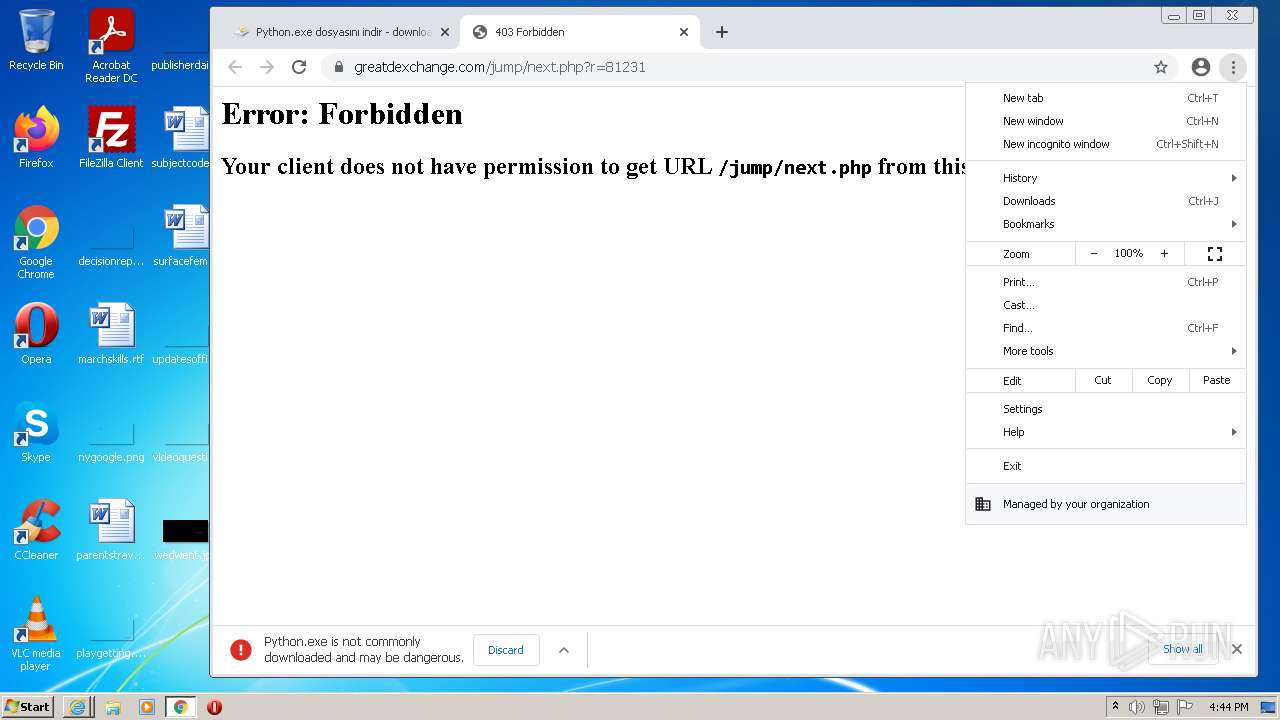
Drops executable file immediately after starts
- chrome.exe (PID: 2548)
Actions looks like stealing of personal data
- python-3.7.1.exe (PID: 2572)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3860)
- iexplore.exe (PID: 2240)
Modifies files in Chrome extension folder
- chrome.exe (PID: 1140)
Executable content was dropped or overwritten
- chrome.exe (PID: 1140)
- chrome.exe (PID: 3816)
- Python.exe (PID: 2128)
- chrome.exe (PID: 2548)
Checks supported languages
- Python.exe (PID: 2128)
- cmd.exe (PID: 1700)
- python-3.7.1.exe (PID: 2572)
Starts CMD.EXE for commands execution
- Python.exe (PID: 2128)
Reads the computer name
- Python.exe (PID: 2128)
- python-3.7.1.exe (PID: 2572)
Reads Environment values
- python-3.7.1.exe (PID: 2572)
Creates files in the user directory
- Python.exe (PID: 2128)
Drops a file that was compiled in debug mode
- chrome.exe (PID: 2548)
Loads DLL from Mozilla Firefox
- python-3.7.1.exe (PID: 2572)
Reads the cookies of Mozilla Firefox
- python-3.7.1.exe (PID: 2572)
INFO
Checks supported languages
- iexplore.exe (PID: 3464)
- iexplore.exe (PID: 3860)
- iexplore.exe (PID: 2240)
- chrome.exe (PID: 1140)
- chrome.exe (PID: 2932)
- chrome.exe (PID: 3744)
- chrome.exe (PID: 3816)
- chrome.exe (PID: 2600)
- chrome.exe (PID: 2824)
- chrome.exe (PID: 2292)
- chrome.exe (PID: 2844)
- chrome.exe (PID: 2900)
- chrome.exe (PID: 2816)
- chrome.exe (PID: 3092)
- chrome.exe (PID: 2624)
- chrome.exe (PID: 1940)
- chrome.exe (PID: 1332)
- chrome.exe (PID: 2800)
- iexplore.exe (PID: 1708)
- chrome.exe (PID: 2868)
- chrome.exe (PID: 904)
- chrome.exe (PID: 2364)
- chrome.exe (PID: 2900)
- chrome.exe (PID: 408)
- chrome.exe (PID: 2452)
- chrome.exe (PID: 3248)
- chrome.exe (PID: 1492)
- chrome.exe (PID: 3092)
- chrome.exe (PID: 3136)
- chrome.exe (PID: 3404)
- chrome.exe (PID: 2712)
- chrome.exe (PID: 1240)
- chrome.exe (PID: 3204)
- chrome.exe (PID: 3032)
- chrome.exe (PID: 3504)
- chrome.exe (PID: 3988)
- chrome.exe (PID: 528)
- chrome.exe (PID: 2992)
- chrome.exe (PID: 1392)
- chrome.exe (PID: 3516)
- chrome.exe (PID: 848)
- chrome.exe (PID: 3216)
- chrome.exe (PID: 4092)
- chrome.exe (PID: 3684)
- chrome.exe (PID: 1432)
- chrome.exe (PID: 3024)
- chrome.exe (PID: 3140)
- chrome.exe (PID: 2140)
- chrome.exe (PID: 2312)
- chrome.exe (PID: 3728)
- chrome.exe (PID: 2084)
- chrome.exe (PID: 3704)
- chrome.exe (PID: 884)
- chrome.exe (PID: 2672)
- chrome.exe (PID: 3180)
- chrome.exe (PID: 1952)
- timeout.exe (PID: 2232)
- chrome.exe (PID: 2548)
- chrome.exe (PID: 3568)
Changes internet zones settings
- iexplore.exe (PID: 3464)
Reads the computer name
- iexplore.exe (PID: 3860)
- iexplore.exe (PID: 3464)
- chrome.exe (PID: 1140)
- iexplore.exe (PID: 2240)
- chrome.exe (PID: 2292)
- chrome.exe (PID: 3816)
- chrome.exe (PID: 3092)
- iexplore.exe (PID: 1708)
- chrome.exe (PID: 3092)
- chrome.exe (PID: 2364)
- chrome.exe (PID: 3032)
- chrome.exe (PID: 2712)
- chrome.exe (PID: 3744)
- chrome.exe (PID: 1432)
- chrome.exe (PID: 2312)
- chrome.exe (PID: 3704)
- chrome.exe (PID: 2672)
Reads internet explorer settings
- iexplore.exe (PID: 2240)
- iexplore.exe (PID: 3860)
Application launched itself
- iexplore.exe (PID: 3464)
- chrome.exe (PID: 1140)
- iexplore.exe (PID: 3860)
Reads settings of System Certificates
- iexplore.exe (PID: 3464)
- chrome.exe (PID: 3816)
- iexplore.exe (PID: 2240)
- python-3.7.1.exe (PID: 2572)
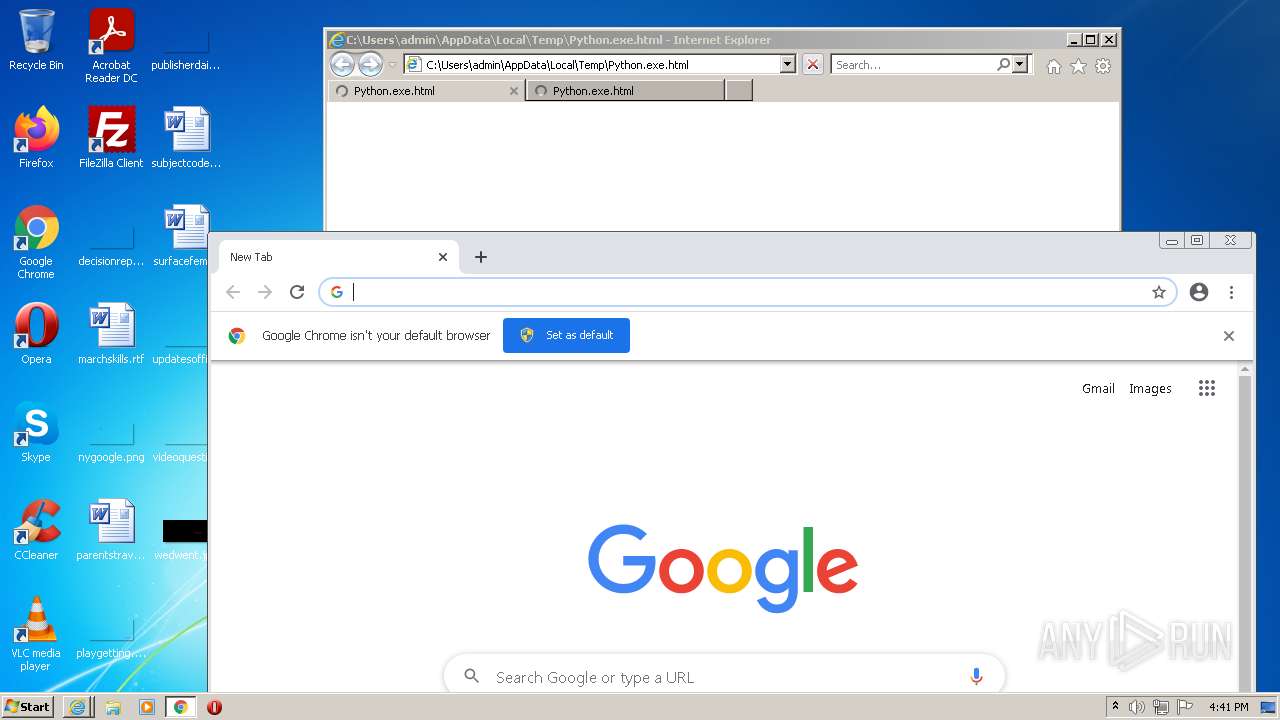
Manual execution by user
- chrome.exe (PID: 1140)
Checks Windows Trust Settings
- iexplore.exe (PID: 3464)
- iexplore.exe (PID: 2240)
- chrome.exe (PID: 1140)
Reads the hosts file
- chrome.exe (PID: 1140)
- chrome.exe (PID: 3816)
Reads the date of Windows installation
- chrome.exe (PID: 3092)
Creates files in the user directory
- iexplore.exe (PID: 3464)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3464)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 3464)
Changes settings of System certificates
- iexplore.exe (PID: 3464)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
EXIF
HTML
| viewport: | width=device-width, initial-scale=1.0 |
|---|---|
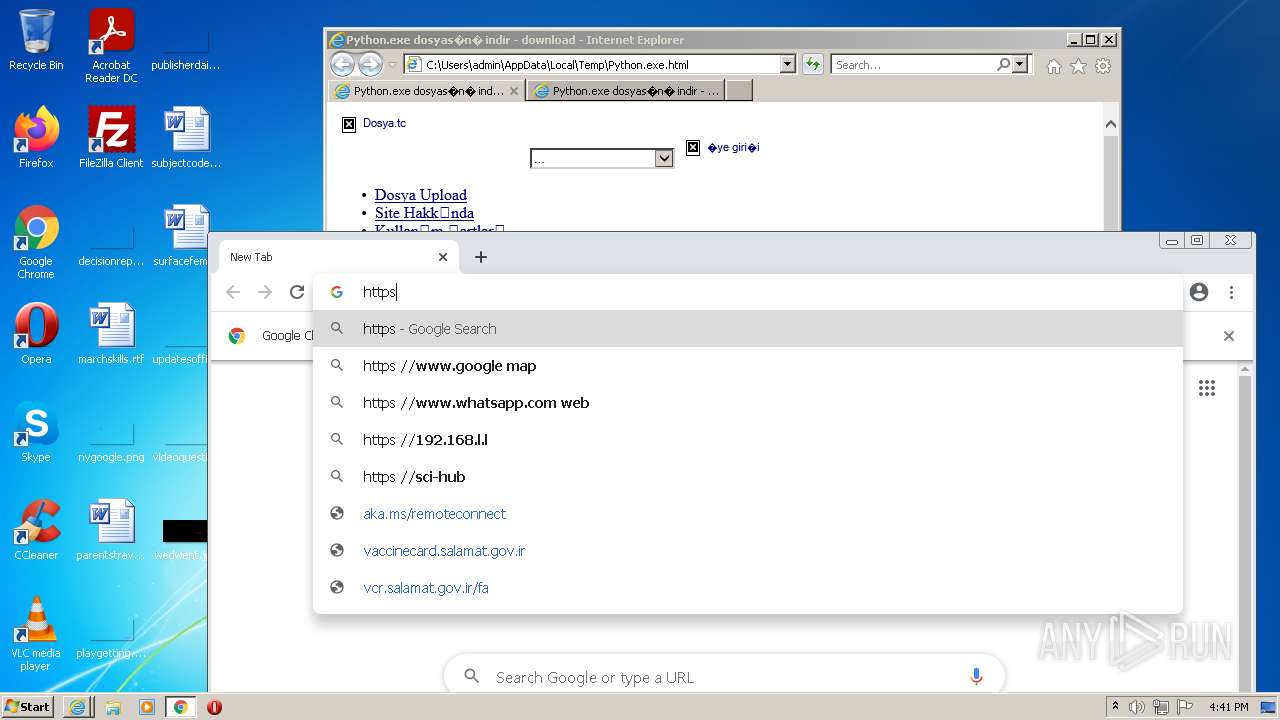
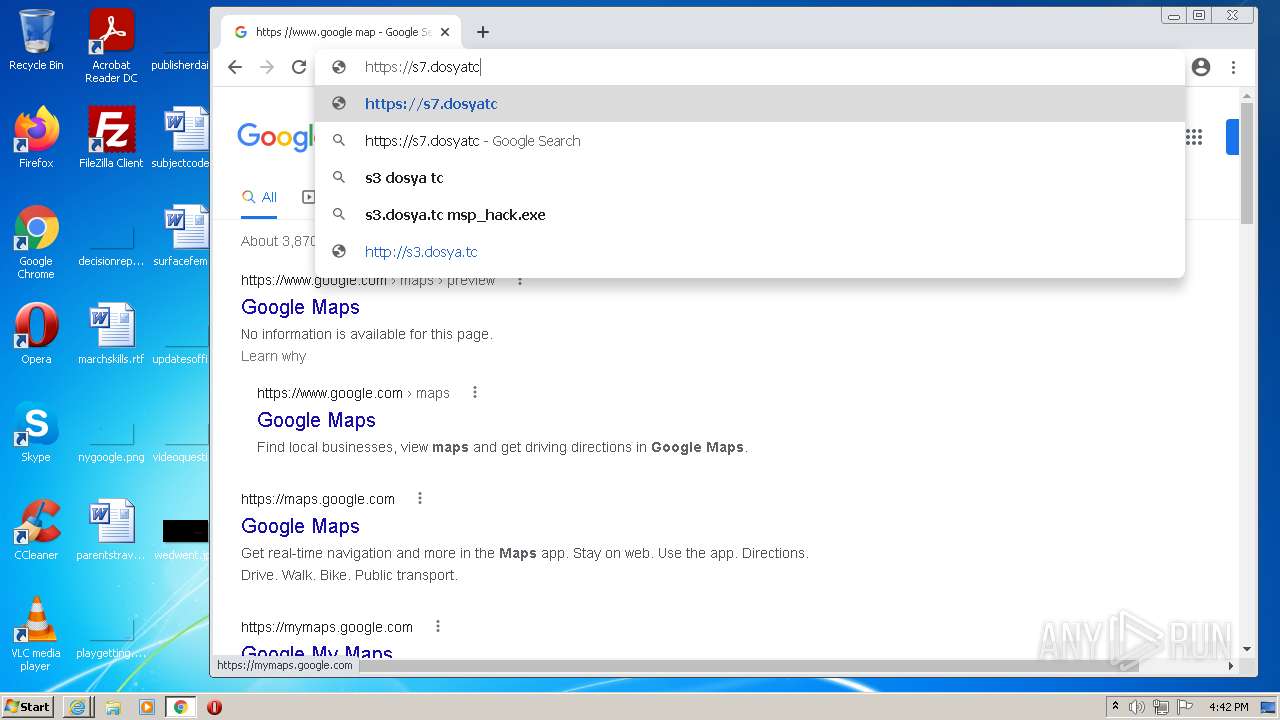
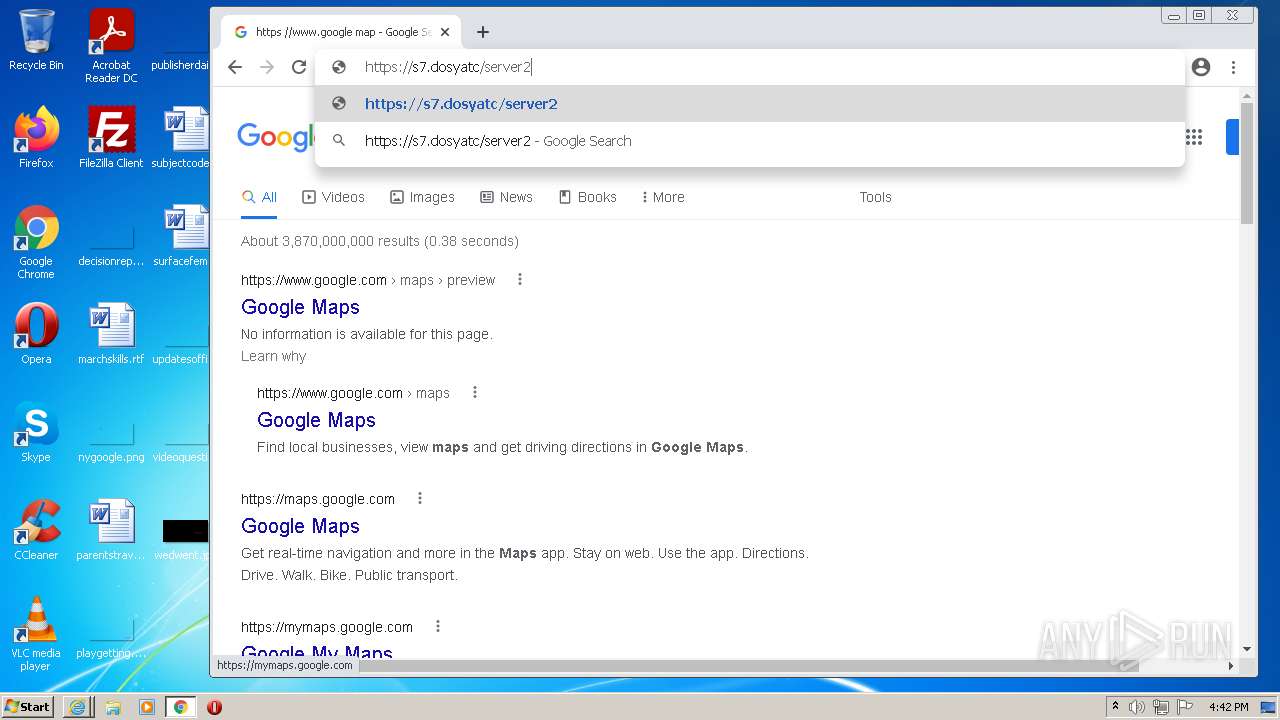
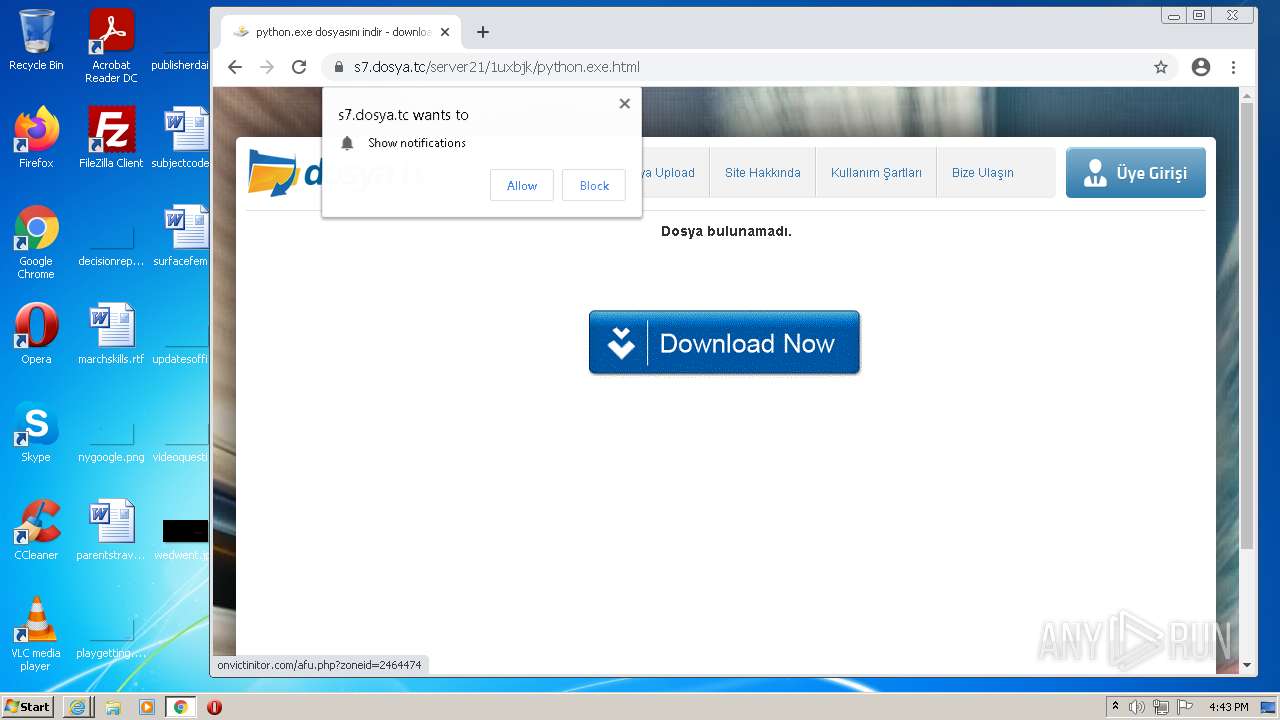
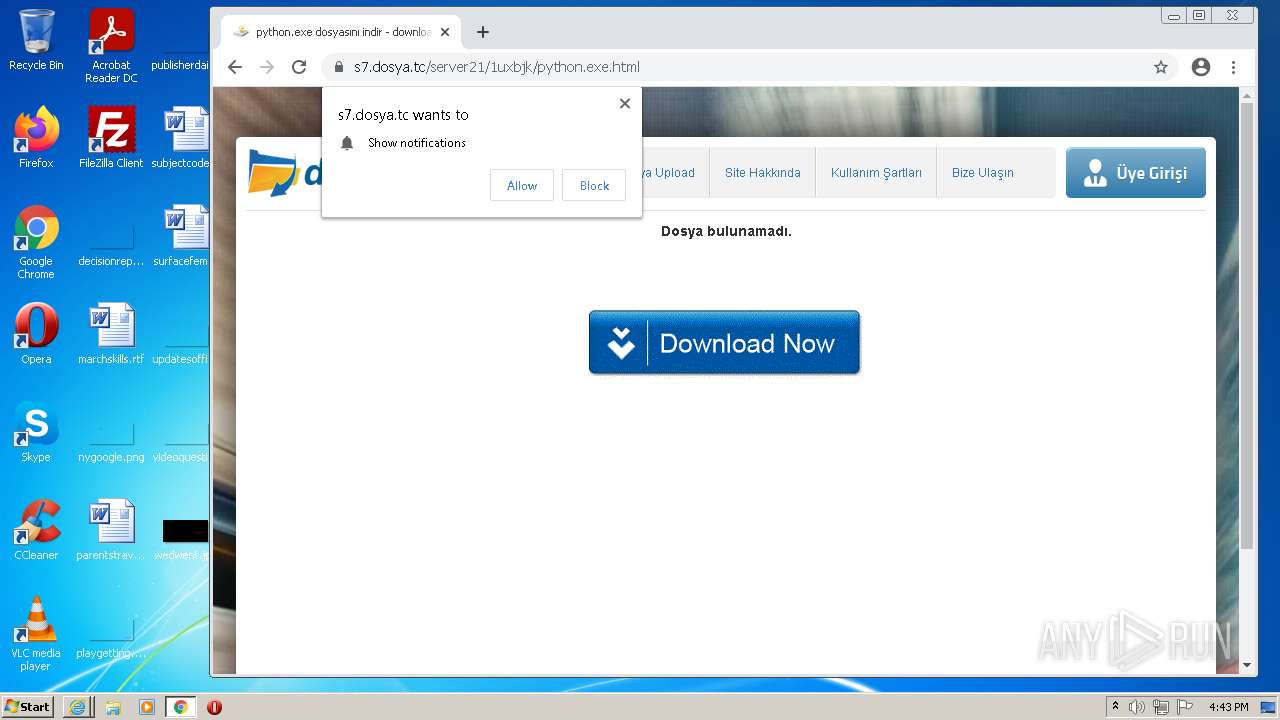
| Keywords: | Python.exe, download, indir, dosya, dosya y?kle, dosya payla?, dosya upload, dosya indir, dosya g?nder, file, file upload, file download, free file hosting, file hosting, file share |
| Description: | Python.exe dosyas?n? indir, download. Dosya.tc .Dosya Upload. Dosya Payla?. Dosya Y?kle |
| Title: | Python.exe dosyas?n? indir - download |
Total processes
104
Monitored processes
62
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1048,14029390430756532949,850402968613658901,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3084 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 528 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,14029390430756532949,850402968613658901,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=33 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3640 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,14029390430756532949,850402968613658901,131072 --enable-features=PasswordImport --lang=en-US --instant-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1948 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1048,14029390430756532949,850402968613658901,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=4268 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 904 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1048,14029390430756532949,850402968613658901,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3696 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,14029390430756532949,850402968613658901,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=31 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3196 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1048,14029390430756532949,850402968613658901,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2708 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1048,14029390430756532949,850402968613658901,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2020 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1432 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1048,14029390430756532949,850402968613658901,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3080 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
38 468
Read events
37 975
Write events
482
Delete events
11
Modification events
| (PID) Process: | (3464) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3464) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 587113936 | |||
| (PID) Process: | (3464) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30937409 | |||
| (PID) Process: | (3464) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 887115420 | |||
| (PID) Process: | (3464) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30937409 | |||
| (PID) Process: | (3464) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3464) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3464) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3464) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3464) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
6
Suspicious files
201
Text files
225
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1140 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61EED6A4-474.pma | — | |
MD5:— | SHA256:— | |||
| 3464 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3464 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
| 3464 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 1140 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF11a323.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 3464 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 3464 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 1140 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:995C92837E4775CAFFE387D51ADBA520 | SHA256:51247C3464FD988B72670002D01A57FBFF1348704D325DC8FF8817ED2459D0D9 | |||
| 3464 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 1140 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
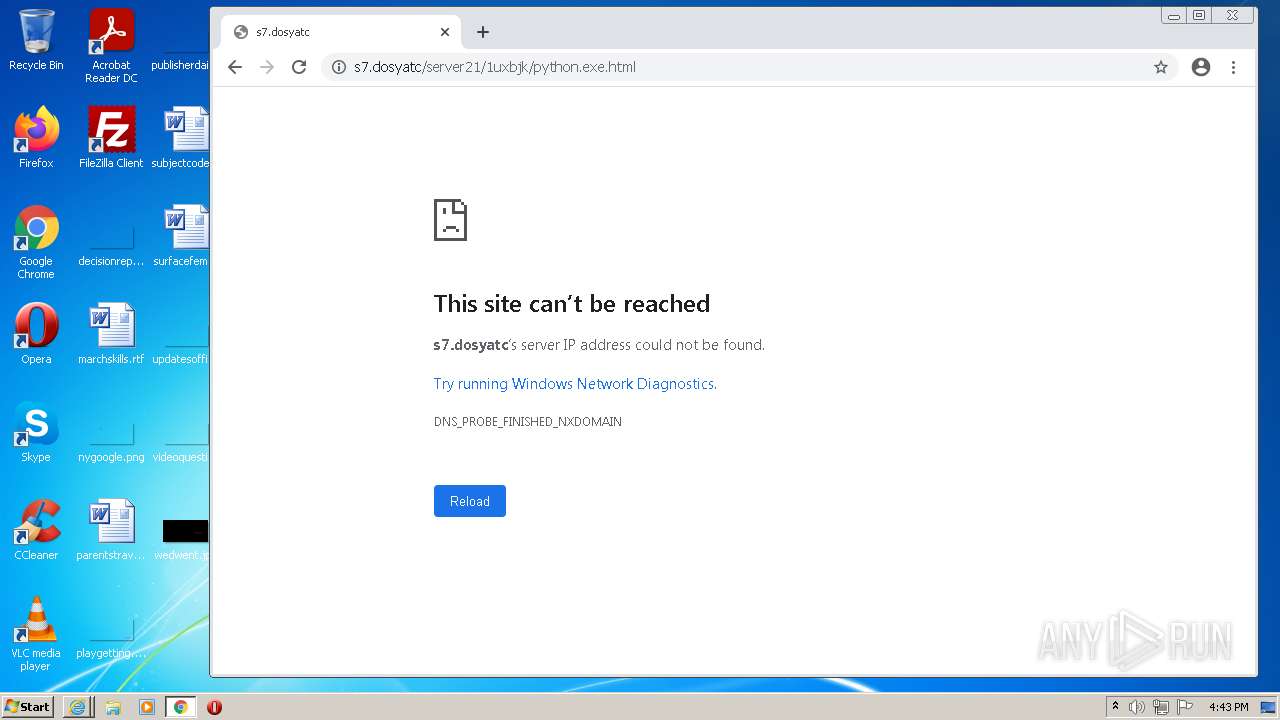
HTTP(S) requests
69
TCP/UDP connections
94
DNS requests
65
Threats
3
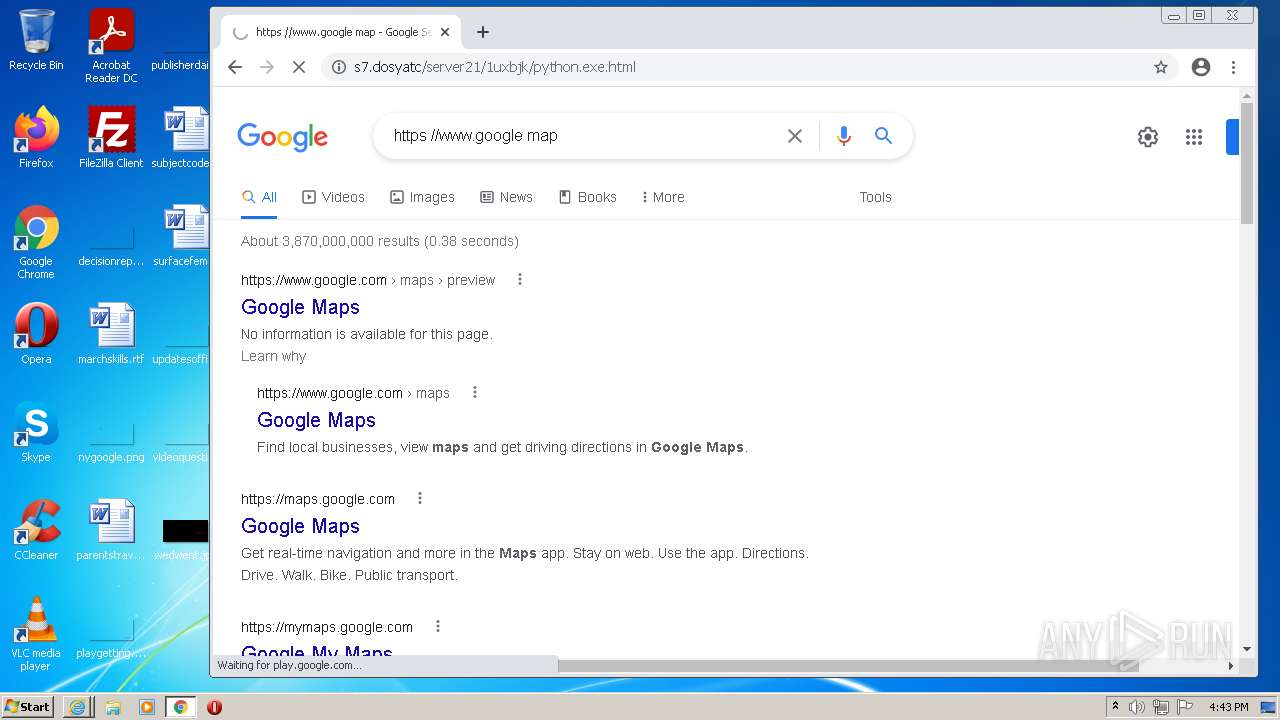
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
876 | svchost.exe | HEAD | 302 | 142.250.185.174:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | — | — | whitelisted |
876 | svchost.exe | HEAD | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | — | — | whitelisted |
876 | svchost.exe | HEAD | 200 | 74.125.108.167:80 | http://r2---sn-2gb7sn7y.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=45.86.202.16&mm=28&mn=sn-2gb7sn7y&ms=nvh&mt=1643042189&mv=m&mvi=2&pl=24&rmhost=r3---sn-2gb7sn7y.gvt1.com&shardbypass=yes | US | — | — | whitelisted |
3816 | chrome.exe | GET | 302 | 172.217.18.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 555 b | whitelisted |
3464 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | US | der | 471 b | whitelisted |
3464 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3464 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3816 | chrome.exe | POST | 200 | 142.250.186.67:80 | http://update.googleapis.com/service/update2/json?cup2key=10:223301408&cup2hreq=213c5672b14db571cb990df290ff27745661ecf7a560a40492758c08a6973cb5 | US | text | 2.60 Kb | whitelisted |
876 | svchost.exe | GET | 206 | 74.125.108.167:80 | http://r2---sn-2gb7sn7y.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=45.86.202.16&mm=28&mn=sn-2gb7sn7y&ms=nvh&mt=1643042425&mv=m&mvi=2&pl=24&rmhost=r3---sn-2gb7sn7y.gvt1.com&shardbypass=yes | US | binary | 9.47 Kb | whitelisted |
876 | svchost.exe | GET | 206 | 74.125.108.167:80 | http://r2---sn-2gb7sn7y.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=45.86.202.16&mm=28&mn=sn-2gb7sn7y&ms=nvh&mt=1643042189&mv=m&mvi=2&pl=24&rmhost=r3---sn-2gb7sn7y.gvt1.com&shardbypass=yes | US | binary | 9.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3464 | iexplore.exe | 131.253.33.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
4 | System | 139.45.197.250:445 | pushlommy.com | — | US | suspicious |
— | — | 131.253.33.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3464 | iexplore.exe | 67.26.75.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
3816 | chrome.exe | 142.250.185.68:443 | www.google.com | Google Inc. | US | whitelisted |
3816 | chrome.exe | 142.250.185.78:443 | clients2.google.com | Google Inc. | US | whitelisted |
— | — | 142.250.186.162:139 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
3816 | chrome.exe | 142.250.184.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3816 | chrome.exe | 142.250.185.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3816 | chrome.exe | 142.250.185.238:443 | apis.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pushlommy.com |
| suspicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potential Corporate Privacy Violation | ET POLICY DNS Query to a *.ngrok domain (ngrok.io) |
2572 | python-3.7.1.exe | A Network Trojan was detected | ET TROJAN Observed Malicious SSL Cert (AsyncRAT Server) |
1 ETPRO signatures available at the full report