| File name: | Bestellung Nr. 753.exe |
| Full analysis: | https://app.any.run/tasks/5f78e359-7ec6-41b5-a2fa-c928613fafe4 |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | September 03, 2025, 16:58:45 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | 20965E23197DF28704BAB1CB2CA58A4D |
| SHA1: | F67E168D80F8189DA5C95BDF70FF05CAC6F0A4E4 |
| SHA256: | F863D6F9552ACA996768B5D21F3A51BA32B0E918295102DE475DD16562EC08C9 |
| SSDEEP: | 6144:lJ8OpDAFQOrdwe6C+l1+i9mFxoE+06Rvkxs6BnI1zIG8jnooDj+ay83igNW3GPN7:lJ8MA+VeKlR0IvONBI1EGkoK+ay83TT7 |
MALICIOUS
FORMBOOK has been detected (YARA)
- xmynjhje.exe (PID: 4648)
SUSPICIOUS
Application launched itself
- xmynjhje.exe (PID: 4648)
Executable content was dropped or overwritten
- Bestellung Nr. 753.exe (PID: 640)
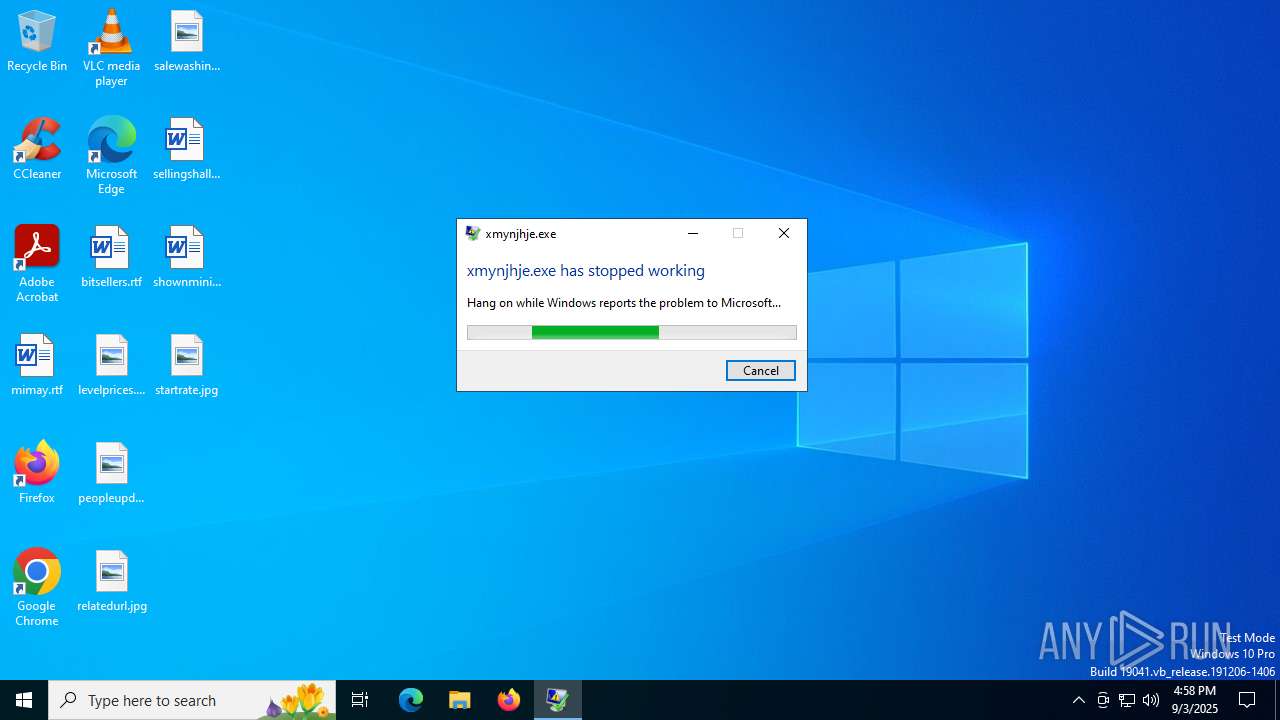
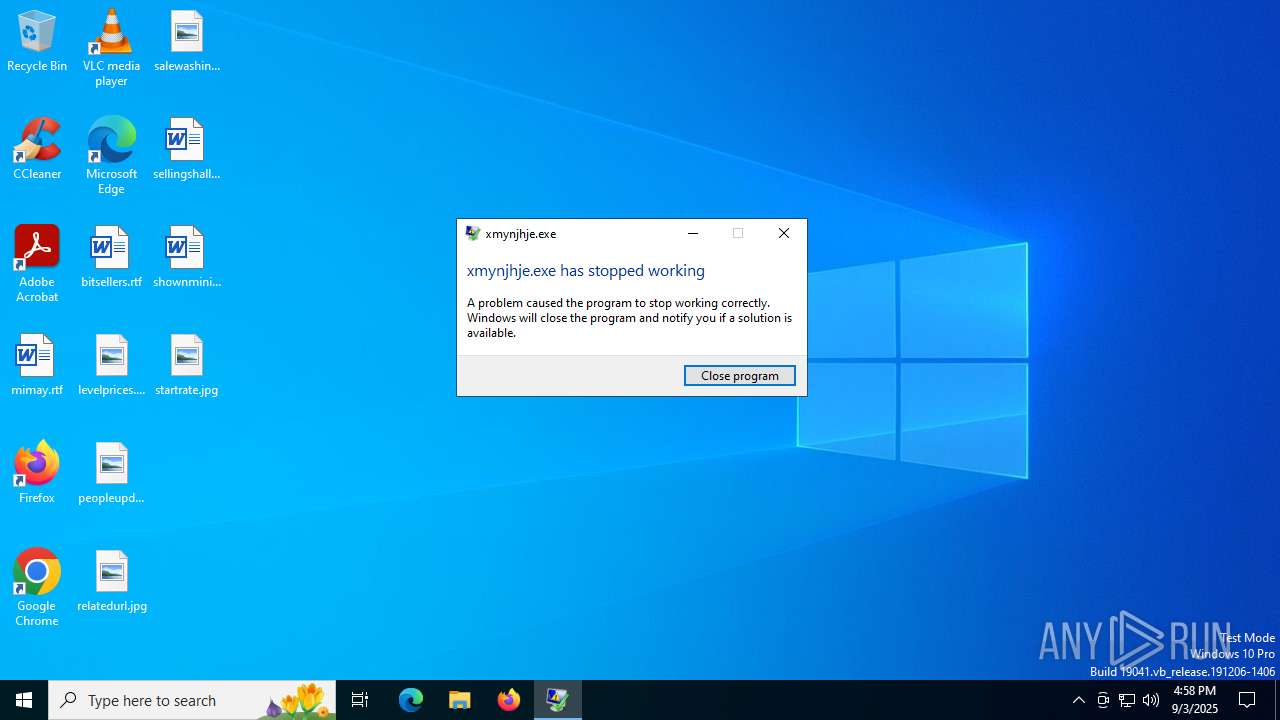
Executes application which crashes
- xmynjhje.exe (PID: 4648)
There is functionality for taking screenshot (YARA)
- Bestellung Nr. 753.exe (PID: 640)
INFO
The sample compiled with english language support
- Bestellung Nr. 753.exe (PID: 640)
Create files in a temporary directory
- Bestellung Nr. 753.exe (PID: 640)
Checks supported languages
- Bestellung Nr. 753.exe (PID: 640)
- xmynjhje.exe (PID: 4648)
Creates files or folders in the user directory
- WerFault.exe (PID: 4520)
Checks proxy server information
- WerFault.exe (PID: 4520)
Reads the software policy settings
- WerFault.exe (PID: 4520)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Formbook
(PID) Process(4648) xmynjhje.exe
C2www.naijabrain.africa/k04s/
Strings (79)USERNAME
LOCALAPPDATA
USERPROFILE
APPDATA
TEMP
ProgramFiles
CommonProgramFiles
ALLUSERSPROFILE
/c copy "
/c del "
\Run
\Policies
\Explorer
\Registry\User
\Registry\Machine
\SOFTWARE\Microsoft\Windows\CurrentVersion
Office\15.0\Outlook\Profiles\Outlook\
NT\CurrentVersion\Windows Messaging Subsystem\Profiles\Outlook\
\SOFTWARE\Mozilla\Mozilla
\Mozilla
Username:
Password:
formSubmitURL
usernameField
encryptedUsername
encryptedPassword
\logins.json
\signons.sqlite
\Microsoft\Vault\
SELECT encryptedUsername, encryptedPassword, formSubmitURL FROM moz_logins
\Google\Chrome\User Data\Default\Login Data
SELECT origin_url, username_value, password_value FROM logins
.exe
.com
.scr
.pif
.cmd
.bat
ms
win
gdi
mfc
vga
igfx
user
help
config
update
regsvc
chkdsk
systray
audiodg
certmgr
autochk
taskhost
colorcpl
services
IconCache
ThumbCache
Cookies
SeDebugPrivilege
SeShutdownPrivilege
\BaseNamedObjects
config.php
POST
HTTP/1.1
Host:
Connection: close
Content-Length:
Cache-Control: no-cache
Origin: http://
User-Agent: Mozilla Firefox/4.0
Content-Type: application/x-www-form-urlencoded
Accept: */*
Referer: http://
Accept-Language: en-US
Accept-Encoding: gzip, deflate
dat=
f-start
f-end
Decoy C2 (64)draanabellrojas.com
in03.one
kyraloves.co.uk
laluma.store
londoncell.com
kanurikibueadvocates.com
buyeasynow.net
escapefromtarkov-wiki.com
crewint.net
f-b.boats
beautyaidstudio.com
ashfieldconsultancy.uk
dlogsadood.com
ftgam.xyz
constantinopanama.com
yellowpocket.africa
konyil.com
easomobility.com
1135wickloecourt.com
indexb2b.com
kabridates.com
forty04.com
fourjaysgsps.com
bukkaluy.com
elvanite.co.uk
ccnds.online
medicswellnessconsult.africa
dashuzhupin.com
woodstockwine.africa
advisorsforcharities.com
jathinel.com
bwin6789.com
brandologic.net
courier.africa
f6zx.shop
efefcondemned.buzz
cosmochroniclesblog.com
karmaapps.site
kielenki.africa
classbetter.online
ffp78.com
goodwebob.com
facroryoutletstore.com
kart746.xyz
current-vaancies.com
fourblendedsistas.store
anjuhepay.com
lawexpert9.info
family-doctor-96425.com
telcs.net
huodede.com
clarkwire.xyz
aliencultist.com
innovantexclusive.com
theepiclandings.net
happy-christmass.com
bearcreekwood.com
370zhitch.com
game2casino.com
betternook.com
ginkfazoltrelo.info
andyrichardsonwv.com
handygiftstore.com
orientalwholesale.uk
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:09:25 21:56:47+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26624 |
| InitializedDataSize: | 141824 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x3640 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 27.30.16.98 |
| ProductVersionNumber: | 27.30.16.98 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | creatic |
| FileDescription: | villous |
| FileVersion: | 27.30.16.98 |
| LegalCopyright: | Copyright regressors |
| LegalTrademarks: | quetzal |
| ProductName: | 27.30.16.98 |
Total processes
143
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 32 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | xmynjhje.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 640 | "C:\Users\admin\AppData\Local\Temp\Bestellung Nr. 753.exe" | C:\Users\admin\AppData\Local\Temp\Bestellung Nr. 753.exe | explorer.exe | ||||||||||||
User: admin Company: creatic Integrity Level: MEDIUM Description: villous Exit code: 0 Version: 27.30.16.98 Modules
| |||||||||||||||
| 2388 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4520 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 4648 -s 664 | C:\Windows\SysWOW64\WerFault.exe | xmynjhje.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4648 | "C:\Users\admin\AppData\Local\Temp\xmynjhje.exe" C:\Users\admin\AppData\Local\Temp\jpjxbpp.q | C:\Users\admin\AppData\Local\Temp\xmynjhje.exe | Bestellung Nr. 753.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
Formbook(PID) Process(4648) xmynjhje.exe C2www.naijabrain.africa/k04s/ Strings (79)USERNAME LOCALAPPDATA USERPROFILE APPDATA TEMP ProgramFiles CommonProgramFiles ALLUSERSPROFILE /c copy " /c del " \Run \Policies \Explorer \Registry\User \Registry\Machine \SOFTWARE\Microsoft\Windows\CurrentVersion Office\15.0\Outlook\Profiles\Outlook\ NT\CurrentVersion\Windows Messaging Subsystem\Profiles\Outlook\ \SOFTWARE\Mozilla\Mozilla \Mozilla Username: Password: formSubmitURL usernameField encryptedUsername encryptedPassword \logins.json \signons.sqlite \Microsoft\Vault\ SELECT encryptedUsername, encryptedPassword, formSubmitURL FROM moz_logins \Google\Chrome\User Data\Default\Login Data SELECT origin_url, username_value, password_value FROM logins .exe .com .scr .pif .cmd .bat ms win gdi mfc vga igfx user help config update regsvc chkdsk systray audiodg certmgr autochk taskhost colorcpl services IconCache ThumbCache Cookies SeDebugPrivilege SeShutdownPrivilege \BaseNamedObjects config.php POST HTTP/1.1 Host: Connection: close Content-Length: Cache-Control: no-cache Origin: http:// User-Agent: Mozilla Firefox/4.0 Content-Type: application/x-www-form-urlencoded Accept: */* Referer: http:// Accept-Language: en-US Accept-Encoding: gzip, deflate
dat= f-start f-end Decoy C2 (64)draanabellrojas.com in03.one kyraloves.co.uk laluma.store londoncell.com kanurikibueadvocates.com buyeasynow.net escapefromtarkov-wiki.com crewint.net f-b.boats beautyaidstudio.com ashfieldconsultancy.uk dlogsadood.com ftgam.xyz constantinopanama.com yellowpocket.africa konyil.com easomobility.com 1135wickloecourt.com indexb2b.com kabridates.com forty04.com fourjaysgsps.com bukkaluy.com elvanite.co.uk ccnds.online medicswellnessconsult.africa dashuzhupin.com woodstockwine.africa advisorsforcharities.com jathinel.com bwin6789.com brandologic.net courier.africa f6zx.shop efefcondemned.buzz cosmochroniclesblog.com karmaapps.site kielenki.africa classbetter.online ffp78.com goodwebob.com facroryoutletstore.com kart746.xyz current-vaancies.com fourblendedsistas.store anjuhepay.com lawexpert9.info family-doctor-96425.com telcs.net huodede.com clarkwire.xyz aliencultist.com innovantexclusive.com theepiclandings.net happy-christmass.com bearcreekwood.com 370zhitch.com game2casino.com betternook.com ginkfazoltrelo.info andyrichardsonwv.com handygiftstore.com orientalwholesale.uk | |||||||||||||||
| 4748 | "C:\Users\admin\AppData\Local\Temp\xmynjhje.exe" | C:\Users\admin\AppData\Local\Temp\xmynjhje.exe | — | xmynjhje.exe | |||||||||||
User: admin Integrity Level: MEDIUM | |||||||||||||||
Total events
7 382
Read events
7 382
Write events
0
Delete events
0
Modification events
Executable files
1
Suspicious files
9
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4520 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_xmynjhje.exe_9c54f0f5f634c1c238c3f39f318c64c653a9786a_d07397a6_e50d826a-03ac-4a22-aa4f-358d29b78ad4\Report.wer | — | |
MD5:— | SHA256:— | |||
| 640 | Bestellung Nr. 753.exe | C:\Users\admin\AppData\Local\Temp\jpjxbpp.q | binary | |
MD5:234C9147471E7987A49981AA5AF78023 | SHA256:67D607FFF5D11046F184C928B742D71D8D611DEE35A523227513652381F918D1 | |||
| 640 | Bestellung Nr. 753.exe | C:\Users\admin\AppData\Local\Temp\olsmltgrn.p | binary | |
MD5:725DCC290DB30DBA4284517916E1B2DD | SHA256:CF5E2C4039BF6695EEA7128BAD408E2FB75B90C8CDA7E986C0233F0B7CC3D91F | |||
| 640 | Bestellung Nr. 753.exe | C:\Users\admin\AppData\Local\Temp\nsnC59E.tmp | binary | |
MD5:265E4FAC276CEE016D7DE6D54C91A13C | SHA256:4D676A5CA4526A3A8D185EAB749789FFA071BB82348D4AF8DDC50A560B0CE551 | |||
| 4520 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\21253908F3CB05D51B1C2DA8B681A785 | binary | |
MD5:D310523737A0D4D05066857AC157F458 | SHA256:0A0520D498306689AFA3CAC09ACE82E09229108FC9FABA5A906291D077004484 | |||
| 4520 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\21253908F3CB05D51B1C2DA8B681A785 | binary | |
MD5:6CE84DDCFEFE0C7B65AEE5F506CCEA73 | SHA256:25E46014DC91339B8E502A05B1423E84B1CEC8A13871376CA5C3845341452852 | |||
| 4520 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERCA13.tmp.xml | xml | |
MD5:FE90D617E36EE110F89247E7EF00BCA1 | SHA256:1FB556C59EC912F756FBE56D54F2A85C119DF090E25DA9B6F8F644AAE2BD0D33 | |||
| 4520 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\xmynjhje.exe.4648.dmp | binary | |
MD5:DF28F81A5E3468FA457F088A73771C35 | SHA256:3EE120CB06223421548E1189064A5A89D5285CC3E178E874B2555F76AA1AD18C | |||
| 4520 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\37C951188967C8EB88D99893D9D191FE | binary | |
MD5:399B8A260A3FE6BB6F2D2DAE89FB82BB | SHA256:0DC7CEC07635BC159BA8B7FB1D7FC9AA00DE1C0C045BD688351878B65EAFF57B | |||
| 4520 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERC965.tmp.dmp | binary | |
MD5:07D23926ADE6896CE32AD483AC801455 | SHA256:79A5D1E1BD8B7710F37EE3FC90A509C7F026BDDE781E4C0A419219CAE30912DD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
23
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4520 | WerFault.exe | GET | 200 | 2.19.117.91:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4520 | WerFault.exe | GET | 200 | 23.200.197.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5644 | svchost.exe | GET | 200 | 23.203.176.221:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.19.117.91:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.200.197.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3624 | SIHClient.exe | GET | 200 | 23.37.198.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3624 | SIHClient.exe | GET | 200 | 23.37.198.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5476 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4520 | WerFault.exe | 135.233.45.223:443 | watson.events.data.microsoft.com | LUCENT-CIO | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4520 | WerFault.exe | 2.19.117.91:80 | crl.microsoft.com | Akamai International B.V. | GB | whitelisted |
4520 | WerFault.exe | 23.200.197.152:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
5644 | svchost.exe | 20.190.160.17:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5644 | svchost.exe | 23.203.176.221:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
watson.events.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |