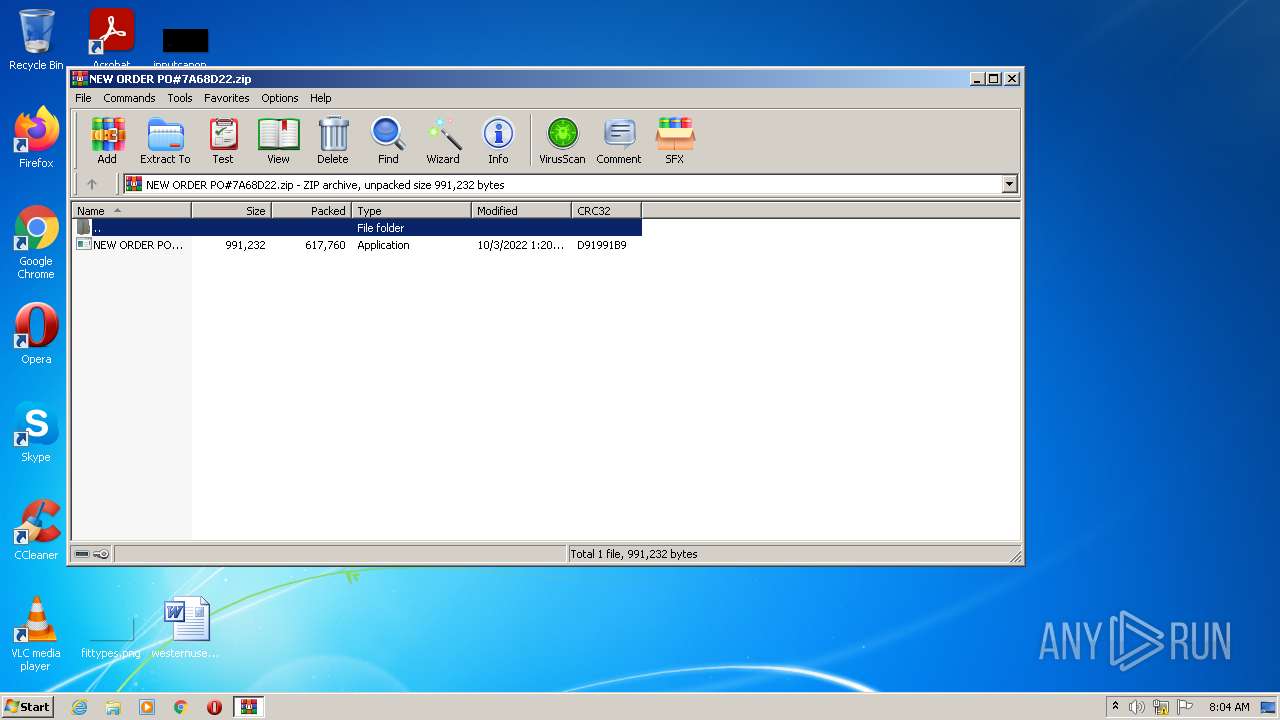
| File name: | NEW ORDER PO#7A68D22.zip |
| Full analysis: | https://app.any.run/tasks/a428c5b6-ac32-4251-b451-1f44f1b53e57 |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | October 05, 2022, 07:04:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 852DC49EFB8699889906B650BB73F82D |
| SHA1: | 4EAED5C5ABBD3FE13E45BBA2BAD1209D3CF005E5 |
| SHA256: | F7A3063CD46B779DCEA973720641CC55A3775AA5F19D581DC5EDE573FA8B5A3C |
| SSDEEP: | 12288:2i0oZ1hFg6qgXXa/HTrnDmwFxTgScU30OLtaPXU0dL0hYT:2i5n3PqS6ThFaSh5LtaPZ0h6 |
MALICIOUS
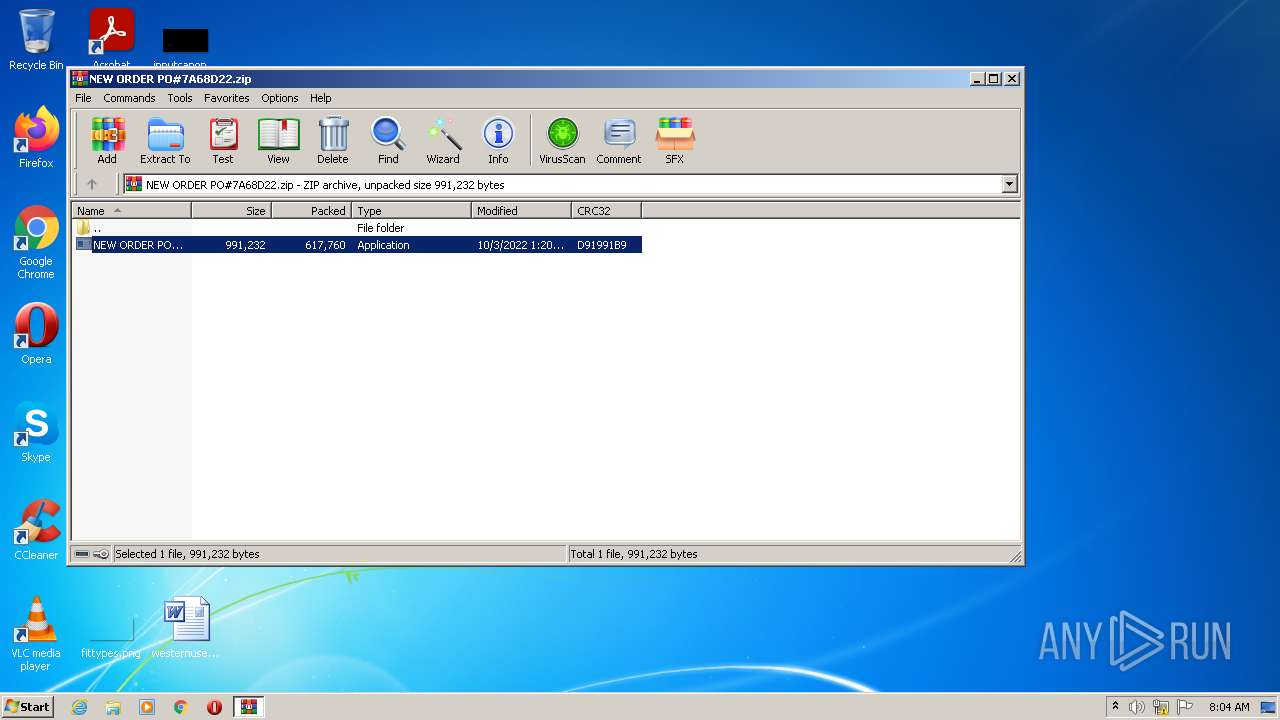
Drops the executable file immediately after the start
- WinRAR.exe (PID: 1144)
Application was dropped or rewritten from another process
- NEW ORDER PO#7A68D22.exe (PID: 2072)
- NEW ORDER PO#7A68D22.exe (PID: 1884)
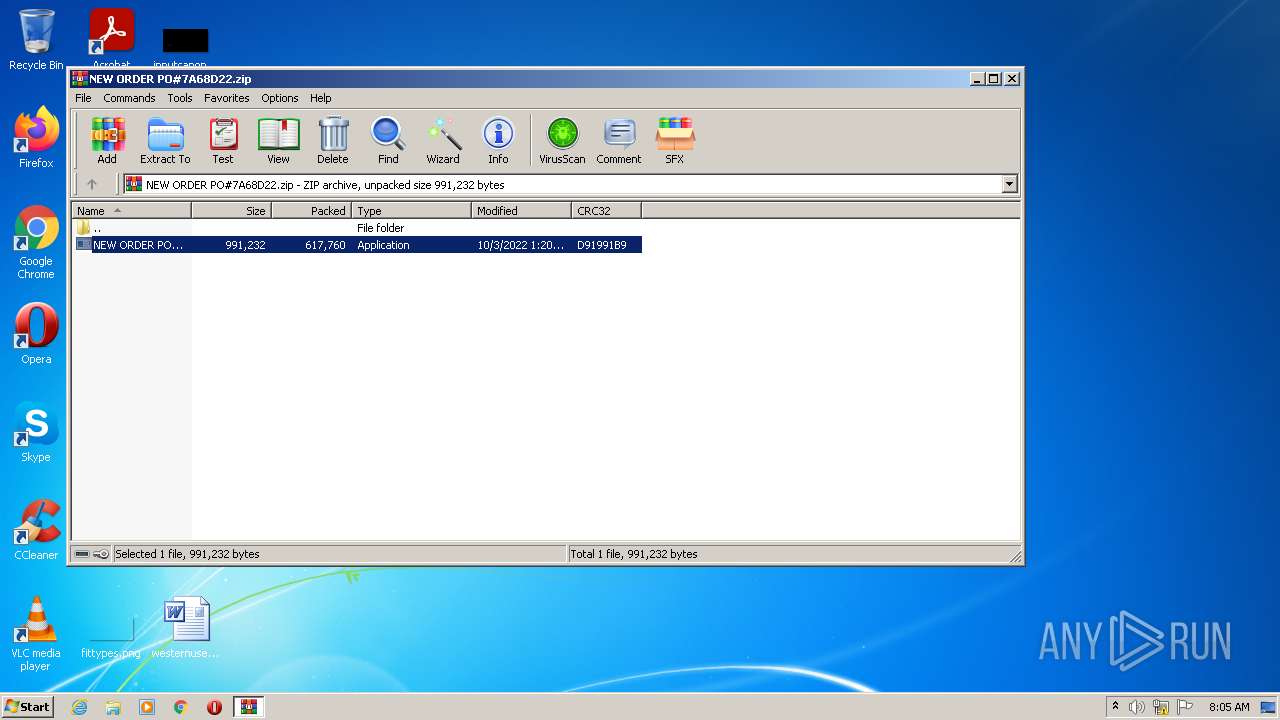
Formbook is detected
- NETSTAT.EXE (PID: 3172)
FORMBOOK detected by memory dumps
- NETSTAT.EXE (PID: 3172)
FORMBOOK was detected
- Explorer.EXE (PID: 1488)
Connects to the CnC server
- Explorer.EXE (PID: 1488)
SUSPICIOUS
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 1144)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1144)
Reads Internet Settings
- WinRAR.exe (PID: 1144)
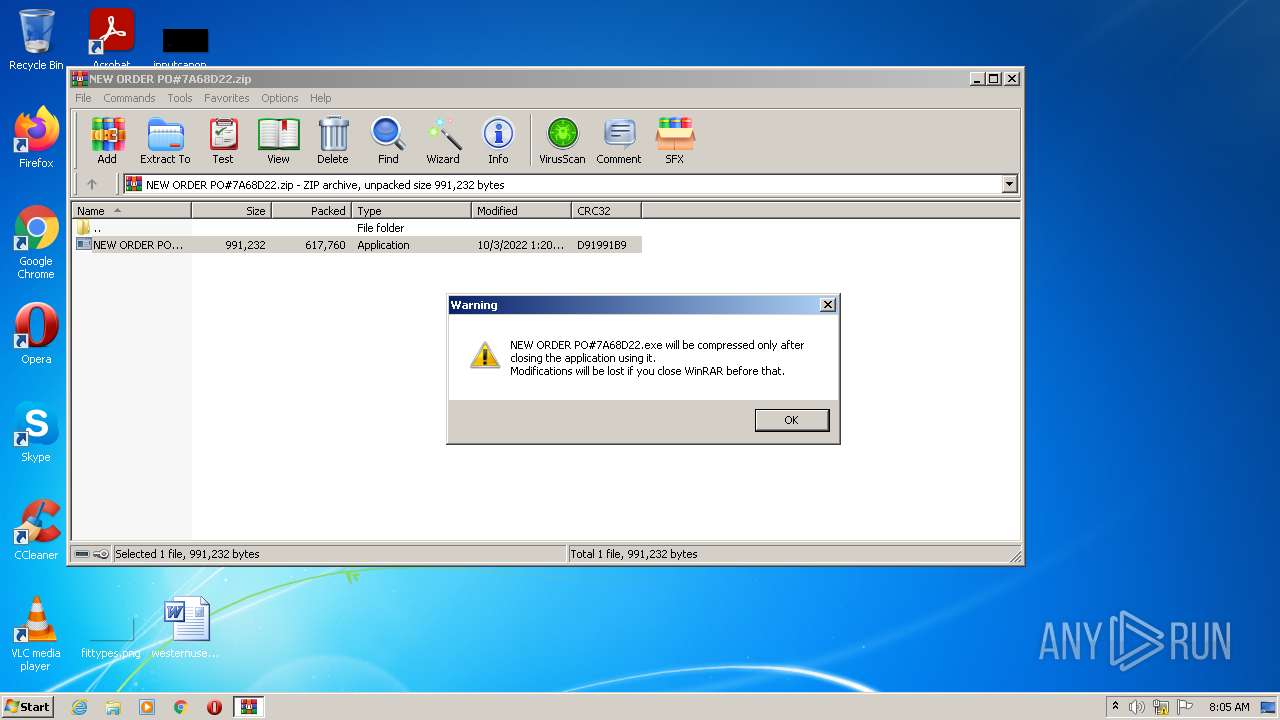
Application launched itself
- NEW ORDER PO#7A68D22.exe (PID: 2072)
Reads the machine GUID from the registry
- NEW ORDER PO#7A68D22.exe (PID: 2072)
Uses NETSTAT.EXE to discover network connections
- Explorer.EXE (PID: 1488)
Loads DLL from Mozilla Firefox
- NETSTAT.EXE (PID: 3172)
INFO
Reads the computer name
- WinRAR.exe (PID: 1144)
- NEW ORDER PO#7A68D22.exe (PID: 2072)
- NEW ORDER PO#7A68D22.exe (PID: 1884)
Process checks LSA protection
- WinRAR.exe (PID: 1144)
- NEW ORDER PO#7A68D22.exe (PID: 2072)
Checks supported languages
- WinRAR.exe (PID: 1144)
- NEW ORDER PO#7A68D22.exe (PID: 2072)
- NEW ORDER PO#7A68D22.exe (PID: 1884)
Creates files in the user directory
- WinRAR.exe (PID: 1144)
- Explorer.EXE (PID: 1488)
- NETSTAT.EXE (PID: 3172)
Creates a file in a temporary directory
- WinRAR.exe (PID: 1144)
Process checks computer location settings
- NEW ORDER PO#7A68D22.exe (PID: 1884)
Manual execution by user
- NETSTAT.EXE (PID: 3172)
Reads the machine GUID from the registry
- NETSTAT.EXE (PID: 3172)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
Total processes
37
Monitored processes
5
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1144 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\NEW ORDER PO#7A68D22.zip" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1488 | C:\Windows\Explorer.EXE | C:\Windows\Explorer.EXE | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1884 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1144.12033\NEW ORDER PO#7A68D22.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa1144.12033\NEW ORDER PO#7A68D22.exe | — | NEW ORDER PO#7A68D22.exe | |||||||||||
User: admin Company: Magic Bone Integrity Level: MEDIUM Description: LibertyReserve Exit code: 0 Version: 2.1.0 Modules
| |||||||||||||||
| 2072 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1144.12033\NEW ORDER PO#7A68D22.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa1144.12033\NEW ORDER PO#7A68D22.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Magic Bone Integrity Level: MEDIUM Description: LibertyReserve Exit code: 0 Version: 2.1.0 Modules
| |||||||||||||||
| 3172 | "C:\Windows\System32\NETSTAT.EXE" | C:\Windows\System32\NETSTAT.EXE | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Netstat Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 666
Read events
1 623
Write events
43
Delete events
0
Modification events
| (PID) Process: | (1144) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1144) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1144) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1144) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (1144) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (1144) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\NEW ORDER PO#7A68D22.zip | |||
| (PID) Process: | (1144) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1144) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1144) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1144) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1144 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1144.12033\NEW ORDER PO#7A68D22.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
2
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3172 | NETSTAT.EXE | GET | — | 45.33.6.223:80 | http://www.sqlite.org/2019/sqlite-dll-win32-x86-3280000.zip | US | — | — | whitelisted |
1488 | Explorer.EXE | GET | 200 | 23.217.138.108:80 | http://www.tpc-tt.site/uymo/?GfmTF=f3Tz8X0lqlQP2bcTaQr4jK0Z7s3wlLyYRo3l3YB4W1GMfZ0l0szoECJEG9ymWJe8BHn+tcx2JKRSzKTp15sR2S+zEev8DlGOfd/9yT0=&ARM=7n3DUfwxGrtP1zyp | US | html | 374 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1488 | Explorer.EXE | 23.217.138.108:80 | www.tpc-tt.site | Akamai International B.V. | US | whitelisted |
— | — | 45.33.6.223:80 | www.sqlite.org | Linode, LLC | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.tpc-tt.site |
| malicious |
www.sqlite.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1488 | Explorer.EXE | Generic Protocol Command Decode | SURICATA HTTP Unexpected Request body |
1488 | Explorer.EXE | A Network Trojan was detected | ET TROJAN FormBook CnC Checkin (GET) |
1488 | Explorer.EXE | A Network Trojan was detected | ET TROJAN FormBook CnC Checkin (GET) |
1488 | Explorer.EXE | A Network Trojan was detected | ET TROJAN FormBook CnC Checkin (GET) |