| File name: | 4afa11247ab2f8870bba22d8df0b81ec.exe |
| Full analysis: | https://app.any.run/tasks/82379f9c-aef7-4da6-8700-276d24807ba4 |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | May 10, 2025, 01:48:49 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
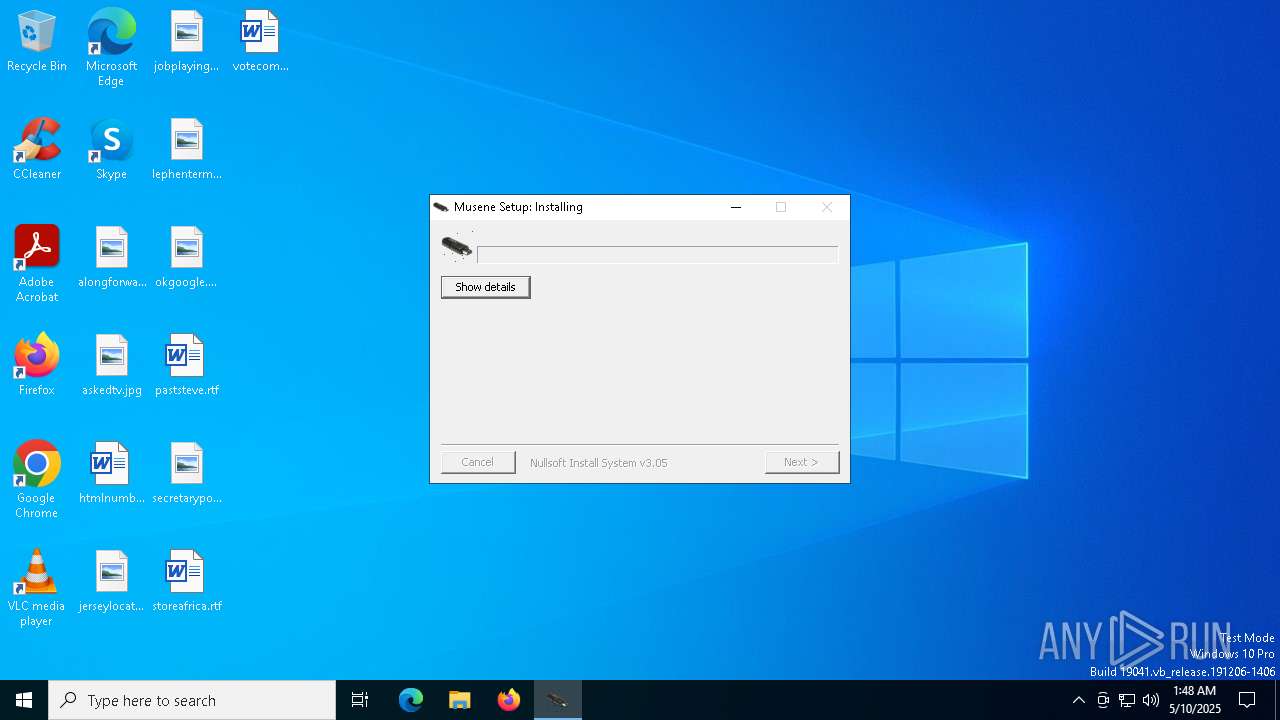
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | 4AFA11247AB2F8870BBA22D8DF0B81EC |
| SHA1: | B7792BC4EFAEB783BB66BA574C485F1B6DBAC49C |
| SHA256: | F7A0E4CF5E8723622315DC48201E61E0D619A7FAD34E2F7AB26592B66B7ED7E3 |
| SSDEEP: | 24576:jwew8LUeWCPUD7F9U55G0ZEB4jLFRRfW10EHs91UHBad/zL1DZ19JbPD12LhSEEU:jwew8LUeWCPUDh9U55G0ZEqjLFRRfW1v |
MALICIOUS
AGENTTESLA has been detected (YARA)
- 4afa11247ab2f8870bba22d8df0b81ec.exe (PID: 7488)
AGENTTESLA has been detected (SURICATA)
- 4afa11247ab2f8870bba22d8df0b81ec.exe (PID: 7488)
Steals credentials from Web Browsers
- 4afa11247ab2f8870bba22d8df0b81ec.exe (PID: 7488)
Actions looks like stealing of personal data
- 4afa11247ab2f8870bba22d8df0b81ec.exe (PID: 7488)
SUSPICIOUS
Checks for external IP
- svchost.exe (PID: 2196)
- 4afa11247ab2f8870bba22d8df0b81ec.exe (PID: 7488)
Malware-specific behavior (creating "System.dll" in Temp)
- 4afa11247ab2f8870bba22d8df0b81ec.exe (PID: 7296)
Executable content was dropped or overwritten
- 4afa11247ab2f8870bba22d8df0b81ec.exe (PID: 7296)
Application launched itself
- 4afa11247ab2f8870bba22d8df0b81ec.exe (PID: 7296)
The process creates files with name similar to system file names
- 4afa11247ab2f8870bba22d8df0b81ec.exe (PID: 7296)
Connects to the server without a host name
- 4afa11247ab2f8870bba22d8df0b81ec.exe (PID: 7488)
Reads security settings of Internet Explorer
- 4afa11247ab2f8870bba22d8df0b81ec.exe (PID: 7488)
There is functionality for taking screenshot (YARA)
- 4afa11247ab2f8870bba22d8df0b81ec.exe (PID: 7488)
Connects to unusual port
- 4afa11247ab2f8870bba22d8df0b81ec.exe (PID: 7488)
Connects to FTP
- 4afa11247ab2f8870bba22d8df0b81ec.exe (PID: 7488)
INFO
Reads the computer name
- 4afa11247ab2f8870bba22d8df0b81ec.exe (PID: 7296)
- 4afa11247ab2f8870bba22d8df0b81ec.exe (PID: 7488)
Create files in a temporary directory
- 4afa11247ab2f8870bba22d8df0b81ec.exe (PID: 7296)
The sample compiled with english language support
- 4afa11247ab2f8870bba22d8df0b81ec.exe (PID: 7296)
Checks supported languages
- 4afa11247ab2f8870bba22d8df0b81ec.exe (PID: 7296)
- 4afa11247ab2f8870bba22d8df0b81ec.exe (PID: 7488)
Disables trace logs
- 4afa11247ab2f8870bba22d8df0b81ec.exe (PID: 7488)
Reads the software policy settings
- slui.exe (PID: 7384)
Reads the machine GUID from the registry
- 4afa11247ab2f8870bba22d8df0b81ec.exe (PID: 7488)
Checks proxy server information
- 4afa11247ab2f8870bba22d8df0b81ec.exe (PID: 7488)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:12:16 00:50:53+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26112 |
| InitializedDataSize: | 141824 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x350d |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.3.0.0 |
| ProductVersionNumber: | 2.3.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comments: | powerset |
| CompanyName: | masjas shakable |
| FileDescription: | upgirds protuberous |
| ProductName: | spandes gaardhavehus unnumbed |
Total processes
134
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7204 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7296 | "C:\Users\admin\AppData\Local\Temp\4afa11247ab2f8870bba22d8df0b81ec.exe" | C:\Users\admin\AppData\Local\Temp\4afa11247ab2f8870bba22d8df0b81ec.exe | explorer.exe | ||||||||||||
User: admin Company: masjas shakable Integrity Level: MEDIUM Description: upgirds protuberous Exit code: 0 Modules
| |||||||||||||||
| 7352 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7384 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7488 | "C:\Users\admin\AppData\Local\Temp\4afa11247ab2f8870bba22d8df0b81ec.exe" | C:\Users\admin\AppData\Local\Temp\4afa11247ab2f8870bba22d8df0b81ec.exe | 4afa11247ab2f8870bba22d8df0b81ec.exe | ||||||||||||
User: admin Company: masjas shakable Integrity Level: MEDIUM Description: upgirds protuberous Modules
| |||||||||||||||
Total events
3 481
Read events
2 151
Write events
1 330
Delete events
0
Modification events
| (PID) Process: | (7296) 4afa11247ab2f8870bba22d8df0b81ec.exe | Key: | HKEY_CURRENT_USER\alkali\Uninstall\Iconically95 |
| Operation: | write | Name: | yesternight |
Value: 1 | |||
| (PID) Process: | (7296) 4afa11247ab2f8870bba22d8df0b81ec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Locales Approx |
| Operation: | write | Name: | C Langs |
Value: u | |||
| (PID) Process: | (7296) 4afa11247ab2f8870bba22d8df0b81ec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Locales Approx |
| Operation: | write | Name: | C Langs |
Value: us | |||
| (PID) Process: | (7296) 4afa11247ab2f8870bba22d8df0b81ec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Locales Approx |
| Operation: | write | Name: | C Langs |
Value: use | |||
| (PID) Process: | (7296) 4afa11247ab2f8870bba22d8df0b81ec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Locales Approx |
| Operation: | write | Name: | C Langs |
Value: user | |||
| (PID) Process: | (7296) 4afa11247ab2f8870bba22d8df0b81ec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Locales Approx |
| Operation: | write | Name: | C Langs |
Value: user3 | |||
| (PID) Process: | (7296) 4afa11247ab2f8870bba22d8df0b81ec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Locales Approx |
| Operation: | write | Name: | C Langs |
Value: user32 | |||
| (PID) Process: | (7296) 4afa11247ab2f8870bba22d8df0b81ec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Locales Approx |
| Operation: | write | Name: | C Langs |
Value: user32: | |||
| (PID) Process: | (7296) 4afa11247ab2f8870bba22d8df0b81ec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Locales Approx |
| Operation: | write | Name: | C Langs |
Value: user32:: | |||
| (PID) Process: | (7296) 4afa11247ab2f8870bba22d8df0b81ec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Locales Approx |
| Operation: | write | Name: | C Langs |
Value: user32::S | |||
Executable files
1
Suspicious files
5
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7296 | 4afa11247ab2f8870bba22d8df0b81ec.exe | C:\Users\admin\AppData\Local\Temp\ostene\Barfodsdanss\Flberiets.Par | binary | |
MD5:8702B8BD7943A42915857027A8D638F3 | SHA256:5CF93CAC004129677791E49BAEC232637814D7983046E890847AEDAF521759E8 | |||
| 7296 | 4afa11247ab2f8870bba22d8df0b81ec.exe | C:\Users\admin\AppData\Local\Temp\ostene\Barfodsdanss\Underkue\tatchy.sti | binary | |
MD5:8D879505BD68E608A20B75B0B4A493CD | SHA256:766540C36B244E4DEBF17A600C5E602D156BEBFA29B54D34B1F525A9C7AAEF94 | |||
| 7296 | 4afa11247ab2f8870bba22d8df0b81ec.exe | C:\Users\admin\AppData\Local\Temp\Settings.ini | text | |
MD5:A6216EF9FBE57B11DEEB1B1FD840C392 | SHA256:EDF6C9DA71DAF3B3DA2E89A1BC6B9F4B812F18FC133CF4706A3AE983E4040946 | |||
| 7296 | 4afa11247ab2f8870bba22d8df0b81ec.exe | C:\Users\admin\AppData\Local\Temp\ostene\Barfodsdanss\Underkue\libertinerens.trk | binary | |
MD5:EAD518D3C64C03D2D94DB19D7E650EFF | SHA256:F677AB6FDA35EE637C7CAC9DC5A9EF8D06DEDA2B37C67EC21A4DD36F417E565E | |||
| 7296 | 4afa11247ab2f8870bba22d8df0b81ec.exe | C:\Users\admin\AppData\Local\Temp\ostene\Barfodsdanss\Underkue\snetykning.jpg | image | |
MD5:5C16C56F093146AE96CD40F58062D40D | SHA256:4C52D8B84F837BA3A57F3C2799C864CFC5ABA4B891A7849AB46CE1384179AF9A | |||
| 7296 | 4afa11247ab2f8870bba22d8df0b81ec.exe | C:\Users\admin\AppData\Local\Temp\ostene\Pitmen\undersgelseskommision.jpg | image | |
MD5:64913A1D2CAA43204A7293BAD88E9E13 | SHA256:8FAFCDB3462454BE61FE3586AAA7897577E16743164C8840C68780A58718B91A | |||
| 7296 | 4afa11247ab2f8870bba22d8df0b81ec.exe | C:\Users\admin\AppData\Local\Temp\ostene\Barfodsdanss\amtsplejehjem.ftc | binary | |
MD5:703A3F5142242E63C1ABA6C1A4494028 | SHA256:3B0D585D3841E0FE254D2296A589252955290F6DC52A7A700ACFF31EE8DA4878 | |||
| 7296 | 4afa11247ab2f8870bba22d8df0b81ec.exe | C:\Users\admin\AppData\Local\Temp\nsxBC50.tmp\System.dll | executable | |
MD5:8CF2AC271D7679B1D68EEFC1AE0C5618 | SHA256:6950991102462D84FDC0E3B0AE30C95AF8C192F77CE3D78E8D54E6B22F7C09BA | |||
| 7296 | 4afa11247ab2f8870bba22d8df0b81ec.exe | C:\Users\admin\AppData\Local\Temp\nsgB931.tmp | binary | |
MD5:7F9799C5549872CA3D911B3BD3C0CA5A | SHA256:064D2E6E31DE35850FD455E3CF42F03B450F926DF82CA67FA5C42B01DED056EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
26
DNS requests
17
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.25:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.25:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7488 | 4afa11247ab2f8870bba22d8df0b81ec.exe | GET | 200 | 192.210.214.133:80 | http://192.210.214.133/ryYoBjjOUNK30.bin | unknown | — | — | unknown |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7488 | 4afa11247ab2f8870bba22d8df0b81ec.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | — | — | whitelisted |
8144 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8144 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.216.77.25:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.25:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7488 | 4afa11247ab2f8870bba22d8df0b81ec.exe | 192.210.214.133:80 | — | AS-COLOCROSSING | US | unknown |
6544 | svchost.exe | 40.126.32.140:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ip-api.com |
| whitelisted |
ftp.horeca-bucuresti.ro |
| unknown |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7488 | 4afa11247ab2f8870bba22d8df0b81ec.exe | Potentially Bad Traffic | ET HUNTING Generic .bin download from Dotted Quad |
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
7488 | 4afa11247ab2f8870bba22d8df0b81ec.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |
7488 | 4afa11247ab2f8870bba22d8df0b81ec.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
7488 | 4afa11247ab2f8870bba22d8df0b81ec.exe | Misc activity | INFO [ANY.RUN] FTP protocol command for uploading a file |
7488 | 4afa11247ab2f8870bba22d8df0b81ec.exe | A Network Trojan was detected | ET MALWARE AgentTesla Exfil via FTP |
7488 | 4afa11247ab2f8870bba22d8df0b81ec.exe | A Network Trojan was detected | STEALER [ANY.RUN] AgentTesla Exfiltration (raw TCP) |
7488 | 4afa11247ab2f8870bba22d8df0b81ec.exe | A Network Trojan was detected | STEALER [ANY.RUN] AgentTesla Exfiltration (raw TCP) |
7488 | 4afa11247ab2f8870bba22d8df0b81ec.exe | Misc activity | INFO [ANY.RUN] FTP server is ready for the new user |