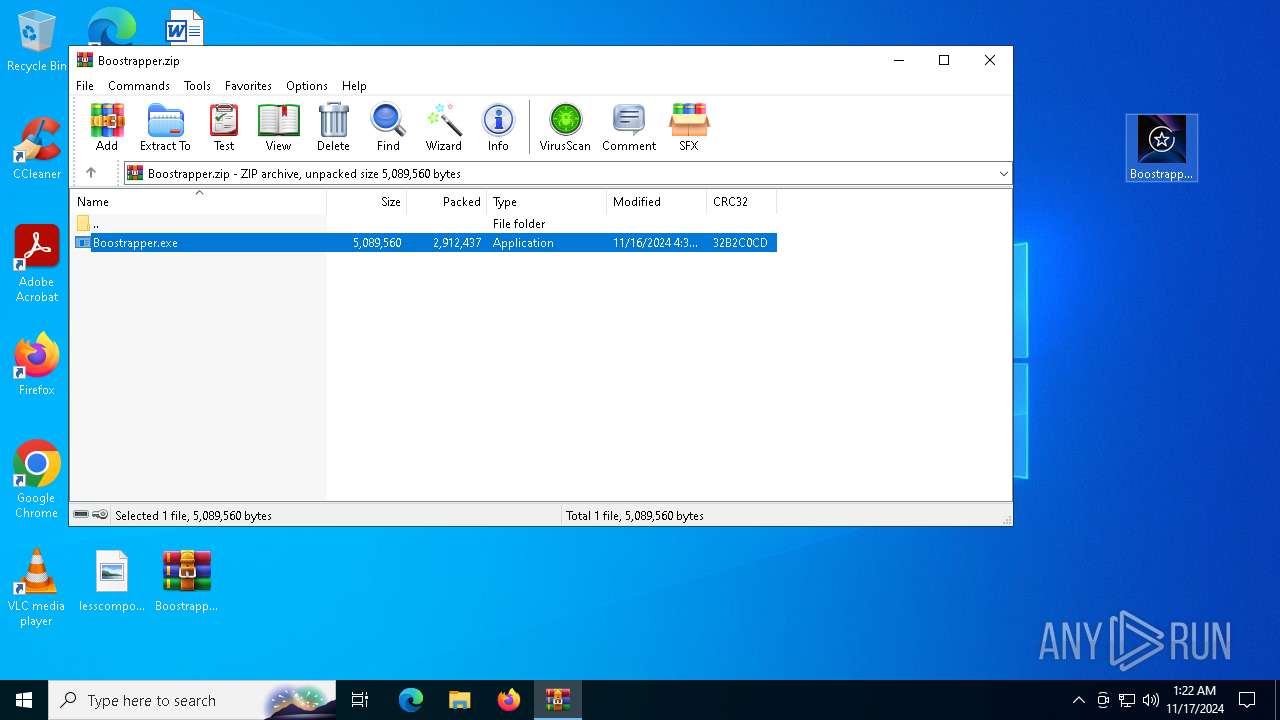
| File name: | Boostrapper.zip |
| Full analysis: | https://app.any.run/tasks/f64adf90-3f64-4766-b28f-556c9ff0651a |
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | November 17, 2024, 01:22:28 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
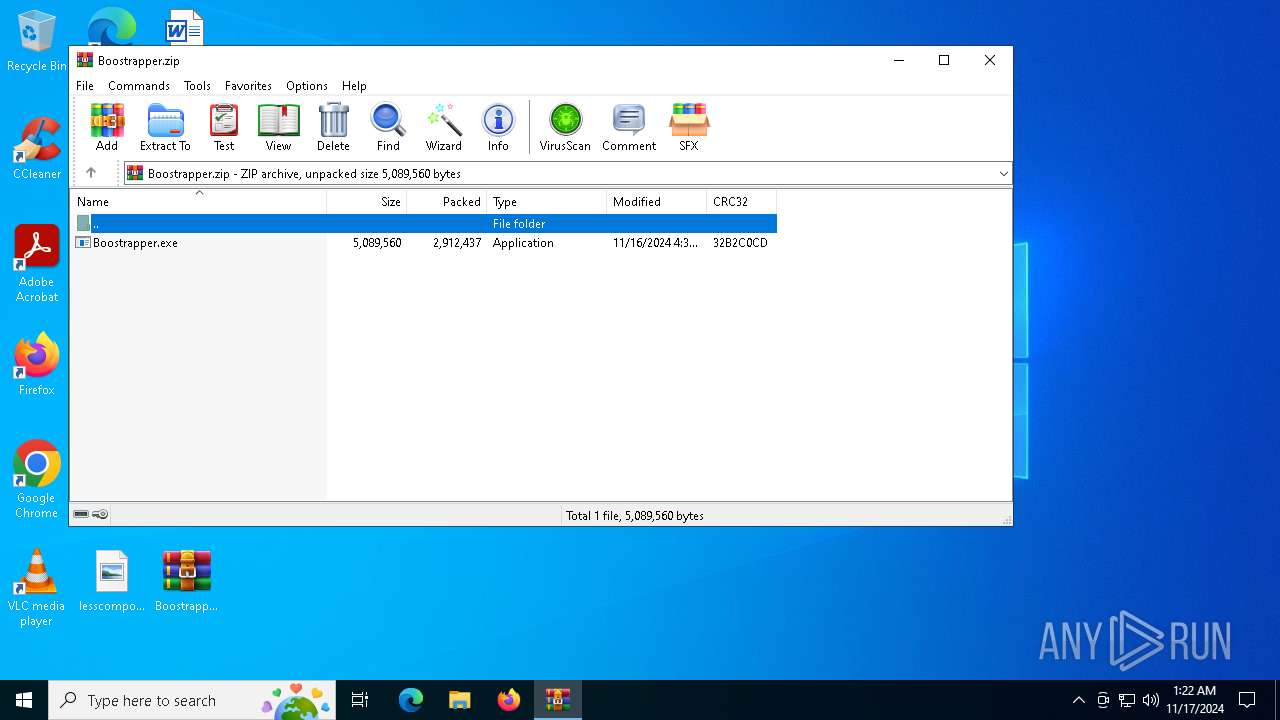
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 6DF00C2C21AC7903FAFAD3934E921BD1 |
| SHA1: | BD12ACBAC708902A62AD5F1425D20B2B73939FFE |
| SHA256: | F77F6A111A3C4B43E65EF17B6313DB21AB766BC67046DE4E78E3DE5A0439FEBC |
| SSDEEP: | 98304:oUJxiOWh9lMYV37VR45eXH5z7E2hEcFJRCAJG9di7wePSvtlcVdyzdG6jdbSJbtL:ld+Cu |
MALICIOUS
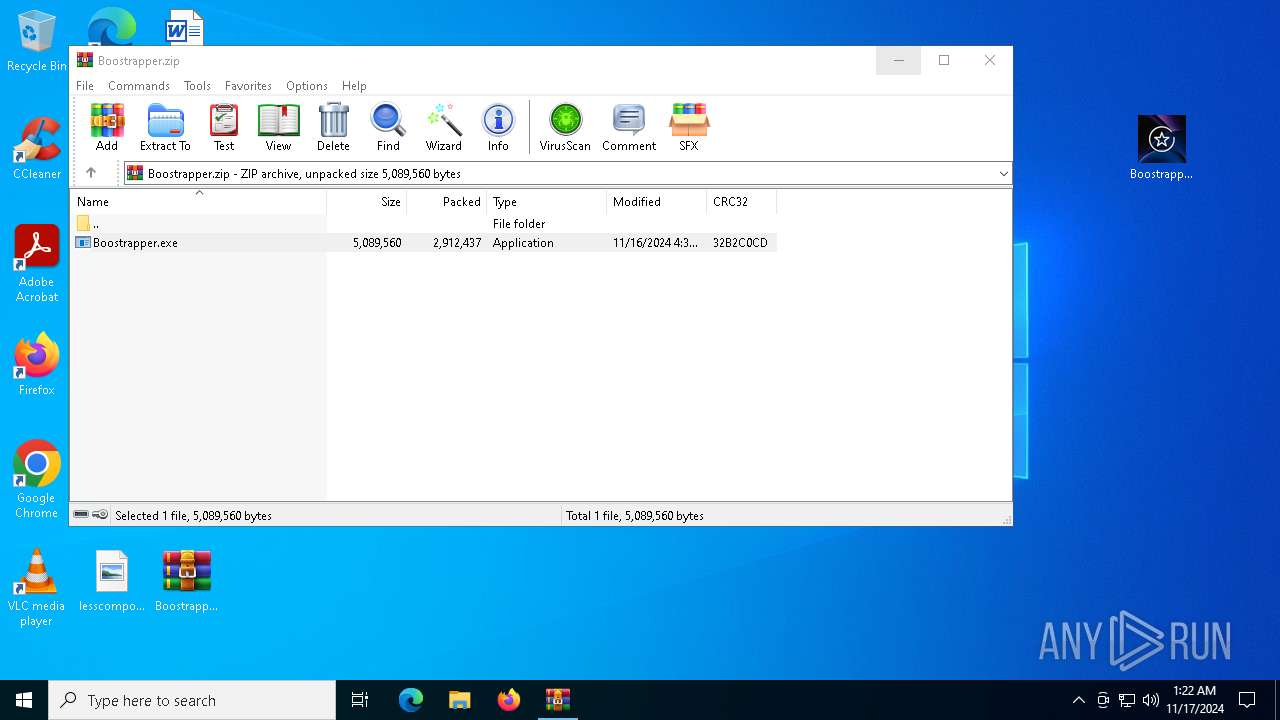
Generic archive extractor
- WinRAR.exe (PID: 4072)
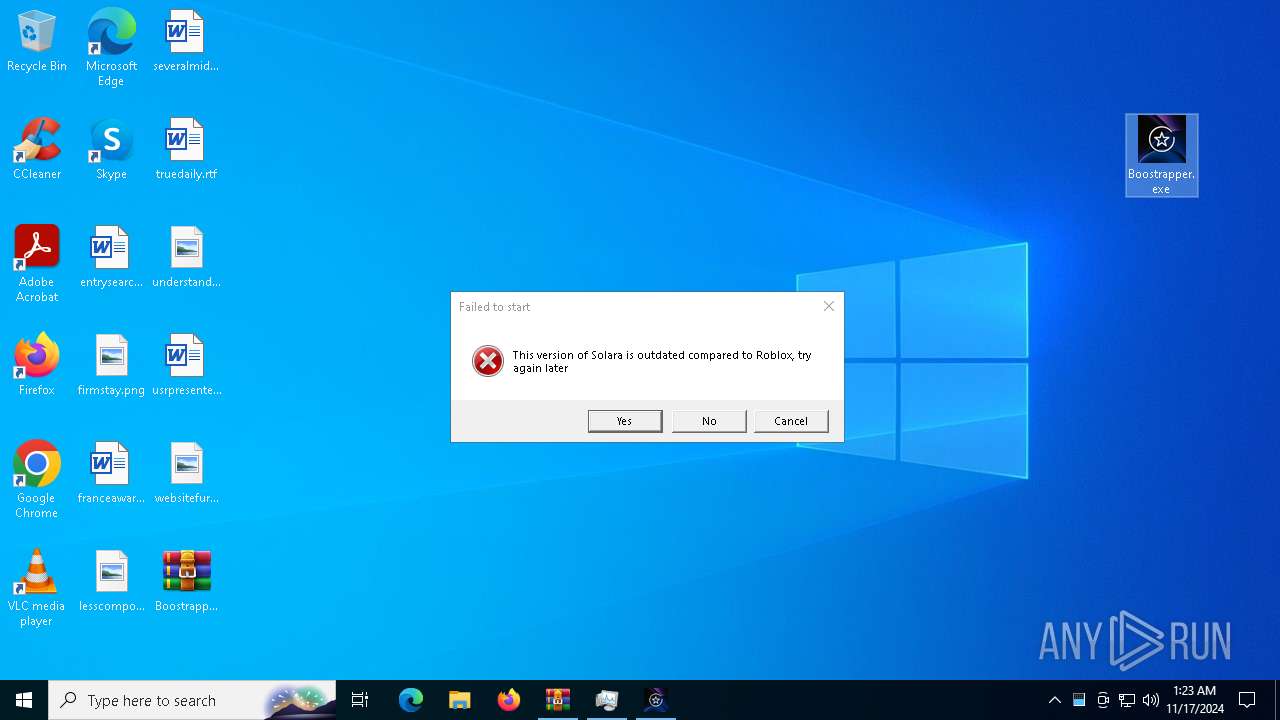
Executing a file with an untrusted certificate
- Boostrapper.exe (PID: 6684)
- Boostrapper.exe (PID: 1952)
Looks like the application has launched a miner
- AddInProcess32.exe (PID: 4548)
MINER has been detected (SURICATA)
- AntiMalwareService.exe (PID: 5236)
- AntiMalwareService.exe (PID: 7080)
Connects to the CnC server
- AntiMalwareService.exe (PID: 5236)
- AntiMalwareService.exe (PID: 7080)
SUSPICIOUS
Process drops legitimate windows executable
- AddInProcess32.exe (PID: 4548)
Executable content was dropped or overwritten
- AddInProcess32.exe (PID: 4548)
Potential Corporate Privacy Violation
- AntiMalwareService.exe (PID: 5236)
- AntiMalwareService.exe (PID: 7080)
Crypto Currency Mining Activity Detected
- AntiMalwareService.exe (PID: 5236)
- AntiMalwareService.exe (PID: 7080)
Connects to unusual port
- AntiMalwareService.exe (PID: 5236)
- AntiMalwareService.exe (PID: 7080)
INFO
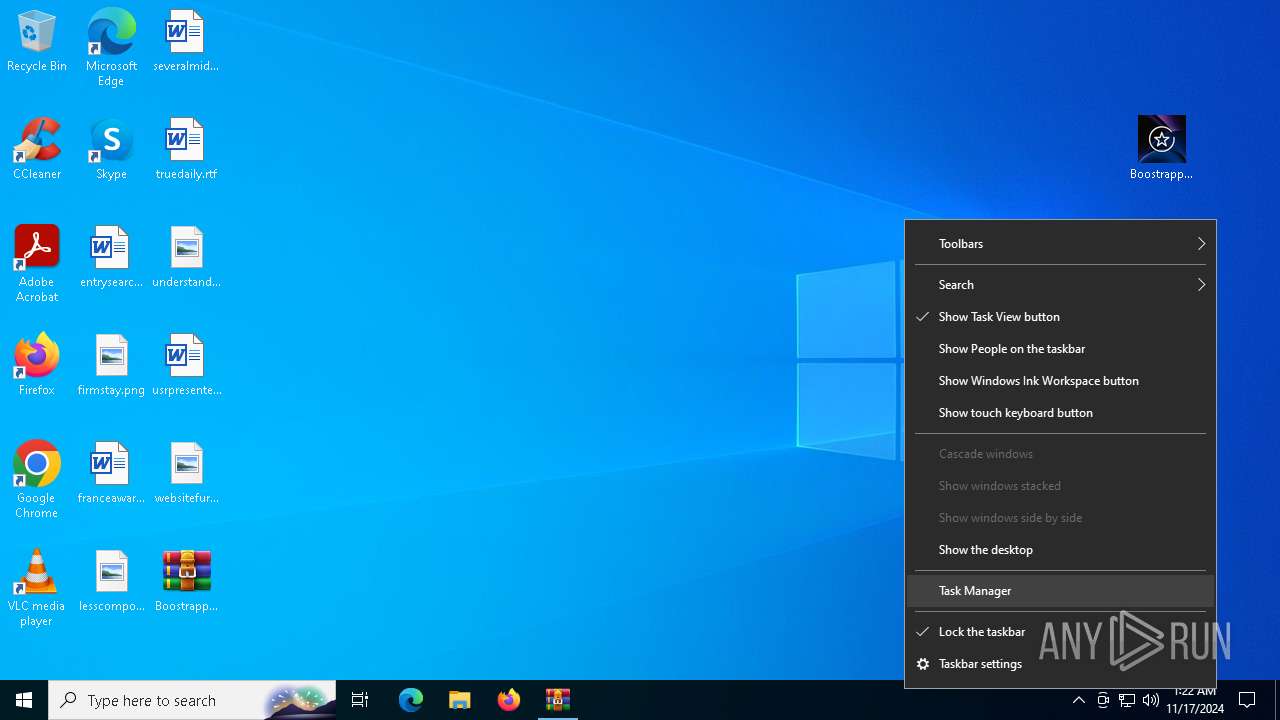
Manual execution by a user
- Boostrapper.exe (PID: 6684)
- Taskmgr.exe (PID: 6992)
- Taskmgr.exe (PID: 7132)
- Boostrapper.exe (PID: 1952)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4072)
Sends debugging messages
- Boostrapper.exe (PID: 6684)
- Boostrapper.exe (PID: 1952)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:11:15 23:36:24 |
| ZipCRC: | 0x32b2c0cd |
| ZipCompressedSize: | 2912437 |
| ZipUncompressedSize: | 5089560 |
| ZipFileName: | Boostrapper.exe |
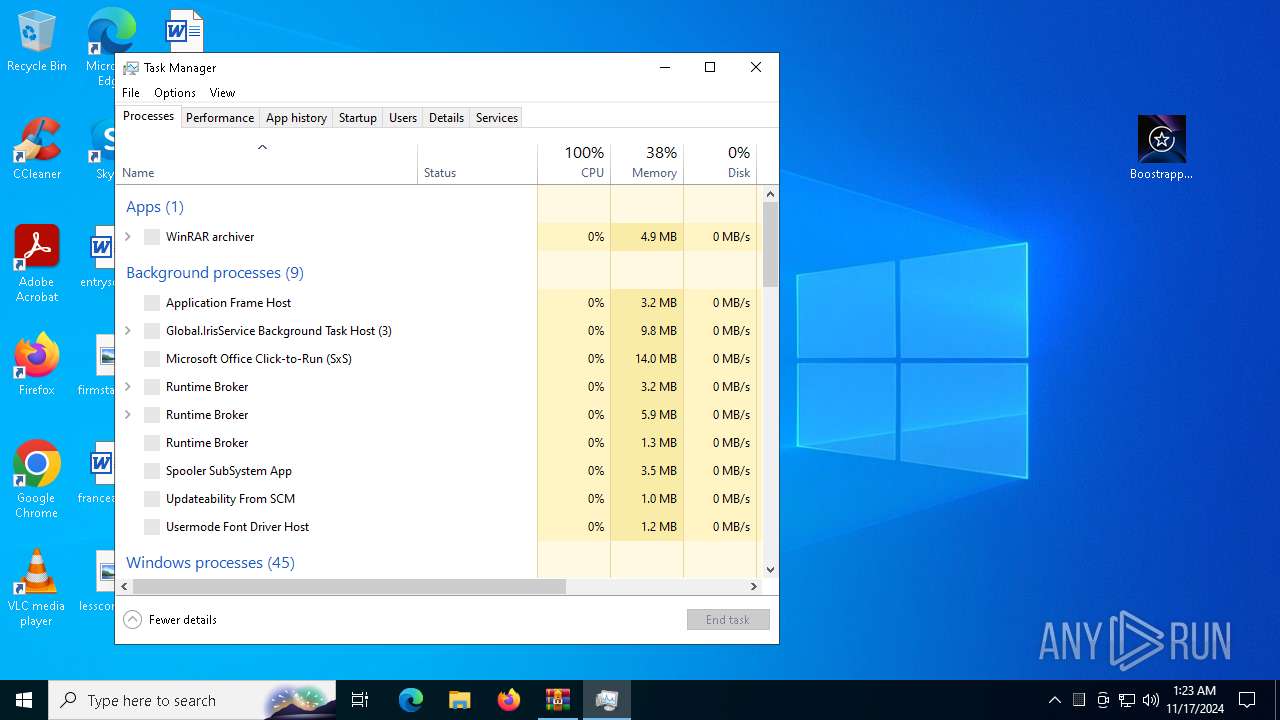
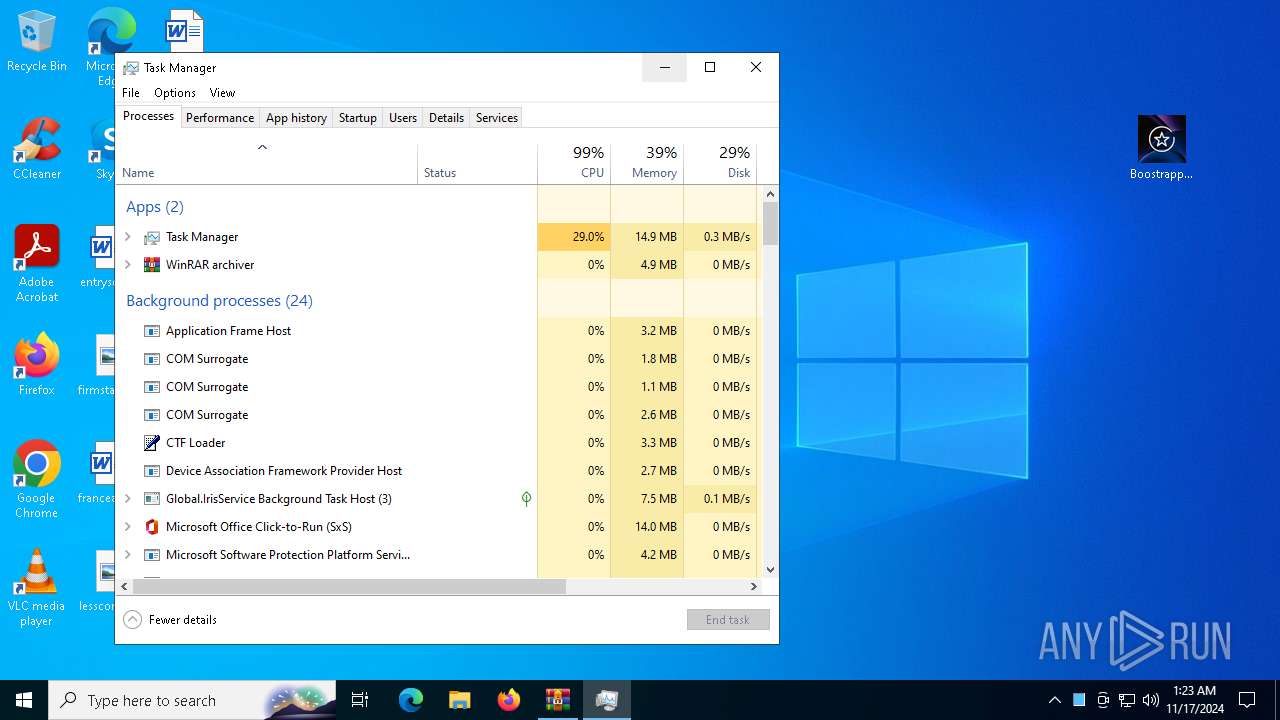
Total processes
144
Monitored processes
12
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1952 | "C:\Users\admin\Desktop\Boostrapper.exe" | C:\Users\admin\Desktop\Boostrapper.exe | — | explorer.exe | |||||||||||
User: admin Company: 1 Integrity Level: MEDIUM Description: Solara V3 Version: 1.1.1.1 Modules
| |||||||||||||||
| 3028 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | AntiMalwareService.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
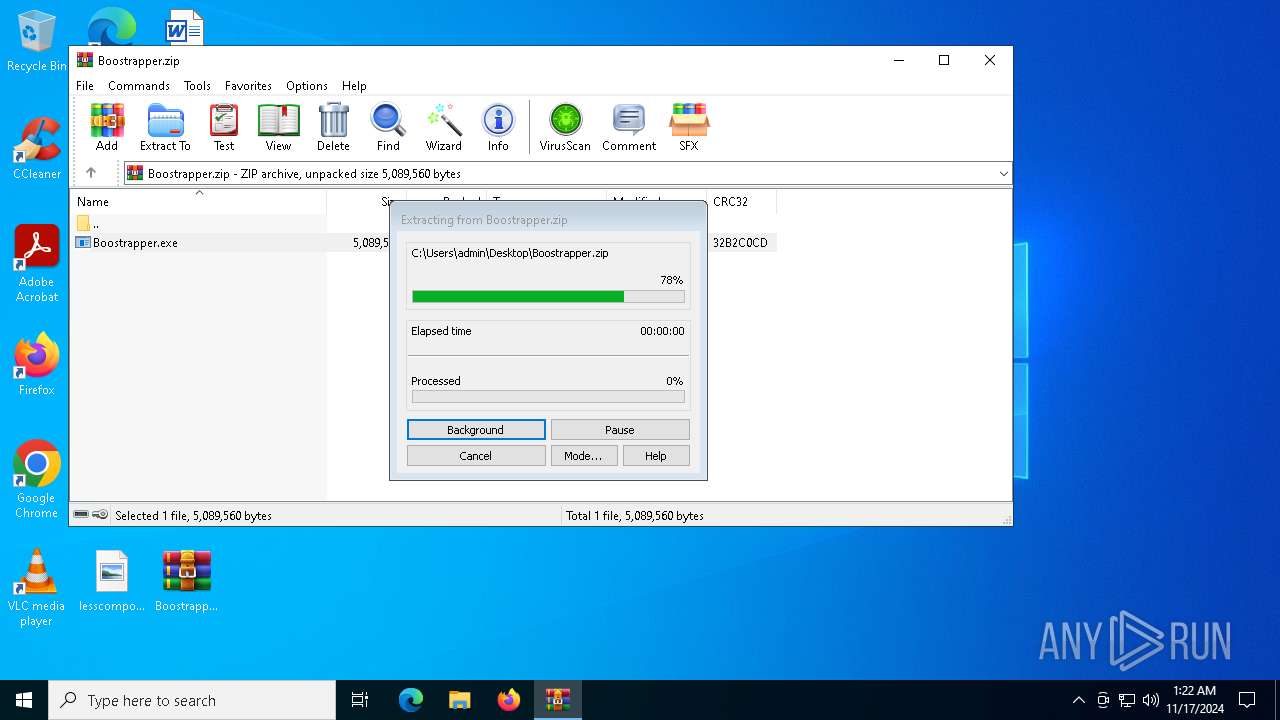
| 4072 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\Boostrapper.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 4548 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\AddInProcess32.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\AddInProcess32.exe | Boostrapper.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: AddInProcess.exe Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 5236 | --scrypt -o stratum+tcp://us2.litecoinpool.org:3333 -u youngaos.231 -p 123456 | C:\Users\admin\AppData\Roaming\Windows Defender\AntiMalwareService.exe | AddInProcess32.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 6684 | "C:\Users\admin\Desktop\Boostrapper.exe" | C:\Users\admin\Desktop\Boostrapper.exe | — | explorer.exe | |||||||||||
User: admin Company: 1 Integrity Level: MEDIUM Description: Solara V3 Exit code: 0 Version: 1.1.1.1 Modules
| |||||||||||||||
| 6992 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\Windows\System32\Taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Manager Exit code: 3221226540 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6992 | --scrypt -o stratum+tcp://us2.litecoinpool.org:3333 -u youngaos.231 -p 123456 | C:\Users\admin\AppData\Roaming\Windows Defender\AntiMalwareService.exe | — | AddInProcess32.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 7052 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\AddInProcess32.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\AddInProcess32.exe | — | Boostrapper.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: AddInProcess.exe Exit code: 4294967295 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 7080 | --scrypt -o stratum+tcp://us2.litecoinpool.org:3333 -u youngaos.231 -p 123456 | C:\Users\admin\AppData\Roaming\Windows Defender\AntiMalwareService.exe | AddInProcess32.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
Total events
3 897
Read events
3 888
Write events
8
Delete events
1
Modification events
| (PID) Process: | (4072) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (4072) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Boostrapper.zip | |||
| (PID) Process: | (4072) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4072) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4072) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4072) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7132) Taskmgr.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\TaskManager |
| Operation: | delete value | Name: | Preferences |
Value: | |||
| (PID) Process: | (7132) Taskmgr.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\TaskManager |
| Operation: | write | Name: | Preferences |
Value: 0D00000060000000600000006800000068000000E3010000DC010000000001000000008000000080D8010080DF010080000100016B00000034000000130300008C020000E80300000000000000000000000000000F000000010000000000000058AAE92EF77F00000000000000000000000000002E0100001E0000008990000000000000FF00000001015002000000000D0000000000000098AAE92EF77F00000000000000000000FFFFFFFF960000001E0000008B900000010000000000000000101001000000000300000000000000B0AAE92EF77F00000000000000000000FFFFFFFF780000001E0000008C900000020000000000000001021200000000000400000000000000C8AAE92EF77F00000000000000000000FFFFFFFF960000001E0000008D900000030000000000000000011001000000000200000000000000E8AAE92EF77F00000000000000000000FFFFFFFF320000001E0000008A90000004000000000000000008200100000000050000000000000000ABE92EF77F00000000000000000000FFFFFFFFC80000001E0000008E90000005000000000000000001100100000000060000000000000028ABE92EF77F00000000000000000000FFFFFFFF040100001E0000008F90000006000000000000000001100100000000070000000000000050ABE92EF77F00000000000000000000FFFFFFFF49000000490000009090000007000000000000000004250000000000080000000000000080AAE92EF77F00000000000000000000FFFFFFFF49000000490000009190000008000000000000000004250000000000090000000000000070ABE92EF77F00000000000000000000FFFFFFFF490000004900000092900000090000000000000000042508000000000A0000000000000088ABE92EF77F00000000000000000000FFFFFFFF4900000049000000939000000A0000000000000000042508000000000B00000000000000A8ABE92EF77F00000000000000000000FFFFFFFF490000004900000039A000000B0000000000000000042509000000001C00000000000000C8ABE92EF77F00000000000000000000FFFFFFFFC8000000490000003AA000000C0000000000000000011009000000001D00000000000000F0ABE92EF77F00000000000000000000FFFFFFFF64000000490000004CA000000D0000000000000000021508000000001E0000000000000010ACE92EF77F00000000000000000000FFFFFFFF64000000490000004DA000000E000000000000000002150800000000030000000A000000010000000000000058AAE92EF77F0000000000000000000000000000D70000001E0000008990000000000000FF00000001015002000000000400000000000000C8AAE92EF77F0000000000000000000001000000960000001E0000008D900000010000000000000001011000000000000300000000000000B0AAE92EF77F00000000000000000000FFFFFFFF640000001E0000008C900000020000000000000000021000000000000C0000000000000040ACE92EF77F0000000000000000000003000000640000001E00000094900000030000000000000001021000000000000D0000000000000068ACE92EF77F00000000000000000000FFFFFFFF640000001E00000095900000040000000000000000011001000000000E0000000000000090ACE92EF77F0000000000000000000005000000320000001E00000096900000050000000000000001042001000000000F00000000000000B8ACE92EF77F0000000000000000000006000000320000001E00000097900000060000000000000001042001000000001000000000000000D8ACE92EF77F0000000000000000000007000000460000001E00000098900000070000000000000001011001000000001100000000000000F8ACE92EF77F00000000000000000000FFFFFFFF640000001E0000009990000008000000000000000001100100000000060000000000000028ABE92EF77F0000000000000000000009000000040100001E0000008F9000000900000000000000010110010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000040000000B000000010000000000000058AAE92EF77F0000000000000000000000000000D70000001E0000009E90000000000000FF0000000101500200000000120000000000000020ADE92EF77F00000000000000000000FFFFFFFF2D0000001E0000009B90000001000000000000000004200100000000140000000000000040ADE92EF77F00000000000000000000FFFFFFFF640000001E0000009D90000002000000000000000001100100000000130000000000000068ADE92EF77F00000000000000000000FFFFFFFF640000001E0000009C900000030000000000000000011001000000000300000000000000B0AAE92EF77F00000000000000000000FFFFFFFF640000001E0000008C90000004000000000000000102100000000000070000000000000050ABE92EF77F000000000000000000000500000049000000490000009090000005000000000000000104210000000000080000000000000080AAE92EF77F000000000000000000000600000049000000490000009190000006000000000000000104210000000000090000000000000070ABE92EF77F0000000000000000000007000000490000004900000092900000070000000000000001042108000000000A0000000000000088ABE92EF77F0000000000000000000008000000490000004900000093900000080000000000000001042108000000000B00000000000000A8ABE92EF77F0000000000000000000009000000490000004900000039A00000090000000000000001042109000000001C00000000000000C8ABE92EF77F000000000000000000000A00000064000000490000003AA000000A00000000000000000110090000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000200000008000000010000000000000058AAE92EF77F0000000000000000000000000000C60000001E000000B090000000000000FF0000000101500200000000150000000000000088ADE92EF77F00000000000000000000FFFFFFFF6B0000001E000000B1900000010000000000000000042500000000001600000000000000B8ADE92EF77F00000000000000000000FFFFFFFF6B0000001E000000B2900000020000000000000000042500000000001800000000000000E0ADE92EF77F00000000000000000000FFFFFFFF6B0000001E000000B490000003000000000000000004250000000000170000000000000008AEE92EF77F00000000000000000000FFFFFFFF6B0000001E000000B390000004000000000000000004250000000000190000000000000040AEE92EF77F00000000000000000000FFFFFFFFA00000001E000000B5900000050000000000000000042001000000001A0000000000000070AEE92EF77F00000000000000000000FFFFFFFF7D0000001E000000B6900000060000000000000000042001000000001B00000000000000A0AEE92EF77F00000000000000000000FFFFFFFF7D0000001E000000B790000007000000000000000004200100000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000DA00000000000000000000000000000000000000000000009D200000200000009100000064000000320000006400000050000000320000003200000028000000500000003C0000005000000050000000320000005000000050000000500000005000000050000000500000002800000050000000230000002300000023000000230000005000000050000000500000003200000032000000320000007800000078000000500000003C00000050000000500000009700000032000000780000003200000050000000500000005000000050000000000000000100000002000000030000000400000005000000060000000700000008000000090000000A0000000B0000000C0000000D0000000E0000000F000000100000001100000012000000130000001400000015000000160000001700000018000000190000001A0000001B0000001C0000001D0000001E0000001F000000200000002100000022000000230000002400000025000000260000002700000028000000290000002A0000002B0000002C00000000000000000000001F00000000000000B400000032000000D8000000640000006400000000000000000000000000000000000000000000000000000000000000000000000000000000000000DA000000000000000000000000000000000000009D200000200000009100000064000000320000009700000050000000320000003200000028000000500000003C000000500000005000000032000000500000005000000050000000500000005000000050000000500000002800000050000000230000002300000023000000230000005000000050000000500000003200000032000000320000007800000078000000500000003C0000005000000064000000780000003200000078000000780000003200000050000000500000005000000050000000C8000000000000000100000002000000030000000400000005000000060000000700000008000000090000000A0000000B0000000C0000000D0000000E0000000F000000100000001100000012000000130000001400000015000000160000001700000018000000190000001A0000001B0000001C0000001D0000001E0000001F000000200000002100000022000000230000002400000025000000260000002700000028000000290000002A0000002B0000002C0000002D0000002E0000002F00000000000000000000001F00000000000000B400000032000000D8000000640000006400000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000100000002000000030000000400000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000001000000000000000000000000000000 | |||
| (PID) Process: | (4548) AddInProcess32.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Windows Defender |
Value: "C:\Users\admin\AppData\Roaming\Windows Defender\Windows Defenderservice.exe" | |||
Executable files
12
Suspicious files
0
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4072 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa4072.37006\Boostrapper.exe | executable | |
MD5:472177EB02390087172670EDB0814B61 | SHA256:3C04ADD52FC973BD2A33B0702D7744D27E86D6AAB07AAEE2ED865C123F393D24 | |||
| 4548 | AddInProcess32.exe | C:\Users\admin\AppData\Roaming\Windows Defender\libidn-11.dll | executable | |
MD5:7C6F8DEE62B2E68938C5B65505248333 | SHA256:49E4B17129D1586EB80F48523F274914AEE9D5DCFA39D9F832C1DDE0B380A836 | |||
| 7132 | Taskmgr.exe | C:\Users\admin\AppData\Local\D3DSCache\3534848bb9f4cb71\F4EB2D6C-ED2B-4BDD-AD9D-F913287E6768.lock | text | |
MD5:F49655F856ACB8884CC0ACE29216F511 | SHA256:7852FCE59C67DDF1D6B8B997EAA1ADFAC004A9F3A91C37295DE9223674011FBA | |||
| 4548 | AddInProcess32.exe | C:\Users\admin\AppData\Roaming\Windows Defender\libcurl-4.dll | executable | |
MD5:48131A7C1CD5BCE34DA3EDA489A81158 | SHA256:A899458036E4CBF1B13F755FB1C65B6A63E537EE72AEFA569A9DEA590E8D3FF6 | |||
| 4548 | AddInProcess32.exe | C:\Users\admin\AppData\Roaming\Windows Defender\libeay32.dll | executable | |
MD5:9462CB83718CCAB3C744F0F5561A289D | SHA256:F08009F941680657077FFF1C8D58FAC8AFFA2216B3A478312AC48948C228C73A | |||
| 4548 | AddInProcess32.exe | C:\Users\admin\AppData\Roaming\Windows Defender\ssleay32.dll | executable | |
MD5:5935940918FA77C777FCD0475149A217 | SHA256:ED0B0F0D40C902703E212279F99C6DCF403EB75EBA4ABB058CB39129D09A6467 | |||
| 4548 | AddInProcess32.exe | C:\Users\admin\AppData\Roaming\Windows Defender\diakgcn121016.cl | text | |
MD5:E316C3C6069AEC5DAF069CAB14D44F1C | SHA256:D1BC7A702C3D0A5D7A1FC34C2432F6E16C67A006F9BF9899BA063098CD533B55 | |||
| 4548 | AddInProcess32.exe | C:\Users\admin\AppData\Roaming\Windows Defender\zlib1.dll | executable | |
MD5:15D6AF5C659FE2D9524DD9A90A674D02 | SHA256:AAD5344650F7AB0A0A396F518F7EF827B8773748220D9E48D28FE4BC7888EB0C | |||
| 4548 | AddInProcess32.exe | C:\Users\admin\AppData\Roaming\Windows Defender\diablo130302.cl | text | |
MD5:C4364C3B5D58799F6C12A3FC01B0BE01 | SHA256:0B014F0CA49CA92E3C4BD6FFF0D718FDB5A96F7699AA4DD1C67F09D562221FDA | |||
| 4548 | AddInProcess32.exe | C:\Users\admin\AppData\Roaming\Windows Defender\poclbm130302.cl | text | |
MD5:2BE08BD072F9592A44D4DD7D128CB77B | SHA256:96DE126281C280EE1A9E9FB4C9C06DCE76017E3FCC32B87B12B50958085E870D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
39
DNS requests
23
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5488 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.42:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4700 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3648 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
7164 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7164 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6944 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5640 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 23.216.77.42:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5488 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4020 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
816 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4360 | SearchApp.exe | 104.126.37.130:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5236 | AntiMalwareService.exe | Potential Corporate Privacy Violation | AV POLICY NiceHash Miner Subscribing To Pool |
5236 | AntiMalwareService.exe | Crypto Currency Mining Activity Detected | ET COINMINER W32/BitCoinMiner.MultiThreat Subscribe/Authorize Stratum Protocol Message |
5236 | AntiMalwareService.exe | Crypto Currency Mining Activity Detected | ET COINMINER W32/BitCoinMiner.MultiThreat Subscribe/Authorize Stratum Protocol Message |
7080 | AntiMalwareService.exe | Potential Corporate Privacy Violation | AV POLICY NiceHash Miner Subscribing To Pool |
7080 | AntiMalwareService.exe | Crypto Currency Mining Activity Detected | ET COINMINER W32/BitCoinMiner.MultiThreat Subscribe/Authorize Stratum Protocol Message |
7080 | AntiMalwareService.exe | Crypto Currency Mining Activity Detected | ET COINMINER W32/BitCoinMiner.MultiThreat Subscribe/Authorize Stratum Protocol Message |
7080 | AntiMalwareService.exe | Potential Corporate Privacy Violation | AV POLICY NiceHash Miner Subscribing To Pool |
7080 | AntiMalwareService.exe | Crypto Currency Mining Activity Detected | ET COINMINER W32/BitCoinMiner.MultiThreat Subscribe/Authorize Stratum Protocol Message |
5236 | AntiMalwareService.exe | Potential Corporate Privacy Violation | AV POLICY NiceHash Miner Subscribing To Pool |
5236 | AntiMalwareService.exe | Crypto Currency Mining Activity Detected | ET COINMINER W32/BitCoinMiner.MultiThreat Subscribe/Authorize Stratum Protocol Message |
4 ETPRO signatures available at the full report