| File name: | citrioloader-unpacked.rar |
| Full analysis: | https://app.any.run/tasks/eb11b66b-9774-42cd-9dab-722fd07988fc |
| Verdict: | Malicious activity |
| Threats: | Quasar is a very popular RAT in the world thanks to its code being available in open-source. This malware can be used to control the victim’s computer remotely. |
| Analysis date: | May 30, 2020, 06:34:32 |
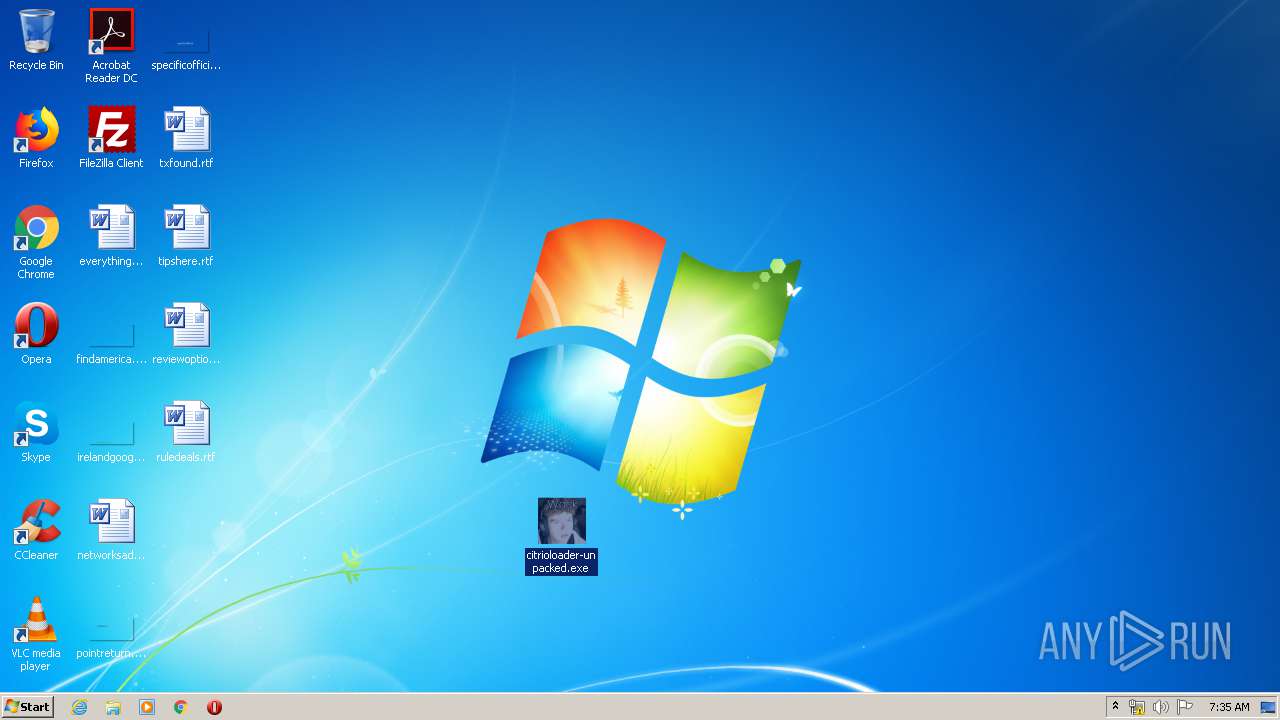
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 50ACD40EB09E10A64DBF8D3B391D9180 |
| SHA1: | E9E08329CB03D9AD3C2713BEF00F08B8C41FF1AB |
| SHA256: | F759118992AAF80AF3B17F57322FC70C56A55E459D9EBE7BBB35A558DDC60402 |
| SSDEEP: | 6144:on/BSkHFpWAhSaSXnxB0eTmjuqsgBRbTXxmGPs5Uo4cOVDjqSRVY1L5spyw:OZbliaSBBzTmNB5xmGPCUxcqzVY1Lu/ |
MALICIOUS
Application was dropped or rewritten from another process
- citrioloader-unpacked.exe (PID: 308)
- scvhost.exe (PID: 1044)
Drops/Copies Quasar RAT executable
- citrioloader-unpacked.exe (PID: 308)
Changes the autorun value in the registry
- citrioloader-unpacked.exe (PID: 308)
- scvhost.exe (PID: 1044)
QUASAR was detected
- citrioloader-unpacked.exe (PID: 308)
- scvhost.exe (PID: 1044)
SUSPICIOUS
Executable content was dropped or overwritten
- citrioloader-unpacked.exe (PID: 308)
Creates files in the user directory
- citrioloader-unpacked.exe (PID: 308)
- scvhost.exe (PID: 1044)
Starts itself from another location
- citrioloader-unpacked.exe (PID: 308)
Checks for external IP
- citrioloader-unpacked.exe (PID: 308)
- scvhost.exe (PID: 1044)
INFO
Manual execution by user
- citrioloader-unpacked.exe (PID: 308)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
41
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 308 | "C:\Users\admin\Desktop\citrioloader-unpacked.exe" | C:\Users\admin\Desktop\citrioloader-unpacked.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.3.0.0 Modules
| |||||||||||||||
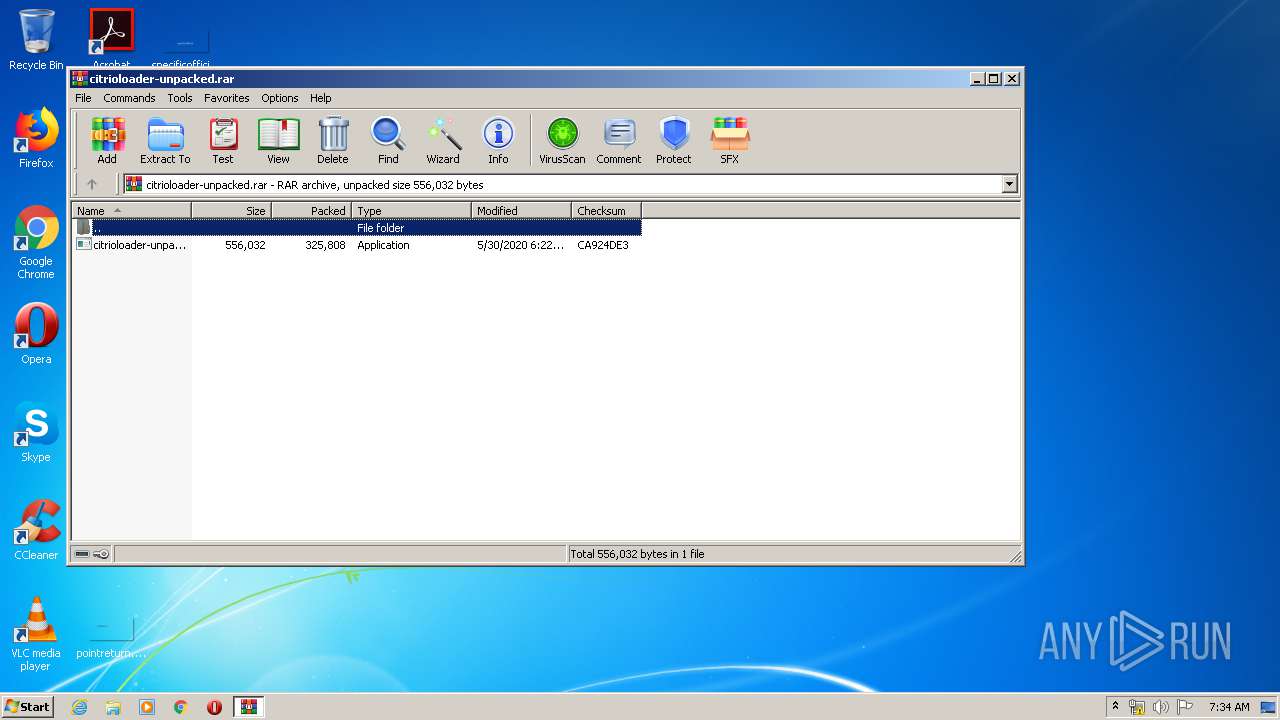
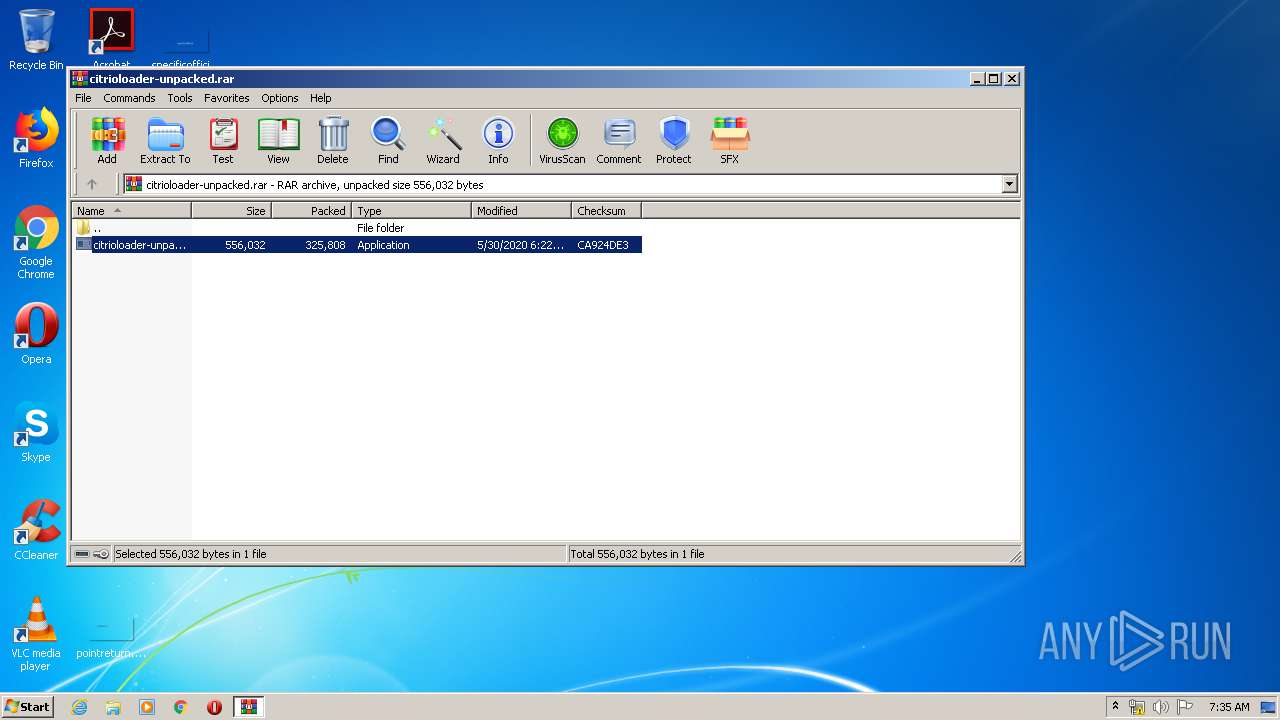
| 964 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\citrioloader-unpacked.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1044 | "C:\Users\admin\AppData\Roaming\SubDir\scvhost.exe" | C:\Users\admin\AppData\Roaming\SubDir\scvhost.exe | citrioloader-unpacked.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.3.0.0 Modules
| |||||||||||||||
Total events
532
Read events
485
Write events
47
Delete events
0
Modification events
| (PID) Process: | (964) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (964) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (964) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (964) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (964) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\citrioloader-unpacked.rar | |||
| (PID) Process: | (964) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (964) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (964) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (964) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
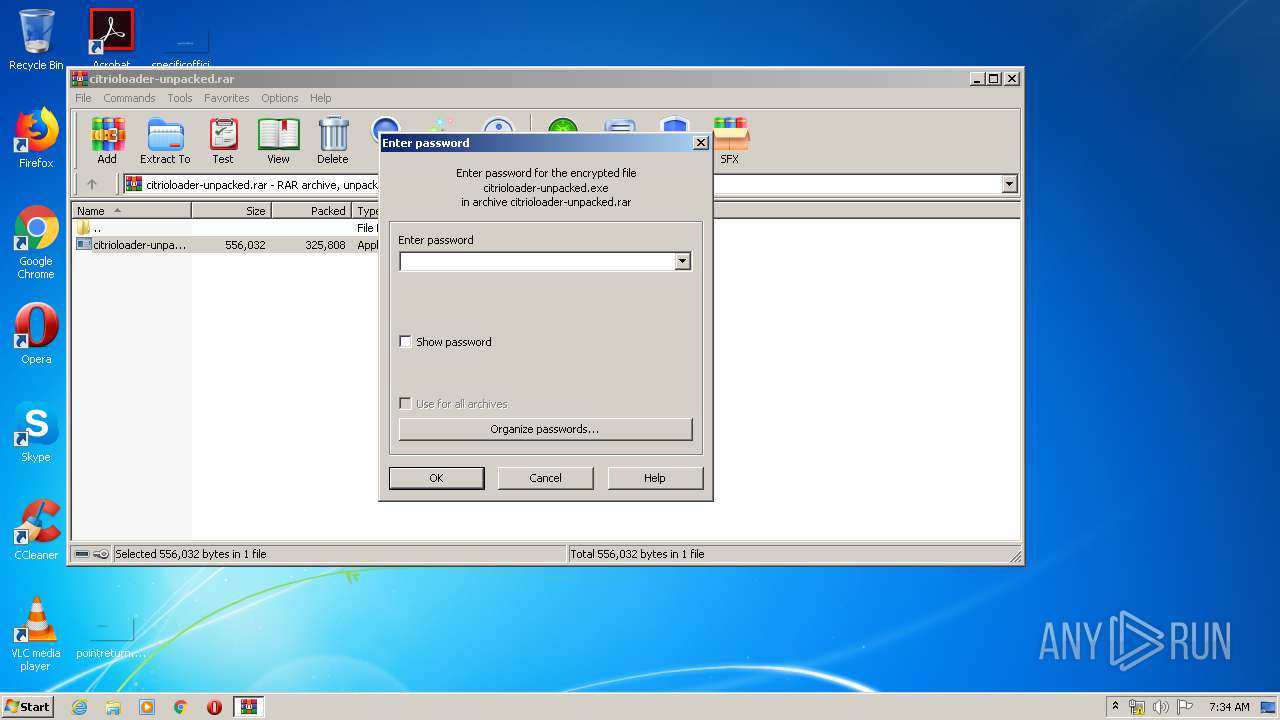
| (PID) Process: | (964) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
1
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 964 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb964.32771\citrioloader-unpacked.exe | — | |
MD5:— | SHA256:— | |||
| 308 | citrioloader-unpacked.exe | C:\Users\admin\AppData\Roaming\SubDir\scvhost.exe | executable | |
MD5:— | SHA256:— | |||
| 1044 | scvhost.exe | C:\Users\admin\AppData\Roaming\bin\05-30-2020 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
2
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1044 | scvhost.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/ | unknown | text | 301 b | malicious |
308 | citrioloader-unpacked.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/ | unknown | text | 301 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 208.95.112.1:80 | ip-api.com | IBURST | — | malicious |
1044 | scvhost.exe | 3.137.63.131:11461 | 0.tcp.ngrok.io | — | US | malicious |
1044 | scvhost.exe | 208.95.112.1:80 | ip-api.com | IBURST | — | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ip-api.com |
| malicious |
0.tcp.ngrok.io |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
308 | citrioloader-unpacked.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
308 | citrioloader-unpacked.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
308 | citrioloader-unpacked.exe | A Network Trojan was detected | REMOTE [PTsecurity] Quasar.RAT IP Lookup |
1044 | scvhost.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
1044 | scvhost.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
1044 | scvhost.exe | A Network Trojan was detected | REMOTE [PTsecurity] Quasar.RAT IP Lookup |
1060 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query to a *.ngrok domain (ngrok.io) |
1044 | scvhost.exe | A Network Trojan was detected | REMOTE [PTsecurity] Quasar |
2 ETPRO signatures available at the full report