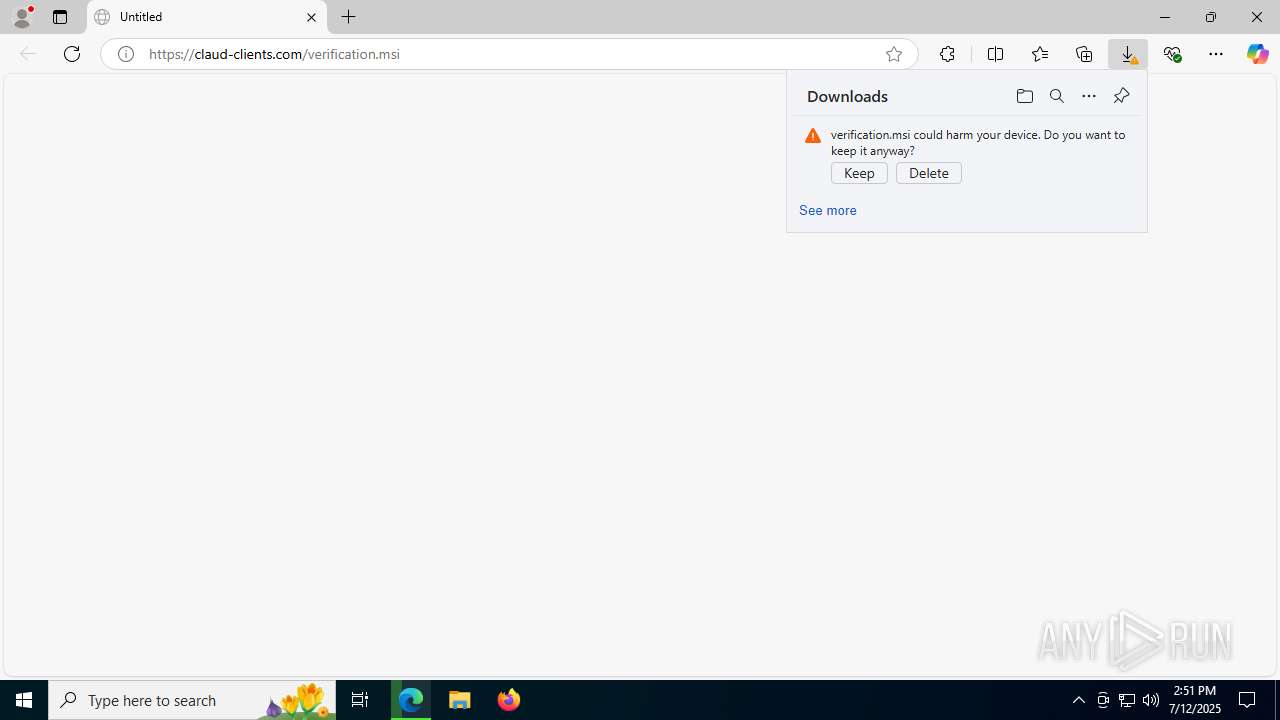
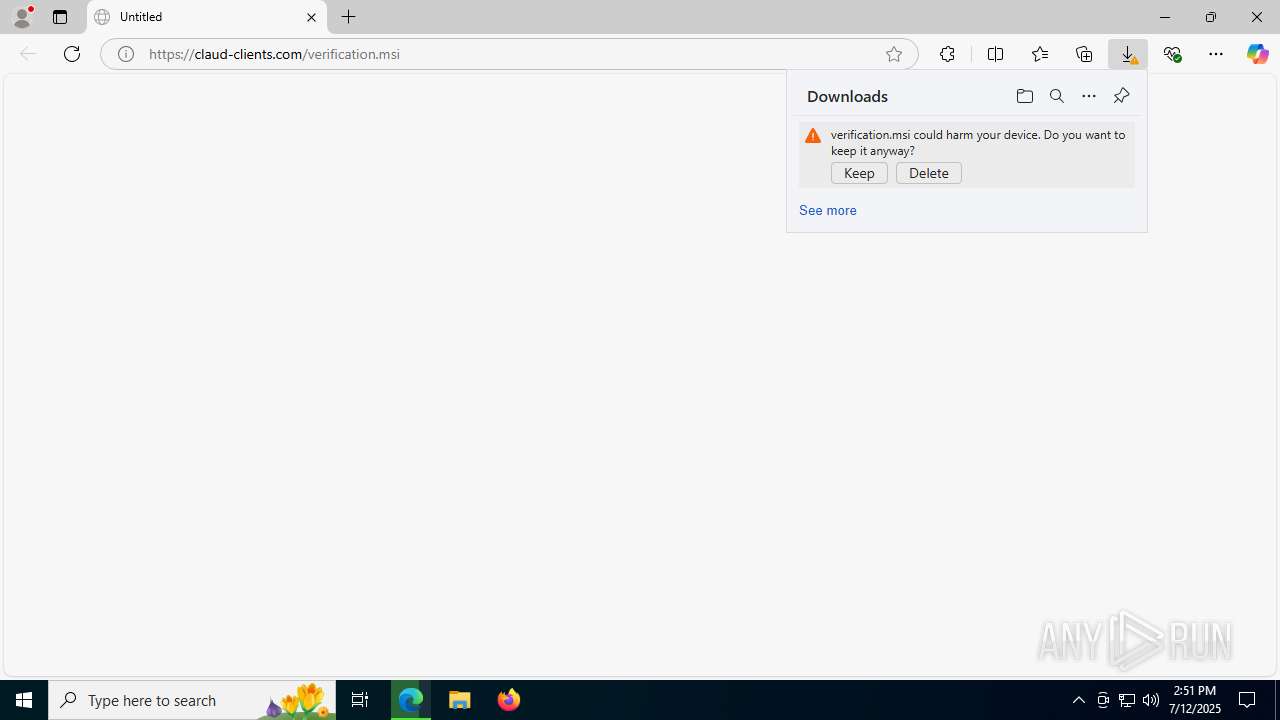
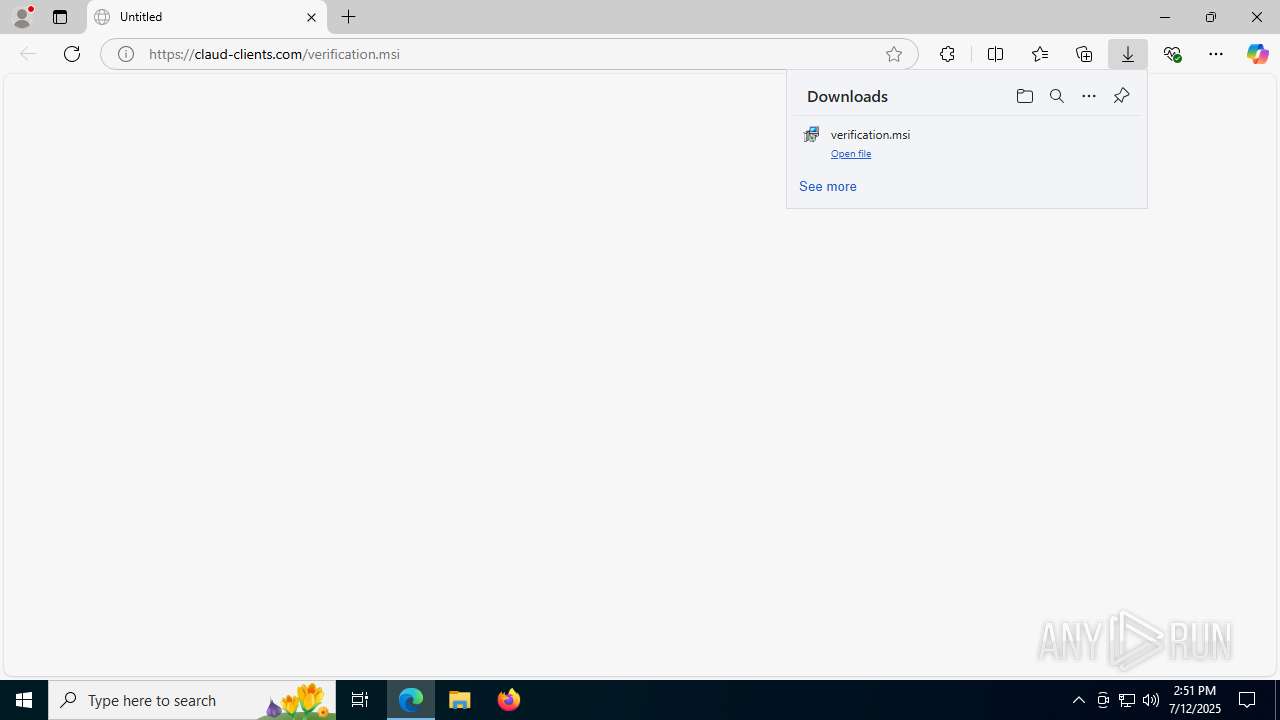
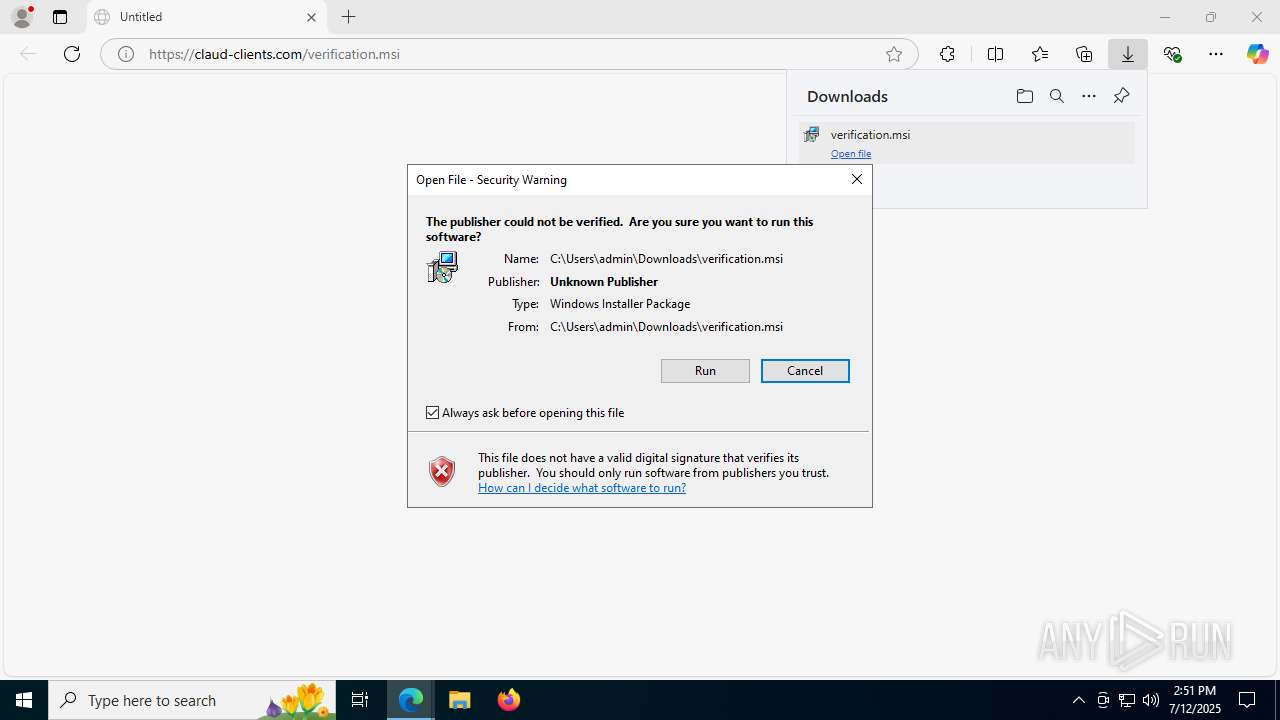
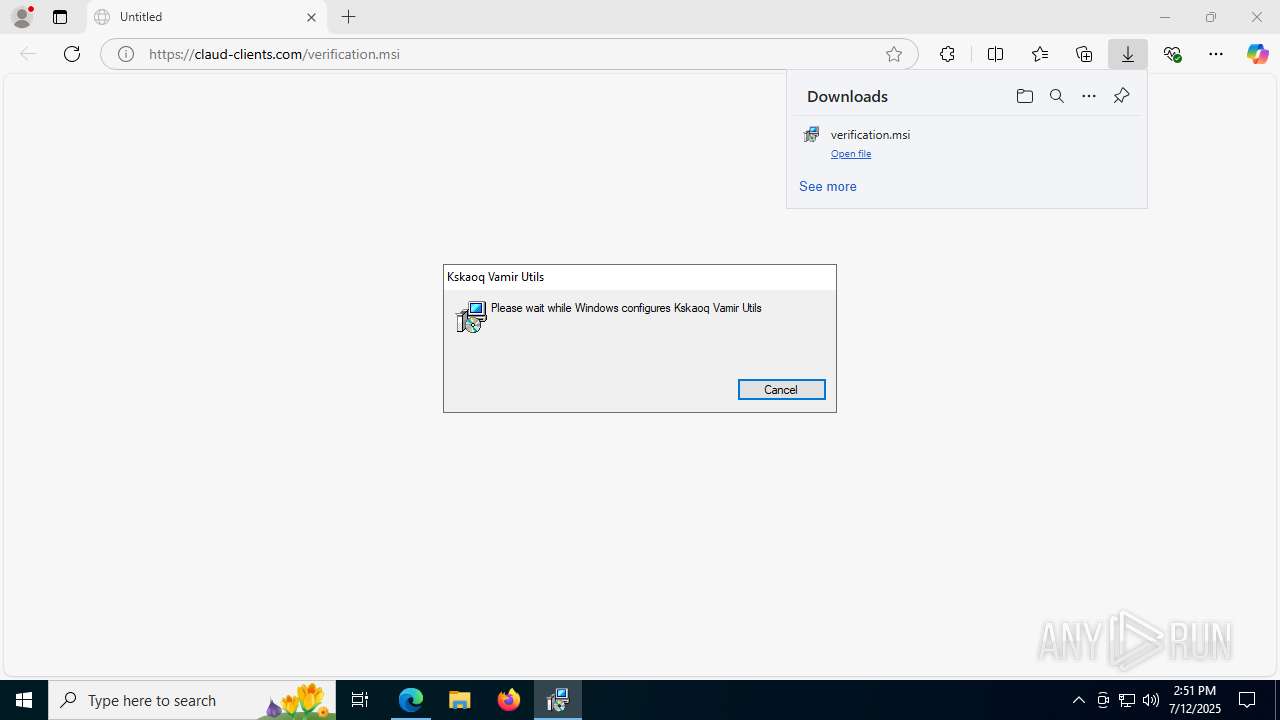
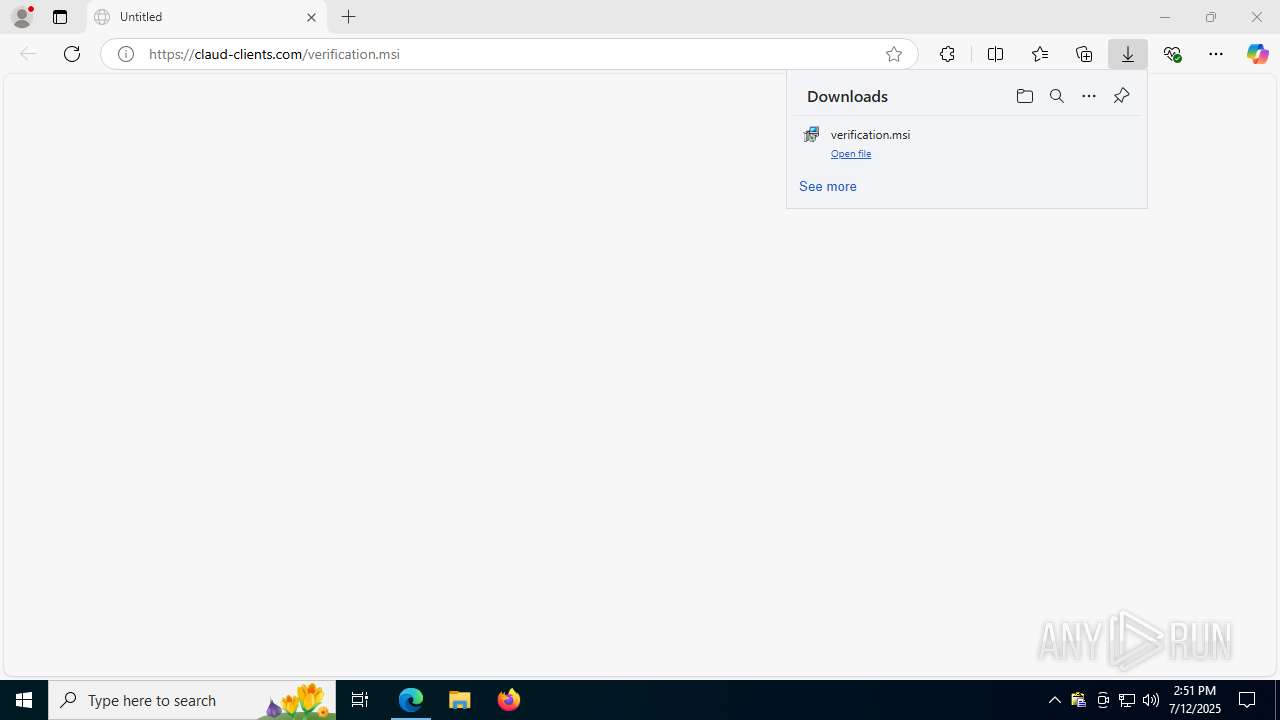
| URL: | https://claud-clients.com/verification.msi |
| Full analysis: | https://app.any.run/tasks/96285499-a08b-4bd9-8816-07b15d8e711f |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | July 12, 2025, 14:51:22 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | A1BB3D8C08233686F6FFC476F8A8BC29 |
| SHA1: | C8D2AE39C959A72F36AA502C074F2E07A1DC2277 |
| SHA256: | F709D35E070A1B74F9465149226EDF3DEBBCE18C544E3CFCA28CAF82A82E20BB |
| SSDEEP: | 3:N8UgGBMKKTfDHas:2UgGOl |
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 7652)
LUMMA has been detected (SURICATA)
- explorer.exe (PID: 7904)
- svchost.exe (PID: 2200)
Connects to the CnC server
- svchost.exe (PID: 2200)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 7652)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 7652)
Actions looks like stealing of personal data
- powershell.exe (PID: 7652)
Steals credentials from Web Browsers
- powershell.exe (PID: 7652)
SUSPICIOUS
Reads the Windows owner or organization settings
- msiexec.exe (PID: 8024)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 8080)
The process drops C-runtime libraries
- msiexec.exe (PID: 8024)
- 7z.exe (PID: 7760)
Process drops legitimate windows executable
- msiexec.exe (PID: 8024)
- 7z.exe (PID: 7760)
The process creates files with name similar to system file names
- msiexec.exe (PID: 8024)
Drops 7-zip archiver for unpacking
- msiexec.exe (PID: 8024)
Executing commands from a ".bat" file
- msiexec.exe (PID: 8024)
The executable file from the user directory is run by the CMD process
- 7z.exe (PID: 7760)
Starts CMD.EXE for commands execution
- msiexec.exe (PID: 8024)
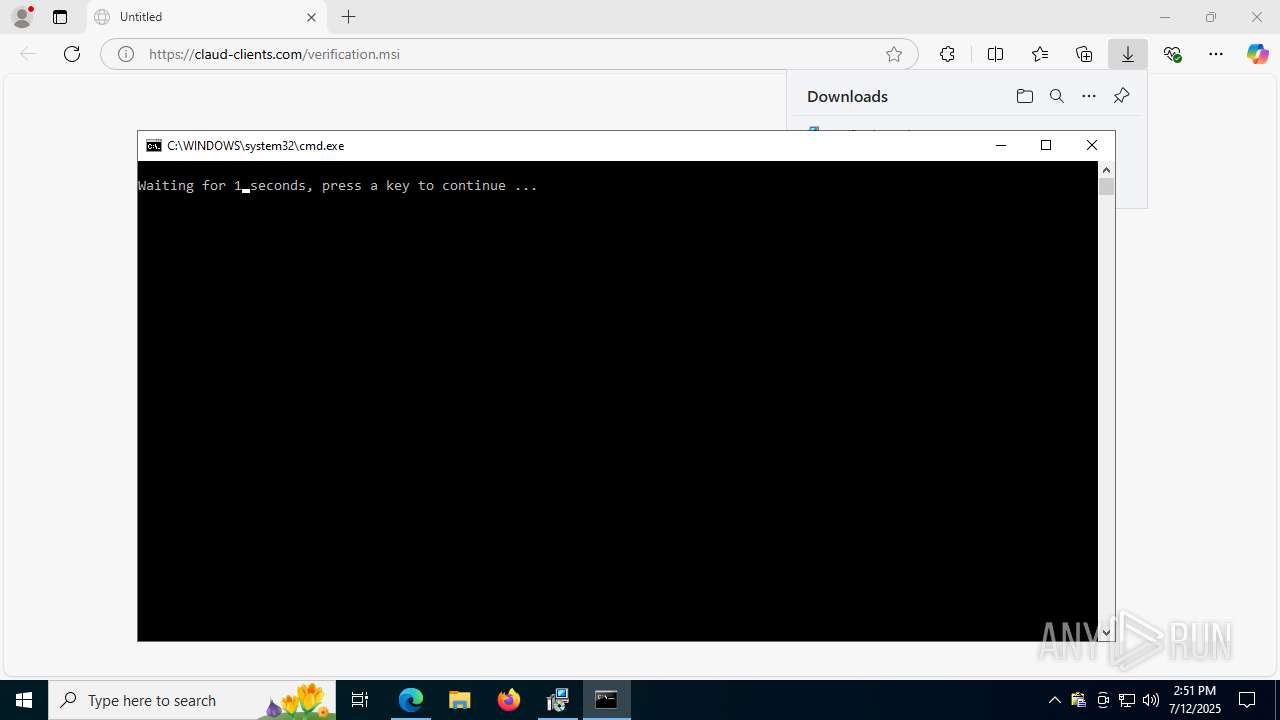
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 4844)
Executable content was dropped or overwritten
- 7z.exe (PID: 7760)
Starts POWERSHELL.EXE for commands execution
- explorer.exe (PID: 7904)
Base64-obfuscated command line is found
- explorer.exe (PID: 7904)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- explorer.exe (PID: 7904)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2200)
- explorer.exe (PID: 7904)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7652)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 7652)
Converts a string into array of characters (POWERSHELL)
- powershell.exe (PID: 7652)
Converts a specified value to an integer (POWERSHELL)
- powershell.exe (PID: 7652)
There is functionality for taking screenshot (YARA)
- clipx.exe (PID: 2320)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 7652)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 7652)
Converts a specified value to a byte (POWERSHELL)
- powershell.exe (PID: 7652)
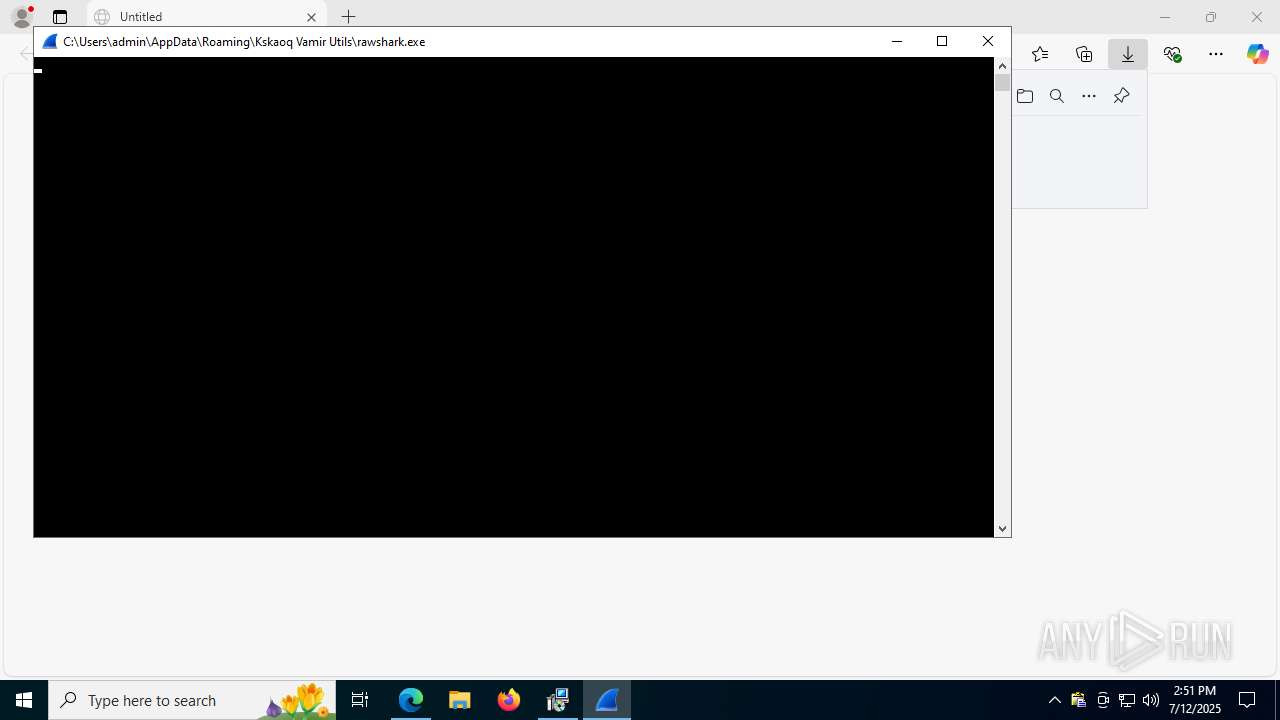
Executes application which crashes
- rawshark.exe (PID: 7892)
BASE64 encoded PowerShell command has been detected
- explorer.exe (PID: 7904)
INFO
Application launched itself
- msedge.exe (PID: 2972)
- msedge.exe (PID: 2648)
Reads Environment values
- identity_helper.exe (PID: 7412)
- msiexec.exe (PID: 8080)
- identity_helper.exe (PID: 7116)
Reads the computer name
- msiexec.exe (PID: 8024)
- identity_helper.exe (PID: 7412)
- msiexec.exe (PID: 8080)
- clipx.exe (PID: 2320)
- 7z.exe (PID: 7760)
- identity_helper.exe (PID: 7116)
Checks supported languages
- identity_helper.exe (PID: 7412)
- msiexec.exe (PID: 8024)
- msiexec.exe (PID: 8080)
- clipx.exe (PID: 2320)
- 7z.exe (PID: 7760)
- rawshark.exe (PID: 7892)
- identity_helper.exe (PID: 7116)
Create files in a temporary directory
- msiexec.exe (PID: 7988)
- explorer.exe (PID: 7904)
- rawshark.exe (PID: 7892)
Reads Microsoft Office registry keys
- msedge.exe (PID: 2972)
Executable content was dropped or overwritten
- msiexec.exe (PID: 8024)
The sample compiled with english language support
- msiexec.exe (PID: 8024)
- 7z.exe (PID: 7760)
Checks proxy server information
- msiexec.exe (PID: 8080)
- explorer.exe (PID: 7904)
- powershell.exe (PID: 7652)
Reads the machine GUID from the registry
- msiexec.exe (PID: 8080)
Reads the software policy settings
- msiexec.exe (PID: 8080)
- explorer.exe (PID: 7904)
Creates files or folders in the user directory
- msiexec.exe (PID: 8080)
- msiexec.exe (PID: 8024)
- clipx.exe (PID: 2320)
- 7z.exe (PID: 7760)
- explorer.exe (PID: 7904)
Creates a software uninstall entry
- msiexec.exe (PID: 8024)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 7652)
Reads security settings of Internet Explorer
- explorer.exe (PID: 7904)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 7652)
Disables trace logs
- powershell.exe (PID: 7652)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 7652)
Gets data length (POWERSHELL)
- powershell.exe (PID: 7652)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 7652)
UPX packer has been detected
- clipx.exe (PID: 2320)
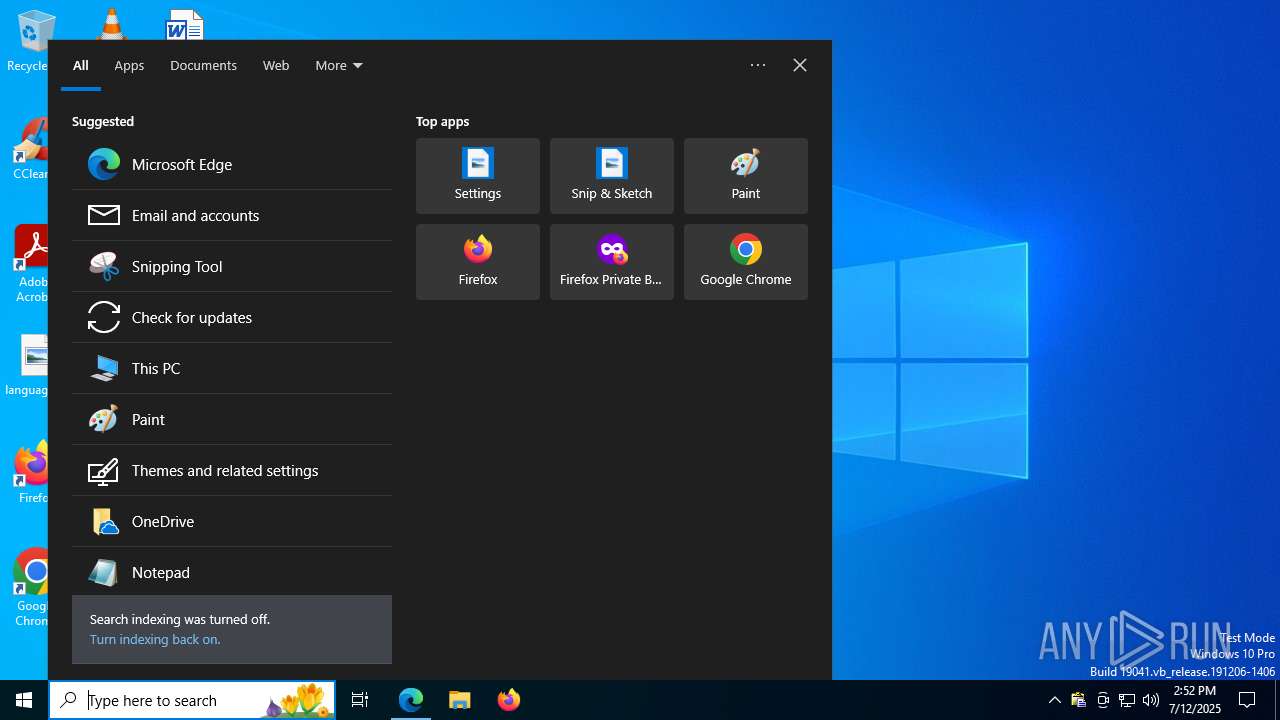
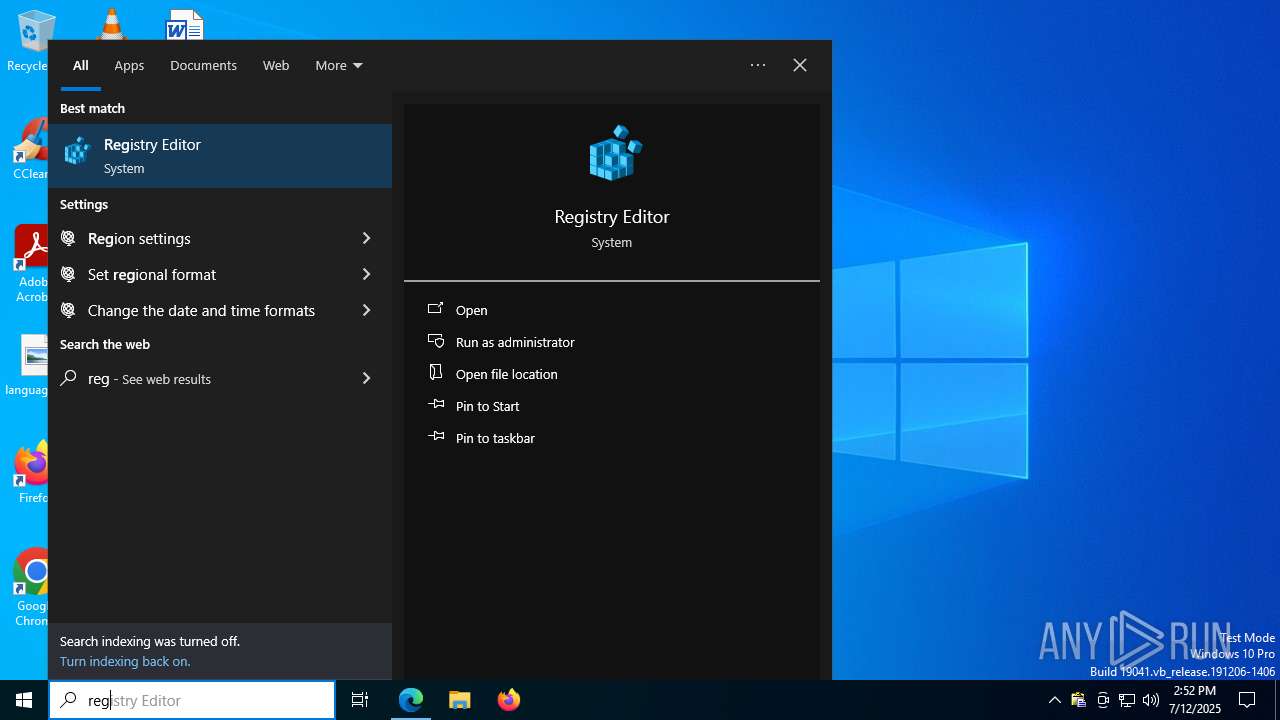
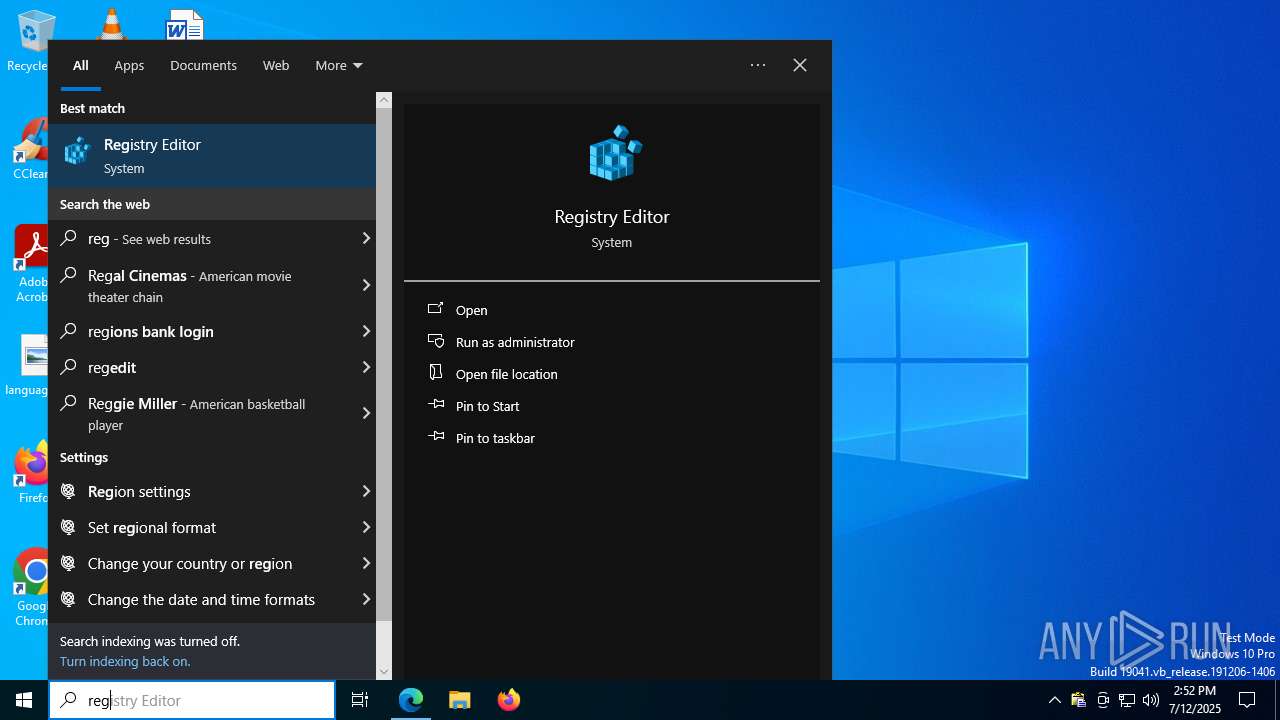
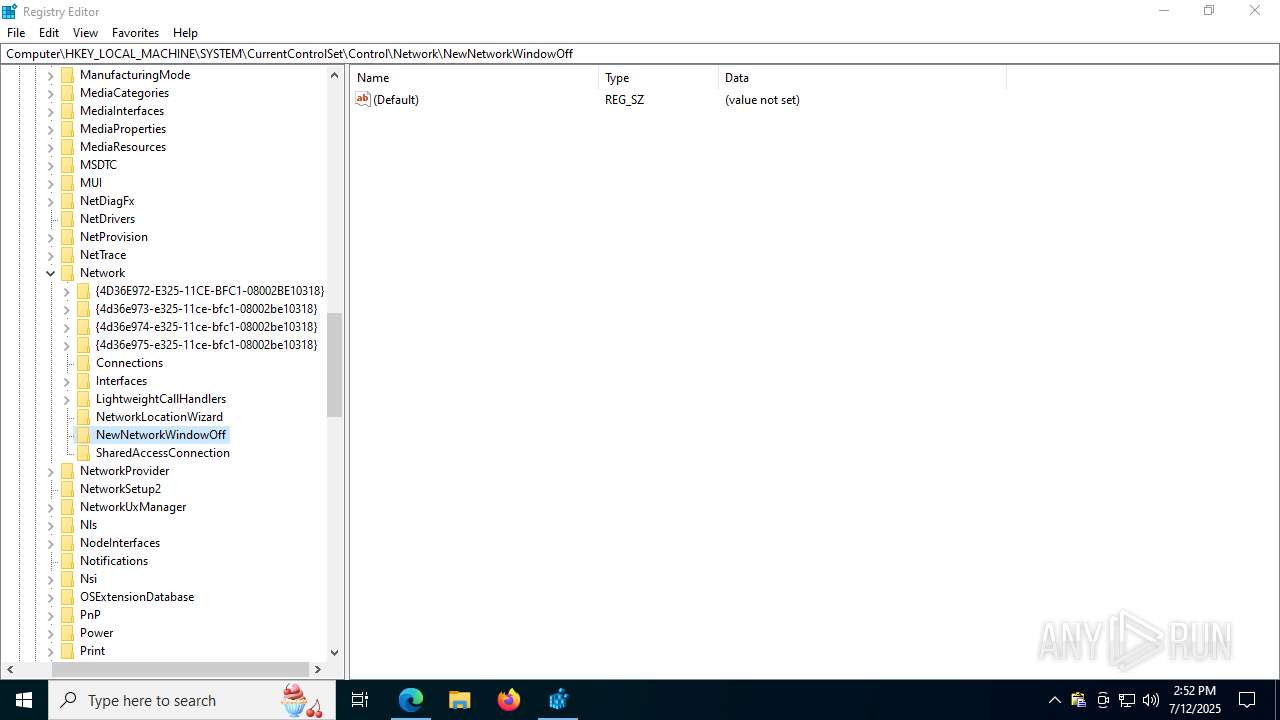
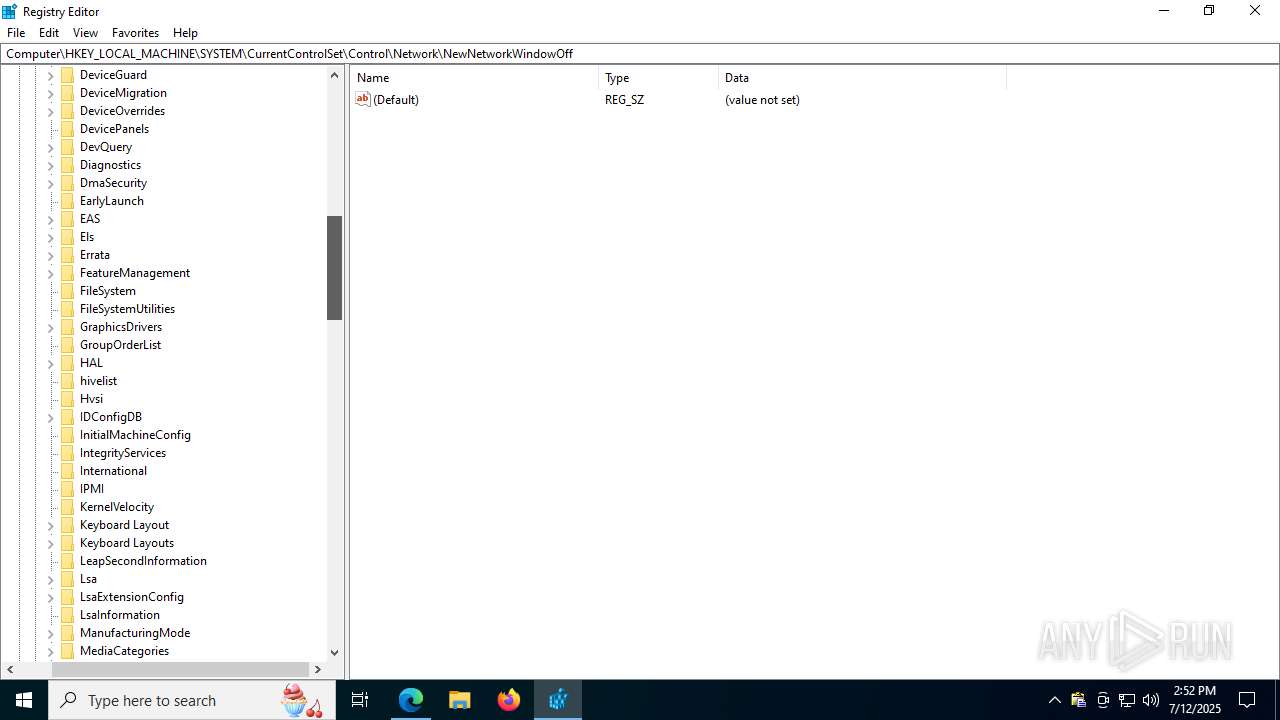
Manual execution by a user
- regedit.exe (PID: 856)
- regedit.exe (PID: 6764)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
195
Monitored processes
51
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 856 | "C:\WINDOWS\regedit.exe" | C:\Windows\regedit.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Editor Exit code: 3221226540 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 864 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2204,i,14021217770605319269,5206057598802082677,262144 --variations-seed-version --mojo-platform-channel-handle=2572 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 4294967295 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1156 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --disable-quic --onnx-enabled-for-ee --string-annotations --always-read-main-dll --field-trial-handle=4040,i,14021217770605319269,5206057598802082677,262144 --variations-seed-version --mojo-platform-channel-handle=5128 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 4294967295 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1164 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=4432,i,14021217770605319269,5206057598802082677,262144 --variations-seed-version --mojo-platform-channel-handle=4456 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 4294967295 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1392 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4024,i,14021217770605319269,5206057598802082677,262144 --variations-seed-version --mojo-platform-channel-handle=4072 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 4294967295 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1520 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2792,i,14021217770605319269,5206057598802082677,262144 --variations-seed-version --mojo-platform-channel-handle=2772 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 4294967295 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1800 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --disable-quic --onnx-enabled-for-ee --string-annotations --always-read-main-dll --field-trial-handle=6020,i,5646790360464747008,7975754701800210229,262144 --variations-seed-version --mojo-platform-channel-handle=5960 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=4448,i,14021217770605319269,5206057598802082677,262144 --variations-seed-version --mojo-platform-channel-handle=3316 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 4294967295 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2200 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2320 | "C:\Users\admin\AppData\Roaming\Kskaoq Vamir Utils\clipx.exe" | C:\Users\admin\AppData\Roaming\Kskaoq Vamir Utils\clipx.exe | msiexec.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
Total events
22 361
Read events
22 110
Write events
242
Delete events
9
Modification events
| (PID) Process: | (2972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2972) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 235356D852982F00 | |||
| (PID) Process: | (2972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\721710 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {93DB3F61-8356-4F45-9933-16B54E46BB6B} | |||
| (PID) Process: | (2972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\721710 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {2BC17B0C-3FC2-477C-8050-6FC251B7A80C} | |||
| (PID) Process: | (2972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
| (PID) Process: | (2972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
| (PID) Process: | (2972) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: E81469D852982F00 | |||
Executable files
156
Suspicious files
598
Text files
180
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF17569c.TMP | — | |
MD5:— | SHA256:— | |||
| 2972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF17569c.TMP | — | |
MD5:— | SHA256:— | |||
| 2972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1756bb.TMP | — | |
MD5:— | SHA256:— | |||
| 2972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1756ca.TMP | — | |
MD5:— | SHA256:— | |||
| 2972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1756da.TMP | — | |
MD5:— | SHA256:— | |||
| 2972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
138
DNS requests
117
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
864 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:EFy1F7iM9Nz99CQxlTuXF-PnDkgQ36t70rxqNG_rSh4&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.16.241.14:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2464 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8080 | msiexec.exe | GET | 200 | 104.18.20.213:80 | http://r10.c.lencr.org/21.crl | unknown | — | — | whitelisted |
7904 | explorer.exe | GET | 200 | 169.150.247.36:80 | http://xiyanqiu.com/front.php?a=TAbyc6jIHIVFiPx&id=0 | unknown | — | — | unknown |
7904 | explorer.exe | GET | 200 | 169.150.247.36:80 | http://xiyanqiu.com/back.php?a=xjWtphu6sSKAi5ZOo2eNGQSCrdG9Ej%2FJUKfAVNvGbuZeo%2BbFwcjI%2FgWwaCWT8WcdAOeFEkh89F%2B7kP1g%2By7IiChe1AHr5qw3yoxw0neKfuYbQoEkHlYDl1MwdjzPYw%3D%3D | unknown | — | — | unknown |
7904 | explorer.exe | GET | 301 | 104.21.40.121:80 | http://torchwarp-back.com/click?cnv_id=d1p22e2antdc73bovqig&value=1 | unknown | — | — | unknown |
7904 | explorer.exe | GET | 200 | 142.250.186.67:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
7904 | explorer.exe | GET | 200 | 142.250.186.67:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2148 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
864 | msedge.exe | 188.114.97.3:443 | claud-clients.com | CLOUDFLARENET | NL | unknown |
864 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
864 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
864 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
864 | msedge.exe | 2.16.241.224:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
claud-clients.com |
| unknown |
copilot.microsoft.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
www.bing.com |
| whitelisted |
edgeassetservice.azureedge.net |
| whitelisted |
www.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2200 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
7904 | explorer.exe | Misc activity | ET INFO Observed Telegram Domain (t .me in TLS SNI) |
7904 | explorer.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 30 |
2200 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (lnofi .xyz) |
7904 | explorer.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (lnofi .xyz in TLS SNI) |
7904 | explorer.exe | Not Suspicious Traffic | ET INFO OpenSSL Demo CA - Internet Widgits Pty (O) |
2200 | svchost.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Suspected Domain Associated with Malware Distribution (shoshanameltzer .com) |
7824 | msedge.exe | Potentially Bad Traffic | ET INFO Observed Blockchain Domain (api .blockcypher .com in TLS SNI) |
7824 | msedge.exe | Potentially Bad Traffic | ET INFO Observed Blockchain Domain (api .blockcypher .com in TLS SNI) |
Process | Message |
|---|---|
clipx.exe | >>>
|
clipx.exe | >>>
|
clipx.exe | >
|
clipx.exe | >
|
clipx.exe | Auto-initializing 0 services (system pass)
|
clipx.exe | Auto-initializing 2 services (user pass)
|
rawshark.exe | sadjiogasjoi aio aoj io |
rawshark.exe | 4748f672d4a3a88718e980646c3a67f7b50d6e675a3e7d2310f36ca77a901efc |
rawshark.exe | mutex: sjvsoies_PHQGHUME
|