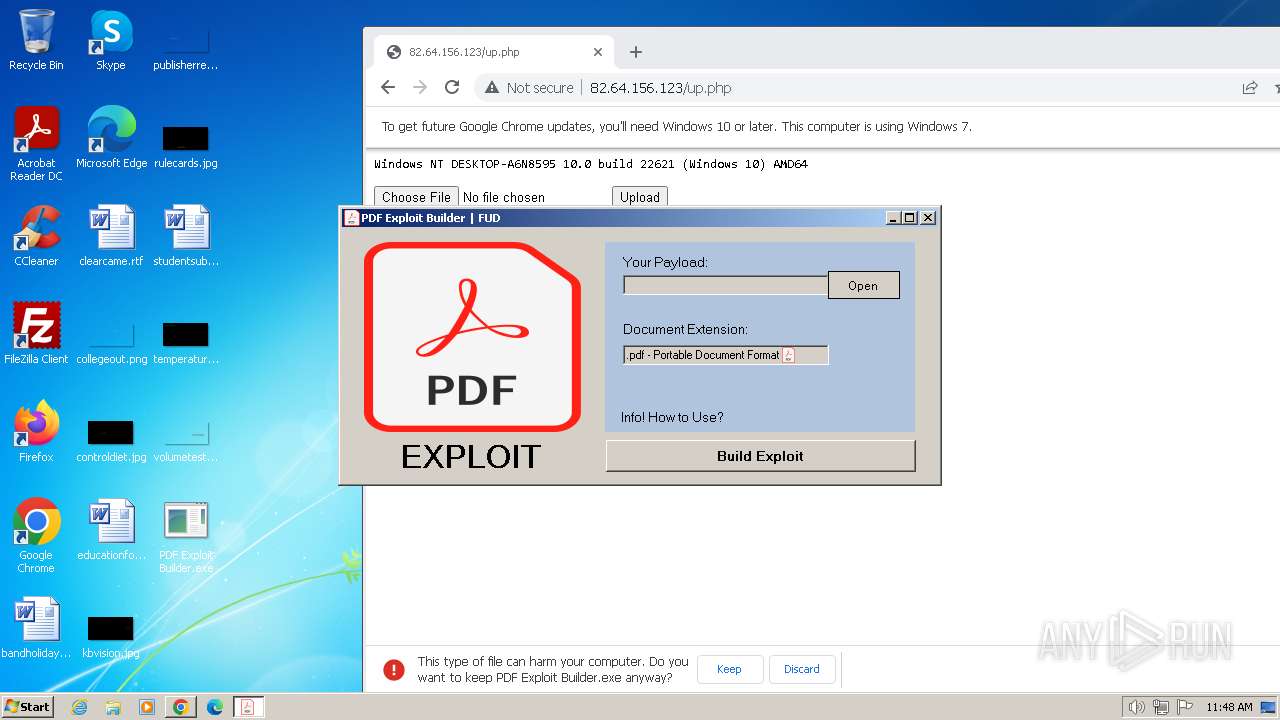
| File name: | PDF Exploit Builder.exe |
| Full analysis: | https://app.any.run/tasks/c19f6854-3163-4855-ad6f-9f002051ac65 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | February 07, 2024, 11:47:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | E5D09531399E6D140F0F069F46B9800C |
| SHA1: | FAD965D7531C419F5F19C77632F9D661E7B18A8F |
| SHA256: | F6ECE697E5C1D77382C738BFFF4EB6FF7FA4AFAEF95E42557EABEF5C6E75D79A |
| SSDEEP: | 6144:+en08JTPixztvLLDbLMRtGUv1+9OtKzJQn59:+en08JT6xztvLLLetGUt+9OtK+nT |
MALICIOUS
ASYNCRAT has been detected (MUTEX)
- Naqebawbhht.exe (PID: 2752)
- update.exe (PID: 3500)
Drops the executable file immediately after the start
- PDF Exploit Builder.exe (PID: 3732)
- chrome.exe (PID: 572)
- Naqebawbhht.exe (PID: 2752)
ASYNCRAT has been detected (YARA)
- update.exe (PID: 3500)
SUSPICIOUS
Executable content was dropped or overwritten
- PDF Exploit Builder.exe (PID: 3732)
- Naqebawbhht.exe (PID: 2752)
Reads the Internet Settings
- PDF Exploit Builder.exe (PID: 3732)
Starts CMD.EXE for commands execution
- Naqebawbhht.exe (PID: 2752)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 2304)
The executable file from the user directory is run by the CMD process
- update.exe (PID: 3500)
Connects to unusual port
- update.exe (PID: 3500)
Executing commands from a ".bat" file
- Naqebawbhht.exe (PID: 2752)
INFO
Reads the machine GUID from the registry
- Naqebawbhht.exe (PID: 2752)
- Crhz.exe (PID: 2848)
- PDF Exploit Builder.exe (PID: 3732)
- update.exe (PID: 3500)
Reads the computer name
- Crhz.exe (PID: 2848)
- Naqebawbhht.exe (PID: 2752)
- PDF Exploit Builder.exe (PID: 3732)
- update.exe (PID: 3500)
Checks supported languages
- Naqebawbhht.exe (PID: 2752)
- PDF Exploit Builder.exe (PID: 3732)
- Crhz.exe (PID: 2848)
- update.exe (PID: 3500)
Create files in a temporary directory
- PDF Exploit Builder.exe (PID: 3732)
- Naqebawbhht.exe (PID: 2752)
Executable content was dropped or overwritten
- chrome.exe (PID: 572)
Application launched itself
- chrome.exe (PID: 572)
Manual execution by a user
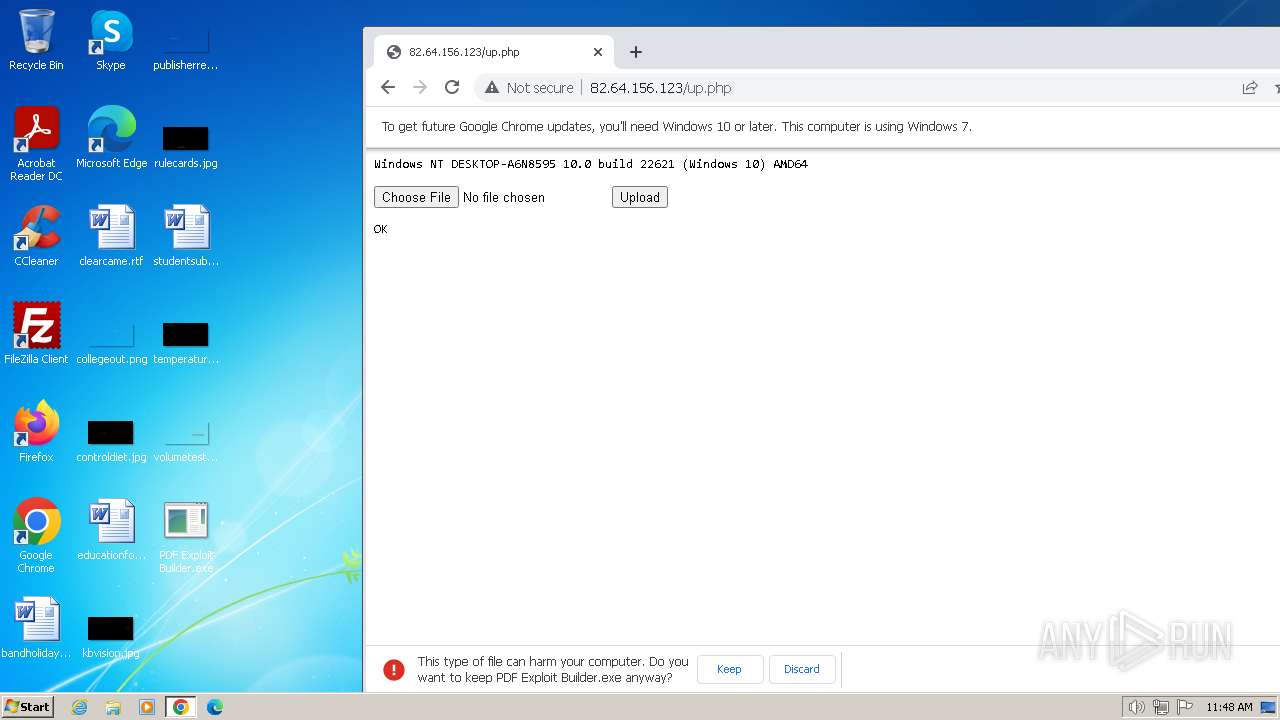
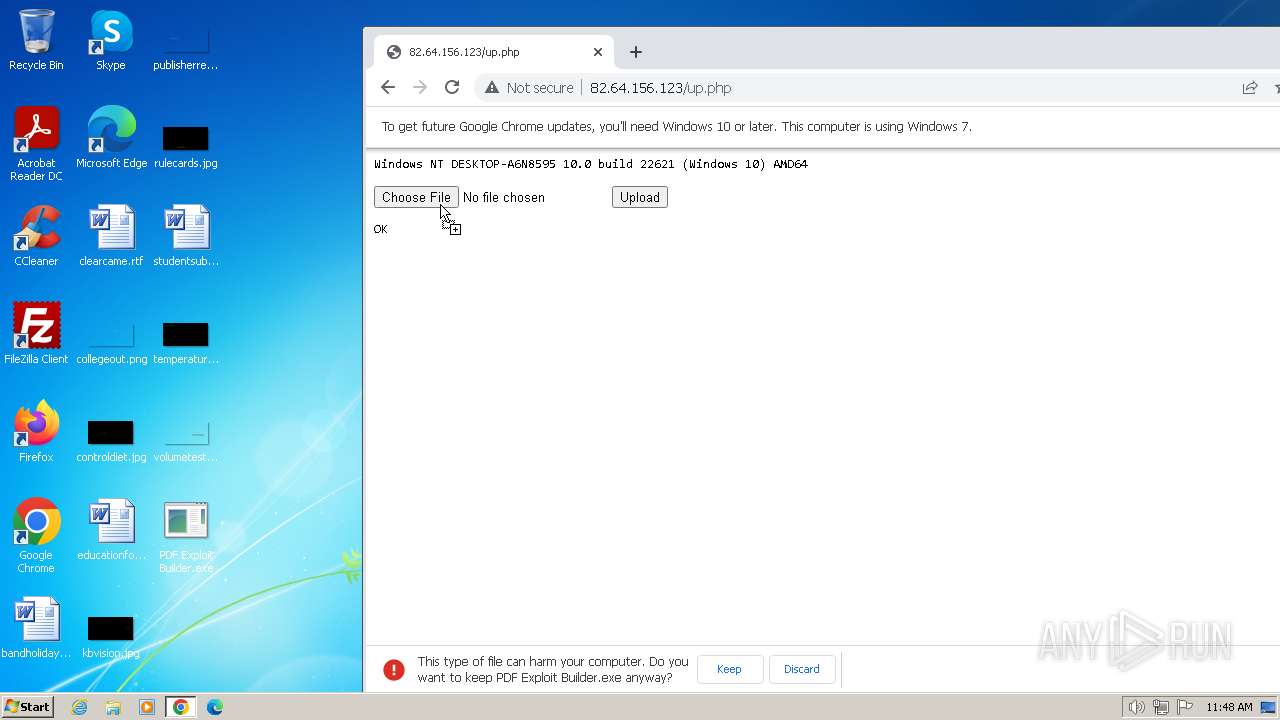
- PDF Exploit Builder.exe (PID: 3732)
Creates files or folders in the user directory
- Naqebawbhht.exe (PID: 2752)
The process uses the downloaded file
- chrome.exe (PID: 2856)
- chrome.exe (PID: 2064)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AsyncRat
(PID) Process(3500) update.exe
C2 (1)23.105.131.227
Ports (1)1111
BotnetDefault
Version0.5.7B
Options
AutoRuntrue
MutexAsyncMutex_6SI8OkPnk
InstallFolder%AppData%
BSoDfalse
AntiVMfalse
Certificates
Cert1MIIE8jCCAtqgAwIBAgIQAP/IribDFmgsbzOMMEuQmTANBgkqhkiG9w0BAQ0FADAaMRgwFgYDVQQDDA9Bc3luY1JBVCBTZXJ2ZXIwIBcNMjEwMjA4MTQ1OTQ0WhgPOTk5OTEyMzEyMzU5NTlaMBoxGDAWBgNVBAMMD0FzeW5jUkFUIFNlcnZlcjCCAiIwDQYJKoZIhvcNAQEBBQADggIPADCCAgoCggIBAOkzyuGp240ovE1TRi57wKIyYwNLRpJr4lXEiTQz3lRTk5FbhnsqndtmWTWR1W4BLZXbT7o+kFkd...
Server_SignaturepMEfbWaSL8FKy0p72vykWP+6OVwId9VsjWQaMsmyr2rf/d4LS+/lyupiZWZWbOUBXEYzVXd6zryA9Hjs7KvdQAta3v1oUX2mdADfRinCcWGADatQCFYba32FtJeGzuW9dAXJhEqALpg/LVzYPTDQGURHw+ErB5dP5O9K1PPGeXCXwzC8aunA3Vi24Xt5q1yS08AhApgi24oqYar7VF33p0Nr5XzYeKs4HXi7+PM4FOP4ULT/SOsWaaLfgtgEUb/Iqgx4gXAx3DAbBexAr/SMSOsJ7ijQqiwho5czRp6OcuJI...
Keys
AES6c72fef5c5f41f1dc1a4d81ae0708bdd95f98f04b7059696d412ed28fdaf7c86
Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:02:24 19:22:07+01:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 199680 |
| InitializedDataSize: | 201216 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x32b5a |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 0.0.0.0 |
| InternalName: | PDF Exploit Builder (1).exe |
| LegalCopyright: | |
| OriginalFileName: | PDF Exploit Builder (1).exe |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
59
Monitored processes
21
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=3156 --field-trial-handle=1228,i,2716092218637035450,371262528521185284,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
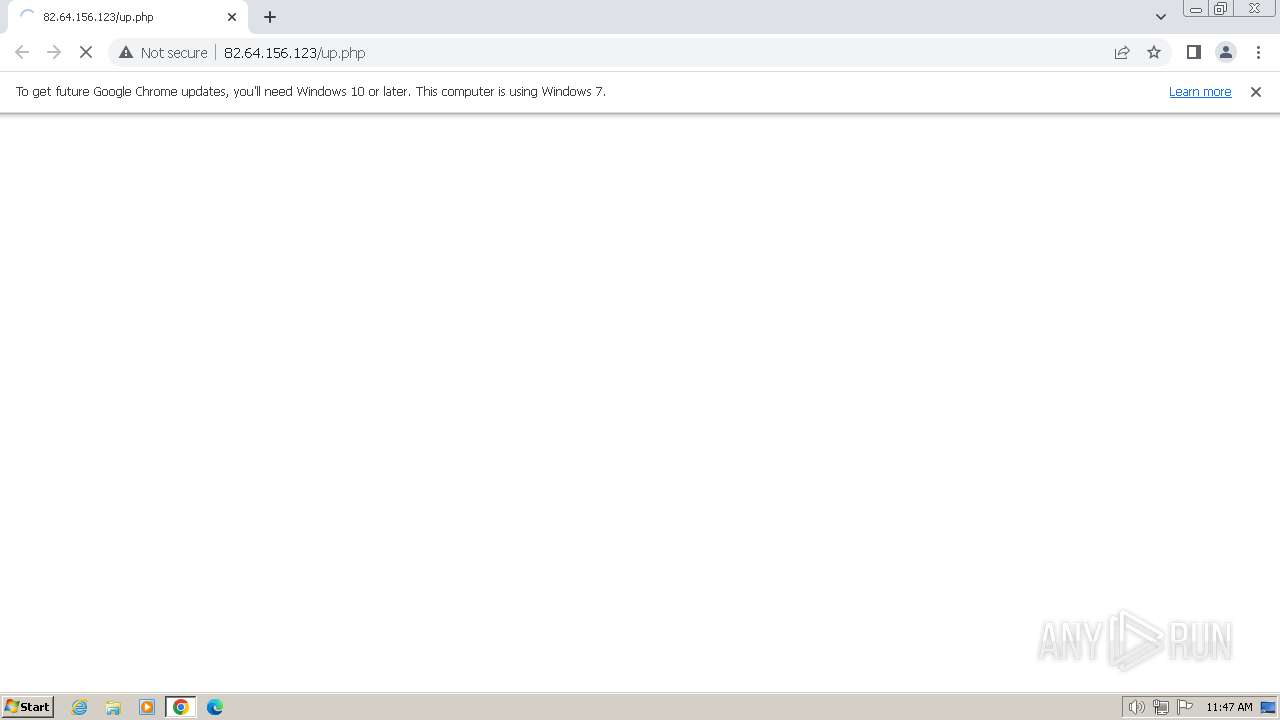
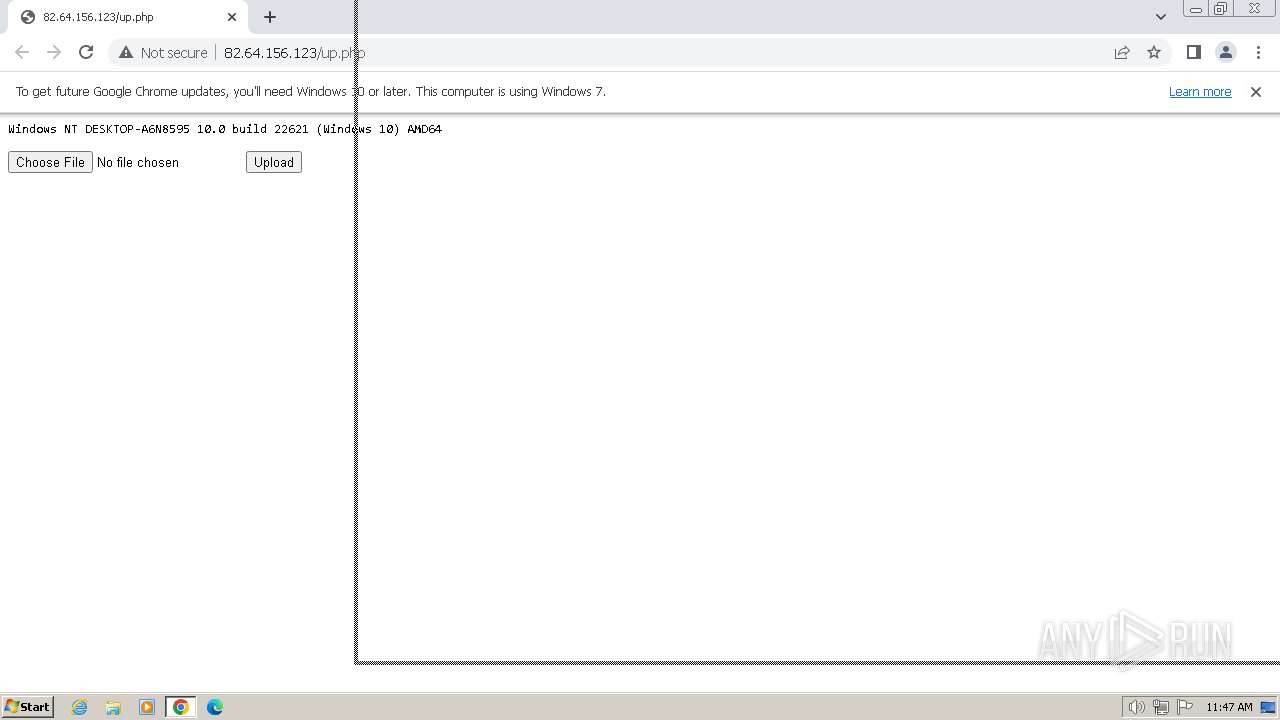
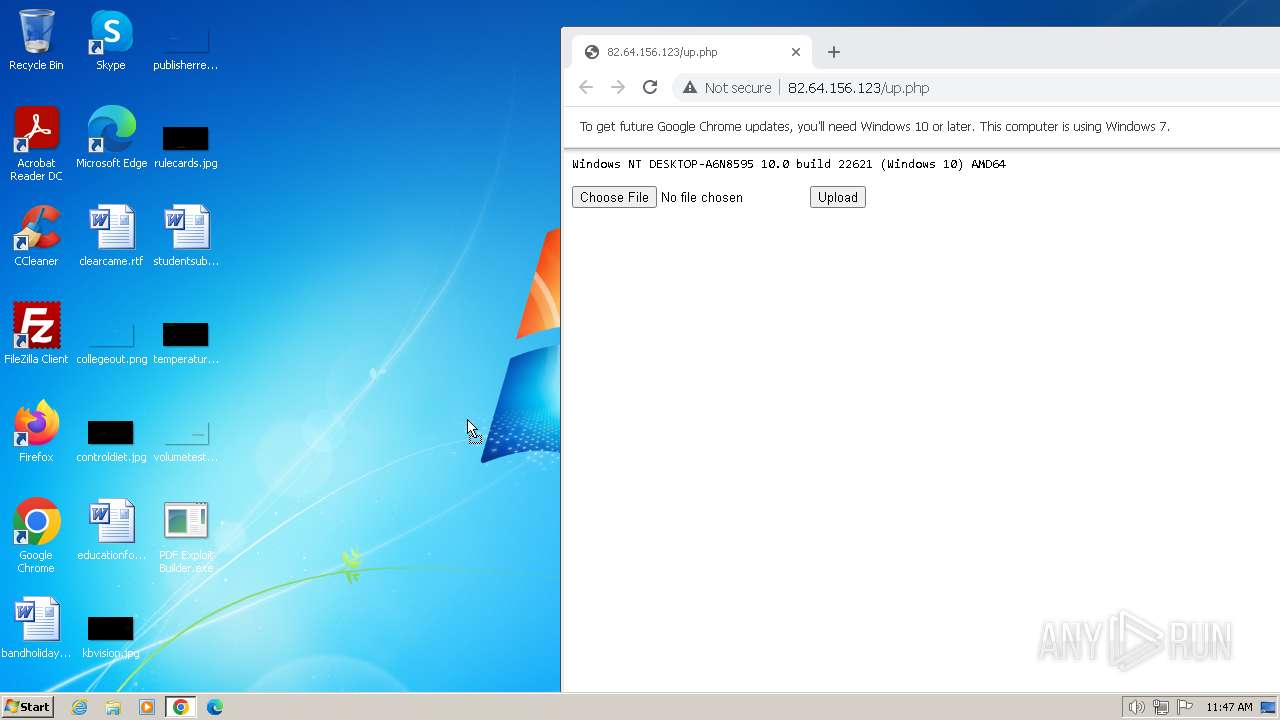
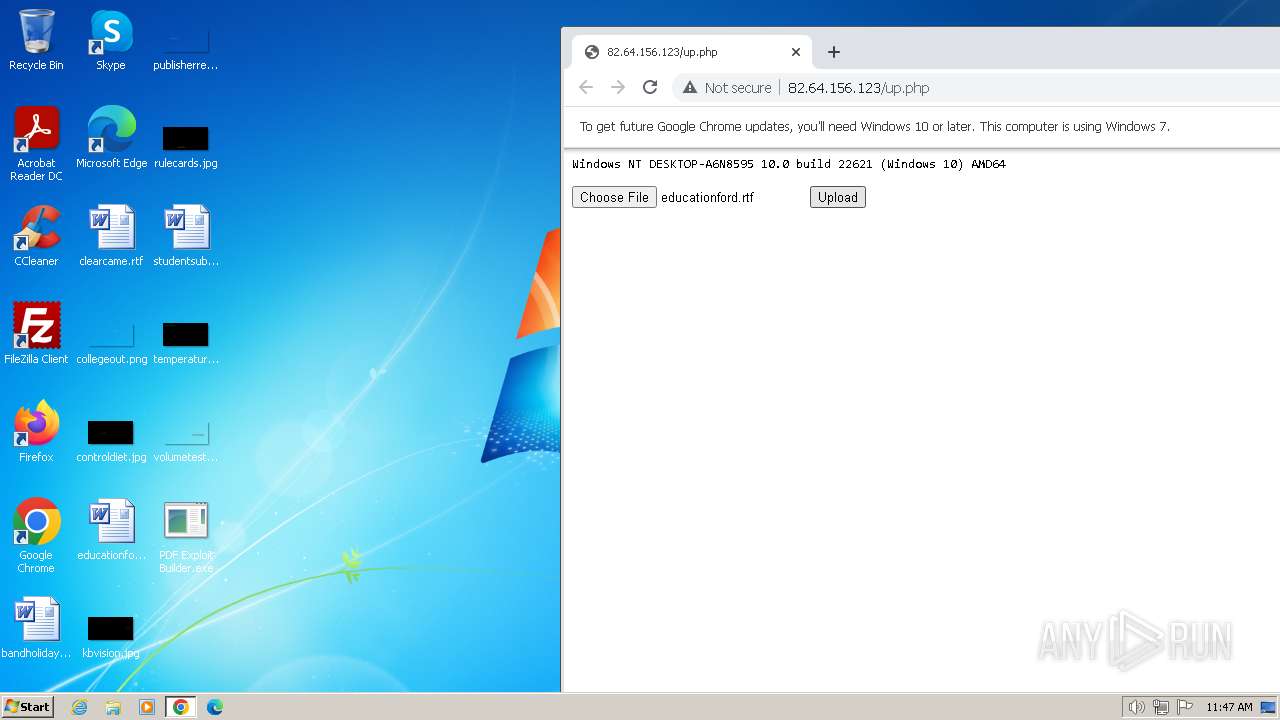
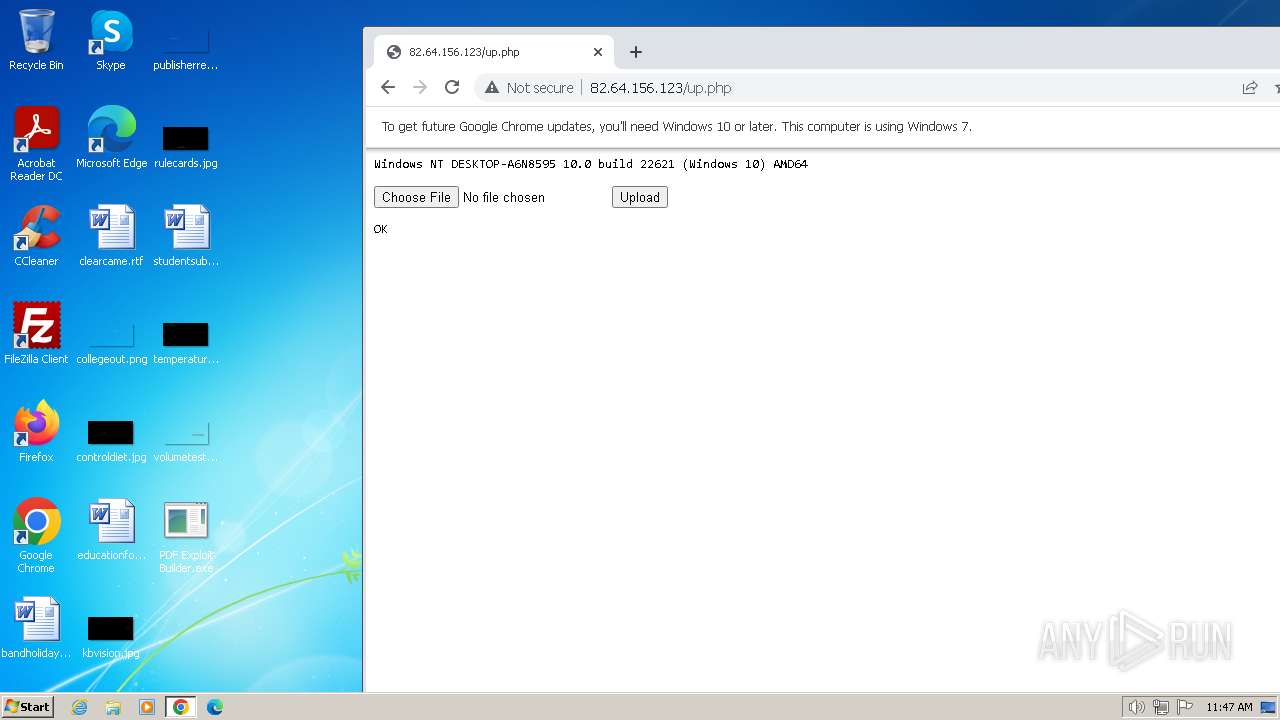
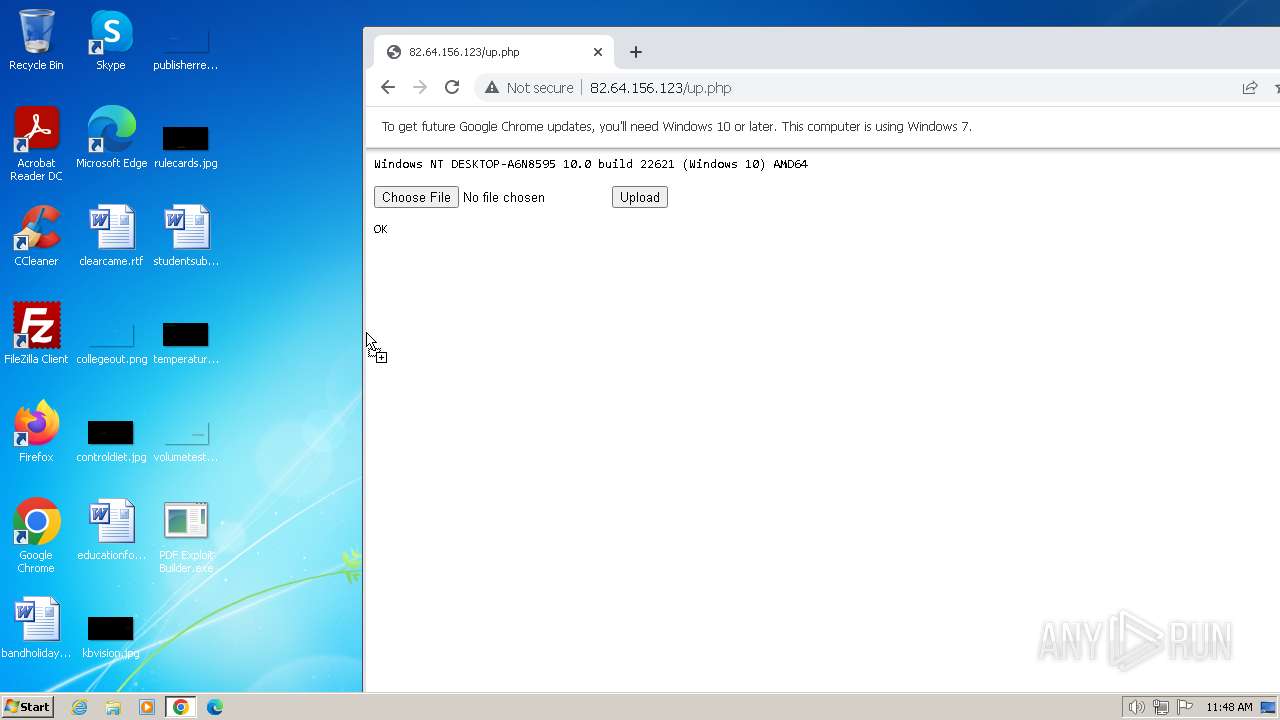
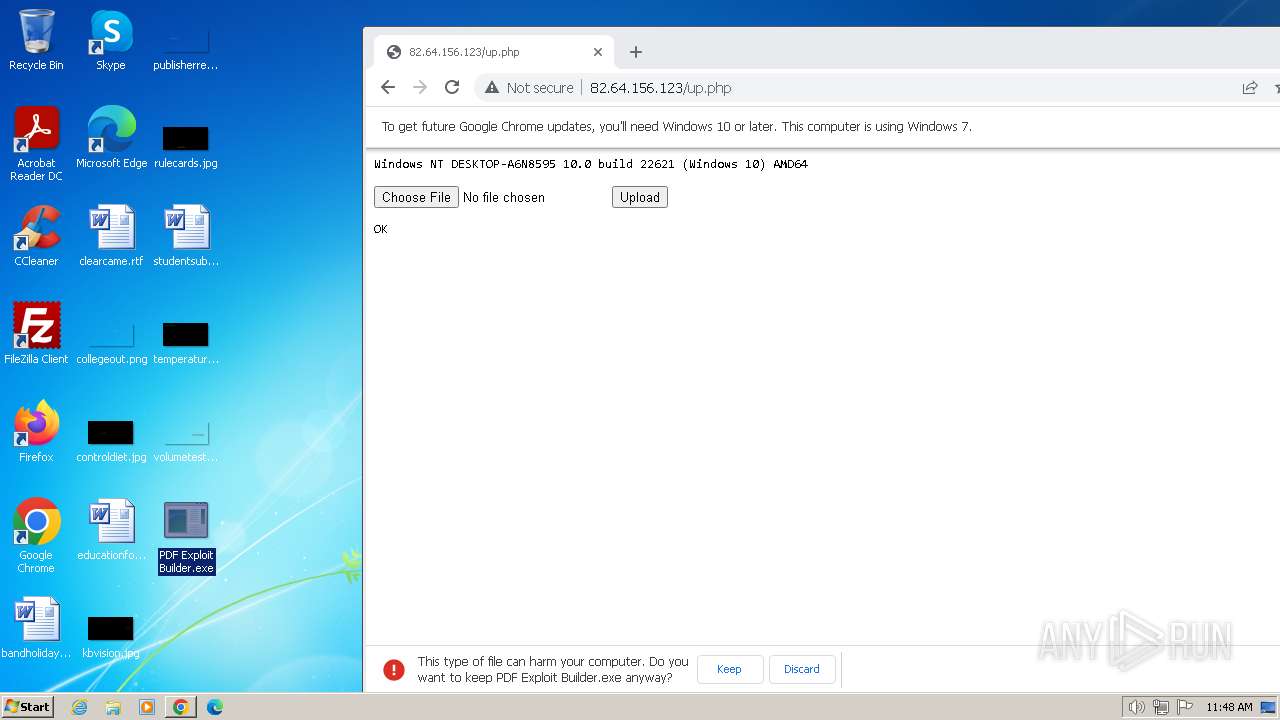
| 572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://82.64.156.123/up.php | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1380 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6bcd8b38,0x6bcd8b48,0x6bcd8b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1156 --field-trial-handle=1228,i,2716092218637035450,371262528521185284,131072 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3736 --field-trial-handle=1228,i,2716092218637035450,371262528521185284,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2304 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\tmpAD4C.tmp.bat"" | C:\Windows\System32\cmd.exe | — | Naqebawbhht.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2476 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3368 --field-trial-handle=1228,i,2716092218637035450,371262528521185284,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2524 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --mojo-platform-channel-handle=3276 --field-trial-handle=1228,i,2716092218637035450,371262528521185284,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2752 | "C:\Users\admin\AppData\Local\Temp\Naqebawbhht.exe" | C:\Users\admin\AppData\Local\Temp\Naqebawbhht.exe | PDF Exploit Builder.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 2848 | "C:\Users\admin\AppData\Local\Temp\Crhz.exe" | C:\Users\admin\AppData\Local\Temp\Crhz.exe | — | PDF Exploit Builder.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: PDF Exploit Builder Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
4 962
Read events
4 863
Write events
99
Delete events
0
Modification events
| (PID) Process: | (572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (572) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
5
Suspicious files
37
Text files
22
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF163b87.TMP | — | |
MD5:— | SHA256:— | |||
| 572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF163daa.TMP | — | |
MD5:— | SHA256:— | |||
| 572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF163b87.TMP | text | |
MD5:05CF4C3C5148DA6355D3561A9EAA5E8A | SHA256:8D720243F6876898E4F197C8867C4CEE69F1C7335C55B8A29C120B1028D93E41 | |||
| 572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF163b87.TMP | text | |
MD5:ADB669AB4CD1C63883C64FB0DBA2C7DA | SHA256:18BFF89047EC5B122573D089B3DC7A7DD14A5A7A515B2D8141584B41E723253F | |||
| 572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:ECD3386BCC950E73B86EB128A5F57622 | SHA256:C9A068EAFBC587EDFC89392F64DDD350EEB96C5CF195CDB030BAB8F6DD33833B | |||
| 572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:358570F689377CE6838812643E03734B | SHA256:5B41FCC2E1A843AEAB9437B06E27B798870FF10D86A51B163BF48862BCD32590 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
17
DNS requests
12
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3416 | chrome.exe | GET | 200 | 82.64.156.123:80 | http://82.64.156.123/up.php | FR | text | 204 b | unknown |
3416 | chrome.exe | POST | 200 | 82.64.156.123:80 | http://82.64.156.123/up.php | FR | text | 206 b | unknown |
3416 | chrome.exe | POST | 200 | 82.64.156.123:80 | http://82.64.156.123/up.php | FR | text | 206 b | unknown |
3416 | chrome.exe | GET | 404 | 82.64.156.123:80 | http://82.64.156.123/favicon.ico | FR | html | 299 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
572 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
3416 | chrome.exe | 82.64.156.123:80 | — | Free SAS | FR | malicious |
3416 | chrome.exe | 74.125.71.84:443 | accounts.google.com | GOOGLE | US | unknown |
3416 | chrome.exe | 142.250.186.163:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
572 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
3416 | chrome.exe | 142.250.186.67:443 | update.googleapis.com | GOOGLE | US | whitelisted |
3416 | chrome.exe | 172.217.18.4:443 | www.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
update.googleapis.com |
| whitelisted |
www.google.com |
| whitelisted |
optimizationguide-pa.googleapis.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3416 | chrome.exe | Misc activity | ET INFO Generic HTTP EXE Upload Outbound |