| File name: | Mal%20Files.zip |
| Full analysis: | https://app.any.run/tasks/932e2745-7c22-4078-969b-9874affdf732 |
| Verdict: | Malicious activity |
| Threats: | LokiBot was developed in 2015 to steal information from a variety of applications. Despite the age, this malware is still rather popular among cybercriminals. |
| Analysis date: | June 18, 2019, 17:32:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | D7F122639CD5BF1FD34D04970EDA3555 |
| SHA1: | 73C5E18B73FCD336DB48F2027CAD88089A5A3C91 |
| SHA256: | F6D3043828A85E68CABF9700B347C2A137BAC5865BD3D6D88151A2B3C454CA25 |
| SSDEEP: | 24576:Q44NAMqgYWyURTSFbqS5N3QeMBc661jCDT:74N9humqAylq |
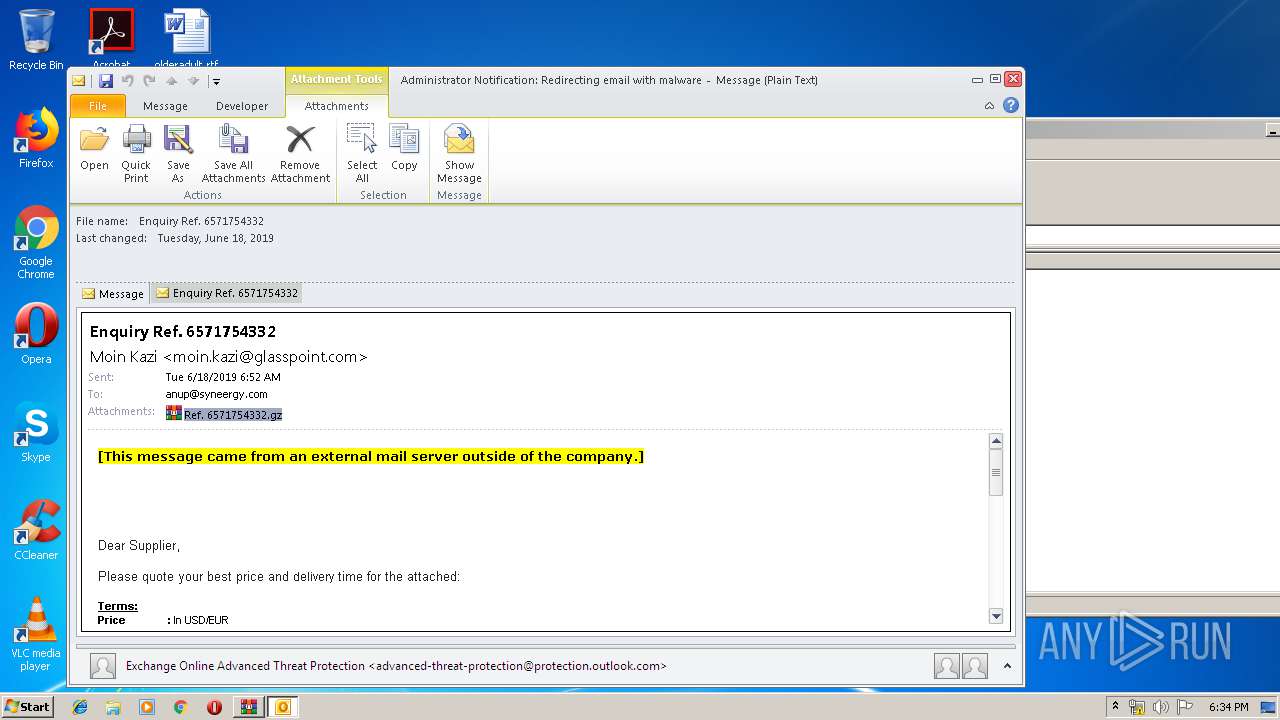
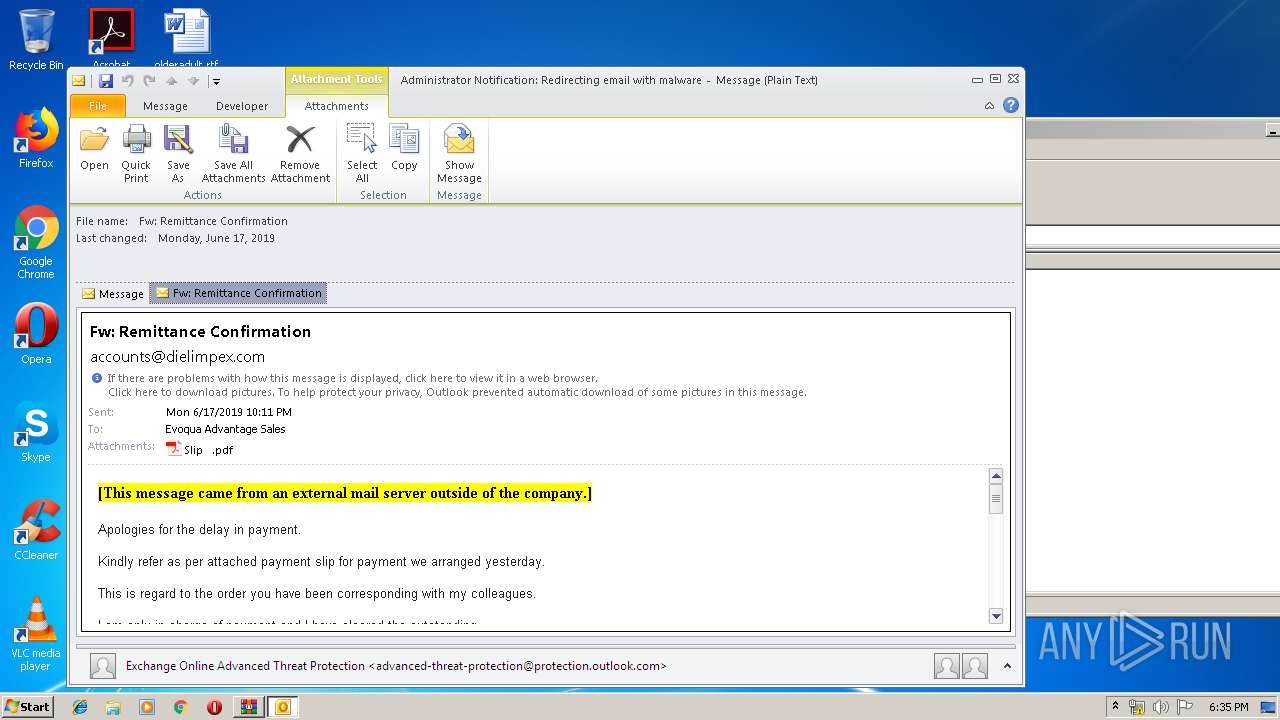
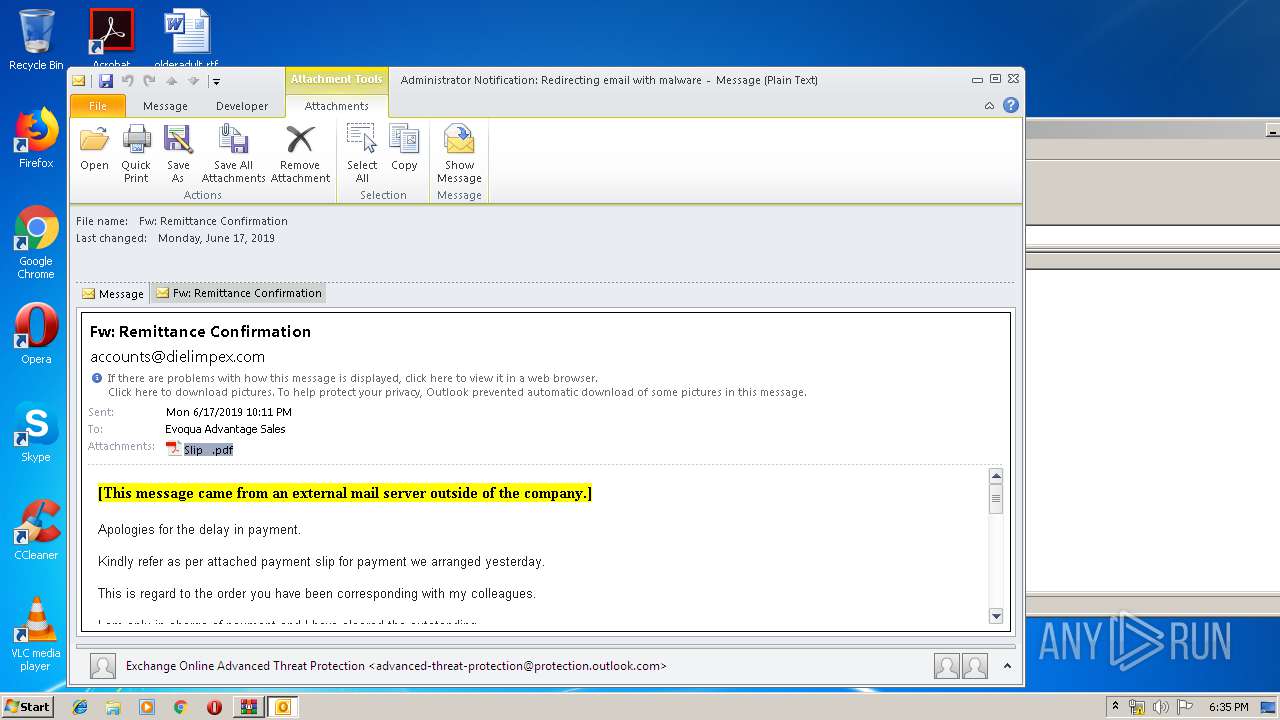
MALICIOUS
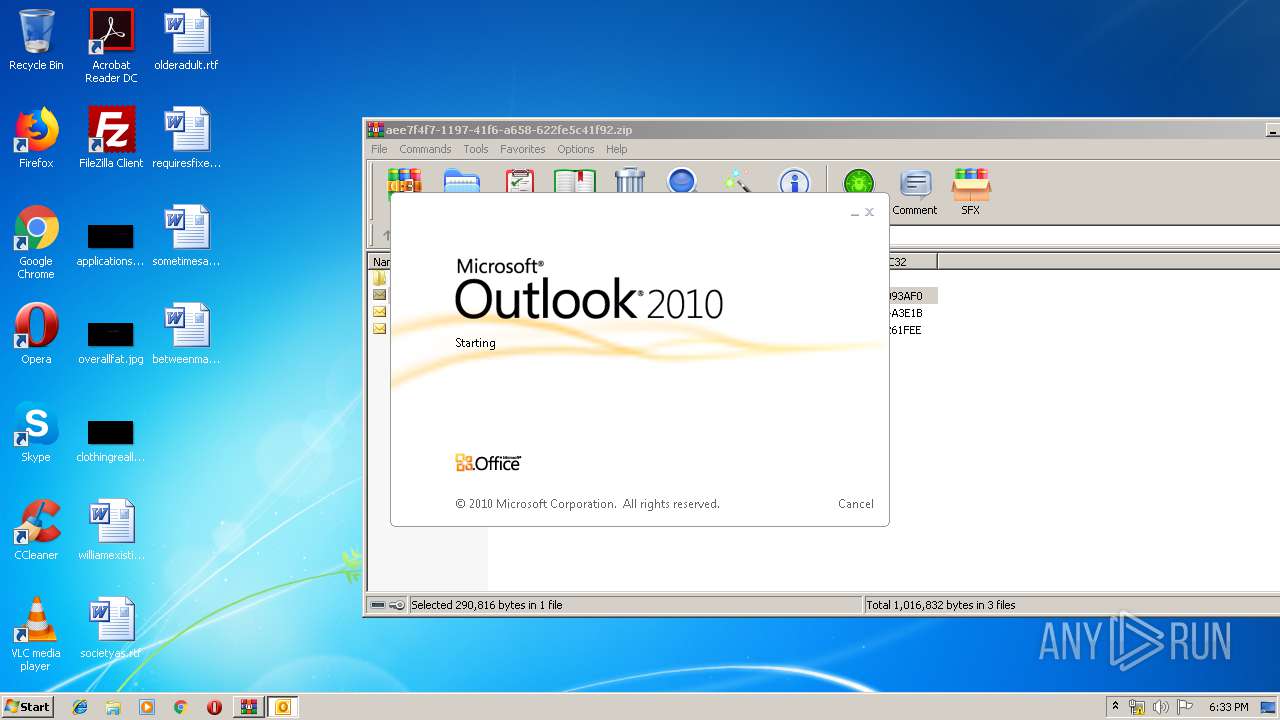
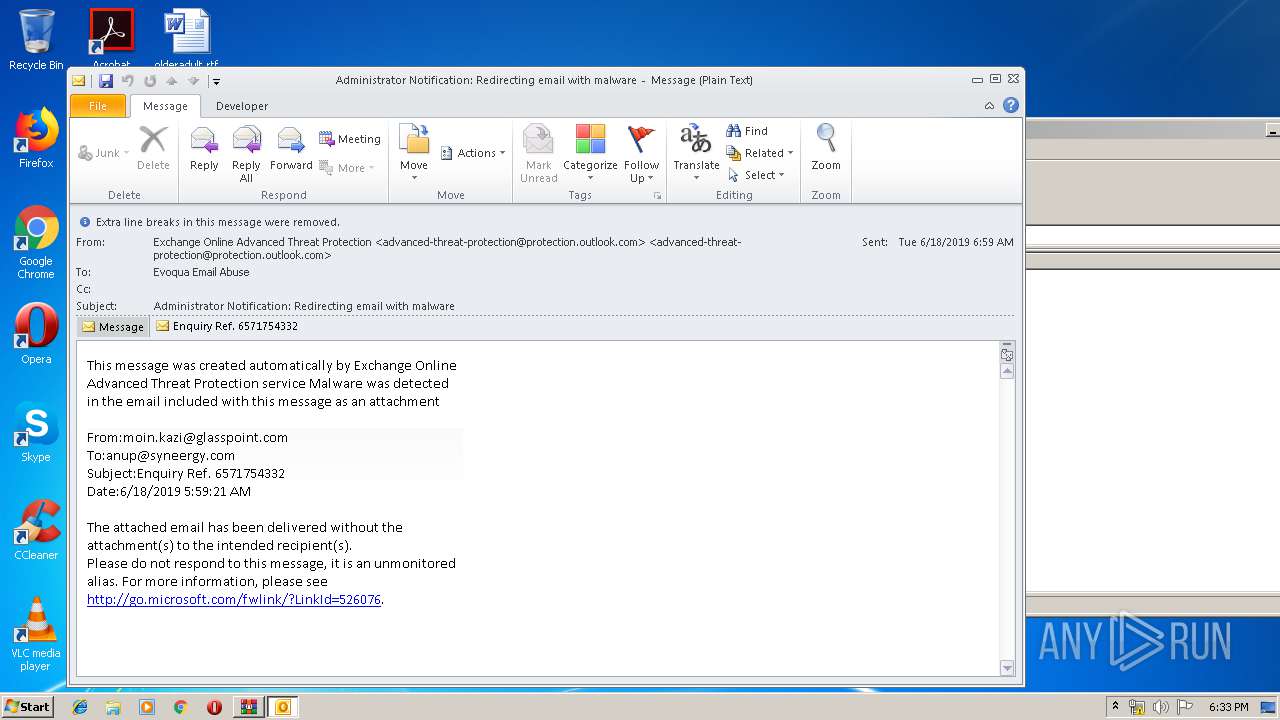
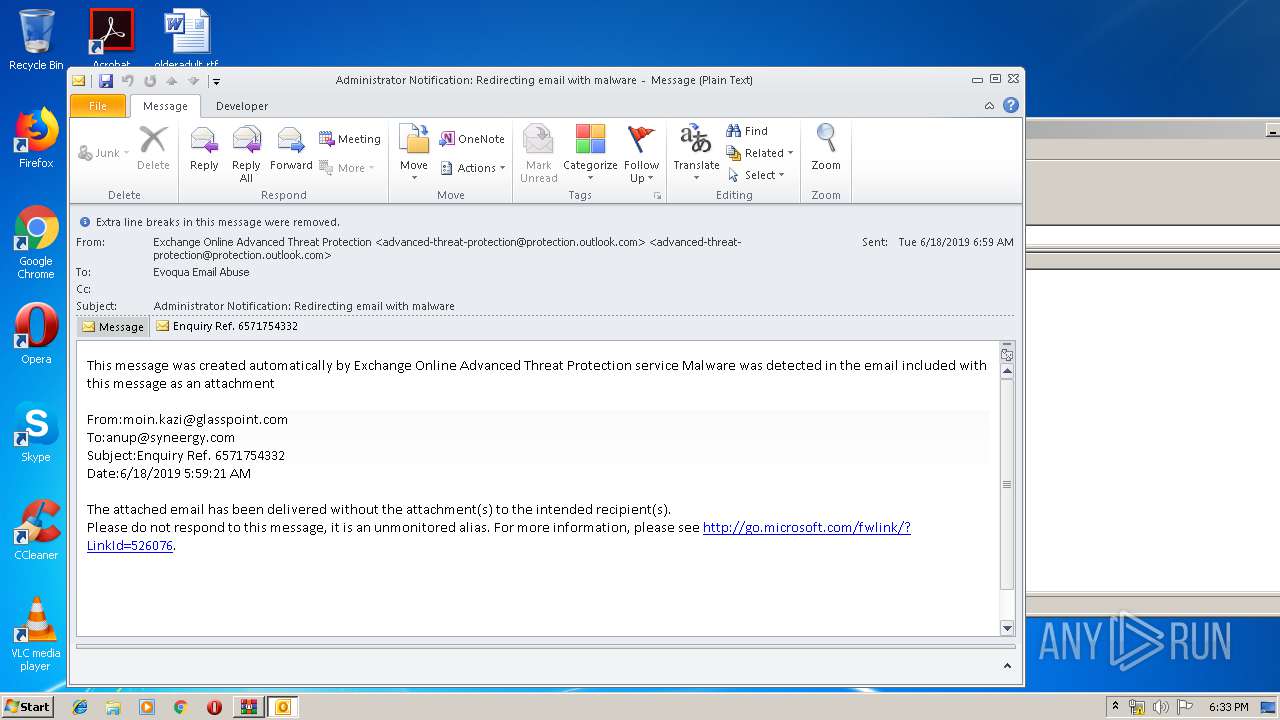
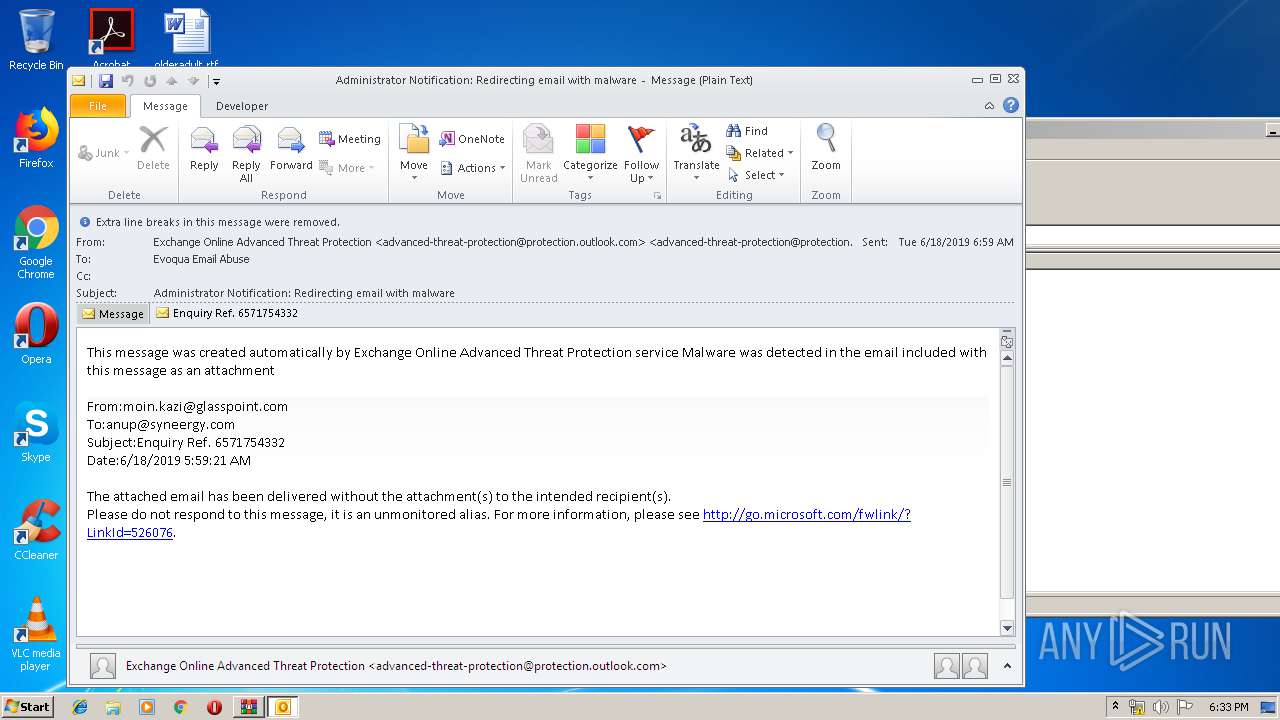
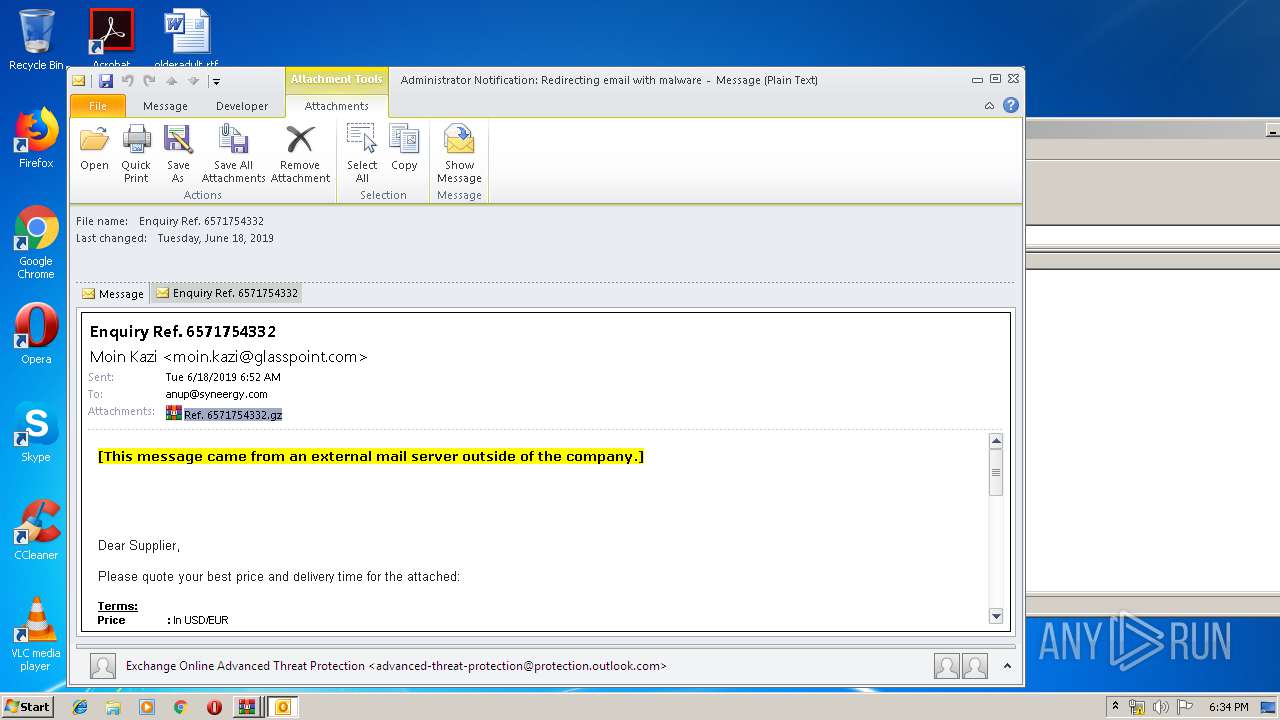
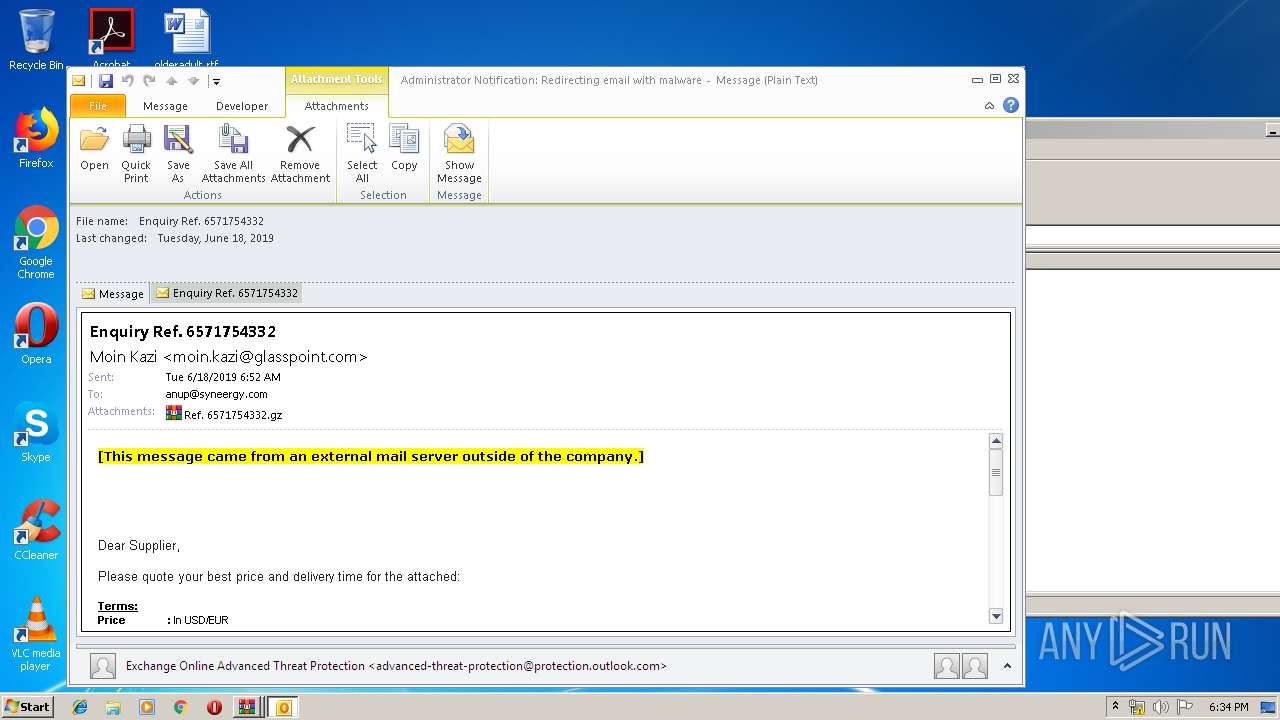
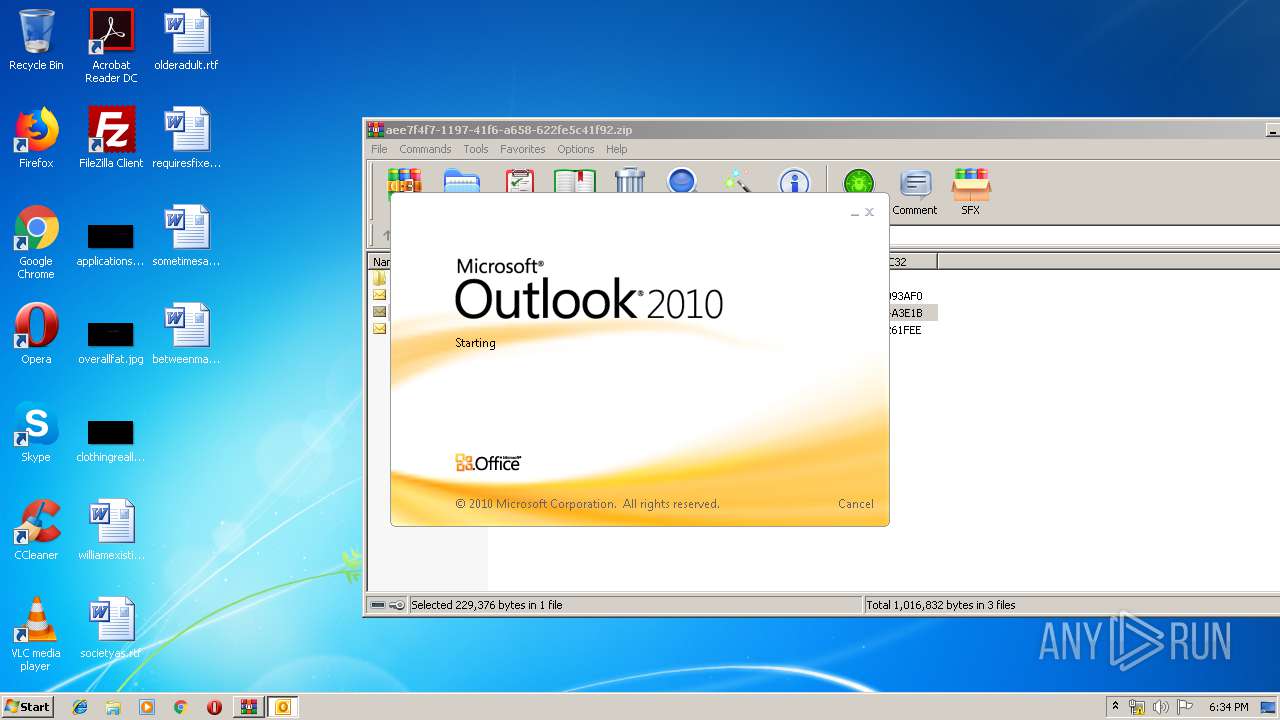
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 2940)
- OUTLOOK.EXE (PID: 2212)
- OUTLOOK.EXE (PID: 1652)
Application was dropped or rewritten from another process
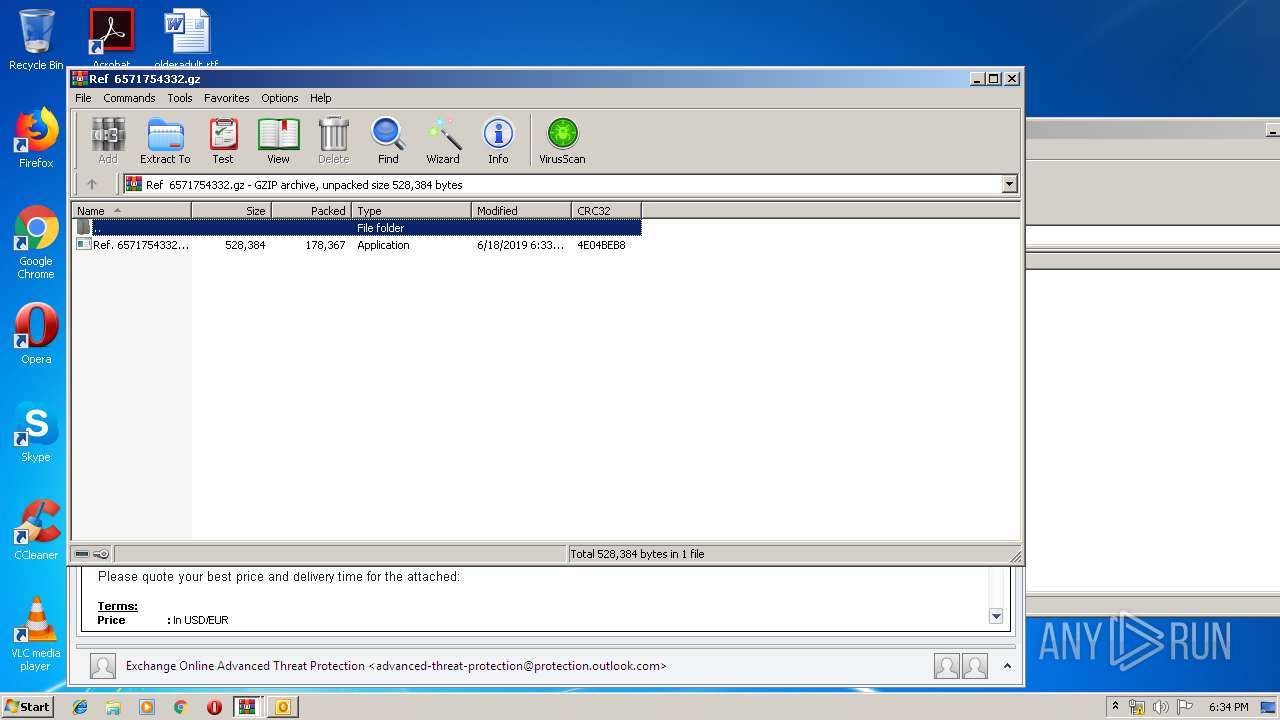
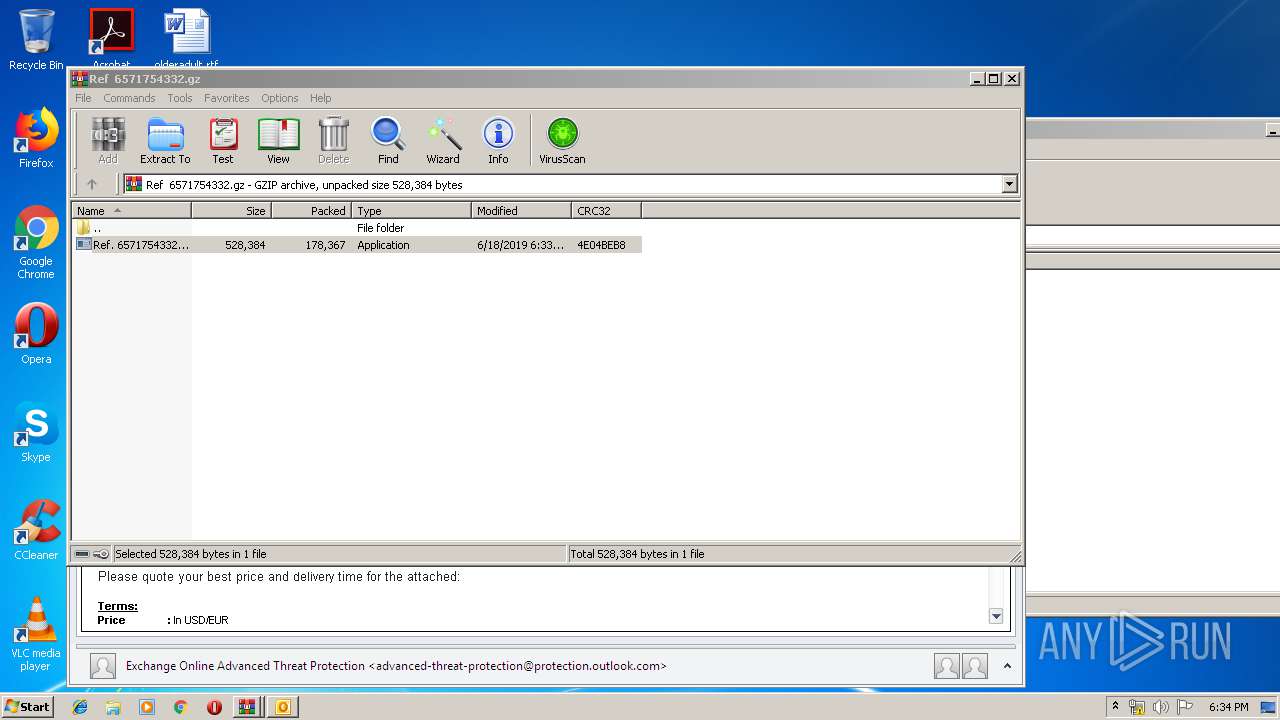
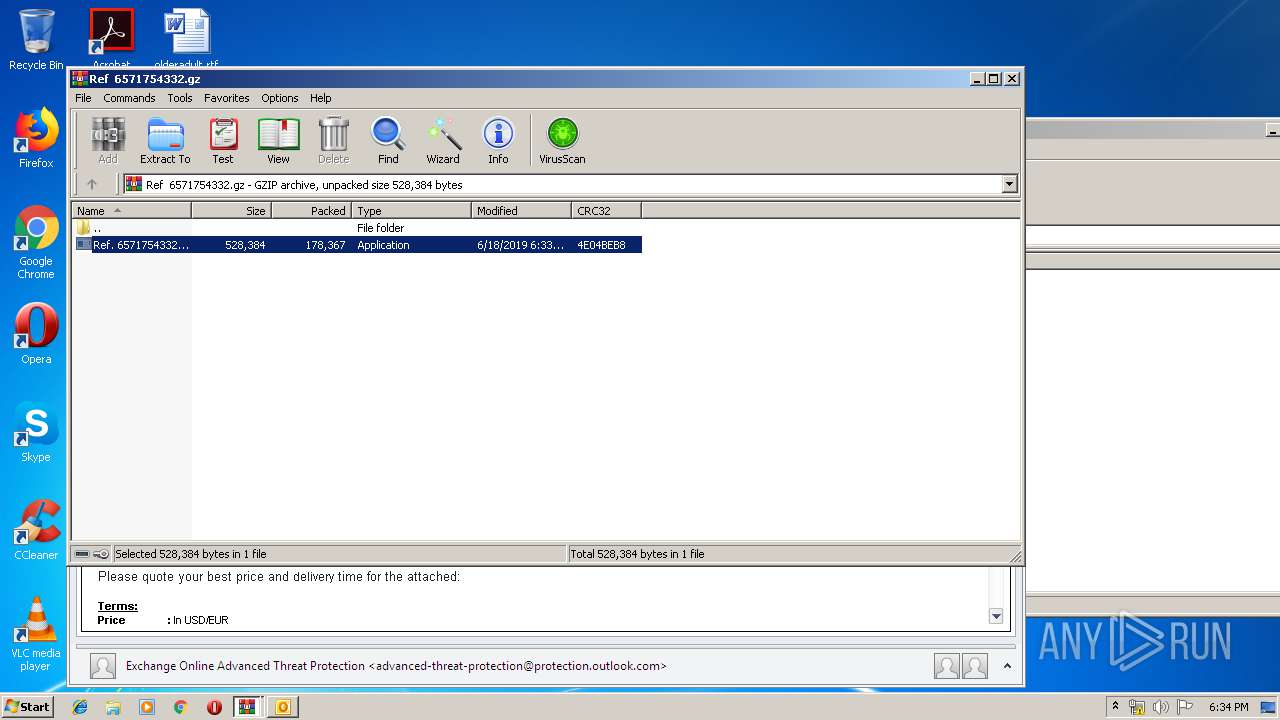
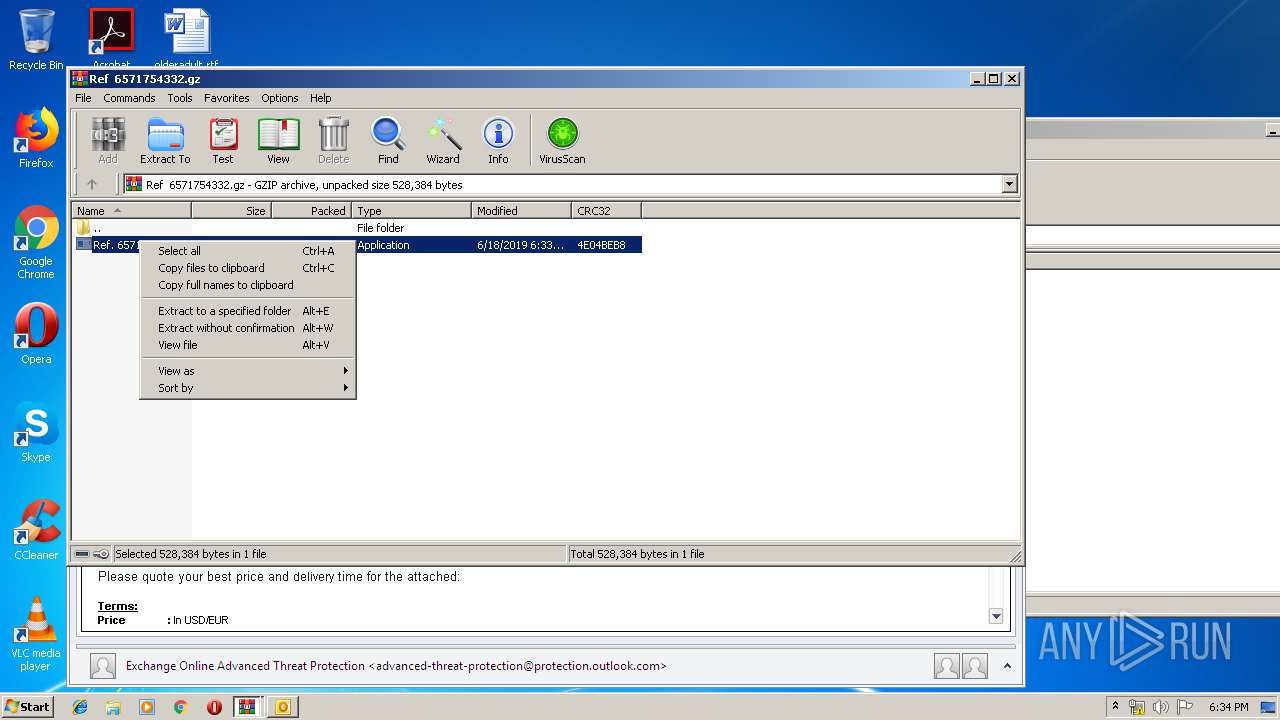
- Ref. 6571754332.exe (PID: 2588)
- Ref. 6571754332.exe (PID: 3688)
- Ref. 6571754332.exe (PID: 2604)
Detected artifacts of LokiBot
- Ref. 6571754332.exe (PID: 2604)
LOKIBOT was detected
- Ref. 6571754332.exe (PID: 2604)
Connects to CnC server
- Ref. 6571754332.exe (PID: 2604)
Actions looks like stealing of personal data
- Ref. 6571754332.exe (PID: 2604)
SUSPICIOUS
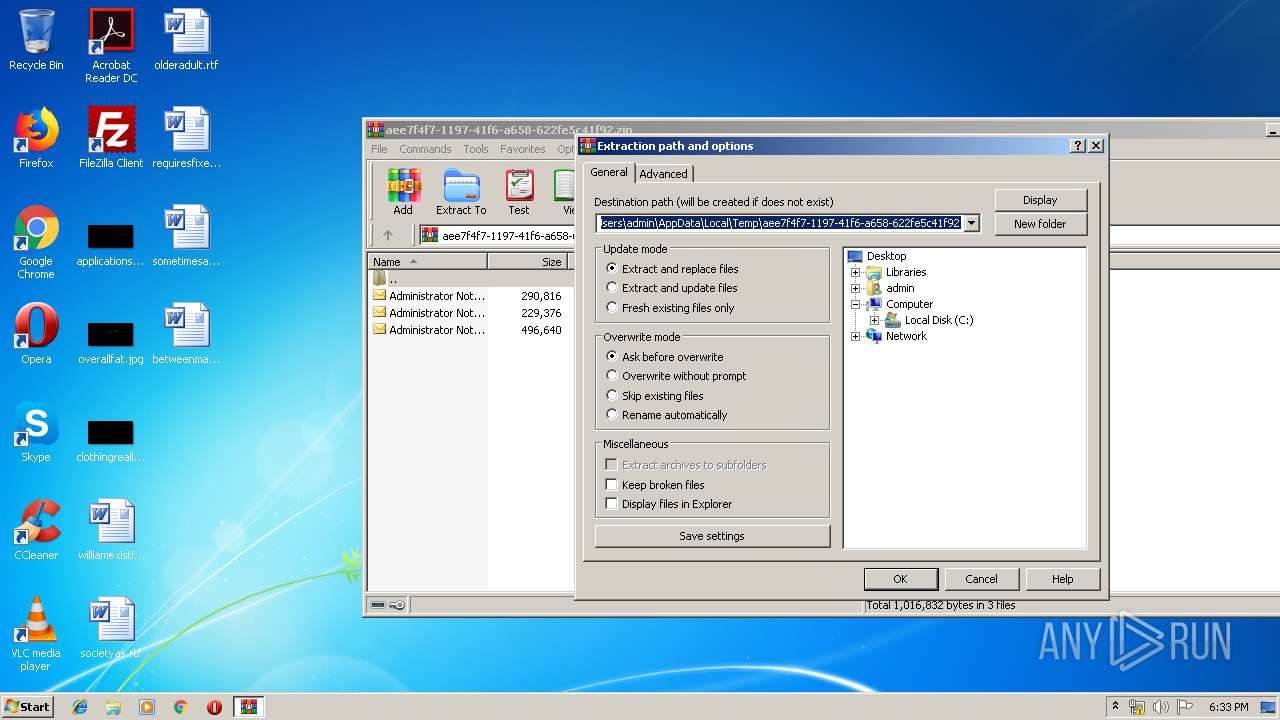
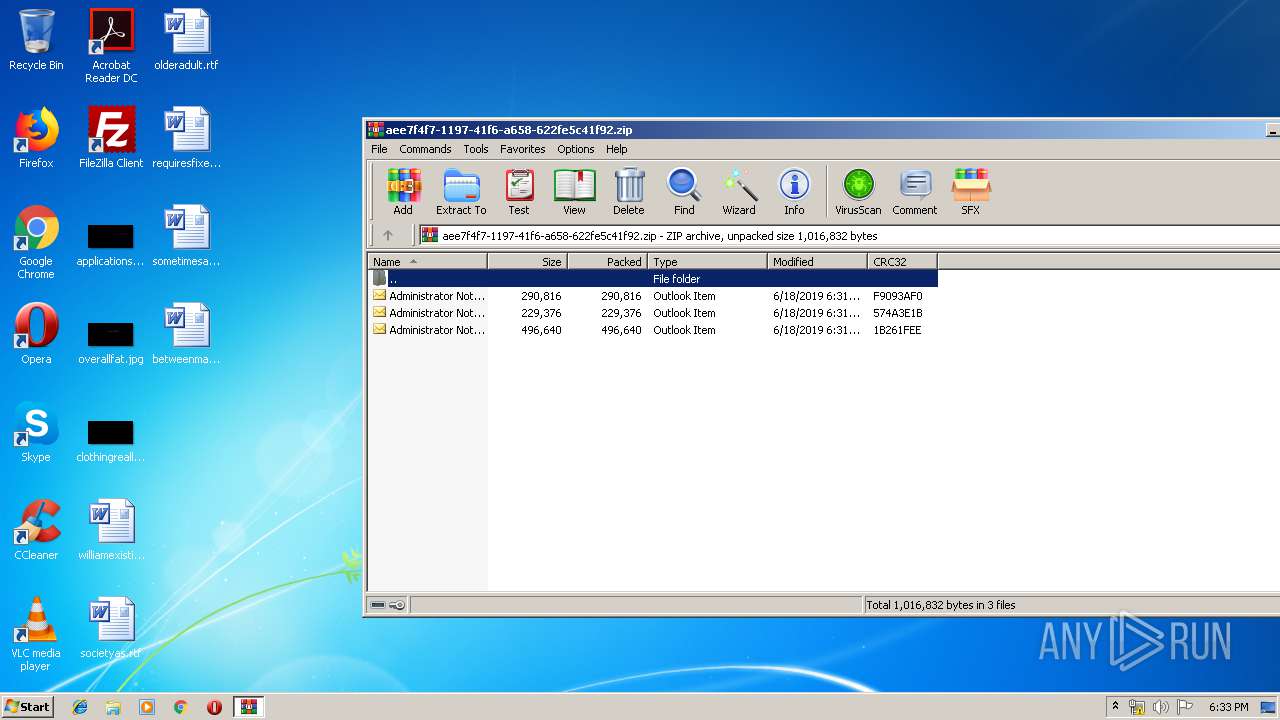
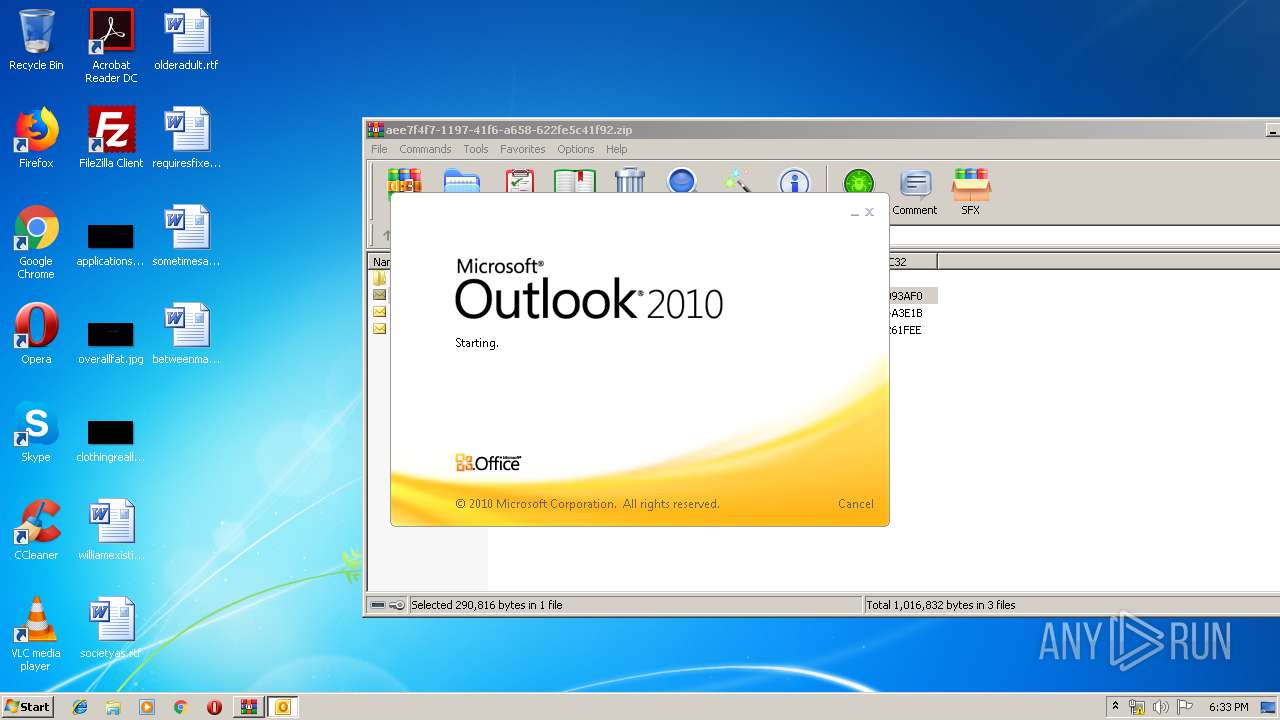
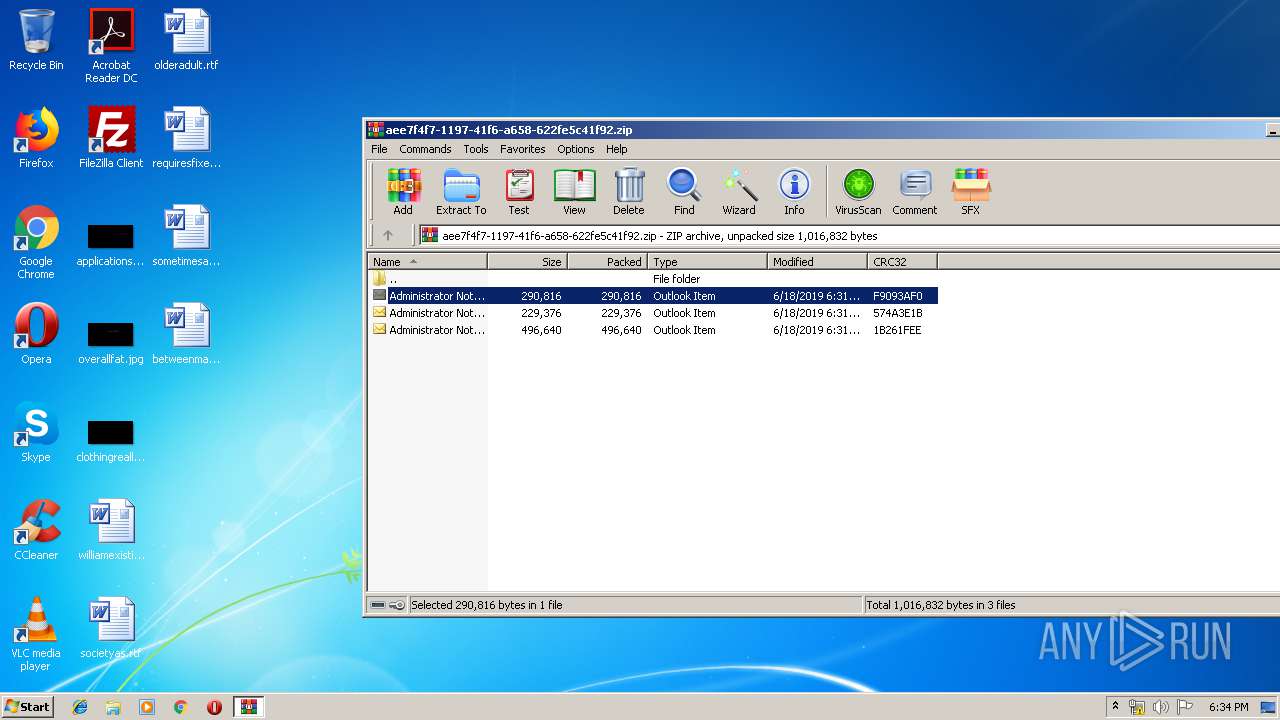
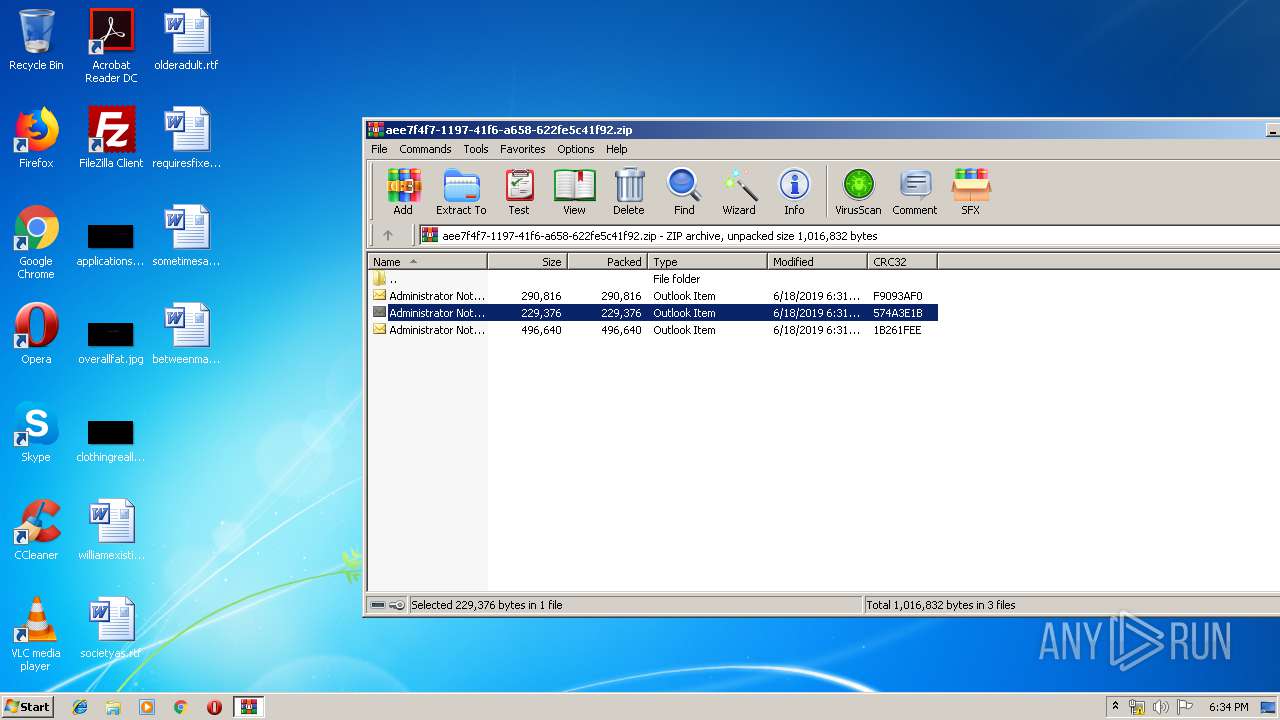
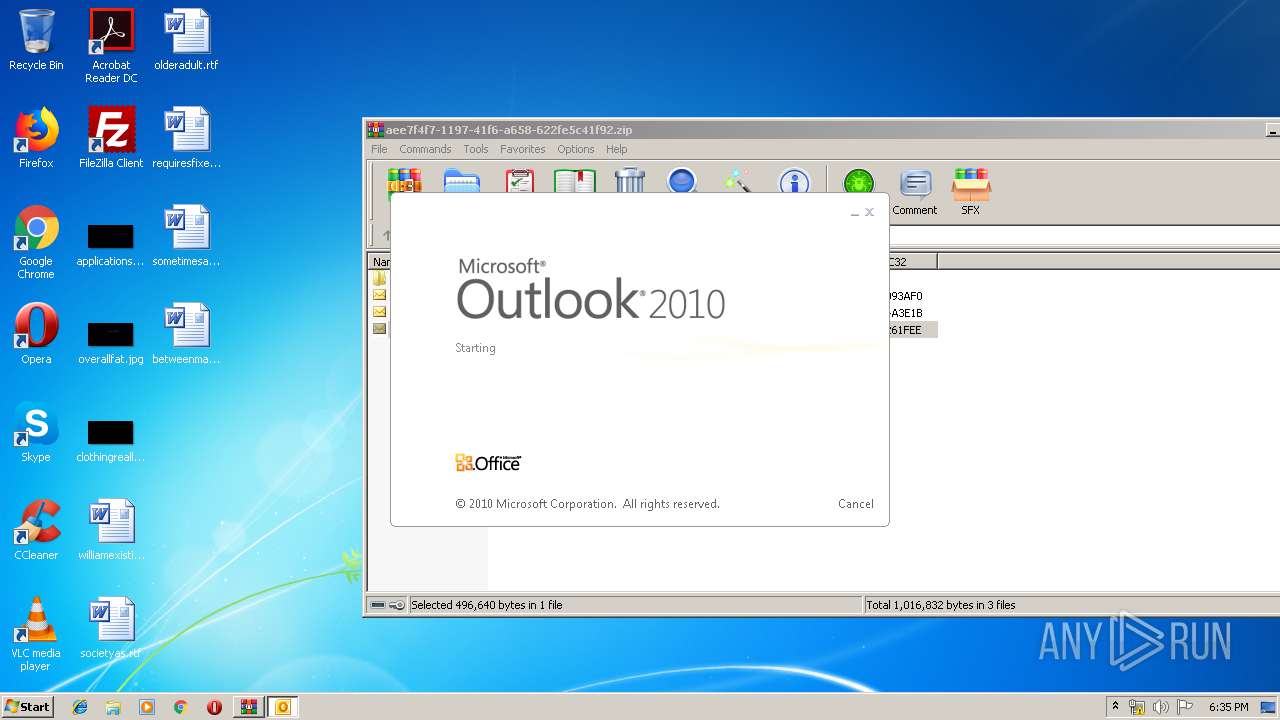
Starts Microsoft Office Application
- WinRAR.exe (PID: 3660)
Creates files in the user directory
- OUTLOOK.EXE (PID: 2940)
- Ref. 6571754332.exe (PID: 2604)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2940)
- OUTLOOK.EXE (PID: 2212)
- OUTLOOK.EXE (PID: 1652)
Executed via COM
- OUTLOOK.EXE (PID: 1380)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2776)
- Ref. 6571754332.exe (PID: 2604)
Application launched itself
- Ref. 6571754332.exe (PID: 2588)
- Ref. 6571754332.exe (PID: 3688)
Loads DLL from Mozilla Firefox
- Ref. 6571754332.exe (PID: 2604)
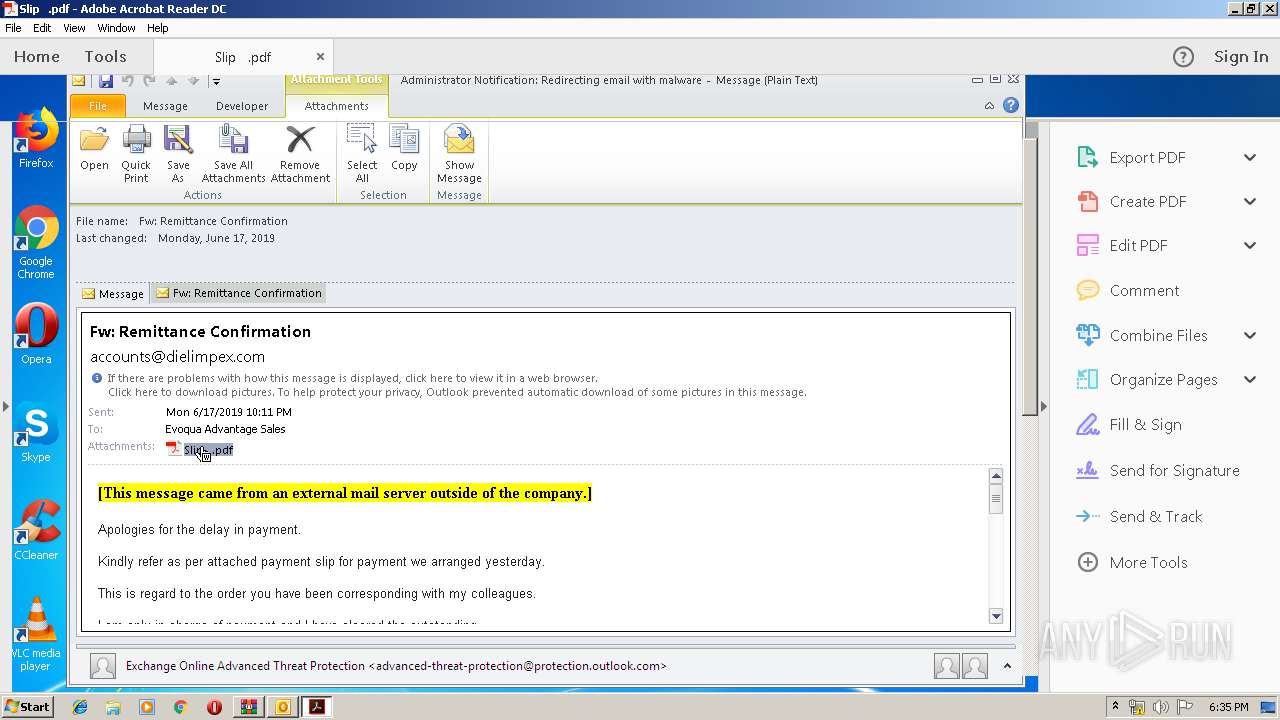
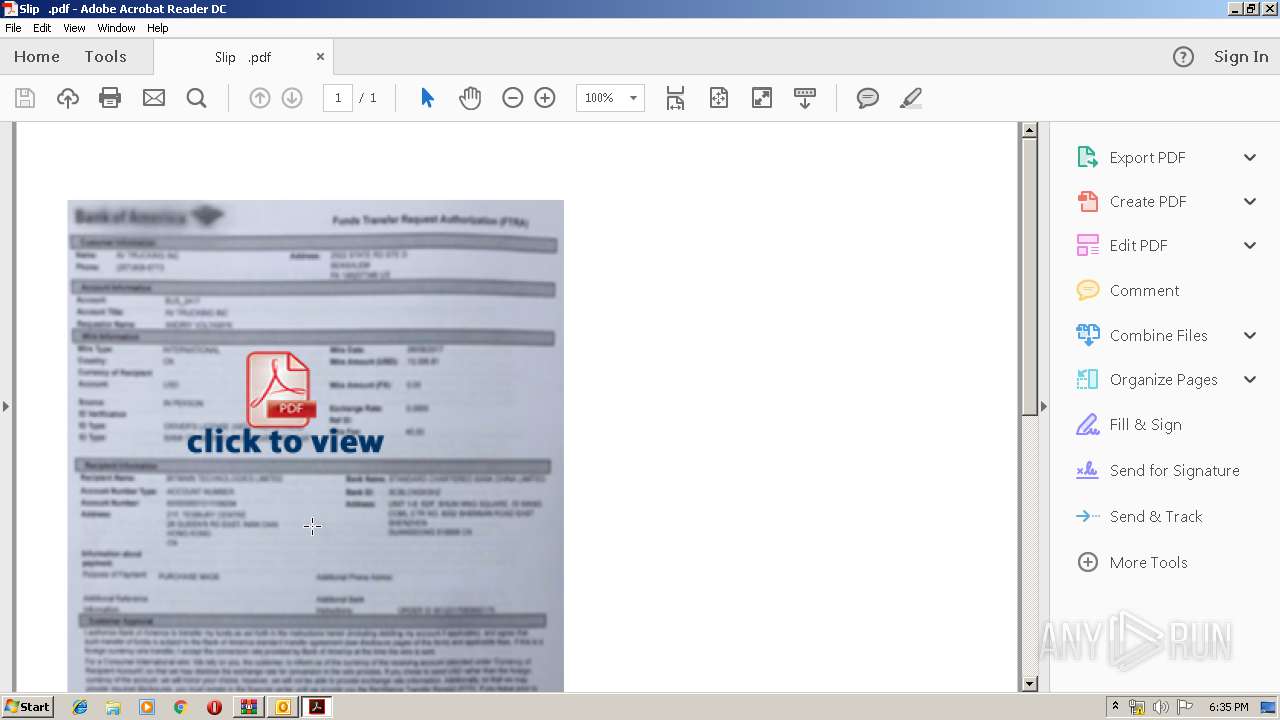
Starts Internet Explorer
- AcroRd32.exe (PID: 2388)
- AcroRd32.exe (PID: 1892)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 1380)
- OUTLOOK.EXE (PID: 2940)
- OUTLOOK.EXE (PID: 2212)
- OUTLOOK.EXE (PID: 1652)
Application launched itself
- AcroRd32.exe (PID: 2388)
- iexplore.exe (PID: 1136)
- RdrCEF.exe (PID: 3316)
- RdrCEF.exe (PID: 2864)
- iexplore.exe (PID: 584)
Creates files in the user directory
- AcroRd32.exe (PID: 2388)
- iexplore.exe (PID: 2676)
Changes internet zones settings
- iexplore.exe (PID: 1136)
- iexplore.exe (PID: 584)
Reads internet explorer settings
- iexplore.exe (PID: 2676)
- iexplore.exe (PID: 3616)
Reads Internet Cache Settings
- iexplore.exe (PID: 2676)
- iexplore.exe (PID: 3616)
- iexplore.exe (PID: 584)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (36.3) |
|---|
EXIF
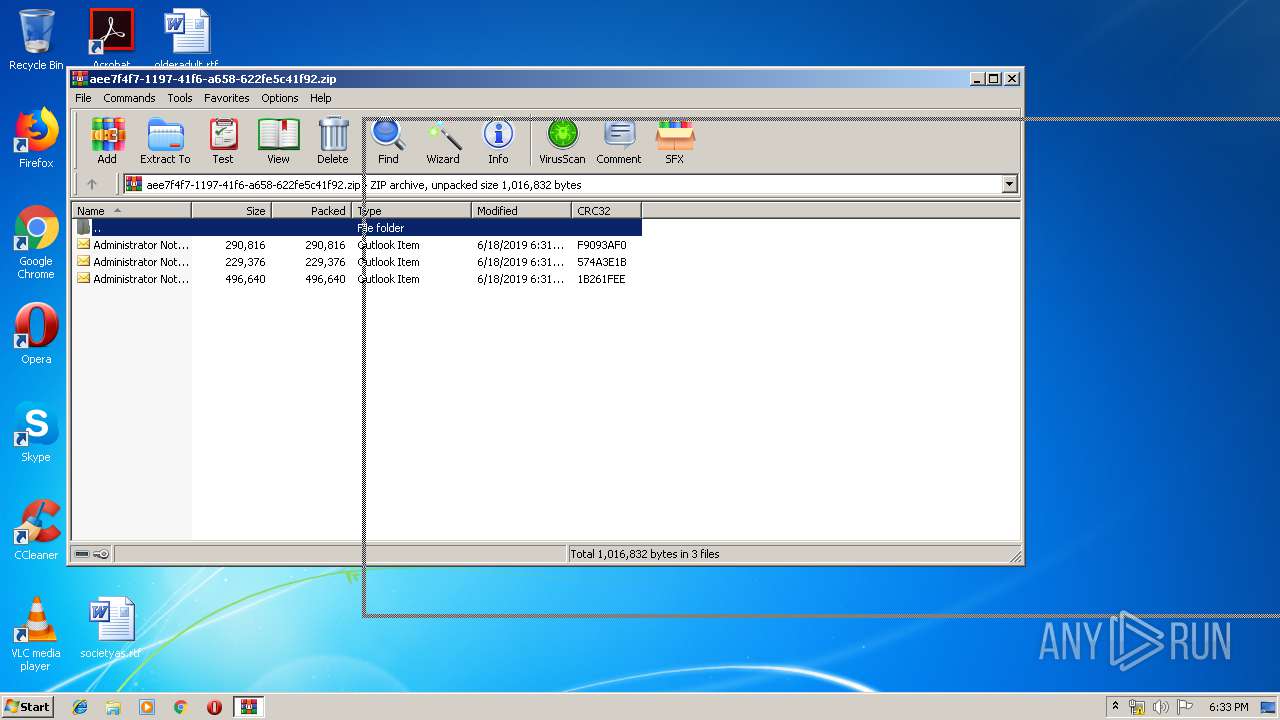
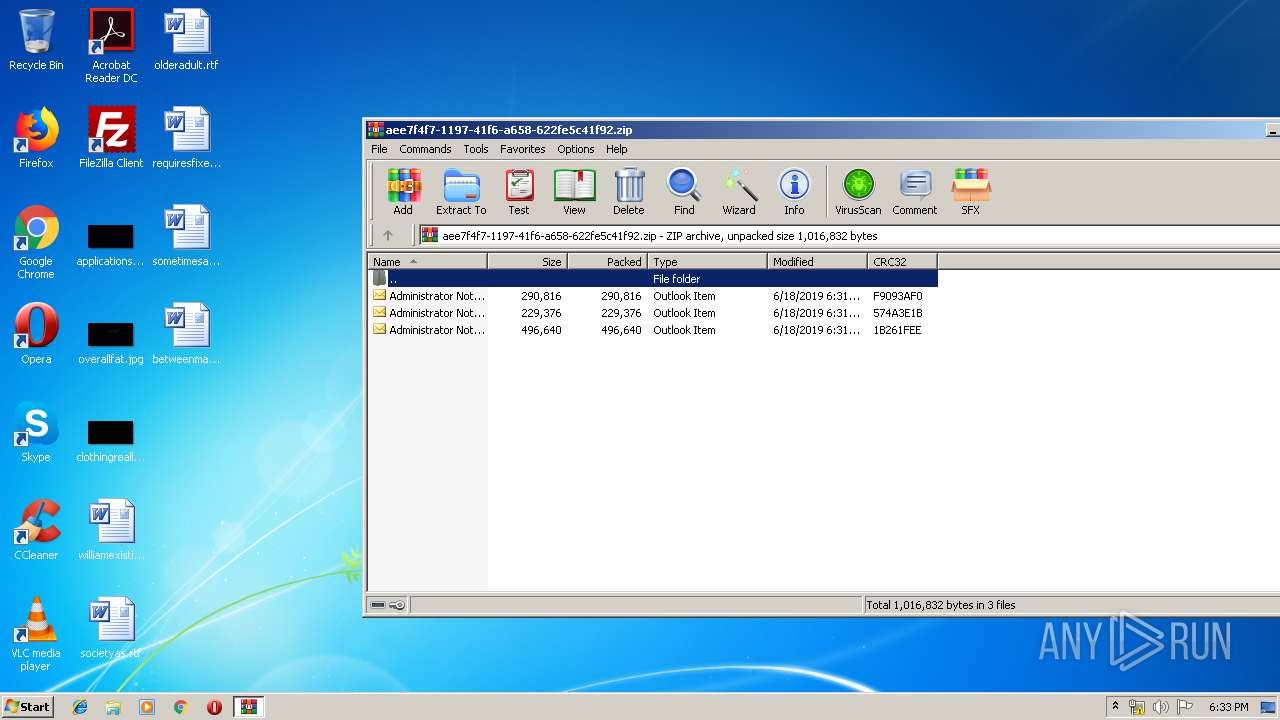
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | 0x0800 |
| ZipCompression: | None |
| ZipModifyDate: | 2019:06:18 17:31:01 |
| ZipCRC: | 0xf9093af0 |
| ZipCompressedSize: | 290816 |
| ZipUncompressedSize: | 290816 |
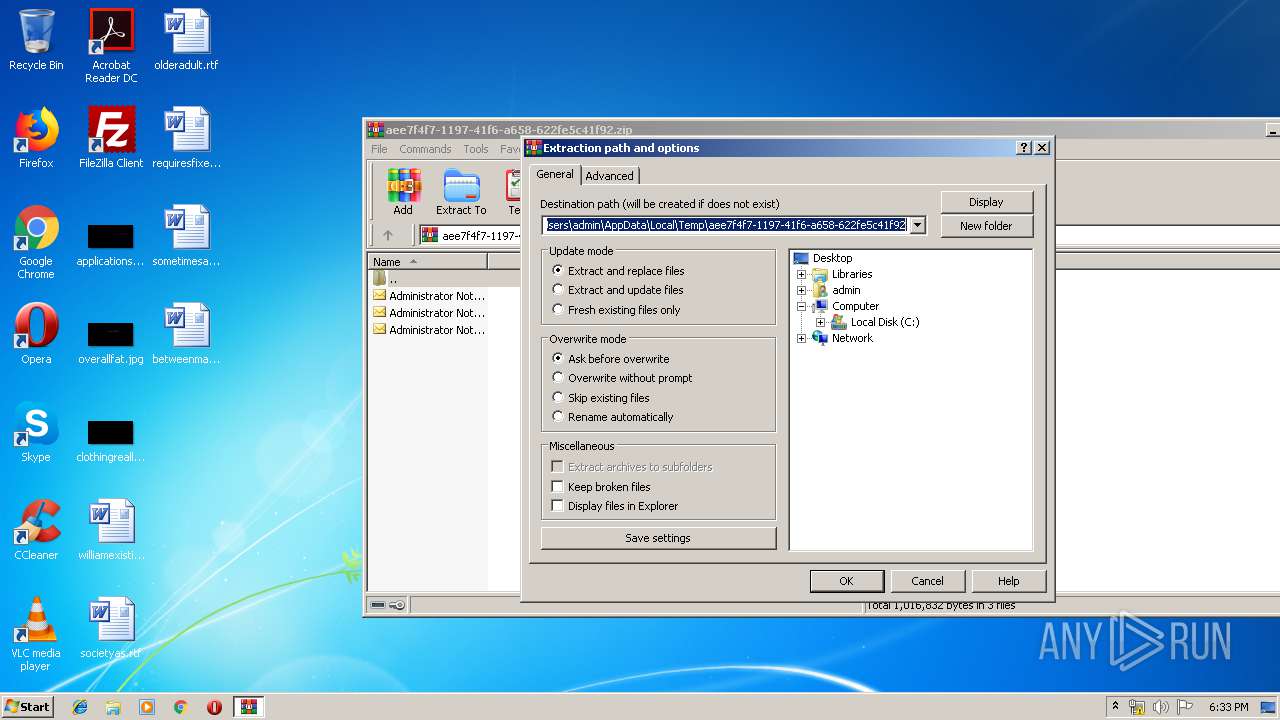
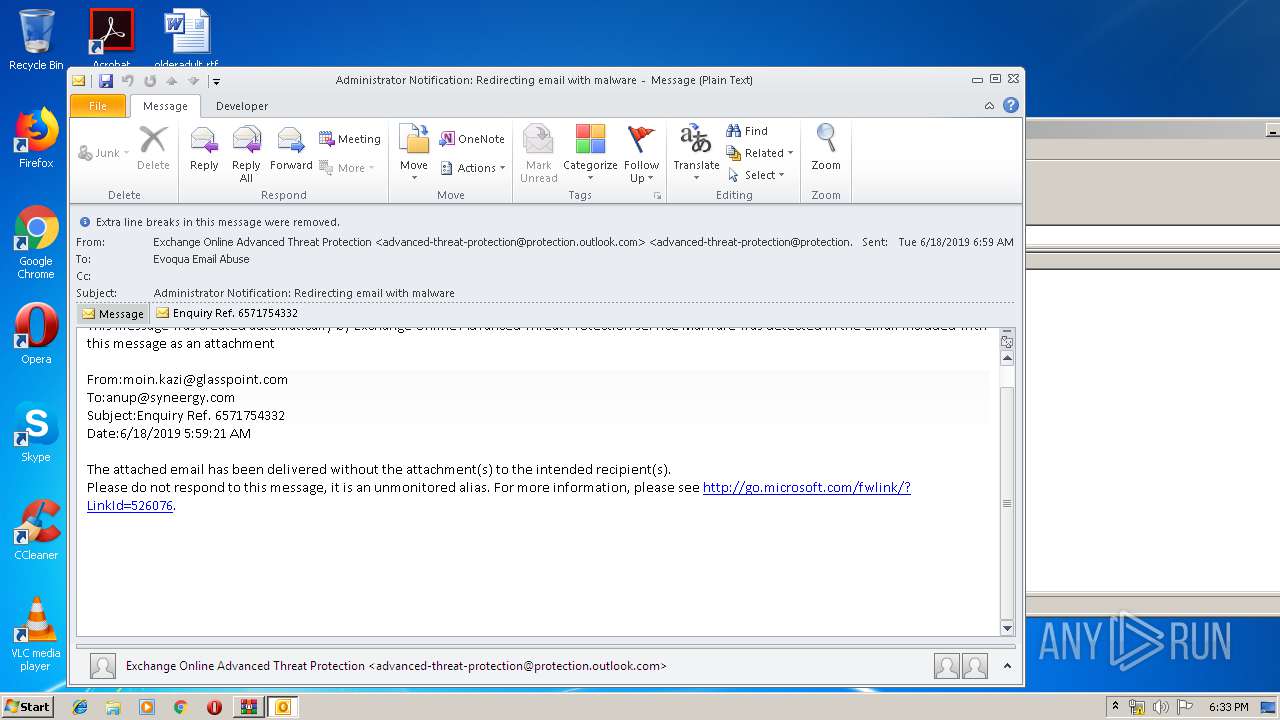
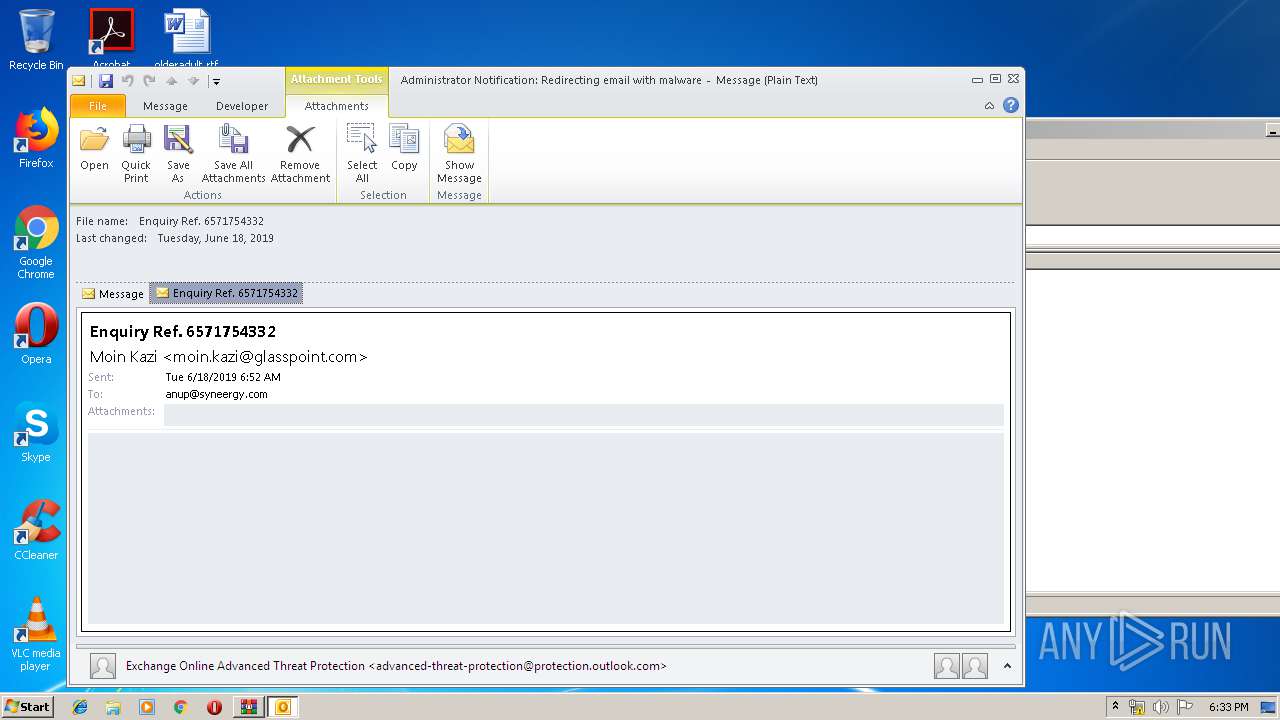
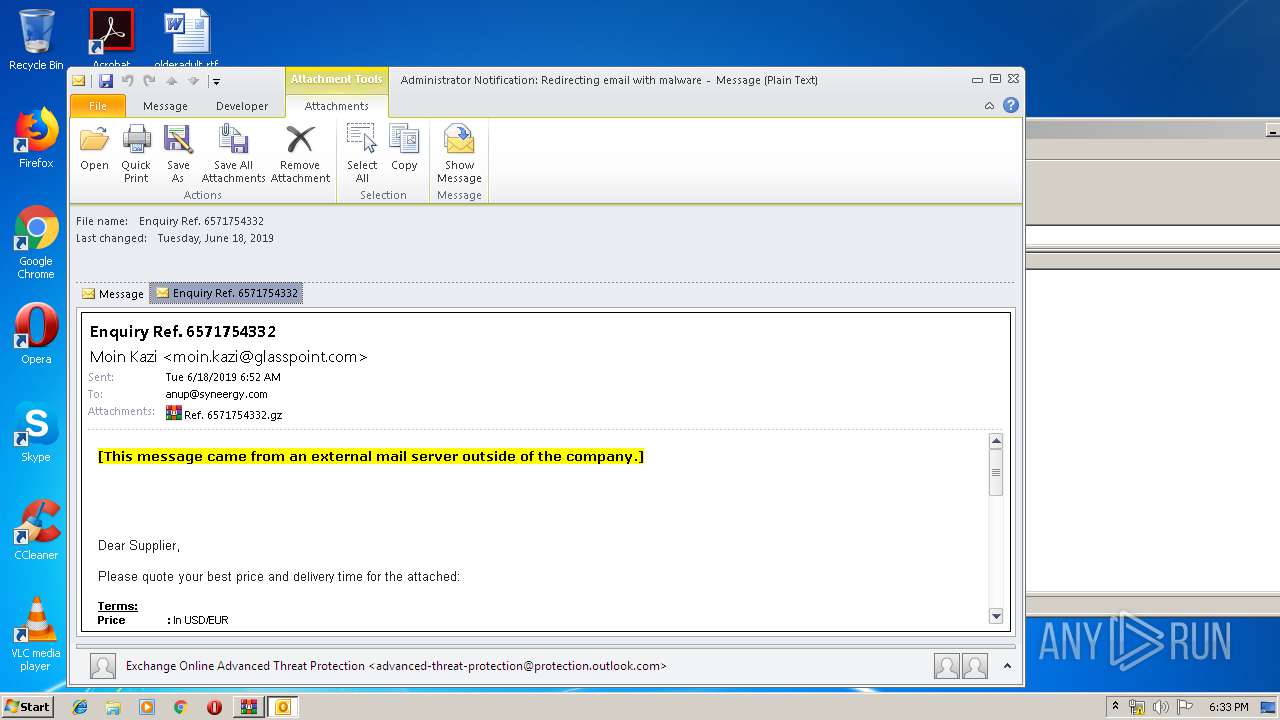
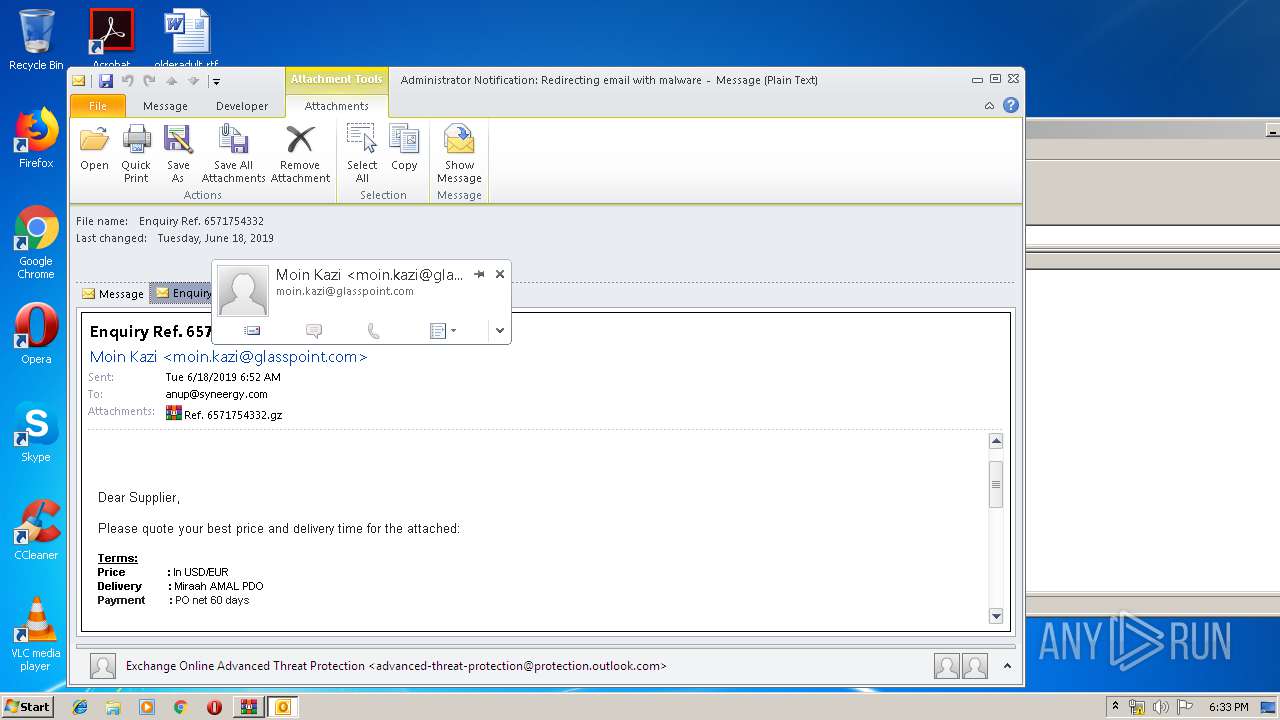
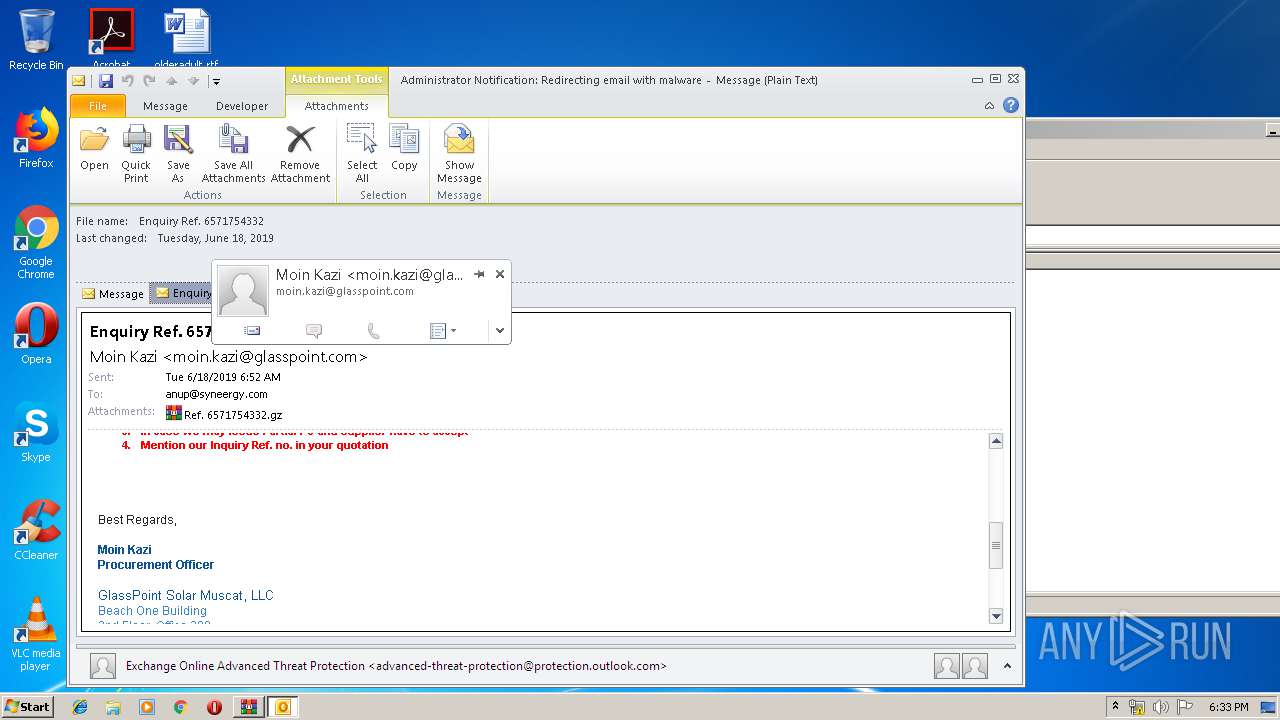
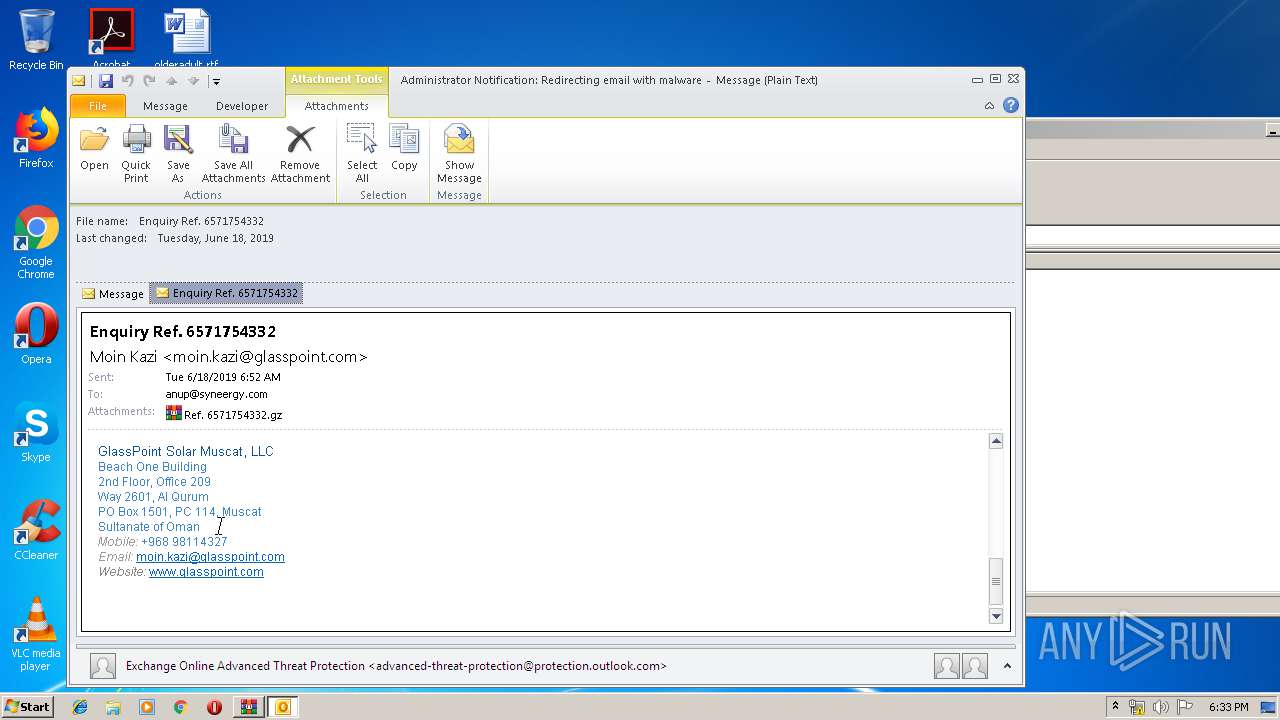
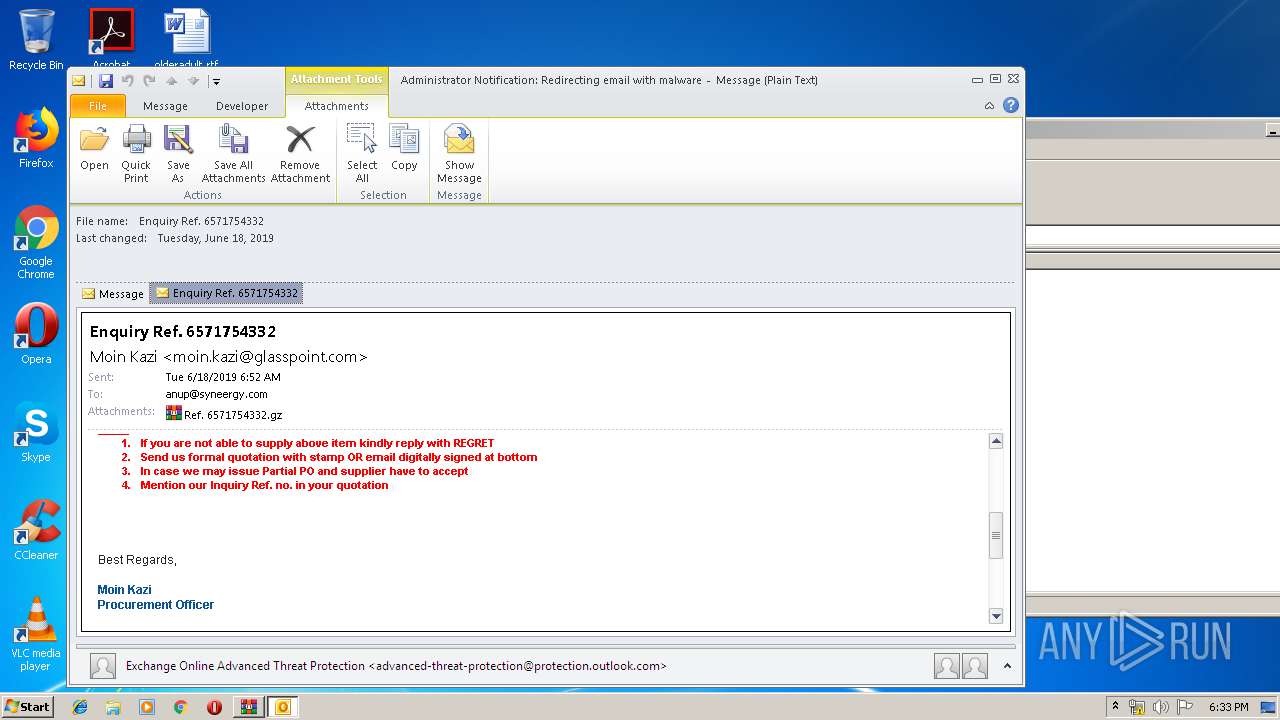
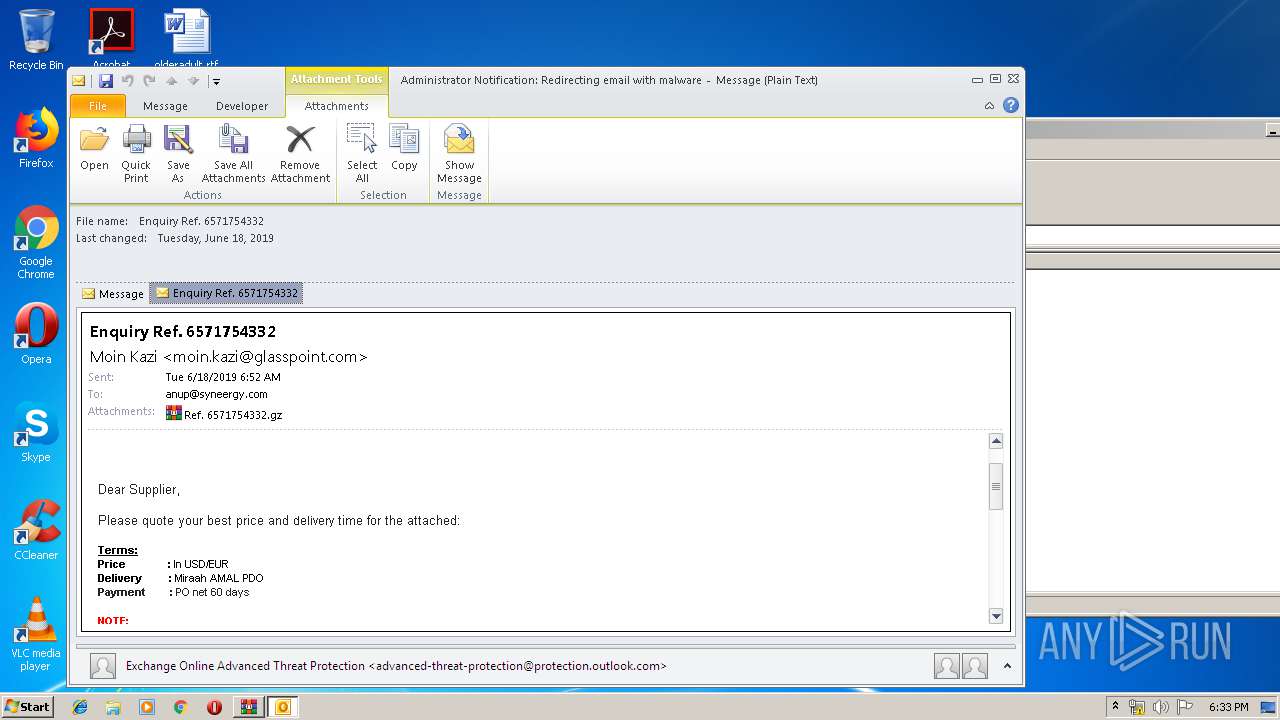
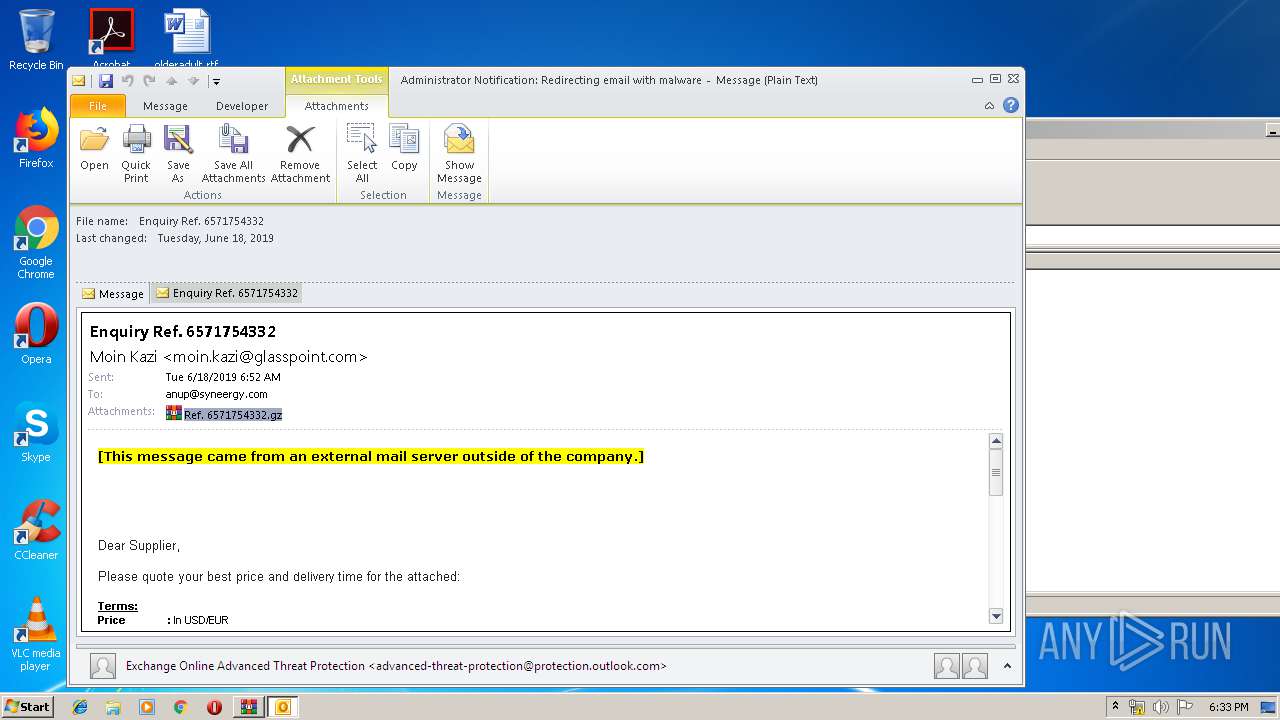
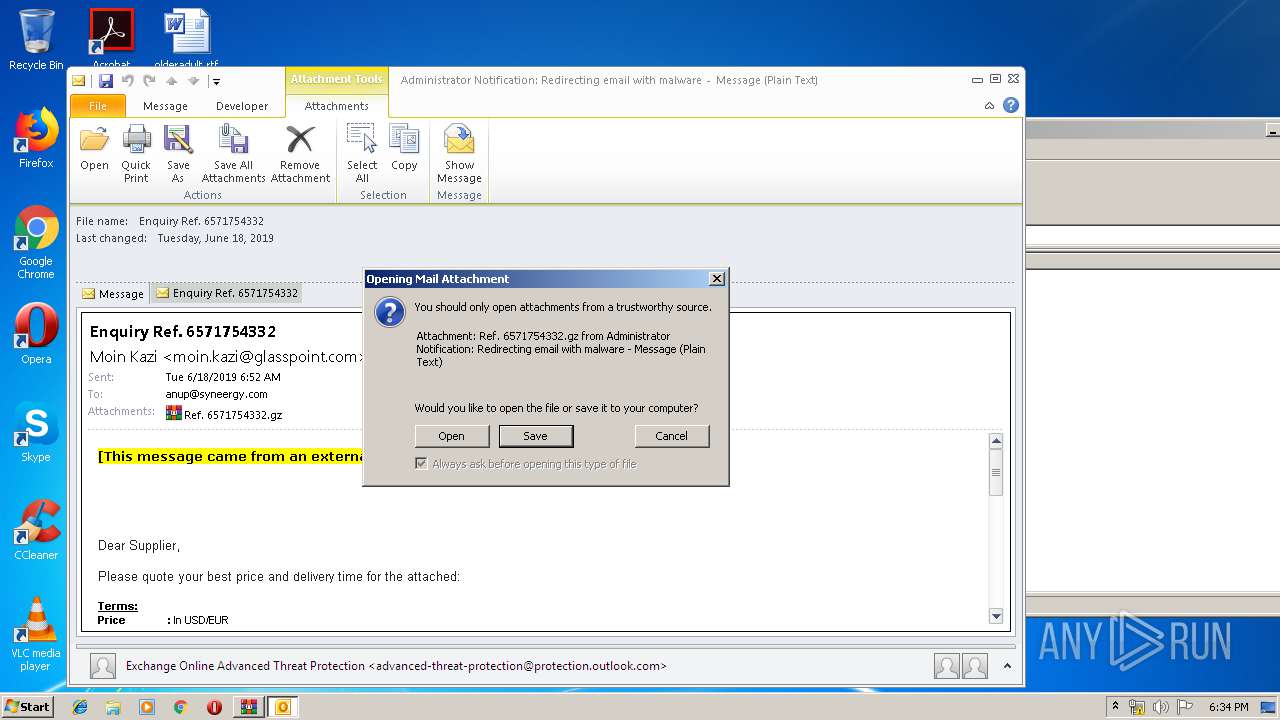
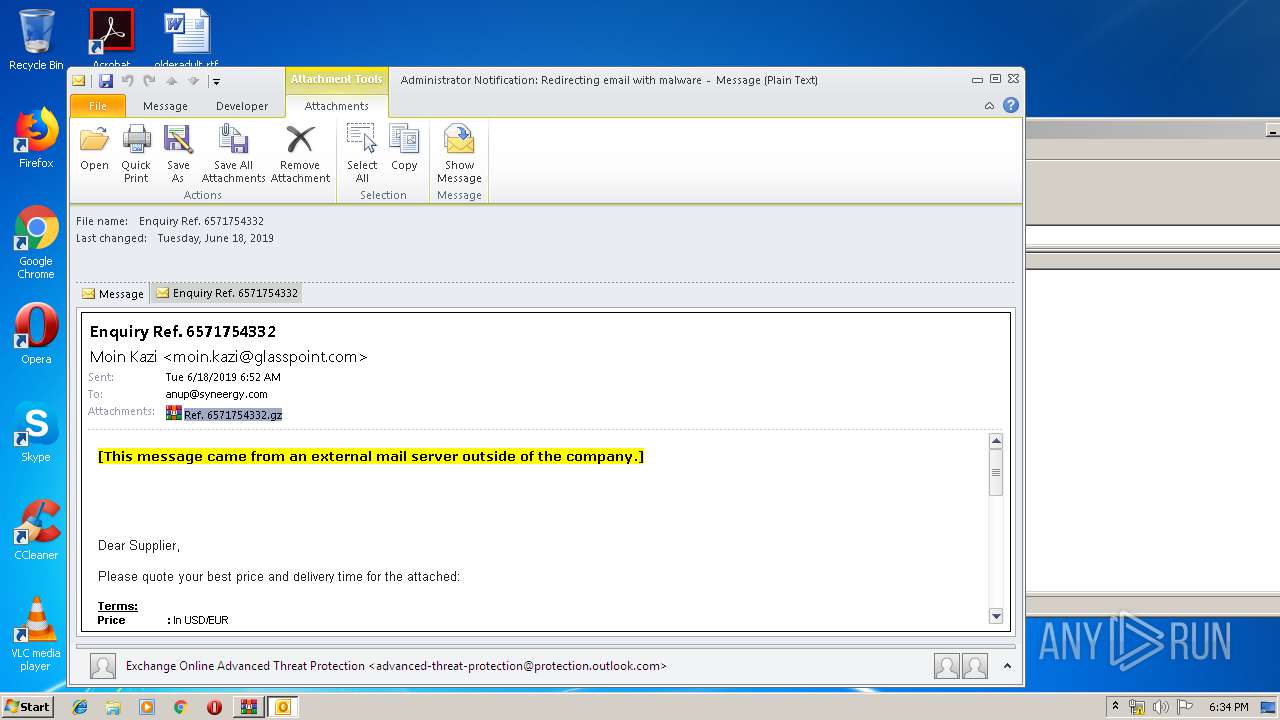
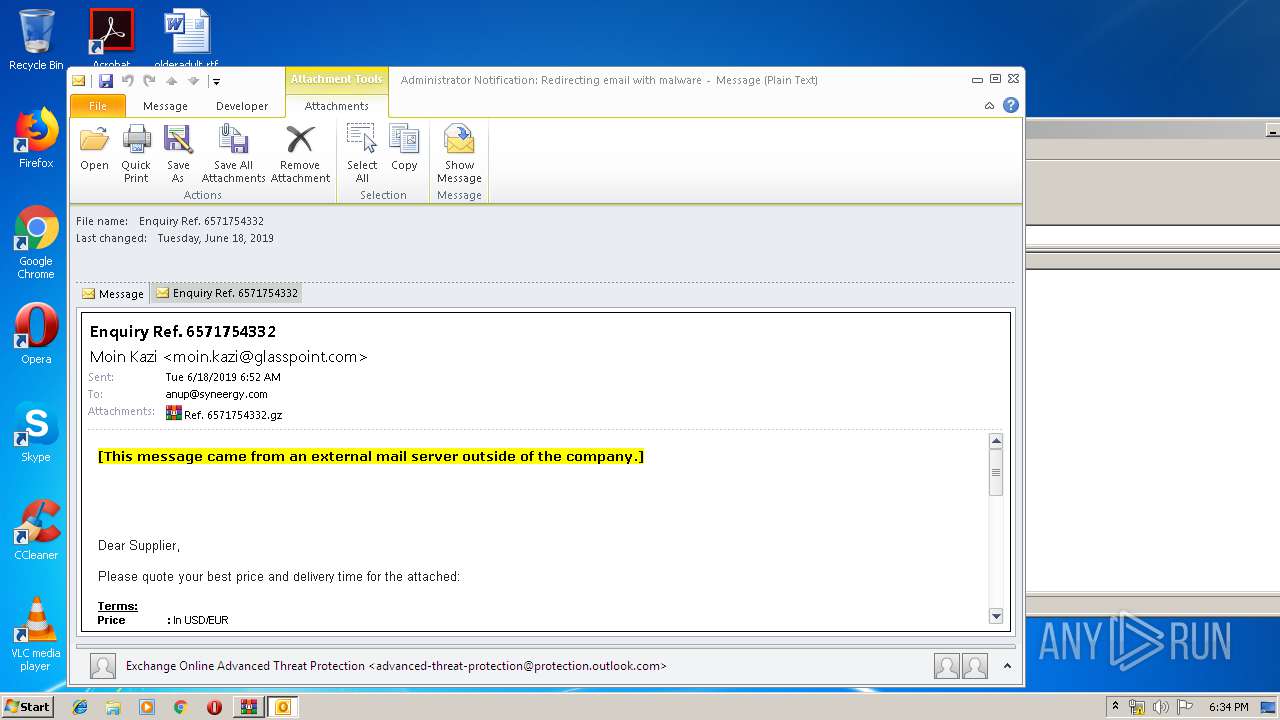
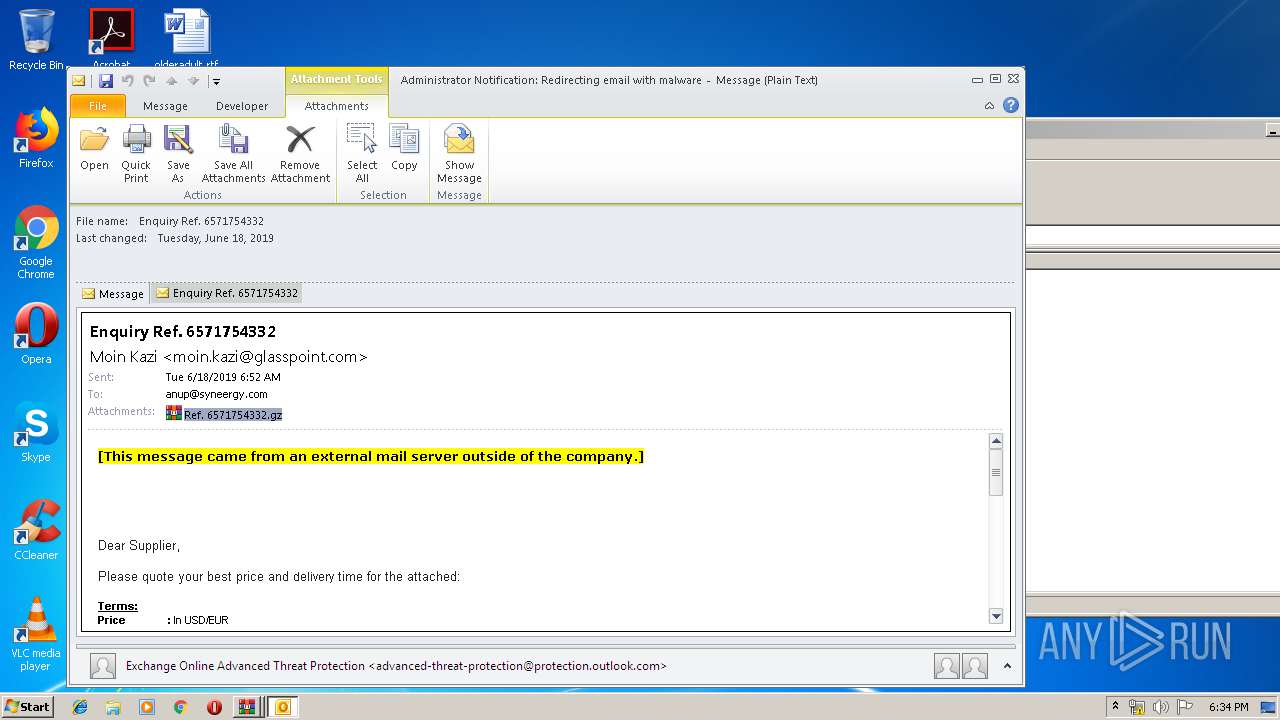
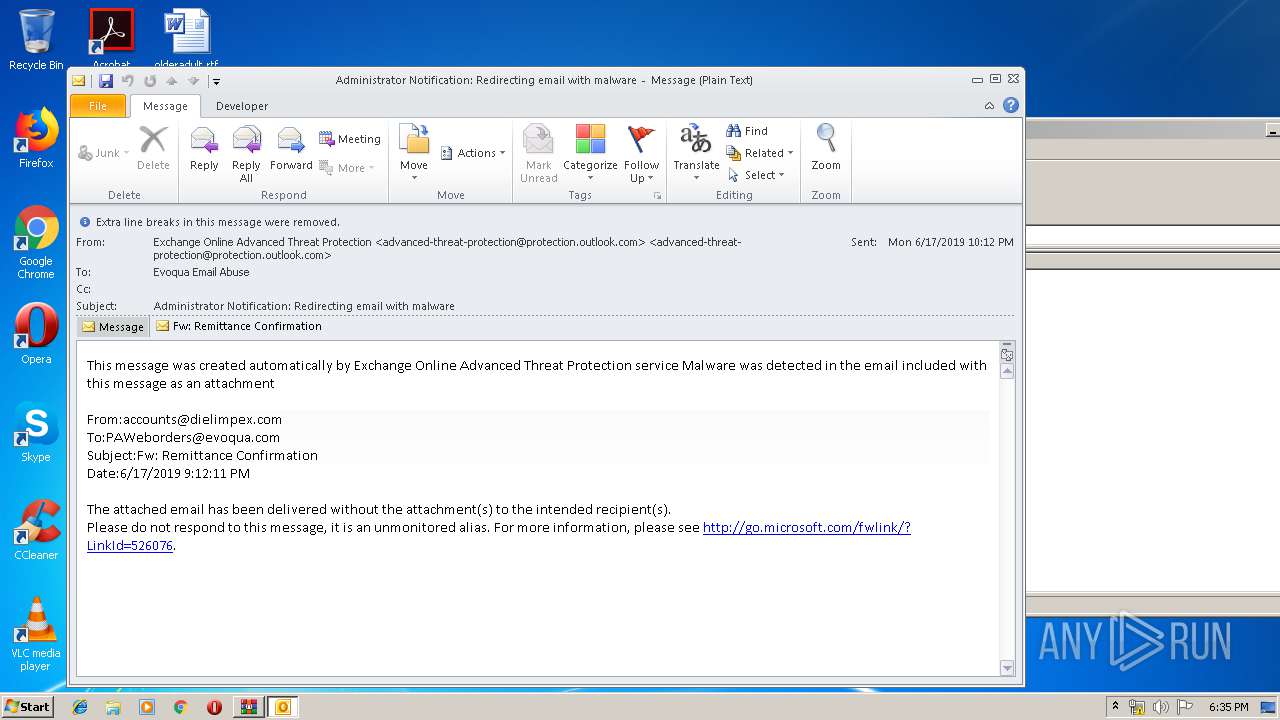
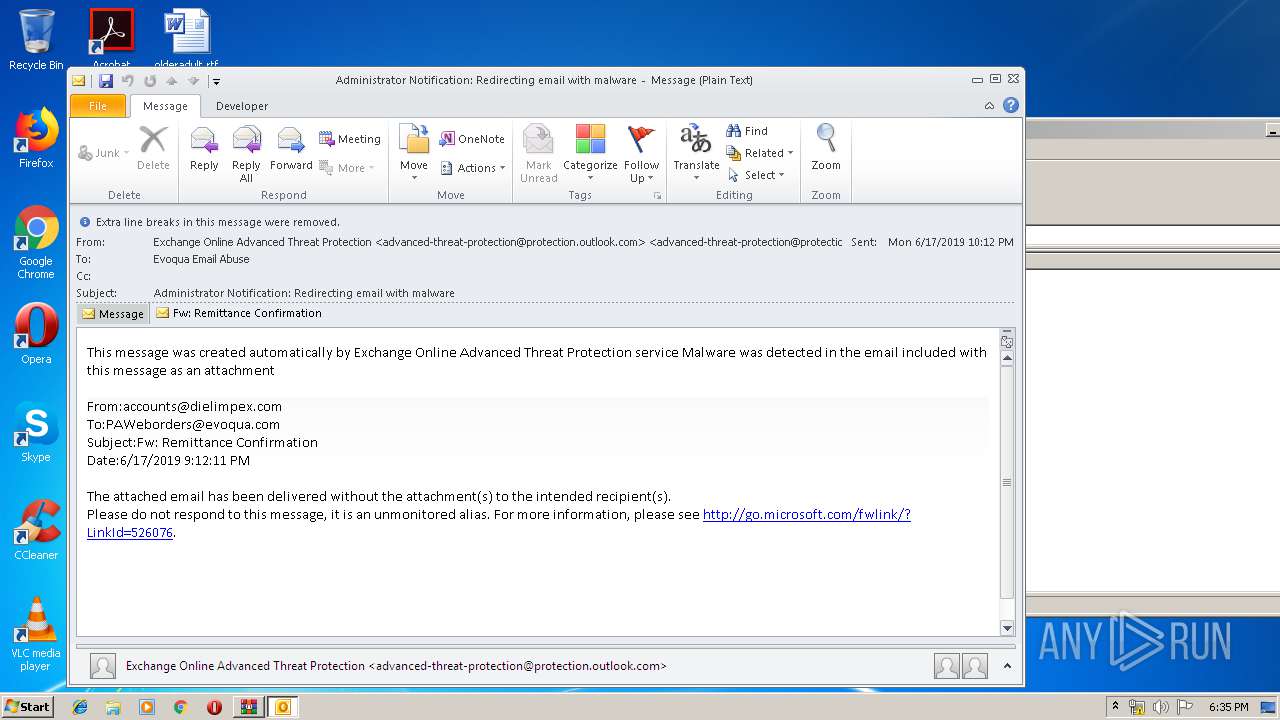
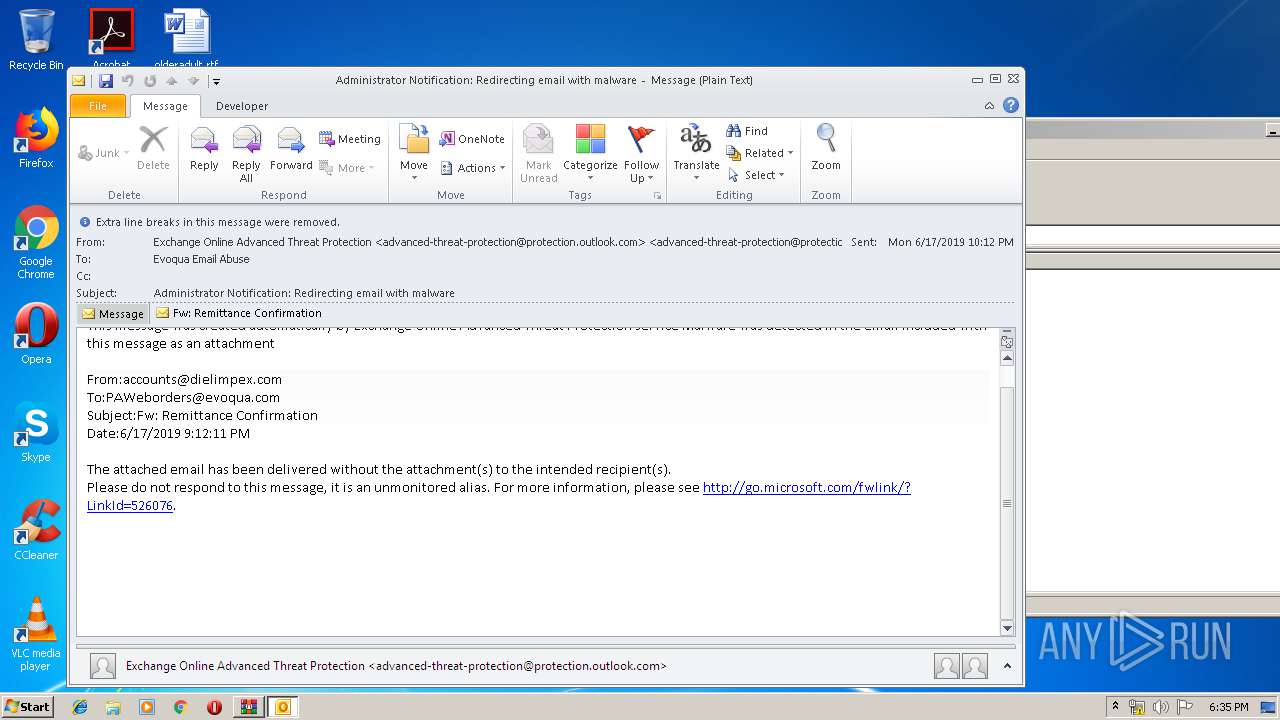
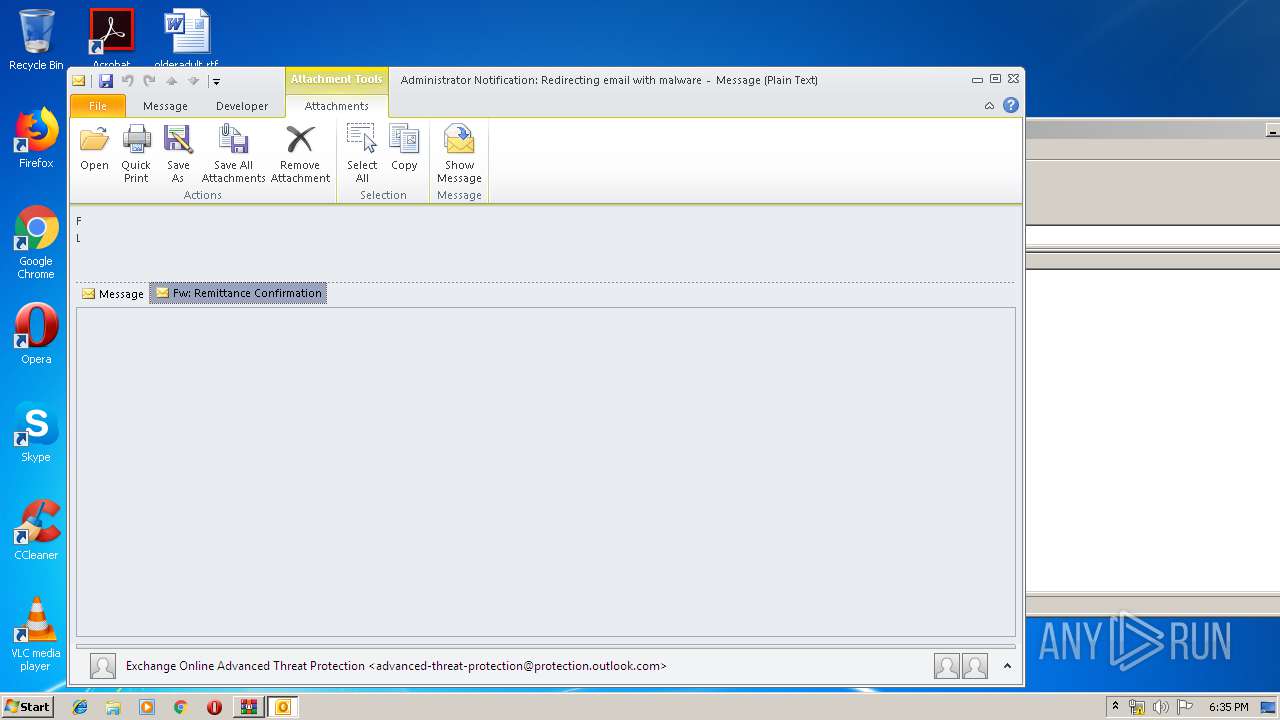
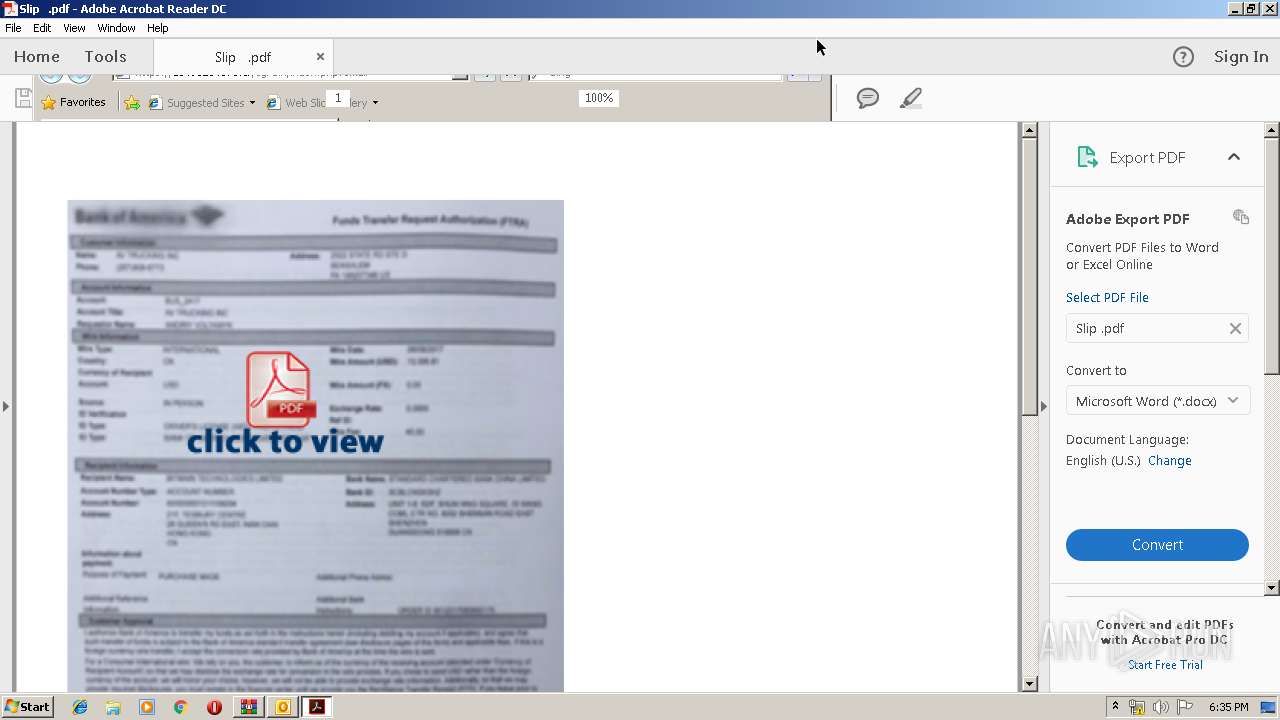
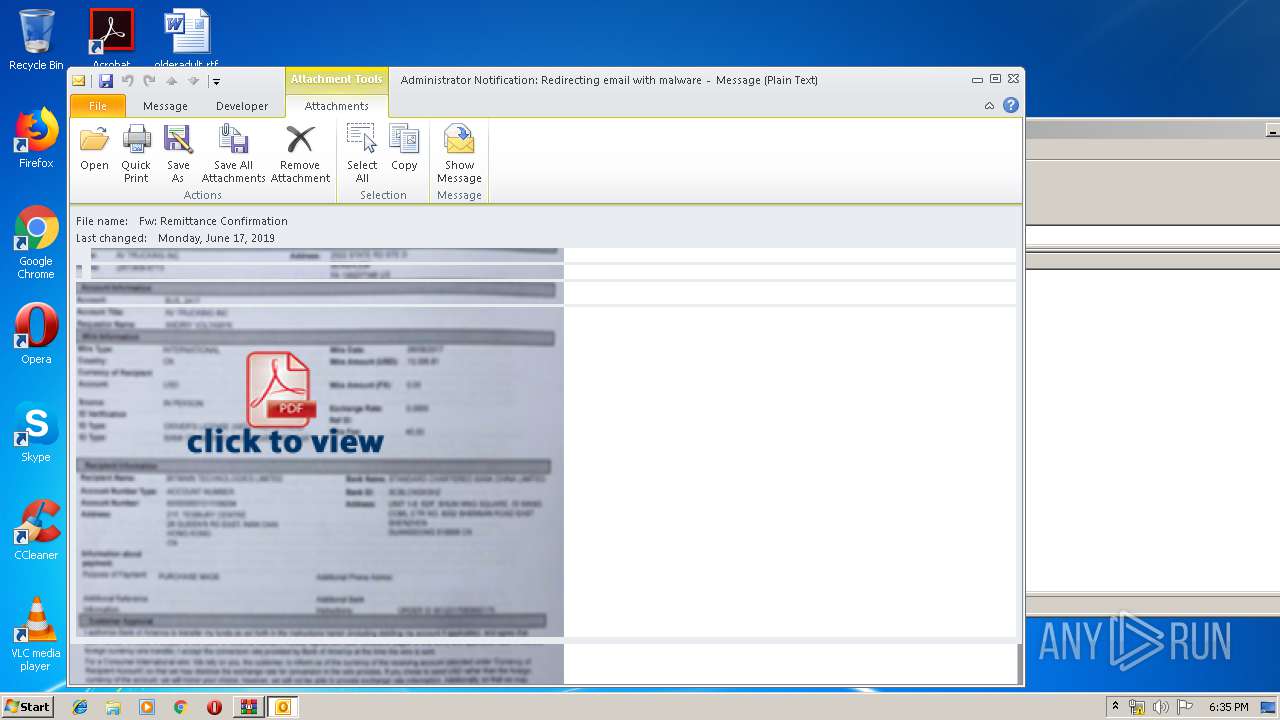
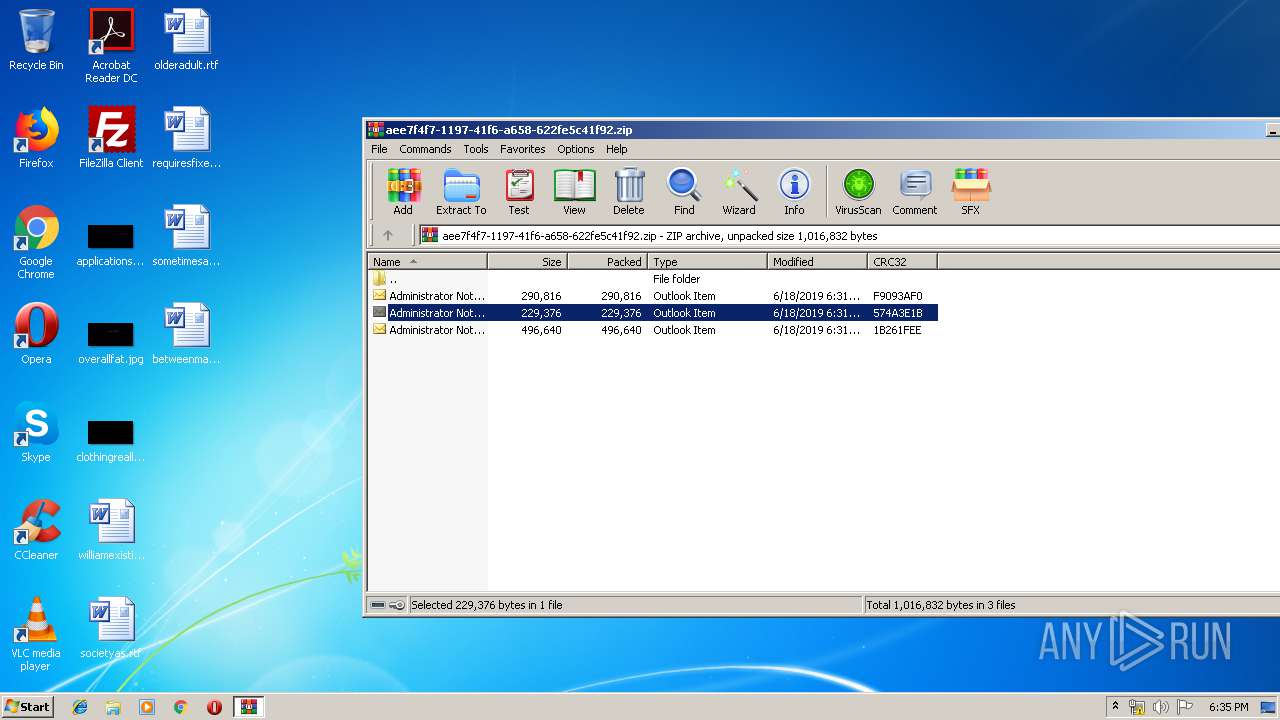
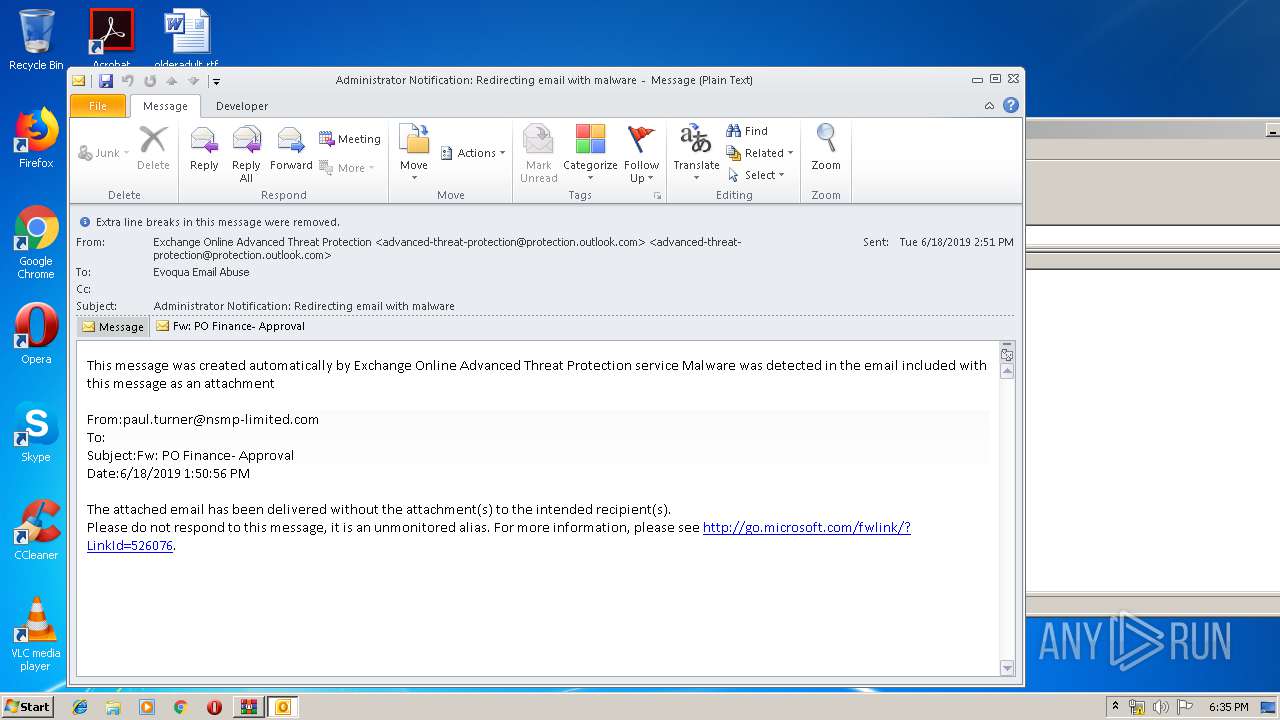
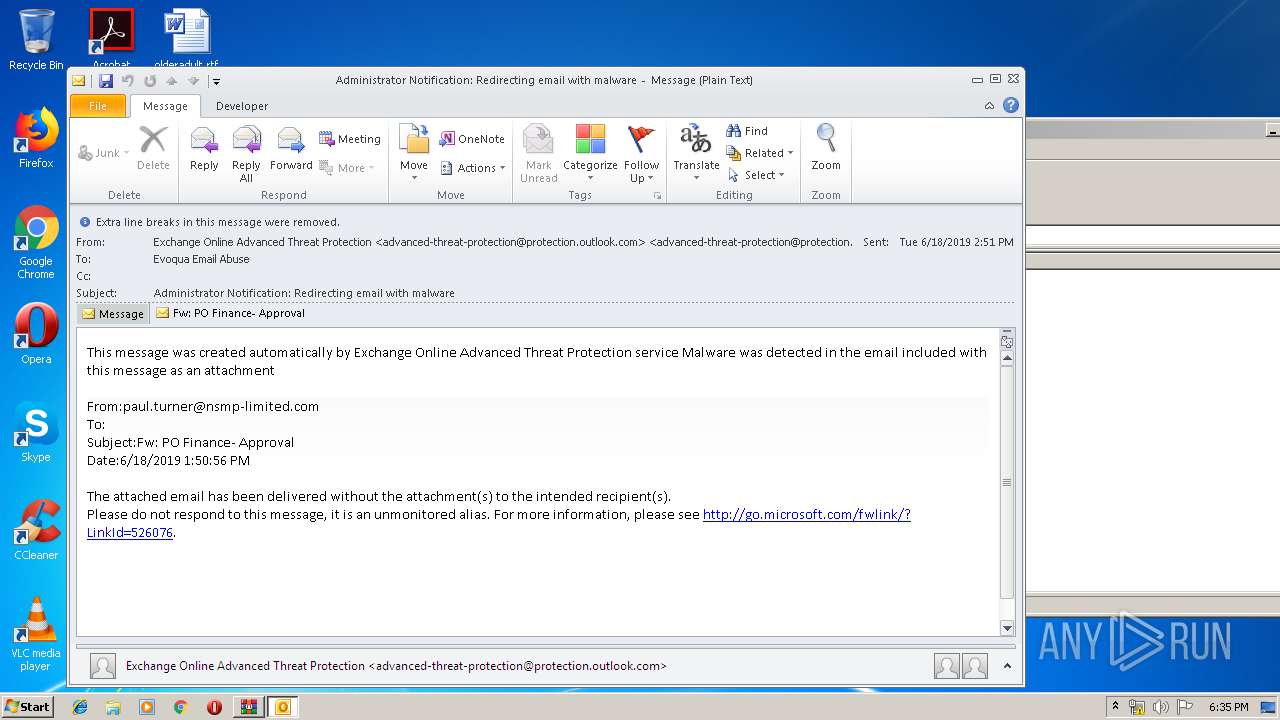
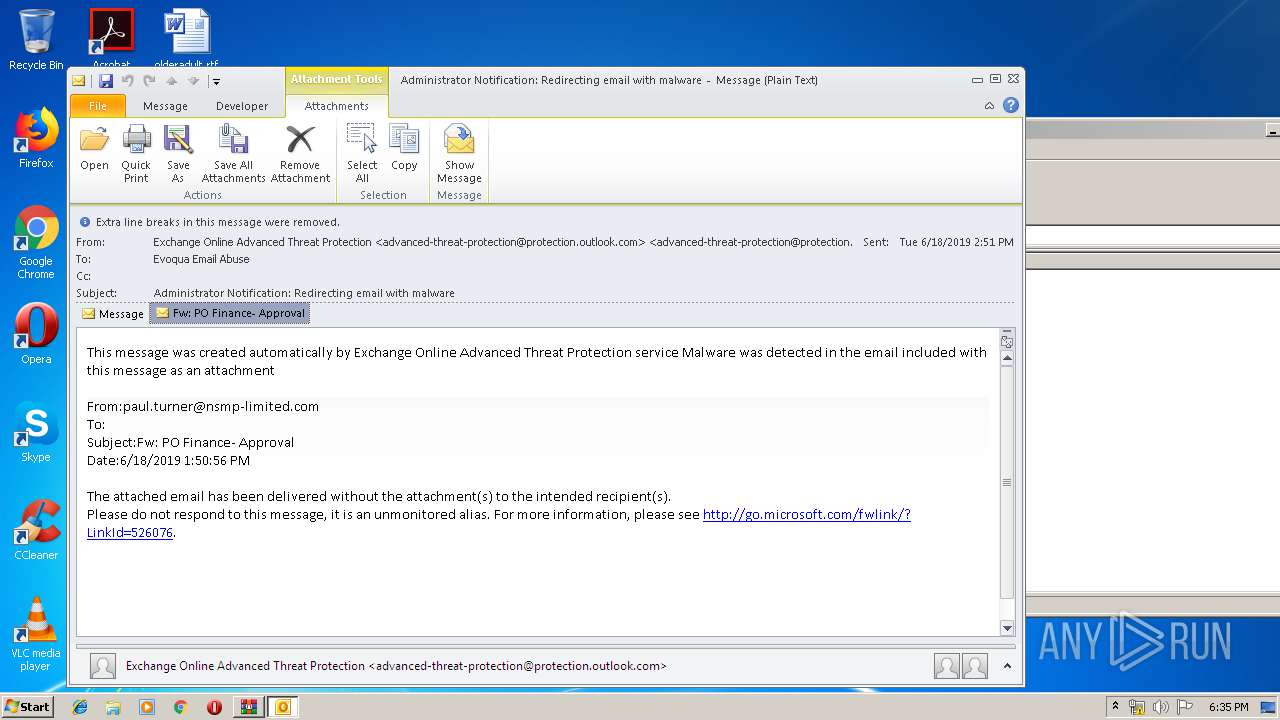
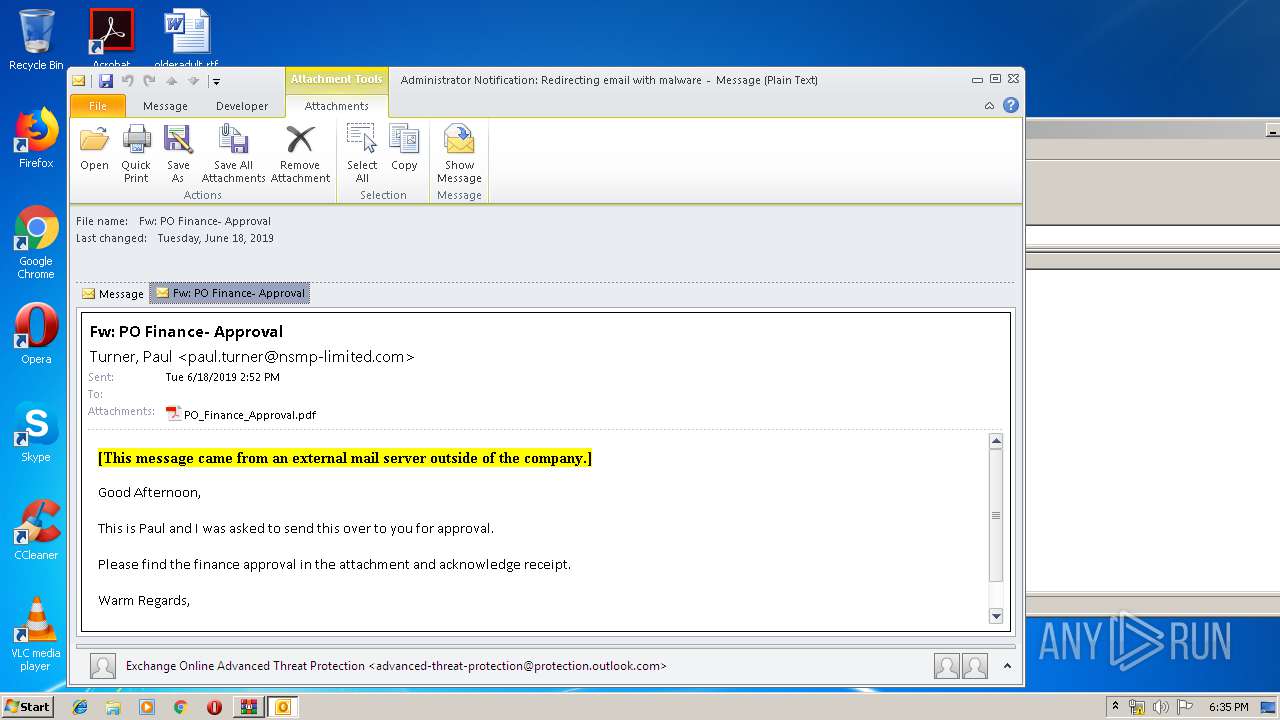
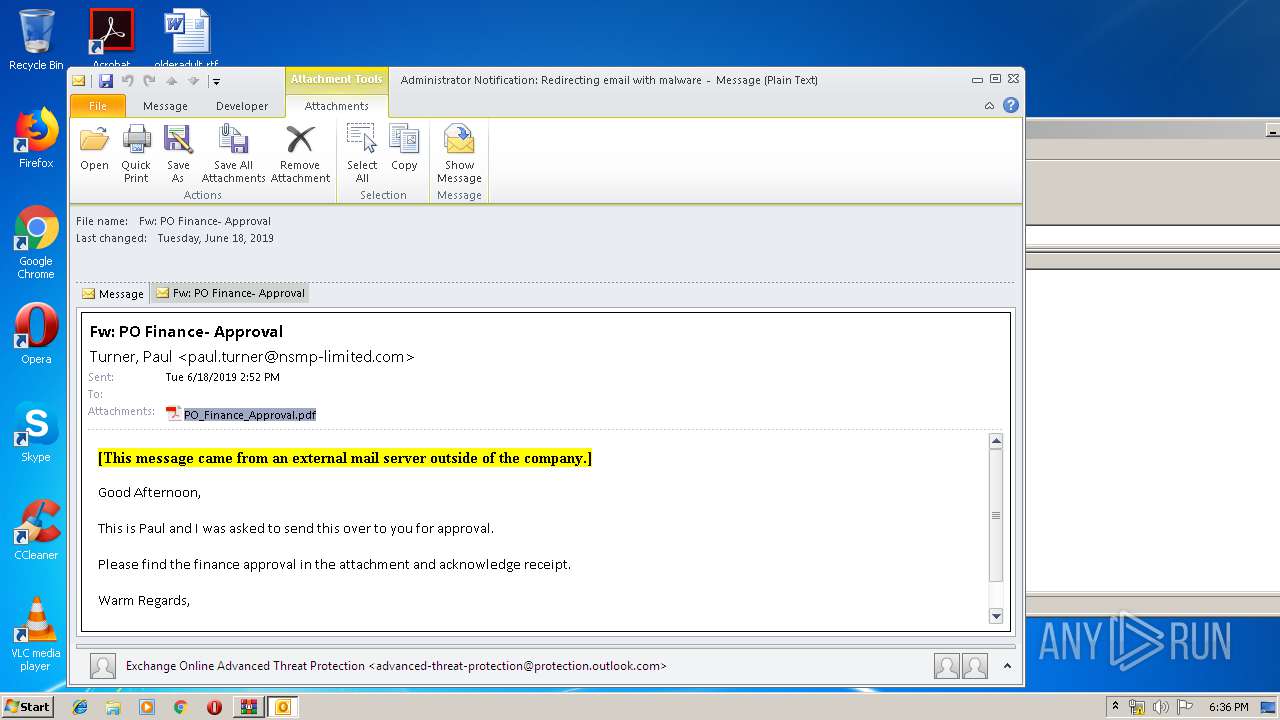
| ZipFileName: | Administrator Notification_ Redirecting email with malware (1).msg |
Total processes
62
Monitored processes
25
Malicious processes
8
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 584 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | AcroRd32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1136 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | AcroRd32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1160 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --disable-3d-apis --disable-databases --disable-direct-npapi-requests --disable-file-system --disable-notifications --disable-shared-workers --disable-direct-write --lang=en-US --lang=en-US --log-severity=disable --product-version="ReaderServices/15.23.20053 Chrome/45.0.2454.85" --device-scale-factor=1 --enable-delegated-renderer --num-raster-threads=2 --gpu-rasterization-msaa-sample-count=8 --content-image-texture-target=3553 --video-image-texture-target=3553 --disable-accelerated-video-decode --disable-webrtc-hw-encoding --disable-gpu-compositing --channel="3316.0.656816857\1584557771" --allow-no-sandbox-job /prefetch:673131151 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 1380 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 1652 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Rar$DIa3660.33854\Administrator Notification_ Redirecting email with malware.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 1812 | "C:\Program Files\Common Files\Adobe\ARM\1.0\AdobeARM.exe" /PRODUCT:Reader /VERSION:15.0 /MODE:3 | C:\Program Files\Common Files\Adobe\ARM\1.0\AdobeARM.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Reader and Acrobat Manager Exit code: 0 Version: 1.824.27.2646 Modules
| |||||||||||||||
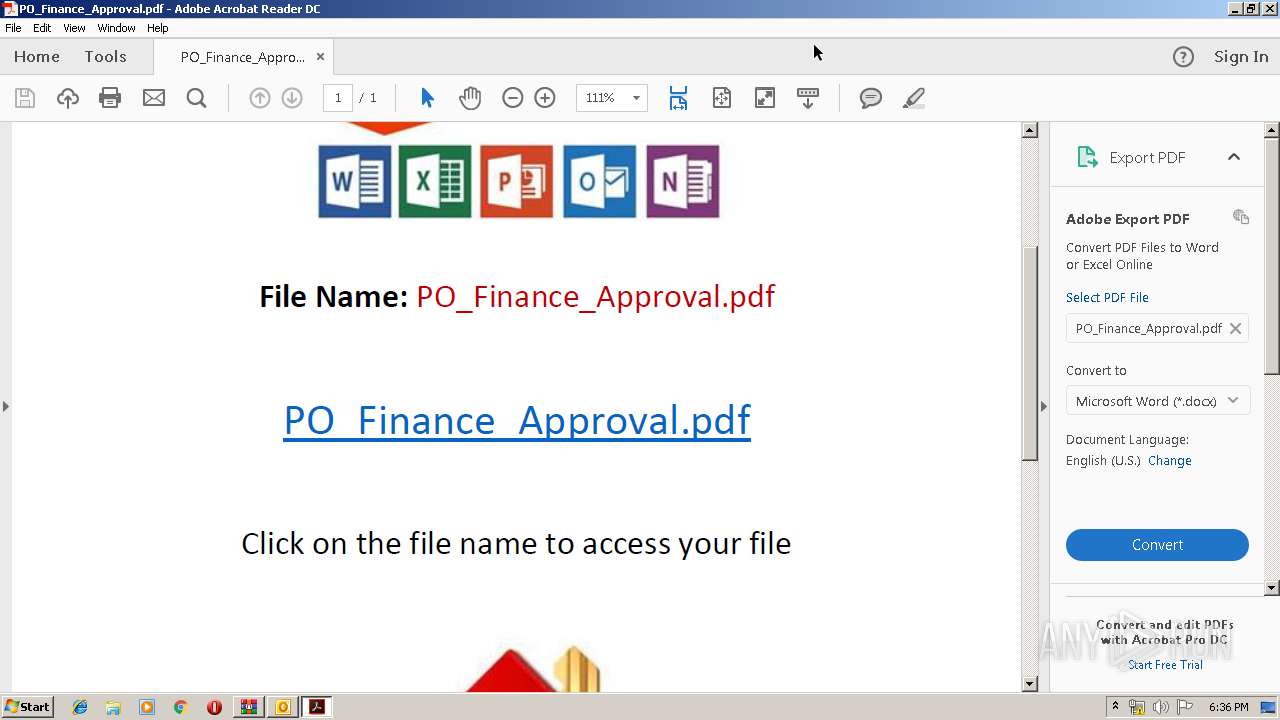
| 1892 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\8YD2N4IR\PO_Finance_Approval.pdf" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Reader DC Exit code: 1 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 2212 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Rar$DIa3660.30049\Administrator Notification_ Redirecting email with malware (2).msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2244 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --disable-3d-apis --disable-databases --disable-direct-npapi-requests --disable-file-system --disable-notifications --disable-shared-workers --disable-direct-write --lang=en-US --lang=en-US --log-severity=disable --product-version="ReaderServices/15.23.20053 Chrome/45.0.2454.85" --device-scale-factor=1 --enable-delegated-renderer --num-raster-threads=2 --gpu-rasterization-msaa-sample-count=8 --content-image-texture-target=3553 --video-image-texture-target=3553 --disable-accelerated-video-decode --disable-webrtc-hw-encoding --disable-gpu-compositing --channel="3316.1.864243416\27016460" --allow-no-sandbox-job /prefetch:673131151 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 2388 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\8YD2N4IR\Slip .pdf" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Reader DC Exit code: 1 Version: 15.23.20070.215641 Modules
| |||||||||||||||
Total events
7 179
Read events
5 732
Write events
1 375
Delete events
72
Modification events
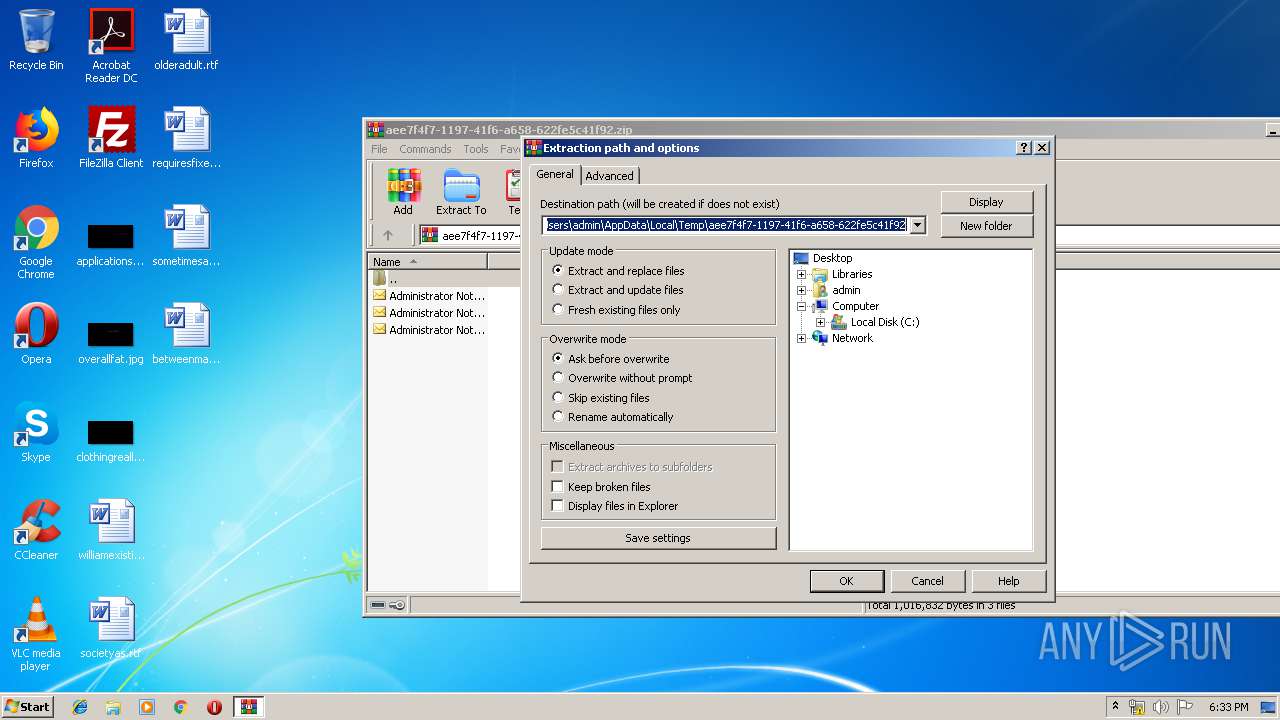
| (PID) Process: | (3660) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3660) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3660) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3660) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
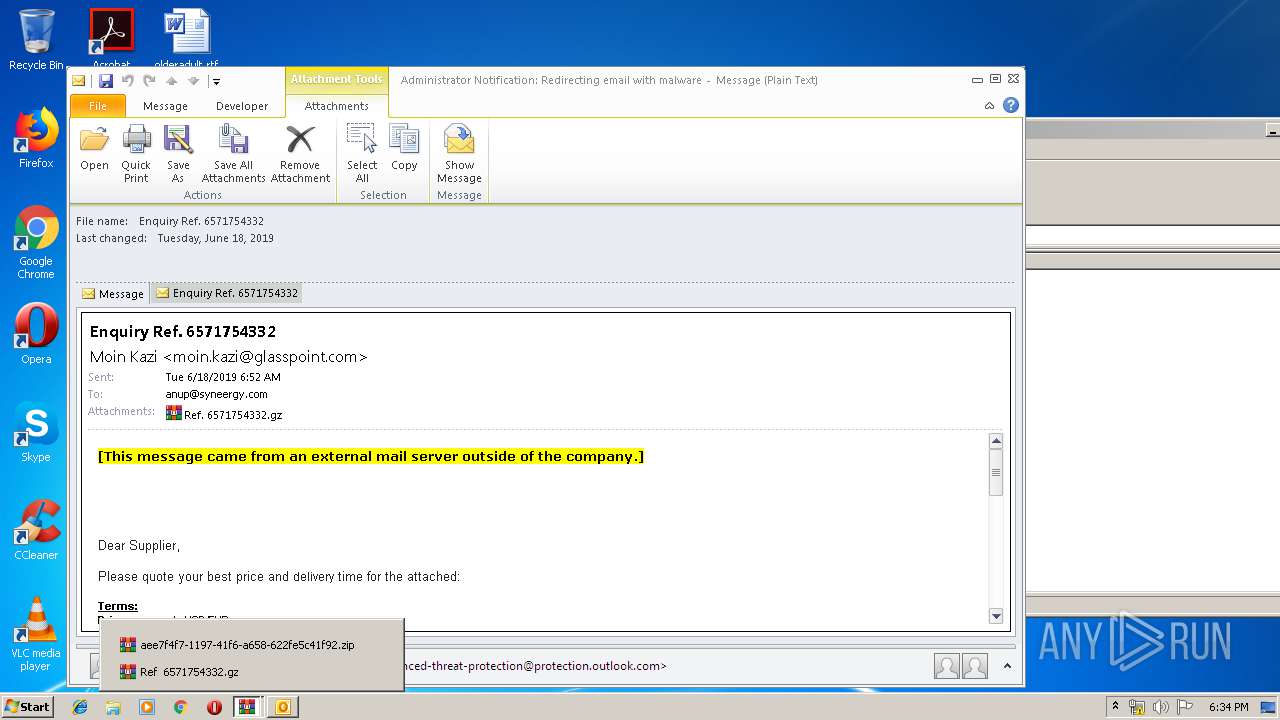
Value: C:\Users\admin\AppData\Local\Temp\aee7f4f7-1197-41f6-a658-622fe5c41f92.zip | |||
| (PID) Process: | (3660) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3660) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3660) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3660) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3660) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {0006F045-0000-0000-C000-000000000046} {000214FA-0000-0000-C000-000000000046} 0xFFFF |
Value: 01000000000000004C02AFD7FB25D501 | |||
| (PID) Process: | (3660) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {0006F045-0000-0000-C000-000000000046} {000214EB-0000-0000-C000-000000000046} 0xFFFF |
Value: 01000000000000005A29B6D7FB25D501 | |||
Executable files
2
Suspicious files
23
Text files
106
Unknown types
46
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2940 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRADEB.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2940 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DFE488C4DA0B13D4DC.TMP | — | |
MD5:— | SHA256:— | |||
| 1380 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR274.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2940 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\8YD2N4IR\Ref 6571754332 (2).gz\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3660 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\aee7f4f7-1197-41f6-a658-622fe5c41f92\Administrator Notification_ Redirecting email with malware (1).msg | msg | |
MD5:— | SHA256:— | |||
| 3660 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\aee7f4f7-1197-41f6-a658-622fe5c41f92\Administrator Notification_ Redirecting email with malware.msg | msg | |
MD5:— | SHA256:— | |||
| 2940 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3660 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\aee7f4f7-1197-41f6-a658-622fe5c41f92\Administrator Notification_ Redirecting email with malware (2).msg | msg | |
MD5:— | SHA256:— | |||
| 2940 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\8YD2N4IR\Ref 6571754332 (2).gz | compressed | |
MD5:— | SHA256:— | |||
| 2940 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\8YD2N4IR\Ref 6571754332.gz | compressed | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
35
TCP/UDP connections
32
DNS requests
13
Threats
26
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
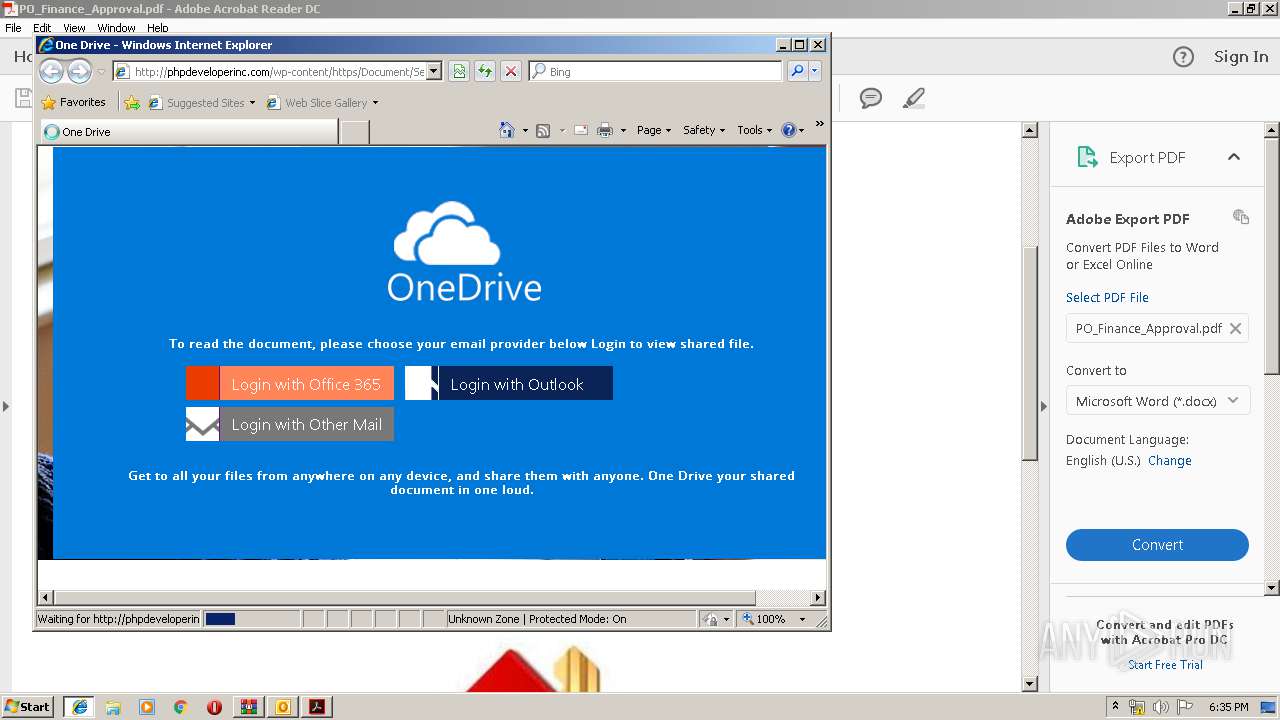
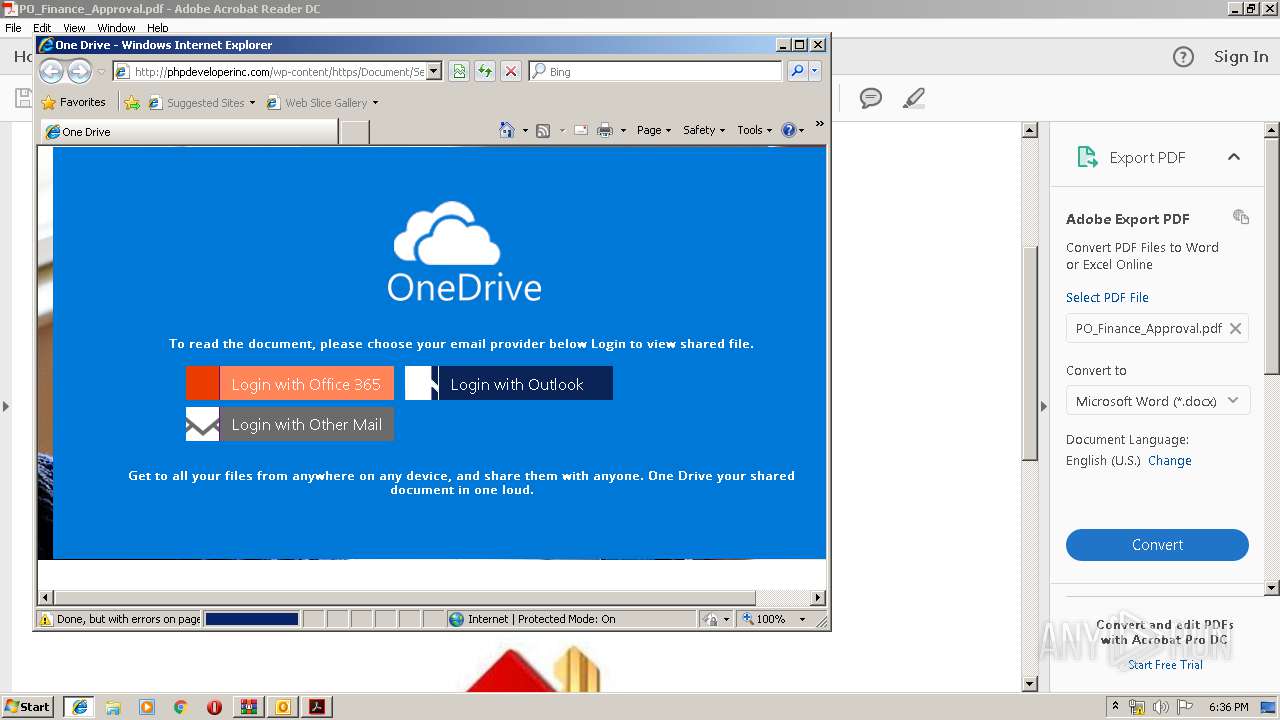
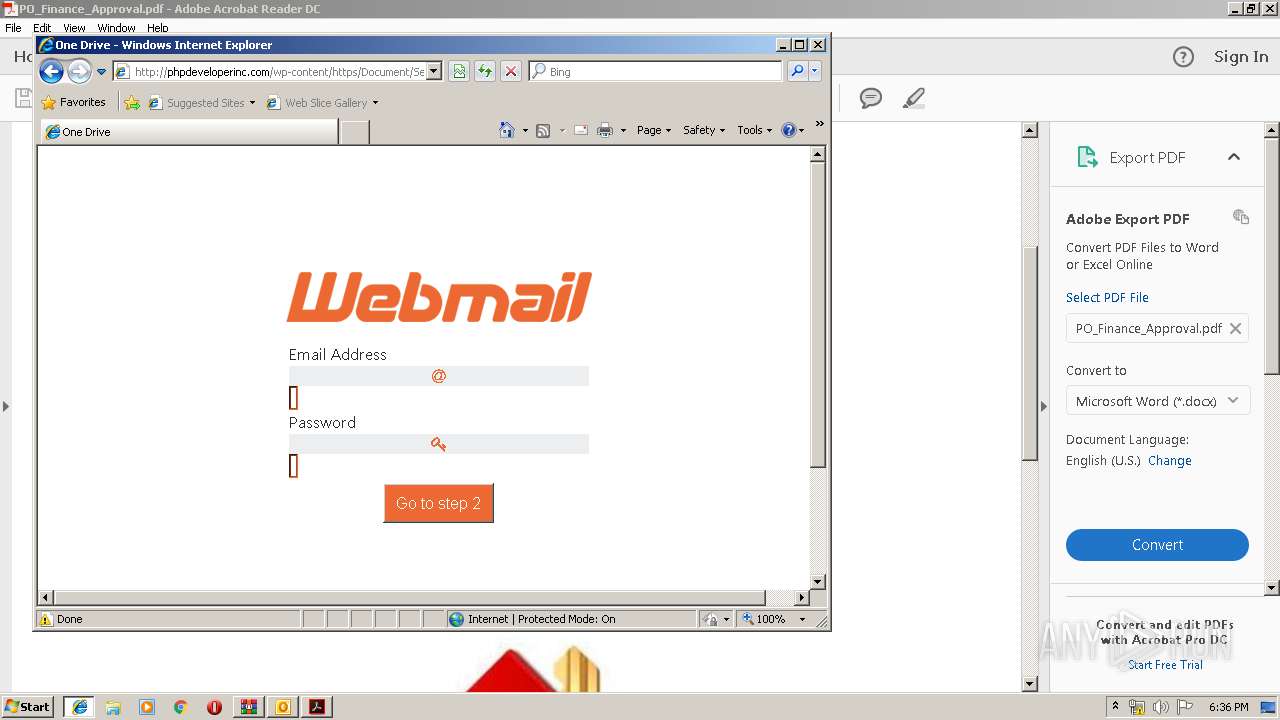
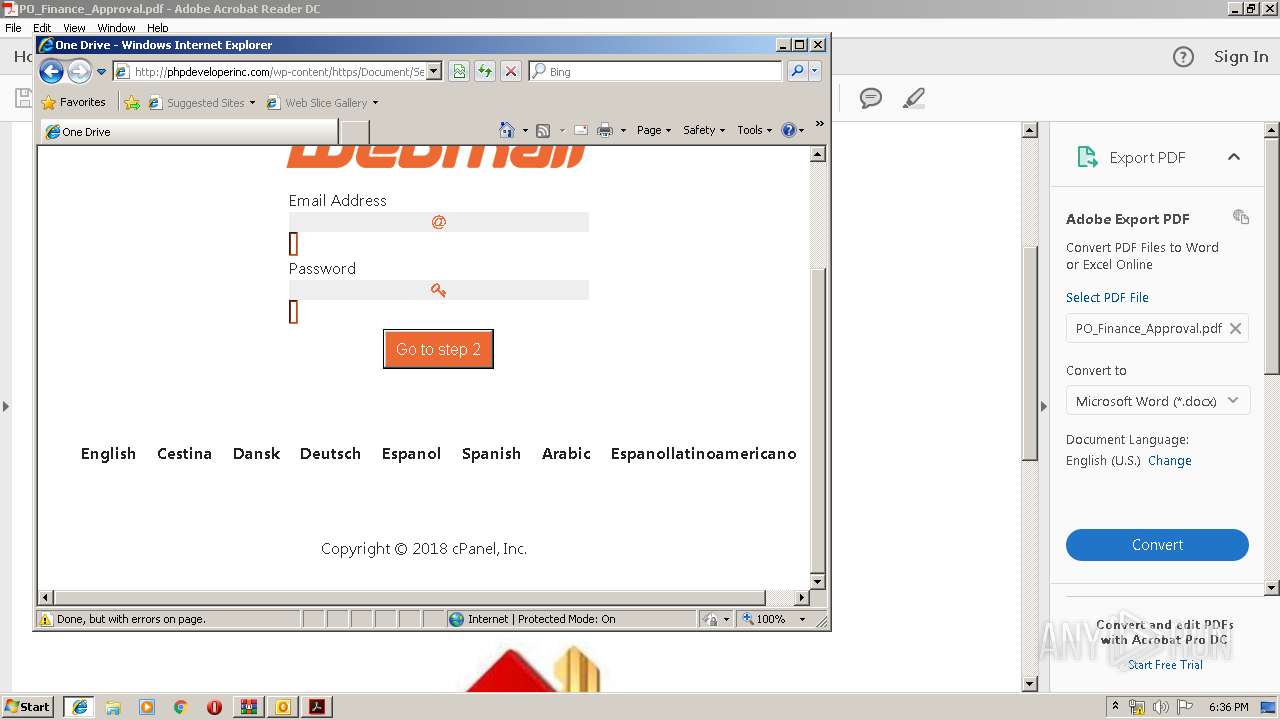
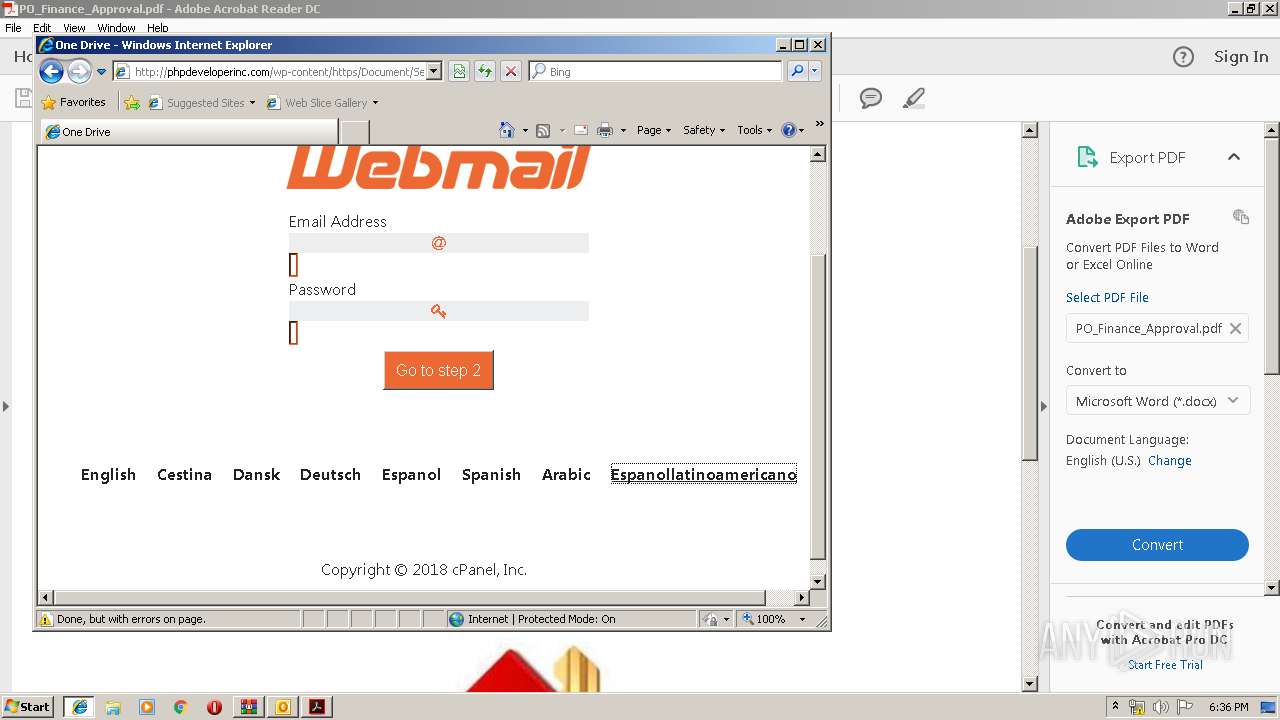
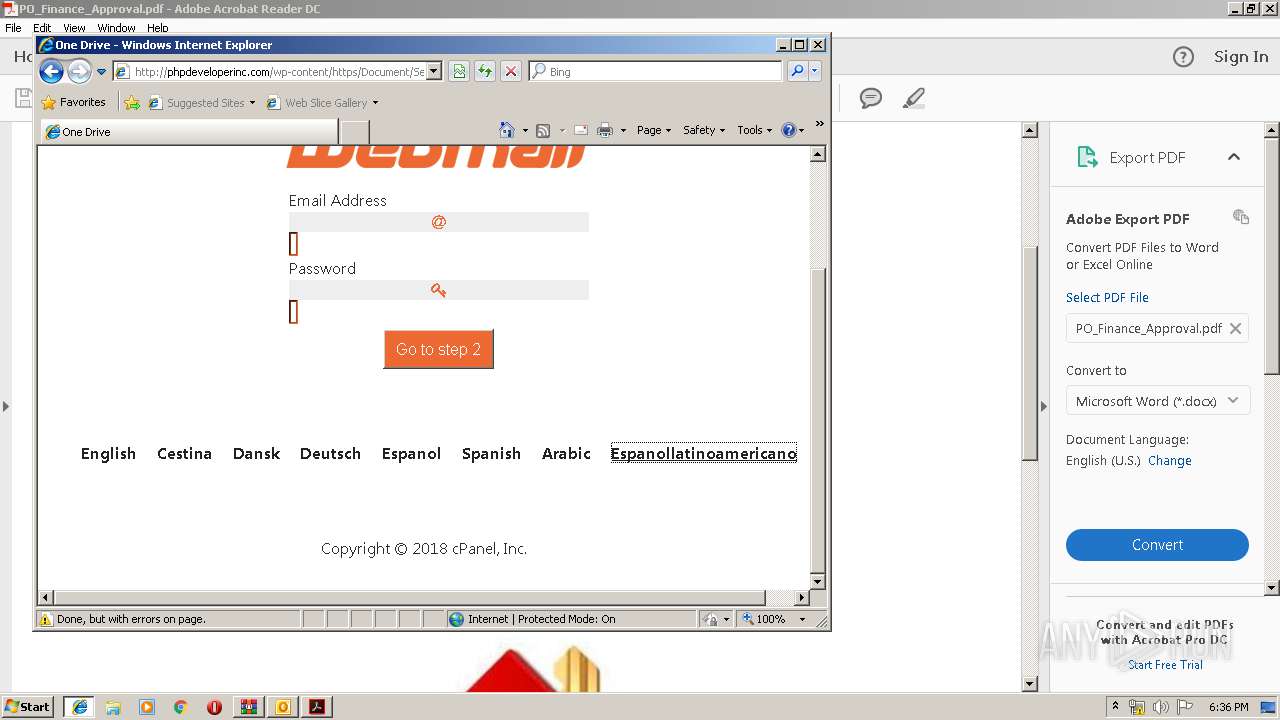
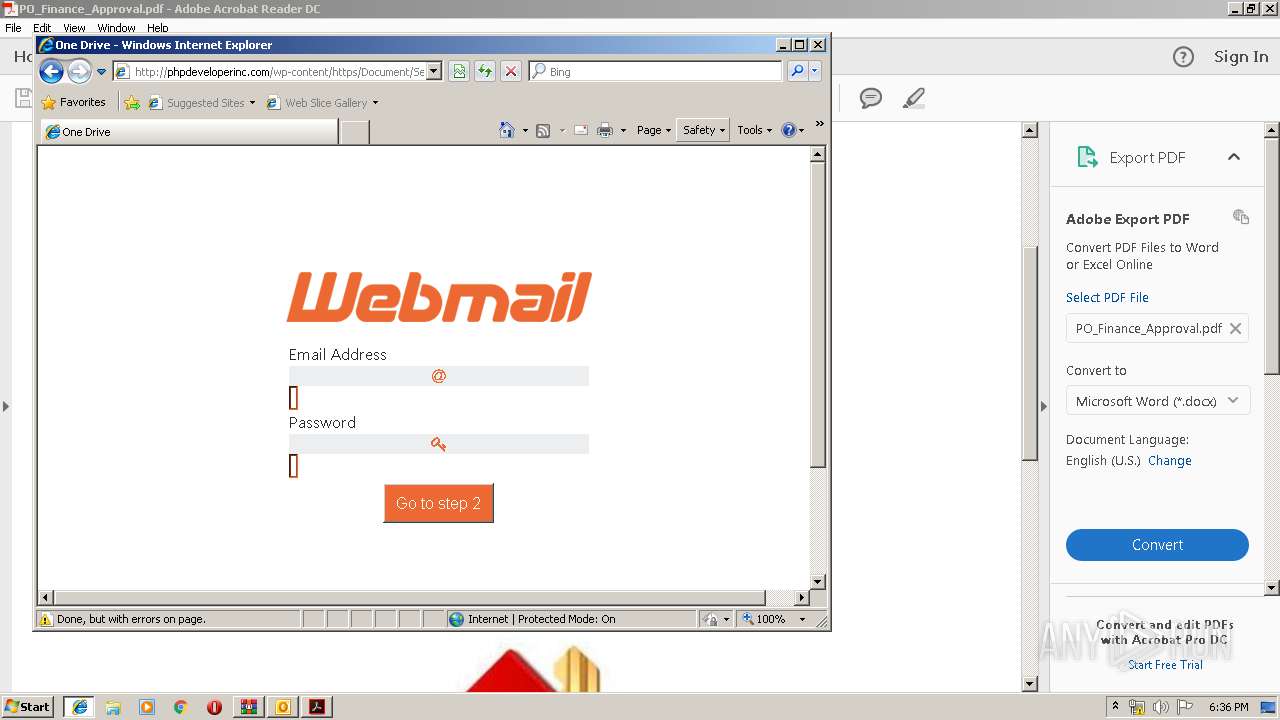
3616 | iexplore.exe | GET | — | 184.154.52.186:80 | http://phpdeveloperinc.com/wp-content/https/Document/Secure/Access/index_files/tether.min.js.download | US | — | — | malicious |
2940 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
2212 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
2388 | AcroRd32.exe | GET | 304 | 2.16.186.26:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/277_15_23_20070.zip | unknown | — | — | whitelisted |
3616 | iexplore.exe | GET | 200 | 184.154.52.186:80 | http://phpdeveloperinc.com/wp-content/https/Document/Secure/Access/ | US | html | 2.64 Kb | malicious |
3616 | iexplore.exe | GET | 200 | 184.154.52.186:80 | http://phpdeveloperinc.com/wp-content/https/Document/Secure/Access/index_files/style.css | US | text | 10.1 Kb | malicious |
3616 | iexplore.exe | GET | 200 | 184.154.52.186:80 | http://phpdeveloperinc.com/wp-content/https/Document/Secure/Access/index_files/jquery-3.1.1.slim.min.js.download | US | html | 52.4 Kb | malicious |
2604 | Ref. 6571754332.exe | POST | — | 149.255.62.61:80 | http://reyesfgt.org/jk/five/fre.php | GB | — | — | malicious |
2604 | Ref. 6571754332.exe | POST | — | 149.255.62.61:80 | http://reyesfgt.org/jk/five/fre.php | GB | — | — | malicious |
1652 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2940 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
2604 | Ref. 6571754332.exe | 149.255.62.61:80 | reyesfgt.org | Awareness Software Limited | GB | malicious |
2212 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
1136 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2676 | iexplore.exe | 67.220.188.162:443 | u8490214678.cf | 24 SHELLS | US | malicious |
2388 | AcroRd32.exe | 2.16.186.26:80 | acroipm2.adobe.com | Akamai International B.V. | — | whitelisted |
2388 | AcroRd32.exe | 2.18.233.74:443 | armmf.adobe.com | Akamai International B.V. | — | whitelisted |
1652 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
584 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3616 | iexplore.exe | 184.154.52.186:80 | phpdeveloperinc.com | SingleHop, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
reyesfgt.org |
| malicious |
www.bing.com |
| whitelisted |
u8490214678.cf |
| suspicious |
acroipm2.adobe.com |
| whitelisted |
armmf.adobe.com |
| whitelisted |
phpdeveloperinc.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
maxcdn.bootstrapcdn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2604 | Ref. 6571754332.exe | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
2604 | Ref. 6571754332.exe | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
2604 | Ref. 6571754332.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M1 |
2604 | Ref. 6571754332.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M2 |
2604 | Ref. 6571754332.exe | A Network Trojan was detected | MALWARE [PTsecurity] Loki Bot Check-in M2 |
2604 | Ref. 6571754332.exe | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
2604 | Ref. 6571754332.exe | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
2604 | Ref. 6571754332.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M1 |
2604 | Ref. 6571754332.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M2 |
2604 | Ref. 6571754332.exe | A Network Trojan was detected | MALWARE [PTsecurity] Loki Bot Check-in M2 |
4 ETPRO signatures available at the full report