| File name: | file |
| Full analysis: | https://app.any.run/tasks/0bc3f3a4-be0d-44c1-b236-b91106e6c4ff |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | December 14, 2024, 07:53:44 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | EC7B05F32FD59CA03E74B81122E281E1 |
| SHA1: | EEE35A743247328EC1A72D86D7EF88F28052F07F |
| SHA256: | F638D07D2ED9CA3C918BBEEF9D93B67B6409E8A174F516AFA184019D7C94DE58 |
| SSDEEP: | 98304:8jhw3pxhbz+N4wzBhn1Ua81jVDyA37HqmwjnFrC8rL2zoanO6PsHapMytN+v2Sms: |
MALICIOUS
Connects to the CnC server
- skotes.exe (PID: 6504)
- 8401ae77a5.exe (PID: 2072)
- svchost.exe (PID: 2192)
AMADEY has been detected (SURICATA)
- skotes.exe (PID: 6504)
Executing a file with an untrusted certificate
- 8fefc93b27.exe (PID: 6312)
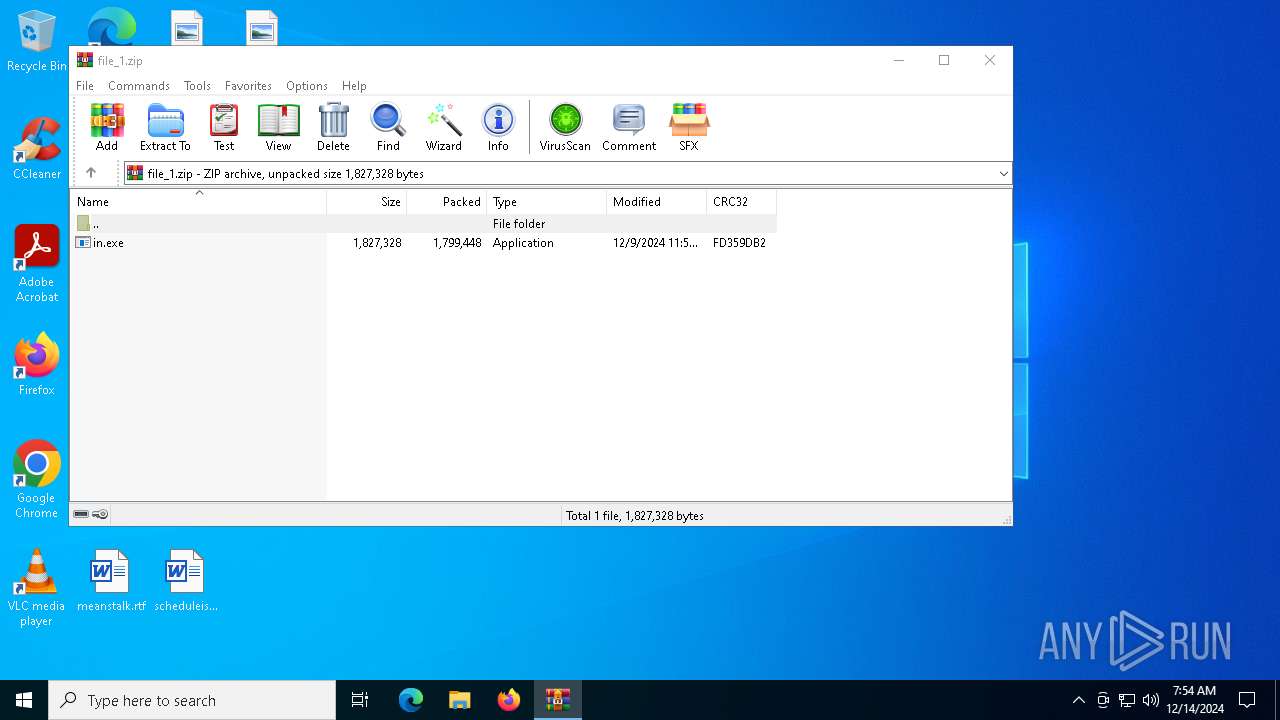
Uses Task Scheduler to run other applications
- in.exe (PID: 6328)
- in.exe (PID: 7600)
Steals credentials from Web Browsers
- 119596a2d6.exe (PID: 6916)
- 0abb235425.exe (PID: 6936)
- 8401ae77a5.exe (PID: 2072)
- 248def5026.exe (PID: 2928)
VIDAR mutex has been found
- 0abb235425.exe (PID: 6936)
Actions looks like stealing of personal data
- 119596a2d6.exe (PID: 6916)
- 0abb235425.exe (PID: 6936)
- 8401ae77a5.exe (PID: 2072)
- 248def5026.exe (PID: 2928)
Changes the autorun value in the registry
- skotes.exe (PID: 6504)
Possible tool for stealing has been detected
- 7ba4a48b63.exe (PID: 1684)
- firefox.exe (PID: 2216)
StealC has been detected
- 8401ae77a5.exe (PID: 2072)
STEALC has been detected (SURICATA)
- 8401ae77a5.exe (PID: 2072)
LUMMA has been found (auto)
- skotes.exe (PID: 6504)
AMADEY has been detected (YARA)
- skotes.exe (PID: 6504)
LUMMA mutex has been found
- 119596a2d6.exe (PID: 6916)
- 248def5026.exe (PID: 2928)
LUMMA has been detected (SURICATA)
- 248def5026.exe (PID: 2928)
- svchost.exe (PID: 2192)
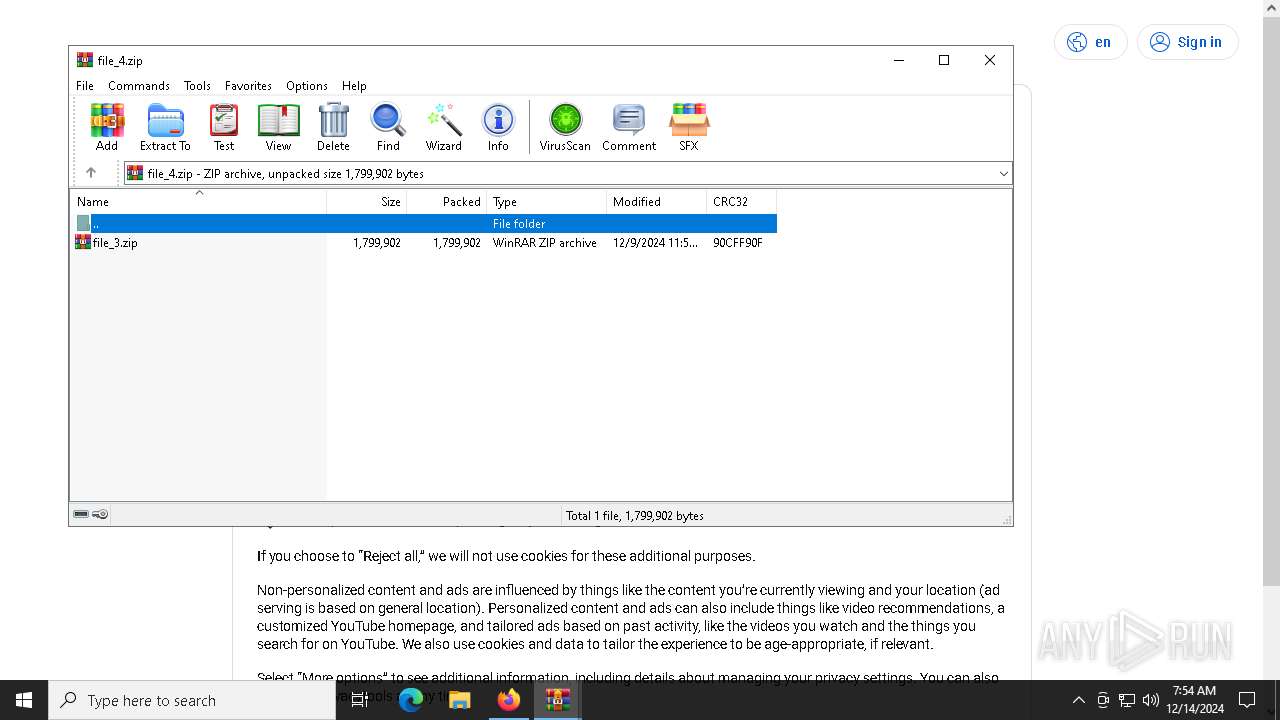
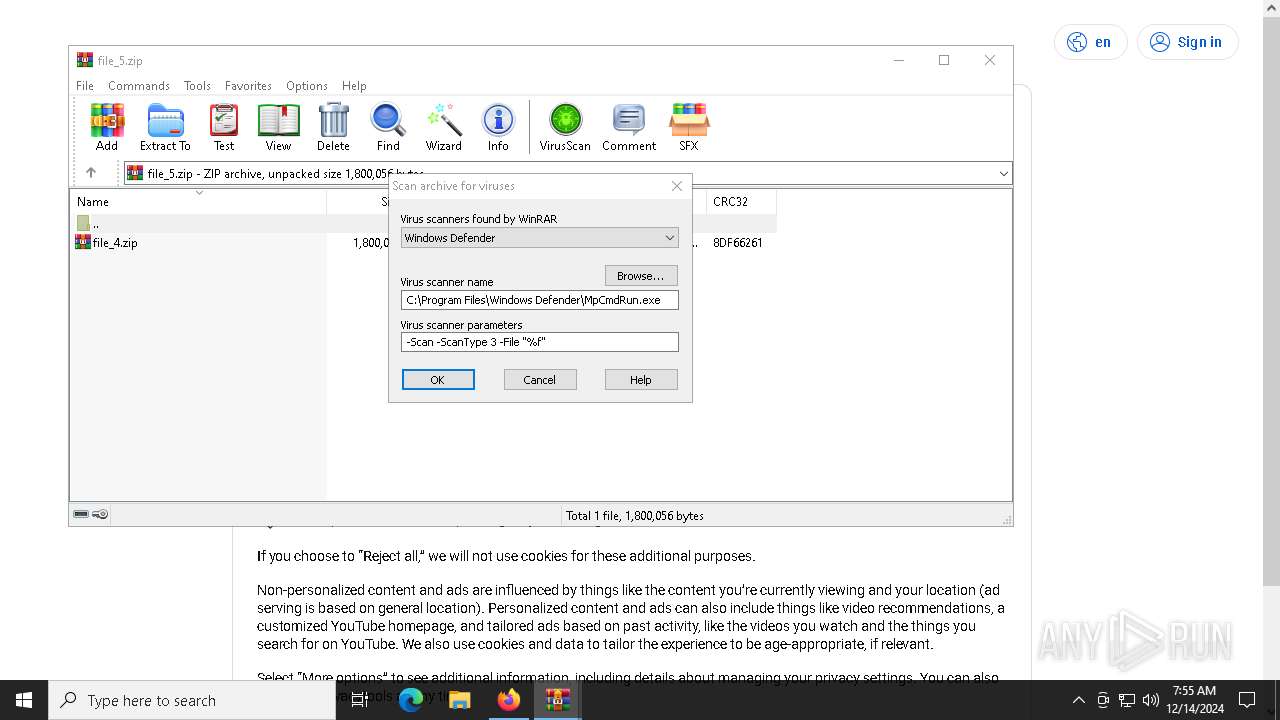
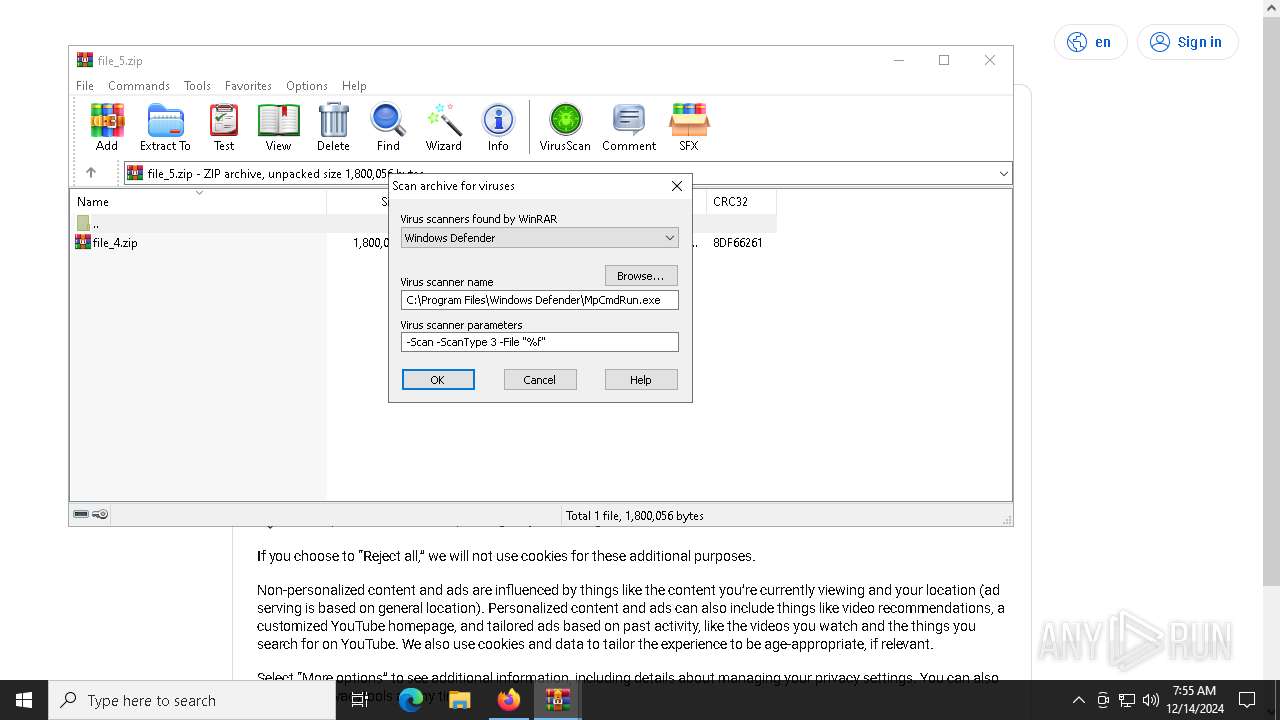
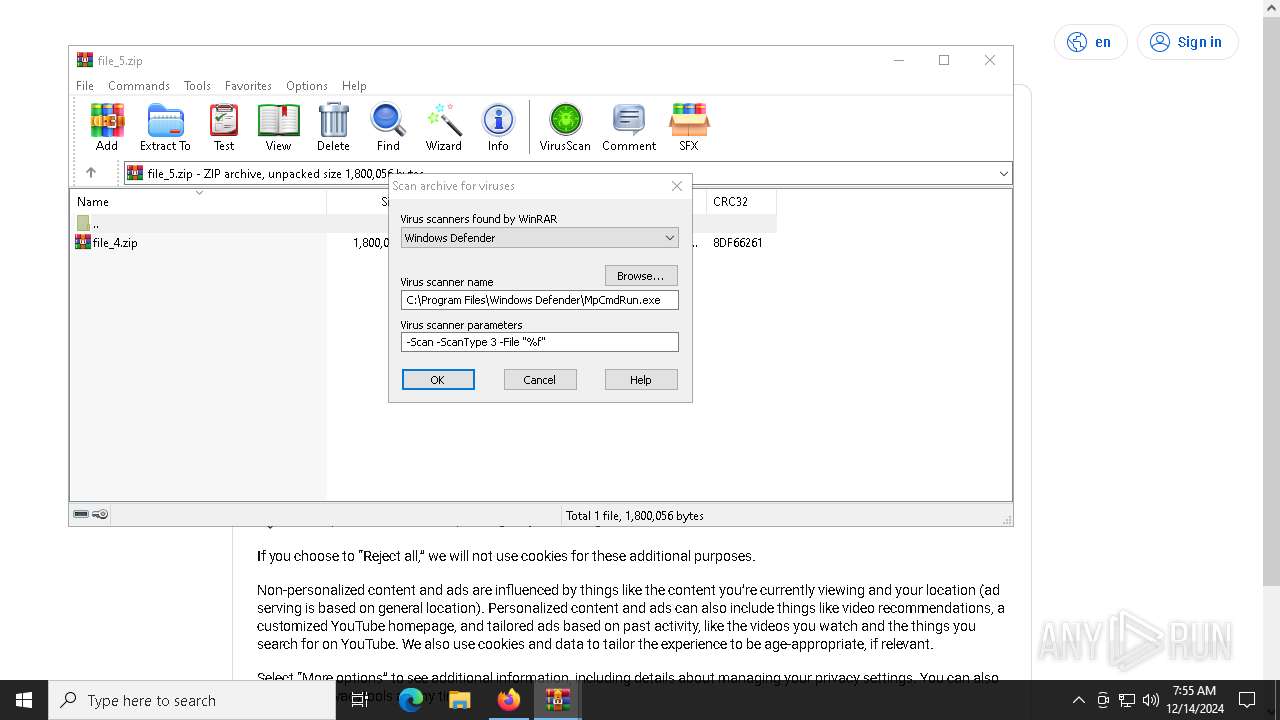
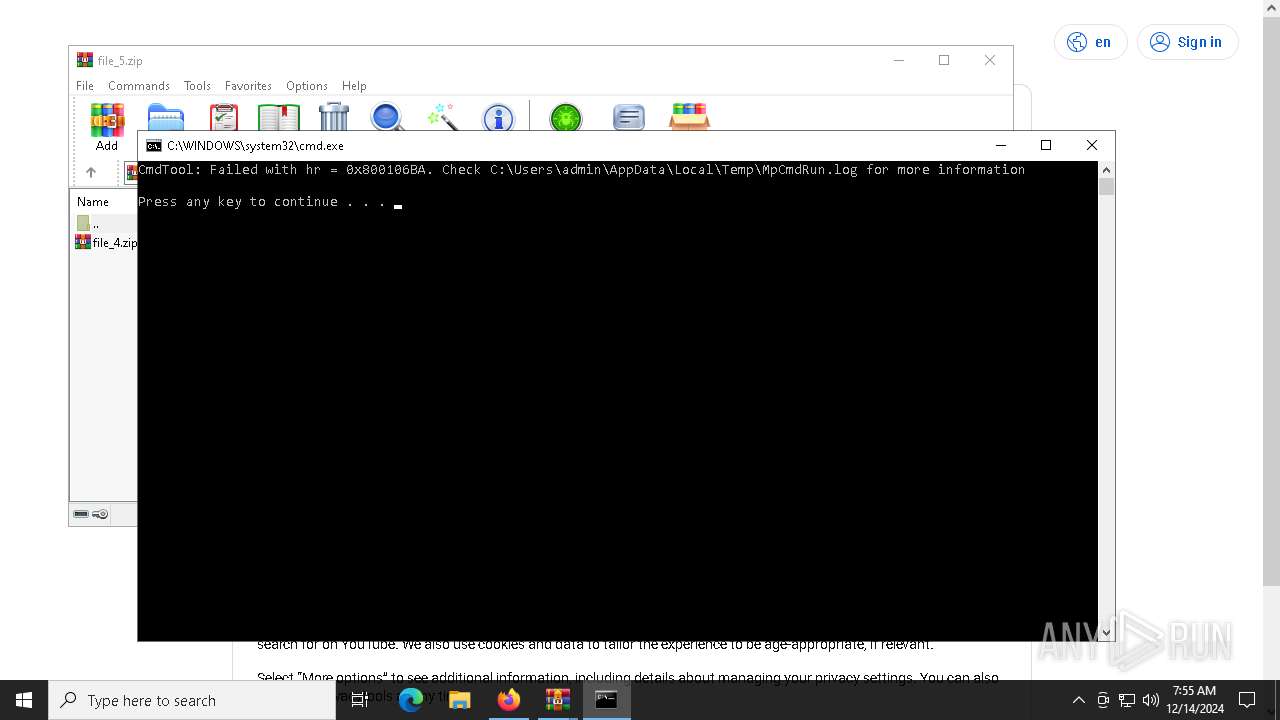
Antivirus name has been found in the command line (generic signature)
- MpCmdRun.exe (PID: 4556)
SUSPICIOUS
Reads the BIOS version
- file.exe (PID: 6316)
- skotes.exe (PID: 6504)
- skotes.exe (PID: 6208)
- 8401ae77a5.exe (PID: 2072)
- e65a0212bf.exe (PID: 7992)
- FHCBGIIJKE.exe (PID: 9380)
- skotes.exe (PID: 7996)
Reads security settings of Internet Explorer
- file.exe (PID: 6316)
- 8fefc93b27.exe (PID: 6312)
- skotes.exe (PID: 6504)
- 0abb235425.exe (PID: 6936)
- 8401ae77a5.exe (PID: 2072)
- WinRAR.exe (PID: 9840)
Executable content was dropped or overwritten
- file.exe (PID: 6316)
- skotes.exe (PID: 6504)
- 8fefc93b27.exe (PID: 6312)
- cmd.exe (PID: 5992)
- 7z.exe (PID: 644)
- in.exe (PID: 6328)
- 8401ae77a5.exe (PID: 2072)
Starts itself from another location
- file.exe (PID: 6316)
Contacting a server suspected of hosting an CnC
- skotes.exe (PID: 6504)
- 8401ae77a5.exe (PID: 2072)
- 248def5026.exe (PID: 2928)
- svchost.exe (PID: 2192)
Process requests binary or script from the Internet
- skotes.exe (PID: 6504)
- 8401ae77a5.exe (PID: 2072)
Potential Corporate Privacy Violation
- skotes.exe (PID: 6504)
- 8401ae77a5.exe (PID: 2072)
The process executes via Task Scheduler
- skotes.exe (PID: 6208)
- skotes.exe (PID: 7996)
- Intel_PTT_EK_Recertification.exe (PID: 8244)
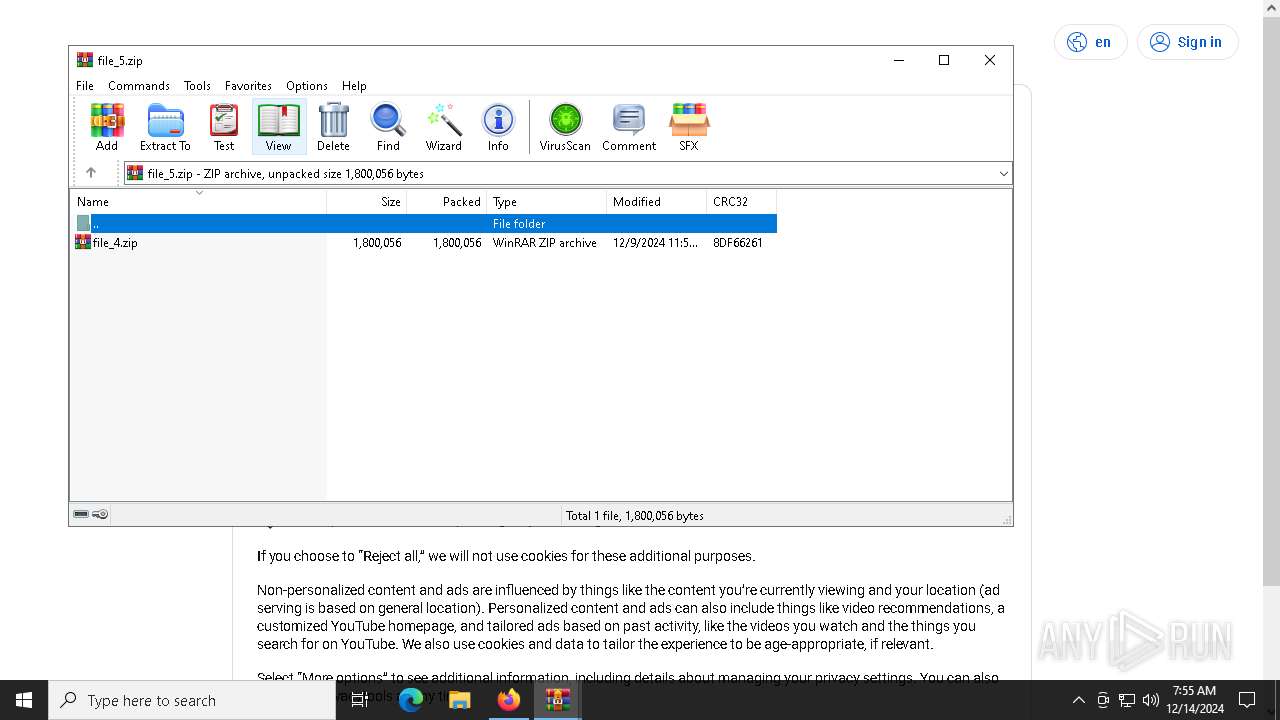
Drops 7-zip archiver for unpacking
- 8fefc93b27.exe (PID: 6312)
Starts CMD.EXE for commands execution
- 8fefc93b27.exe (PID: 6312)
- 8401ae77a5.exe (PID: 2072)
- 0abb235425.exe (PID: 6936)
- WinRAR.exe (PID: 9840)
The executable file from the user directory is run by the CMD process
- 7z.exe (PID: 4556)
- 7z.exe (PID: 624)
- 7z.exe (PID: 2928)
- 7z.exe (PID: 4468)
- 7z.exe (PID: 5576)
- 7z.exe (PID: 5080)
- 7z.exe (PID: 5236)
- 7z.exe (PID: 644)
- in.exe (PID: 6328)
- FHCBGIIJKE.exe (PID: 9380)
Executing commands from a ".bat" file
- 8fefc93b27.exe (PID: 6312)
- WinRAR.exe (PID: 9840)
Connects to the server without a host name
- skotes.exe (PID: 6504)
- 8401ae77a5.exe (PID: 2072)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 5992)
- in.exe (PID: 6328)
- in.exe (PID: 7600)
Starts POWERSHELL.EXE for commands execution
- in.exe (PID: 6328)
- in.exe (PID: 7600)
- Intel_PTT_EK_Recertification.exe (PID: 8244)
Found IP address in command line
- powershell.exe (PID: 6420)
- powershell.exe (PID: 7696)
- powershell.exe (PID: 8072)
Application launched itself
- 119596a2d6.exe (PID: 4388)
Checks Windows Trust Settings
- 0abb235425.exe (PID: 6936)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- 0abb235425.exe (PID: 6936)
Uses TASKKILL.EXE to kill Browsers
- 7ba4a48b63.exe (PID: 1684)
Searches for installed software
- 0abb235425.exe (PID: 6936)
- 8401ae77a5.exe (PID: 2072)
Uses TASKKILL.EXE to kill process
- 7ba4a48b63.exe (PID: 1684)
Windows Defender mutex has been found
- 8401ae77a5.exe (PID: 2072)
The process drops Mozilla's DLL files
- 8401ae77a5.exe (PID: 2072)
Process drops legitimate windows executable
- 8401ae77a5.exe (PID: 2072)
The process drops C-runtime libraries
- 8401ae77a5.exe (PID: 2072)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 10136)
Executes application which crashes
- 0abb235425.exe (PID: 6936)
INFO
Checks supported languages
- file.exe (PID: 6316)
- skotes.exe (PID: 6504)
- 8fefc93b27.exe (PID: 6312)
- skotes.exe (PID: 6208)
- 119596a2d6.exe (PID: 4388)
- mode.com (PID: 3988)
- 7z.exe (PID: 4556)
- 7z.exe (PID: 624)
- 7z.exe (PID: 2928)
- 7z.exe (PID: 4468)
- 7z.exe (PID: 5576)
- 7z.exe (PID: 5080)
- 7z.exe (PID: 5236)
- 7z.exe (PID: 644)
- in.exe (PID: 6328)
- 119596a2d6.exe (PID: 6916)
- 0abb235425.exe (PID: 6936)
- 7ba4a48b63.exe (PID: 1684)
- 8401ae77a5.exe (PID: 2072)
- in.exe (PID: 7600)
- e65a0212bf.exe (PID: 7992)
- 248def5026.exe (PID: 2928)
- FHCBGIIJKE.exe (PID: 9380)
- skotes.exe (PID: 7996)
- Intel_PTT_EK_Recertification.exe (PID: 8244)
- MpCmdRun.exe (PID: 4556)
Sends debugging messages
- file.exe (PID: 6316)
- skotes.exe (PID: 6504)
- skotes.exe (PID: 6208)
- 8401ae77a5.exe (PID: 2072)
- e65a0212bf.exe (PID: 7992)
- FHCBGIIJKE.exe (PID: 9380)
- skotes.exe (PID: 7996)
Create files in a temporary directory
- file.exe (PID: 6316)
- skotes.exe (PID: 6504)
- 8fefc93b27.exe (PID: 6312)
- 7z.exe (PID: 4556)
- 7z.exe (PID: 624)
- 7z.exe (PID: 2928)
- 7z.exe (PID: 4468)
- 7z.exe (PID: 5080)
- 7z.exe (PID: 5576)
- 7z.exe (PID: 5236)
- 7z.exe (PID: 644)
- MpCmdRun.exe (PID: 4556)
Reads the computer name
- file.exe (PID: 6316)
- skotes.exe (PID: 6504)
- 8fefc93b27.exe (PID: 6312)
- 7z.exe (PID: 4556)
- 7z.exe (PID: 624)
- 7z.exe (PID: 2928)
- 7z.exe (PID: 4468)
- 7z.exe (PID: 5080)
- 7z.exe (PID: 5576)
- 7z.exe (PID: 5236)
- 7z.exe (PID: 644)
- 119596a2d6.exe (PID: 6916)
- 0abb235425.exe (PID: 6936)
- 7ba4a48b63.exe (PID: 1684)
- 8401ae77a5.exe (PID: 2072)
- e65a0212bf.exe (PID: 7992)
- 248def5026.exe (PID: 2928)
- MpCmdRun.exe (PID: 4556)
The process uses the downloaded file
- file.exe (PID: 6316)
- skotes.exe (PID: 6504)
- 8fefc93b27.exe (PID: 6312)
- 0abb235425.exe (PID: 6936)
- 8401ae77a5.exe (PID: 2072)
- WinRAR.exe (PID: 9840)
Process checks computer location settings
- file.exe (PID: 6316)
- skotes.exe (PID: 6504)
- 8fefc93b27.exe (PID: 6312)
- 8401ae77a5.exe (PID: 2072)
- 0abb235425.exe (PID: 6936)
Checks proxy server information
- skotes.exe (PID: 6504)
- 0abb235425.exe (PID: 6936)
- 8401ae77a5.exe (PID: 2072)
- WerFault.exe (PID: 9220)
Creates files or folders in the user directory
- skotes.exe (PID: 6504)
- in.exe (PID: 6328)
- 0abb235425.exe (PID: 6936)
- 8401ae77a5.exe (PID: 2072)
- WerFault.exe (PID: 9220)
The sample compiled with english language support
- 8fefc93b27.exe (PID: 6312)
- skotes.exe (PID: 6504)
- 8401ae77a5.exe (PID: 2072)
Starts MODE.COM to configure console settings
- mode.com (PID: 3988)
Reads the software policy settings
- 119596a2d6.exe (PID: 6916)
- 0abb235425.exe (PID: 6936)
- 248def5026.exe (PID: 2928)
- WerFault.exe (PID: 9220)
Creates files in the program directory
- 0abb235425.exe (PID: 6936)
- 8401ae77a5.exe (PID: 2072)
Reads the machine GUID from the registry
- 0abb235425.exe (PID: 6936)
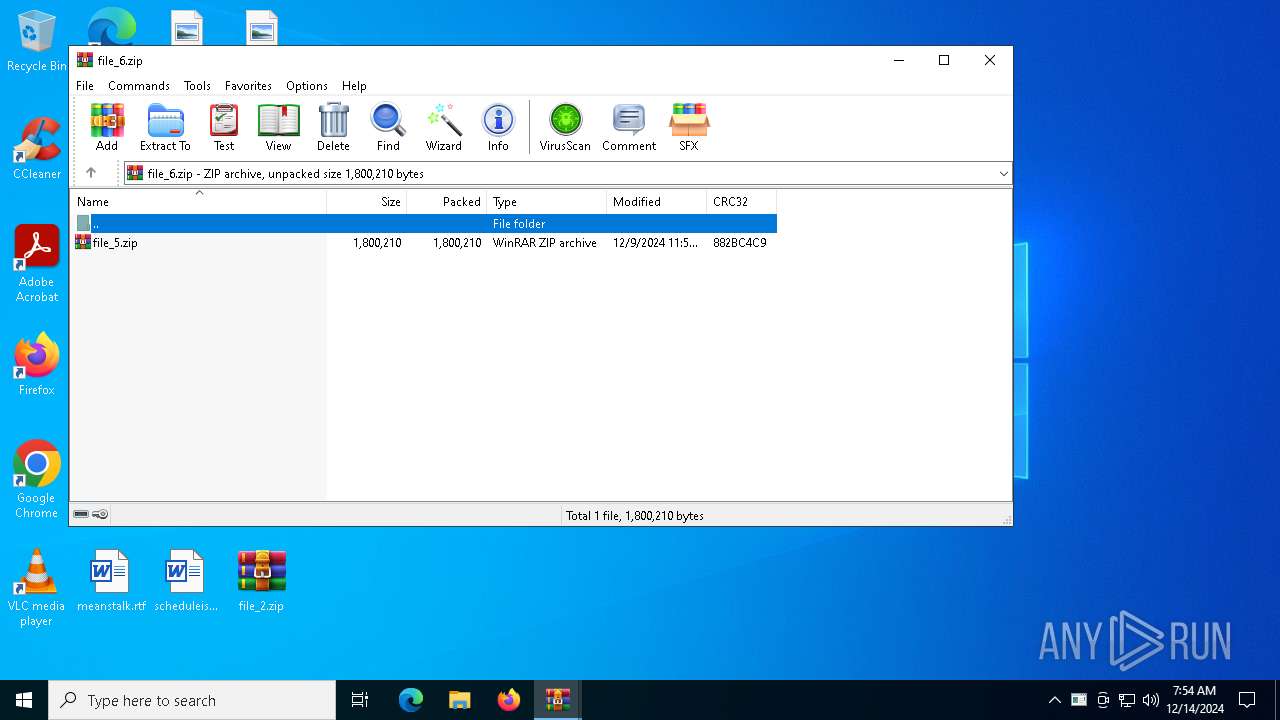
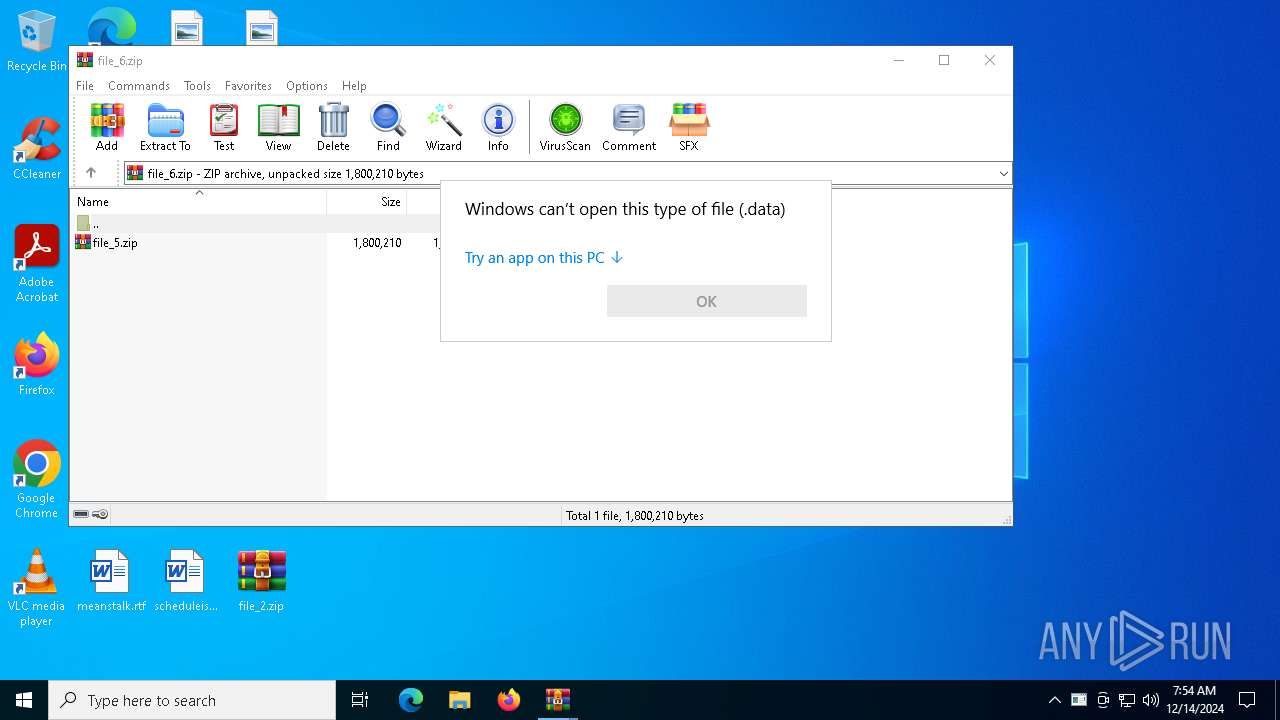
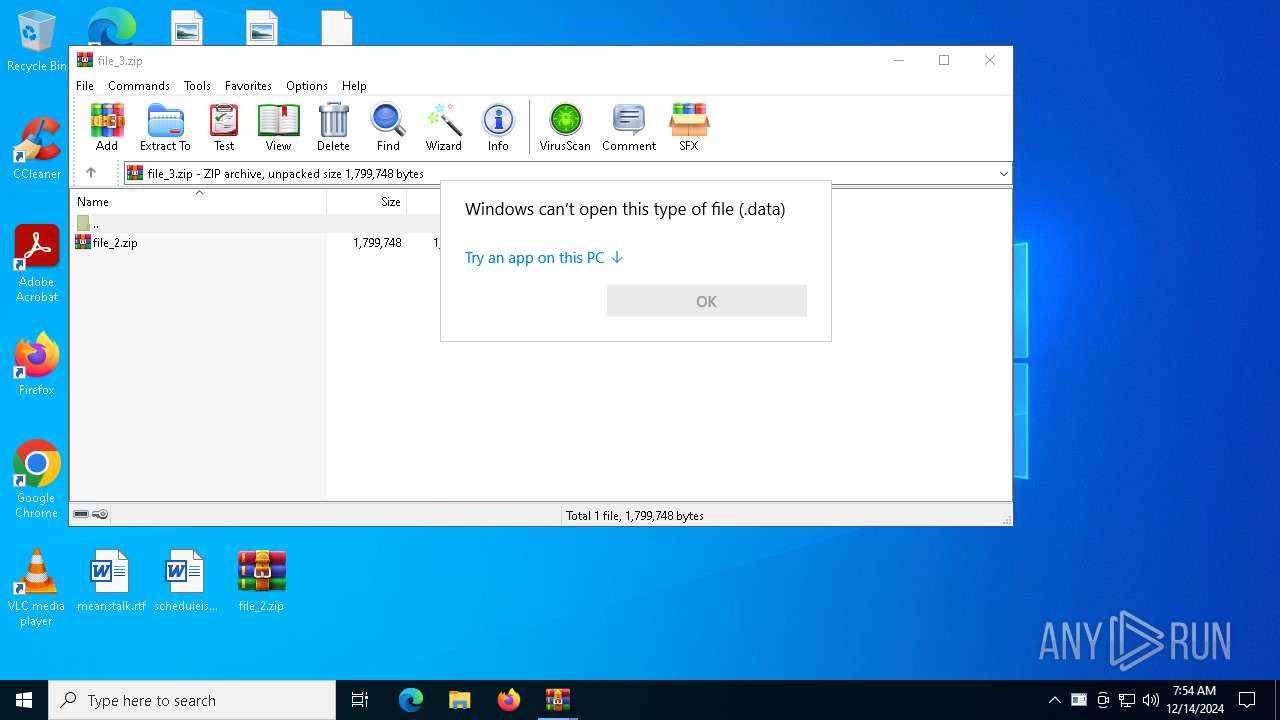
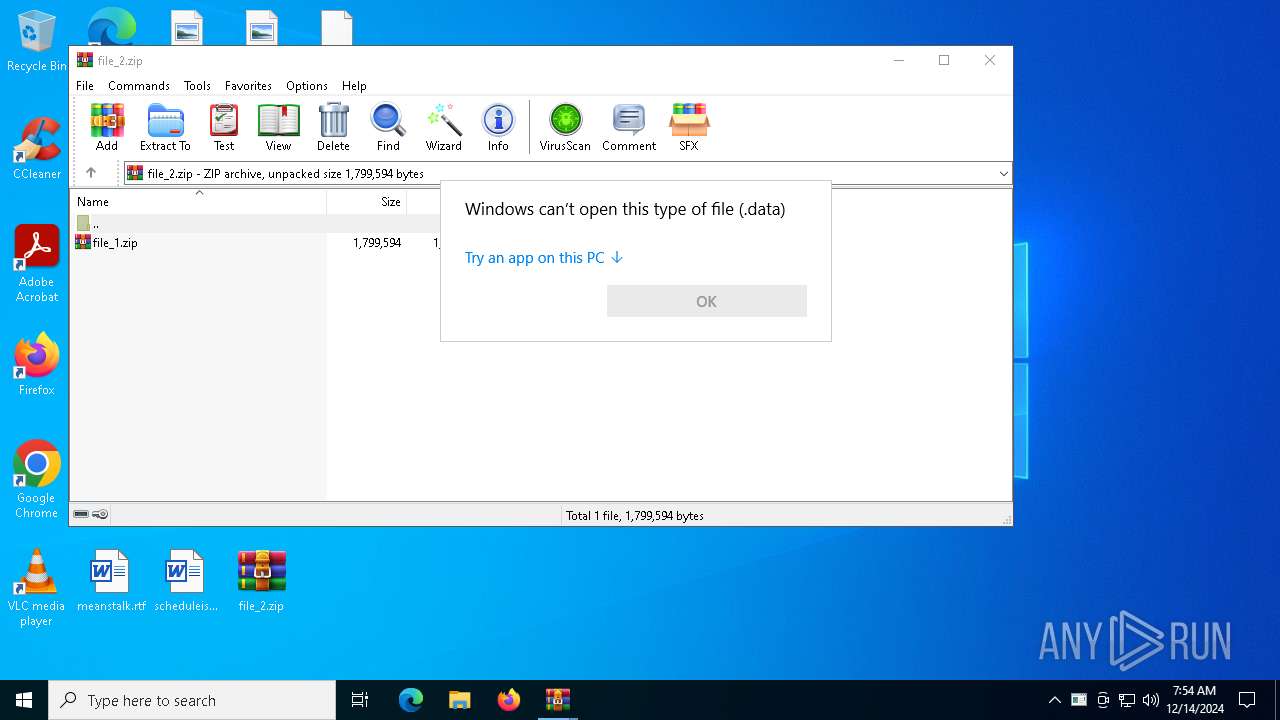
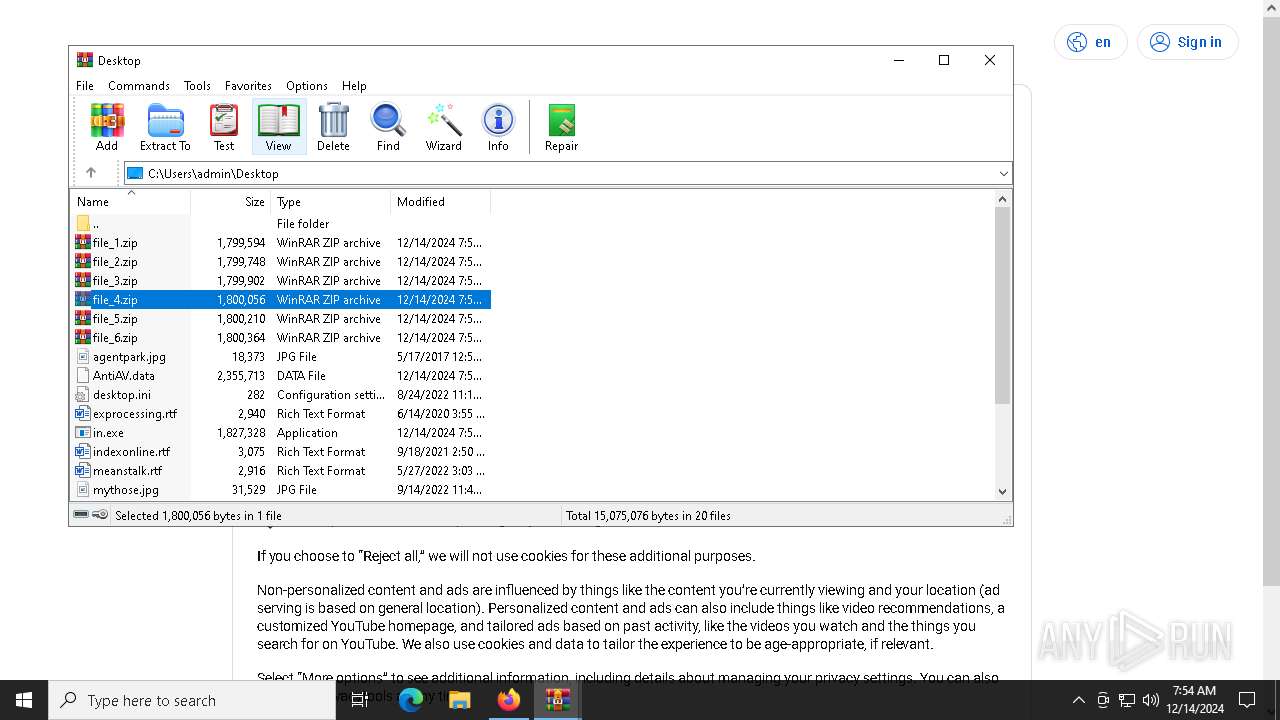
Manual execution by a user
- WinRAR.exe (PID: 5208)
- WinRAR.exe (PID: 5720)
- OpenWith.exe (PID: 5472)
- WinRAR.exe (PID: 2788)
- WinRAR.exe (PID: 3436)
- WinRAR.exe (PID: 5244)
- in.exe (PID: 7600)
- WinRAR.exe (PID: 9840)
Reads mouse settings
- 7ba4a48b63.exe (PID: 1684)
Reads product name
- 0abb235425.exe (PID: 6936)
- 8401ae77a5.exe (PID: 2072)
Reads Environment values
- 0abb235425.exe (PID: 6936)
- 8401ae77a5.exe (PID: 2072)
Reads CPU info
- 0abb235425.exe (PID: 6936)
- 8401ae77a5.exe (PID: 2072)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 5472)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6420)
- powershell.exe (PID: 7696)
- powershell.exe (PID: 8072)
Application launched itself
- chrome.exe (PID: 4468)
- firefox.exe (PID: 2216)
- firefox.exe (PID: 6844)
- chrome.exe (PID: 8148)
- msedge.exe (PID: 8612)
- msedge.exe (PID: 9428)
Themida protector has been detected
- skotes.exe (PID: 6504)
Executable content was dropped or overwritten
- firefox.exe (PID: 6844)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:09:22 17:40:44+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.24 |
| CodeSize: | 322048 |
| InitializedDataSize: | 104448 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x326000 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
246
Monitored processes
116
Malicious processes
13
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 624 | 7z.exe e extracted/file_7.zip -oextracted | C:\Users\admin\AppData\Local\Temp\main\7z.exe | — | cmd.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Console Exit code: 0 Version: 19.00 Modules
| |||||||||||||||
| 644 | 7z.exe e extracted/file_1.zip -oextracted | C:\Users\admin\AppData\Local\Temp\main\7z.exe | cmd.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Console Exit code: 0 Version: 19.00 Modules
| |||||||||||||||
| 836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2004 --field-trial-handle=2008,i,1602119403682433338,14343024628552785331,262144 --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1684 | "C:\Users\admin\AppData\Local\Temp\1015108001\7ba4a48b63.exe" | C:\Users\admin\AppData\Local\Temp\1015108001\7ba4a48b63.exe | skotes.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2072 | "C:\Users\admin\AppData\Local\Temp\1015109001\8401ae77a5.exe" | C:\Users\admin\AppData\Local\Temp\1015109001\8401ae77a5.exe | skotes.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
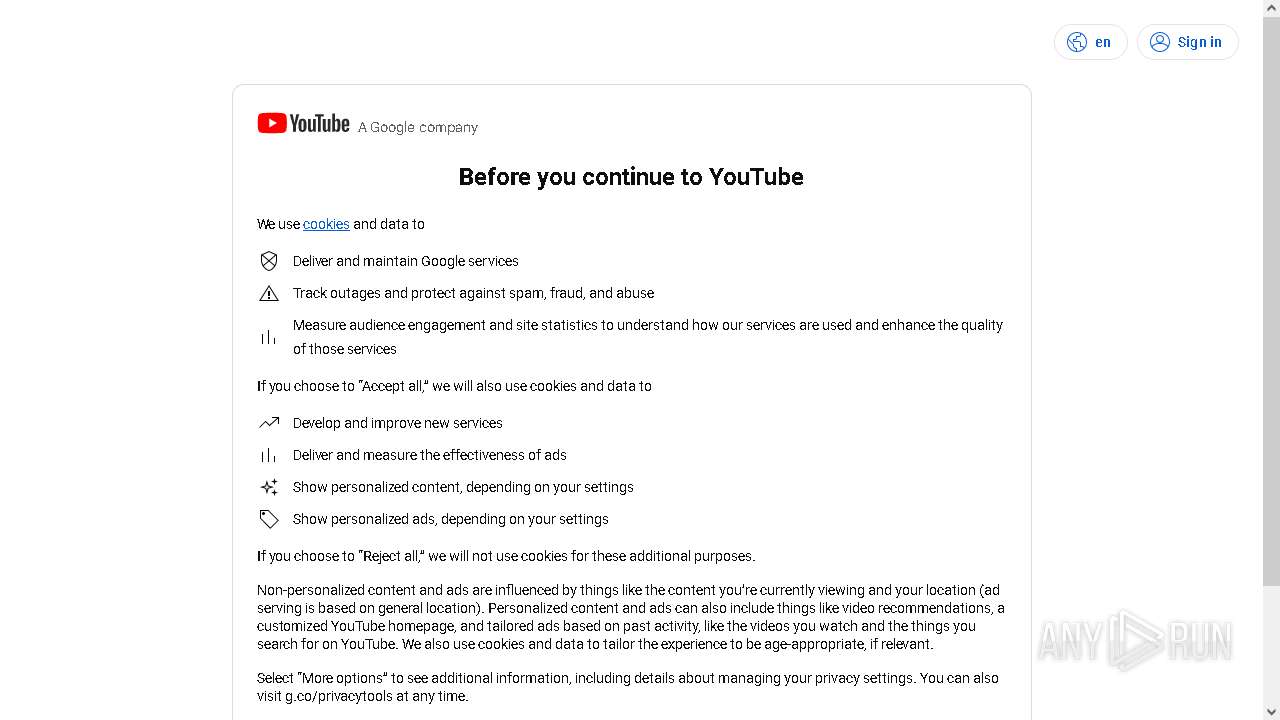
| 2216 | "C:\Program Files\Mozilla Firefox\firefox.exe" --kiosk "https://youtube.com/account?=https://accounts.google.com/v3/signin/challenge/pwd" --no-default-browser-check --disable-popup-blocking | C:\Program Files\Mozilla Firefox\firefox.exe | 7ba4a48b63.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 2496 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --extension-process --no-appcompat-clear --remote-debugging-port=9229 --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=3636 --field-trial-handle=2008,i,1602119403682433338,14343024628552785331,262144 --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2788 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\file_3.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
Total events
54 834
Read events
54 733
Write events
101
Delete events
0
Modification events
| (PID) Process: | (6504) skotes.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6504) skotes.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6504) skotes.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6936) 0abb235425.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6936) 0abb235425.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6936) 0abb235425.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5208) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (5208) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5208) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5208) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\file_1.zip | |||
Executable files
60
Suspicious files
411
Text files
158
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6316 | file.exe | C:\Windows\Tasks\skotes.job | binary | |
MD5:69A592877DD76AD422550464A0EBBC52 | SHA256:C835DC835A8275316B129D8062A4DB62000489D423E11980700E176DCAFC0768 | |||
| 6316 | file.exe | C:\Users\admin\AppData\Local\Temp\abc3bc1985\skotes.exe | executable | |
MD5:EC7B05F32FD59CA03E74B81122E281E1 | SHA256:F638D07D2ED9CA3C918BBEEF9D93B67B6409E8A174F516AFA184019D7C94DE58 | |||
| 6312 | 8fefc93b27.exe | C:\Users\admin\AppData\Local\Temp\main\7z.dll | executable | |
MD5:72491C7B87A7C2DD350B727444F13BB4 | SHA256:34AD9BB80FE8BF28171E671228EB5B64A55CAA388C31CB8C0DF77C0136735891 | |||
| 6312 | 8fefc93b27.exe | C:\Users\admin\AppData\Local\Temp\main\7z.exe | executable | |
MD5:619F7135621B50FD1900FF24AADE1524 | SHA256:344F076BB1211CB02ECA9E5ED2C0CE59BCF74CCBC749EC611538FA14ECB9AAD2 | |||
| 6504 | skotes.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\random[1].exe | executable | |
MD5:3A425626CBD40345F5B8DDDD6B2B9EFA | SHA256:BA9212D2D5CD6DF5EB7933FB37C1B72A648974C1730BF5C32439987558F8E8B1 | |||
| 624 | 7z.exe | C:\Users\admin\AppData\Local\Temp\main\extracted\file_6.zip | compressed | |
MD5:0DC4014FACF82AA027904C1BE1D403C1 | SHA256:A29DDD29958C64E0AF1A848409E97401307277BB6F11777B1CFB0404A6226DE7 | |||
| 6504 | skotes.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\KCV3KQBA\random[1].exe | executable | |
MD5:28E568616A7B792CAC1726DEB77D9039 | SHA256:9597798F7789ADC29FBE97707B1BD8CA913C4D5861B0AD4FDD6B913AF7C7A8E2 | |||
| 624 | 7z.exe | C:\Users\admin\AppData\Local\Temp\main\extracted\AntiAV.data | text | |
MD5:579A63BEBCCBACAB8F14132F9FC31B89 | SHA256:0AC3504D5FA0460CAE3C0FD9C4B628E1A65547A60563E6D1F006D17D5A6354B0 | |||
| 5236 | 7z.exe | C:\Users\admin\AppData\Local\Temp\main\extracted\file_1.zip | compressed | |
MD5:5659EBA6A774F9D5322F249AD989114A | SHA256:E04346FEE15C3F98387A3641E0BBA2E555A5A9B0200E4B9256B1B77094069AE4 | |||
| 6504 | skotes.exe | C:\Users\admin\AppData\Local\Temp\1015105001\8fefc93b27.exe | executable | |
MD5:3A425626CBD40345F5B8DDDD6B2B9EFA | SHA256:BA9212D2D5CD6DF5EB7933FB37C1B72A648974C1730BF5C32439987558F8E8B1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
82
TCP/UDP connections
222
DNS requests
231
Threats
70
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6504 | skotes.exe | GET | — | 31.41.244.11:80 | http://31.41.244.11/files/burpin1/random.exe | unknown | — | — | unknown |
6504 | skotes.exe | POST | 200 | 185.215.113.43:80 | http://185.215.113.43/Zu7JuNko/index.php | unknown | — | — | malicious |
6504 | skotes.exe | POST | 200 | 185.215.113.43:80 | http://185.215.113.43/Zu7JuNko/index.php | unknown | — | — | malicious |
6504 | skotes.exe | POST | 200 | 185.215.113.43:80 | http://185.215.113.43/Zu7JuNko/index.php | unknown | — | — | malicious |
6504 | skotes.exe | GET | 200 | 185.215.113.16:80 | http://185.215.113.16/well/random.exe | unknown | — | — | malicious |
6936 | 0abb235425.exe | GET | 200 | 95.101.54.114:80 | http://e5.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBQeEcDJrP2kU%2B9LL2pzIRVgTVStuQQUmc0pw6FYJq96ekyEWo9ziGCw394CEgP2Bwy2eZF7v0MnOmD3HKKM8Q%3D%3D | unknown | — | — | whitelisted |
6504 | skotes.exe | POST | 200 | 185.215.113.43:80 | http://185.215.113.43/Zu7JuNko/index.php | unknown | — | — | malicious |
6844 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
6504 | skotes.exe | GET | 200 | 185.215.113.16:80 | http://185.215.113.16/steam/random.exe | unknown | — | — | malicious |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5880 | svchost.exe | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5880 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.23.209.149:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
drive-connect.cyou |
| malicious |
t.me |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6504 | skotes.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 33 |
6504 | skotes.exe | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Amadey HTTP POST Request (st=s) |
6504 | skotes.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
6504 | skotes.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
6504 | skotes.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 2 |
6504 | skotes.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
6504 | skotes.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
6504 | skotes.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
6504 | skotes.exe | A Network Trojan was detected | ET MALWARE Win32/Amadey Host Fingerprint Exfil (POST) M2 |
6504 | skotes.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
4 ETPRO signatures available at the full report
Process | Message |
|---|---|
file.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
skotes.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
skotes.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
8401ae77a5.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
e65a0212bf.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
FHCBGIIJKE.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
skotes.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|