| File name: | 8888.png |
| Full analysis: | https://app.any.run/tasks/088562f8-8921-40e3-a936-ae61d2c4a910 |
| Verdict: | Malicious activity |
| Threats: | Qbot is a banking Trojan — a malware designed to collect banking information from victims. Qbot targets organizations mostly in the US. It is equipped with various sophisticated evasion and info-stealing functions and worm-like functionality, and a strong persistence mechanism. |
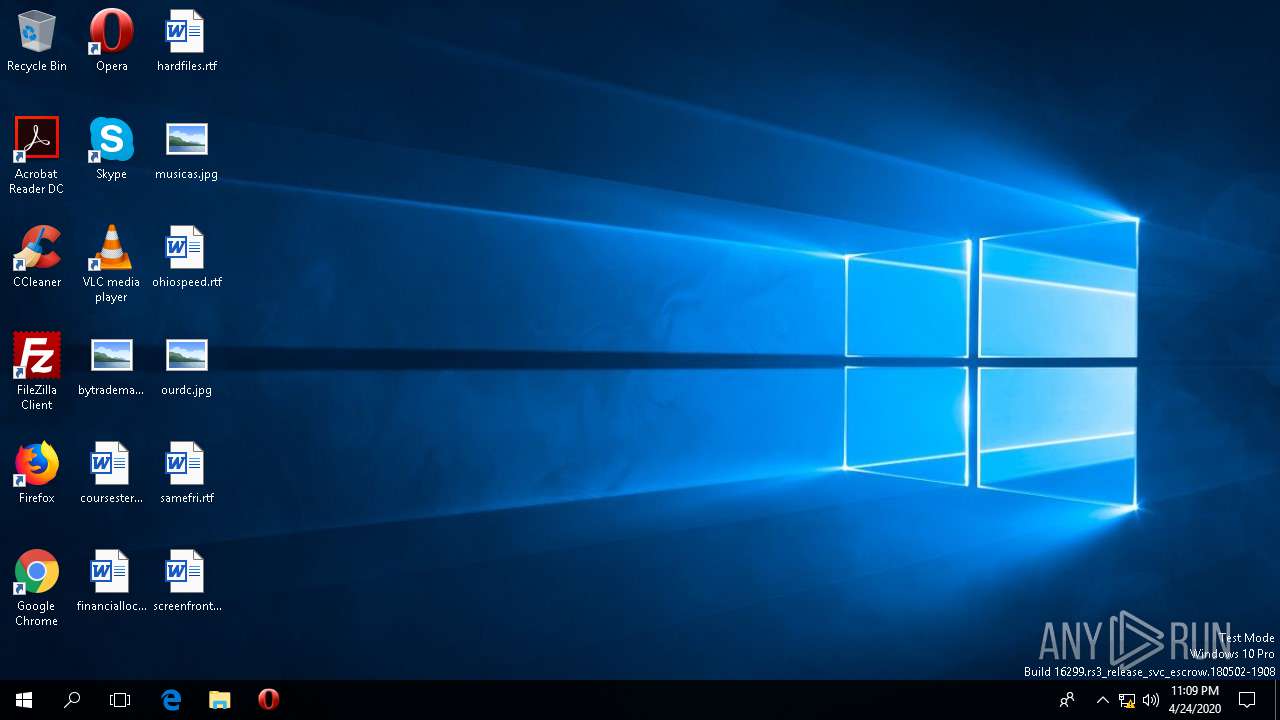
| Analysis date: | April 24, 2020, 23:09:32 |
| OS: | Windows 10 Professional (build: 16299, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 2CF20A1DD3693B996DE4A559F1067850 |
| SHA1: | 6483BB40A7E3817F93A3AE95C6CAEA01715A4946 |
| SHA256: | F6210DA7865E00351C0E79464A1BA14A8ECC59DD79F650F2FF76F1697F6807B1 |
| SSDEEP: | 6144:ztKJnv0N4sc6UKOahwyl2bbuBD9t4Piqqb5wVhFsbnN8ef:pKJnv0N4sd7l1R9Ua5wVoz |
MALICIOUS
QBOT was detected
- 8888.png.exe (PID: 3188)
Runs PING.EXE for delay simulation
- cmd.exe (PID: 3668)
Changes the autorun value in the registry
- explorer.exe (PID: 5192)
SUSPICIOUS
Application launched itself
- 8888.png.exe (PID: 3188)
- fsoevv.exe (PID: 1716)
Starts itself from another location
- 8888.png.exe (PID: 3188)
Executable content was dropped or overwritten
- 8888.png.exe (PID: 3188)
- cmd.exe (PID: 3668)
Starts CMD.EXE for commands execution
- 8888.png.exe (PID: 3188)
Creates files in the user directory
- 8888.png.exe (PID: 3188)
- SystemSettings.exe (PID: 4500)
Executed via COM
- SystemSettings.exe (PID: 4500)
- ApplicationFrameHost.exe (PID: 5376)
- RuntimeBroker.exe (PID: 3420)
- SpeechRuntime.exe (PID: 5544)
- backgroundTaskHost.exe (PID: 564)
Checks supported languages
- backgroundTaskHost.exe (PID: 564)
- SystemSettings.exe (PID: 4500)
Reads the machine GUID from the registry
- backgroundTaskHost.exe (PID: 564)
- explorer.exe (PID: 5192)
- SpeechRuntime.exe (PID: 5544)
Connects to server without host name
- explorer.exe (PID: 5192)
INFO
Reads the software policy settings
- explorer.exe (PID: 5192)
Reads settings of System Certificates
- explorer.exe (PID: 5192)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ 4.x (63.9) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (14.8) |
| .exe | | | Win64 Executable (generic) (13.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.1) |
| .exe | | | Win32 Executable (generic) (2.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:04:23 14:47:57+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 1933824 |
| InitializedDataSize: | 15360 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1ca0 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 7.2.7601.17514 |
| ProductVersionNumber: | 7.2.7601.17514 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Microsoft Connection Manager Profile ikstaller |
| FileVersion: | 7.02.7601.17514 (win7sp1_rtm.101119-1850) |
| InternalName: | CMSTP |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | CMSTP.EXE |
| ProductName: | Microsoft(R) Connection Manager |
| ProductVersion: | 7.02.7601.17514 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 23-Apr-2020 12:47:57 |
| Detected languages: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | Microsoft Connection Manager Profile ikstaller |
| FileVersion: | 7.02.7601.17514 (win7sp1_rtm.101119-1850) |
| InternalName: | CMSTP |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFilename: | CMSTP.EXE |
| ProductName: | Microsoft(R) Connection Manager |
| ProductVersion: | 7.02.7601.17514 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 23-Apr-2020 12:47:57 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x001D804D | 0x001D8200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 1.54122 |
.rdata | 0x001DA000 | 0x000000C9 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.96321 |
.data | 0x001DB000 | 0x00002B18 | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.66044 |
.rsrc | 0x001DE000 | 0x00000DA0 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.65501 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.56398 | 944 | UNKNOWN | English - United States | RT_VERSION |
107 | 1.91924 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
5000 | 5.04236 | 351 | UNKNOWN | English - United States | REGINST |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
ole32.dll |
Total processes
103
Monitored processes
13
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 564 | "C:\WINDOWS\system32\backgroundTaskHost.exe" -ServerName:CortanaUI.AppXy7vb4pc2dr3kc93kfc509b1d0arkfb2x.mca | C:\WINDOWS\system32\backgroundTaskHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Background Task Host Exit code: 1 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1716 | C:\Users\admin\AppData\Roaming\Microsoft\Olhgykmnnfgq\fsoevv.exe | C:\Users\admin\AppData\Roaming\Microsoft\Olhgykmnnfgq\fsoevv.exe | — | 8888.png.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Connection Manager Profile ikstaller Exit code: 0 Version: 7.02.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3188 | "C:\Users\admin\AppData\Local\Temp\8888.png.exe" | C:\Users\admin\AppData\Local\Temp\8888.png.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Connection Manager Profile ikstaller Exit code: 0 Version: 7.02.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3420 | C:\Windows\System32\RuntimeBroker.exe -Embedding | C:\Windows\System32\RuntimeBroker.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Runtime Broker Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3668 | "C:\Windows\System32\cmd.exe" /c ping.exe -n 6 127.0.0.1 & type "C:\WINDOWS\System32\calc.exe" > "C:\Users\admin\AppData\Local\Temp\8888.png.exe" | C:\Windows\SysWOW64\cmd.exe | 8888.png.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4212 | ping.exe -n 6 127.0.0.1 | C:\WINDOWS\SysWOW64\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4472 | C:\Users\admin\AppData\Local\Temp\8888.png.exe /C | C:\Users\admin\AppData\Local\Temp\8888.png.exe | — | 8888.png.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Connection Manager Profile ikstaller Exit code: 0 Version: 7.02.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 4500 | "C:\Windows\ImmersiveControlPanel\SystemSettings.exe" -ServerName:microsoft.windows.immersivecontrolpanel | C:\Windows\ImmersiveControlPanel\SystemSettings.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Settings Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5192 | C:\WINDOWS\SysWOW64\explorer.exe | C:\WINDOWS\SysWOW64\explorer.exe | fsoevv.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5376 | C:\WINDOWS\system32\ApplicationFrameHost.exe -Embedding | C:\WINDOWS\system32\ApplicationFrameHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Application Frame Host Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 681
Read events
1 581
Write events
98
Delete events
2
Modification events
| (PID) Process: | (3188) 8888.png.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3188) 8888.png.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3188) 8888.png.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3188) 8888.png.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (5192) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | euobqqsr |
Value: "C:\Users\admin\AppData\Roaming\Microsoft\Olhgykmnnfgq\fsoevv.exe" | |||
| (PID) Process: | (5376) ApplicationFrameHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MrtCache\C:%5CWindows%5CImmersiveControlPanel%5Cresources.pri\1d33928e47e02c6\a01460c8 |
| Operation: | write | Name: | LanguageList |
Value: _en-US;en_standard_100_US_LTR_dark_Desktop | |||
| (PID) Process: | (564) backgroundTaskHost.exe | Key: | \REGISTRY\A\{fc8c7757-40df-ebc1-df95-18445c85433a}\LocalState\Configuration |
| Operation: | write | Name: | DisabledReason |
Value: 010000006721EB0F8E1AD601 | |||
| (PID) Process: | (564) backgroundTaskHost.exe | Key: | \REGISTRY\A\{fc8c7757-40df-ebc1-df95-18445c85433a}\LocalState\Configuration |
| Operation: | write | Name: | HasDefaultMSA |
Value: 0000000064351D108E1AD601 | |||
| (PID) Process: | (564) backgroundTaskHost.exe | Key: | \REGISTRY\A\{fc8c7757-40df-ebc1-df95-18445c85433a}\LocalState\Configuration |
| Operation: | write | Name: | ConnectedToMSA |
Value: 00000000DAF721108E1AD601 | |||
| (PID) Process: | (564) backgroundTaskHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.cortana_cw5n1h2txyewy\SOFTWARE\Microsoft\Speech_OneCore\Isolated\YjUX0LhiWH34l55J52QWs4VCvCT-efpDIK2ZdqrXKQE\HKEY_CURRENT_USER\SOFTWARE\Microsoft\Speech_OneCore\Recognizers |
| Operation: | write | Name: | DefaultTokenId |
Value: HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Speech_OneCore\Recognizers\Tokens\MS-1033-110-WINMO-DNN | |||
Executable files
2
Suspicious files
14
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4500 | SystemSettings.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\4UPALB4AKG5H1WH3TS2O.temp | — | |
MD5:— | SHA256:— | |||
| 5192 | explorer.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\WLJYL64M\t3[1] | — | |
MD5:— | SHA256:— | |||
| 5192 | explorer.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\WLJYL64M\94KJRMSN.htm | — | |
MD5:— | SHA256:— | |||
| 3188 | 8888.png.exe | C:\Users\admin\AppData\Roaming\Microsoft\Olhgykmnnfgq\fsoevv.dat | binary | |
MD5:— | SHA256:— | |||
| 3668 | cmd.exe | C:\Users\admin\AppData\Local\Temp\8888.png.exe | executable | |
MD5:— | SHA256:— | |||
| 5192 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Olhgykmnnfgq\fsoevv.dat | binary | |
MD5:— | SHA256:— | |||
| 3188 | 8888.png.exe | C:\Users\admin\AppData\Roaming\Microsoft\Olhgykmnnfgq\fsoevv.exe | executable | |
MD5:2CF20A1DD3693B996DE4A559F1067850 | SHA256:F6210DA7865E00351C0E79464A1BA14A8ECC59DD79F650F2FF76F1697F6807B1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
18
DNS requests
6
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1924 | svchost.exe | GET | 304 | 20.191.48.196:443 | https://settings-win-ppe.data.microsoft.com/settings/v2.0/Storage/StorageHealthEvaluation?os=Windows&deviceClass=Windows.Desktop&appVer=1.0.0.0 | US | — | — | whitelisted |
5192 | explorer.exe | POST | — | 73.111.224.222:443 | https://73.111.224.222/t3 | US | — | — | malicious |
5192 | explorer.exe | GET | 200 | 207.38.89.115:443 | https://www.ip-adress.com/ | US | html | 28.7 Kb | shared |
5192 | explorer.exe | GET | 301 | 207.38.89.115:80 | http://www.ip-adress.com/ | US | html | 234 b | shared |
1924 | svchost.exe | POST | 200 | 66.26.160.37:443 | https://66.26.160.37/t3 | US | text | 41 b | malicious |
1924 | svchost.exe | POST | 200 | 199.241.223.66:443 | https://199.241.223.66/t3 | US | text | 41 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5296 | svchost.exe | 20.191.48.196:443 | settings-win-ppe.data.microsoft.com | Microsoft Corporation | US | unknown |
5192 | explorer.exe | 199.241.223.66:443 | — | Haefele TV Inc. | US | malicious |
5192 | explorer.exe | 66.26.160.37:443 | — | Time Warner Cable Internet LLC | US | malicious |
5192 | explorer.exe | 170.82.210.138:2222 | — | Digicel Jamaica | TT | malicious |
5192 | explorer.exe | 98.22.66.236:443 | — | Windstream Communications Inc | US | malicious |
5192 | explorer.exe | 73.111.224.222:443 | — | Comcast Cable Communications, LLC | US | malicious |
5192 | explorer.exe | 1.172.254.207:443 | — | Data Communication Business Group | TW | malicious |
5192 | explorer.exe | 207.38.89.115:80 | www.ip-adress.com | server4you Inc. | US | malicious |
5192 | explorer.exe | 207.38.89.115:443 | www.ip-adress.com | server4you Inc. | US | malicious |
5192 | explorer.exe | 23.49.13.33:7000 | — | Akamai International B.V. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
self.events.data.microsoft.com |
| whitelisted |
settings-win-ppe.data.microsoft.com |
| whitelisted |
dns.msftncsi.com |
| shared |
www.ip-adress.com |
| shared |
113.44.203.85.in-addr.arpa |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5192 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] External IP (possible Qbot) |
5192 | explorer.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] External IP Address Check |
1 ETPRO signatures available at the full report
Process | Message |
|---|---|
conhost.exe | InitSideBySide failed create an activation context. Error: 1814 |