| File name: | Flashplayerpp_install_cn (1).exe |
| Full analysis: | https://app.any.run/tasks/3fd032a3-3c13-41a2-8fc6-63e25fbf4b14 |
| Verdict: | Malicious activity |
| Threats: | Cobalt Strike is a legitimate penetration software toolkit developed by Forta. But its cracked versions are widely adopted by bad actors, who use it as a C2 system of choice for targeted attacks. |
| Analysis date: | October 20, 2020, 05:31:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | ABCE428BE48EC9A8C5B0A7832A09B29B |
| SHA1: | D56172C8E37EC65F0C89E18C9AA21A9B7AC93CC8 |
| SHA256: | F5F6C9FF45502589B27092739A53142D1D1F46470C9A16556896AE9BFA83CB58 |
| SSDEEP: | 49152:Ig8N0jZCuqrq7ql7y9SSSSx7cSSSSSSuCCCCCCWZEIZEEk3NhT0wsRjJeGNHDdAW: |
MALICIOUS
Loads the Task Scheduler COM API
- AT.exe (PID: 4048)
Starts Visual C# compiler
- MSBuild.exe (PID: 3336)
Application was dropped or rewritten from another process
- AT.exe (PID: 4048)
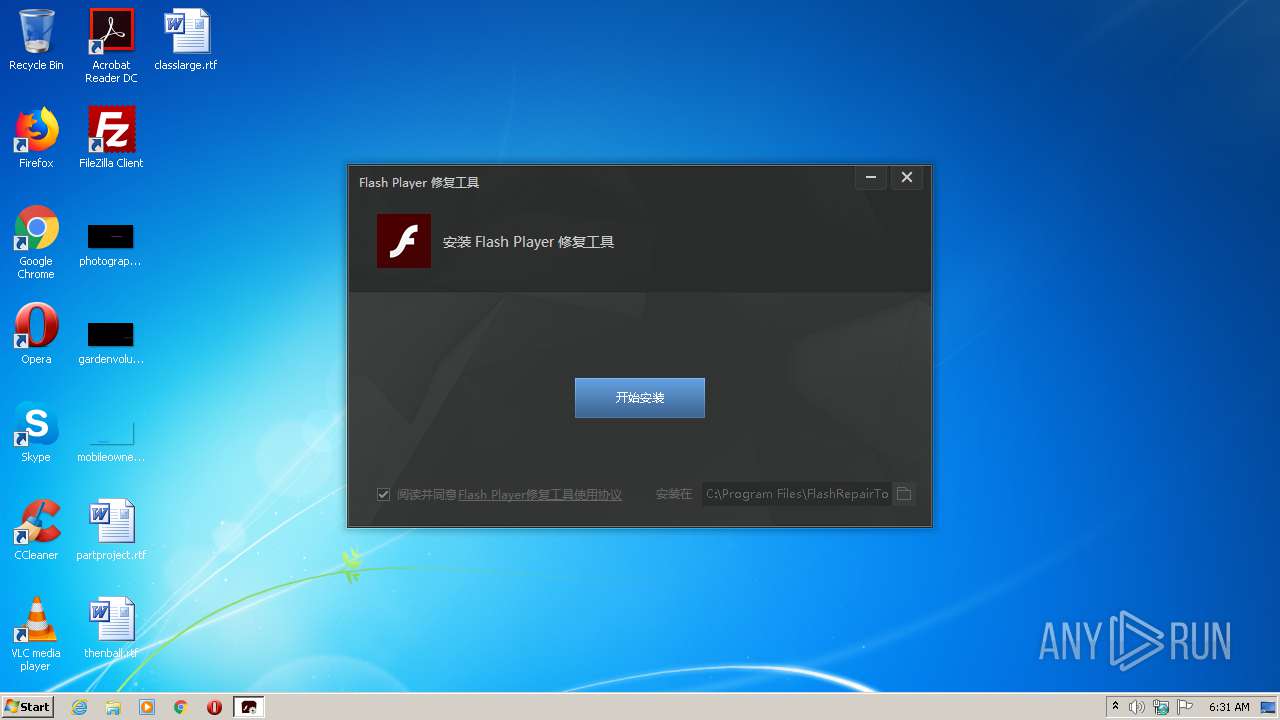
- FlashRepairTool.exe (PID: 3664)
- FlashRepairToolInstaller.exe (PID: 3072)
Loads dropped or rewritten executable
- FlashRepairToolInstaller.exe (PID: 3072)
COBALTSTRIKE was detected
- calc.exe (PID: 3040)
Changes settings of System certificates
- calc.exe (PID: 3040)
Connects to CnC server
- calc.exe (PID: 3040)
SUSPICIOUS
Executable content was dropped or overwritten
- Flashplayerpp_install_cn (1).exe (PID: 3756)
- FlashRepairToolInstaller.exe (PID: 3072)
Changes IE settings (feature browser emulation)
- FlashRepairToolInstaller.exe (PID: 3072)
Creates files in the user directory
- FlashRepairToolInstaller.exe (PID: 3072)
Reads Internet Cache Settings
- FlashRepairTool.exe (PID: 3664)
- calc.exe (PID: 3040)
Creates a software uninstall entry
- FlashRepairToolInstaller.exe (PID: 3072)
Creates files in the program directory
- FlashRepairToolInstaller.exe (PID: 3072)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2096:09:28 03:54:26+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 7442944 |
| InitializedDataSize: | 38912 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x71b19e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | flashplayerpp_install_cn |
| FileVersion: | 1.0.0.0 |
| InternalName: | Flashplayerpp_install_cn.exe |
| LegalCopyright: | Copyright © 2020 |
| LegalTrademarks: | - |
| OriginalFileName: | Flashplayerpp_install_cn.exe |
| ProductName: | flashplayerpp_install_cn |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 22-Aug-1960 19:26:10 |
| Debug artifacts: |
|
| Comments: | - |
| CompanyName: | - |
| FileDescription: | flashplayerpp_install_cn |
| FileVersion: | 1.0.0.0 |
| InternalName: | Flashplayerpp_install_cn.exe |
| LegalCopyright: | Copyright © 2020 |
| LegalTrademarks: | - |
| OriginalFilename: | Flashplayerpp_install_cn.exe |
| ProductName: | flashplayerpp_install_cn |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 22-Aug-1960 19:26:10 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x007191A4 | 0x00719200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 3.97777 |
.rsrc | 0x0071C000 | 0x00009510 | 0x00009600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.97943 |
.reloc | 0x00726000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.88227 | 3301 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 3.09028 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 2.05167 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 7.89204 | 10847 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 3.43985 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 3.58326 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 4.01266 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.71858 | 104 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
50
Monitored processes
9
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2272 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES645C.tmp" "c:\Users\admin\AppData\Local\Temp\0d2n4oit\CSC47FA4DD4E65A41459C3FCC4499432FB2.TMP" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 12.00.52519.0 built by: VSWINSERVICING Modules
| |||||||||||||||
| 3040 | "C:\Windows\System32\calc.exe" | C:\Windows\System32\calc.exe | MSBuild.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Calculator Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
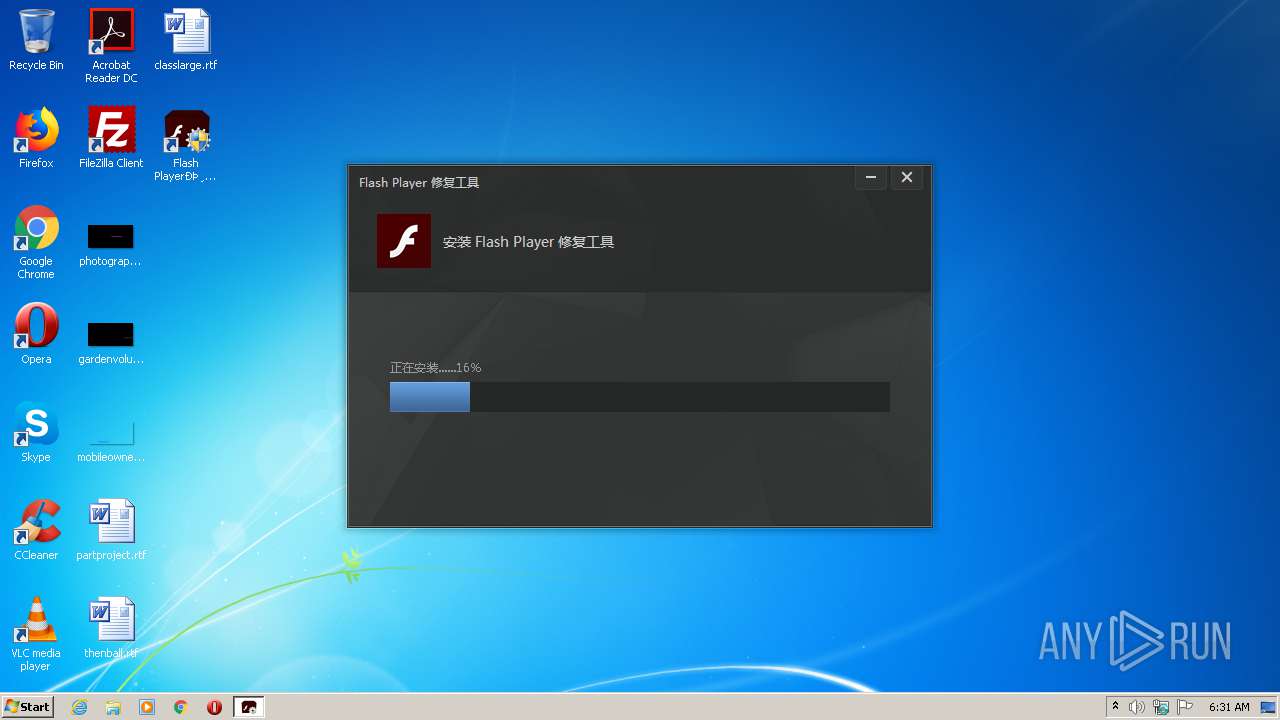
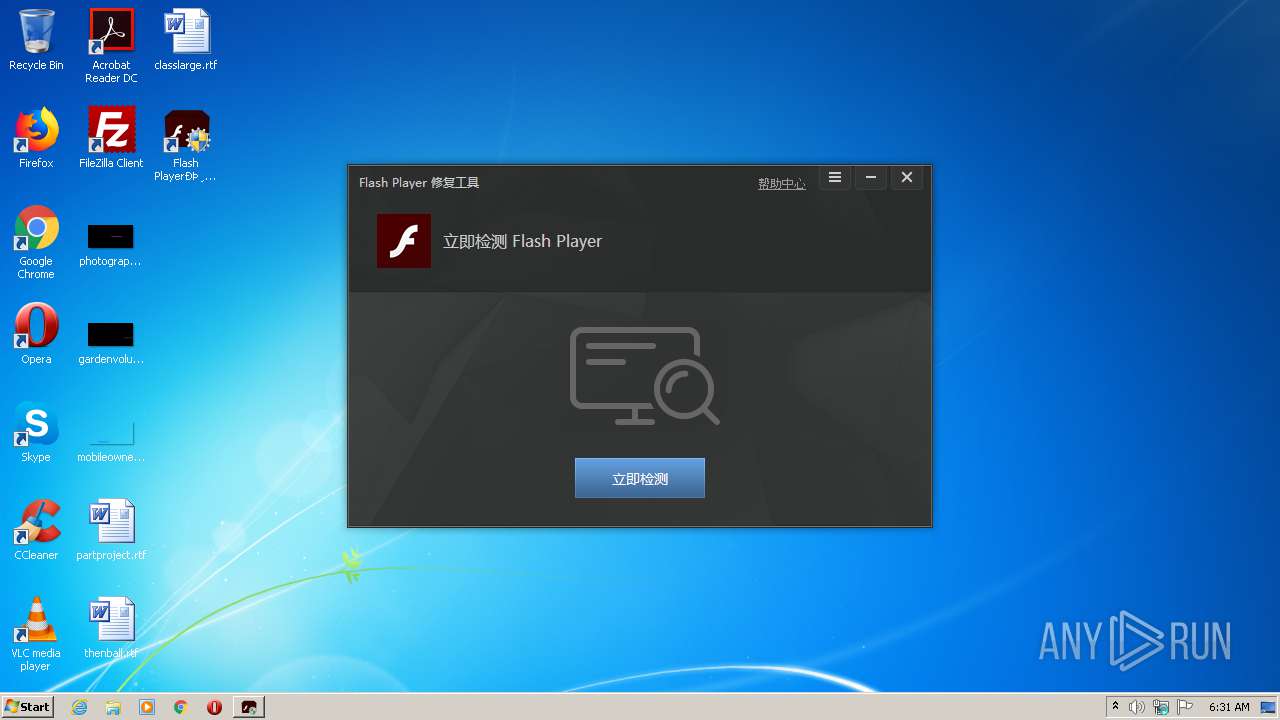
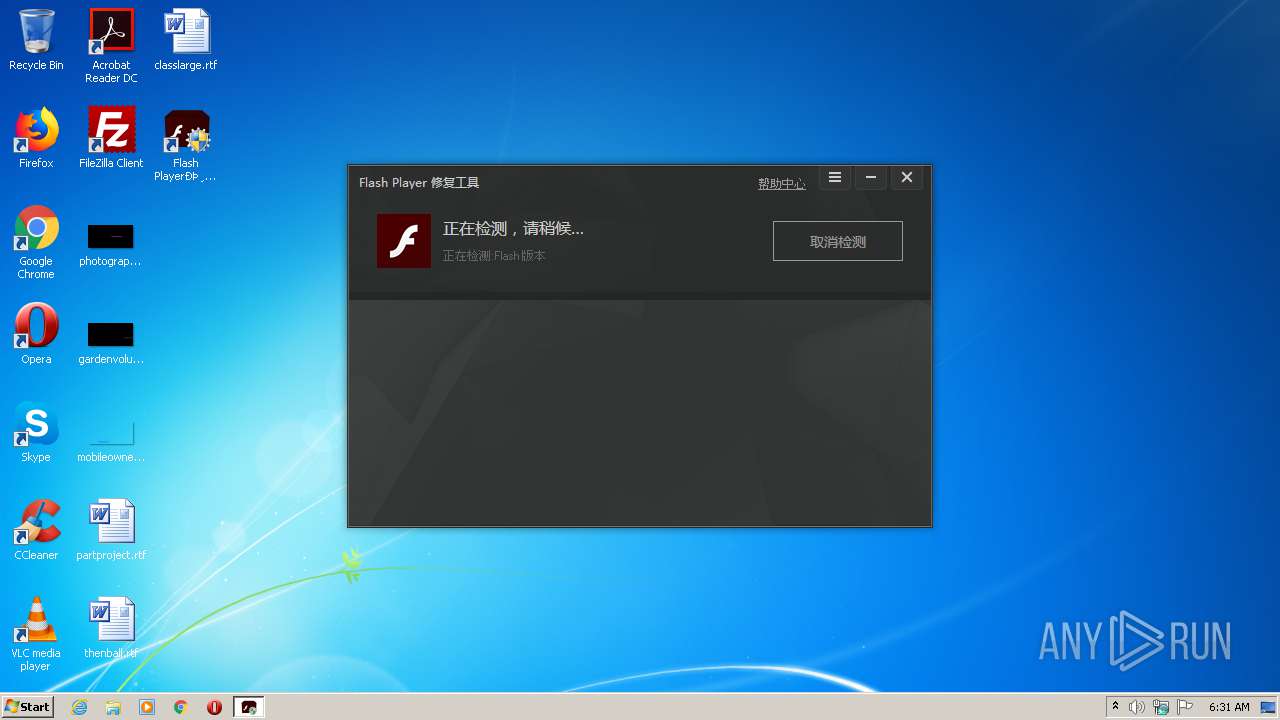
| 3072 | "C:\Users\admin\AppData\Local\Temp\FlashRepairToolInstaller.exe" | C:\Users\admin\AppData\Local\Temp\FlashRepairToolInstaller.exe | Flashplayerpp_install_cn (1).exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Flash Player修复工具 Installer Exit code: 1 Version: 1.0.5.5840 Modules
| |||||||||||||||
| 3164 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\0d2n4oit\0d2n4oit.cmdline" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe | — | MSBuild.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
| 3228 | "C:\Users\admin\AppData\Local\Temp\Flashplayerpp_install_cn (1).exe" | C:\Users\admin\AppData\Local\Temp\Flashplayerpp_install_cn (1).exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: flashplayerpp_install_cn Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3336 | "C:\WINDOWS\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe" C:\Users\admin\AppData\Local\bin\WinUpdate.xml | C:\WINDOWS\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | — | Flashplayerpp_install_cn (1).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: MSBuild.exe Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
| 3664 | "C:\Program Files\FlashRepairTool\\FlashRepairTool.exe" Install | C:\Program Files\FlashRepairTool\FlashRepairTool.exe | FlashRepairToolInstaller.exe | ||||||||||||
User: admin Company: 重庆重橙网络科技有限公司 Integrity Level: HIGH Description: Flash Player 修复工具 Exit code: 0 Version: 1.0.5.5840 Modules
| |||||||||||||||
| 3756 | "C:\Users\admin\AppData\Local\Temp\Flashplayerpp_install_cn (1).exe" | C:\Users\admin\AppData\Local\Temp\Flashplayerpp_install_cn (1).exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: flashplayerpp_install_cn Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
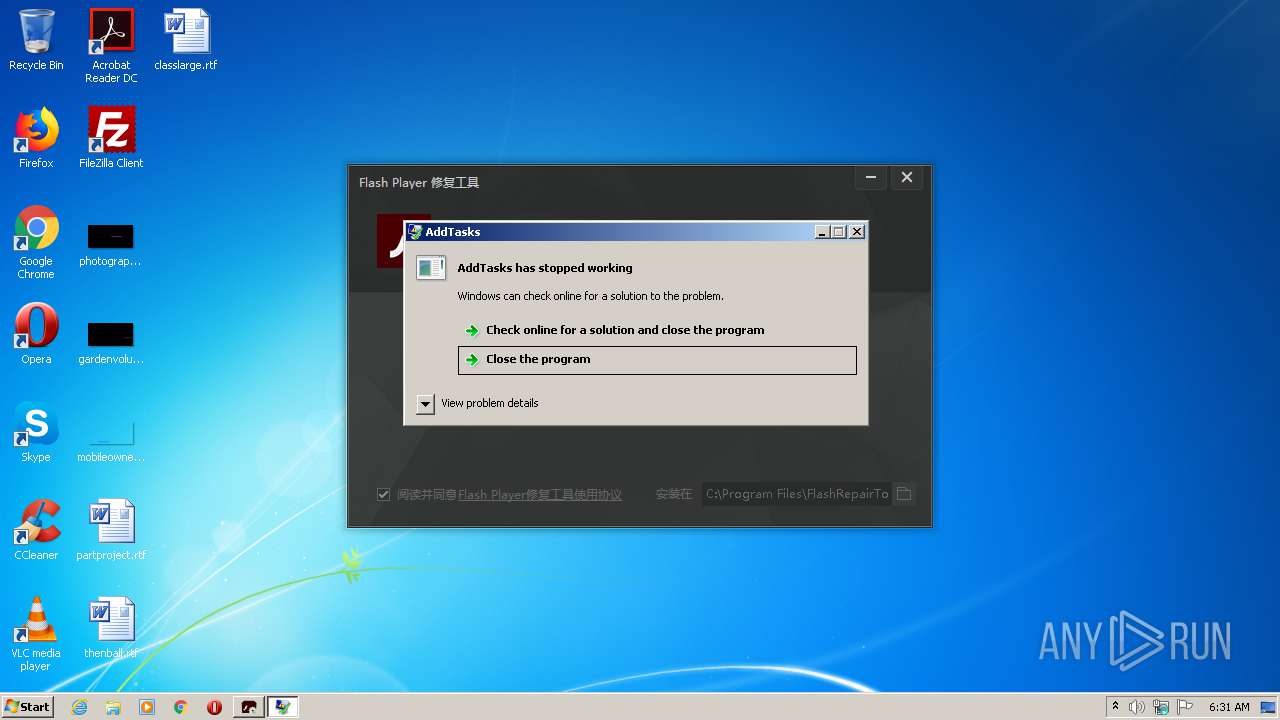
| 4048 | "C:\Users\admin\AppData\Local\Temp\AT.exe" | C:\Users\admin\AppData\Local\Temp\AT.exe | Flashplayerpp_install_cn (1).exe | ||||||||||||
User: admin Integrity Level: HIGH Description: AddTasks Exit code: 3762504530 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
733
Read events
474
Write events
259
Delete events
0
Modification events
| (PID) Process: | (3756) Flashplayerpp_install_cn (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Flashplayerpp_install_cn (1)_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3756) Flashplayerpp_install_cn (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Flashplayerpp_install_cn (1)_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3756) Flashplayerpp_install_cn (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Flashplayerpp_install_cn (1)_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3756) Flashplayerpp_install_cn (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Flashplayerpp_install_cn (1)_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3756) Flashplayerpp_install_cn (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Flashplayerpp_install_cn (1)_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3756) Flashplayerpp_install_cn (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Flashplayerpp_install_cn (1)_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3756) Flashplayerpp_install_cn (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Flashplayerpp_install_cn (1)_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3756) Flashplayerpp_install_cn (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Flashplayerpp_install_cn (1)_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3756) Flashplayerpp_install_cn (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Flashplayerpp_install_cn (1)_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3756) Flashplayerpp_install_cn (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Flashplayerpp_install_cn (1)_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
14
Suspicious files
11
Text files
3
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3164 | csc.exe | C:\Users\admin\AppData\Local\Temp\0d2n4oit\CSC47FA4DD4E65A41459C3FCC4499432FB2.TMP | — | |
MD5:— | SHA256:— | |||
| 3164 | csc.exe | C:\Users\admin\AppData\Local\Temp\0d2n4oit\0d2n4oit.pdb | — | |
MD5:— | SHA256:— | |||
| 3164 | csc.exe | C:\Users\admin\AppData\Local\Temp\0d2n4oit\0d2n4oit.dll | — | |
MD5:— | SHA256:— | |||
| 2272 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RES645C.tmp | — | |
MD5:— | SHA256:— | |||
| 3164 | csc.exe | C:\Users\admin\AppData\Local\Temp\0d2n4oit\0d2n4oit.out | — | |
MD5:— | SHA256:— | |||
| 3040 | calc.exe | C:\Users\admin\AppData\Local\Temp\Cab6C1C.tmp | — | |
MD5:— | SHA256:— | |||
| 3040 | calc.exe | C:\Users\admin\AppData\Local\Temp\Tar6C1D.tmp | — | |
MD5:— | SHA256:— | |||
| 3040 | calc.exe | C:\Users\admin\AppData\Local\Temp\Cab6C3E.tmp | — | |
MD5:— | SHA256:— | |||
| 3040 | calc.exe | C:\Users\admin\AppData\Local\Temp\Tar6C3F.tmp | — | |
MD5:— | SHA256:— | |||
| 3040 | calc.exe | C:\Users\admin\AppData\Local\Temp\Cab6D2A.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
17
DNS requests
4
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3072 | FlashRepairToolInstaller.exe | GET | 200 | 112.65.212.142:80 | http://tongji.flash.cn/hm4.gif?product=repairtools&event=install&uid=533E95D3AA78C4092F0AA9C694122A75&um={3283428F-CBB3-4b03-91D0-C4BD8762A8A7}&platform=Windows&channel=10000&version=1.0.5.5840&key=0&data={"result":0,"time":1603171909,"osversion":"6.1.7601.17932","arch":"x86"}&signature=6f1c21d0713ca70a81e338c8835ea977 | CN | — | — | whitelisted |
3040 | calc.exe | GET | 304 | 8.248.113.254:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.5 Kb | whitelisted |
3756 | Flashplayerpp_install_cn (1).exe | GET | 200 | 35.241.76.6:80 | http://www.flash-load.ml/api.php?up=up | US | binary | 20 b | malicious |
3040 | calc.exe | GET | 200 | 8.248.113.254:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.5 Kb | whitelisted |
3040 | calc.exe | GET | 304 | 8.248.113.254:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.5 Kb | whitelisted |
3040 | calc.exe | GET | 304 | 8.248.113.254:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.5 Kb | whitelisted |
3040 | calc.exe | GET | 304 | 8.248.113.254:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.5 Kb | whitelisted |
3040 | calc.exe | GET | 304 | 8.248.113.254:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.5 Kb | whitelisted |
3040 | calc.exe | GET | 304 | 8.248.113.254:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.5 Kb | whitelisted |
3040 | calc.exe | GET | 304 | 8.248.113.254:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.5 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3756 | Flashplayerpp_install_cn (1).exe | 35.241.76.6:80 | www.flash-load.ml | — | US | malicious |
3040 | calc.exe | 35.241.76.6:443 | www.flash-load.ml | — | US | malicious |
3040 | calc.exe | 8.248.113.254:80 | www.download.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
3072 | FlashRepairToolInstaller.exe | 112.65.212.142:80 | tongji.flash.cn | China Unicom Shanghai network | CN | suspicious |
3664 | FlashRepairTool.exe | 119.28.164.234:443 | api.flash.cn | Tencent Cloud Computing (Beijing) Co., Ltd | CN | unknown |
3664 | FlashRepairTool.exe | 112.65.212.142:443 | tongji.flash.cn | China Unicom Shanghai network | CN | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.flash-load.ml |
| malicious |
www.download.windowsupdate.com |
| whitelisted |
tongji.flash.cn |
| whitelisted |
api.flash.cn |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1048 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .ml Domain |
10 ETPRO signatures available at the full report