| File name: | _f5e2512b17a41303dda15f6cdebcf5b7a3c78e9d8a758422ed7b8261bd6f6db1.exe |
| Full analysis: | https://app.any.run/tasks/52a4655d-424c-419f-acc3-321704e891f2 |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | August 01, 2025, 02:34:36 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | E30AA7E09A6A3FA0C250472909485F14 |
| SHA1: | 50EBB7F2FBC73020D1D1167053928FC9215A2FA0 |
| SHA256: | F5E2512B17A41303DDA15F6CDEBCF5B7A3C78E9D8A758422ED7B8261BD6F6DB1 |
| SSDEEP: | 98304:byi310UZrFCnmK7zPyGNfcoKogj0YjlPuxNc64MGwQi6kOXPGWqYl+O46PvGm9ZX:bEfgh8s1 |
MALICIOUS
REDLINE has been found (auto)
- QV5pHT0h.exe (PID: 5432)
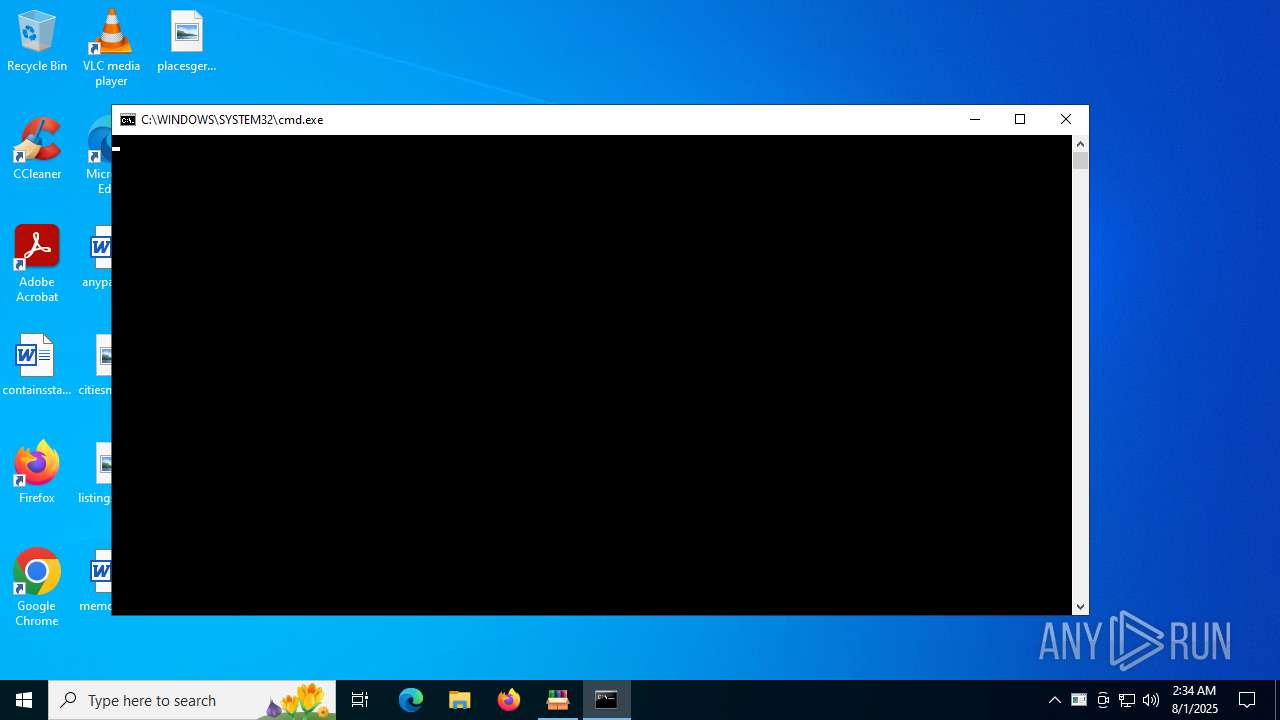
Uses Task Scheduler to run other applications
- cmd.exe (PID: 5032)
AMADEY mutex has been found
- NonwFdKX.exe (PID: 1352)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 2628)
Bypass execution policy to execute commands
- powershell.exe (PID: 4232)
Adds path to the Windows Defender exclusion list
- cmd.exe (PID: 7104)
- NSudoLG.exe (PID: 1976)
Changes the Windows auto-update feature
- reg.exe (PID: 4060)
AMADEY has been detected (YARA)
- NonwFdKX.exe (PID: 1352)
Changes Windows Defender settings
- NSudoLG.exe (PID: 1976)
SUSPICIOUS
Drops 7-zip archiver for unpacking
- _f5e2512b17a41303dda15f6cdebcf5b7a3c78e9d8a758422ed7b8261bd6f6db1.exe (PID: 4948)
- 60wd7zbc.exe (PID: 4120)
Reads security settings of Internet Explorer
- _f5e2512b17a41303dda15f6cdebcf5b7a3c78e9d8a758422ed7b8261bd6f6db1.exe (PID: 4948)
- 60wd7zbc.exe (PID: 4120)
- nircmd.exe (PID: 6816)
- NonwFdKX.exe (PID: 1352)
- Unlocker.exe (PID: 4748)
- Unlocker.exe (PID: 6452)
- Unlocker.exe (PID: 828)
Executable content was dropped or overwritten
- _f5e2512b17a41303dda15f6cdebcf5b7a3c78e9d8a758422ed7b8261bd6f6db1.exe (PID: 4948)
- QV5pHT0h.exe (PID: 5432)
- 60wd7zbc.exe (PID: 4120)
- 7z.exe (PID: 3740)
- Unlocker.exe (PID: 6452)
- Unlocker.exe (PID: 828)
Starts CMD.EXE for commands execution
- kGpnthKN.exe (PID: 2604)
- 60wd7zbc.exe (PID: 4120)
- nircmd.exe (PID: 6816)
- NSudoLG.exe (PID: 2384)
- cmd.exe (PID: 7104)
- _f5e2512b17a41303dda15f6cdebcf5b7a3c78e9d8a758422ed7b8261bd6f6db1.exe (PID: 4948)
- Unlocker.exe (PID: 4748)
- Unlocker.exe (PID: 6452)
- Unlocker.exe (PID: 828)
Executing commands from a ".bat" file
- 60wd7zbc.exe (PID: 4120)
- nircmd.exe (PID: 6816)
- NSudoLG.exe (PID: 2384)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2628)
- NSudoLG.exe (PID: 1976)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 2628)
The executable file from the user directory is run by the CMD process
- nircmd.exe (PID: 5552)
- nircmd.exe (PID: 6816)
- nircmd.exe (PID: 4172)
- NSudoLG.exe (PID: 2384)
- nircmd.exe (PID: 620)
- NSudoLG.exe (PID: 1976)
- 7z.exe (PID: 3740)
- Unlocker.exe (PID: 4748)
- Unlocker.exe (PID: 6452)
- Unlocker.exe (PID: 828)
Reads the date of Windows installation
- nircmd.exe (PID: 6816)
- Unlocker.exe (PID: 4748)
- Unlocker.exe (PID: 6452)
- Unlocker.exe (PID: 828)
Starts application with an unusual extension
- cmd.exe (PID: 1660)
- cmd.exe (PID: 5564)
- cmd.exe (PID: 7104)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 5564)
- cmd.exe (PID: 7104)
Get information on the list of running processes
- cmd.exe (PID: 7104)
- cmd.exe (PID: 6460)
The process creates files with name similar to system file names
- 60wd7zbc.exe (PID: 4120)
Application launched itself
- cmd.exe (PID: 7104)
Connects to the server without a host name
- NonwFdKX.exe (PID: 1352)
Script adds exclusion path to Windows Defender
- NSudoLG.exe (PID: 1976)
PowerShell delay command usage (probably sleep evasion)
- powershell.exe (PID: 4020)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7104)
Starts SC.EXE for service management
- cmd.exe (PID: 2348)
- cmd.exe (PID: 7104)
- cmd.exe (PID: 2716)
- cmd.exe (PID: 6384)
- cmd.exe (PID: 2460)
Windows service management via SC.EXE
- sc.exe (PID: 5460)
- sc.exe (PID: 7064)
- sc.exe (PID: 6312)
- sc.exe (PID: 6816)
- sc.exe (PID: 2428)
- sc.exe (PID: 768)
- sc.exe (PID: 2348)
- sc.exe (PID: 3396)
- sc.exe (PID: 6236)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 6388)
- cmd.exe (PID: 4832)
Stops a currently running service
- sc.exe (PID: 1160)
- sc.exe (PID: 1636)
- sc.exe (PID: 3584)
- sc.exe (PID: 3108)
- sc.exe (PID: 4544)
- sc.exe (PID: 2992)
Creates or modifies Windows services
- reg.exe (PID: 4648)
- Unlocker.exe (PID: 6452)
Drops a system driver (possible attempt to evade defenses)
- Unlocker.exe (PID: 6452)
- Unlocker.exe (PID: 828)
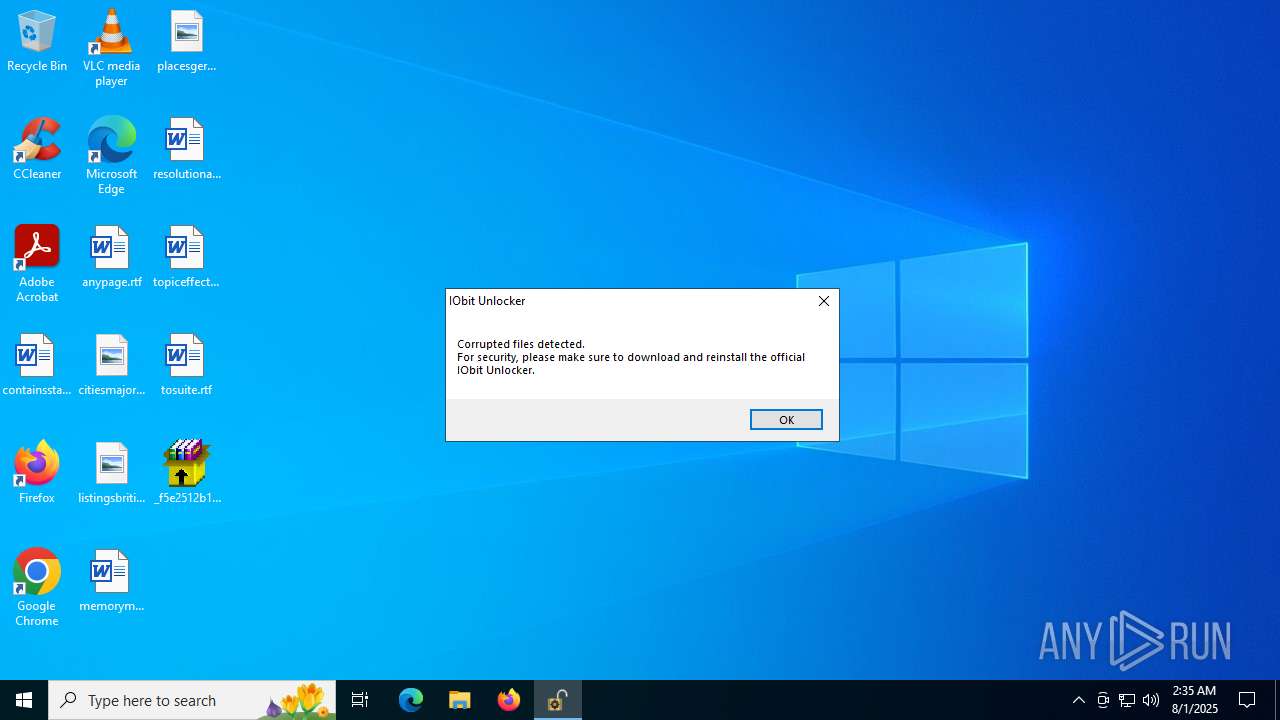
The process verifies whether the antivirus software is installed
- Unlocker.exe (PID: 828)
- IObitUnlocker.exe (PID: 3288)
There is functionality for enable RDP (YARA)
- NonwFdKX.exe (PID: 1352)
There is functionality for taking screenshot (YARA)
- NonwFdKX.exe (PID: 1352)
INFO
Checks supported languages
- _f5e2512b17a41303dda15f6cdebcf5b7a3c78e9d8a758422ed7b8261bd6f6db1.exe (PID: 4948)
- kGpnthKN.exe (PID: 2604)
- QV5pHT0h.exe (PID: 5432)
- NonwFdKX.exe (PID: 1352)
- chcp.com (PID: 1980)
- nircmd.exe (PID: 5552)
- nircmd.exe (PID: 6816)
- nircmd.exe (PID: 4172)
- chcp.com (PID: 4552)
- nircmd.exe (PID: 620)
- chcp.com (PID: 4020)
- mode.com (PID: 6344)
- 60wd7zbc.exe (PID: 4120)
- NSudoLG.exe (PID: 2384)
- NSudoLG.exe (PID: 1976)
- 7z.exe (PID: 3740)
- Unlocker.exe (PID: 4748)
- Unlocker.exe (PID: 6452)
- Unlocker.exe (PID: 828)
- IObitUnlocker.exe (PID: 3288)
- IObitUnlocker.exe (PID: 4916)
Reads the computer name
- _f5e2512b17a41303dda15f6cdebcf5b7a3c78e9d8a758422ed7b8261bd6f6db1.exe (PID: 4948)
- 60wd7zbc.exe (PID: 4120)
- QV5pHT0h.exe (PID: 5432)
- NonwFdKX.exe (PID: 1352)
- nircmd.exe (PID: 6816)
- NSudoLG.exe (PID: 2384)
- NSudoLG.exe (PID: 1976)
- 7z.exe (PID: 3740)
- Unlocker.exe (PID: 4748)
- Unlocker.exe (PID: 6452)
- IObitUnlocker.exe (PID: 3288)
- Unlocker.exe (PID: 828)
- IObitUnlocker.exe (PID: 4916)
The sample compiled with english language support
- _f5e2512b17a41303dda15f6cdebcf5b7a3c78e9d8a758422ed7b8261bd6f6db1.exe (PID: 4948)
- 60wd7zbc.exe (PID: 4120)
- Unlocker.exe (PID: 6452)
- Unlocker.exe (PID: 828)
Process checks computer location settings
- _f5e2512b17a41303dda15f6cdebcf5b7a3c78e9d8a758422ed7b8261bd6f6db1.exe (PID: 4948)
- 60wd7zbc.exe (PID: 4120)
- nircmd.exe (PID: 6816)
Reads mouse settings
- kGpnthKN.exe (PID: 2604)
Create files in a temporary directory
- 60wd7zbc.exe (PID: 4120)
- 7z.exe (PID: 3740)
NirSoft software is detected
- nircmd.exe (PID: 5552)
- nircmd.exe (PID: 6816)
- nircmd.exe (PID: 4172)
- nircmd.exe (PID: 620)
Changes the display of characters in the console
- cmd.exe (PID: 1660)
- cmd.exe (PID: 5564)
- cmd.exe (PID: 7104)
Starts MODE.COM to configure console settings
- mode.com (PID: 6344)
Checks proxy server information
- NonwFdKX.exe (PID: 1352)
- slui.exe (PID: 6680)
Checks operating system version
- cmd.exe (PID: 7104)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 4020)
- powershell.exe (PID: 4232)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4020)
Reads the machine GUID from the registry
- Unlocker.exe (PID: 4748)
- Unlocker.exe (PID: 6452)
- Unlocker.exe (PID: 828)
Manual execution by a user
- IObitUnlocker.exe (PID: 2040)
- IObitUnlocker.exe (PID: 4916)
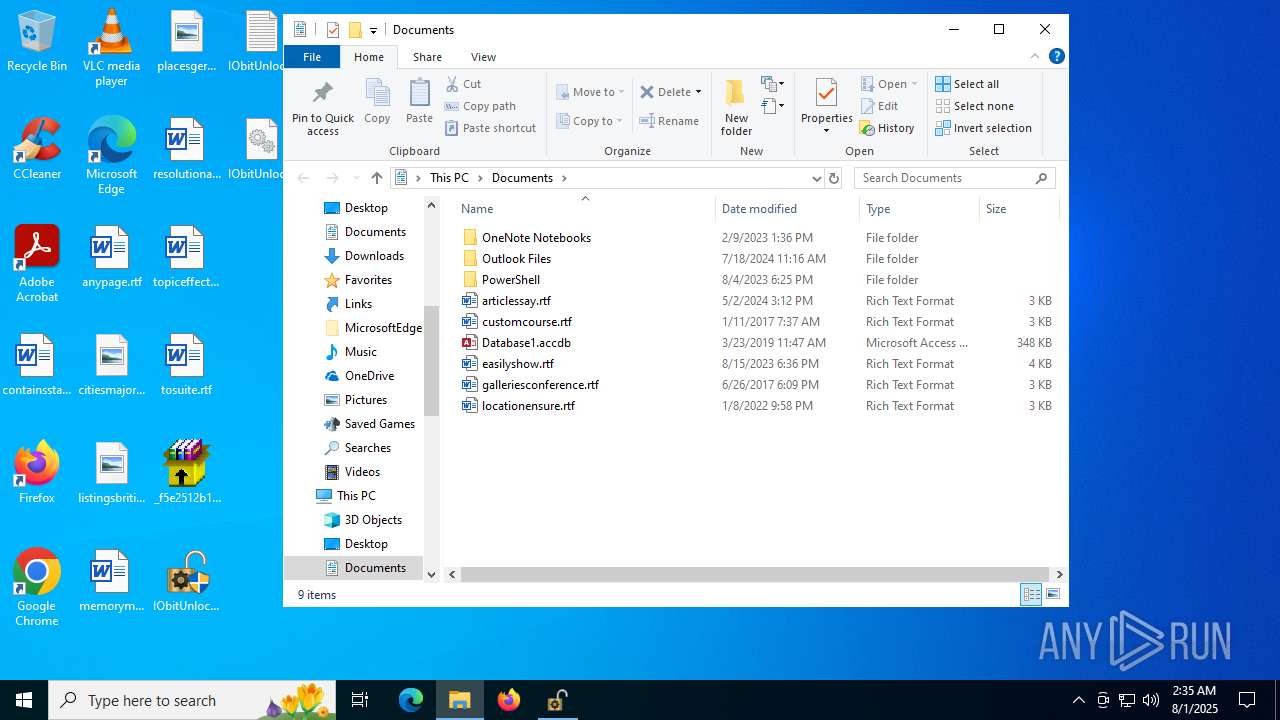
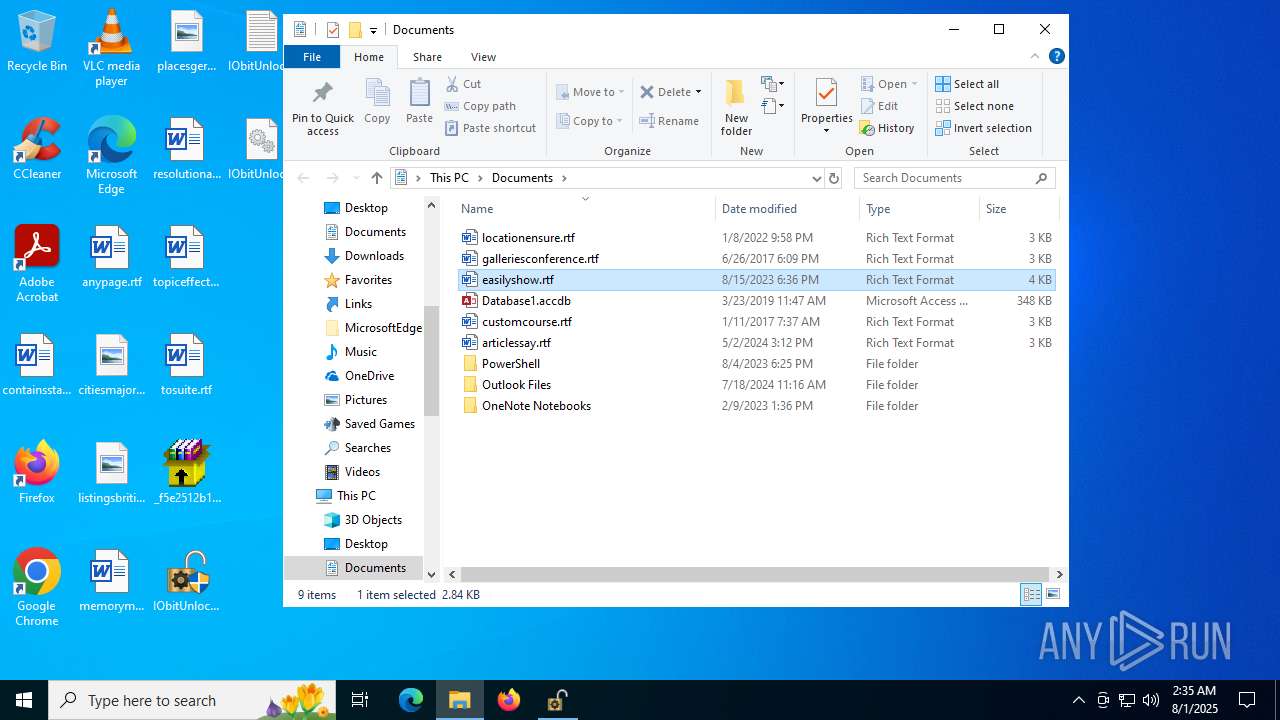
Creates files in the program directory
- IObitUnlocker.exe (PID: 4916)
Reads the software policy settings
- slui.exe (PID: 6680)
Compiled with Borland Delphi (YARA)
- IObitUnlocker.exe (PID: 4916)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Amadey
(PID) Process(1352) NonwFdKX.exe
C294.154.35.25
URLhttp://94.154.35.25/di9ku38f/index.php
Version5.55
Options
Drop directory96a319e745
Drop nameSrxelqcif.exe
Strings (125)os:
" && timeout 1 && del
\App
&&
|
shutdown -s -t 0
Panda Security
r=
:::
" && ren
pc:
random
ProductName
bi:
#
POST
2016
msi
Content-Type: application/x-www-form-urlencoded
0123456789
0000043f
un:
st=s
S-%lu-
SYSTEM\CurrentControlSet\Control\ComputerName\ComputerName
AVAST Software
cmd
Content-Disposition: form-data; name="data"; filename="
SOFTWARE\Microsoft\Windows NT\CurrentVersion
lv:
<c>
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders
00000423
<d>
cred.dll|clip.dll|
exe
og:
Srxelqcif.exe
Powershell.exe
Comodo
5.55
&& Exit"
Startup
%-lu
DefaultSettings.YResolution
SYSTEM\CurrentControlSet\Control\UnitedVideo\CONTROL\VIDEO\
00000422
rundll32
2019
ps1
ar:
%USERPROFILE%
vs:
-executionpolicy remotesigned -File "
shell32.dll
/k
WinDefender
------
http://
cred.dll
Main
Bitdefender
.jpg
?scr=1
"taskkill /f /im "
rb
CurrentBuild
id:
Doctor Web
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
94.154.35.25
ESET
Sophos
00000419
VideoID
dm:
96a319e745
Keyboard Layout\Preload
AVG
------
SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce
2025
--
"
DefaultSettings.XResolution
/quiet
Norton
SYSTEM\ControlSet001\Services\BasicDisplay\Video
dll
zip
=
ProgramData\
cmd /C RMDIR /s/q
/Plugins/
e1
Programs
d1
&unit=
Rem
ComputerName
2022
rundll32.exe
e3
e2
Content-Type: multipart/form-data; boundary=----
-%lu
clip.dll
av:
kernel32.dll
GetNativeSystemInfo
360TotalSecurity
\0000
"
Content-Type: application/octet-stream
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders
+++
Kaspersky Lab
Avira
\
GET
/di9ku38f/index.php
sd:
abcdefghijklmnopqrstuvwxyz0123456789-_
wb
https://
-unicode-
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:03:03 13:15:57+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.3 |
| CodeSize: | 203776 |
| InitializedDataSize: | 77312 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1f530 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
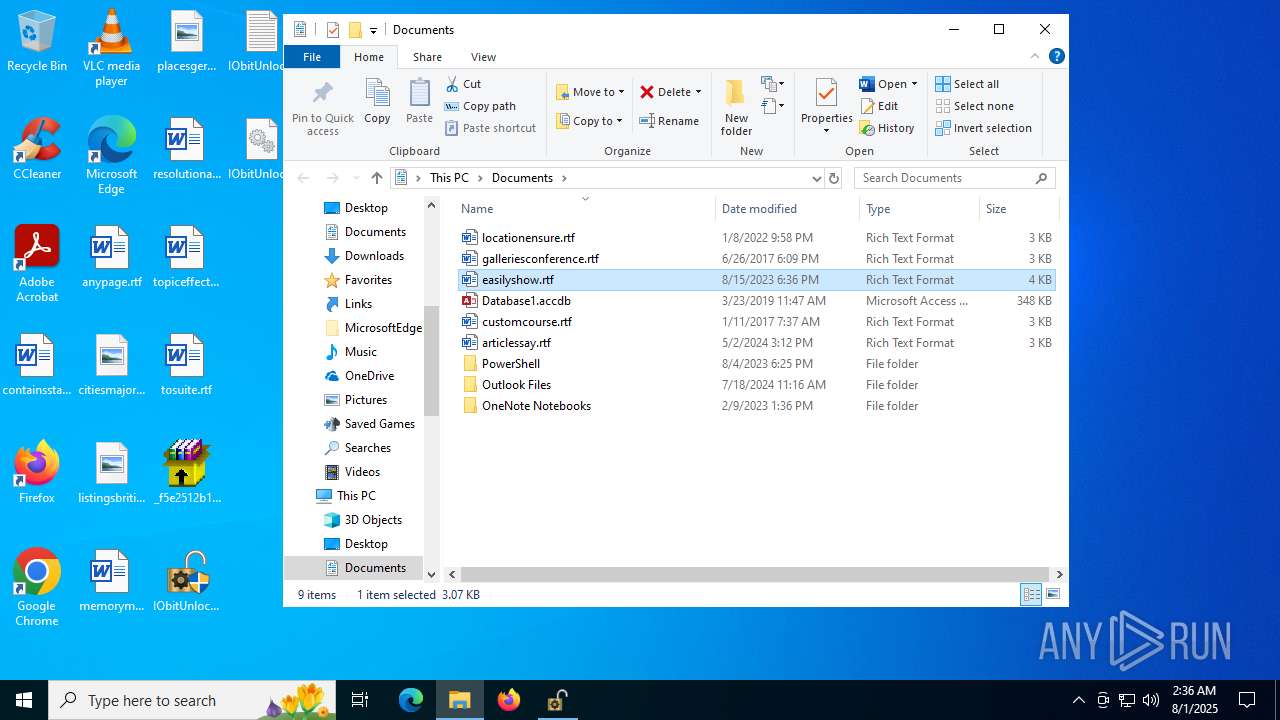
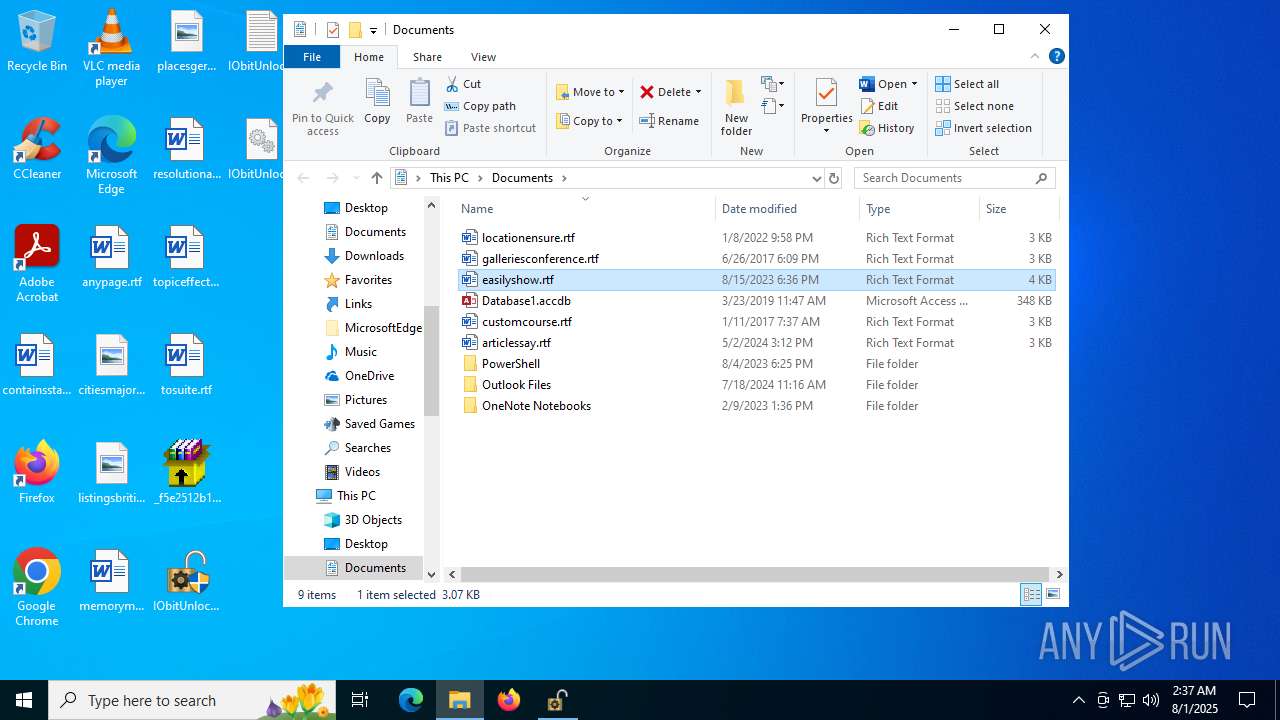
Total processes
254
Monitored processes
112
Malicious processes
14
Suspicious processes
4
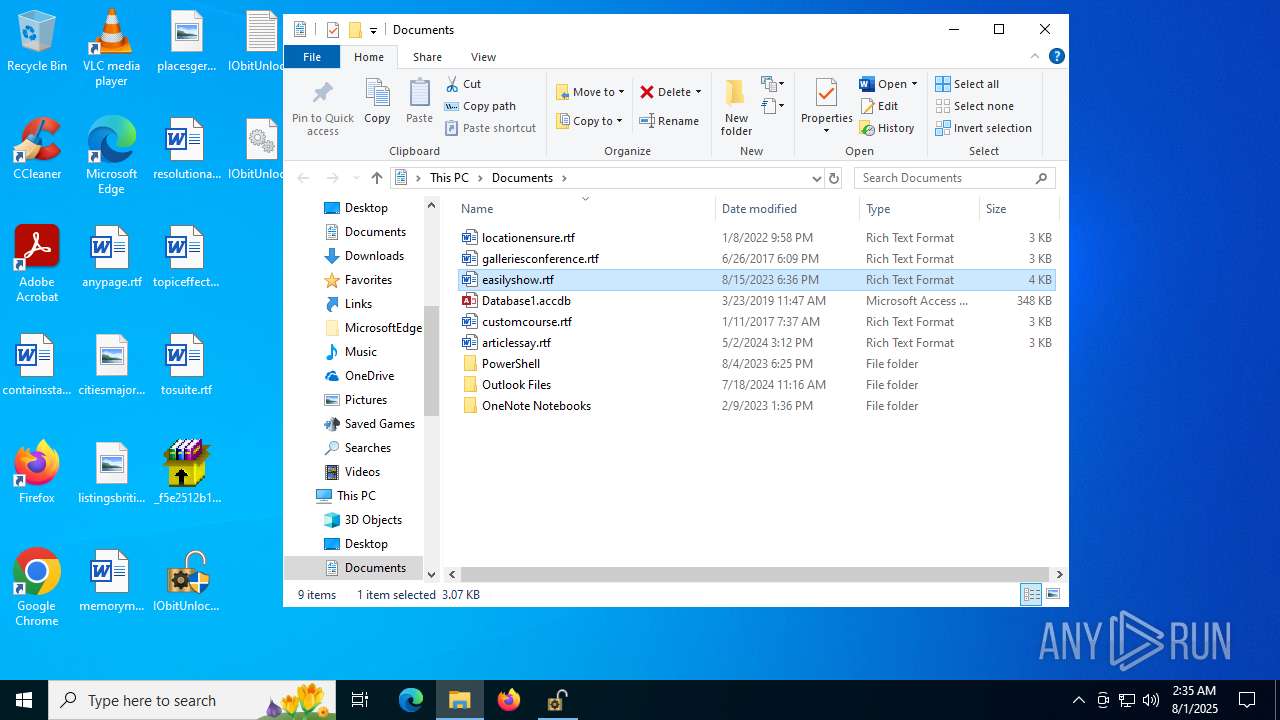
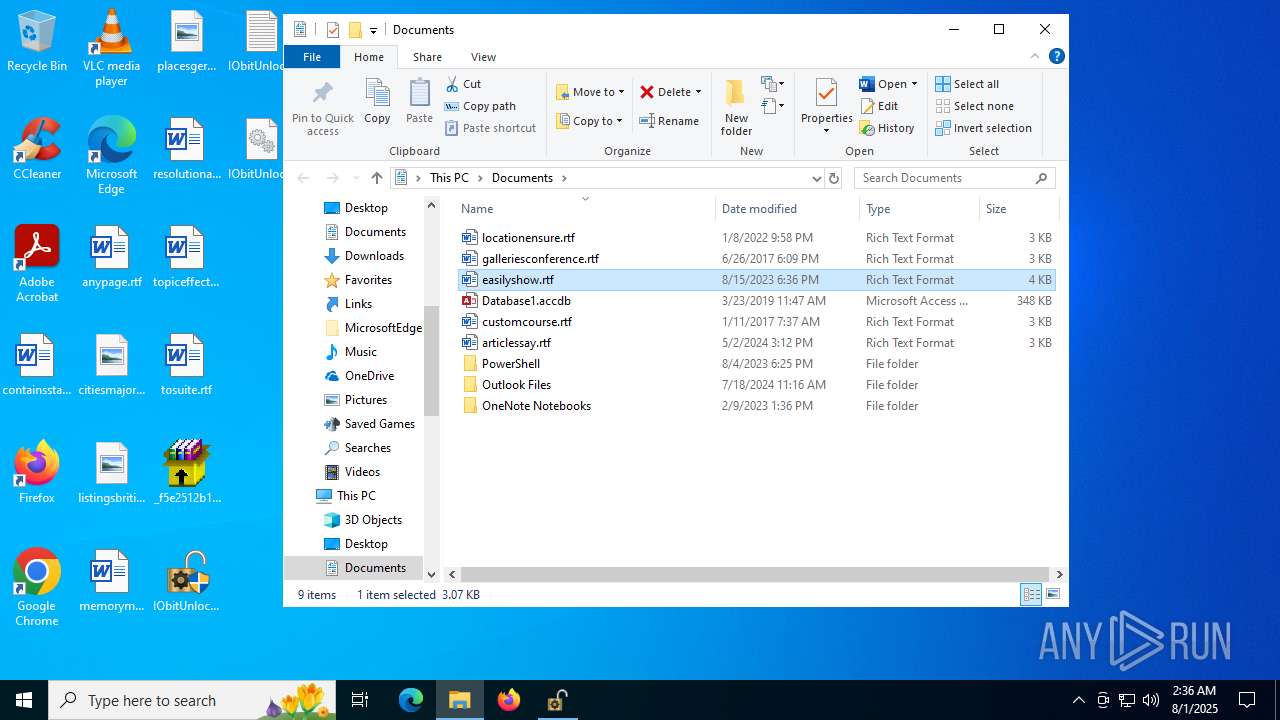
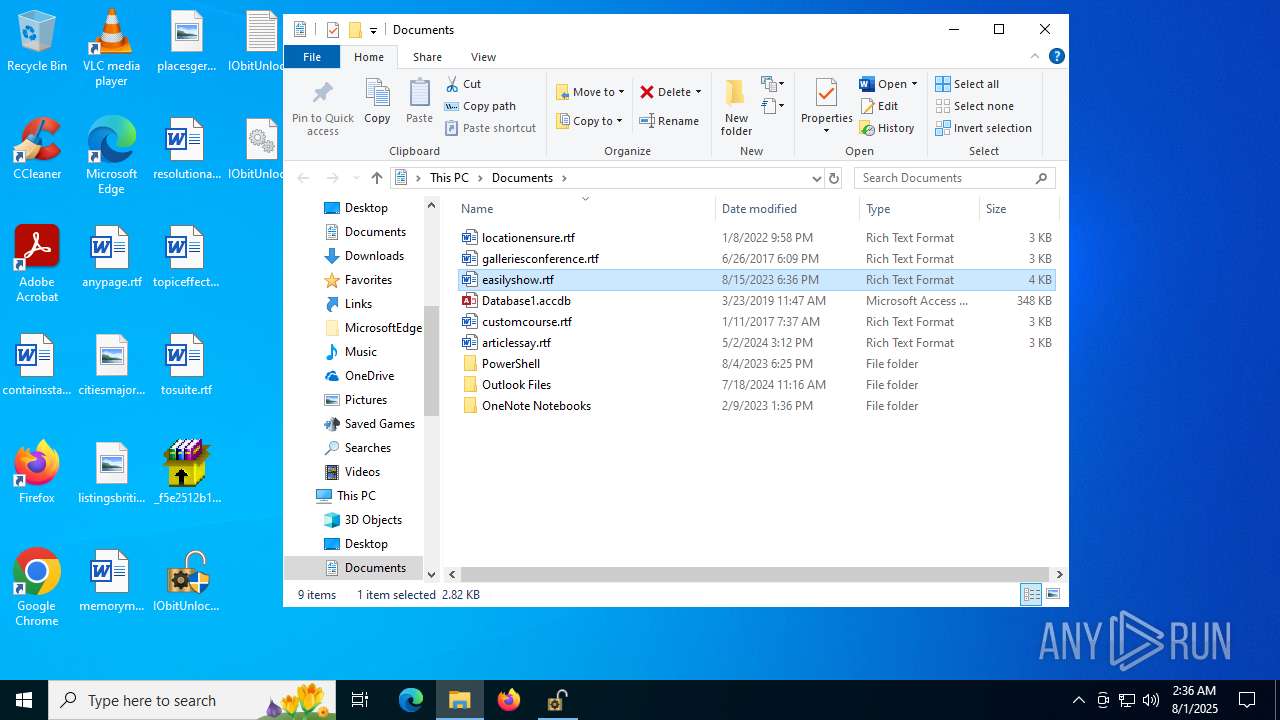
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 440 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 620 | nircmd win min process "cmd.exe" | C:\Users\admin\AppData\Local\Temp\Work\nircmd.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: NirSoft Integrity Level: SYSTEM Description: NirCmd Exit code: 0 Version: 2.87 Modules
| |||||||||||||||
| 684 | reg query "HKLM\System\CurrentControlSet\Services\WdBoot" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 768 | reg query "HKU\S-1-5-19" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 768 | sc config WaaSMedicSvc start= disabled | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 828 | Unlocker /DelWD | C:\Users\admin\AppData\Local\Temp\Work\Unlocker.exe | cmd.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Description: Unlocker by Eject NotOfficial Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 984 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1036 | findstr /c:"6.1.7601" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1036 | reg add "HKLM\TEMP_SYSTEM\ControlSet001\Services\UsoSvc" /v Start /t REG_DWORD /d 4 /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1040 | "C:\Windows\System32\cmd.exe" /c start "" /min "kGpnthKN.exe" & start "" /min "60wd7zbc.exe" | C:\Windows\SysWOW64\cmd.exe | — | _f5e2512b17a41303dda15f6cdebcf5b7a3c78e9d8a758422ed7b8261bd6f6db1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
21 675
Read events
21 660
Write events
15
Delete events
0
Modification events
| (PID) Process: | (4100) reg.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Themes\Personalize |
| Operation: | write | Name: | AppsUseLightTheme |
Value: 0 | |||
| (PID) Process: | (6816) nircmd.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\WINDOWS\System32\cmd.exe.FriendlyAppName |
Value: Windows Command Processor | |||
| (PID) Process: | (6816) nircmd.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\WINDOWS\System32\cmd.exe.ApplicationCompany |
Value: Microsoft Corporation | |||
| (PID) Process: | (1352) NonwFdKX.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1352) NonwFdKX.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1352) NonwFdKX.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4024) reg.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Themes\Personalize |
| Operation: | write | Name: | AppsUseLightTheme |
Value: 0 | |||
| (PID) Process: | (4748) Unlocker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\DK |
| Operation: | write | Name: | CurrentDiskSize |
Value: 228535599104 | |||
| (PID) Process: | (1976) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\WindowsUpdate |
| Operation: | write | Name: | DisableWindowsUpdateAccess |
Value: 1 | |||
| (PID) Process: | (4648) reg.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\WaaSMedicSvc |
| Operation: | write | Name: | Start |
Value: 4 | |||
Executable files
15
Suspicious files
5
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4948 | _f5e2512b17a41303dda15f6cdebcf5b7a3c78e9d8a758422ed7b8261bd6f6db1.exe | C:\ADymsba\kGpnthKN.exe | executable | |
MD5:405C07F357C1EFF92105774A682752C9 | SHA256:B564FB1357C9095120AF4882C80DC545904861EAA8CDA4ED3580F0C22D3E4EDB | |||
| 4120 | 60wd7zbc.exe | C:\Users\admin\AppData\Local\Temp\Work\cecho.exe | executable | |
MD5:E783BC59D0ED6CFBD8891F94AE23D1B3 | SHA256:5C1211559DDA10592CFEDD57681F18F4A702410816D36EDA95AEE6C74E3C6A47 | |||
| 4948 | _f5e2512b17a41303dda15f6cdebcf5b7a3c78e9d8a758422ed7b8261bd6f6db1.exe | C:\ADymsba\l8APwFuw.zip | compressed | |
MD5:9932291AB3AD87DE5C204940ADBB13C6 | SHA256:6B50328C7B9A79AD756783C559FD6296A30D3DE9C686F9ACFD57C128D93821B4 | |||
| 4948 | _f5e2512b17a41303dda15f6cdebcf5b7a3c78e9d8a758422ed7b8261bd6f6db1.exe | C:\ADymsba\QV5pHT0h.exe | executable | |
MD5:426CCB645E50A3143811CFA0E42E2BA6 | SHA256:CF878BFBD9ED93DC551AC038AFF8A8BBA4C935DDF8D48E62122BDDFDB3E08567 | |||
| 4232 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:5A9DC4BB934F37C09ABC791A54A6127E | SHA256:BC6EAC896EC7F380F4CC716A1D38BF0647EB987AC776F7F0A64393D1EE1BF265 | |||
| 4948 | _f5e2512b17a41303dda15f6cdebcf5b7a3c78e9d8a758422ed7b8261bd6f6db1.exe | C:\ADymsba\60wd7zbc.exe | executable | |
MD5:718C30968315825A246B7D8BFD92CA4D | SHA256:31D25959F1DCFAF5D04EEF7B2D3A30AFE674DB1B13130D475EE9C334351AD90D | |||
| 4120 | 60wd7zbc.exe | C:\Users\admin\AppData\Local\Temp\GFVBdE7.bat | text | |
MD5:C2DF80F14AD294A279ED4F4F251960A5 | SHA256:D6E5A4BFA17BC9B9D9AF48FB6CEE2024477F309B48E670F8F49B7720205AAA43 | |||
| 4120 | 60wd7zbc.exe | C:\Users\admin\AppData\Local\Temp\Work\NSudoLG.exe | executable | |
MD5:423129DDB24FB923F35B2DD5787B13DD | SHA256:5094AD359D8CF6DC5324598605C35F68519CC5AF9C7ED5427E02A6B28121E4C7 | |||
| 3740 | 7z.exe | C:\Users\admin\AppData\Local\Temp\Work\Unlocker.exe | executable | |
MD5:FC5496745D6FD03B3F9B8AC9C9FD6C38 | SHA256:1B38B61CF323C7E2DBBD155A1639878A4C93DAC73707C1C1879B94A56C63A951 | |||
| 6452 | Unlocker.exe | C:\Windows\Temp\IObitUnlocker.zip | compressed | |
MD5:6833604A8B0F0BD4E65F14D5DEDB13FD | SHA256:F81163FE8E7C95157797F4D955BB6E9FCBB4C0E16A0798D459974E3320DAB942 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
46
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5824 | RUXIMICS.exe | GET | 200 | 23.216.77.42:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.42:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.42:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | POST | 200 | 20.190.159.129:443 | https://login.live.com/RST2.srf | unknown | xml | 1.24 Kb | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1352 | NonwFdKX.exe | POST | 200 | 94.154.35.25:80 | http://94.154.35.25/di9ku38f/index.php | unknown | — | — | malicious |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 400 | 40.126.31.0:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | whitelisted |
5824 | RUXIMICS.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 400 | 40.126.31.71:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5824 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.216.77.42:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.216.77.42:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5824 | RUXIMICS.exe | 23.216.77.42:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1268 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
Threats
Process | Message |
|---|---|
IObitUnlocker.exe | PostAction_Delete |
IObitUnlocker.exe | C:\ProgramData\Microsoft\Windows Defender-------- |
IObitUnlocker.exe | FileCount:264 |
IObitUnlocker.exe | C:\ProgramData\Microsoft\Windows Defender Advanced Threat Protection-------- |
IObitUnlocker.exe | C:\ProgramData\Microsoft\Windows Security Health-------- |
IObitUnlocker.exe | C:\ProgramData\Microsoft\Storage Health-------- |
IObitUnlocker.exe | C:\Program Files\Windows Defender-------- |
IObitUnlocker.exe | C:\Program Files\Windows Defender Advanced Threat Protection-------- |
IObitUnlocker.exe | C:\Program Files\Windows Security-------- |
IObitUnlocker.exe | C:\Program Files\PCHealthCheck-------- |