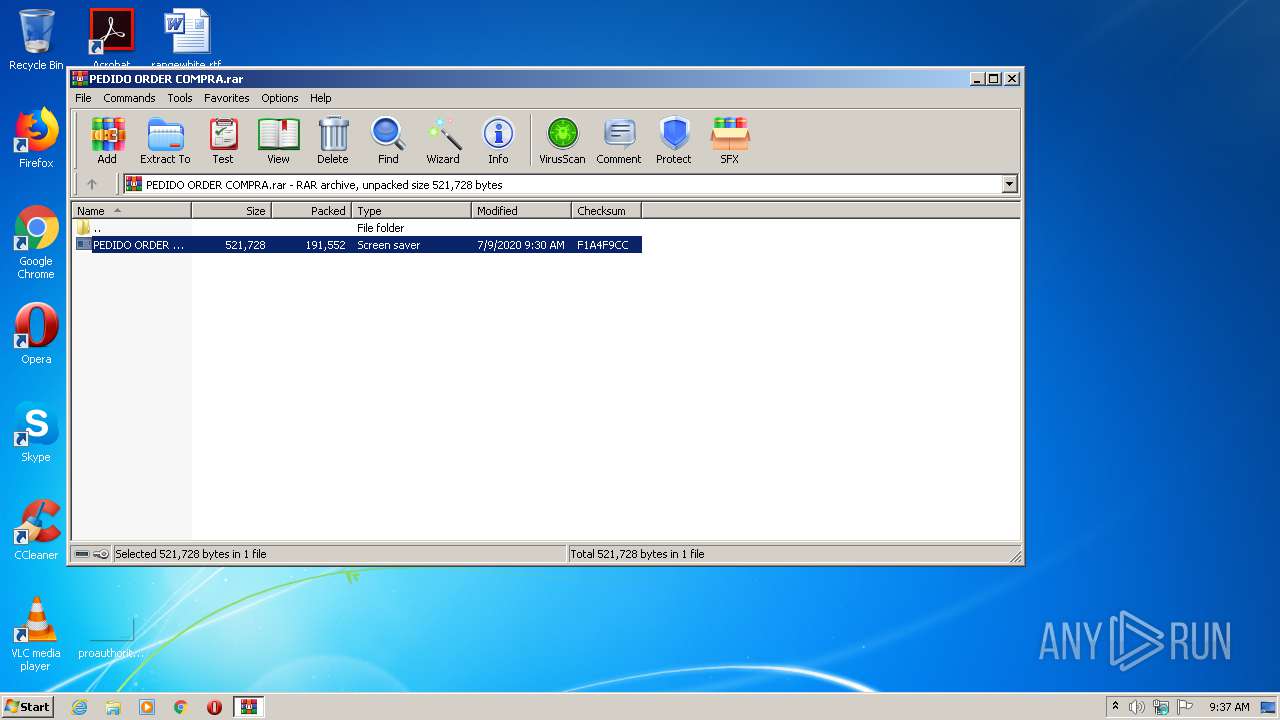
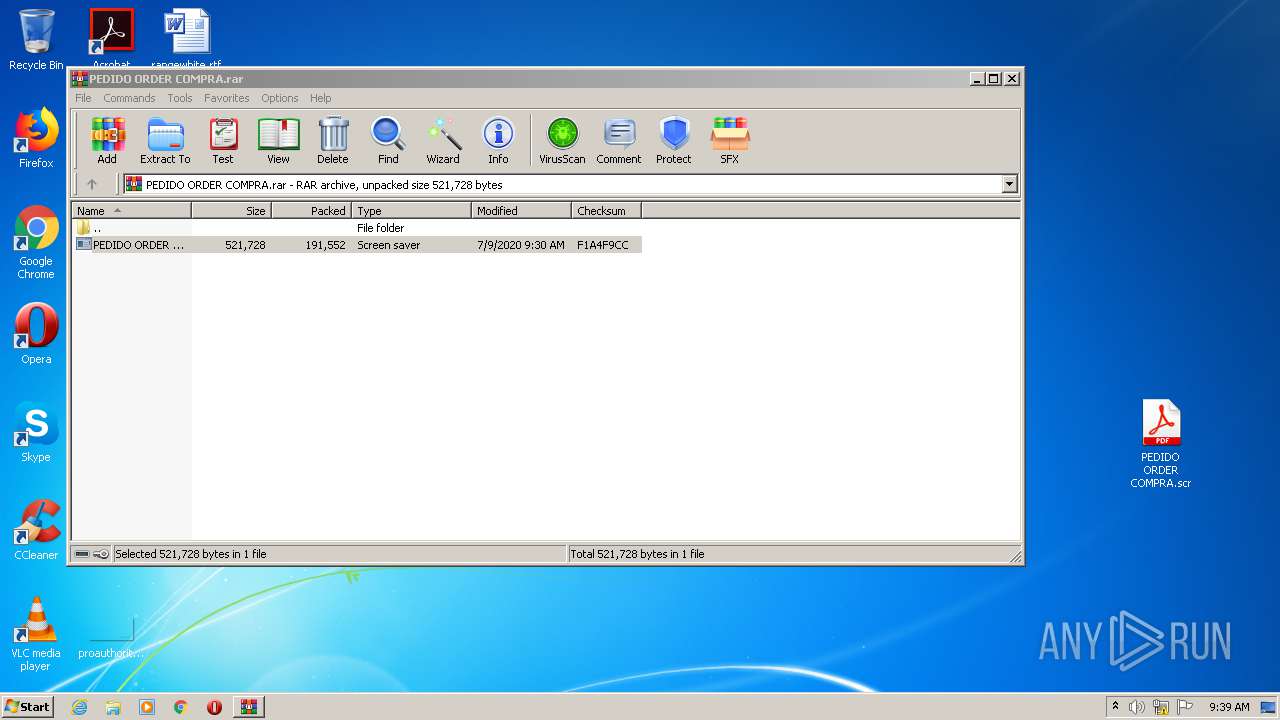
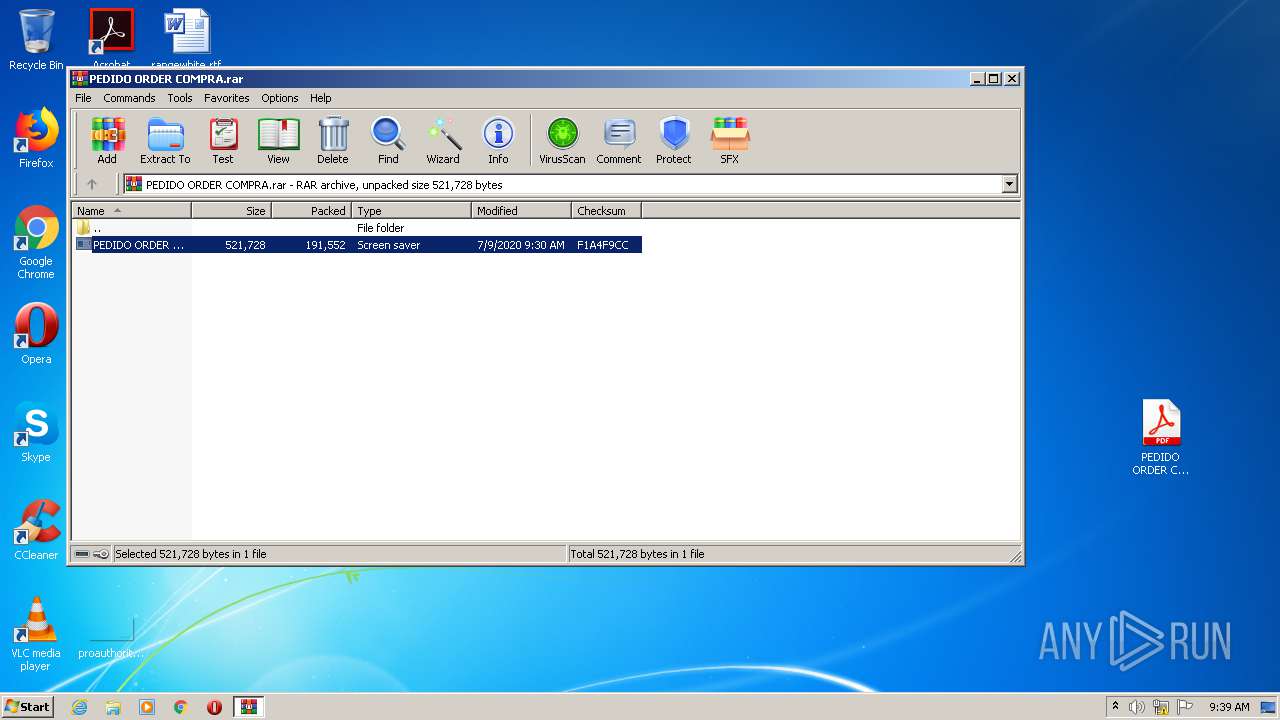
| File name: | PEDIDO ORDER COMPRA.rar |
| Full analysis: | https://app.any.run/tasks/d029abdc-d400-4cdf-952b-95ddd8e1c142 |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | July 12, 2020, 08:36:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
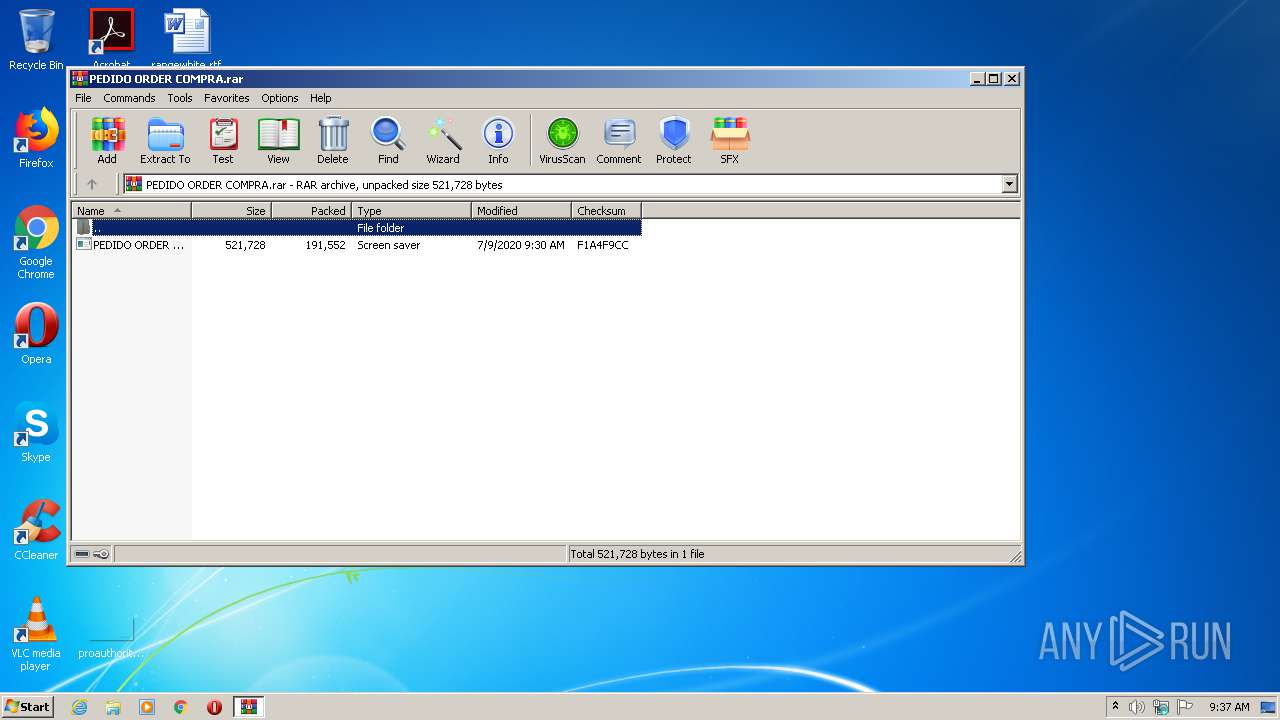
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | C90D978305B8BA64DD04CD567662F4A2 |
| SHA1: | 692C53E8E7F9D47055DF105DE282DC2C639D0DAB |
| SHA256: | F5352F5941FCC11A9ABC5B72FCB3A5B0F1F1575536588D2A1E87FAB87AFD80B4 |
| SSDEEP: | 3072:tOR0RZPQhfL/JCjKTsw3UzKD2wKRkLHSgxEhwKmg9akgZugsmNY3xHu6i1WnlseL:uWyLhTswkzKDrR1xVy9AJbNY3xVK4sHW |
MALICIOUS
Application was dropped or rewritten from another process
- AddInProcess32.exe (PID: 2784)
- PEDIDO ORDER COMPRA.scr (PID: 3308)
- PEDIDO ORDER COMPRA.scr (PID: 3068)
- PEDIDO ORDER COMPRA.scr (PID: 2940)
- PEDIDO ORDER COMPRA.scr (PID: 3120)
- igfxext4sb.exe (PID: 3864)
- PEDIDO ORDER COMPRA.scr (PID: 4088)
- AddInProcess32.exe (PID: 2004)
- PEDIDO ORDER COMPRA.scr (PID: 3024)
- AddInProcess32.exe (PID: 2168)
FORMBOOK was detected
- explorer.exe (PID: 292)
- colorcpl.exe (PID: 3392)
- Firefox.exe (PID: 3000)
Changes the autorun value in the registry
- colorcpl.exe (PID: 3392)
Connects to CnC server
- explorer.exe (PID: 292)
Actions looks like stealing of personal data
- colorcpl.exe (PID: 3392)
Stealing of credential data
- colorcpl.exe (PID: 3392)
SUSPICIOUS
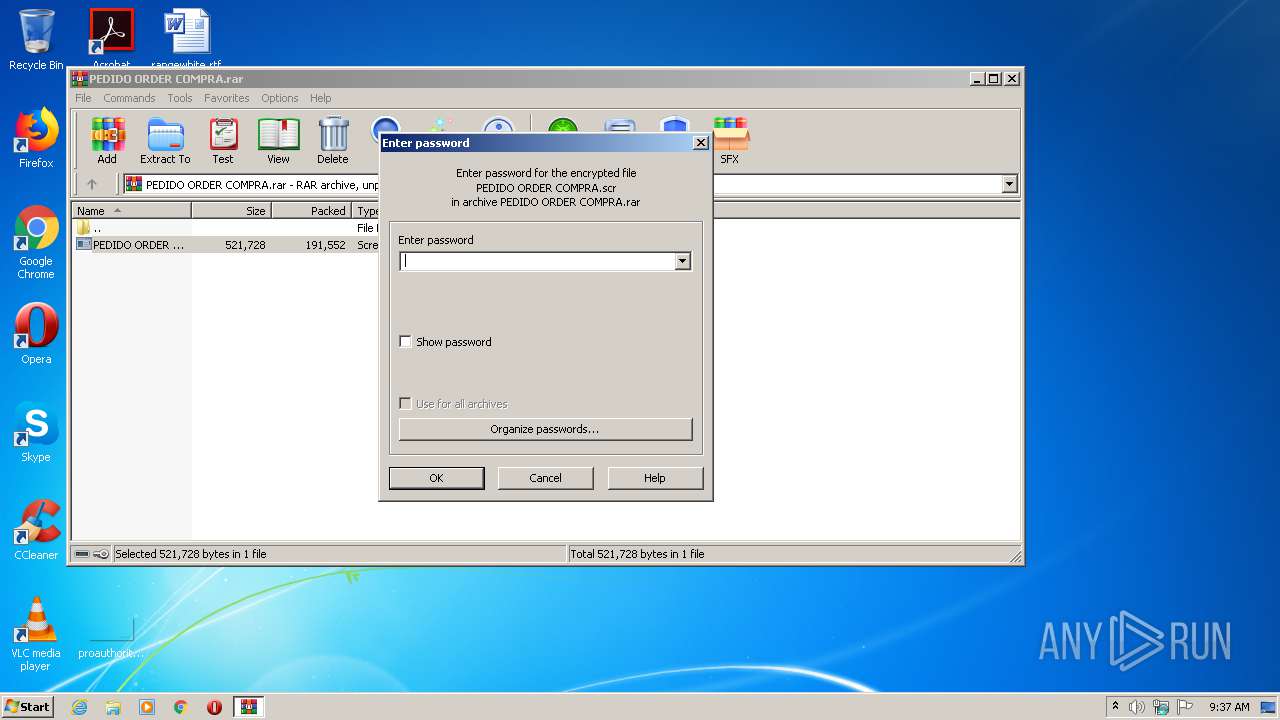
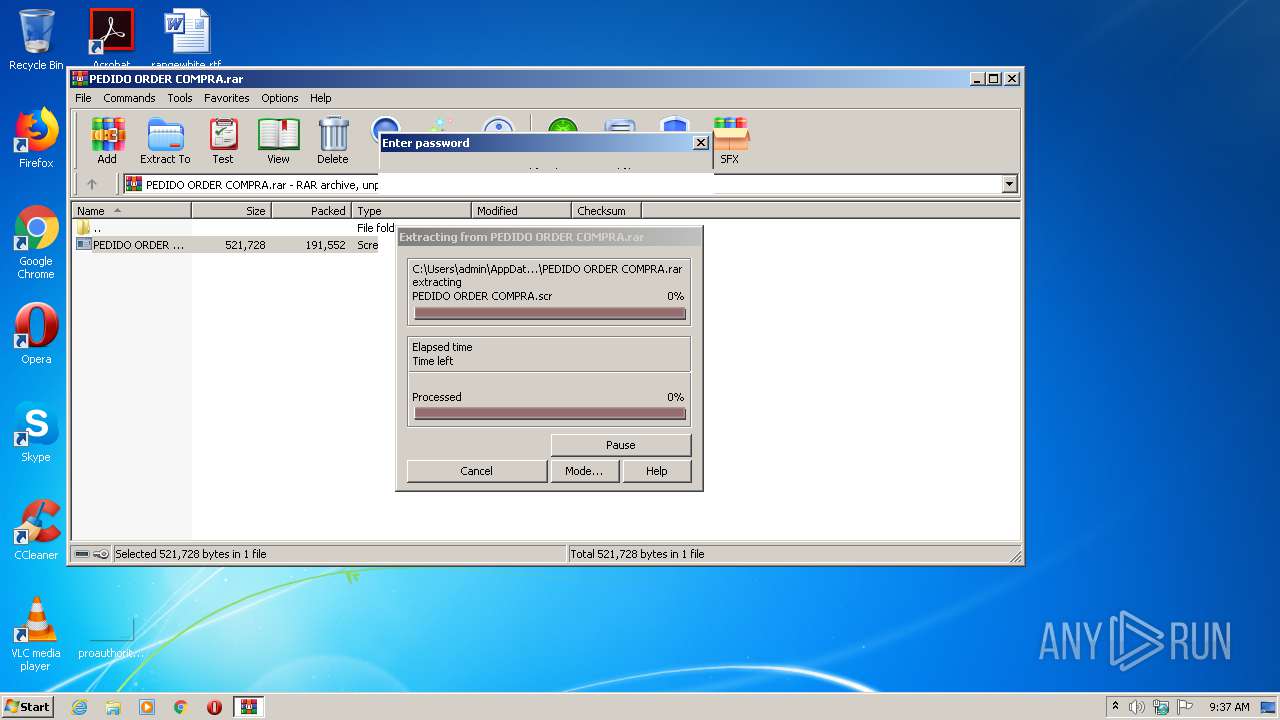
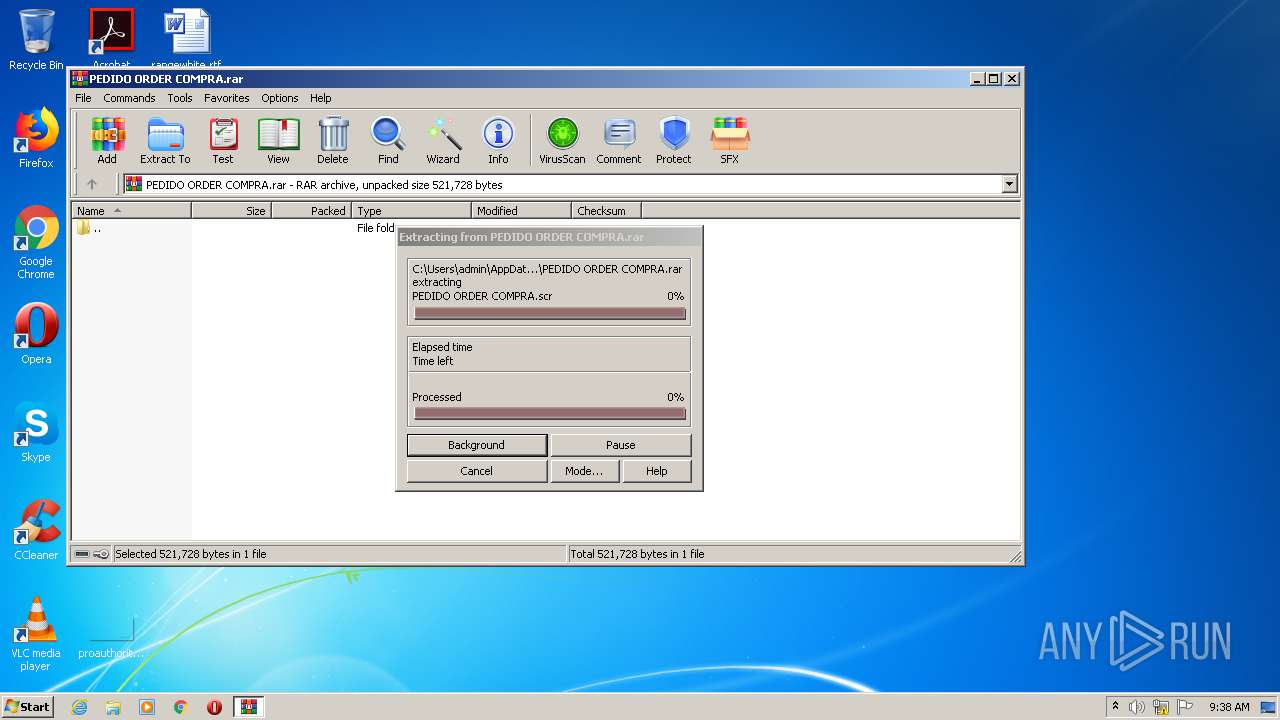
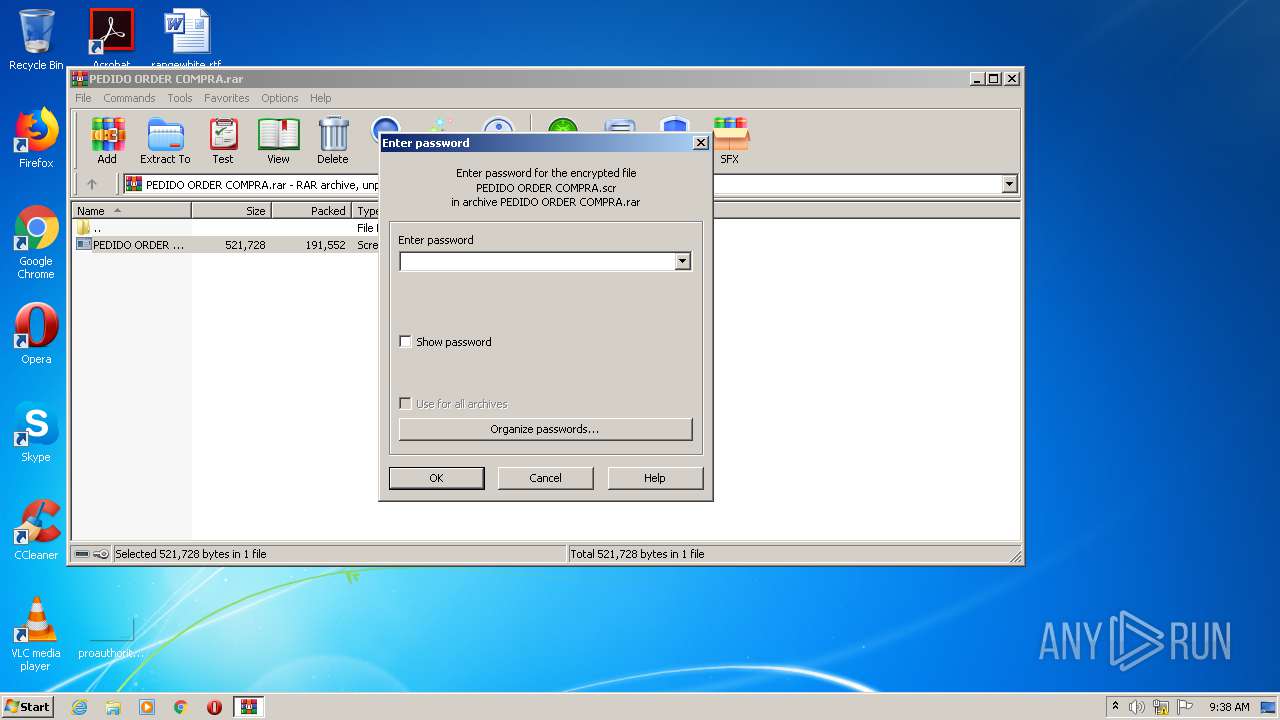
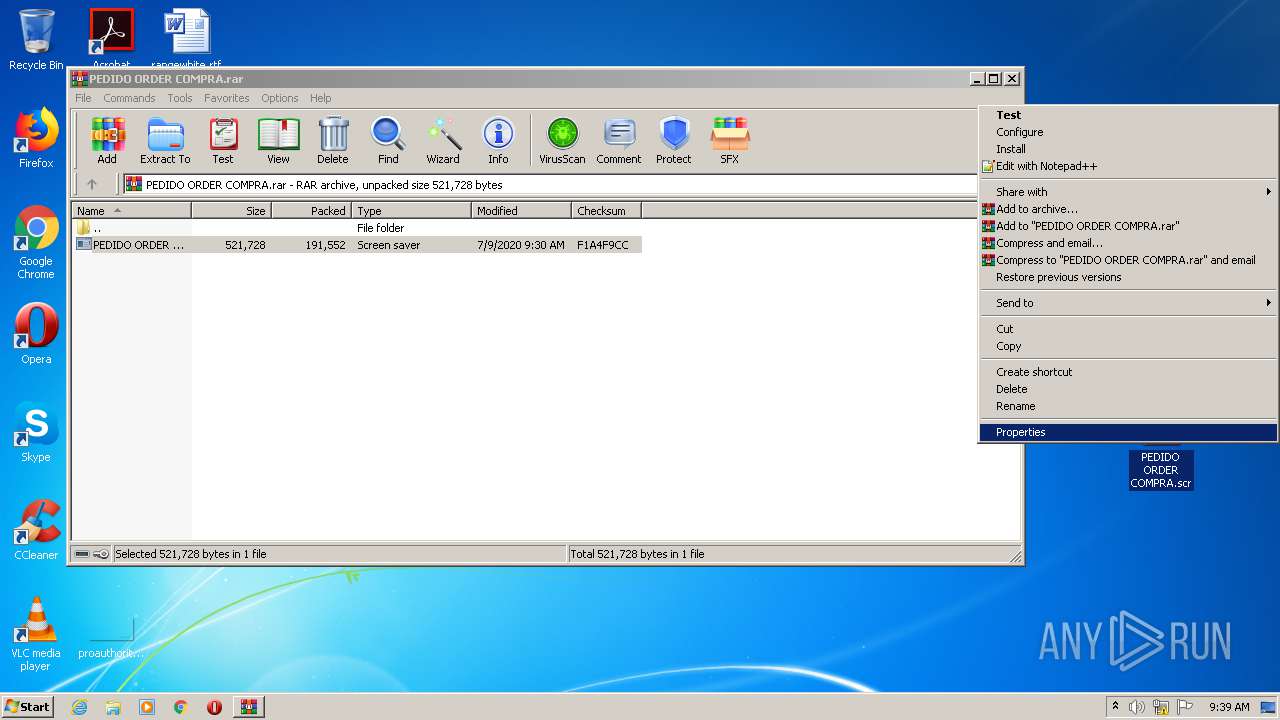
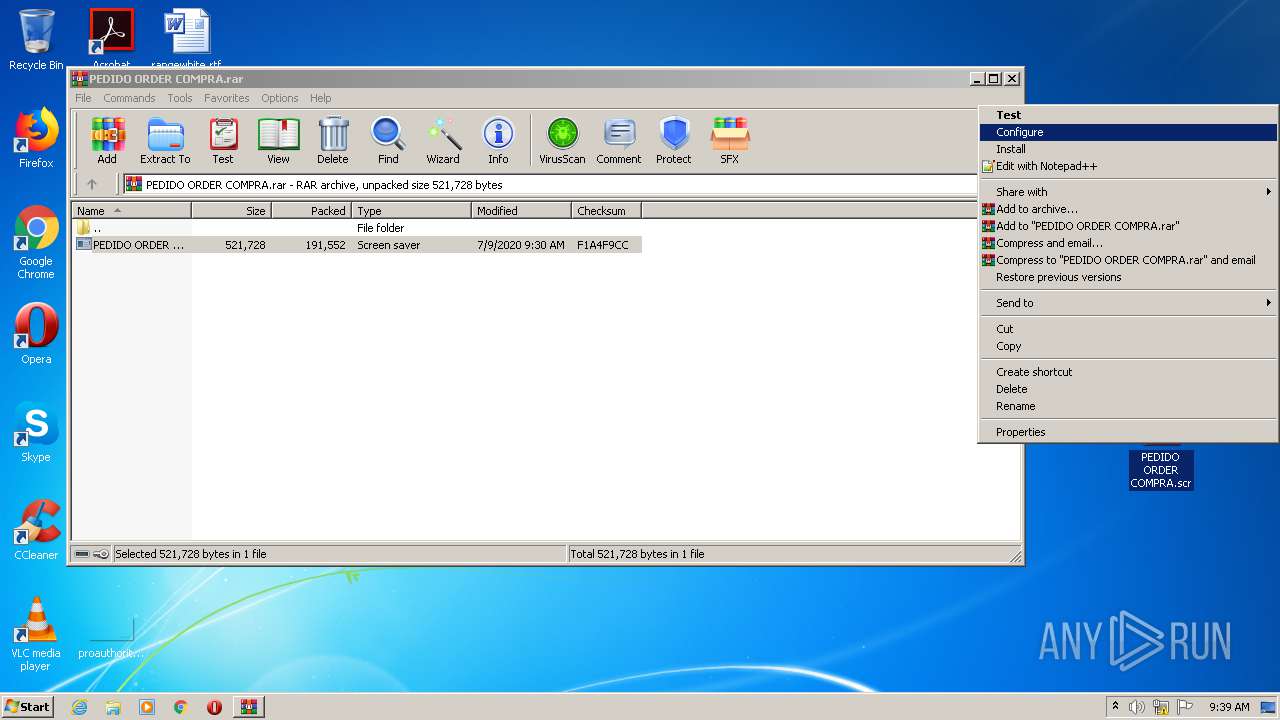
Executable content was dropped or overwritten
- WinRAR.exe (PID: 632)
- PEDIDO ORDER COMPRA.scr (PID: 3308)
- PEDIDO ORDER COMPRA.scr (PID: 3120)
- explorer.exe (PID: 292)
- DllHost.exe (PID: 2828)
Starts CMD.EXE for commands execution
- colorcpl.exe (PID: 3392)
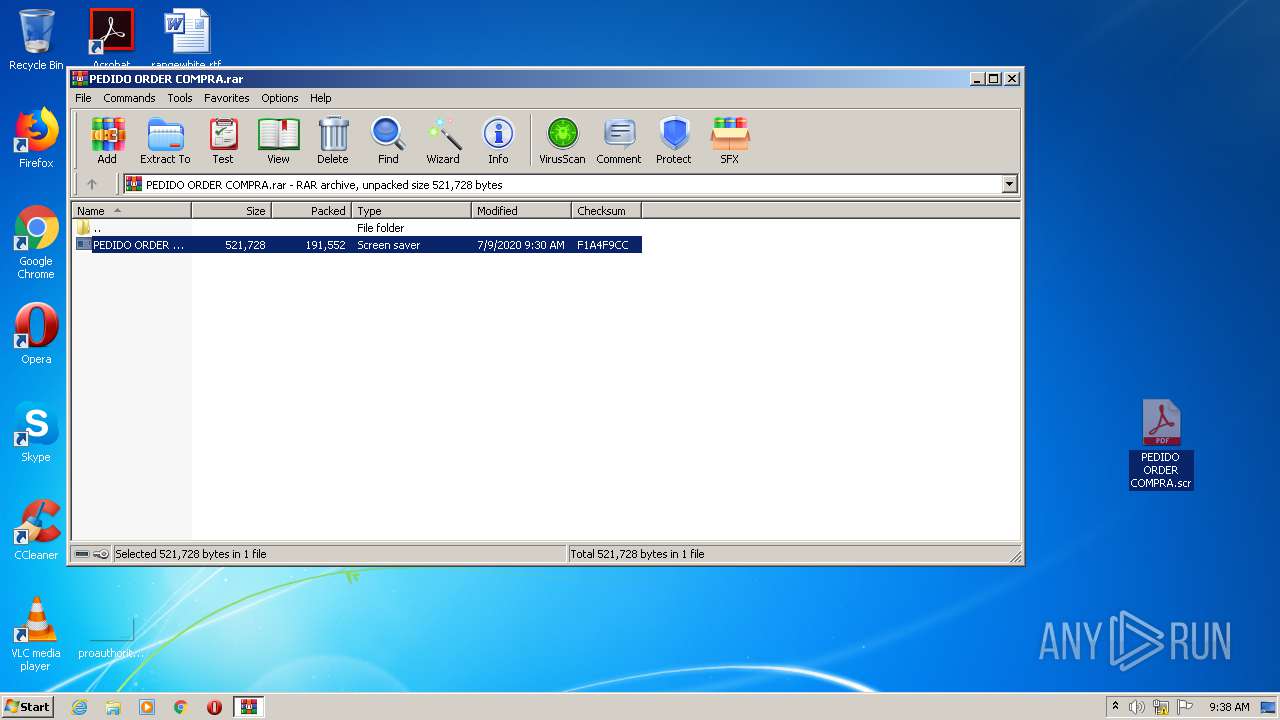
Starts application with an unusual extension
- WinRAR.exe (PID: 632)
- explorer.exe (PID: 292)
Creates files in the user directory
- colorcpl.exe (PID: 3392)
Loads DLL from Mozilla Firefox
- colorcpl.exe (PID: 3392)
Executed via COM
- DllHost.exe (PID: 2828)
Creates files in the program directory
- DllHost.exe (PID: 2828)
Uses NETSH.EXE for network configuration
- explorer.exe (PID: 292)
INFO
Reads the hosts file
- colorcpl.exe (PID: 3392)
Manual execution by user
- colorcpl.exe (PID: 3392)
- PEDIDO ORDER COMPRA.scr (PID: 3120)
- PEDIDO ORDER COMPRA.scr (PID: 3068)
Creates files in the user directory
- Firefox.exe (PID: 3000)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
55
Monitored processes
18
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 632 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\PEDIDO ORDER COMPRA.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2004 | "C:\Users\admin\AppData\Local\Temp\AddInProcess32.exe" | C:\Users\admin\AppData\Local\Temp\AddInProcess32.exe | — | PEDIDO ORDER COMPRA.scr | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: AddInProcess.exe Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
| 2168 | "C:\Users\admin\AppData\Local\Temp\AddInProcess32.exe" | C:\Users\admin\AppData\Local\Temp\AddInProcess32.exe | — | PEDIDO ORDER COMPRA.scr | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: AddInProcess.exe Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
| 2240 | /c del "C:\Users\admin\AppData\Local\Temp\AddInProcess32.exe" | C:\Windows\System32\cmd.exe | — | colorcpl.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2784 | "C:\Users\admin\AppData\Local\Temp\AddInProcess32.exe" | C:\Users\admin\AppData\Local\Temp\AddInProcess32.exe | — | PEDIDO ORDER COMPRA.scr | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: AddInProcess.exe Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
| 2828 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2940 | "C:\Users\admin\Desktop\PEDIDO ORDER COMPRA.scr" /S | C:\Users\admin\Desktop\PEDIDO ORDER COMPRA.scr | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 3000 | "C:\Program Files\Mozilla Firefox\Firefox.exe" | C:\Program Files\Mozilla Firefox\Firefox.exe | colorcpl.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 3024 | "C:\Users\admin\Desktop\PEDIDO ORDER COMPRA.scr" /S | C:\Users\admin\Desktop\PEDIDO ORDER COMPRA.scr | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
Total events
1 557
Read events
1 492
Write events
65
Delete events
0
Modification events
| (PID) Process: | (632) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (632) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (632) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (632) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (632) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\PEDIDO ORDER COMPRA.rar | |||
| (PID) Process: | (632) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (632) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (632) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (632) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (632) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @shell32,-10162 |
Value: Screen saver | |||
Executable files
6
Suspicious files
73
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 632 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb632.45047\PEDIDO ORDER COMPRA.scr | — | |
MD5:— | SHA256:— | |||
| 292 | explorer.exe | C:\Users\admin\Desktop\PEDIDO ORDER COMPRA.scr | executable | |
MD5:— | SHA256:— | |||
| 3392 | colorcpl.exe | C:\Users\admin\AppData\Roaming\76M90RE2\76Mlogrc.ini | binary | |
MD5:— | SHA256:— | |||
| 632 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb632.36202\PEDIDO ORDER COMPRA.scr | executable | |
MD5:— | SHA256:— | |||
| 3308 | PEDIDO ORDER COMPRA.scr | C:\Users\admin\AppData\Local\Temp\AddInProcess32.exe | executable | |
MD5:6A673BFC3B67AE9782CB31AF2F234C68 | SHA256:978A4093058AA2EBF05DC353897D90D950324389879B57741B64160825B5EC0E | |||
| 292 | explorer.exe | C:\Users\admin\AppData\Local\Temp\U3fl\igfxext4sb.exe | executable | |
MD5:6A673BFC3B67AE9782CB31AF2F234C68 | SHA256:978A4093058AA2EBF05DC353897D90D950324389879B57741B64160825B5EC0E | |||
| 3392 | colorcpl.exe | C:\Users\admin\AppData\Roaming\76M90RE2\76Mlogri.ini | binary | |
MD5:D63A82E5D81E02E399090AF26DB0B9CB | SHA256:EAECE2EBA6310253249603033C744DD5914089B0BB26BDE6685EC9813611BAAE | |||
| 3120 | PEDIDO ORDER COMPRA.scr | C:\Users\admin\AppData\Local\Temp\AddInProcess32.exe | executable | |
MD5:6A673BFC3B67AE9782CB31AF2F234C68 | SHA256:978A4093058AA2EBF05DC353897D90D950324389879B57741B64160825B5EC0E | |||
| 3000 | Firefox.exe | C:\Users\admin\AppData\Roaming\76M90RE2\76Mlogrf.ini | binary | |
MD5:— | SHA256:— | |||
| 3392 | colorcpl.exe | C:\Users\admin\AppData\Roaming\76M90RE2\76Mlogim.jpeg | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
5
DNS requests
7
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
292 | explorer.exe | POST | — | 34.102.136.180:80 | http://www.jakru.com/ex8/ | US | — | — | whitelisted |
292 | explorer.exe | POST | — | 34.102.136.180:80 | http://www.jakru.com/ex8/ | US | — | — | whitelisted |
292 | explorer.exe | GET | 403 | 34.102.136.180:80 | http://www.jakru.com/ex8/?EjD4It=qAiYM9MnTobfdchno9WltRaubfWGtUmXQGbQ+fgR4uWNCkKm2U+QgeSr6gbMTkIC2AYRJg==&0pq=FtI0wNn&sql=1 | US | html | 275 b | whitelisted |
292 | explorer.exe | GET | 404 | 149.129.82.236:80 | http://www.moki.ltd/ex8/?EjD4It=9h8b/nNHLord3JVs6FXsucd1os3l/CC8LkkNtdSwQzPllXvfGN4ynMoD8JLIes35UPpqVA==&0pq=FtI0wNn | CN | html | 162 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
292 | explorer.exe | 34.102.136.180:80 | www.jakru.com | — | US | whitelisted |
292 | explorer.exe | 149.129.82.236:80 | www.moki.ltd | — | CN | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.isleofstock.com |
| unknown |
www.pingguobaohuke.com |
| unknown |
www.moki.ltd |
| malicious |
www.ghdgu.info |
| unknown |
www.jakru.com |
| whitelisted |
www.trickoff.net |
| unknown |
www.pmi-ems.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
292 | explorer.exe | Generic Protocol Command Decode | SURICATA HTTP Unexpected Request body |
292 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
292 | explorer.exe | Generic Protocol Command Decode | SURICATA HTTP Unexpected Request body |
292 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
292 | explorer.exe | Generic Protocol Command Decode | SURICATA HTTP Unexpected Request body |
292 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
292 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
292 | explorer.exe | Generic Protocol Command Decode | SURICATA HTTP Unexpected Request body |
292 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
292 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
3 ETPRO signatures available at the full report