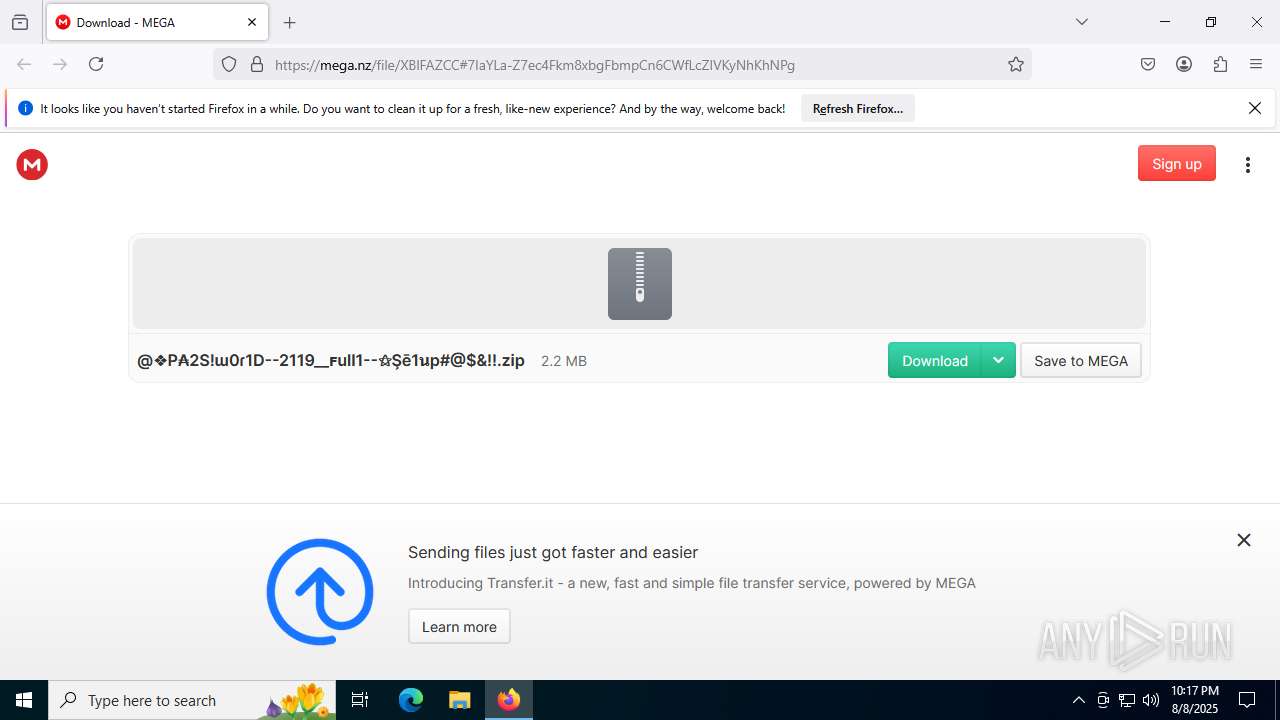
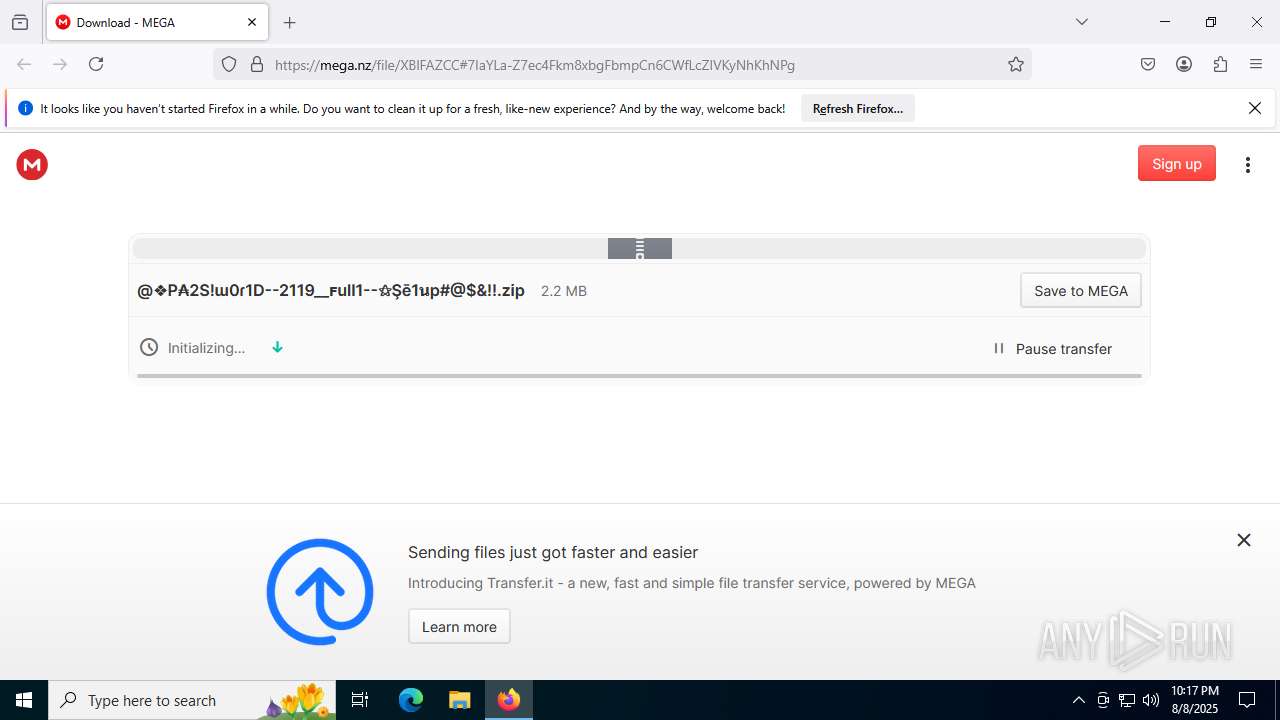
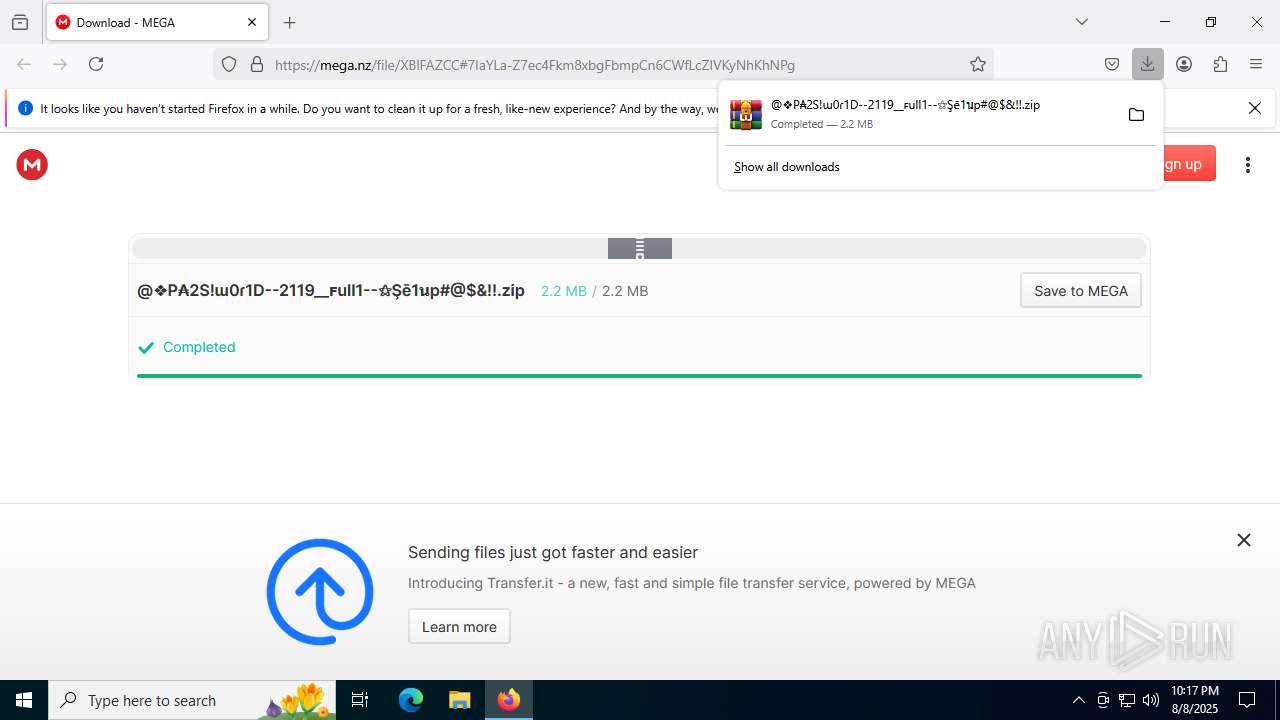
| URL: | https://mega.nz/file/XBlFAZCC#7IaYLa-Z7ec4Fkm8xbgFbmpCn6CWfLcZIVKyNhKhNPg |
| Full analysis: | https://app.any.run/tasks/a2d84433-e869-4000-881c-2613bdf7dfcc |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | August 08, 2025, 22:17:14 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | BF14748485F9DB8FD9E7F80EE432C828 |
| SHA1: | 02FEBFB5436AE92A59ECCE0D6CDB169410486D48 |
| SHA256: | F4DC180FBDDCFFC1C1D8A98CADC477C9093AB9AB2F26D7578E63FB949BF40BE6 |
| SSDEEP: | 3:N8X/i2r1VpEzfHgImL7kaNurC:251DEzfHh2ka+C |
MALICIOUS
Connects to the CnC server
- svchost.exe (PID: 2200)
LUMMA mutex has been found
- Mel.pif (PID: 7660)
- Mel.pif (PID: 4944)
Steals credentials from Web Browsers
- Mel.pif (PID: 7660)
Actions looks like stealing of personal data
- Mel.pif (PID: 7660)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 4200)
- WinRAR.exe (PID: 1336)
- WinRAR.exe (PID: 7044)
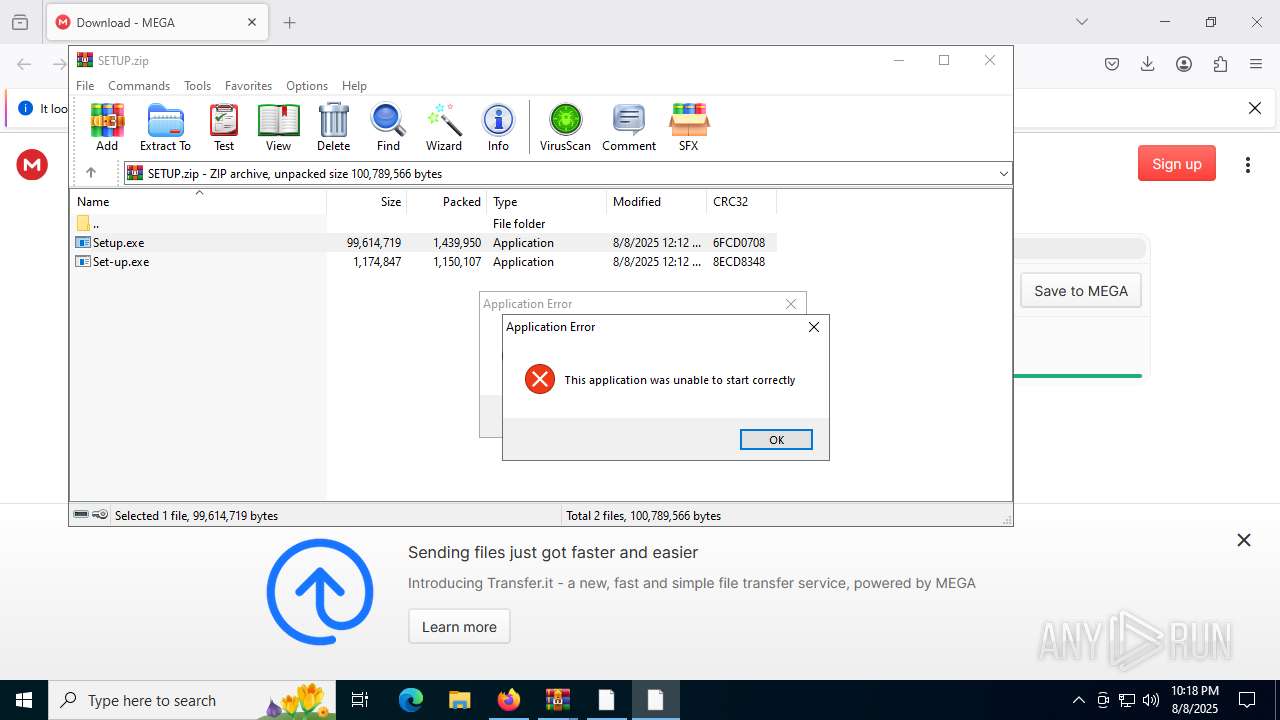
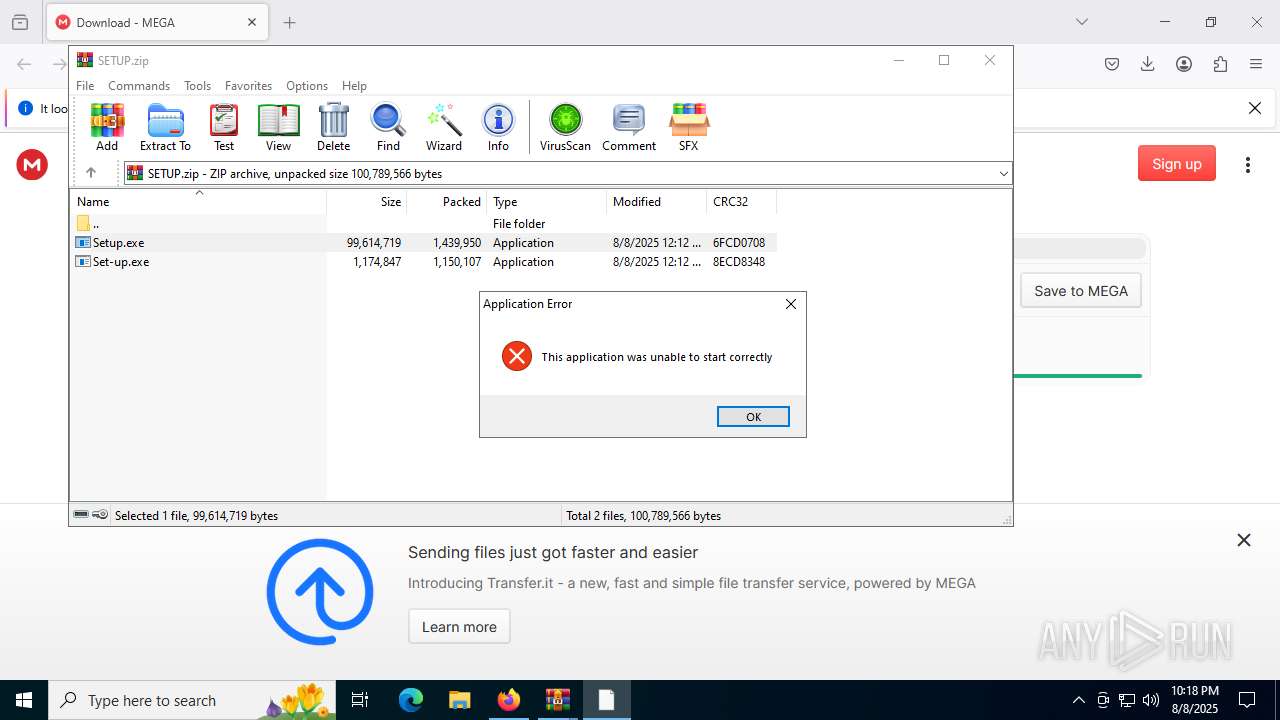
Application launched itself
- WinRAR.exe (PID: 1336)
- WinRAR.exe (PID: 4200)
- cmd.exe (PID: 6868)
- cmd.exe (PID: 7448)
Starts CMD.EXE for commands execution
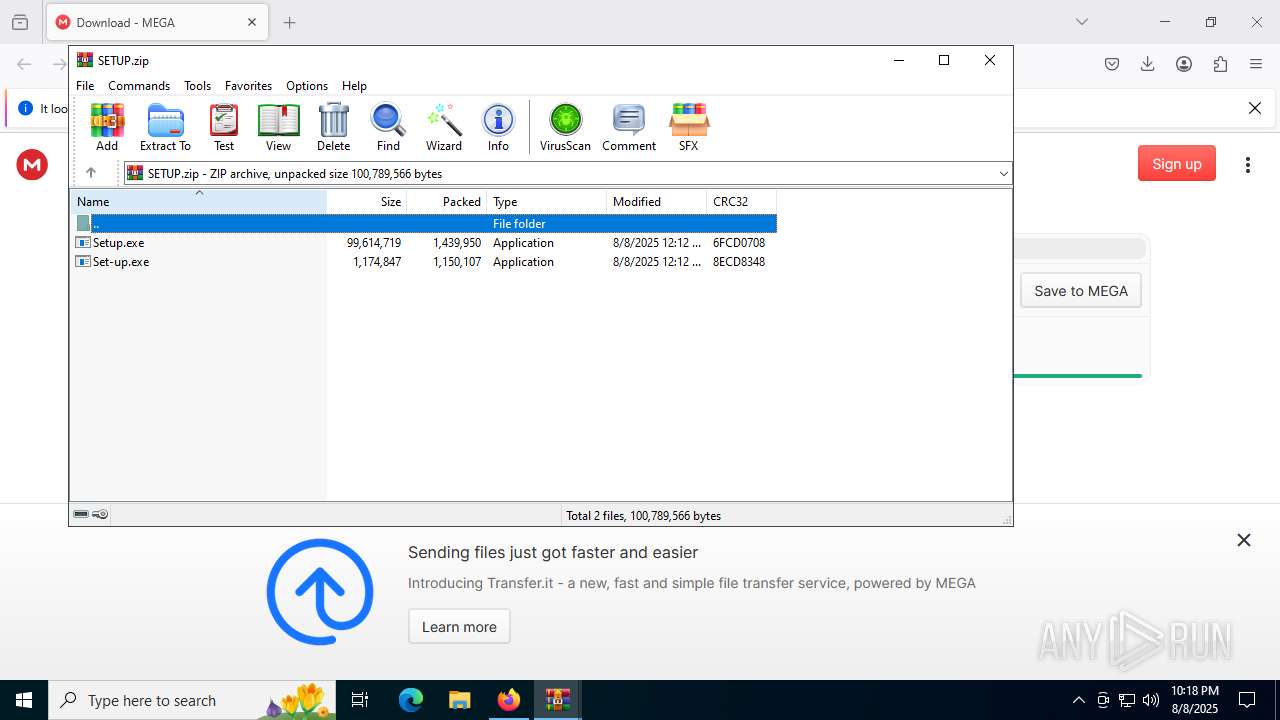
- Set-up.exe (PID: 7796)
- cmd.exe (PID: 6868)
- Setup.exe (PID: 7572)
- cmd.exe (PID: 7448)
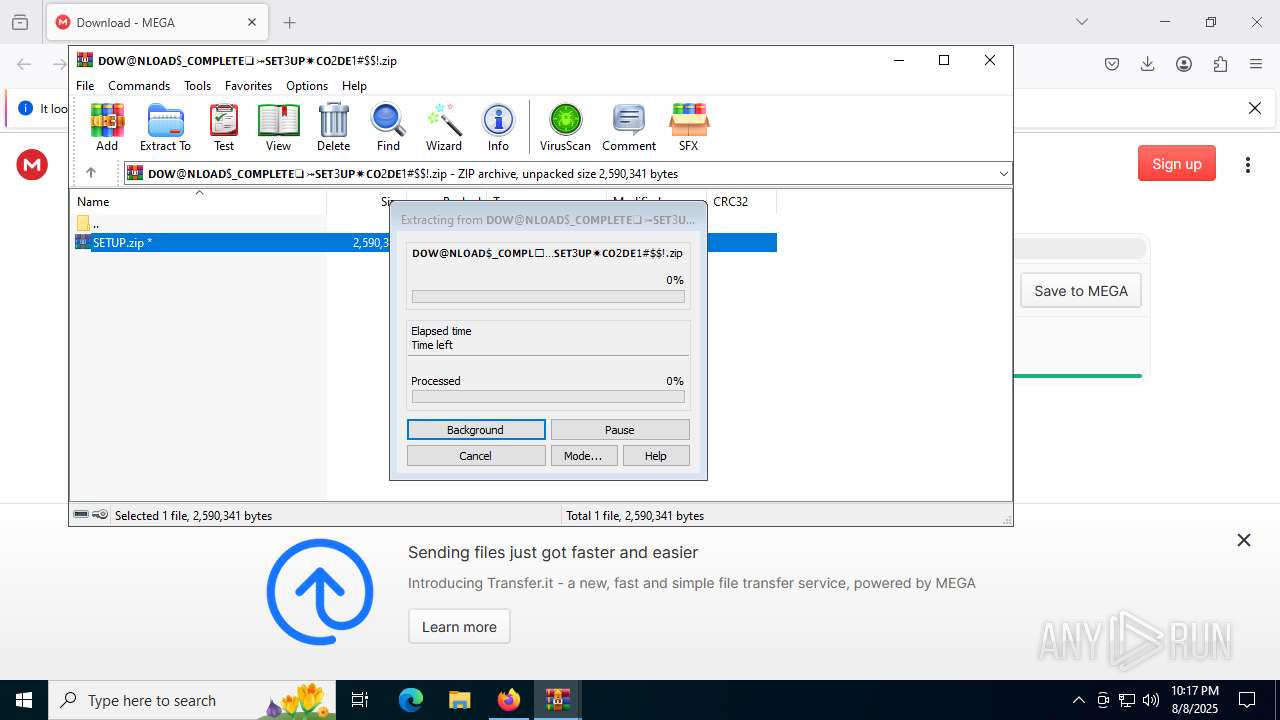
Executable content was dropped or overwritten
- Set-up.exe (PID: 7796)
- Setup.exe (PID: 7572)
Get information on the list of running processes
- cmd.exe (PID: 7616)
- cmd.exe (PID: 7732)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7616)
- cmd.exe (PID: 7732)
Drops a file with a rarely used extension (PIF)
- cmd.exe (PID: 7616)
Starts the AutoIt3 executable file
- cmd.exe (PID: 7616)
- cmd.exe (PID: 7732)
The executable file from the user directory is run by the CMD process
- Mel.pif (PID: 7660)
- Mel.pif (PID: 4944)
Starts application with an unusual extension
- cmd.exe (PID: 7616)
- cmd.exe (PID: 7732)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2200)
- Mel.pif (PID: 7660)
- Mel.pif (PID: 4944)
INFO
Application launched itself
- firefox.exe (PID: 6004)
- firefox.exe (PID: 1508)
- chrome.exe (PID: 7256)
- chrome.exe (PID: 8572)
- chrome.exe (PID: 3476)
- chrome.exe (PID: 2356)
- msedge.exe (PID: 8572)
- msedge.exe (PID: 8952)
Reads Microsoft Office registry keys
- firefox.exe (PID: 6004)
Executable content was dropped or overwritten
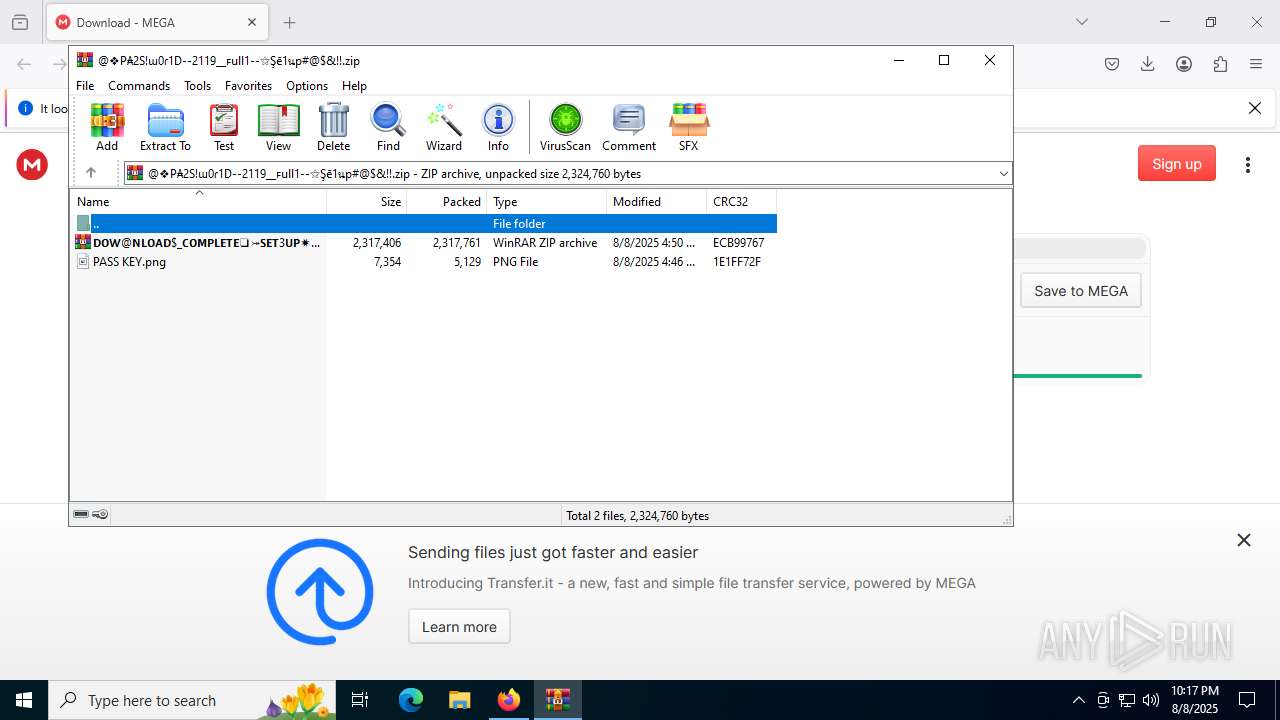
- WinRAR.exe (PID: 7044)
- firefox.exe (PID: 6004)
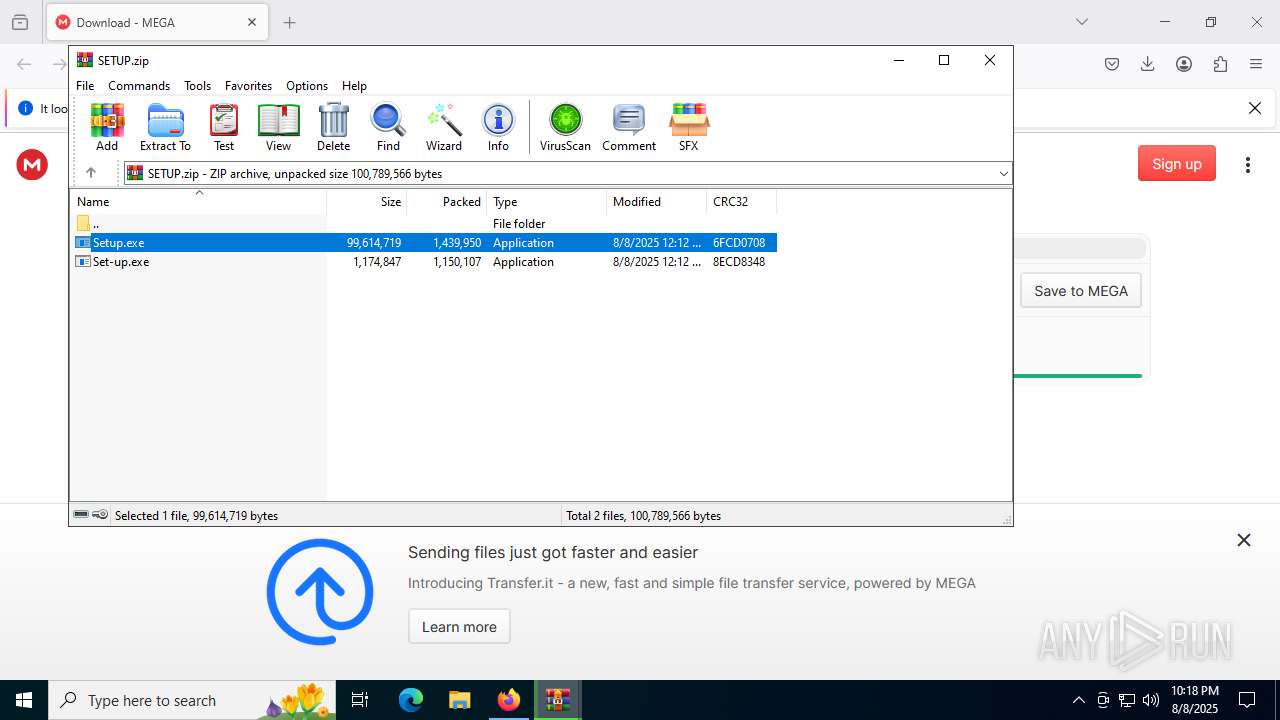
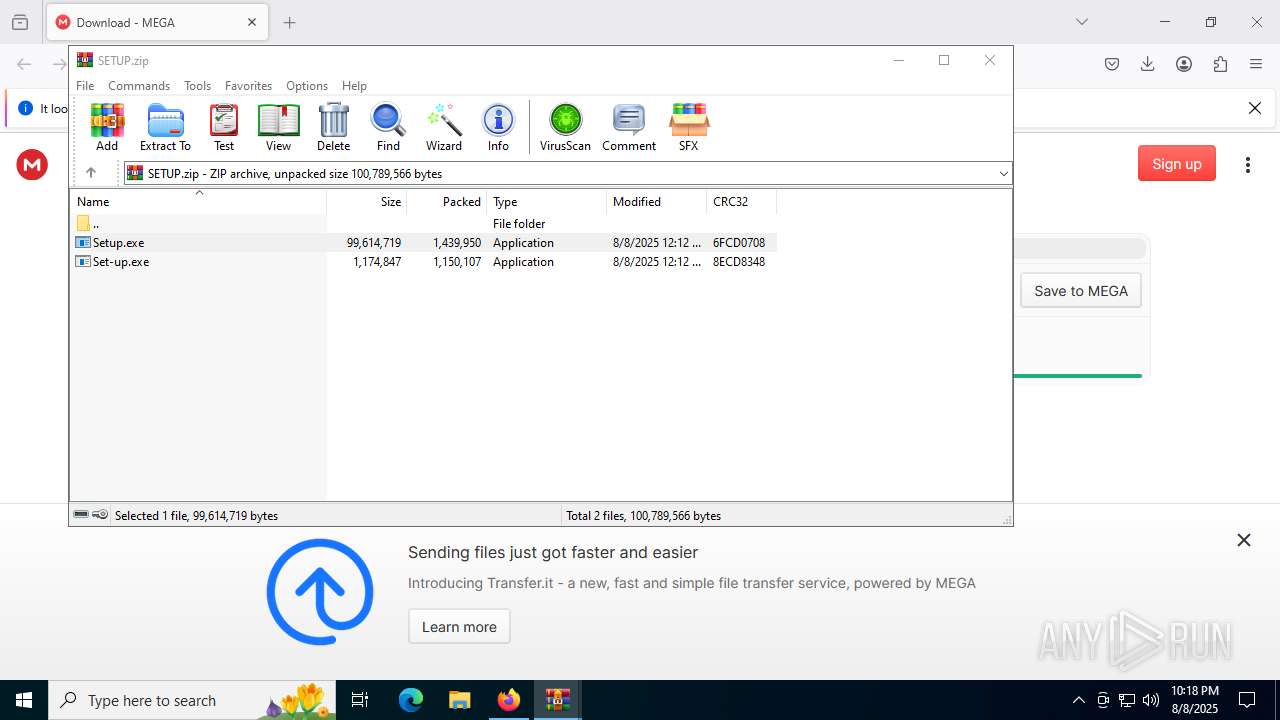
Manual execution by a user
- WinRAR.exe (PID: 4200)
Create files in a temporary directory
- Set-up.exe (PID: 7796)
- Setup.exe (PID: 7572)
- extrac32.exe (PID: 3760)
- extrac32.exe (PID: 7684)
Checks supported languages
- Set-up.exe (PID: 7796)
- extrac32.exe (PID: 3760)
- Mel.pif (PID: 7660)
- Setup.exe (PID: 7572)
- extrac32.exe (PID: 7684)
- Mel.pif (PID: 4944)
- identity_helper.exe (PID: 8752)
Reads the computer name
- Set-up.exe (PID: 7796)
- extrac32.exe (PID: 3760)
- Mel.pif (PID: 7660)
- Setup.exe (PID: 7572)
- extrac32.exe (PID: 7684)
- Mel.pif (PID: 4944)
- identity_helper.exe (PID: 8752)
Reads mouse settings
- Mel.pif (PID: 7660)
- Mel.pif (PID: 4944)
Reads the software policy settings
- Mel.pif (PID: 7660)
- Mel.pif (PID: 4944)
- slui.exe (PID: 2524)
Reads the machine GUID from the registry
- Mel.pif (PID: 7660)
- Mel.pif (PID: 4944)
The sample compiled with english language support
- firefox.exe (PID: 6004)
Checks proxy server information
- slui.exe (PID: 2524)
Reads Environment values
- identity_helper.exe (PID: 8752)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
242
Monitored processes
101
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1036 | findstr "SophosHealth nsWscSvc ekrn bdservicehost AvastUI AVGUI & if not errorlevel 1 Set FzntwKDuAuHQxCCpaNANpcuaAZOn=AutoIt3.exe & Set tTYYdtWvQHawqSuCzXWGIysXiUa=.a3x & Set hoSXeAeZDXCoElcpVmj=300 | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1332 | tasklist | C:\Windows\SysWOW64\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=4892,i,7086387088625697284,14916891455991030571,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=4996 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
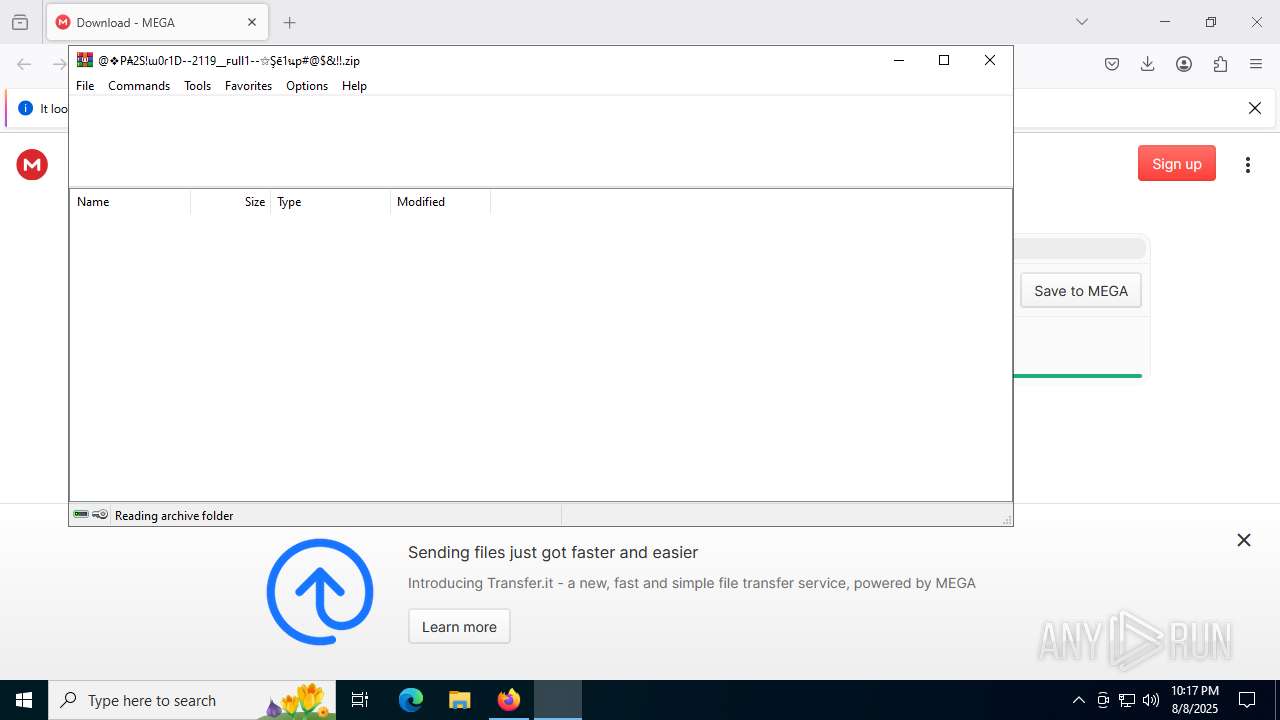
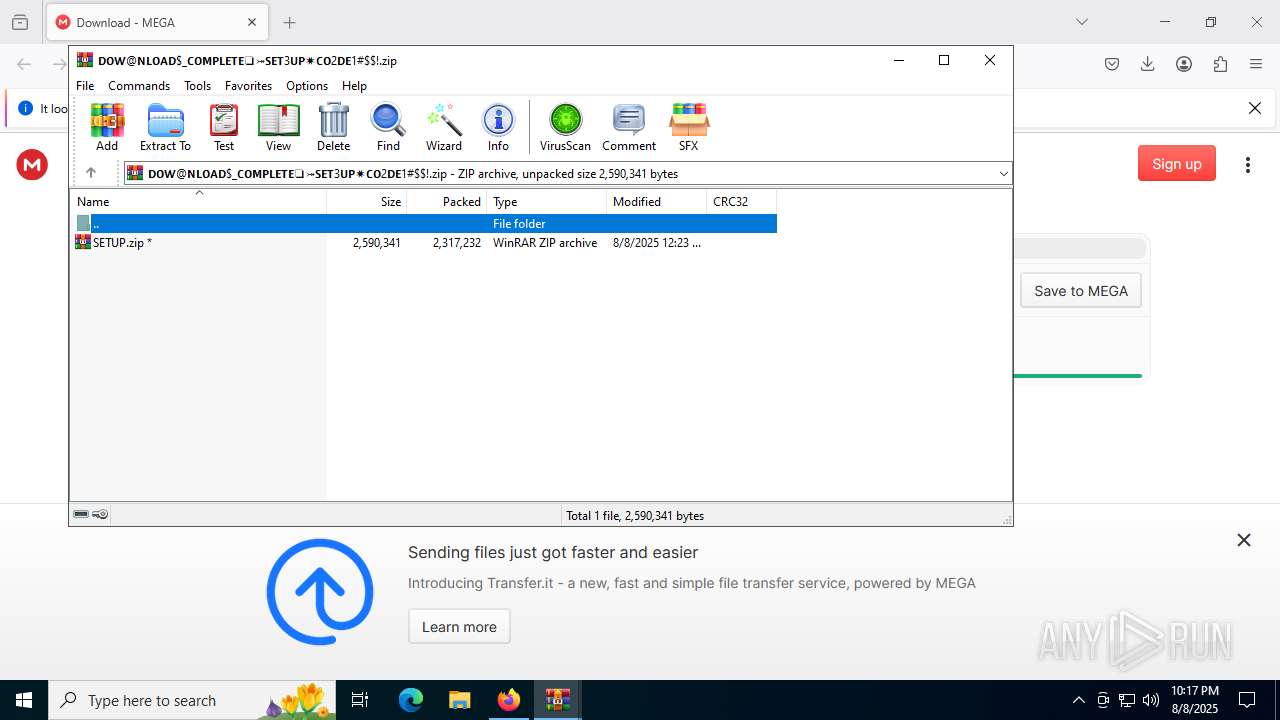
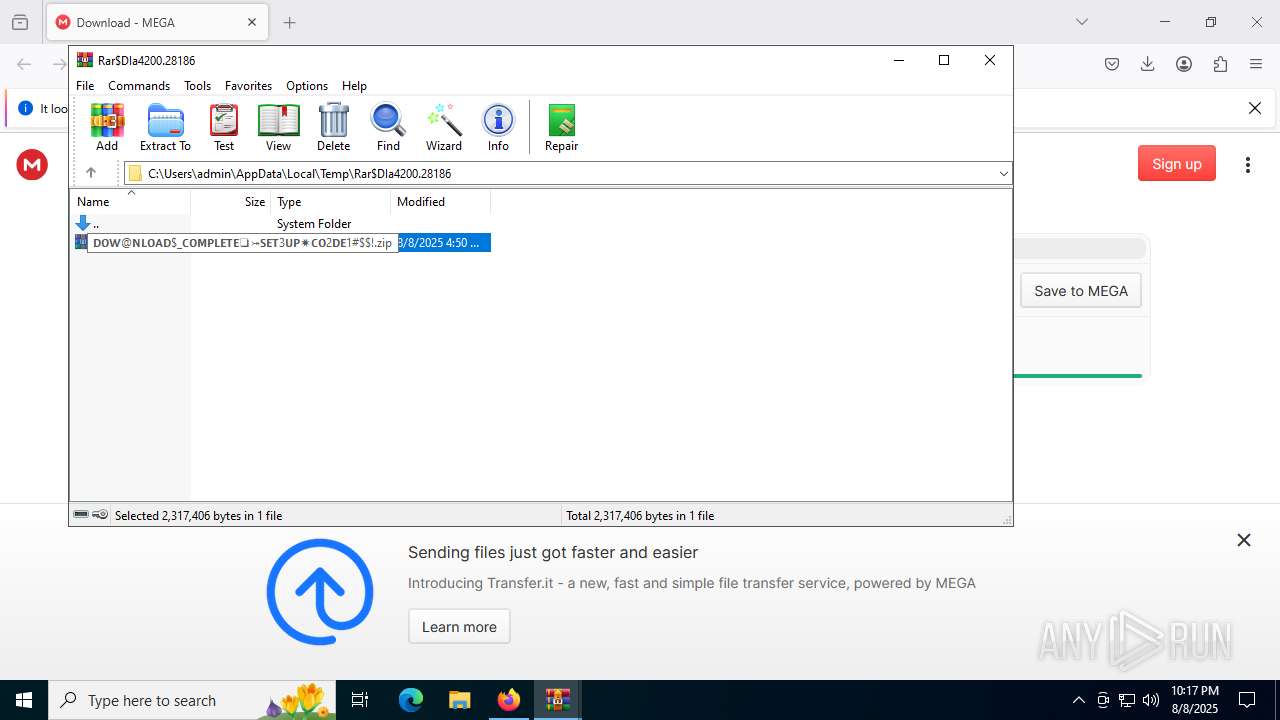
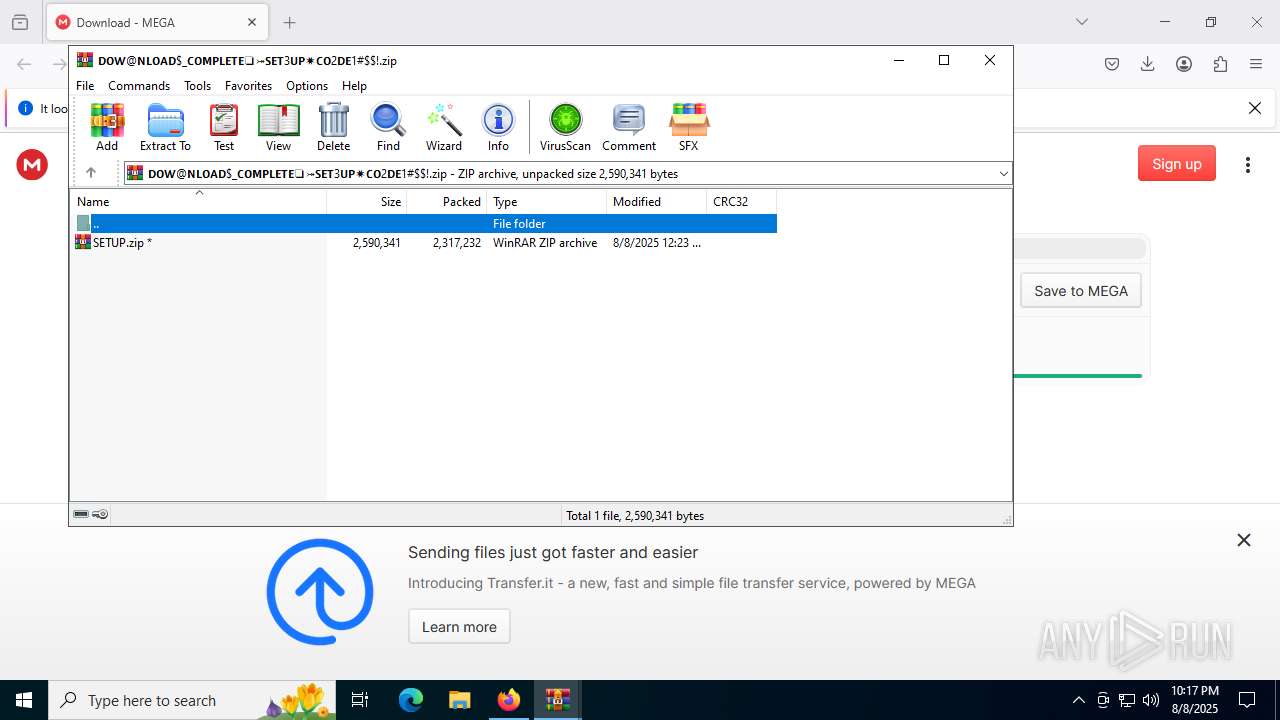
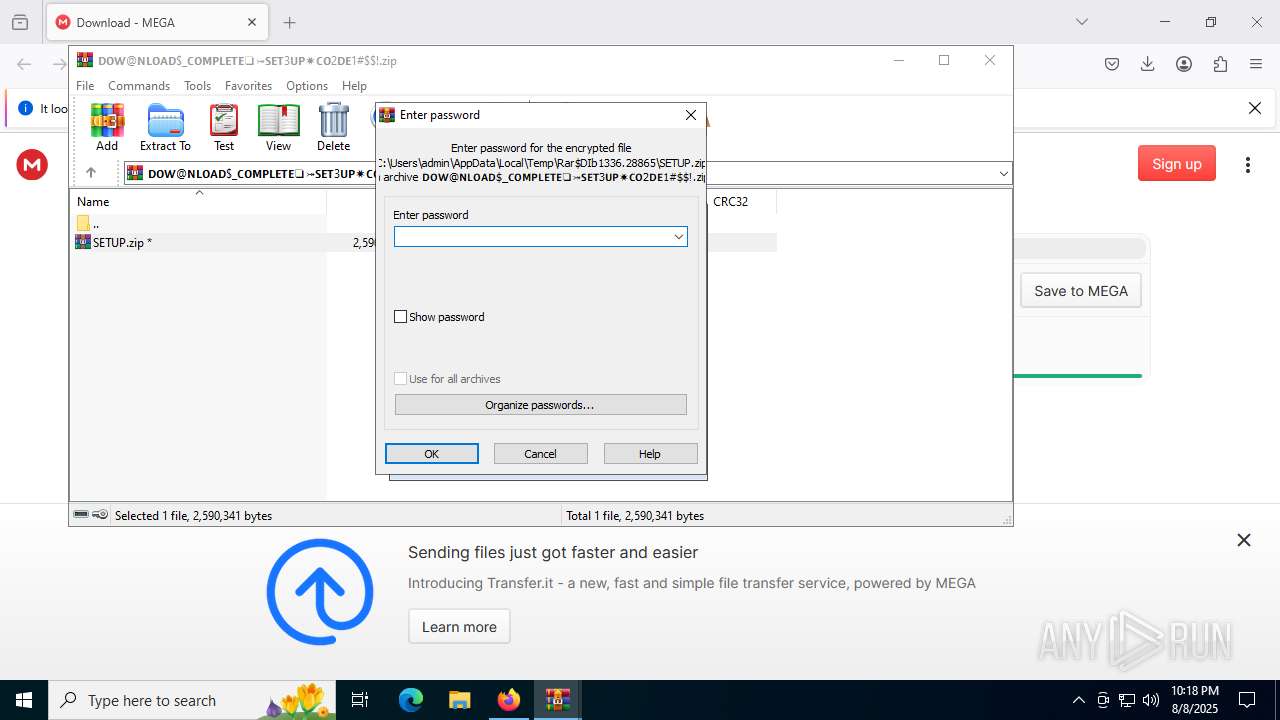
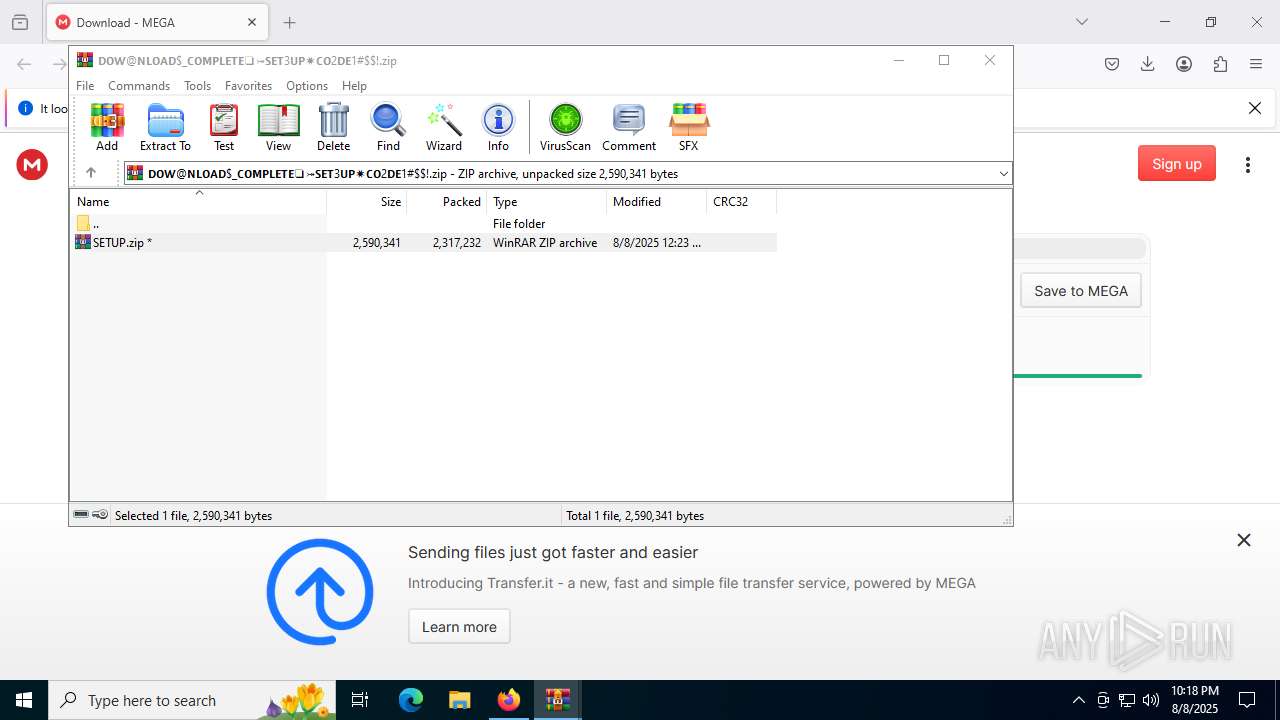
| 1336 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Rar$DIa4200.28186\𝗗𝗢𝗪@𝗡𝗟𝗢𝗔𝗗$_𝗖𝗢𝗠𝗣𝗟𝗘𝗧𝗘❏⤖𝗦𝗘𝗧3𝗨𝗣✷𝗖𝗢2𝗗𝗘1#$!.zip | C:\Program Files\WinRAR\WinRAR.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 1508 | "C:\Program Files\Mozilla Firefox\firefox.exe" "https://mega.nz/file/XBlFAZCC#7IaYLa-Z7ec4Fkm8xbgFbmpCn6CWfLcZIVKyNhKhNPg" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 136.0 Modules
| |||||||||||||||
| 1612 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=4220,i,17495756152885245442,17103468723232151181,262144 --variations-seed-version --mojo-platform-channel-handle=4292 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1704 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=4876,i,12385695232108399733,16977623956298009224,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=5000 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2200 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | Mel.pif | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2384 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --field-trial-handle=4696,i,7086387088625697284,14916891455991030571,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=4464 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
Total events
46 440
Read events
46 356
Write events
84
Delete events
0
Modification events
| (PID) Process: | (6004) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (4200) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (4200) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4200) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4200) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\@❖P₳2S!ɯ0ɾ1D--2119__ꜰull1--⚝Şē1นp#@f7f81a39-5f63-5b42-9efd-1f13b5431005amp;!!.zip | |||
| (PID) Process: | (4200) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4200) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4200) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4200) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1336) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
Executable files
8
Suspicious files
744
Text files
359
Unknown types
168
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6004 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 6004 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6004 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-wal | binary | |
MD5:9F09376150427832AE361F82EA779127 | SHA256:D6731AAD054529E5CF1B89AF0E302A6743EB57FA6635BCBD305FBB444E65A420 | |||
| 6004 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2823318777ntouromlalnodry--naod.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6004 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6004 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\datareporting\glean\db\data.safe.bin | dbf | |
MD5:EFCC9E68E66381B0D3A720A07507C821 | SHA256:0B0AB1E02E6E3991414BA1817EF69A56090206F49E16266C9F6B4E6E3E3C4B8F | |||
| 6004 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs.js | text | |
MD5:2FD670934FEF0C60E2119BD874AAF470 | SHA256:771A7C83CA015BDBC6AB86A7BD9B1D54E40062E28942D311A9178A0FE6433CF2 | |||
| 6004 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\activity-stream.contile.json.tmp | binary | |
MD5:6BB61C2420659ED01B90336136946503 | SHA256:1C4B442C7067A077412A183CF94E7CA29A719F95C546A25636FFDE44123C8F4E | |||
| 6004 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3561288849sdhlie.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6004 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
42
TCP/UDP connections
239
DNS requests
262
Threats
37
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6004 | firefox.exe | POST | 200 | 172.217.16.195:80 | http://o.pki.goog/s/wr3/k58 | unknown | — | — | whitelisted |
6004 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
6004 | firefox.exe | POST | 200 | 172.217.16.195:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
6004 | firefox.exe | POST | 200 | 172.217.16.195:80 | http://o.pki.goog/s/wr3/azY | unknown | — | — | whitelisted |
6004 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
6004 | firefox.exe | POST | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/ | unknown | — | — | whitelisted |
6004 | firefox.exe | POST | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/ | unknown | — | — | whitelisted |
6004 | firefox.exe | POST | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/ | unknown | — | — | whitelisted |
6004 | firefox.exe | POST | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/ | unknown | — | — | whitelisted |
6004 | firefox.exe | POST | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4700 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6004 | firefox.exe | 34.160.144.191:443 | content-signature-2.cdn.mozilla.net | GOOGLE | US | whitelisted |
6004 | firefox.exe | 31.216.145.5:443 | mega.nz | Datacenter Luxembourg S.A. | LU | whitelisted |
6004 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
6004 | firefox.exe | 34.36.137.203:443 | contile.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
6004 | firefox.exe | 34.149.100.209:443 | firefox.settings.services.mozilla.com | GOOGLE | US | whitelisted |
6004 | firefox.exe | 172.217.16.195:80 | o.pki.goog | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
content-signature-2.cdn.mozilla.net |
| whitelisted |
content-signature-chains.prod.autograph.services.mozaws.net |
| whitelisted |
mega.nz |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
spocs.getpocket.com |
| whitelisted |
mc.prod.ads.prod.webservices.mozgcp.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2200 | svchost.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
2200 | svchost.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
2200 | svchost.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
6004 | firefox.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
6004 | firefox.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
2200 | svchost.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |
2200 | svchost.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |
2200 | svchost.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |
2200 | svchost.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |
2200 | svchost.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |