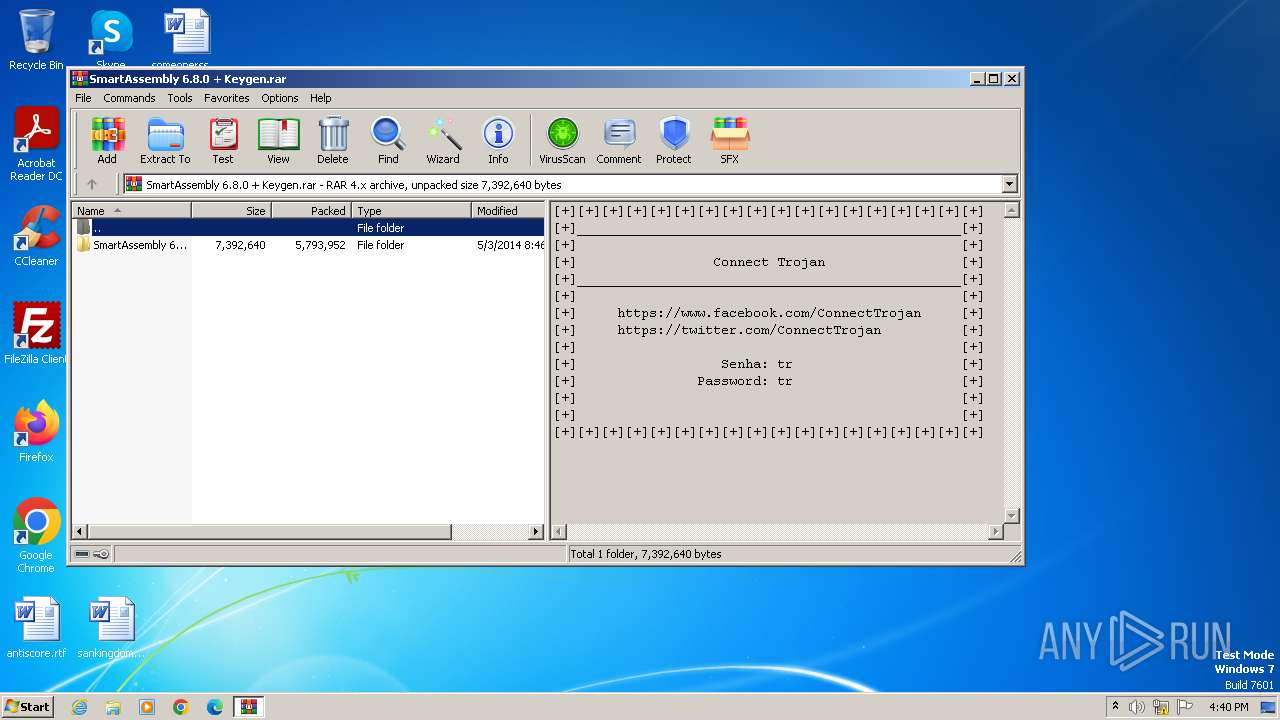
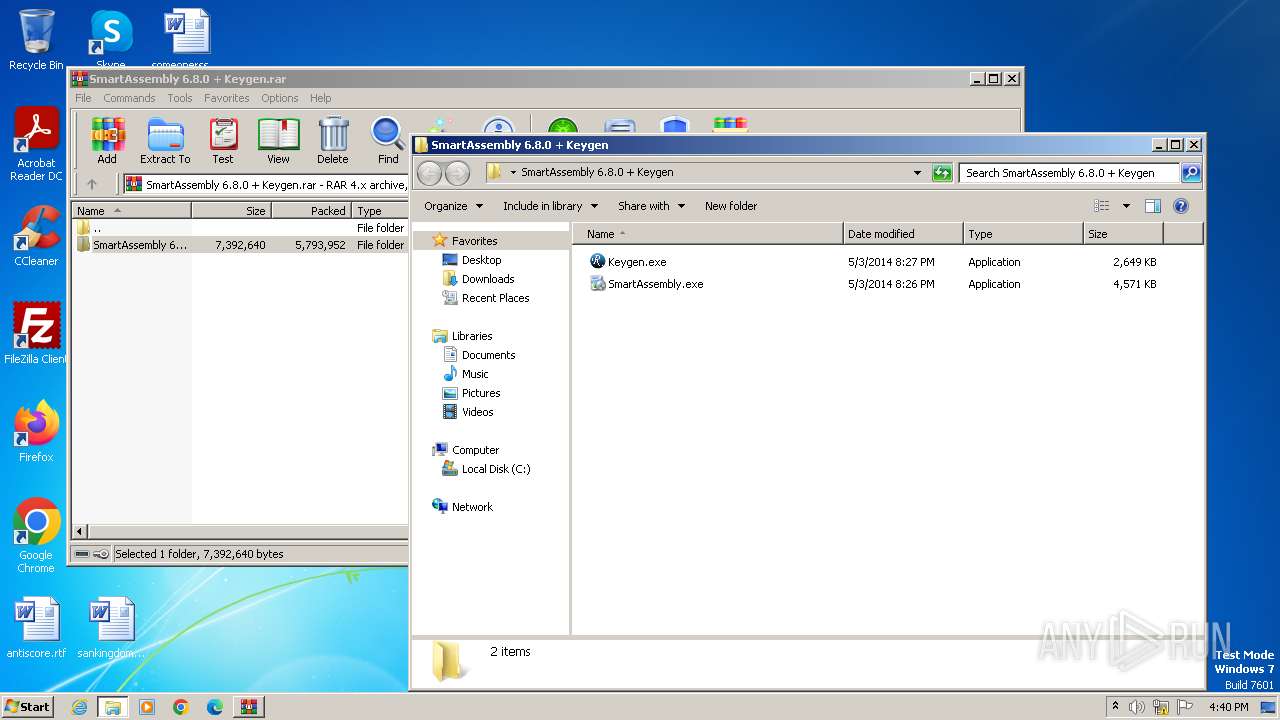
| File name: | SmartAssembly 6.8.0 + Keygen.rar |
| Full analysis: | https://app.any.run/tasks/6f4ad5d3-340f-4d63-8515-0ed94d956c77 |
| Verdict: | Malicious activity |
| Threats: | Ramnit is a highly modular banking trojan and worm that evolved from a file-infecting virus into a powerful cybercrime tool. It specializes in financial fraud, credential theft, remote access, and malware delivery, being a serious threat to businesses and individuals. First spotted in 2010, Ramnit became popular after the 2014 takedown of the GameOver Zeus botnet, as cybercriminals sought alternatives for banking fraud. |
| Analysis date: | November 28, 2023, 16:40:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v4, os: Win32 |
| MD5: | 7AA2426EC2F7FFF2CE537040AD8176E0 |
| SHA1: | 18EA395A79332317F1E0CCFC53D1E5D8F329D86D |
| SHA256: | F4D42160B12898B5B066D6545FB44877B5D346638E0F4317E2138326DA991D21 |
| SSDEEP: | 98304:KdmmBgNit7wdfbuCw2xXhS3i4MeQB6SzDRkqmdsfMtAYJkWkca8cKfh8lBGccuBF:fZhQrkzCkM8nh |
MALICIOUS
Signature: RAMNIT has been detected
- Keygen.exe (PID: 1444)
- KeygenSrv.exe (PID: 1900)
- KeygenSrvSrv.exe (PID: 824)
- DesktopLayer.exe (PID: 1788)
- DesktopLayerSrv.exe (PID: 2252)
- iexplore.exe (PID: 2820)
- iexplore.exe (PID: 2776)
- DesktopLayer.exe (PID: 3120)
RAMNIT has been detected (SURICATA)
- iexplore.exe (PID: 2820)
Connects to the CnC server
- iexplore.exe (PID: 2820)
Changes the login/logoff helper path in the registry
- iexplore.exe (PID: 2820)
SUSPICIOUS
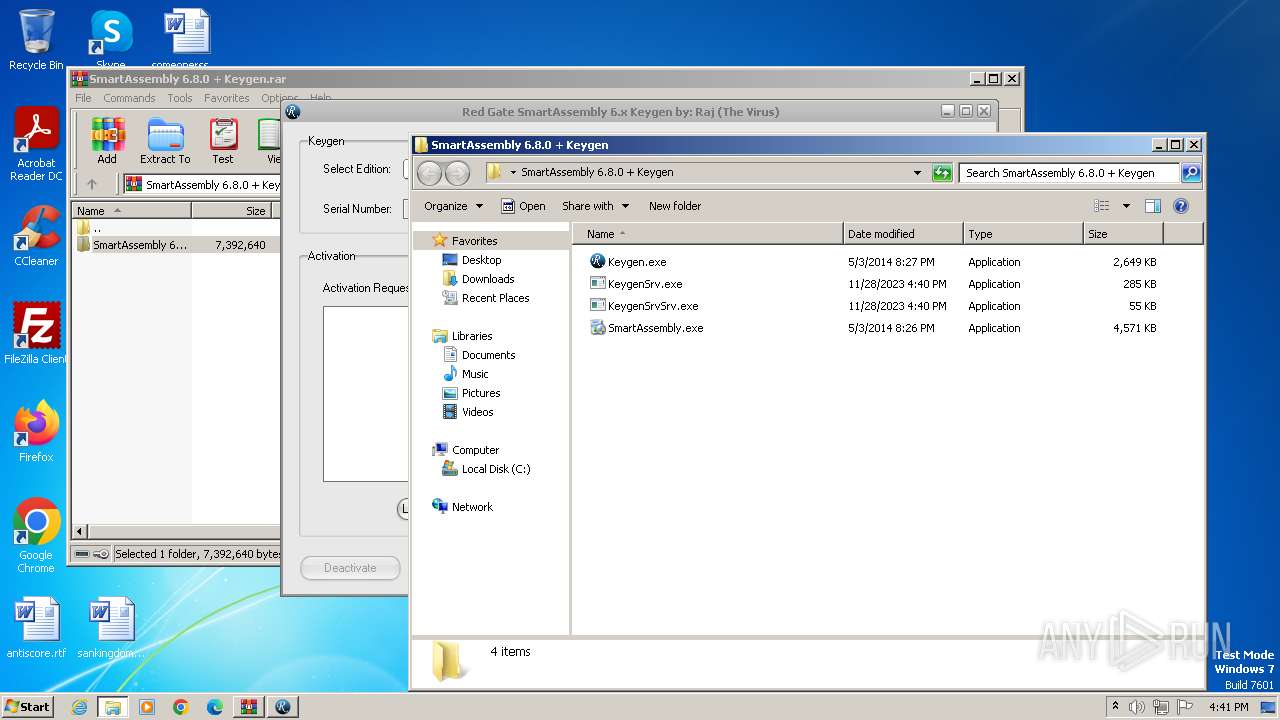
Starts itself from another location
- KeygenSrv.exe (PID: 1900)
- DesktopLayerSrv.exe (PID: 2252)
INFO
Checks supported languages
- KeygenSrv.exe (PID: 1900)
- Keygen.exe (PID: 1444)
- KeygenSrvSrv.exe (PID: 824)
- DesktopLayer.exe (PID: 1788)
- DesktopLayerSrv.exe (PID: 2252)
- DesktopLayer.exe (PID: 3120)
- wmpnscfg.exe (PID: 1784)
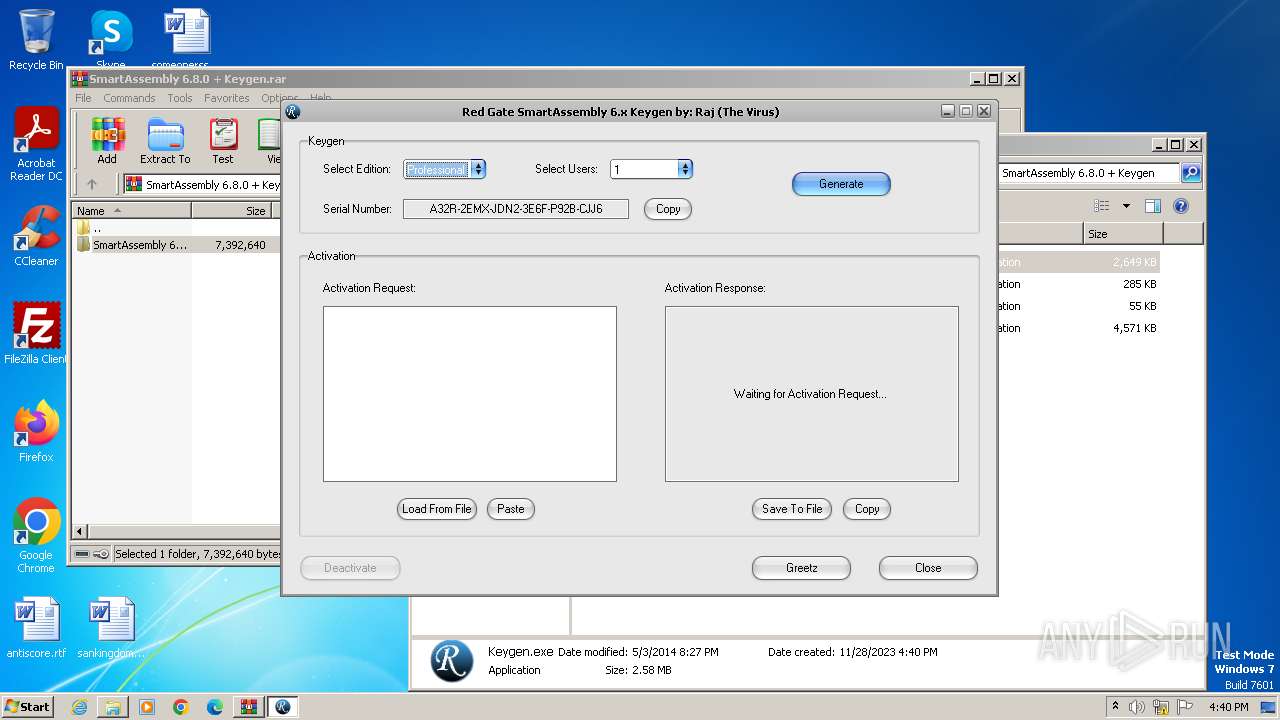
Manual execution by a user
- Keygen.exe (PID: 1444)
- wmpnscfg.exe (PID: 1784)
Create files in a temporary directory
- KeygenSrv.exe (PID: 1900)
- Keygen.exe (PID: 1444)
Reads the machine GUID from the registry
- Keygen.exe (PID: 1444)
- wmpnscfg.exe (PID: 1784)
Reads the computer name
- Keygen.exe (PID: 1444)
- wmpnscfg.exe (PID: 1784)
Creates files or folders in the user directory
- Keygen.exe (PID: 1444)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
EXIF
ZIP
| CompressedSize: | 2462921 |
|---|---|
| UncompressedSize: | 2712576 |
| OperatingSystem: | Win32 |
| ModifyDate: | 2014:05:03 20:27:42 |
| PackingMethod: | Normal |
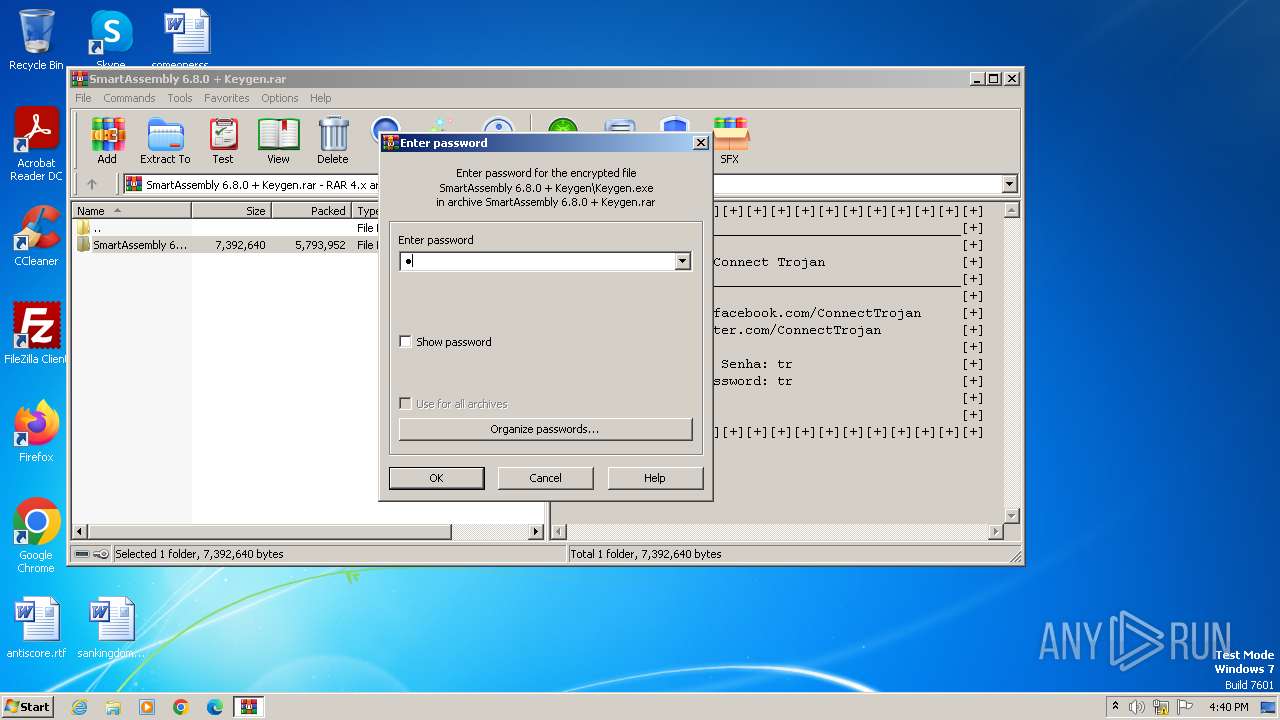
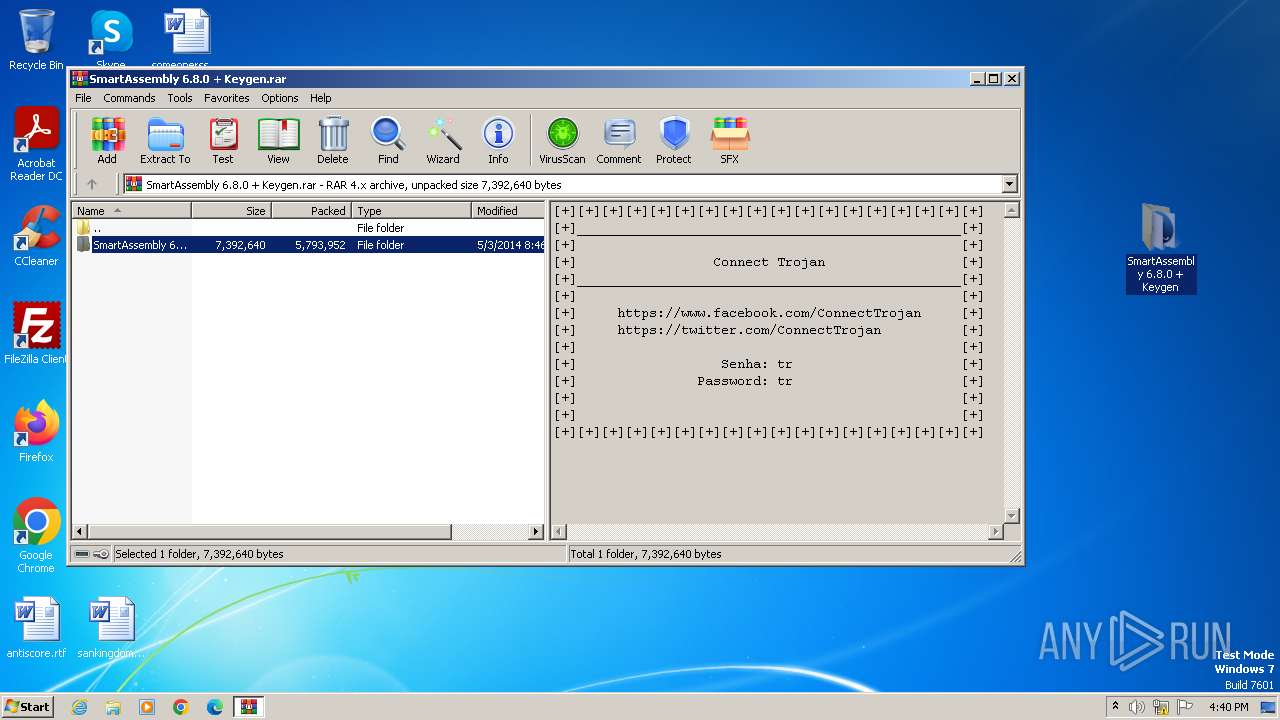
| ArchivedFileName: | SmartAssembly 6.8.0 + Keygen\Keygen.exe |
Total processes
49
Monitored processes
10
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 824 | "C:\Users\admin\Desktop\SmartAssembly 6.8.0 + Keygen\KeygenSrvSrv.exe" | C:\Users\admin\Desktop\SmartAssembly 6.8.0 + Keygen\KeygenSrvSrv.exe | — | KeygenSrv.exe | |||||||||||
User: admin Company: SOFTWIN S.R.L. Integrity Level: MEDIUM Description: BitDefender Management Console Exit code: 0 Version: 106.42.73.61 Modules
| |||||||||||||||
| 1444 | "C:\Users\admin\Desktop\SmartAssembly 6.8.0 + Keygen\Keygen.exe" | C:\Users\admin\Desktop\SmartAssembly 6.8.0 + Keygen\Keygen.exe | — | explorer.exe | |||||||||||
User: admin Company: Raj (The Virus) Integrity Level: MEDIUM Description: Keygen Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1784 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1788 | C:\Users\admin\Microsoft\DesktopLayer.exe | C:\Users\admin\Microsoft\DesktopLayer.exe | — | KeygenSrv.exe | |||||||||||
User: admin Company: SOFTWIN S.R.L. Integrity Level: MEDIUM Description: BitDefender Management Console Exit code: 0 Version: 106.42.73.61 Modules
| |||||||||||||||
| 1900 | "C:\Users\admin\Desktop\SmartAssembly 6.8.0 + Keygen\KeygenSrv.exe" | C:\Users\admin\Desktop\SmartAssembly 6.8.0 + Keygen\KeygenSrv.exe | — | Keygen.exe | |||||||||||
User: admin Company: SOFTWIN S.R.L. Integrity Level: MEDIUM Description: BitDefender Management Console Exit code: 0 Version: 106.42.73.61 Modules
| |||||||||||||||
| 2252 | C:\Users\admin\Microsoft\DesktopLayerSrv.exe | C:\Users\admin\Microsoft\DesktopLayerSrv.exe | — | DesktopLayer.exe | |||||||||||
User: admin Company: SOFTWIN S.R.L. Integrity Level: MEDIUM Description: BitDefender Management Console Exit code: 0 Version: 106.42.73.61 Modules
| |||||||||||||||
| 2776 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | — | DesktopLayer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2820 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | KeygenSrvSrv.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2876 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\SmartAssembly 6.8.0 + Keygen.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3120 | C:\Users\admin\Microsoft\DesktopLayer.exe | C:\Users\admin\Microsoft\DesktopLayer.exe | — | DesktopLayerSrv.exe | |||||||||||
User: admin Company: SOFTWIN S.R.L. Integrity Level: MEDIUM Description: BitDefender Management Console Exit code: 0 Version: 106.42.73.61 Modules
| |||||||||||||||
Total events
2 693
Read events
2 392
Write events
298
Delete events
3
Modification events
| (PID) Process: | (2876) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2876) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2876) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2876) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (2876) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2876) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2876) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2876) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2820) iexplore.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | Userinit |
Value: C:\Windows\system32\userinit.exe, | |||
| (PID) Process: | (1784) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{03D02A8B-7A61-4263-8A58-FC6947629A97}\{20735FDA-5325-491D-BC5A-C076999FE485} |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
9
Suspicious files
0
Text files
9
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2820 | iexplore.exe | C:\Program Files\Microsoft\Skype for Desktop\LICENSES.chromium.html | — | |
MD5:— | SHA256:— | |||
| 2876 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2876.13258\SmartAssembly 6.8.0 + Keygen\Keygen.exe | executable | |
MD5:EA11A3A0A002DCB8B8581041CC8F1AE9 | SHA256:— | |||
| 2876 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2876.13258\SmartAssembly 6.8.0 + Keygen\SmartAssembly.exe | executable | |
MD5:6EB901407FF50F5EDE56AC4F90480F4F | SHA256:38D7DBD2FD38DF509174C3D1B205304313C12D206A7B0DC4635EF56916ECF812 | |||
| 2820 | iexplore.exe | C:\Program Files\Adobe\Acrobat Reader DC\Reader\WebResources\Resource1\index.html | html | |
MD5:89BB70E172DD1DE12EF92A3CFC7DB945 | SHA256:E4B98A2E87231D00E3B91926F2FB531CEF9A3D8F2908F940E3442CB278DCA5F4 | |||
| 1444 | Keygen.exe | C:\Users\admin\AppData\Local\Temp\Temp_Skin.vssf | xml | |
MD5:F3390BCC7835C2DEB64F87642D72D3BF | SHA256:CCF81D134226ACFC3CB6BD2710C551FDAB2E79F335F739A5A55A3EDD69CC71D7 | |||
| 2820 | iexplore.exe | C:\Program Files\Adobe\Acrobat Reader DC\ReadMe.htm | html | |
MD5:73228CB50996251594A1D0C8AA7416ED | SHA256:94CCBE91489635345BA6CB4012C43E5D5E9337CC8CA774E6F8BB8F14D9947593 | |||
| 2820 | iexplore.exe | C:\Program Files\Adobe\Acrobat Reader DC\Reader\ngl_resources\resources\ui\index.html | html | |
MD5:C96625984CD3CF51A3DB24CC0E6EAB89 | SHA256:9595AC02CFC7172BCD46F8F6021E8F61B899F51A05A7CB5B6549B20E6AA91296 | |||
| 1444 | Keygen.exe | C:\Users\admin\AppData\Local\SkinSoft\VisualStyler\2.3.3.3\x86\ssapihook.dll | executable | |
MD5:D7F644C06B4CDE60651D02AED6B4174D | SHA256:A99EA2F5759B34859B484AFA3A58CE82A7F3BF792886A6C838DB852D517D9C0D | |||
| 2820 | iexplore.exe | C:\Program Files\Microsoft Office\Office14\1031\FPSFECFG.HTM | html | |
MD5:9311A5A596AC30A938D454E6CE677C38 | SHA256:E60DA3A14337349B19FA356199A78292553F7ECDDB82DAB9360B03425C249485 | |||
| 2820 | iexplore.exe | C:\Program Files\Java\jre1.8.0_271\Welcome.html | html | |
MD5:713C93CEAEBCC1D9EF532B1600E746BE | SHA256:1F6F1E80C1F4405C863F234A66A255C430D30249C3CE56B058FF047C5F999098 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
12
DNS requests
4
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1080 | svchost.exe | GET | 200 | 8.248.147.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?08208ad102fb932b | unknown | — | 4.66 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | unknown |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2820 | iexplore.exe | 142.250.185.206:80 | — | GOOGLE | US | unknown |
2820 | iexplore.exe | 34.175.230.209:443 | fget-career.com | GOOGLE-CLOUD-PLATFORM | ES | unknown |
2820 | iexplore.exe | 142.250.186.174:80 | google.com | GOOGLE | US | unknown |
1080 | svchost.exe | 8.248.147.254:80 | ctldl.windowsupdate.com | LEVEL3 | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
fget-career.com |
| unknown |
google.com |
| unknown |
ctldl.windowsupdate.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2820 | iexplore.exe | Malware Command and Control Activity Detected | ET MALWARE Win32/Ramnit Checkin |
2820 | iexplore.exe | Malware Command and Control Activity Detected | ET MALWARE Win32/Ramnit Checkin |
2 ETPRO signatures available at the full report