| download: | f.msi |
| Full analysis: | https://app.any.run/tasks/0a9d3c6f-384f-4853-88f5-0e5eef4b2154 |
| Verdict: | Malicious activity |
| Threats: | GuLoader is an advanced downloader written in shellcode. It’s used by criminals to distribute other malware, notably trojans, on a large scale. It’s infamous for using anti-detection and anti-analysis capabilities. |
| Analysis date: | May 22, 2020, 02:19:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
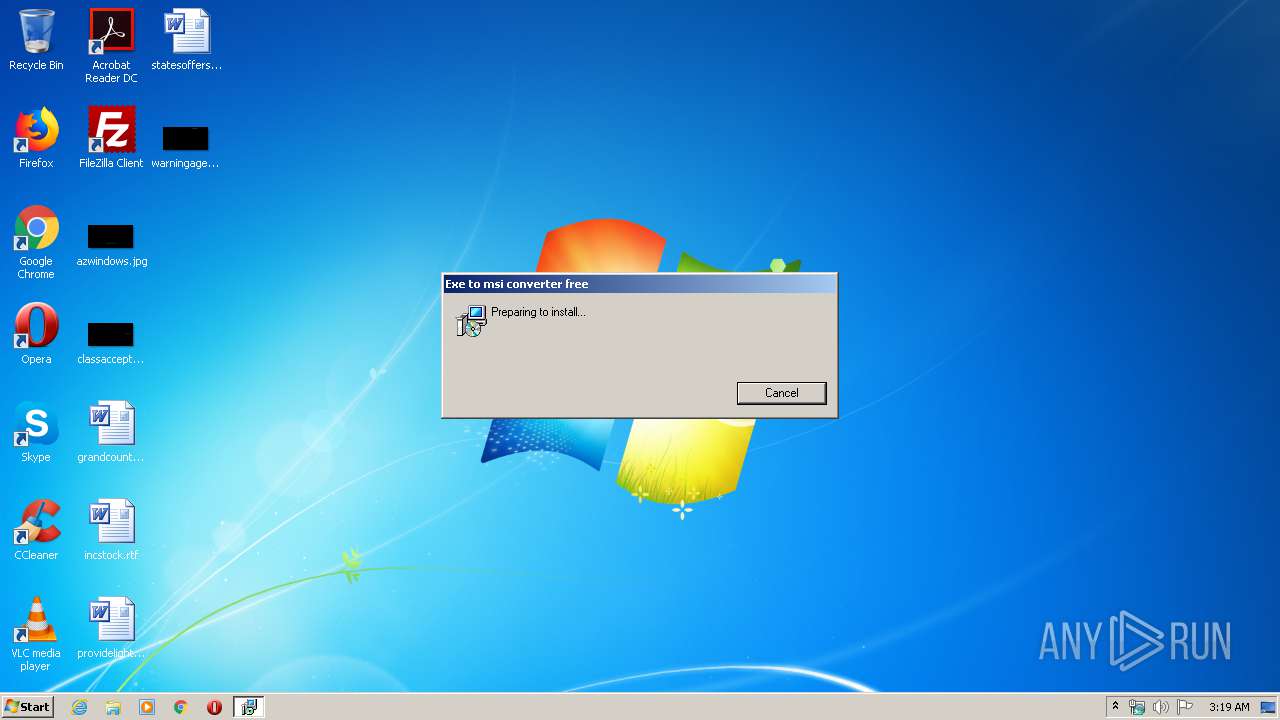
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, MSI Installer, Code page: 1252, Last Printed: Fri Sep 21 10:56:09 2012, Create Time/Date: Fri Sep 21 10:56:09 2012, Name of Creating Application: Windows Installer, Title: Exe to msi converter free, Author: www.exetomsi.com, Template: ;0, Last Saved By: devuser, Revision Number: {C35CF0AA-9B3F-4903-9F05-EBF606D58D3E}, Last Saved Time/Date: Tue May 21 12:56:44 2013, Number of Pages: 100, Number of Words: 0, Security: 0 |
| MD5: | 3716A2D05820EB52C4D67F720DA22922 |
| SHA1: | D3A8408DDBE617B0C30CD6B13D5E33075A9F7B09 |
| SHA256: | F4A7A804E89A57316623E31EC3D3FAF37A138542015D0EB980A0444A585A5840 |
| SSDEEP: | 1536:FE9OThBrFOJ9gp4Dl6Y9pfgokykQrMhVjaFt:FE9UBrFOJ9gKgYLkiejaz |
MALICIOUS
Changes the autorun value in the registry
- ieinstal.exe (PID: 2428)
GULOADER was detected
- ieinstal.exe (PID: 2428)
NETWIRE was detected
- ieinstal.exe (PID: 2428)
SUSPICIOUS
Executed as Windows Service
- vssvc.exe (PID: 4024)
Drop ExeToMSI Application
- msiexec.exe (PID: 788)
Executable content was dropped or overwritten
- msiexec.exe (PID: 788)
- ieinstal.exe (PID: 2428)
Creates files in the user directory
- ieinstal.exe (PID: 2428)
INFO
Application was dropped or rewritten from another process
- MSICFA0.tmp (PID: 2540)
Searches for installed software
- msiexec.exe (PID: 788)
Starts application with an unusual extension
- msiexec.exe (PID: 788)
Low-level read access rights to disk partition
- vssvc.exe (PID: 4024)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Installer (100) |
|---|
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| LastPrinted: | 2012:09:21 09:56:09 |
| CreateDate: | 2012:09:21 09:56:09 |
| Software: | Windows Installer |
| Title: | Exe to msi converter free |
| Subject: | - |
| Author: | www.exetomsi.com |
| Keywords: | - |
| Comments: | - |
| Template: | ;0 |
| LastModifiedBy: | devuser |
| RevisionNumber: | {C35CF0AA-9B3F-4903-9F05-EBF606D58D3E} |
| ModifyDate: | 2013:05:21 11:56:44 |
| Pages: | 100 |
| Words: | - |
| Security: | None |
Total processes
39
Monitored processes
5
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 788 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 984 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\f.msi" | C:\Windows\System32\msiexec.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2428 | "C:\Windows\Installer\MSICFA0.tmp" | C:\Program Files\internet explorer\ieinstal.exe | MSICFA0.tmp | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Internet Explorer Add-on Installer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2540 | "C:\Windows\Installer\MSICFA0.tmp" | C:\Windows\Installer\MSICFA0.tmp | — | msiexec.exe | |||||||||||
User: admin Company: Cream Integrity Level: MEDIUM Exit code: 0 Version: 1.01 Modules
| |||||||||||||||
| 4024 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
647
Read events
463
Write events
172
Delete events
12
Modification events
| (PID) Process: | (788) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4000000000000000AE25BD7DDF2FD60114030000F00D0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (788) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4000000000000000AE25BD7DDF2FD60114030000F00D0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (788) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 36 | |||
| (PID) Process: | (788) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4000000000000000A2350E7EDF2FD60114030000F00D0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (788) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000FC97107EDF2FD60114030000A80B0000E8030000010000000000000000000000B31521DFF25A6A48983B9E3AAE9ACE260000000000000000 | |||
| (PID) Process: | (4024) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 400000000000000018E61E7EDF2FD601B80F0000E00B0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4024) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 400000000000000018E61E7EDF2FD601B80F0000F4080000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4024) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 400000000000000018E61E7EDF2FD601B80F000068070000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4024) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 400000000000000018E61E7EDF2FD601B80F000078030000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4024) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 4000000000000000DAD12A7EDF2FD601B80F000068070000E8030000000000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
3
Suspicious files
5
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 788 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 788 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF2228C4C5FC07DA5F.TMP | — | |
MD5:— | SHA256:— | |||
| 4024 | vssvc.exe | C: | — | |
MD5:— | SHA256:— | |||
| 788 | msiexec.exe | C:\Config.Msi\15c6e6.rbs | — | |
MD5:— | SHA256:— | |||
| 788 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF96B080BF3CF4305D.TMP | — | |
MD5:— | SHA256:— | |||
| 788 | msiexec.exe | C:\Windows\Installer\MSICFA0.tmp | executable | |
MD5:— | SHA256:— | |||
| 788 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:— | SHA256:— | |||
| 788 | msiexec.exe | C:\Windows\Installer\15c6e5.ipi | binary | |
MD5:— | SHA256:— | |||
| 2428 | ieinstal.exe | C:\Users\admin\AppData\Local\Temp\Chequerwise4\Barkbillens.exe | binary | |
MD5:— | SHA256:— | |||
| 788 | msiexec.exe | C:\Windows\Installer\15c6e3.msi | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
1
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2428 | ieinstal.exe | GET | 200 | 89.46.108.69:80 | http://www.cmweenergy.it/of.bin | IT | binary | 161 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2428 | ieinstal.exe | 89.46.108.69:80 | www.cmweenergy.it | Aruba S.p.A. | IT | malicious |
2428 | ieinstal.exe | 79.134.225.35:8030 | — | Andreas Fink trading as Fink Telecom Services | CH | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.cmweenergy.it |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2428 | ieinstal.exe | A Network Trojan was detected | MALWARE [PTsecurity] EJNT_Loader |
1 ETPRO signatures available at the full report