| File name: | DriveMgr.exe |
| Full analysis: | https://app.any.run/tasks/4203f2b8-d0eb-40b8-a188-6ddd235d9c30 |
| Verdict: | Malicious activity |
| Threats: | Phorpiex is a malicious software that has been a significant threat in the cybersecurity landscape since 2016. It is a modular malware known for its ability to maintain an extensive botnet. Unlike other botnets, Phorpiex does not concentrate on DDoS attacks. Instead, it has been involved in numerous large-scale spam email campaigns and the distribution of other malicious payloads, such as LockBit. |
| Analysis date: | November 30, 2020, 08:42:44 |
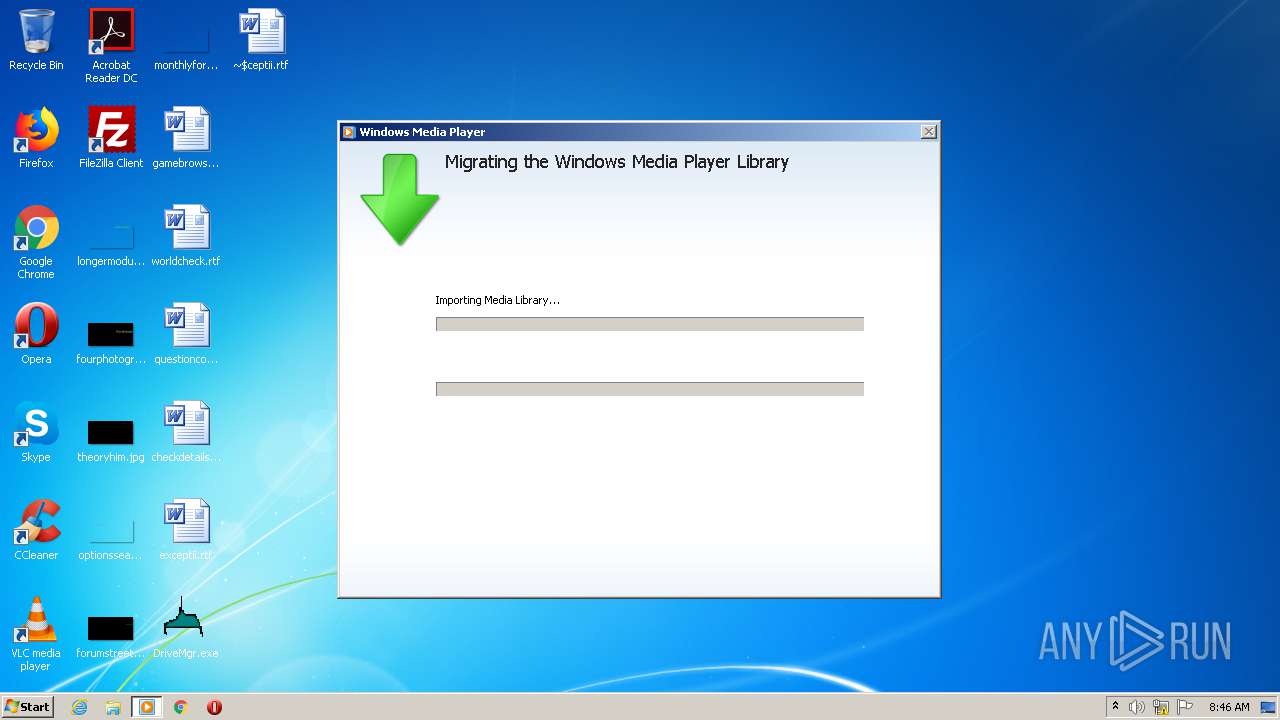
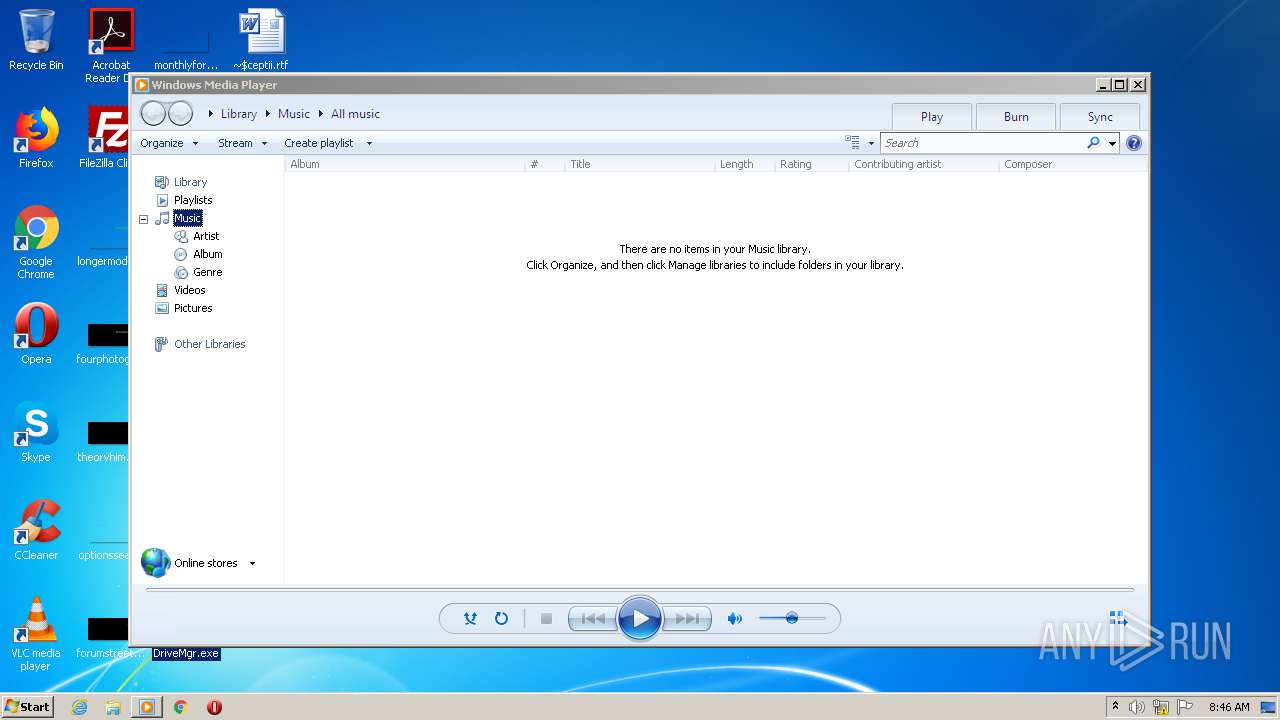
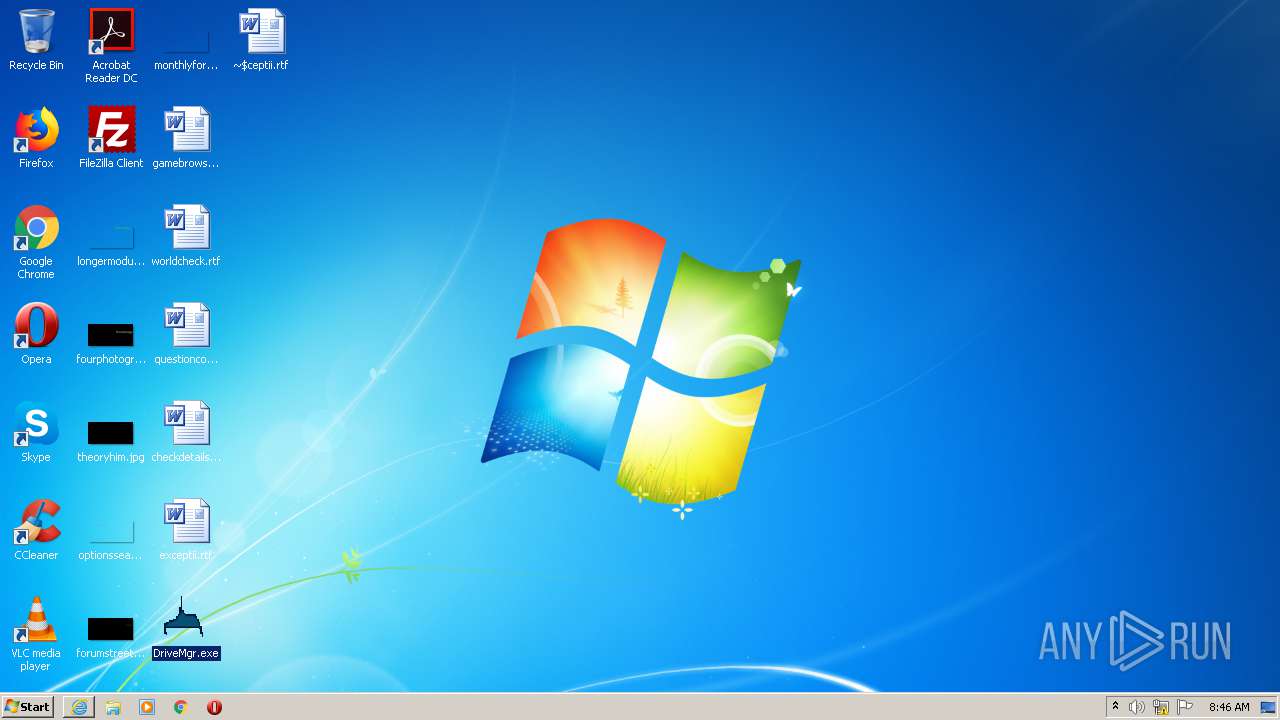
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | AB97F71125A89D4D3D0855B8A419D3E1 |
| SHA1: | 2442D4A7CFBE7FD22708034C853FAF9AA4337907 |
| SHA256: | F4909C420E208E4728116E8B0F4254C9F741D864F9618CDDBE3F51B71F602066 |
| SSDEEP: | 3072:krVZV7IFJc/+mKda7FpoXaoxRypPzB1DuFYJPrbLxYpj5S3BugoIvc/:krNEFJndso2vD3RrbLxYpj5gRy |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- DriveMgr.exe (PID: 2184)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:10:05 03:11:52+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 61440 |
| InitializedDataSize: | 69632 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x7fec |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.1 |
| ProductVersionNumber: | 1.0.0.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Ruksun Software Technologies |
| FileDescription: | AutoWallPaper |
| FileVersion: | 1, 0, 0, 1 |
| InternalName: | AutoWallPaper |
| LegalCopyright: | Copyright © 1999 |
| OriginalFileName: | AutoWallPaper.exe |
| ProductName: | Ruksun Software Technologies AutoWallPaper |
| ProductVersion: | 1, 0, 0, 1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Oct-2019 01:11:52 |
| Detected languages: |
|
| CompanyName: | Ruksun Software Technologies |
| FileDescription: | AutoWallPaper |
| FileVersion: | 1, 0, 0, 1 |
| InternalName: | AutoWallPaper |
| LegalCopyright: | Copyright © 1999 |
| OriginalFilename: | AutoWallPaper.exe |
| ProductName: | Ruksun Software Technologies AutoWallPaper |
| ProductVersion: | 1, 0, 0, 1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 05-Oct-2019 01:11:52 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000EB45 | 0x0000F000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.46023 |
.rdata | 0x00010000 | 0x0000258E | 0x00003000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.91949 |
.data | 0x00013000 | 0x0000C3C8 | 0x0000B000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.43581 |
.rsrc | 0x00020000 | 0x00000CE8 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.57866 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.39046 | 824 | UNKNOWN | English - United States | RT_VERSION |
2 | 1.92886 | 296 | UNKNOWN | English - United States | RT_ICON |
101 | 2.66295 | 150 | UNKNOWN | English - United States | RT_MENU |
102 | 2.37086 | 34 | UNKNOWN | English - United States | RT_GROUP_ICON |
103 | 3.2962 | 400 | UNKNOWN | English - United States | RT_DIALOG |
104 | 3.42721 | 362 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
Total processes
35
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
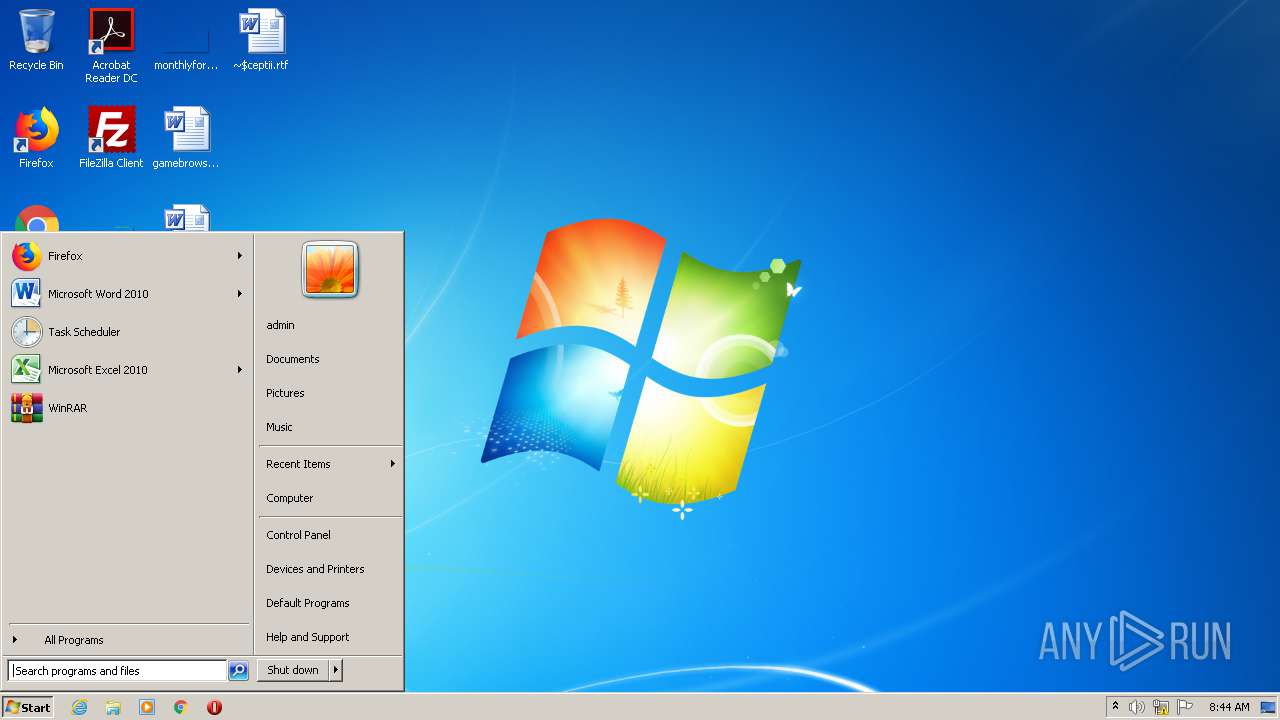
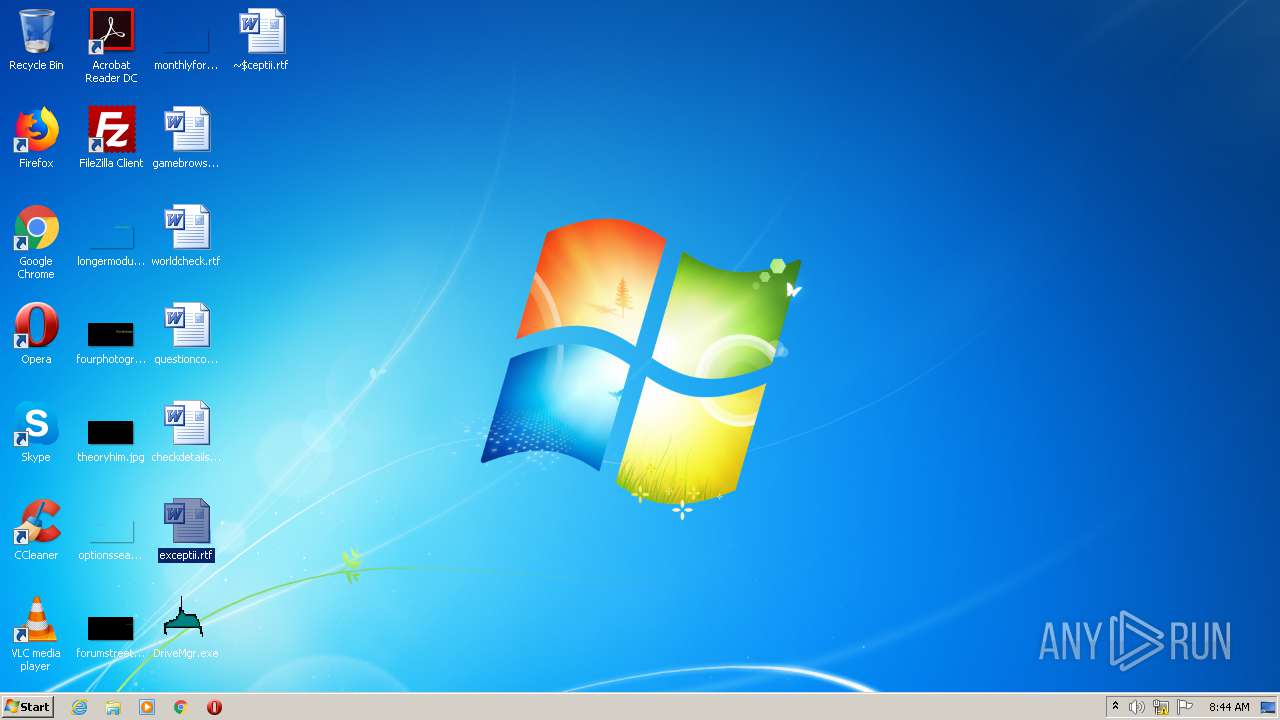
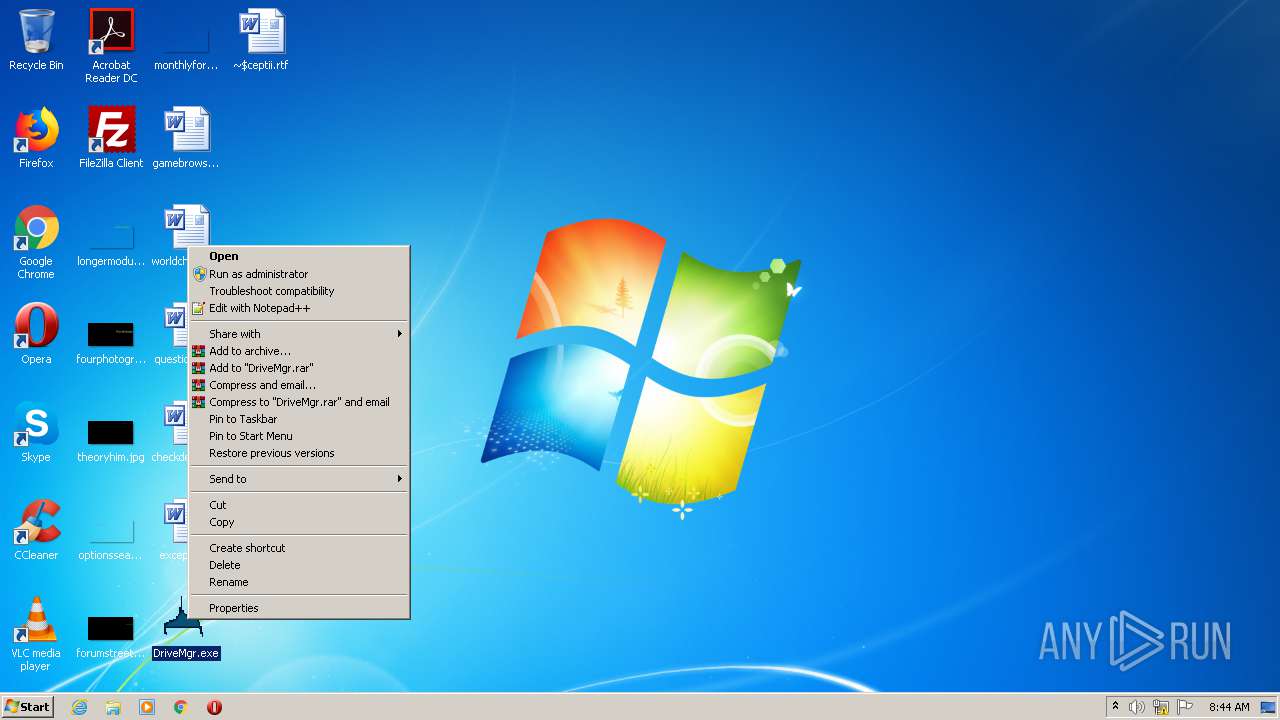
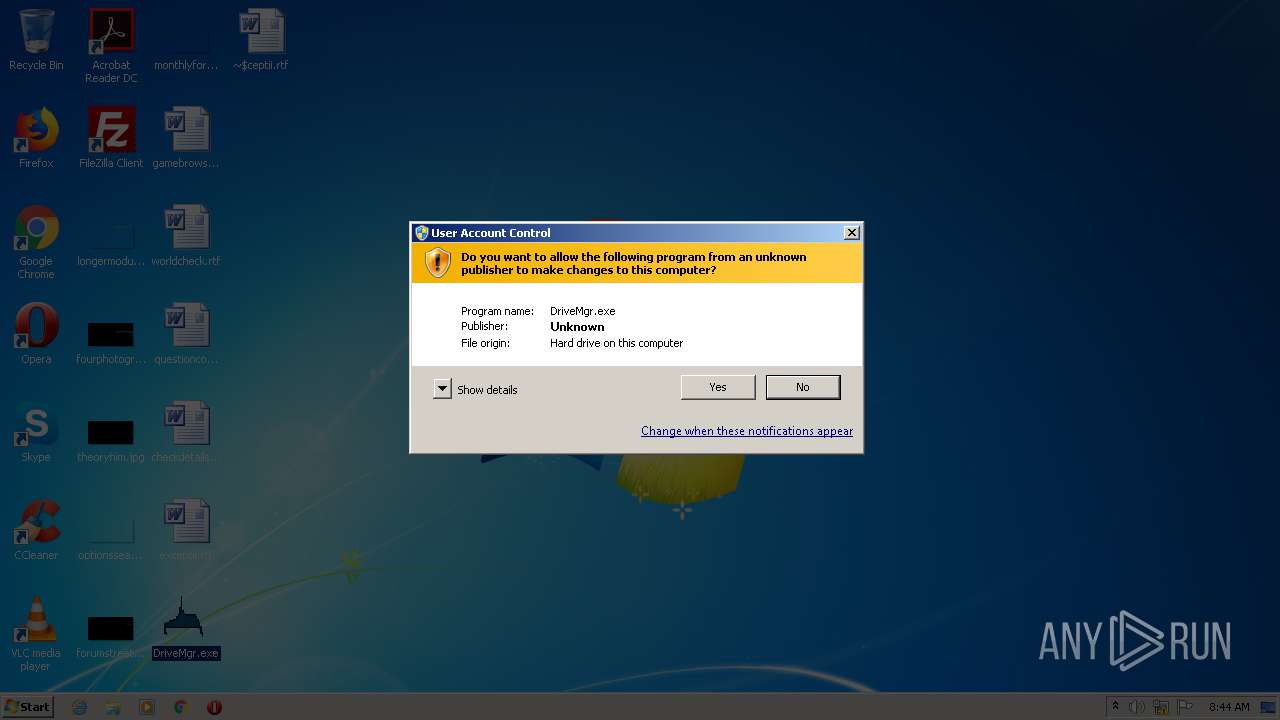
| 2184 | "C:\Users\admin\Desktop\DriveMgr.exe" | C:\Users\admin\Desktop\DriveMgr.exe | explorer.exe | ||||||||||||
User: admin Company: Ruksun Software Technologies Integrity Level: MEDIUM Description: AutoWallPaper Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2184 | DriveMgr.exe | C:\Users\admin\155718718\sysemeu.exe | executable | |
MD5:AB97F71125A89D4D3D0855B8A419D3E1 | SHA256:F4909C420E208E4728116E8B0F4254C9F741D864F9618CDDBE3F51B71F602066 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
164
TCP/UDP connections
184
DNS requests
121
Threats
128
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | — | 185.176.27.132:80 | http://185.176.27.132/t.php?new=1 | GB | — | — | malicious |
— | — | GET | — | 35.205.61.67:80 | http://aeifaeifhutuhuhusd.io/t.php?new=1 | US | — | — | whitelisted |
— | — | GET | — | 35.205.61.67:80 | http://urusurofhsorhfuuhd.io/t.php?new=1 | US | — | — | whitelisted |
— | — | GET | — | 35.205.61.67:80 | http://bfagzzezgaegzgfaid.io/t.php?new=1 | US | — | — | whitelisted |
— | — | GET | — | 35.205.61.67:80 | http://rzhsudhugugfugugsd.io/t.php?new=1 | US | — | — | whitelisted |
— | — | GET | — | 35.205.61.67:80 | http://eaeuafhuaegfugeudd.io/t.php?new=1 | US | — | — | whitelisted |
— | — | GET | — | 35.205.61.67:80 | http://aeufuaehfiuehfuhfd.io/t.php?new=1 | US | — | — | whitelisted |
— | — | GET | — | 35.205.61.67:80 | http://daedagheauehfuuhfd.io/t.php?new=1 | US | — | — | whitelisted |
— | — | GET | — | 35.205.61.67:80 | http://aeoughaoheguaoehdd.io/t.php?new=1 | US | — | — | whitelisted |
— | — | GET | — | 35.205.61.67:80 | http://eguaheoghouughahsd.io/t.php?new=1 | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 185.176.27.132:80 | — | — | GB | malicious |
— | — | 35.205.61.67:80 | urusurofhsorhfuuhd.io | Google Inc. | US | malicious |
— | — | 208.100.26.245:80 | rzhsudhugugfugugsh.co | Steadfast | US | malicious |
— | — | 107.6.74.76:80 | afaeigaifgsgrhhafd.io | Voxel Dot Net, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
urusurofhsorhfuuhp.su |
| malicious |
aeifaeifhutuhuhusp.su |
| malicious |
rzhsudhugugfugugsp.su |
| malicious |
bfagzzezgaegzgfaip.su |
| malicious |
eaeuafhuaegfugeudp.su |
| malicious |
aeufuaehfiuehfuhfp.su |
| malicious |
daedagheauehfuuhfp.su |
| malicious |
aeoughaoheguaoehdp.su |
| malicious |
eguaheoghouughahsp.su |
| malicious |
huaeokaefoaeguaehp.su |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
— | — | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
— | — | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
— | — | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
— | — | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
— | — | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
— | — | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
— | — | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
— | — | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
— | — | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
63 ETPRO signatures available at the full report