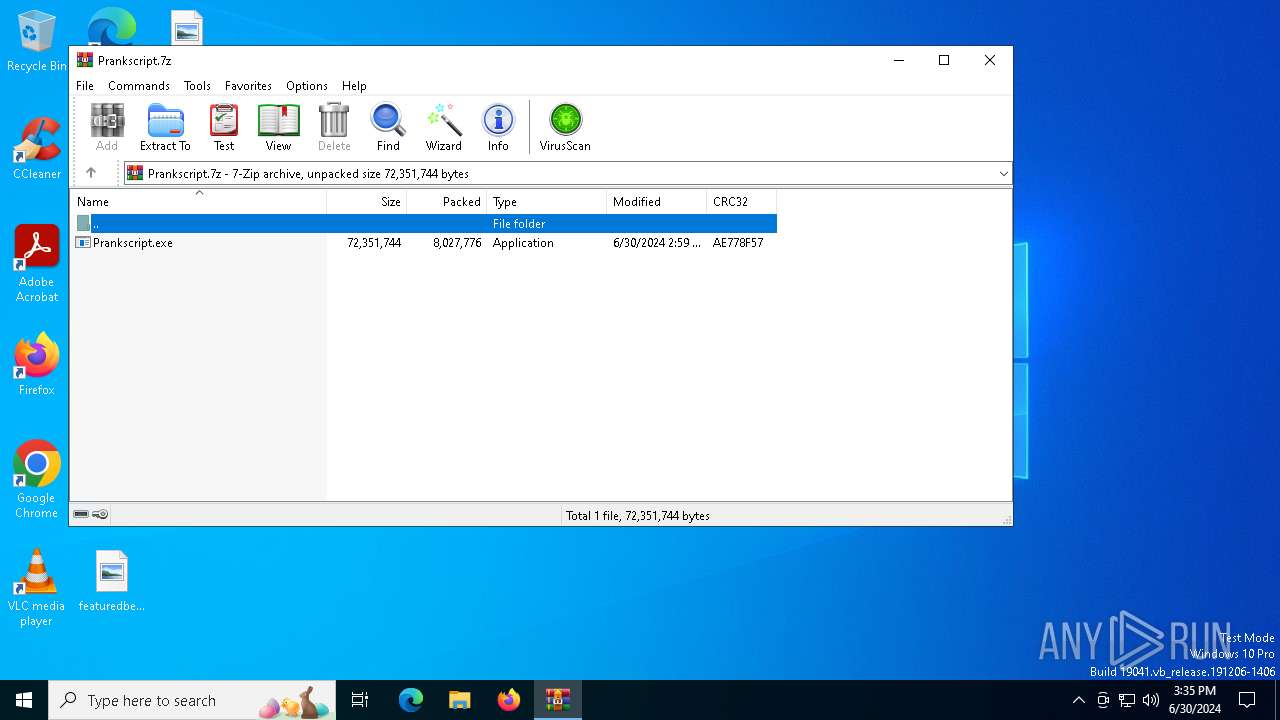
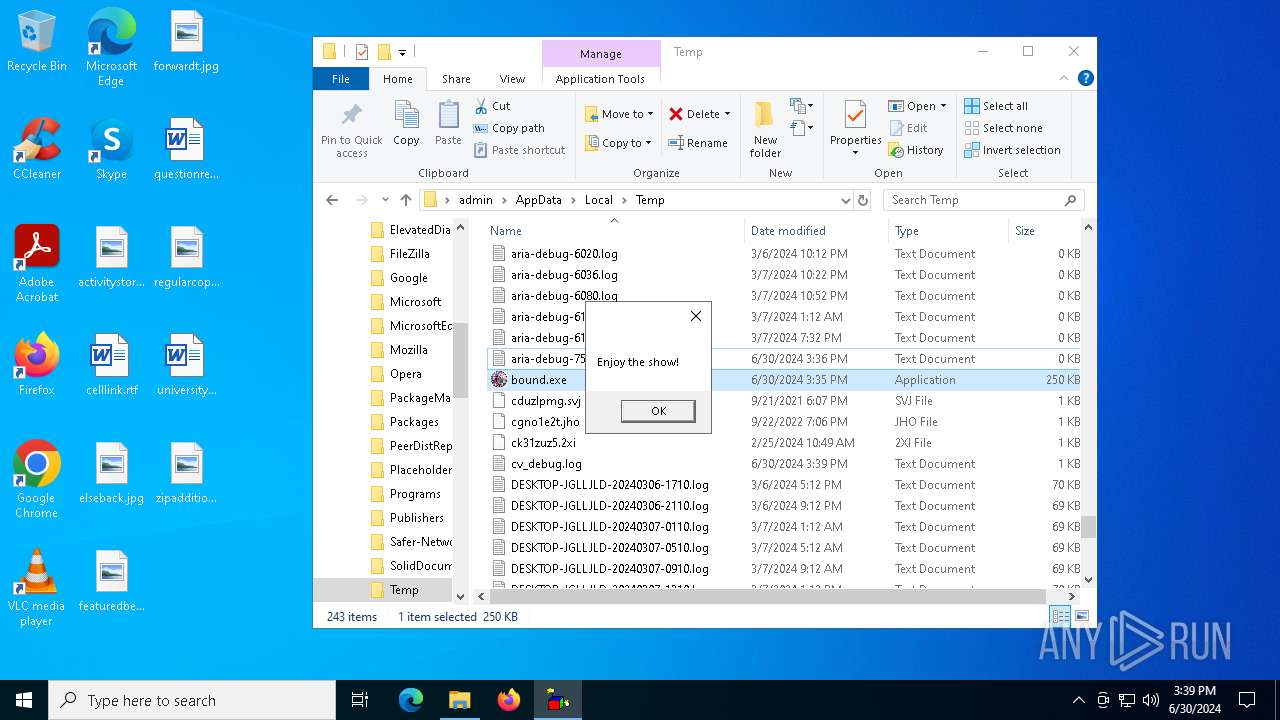
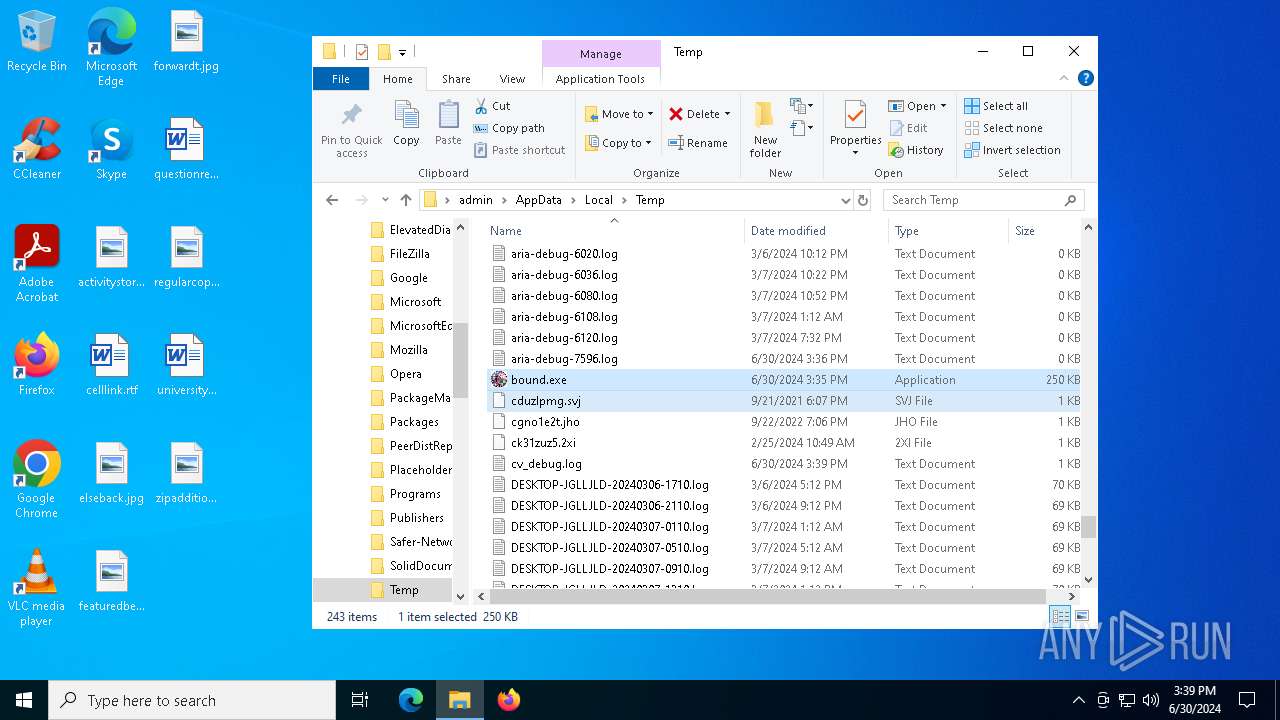
| File name: | Prankscript.7z |
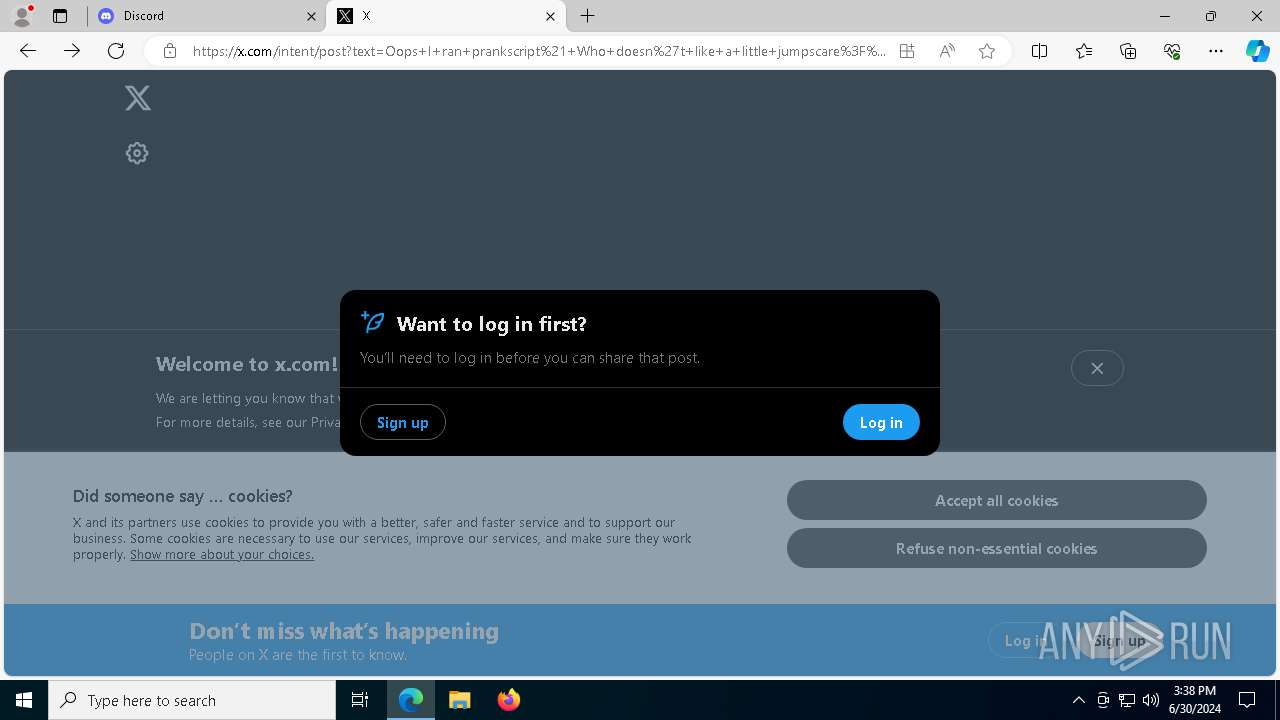
| Full analysis: | https://app.any.run/tasks/455bf718-f40b-4e99-9ece-82647d7f3191 |
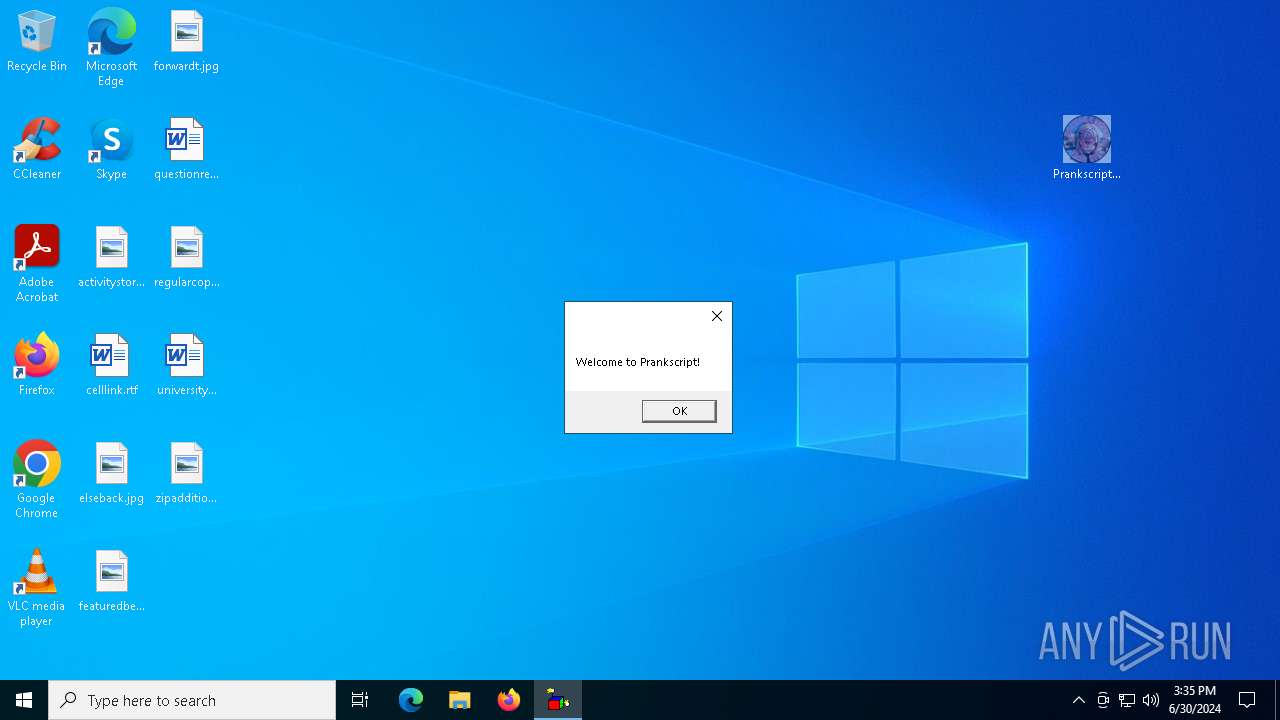
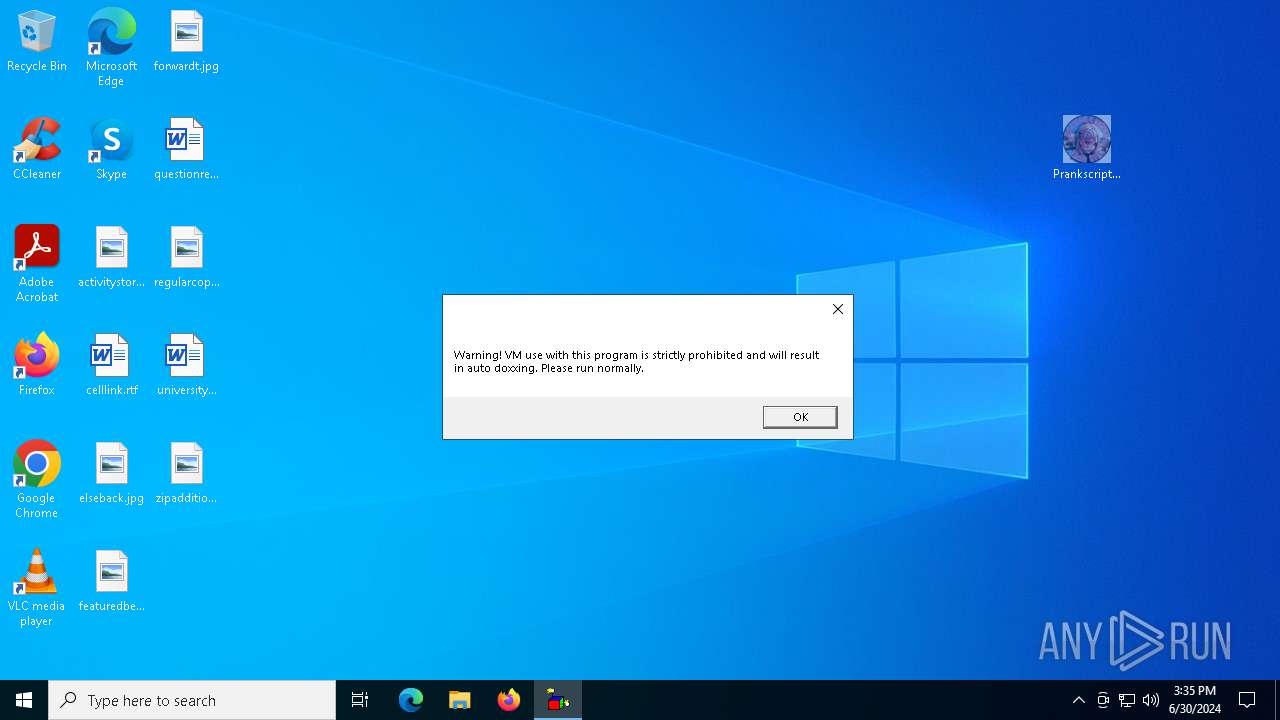
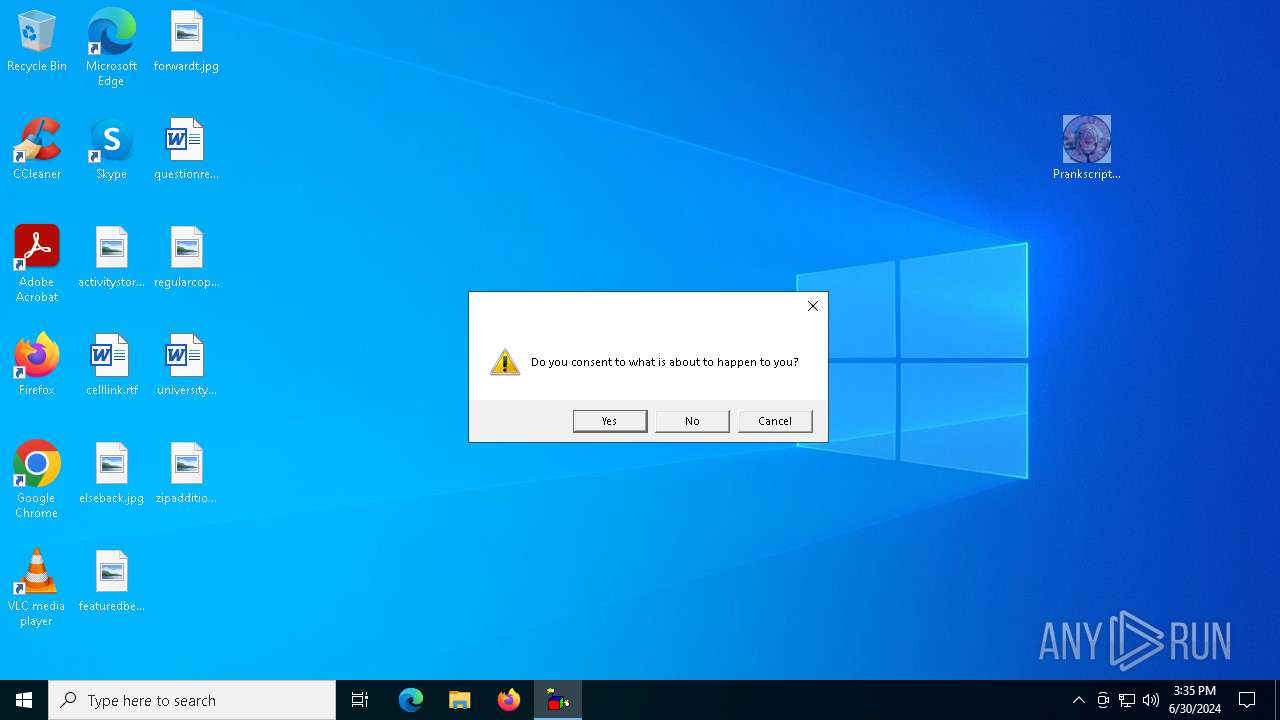
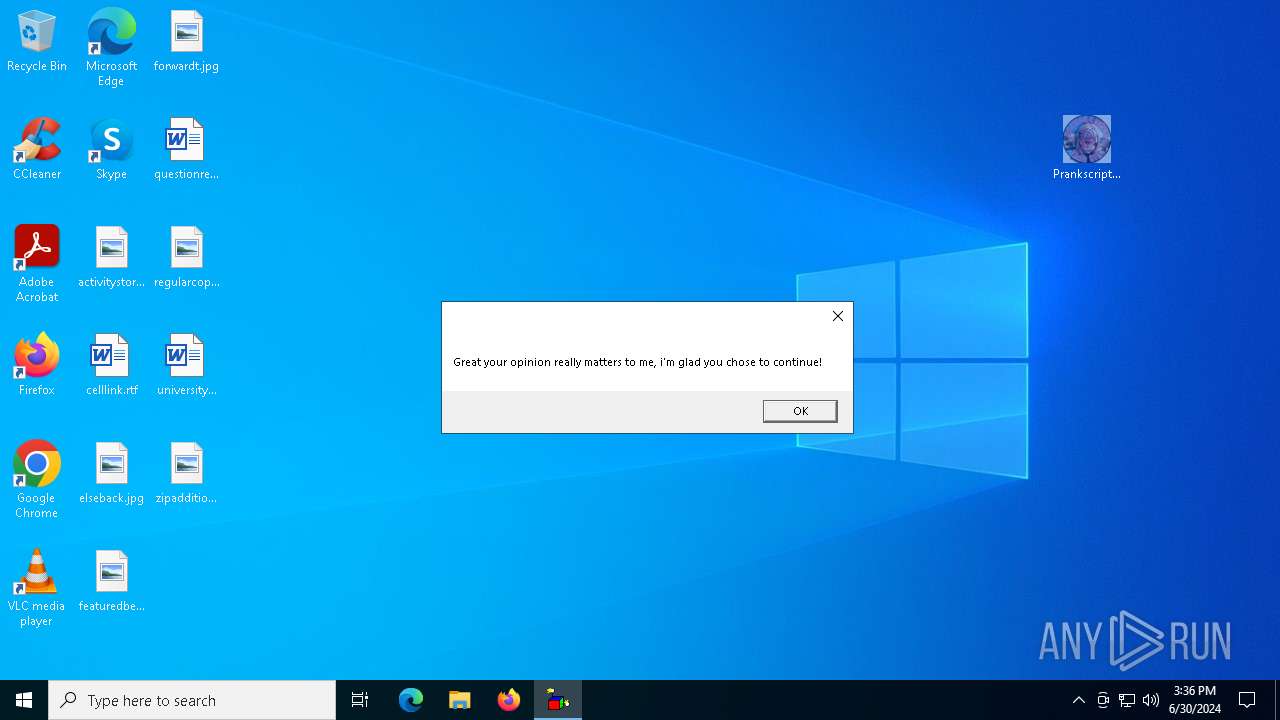
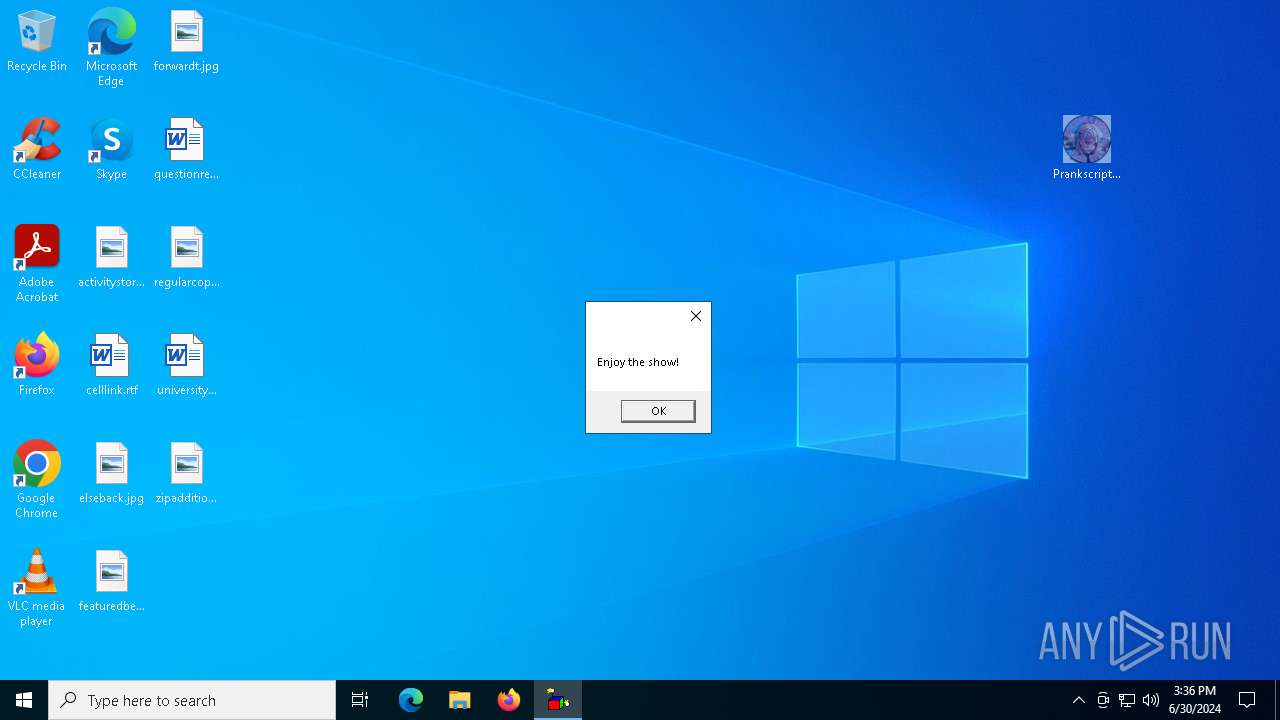
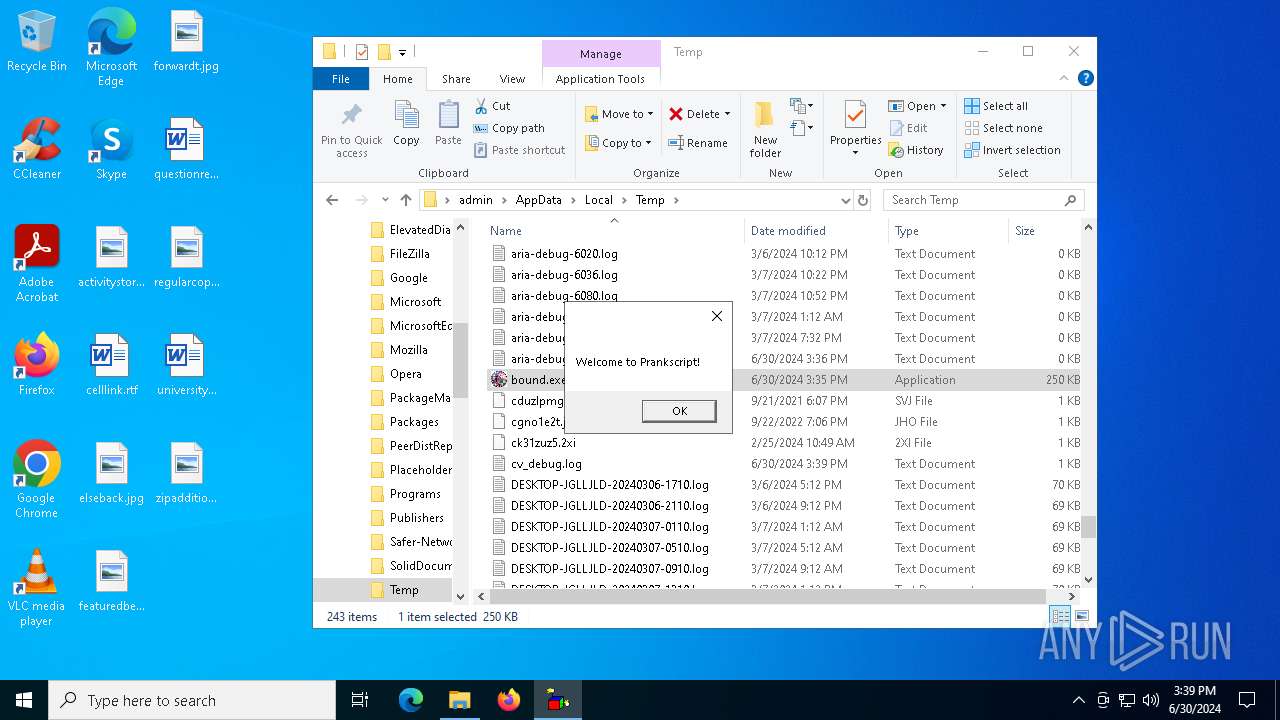
| Verdict: | Malicious activity |
| Threats: | Blank Grabber is an infostealer written in Python. It is designed to steal a wide array of data, such as browser login credentials, crypto wallets, Telegram sessions, and Discord tokens. It is an open-source malware, with its code available on GitHub and regularly receiving updates. Blank Grabber builder’s simple interface lets threat actors even with basic skills to deploy it and conduct attacks. |
| Analysis date: | June 30, 2024, 15:35:32 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 1DF80FC2D31BE574FF76A8309A1DC7A4 |
| SHA1: | 918079516001C53724E9BAAB2414C967301F34EF |
| SHA256: | F48798635FC1D66522C90BA172A9D3A589E6B3D6E9517FEC8E6EAA46261F9030 |
| SSDEEP: | 98304:zFjKFvScI6Cw1QtZW+hPjt2jFCumgET059dqvZJ18UH5SjTpn2wxmT45+KQE5Gcj:Je8nERm9on |
MALICIOUS
Drops the executable file immediately after the start
- WinRAR.exe (PID: 1020)
- Prankscript.exe (PID: 5564)
- Prankscript.exe (PID: 900)
- Prankscript.exe (PID: 4172)
- csc.exe (PID: 7872)
BlankGrabber has been detected
- Prankscript.exe (PID: 5564)
- Prankscript.exe (PID: 900)
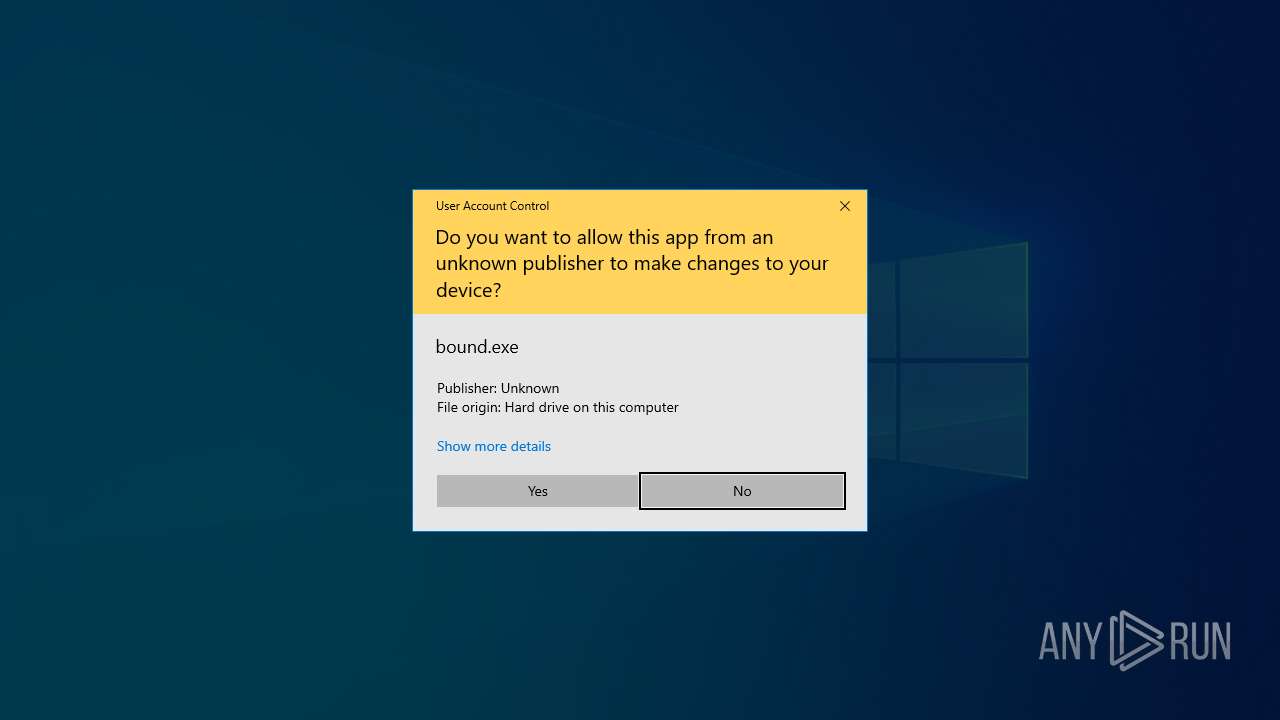
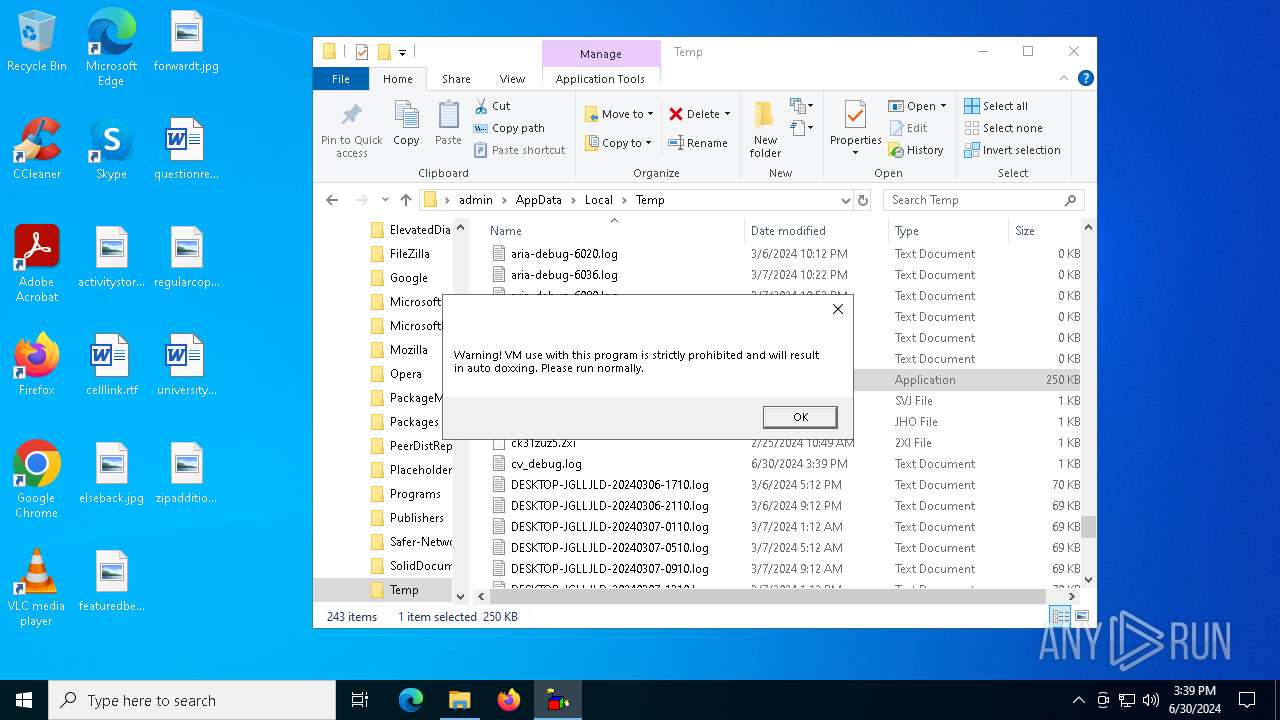
Bypass User Account Control (Modify registry)
- reg.exe (PID: 3880)
Bypass User Account Control (ComputerDefaults)
- ComputerDefaults.exe (PID: 32)
Adds path to the Windows Defender exclusion list
- Prankscript.exe (PID: 4172)
- cmd.exe (PID: 2968)
- cmd.exe (PID: 6020)
Antivirus name has been found in the command line (generic signature)
- cmd.exe (PID: 3944)
- MpCmdRun.exe (PID: 7156)
Windows Defender preferences modified via 'Set-MpPreference'
- cmd.exe (PID: 3944)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 6968)
Bypass execution policy to execute commands
- powershell.exe (PID: 6188)
Starts CMD.EXE for self-deleting
- Prankscript.exe (PID: 4172)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 6388)
- wscript.exe (PID: 8140)
BLANKGRABBER has been detected (SURICATA)
- Prankscript.exe (PID: 4172)
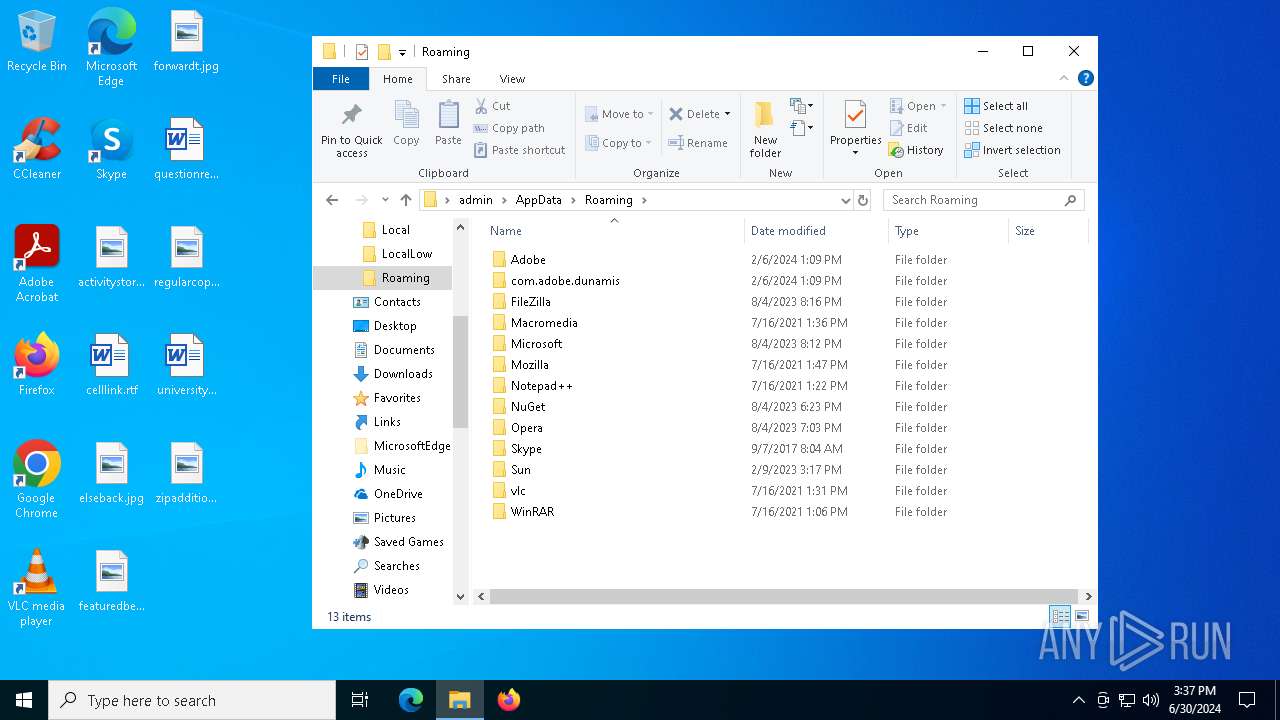
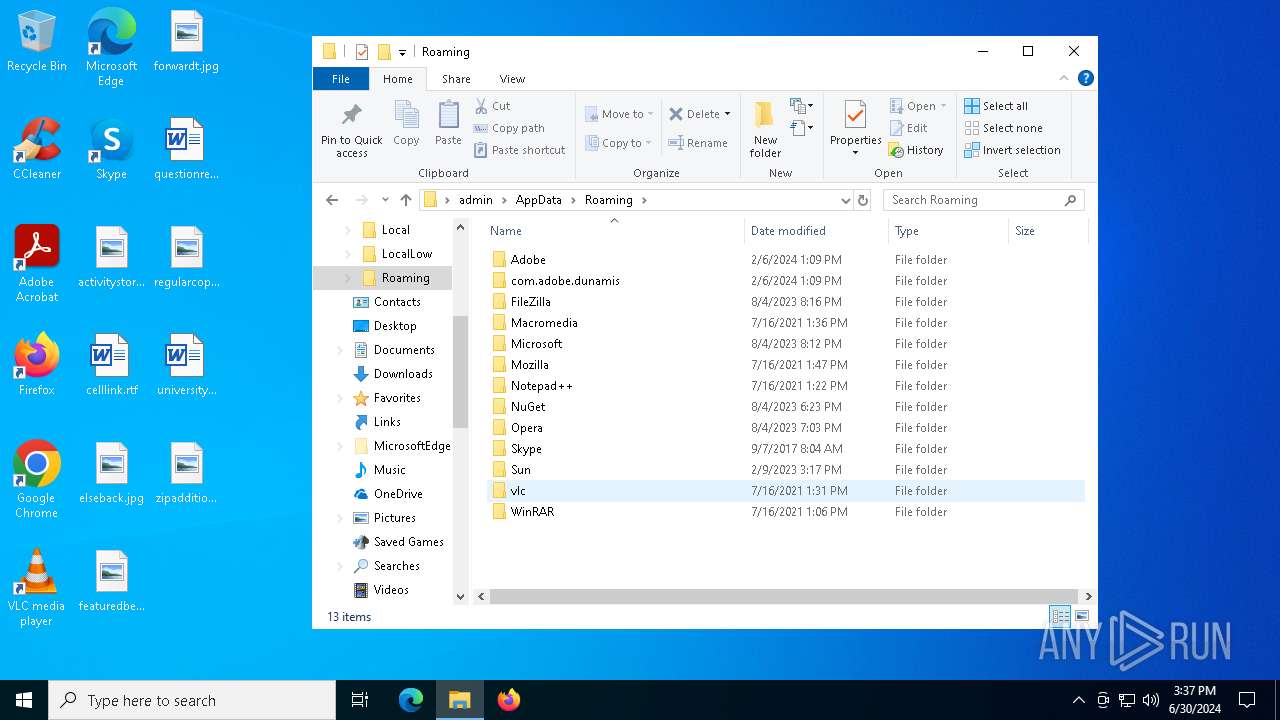
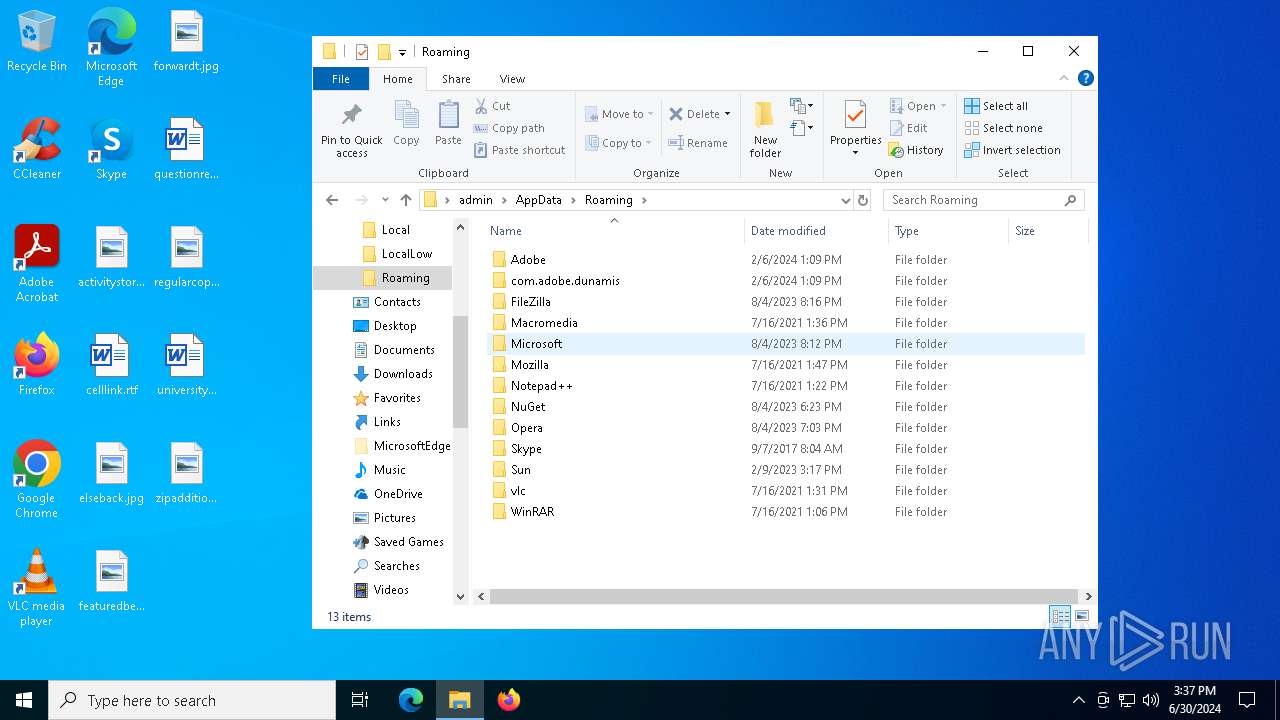
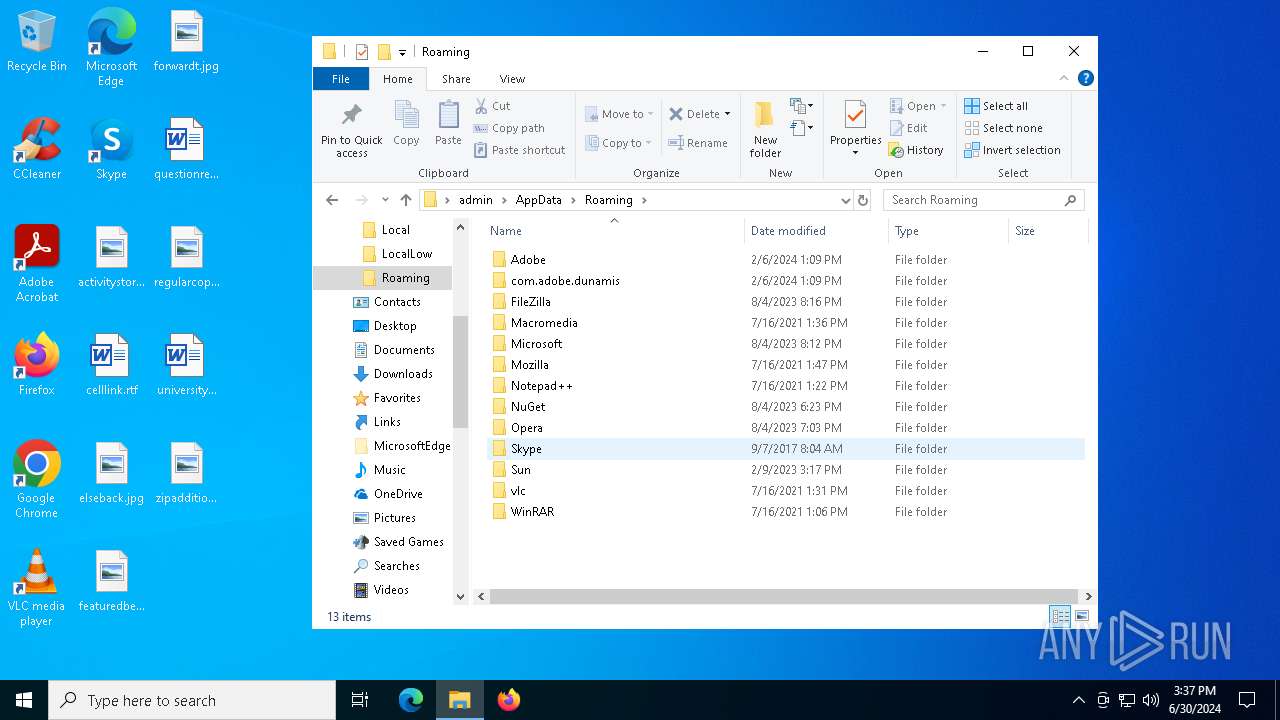
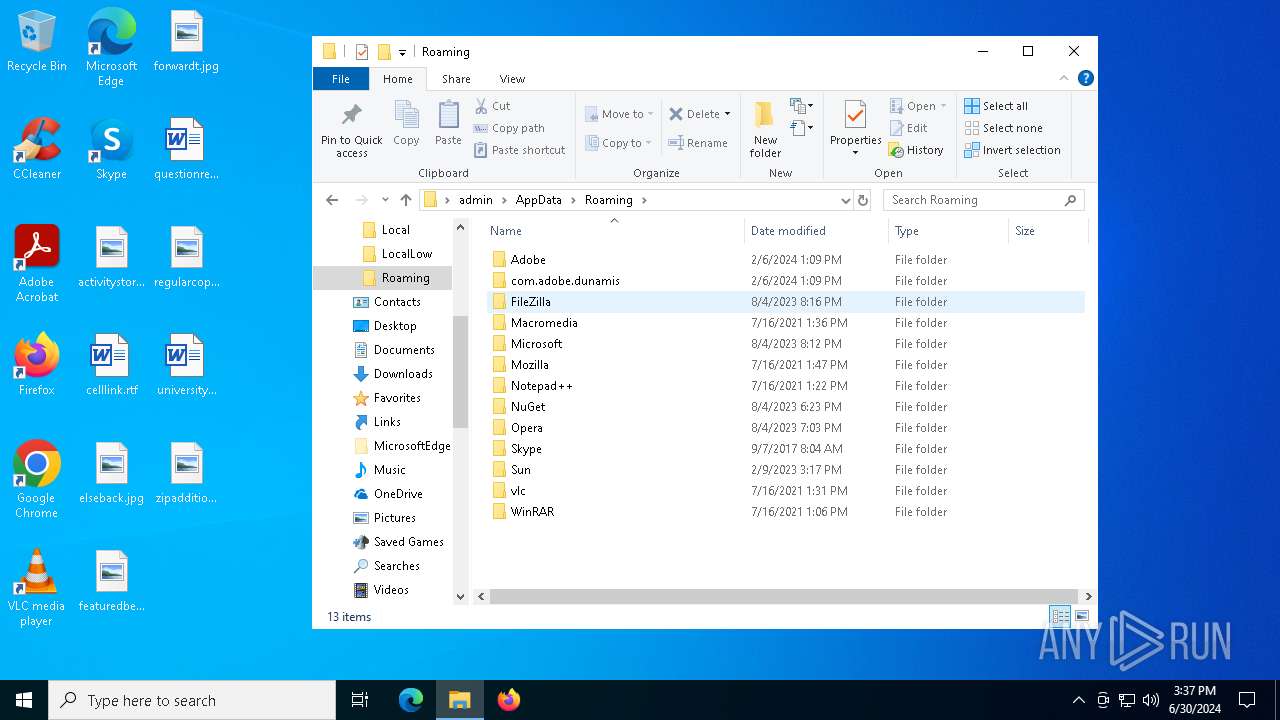
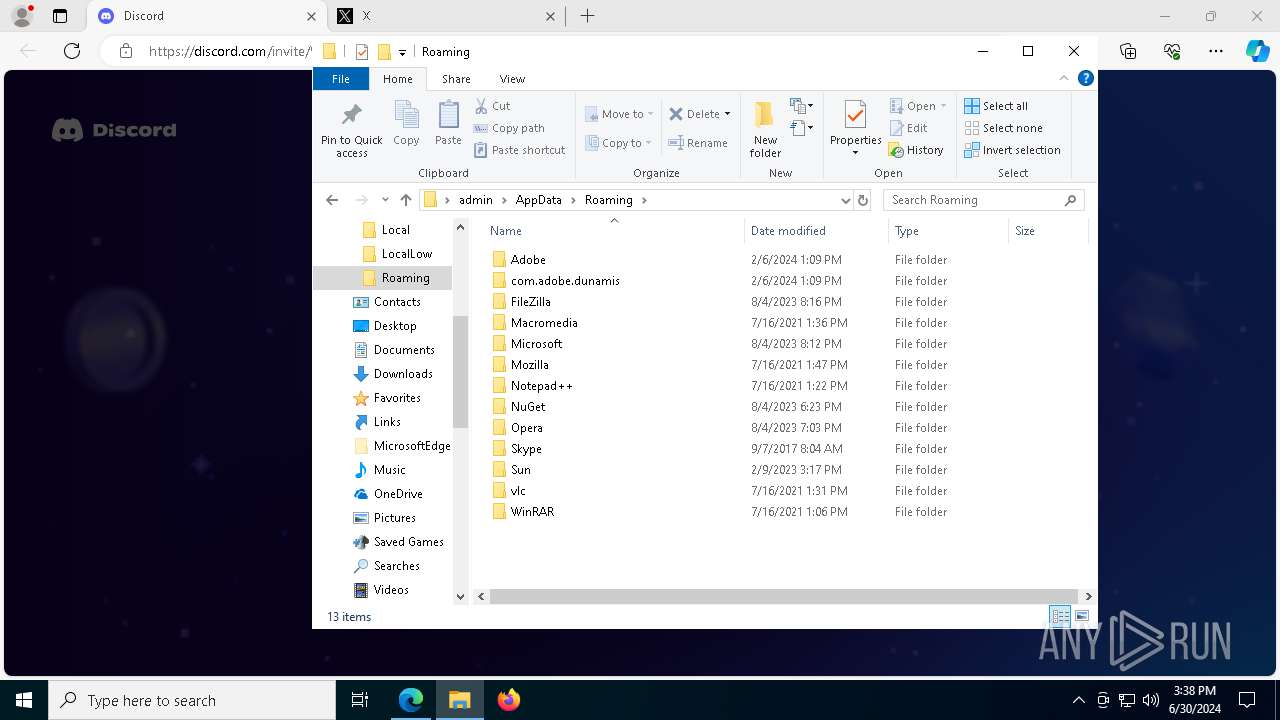
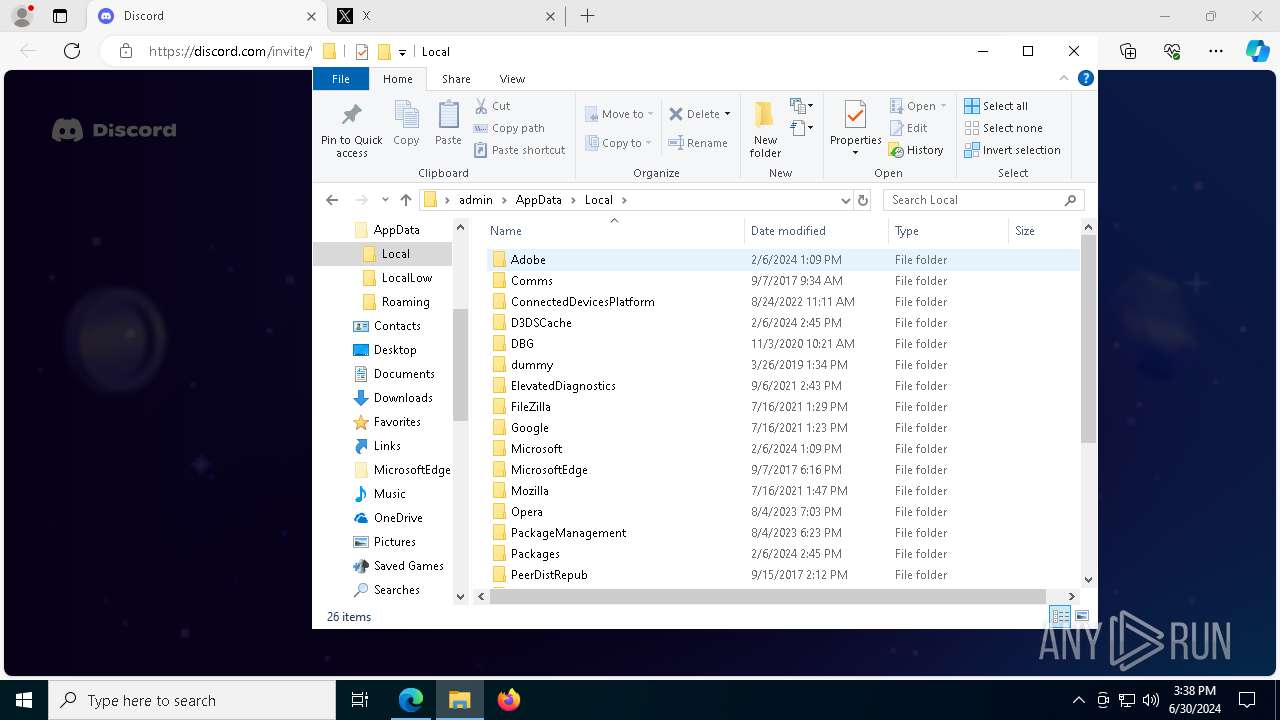
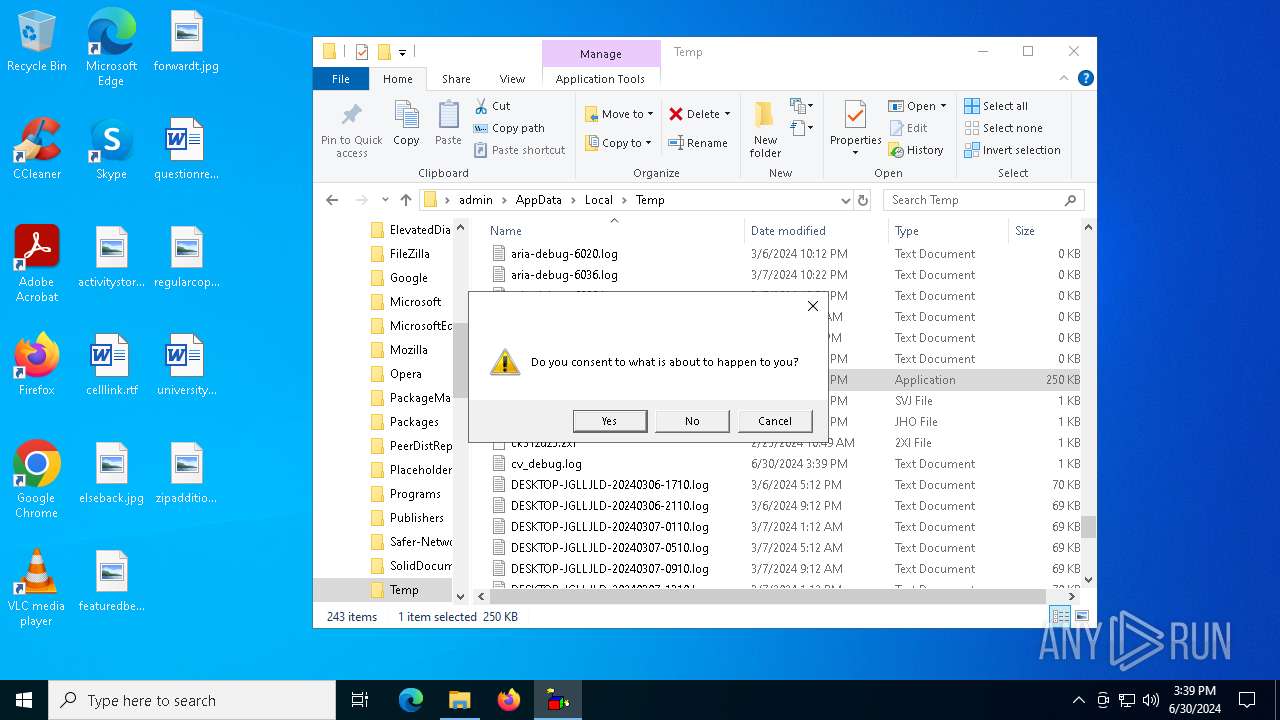
Actions looks like stealing of personal data
- Prankscript.exe (PID: 4172)
SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 1020)
- Prankscript.exe (PID: 5564)
- Prankscript.exe (PID: 900)
The process drops C-runtime libraries
- Prankscript.exe (PID: 5564)
- Prankscript.exe (PID: 900)
Starts a Microsoft application from unusual location
- Prankscript.exe (PID: 5564)
- Prankscript.exe (PID: 4084)
- Prankscript.exe (PID: 4172)
- Prankscript.exe (PID: 900)
Process drops python dynamic module
- Prankscript.exe (PID: 5564)
- Prankscript.exe (PID: 900)
Executable content was dropped or overwritten
- Prankscript.exe (PID: 5564)
- Prankscript.exe (PID: 900)
- Prankscript.exe (PID: 4172)
- csc.exe (PID: 7872)
Application launched itself
- Prankscript.exe (PID: 5564)
- Prankscript.exe (PID: 900)
Loads Python modules
- Prankscript.exe (PID: 4084)
- Prankscript.exe (PID: 4172)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 5956)
- cmd.exe (PID: 936)
- cmd.exe (PID: 1324)
Starts CMD.EXE for commands execution
- Prankscript.exe (PID: 4084)
- Prankscript.exe (PID: 4172)
Changes default file association
- reg.exe (PID: 3880)
Found strings related to reading or modifying Windows Defender settings
- Prankscript.exe (PID: 4084)
- Prankscript.exe (PID: 4172)
Uses WEVTUTIL.EXE to query events from a log or log file
- cmd.exe (PID: 4308)
- cmd.exe (PID: 5896)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6020)
- cmd.exe (PID: 3944)
- cmd.exe (PID: 2968)
- cmd.exe (PID: 6752)
- cmd.exe (PID: 6968)
- cmd.exe (PID: 8004)
- cmd.exe (PID: 7356)
- cmd.exe (PID: 6464)
- cmd.exe (PID: 6968)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 6020)
- cmd.exe (PID: 2968)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 544)
Script disables Windows Defender's real-time protection
- cmd.exe (PID: 3944)
Script disables Windows Defender's IPS
- cmd.exe (PID: 3944)
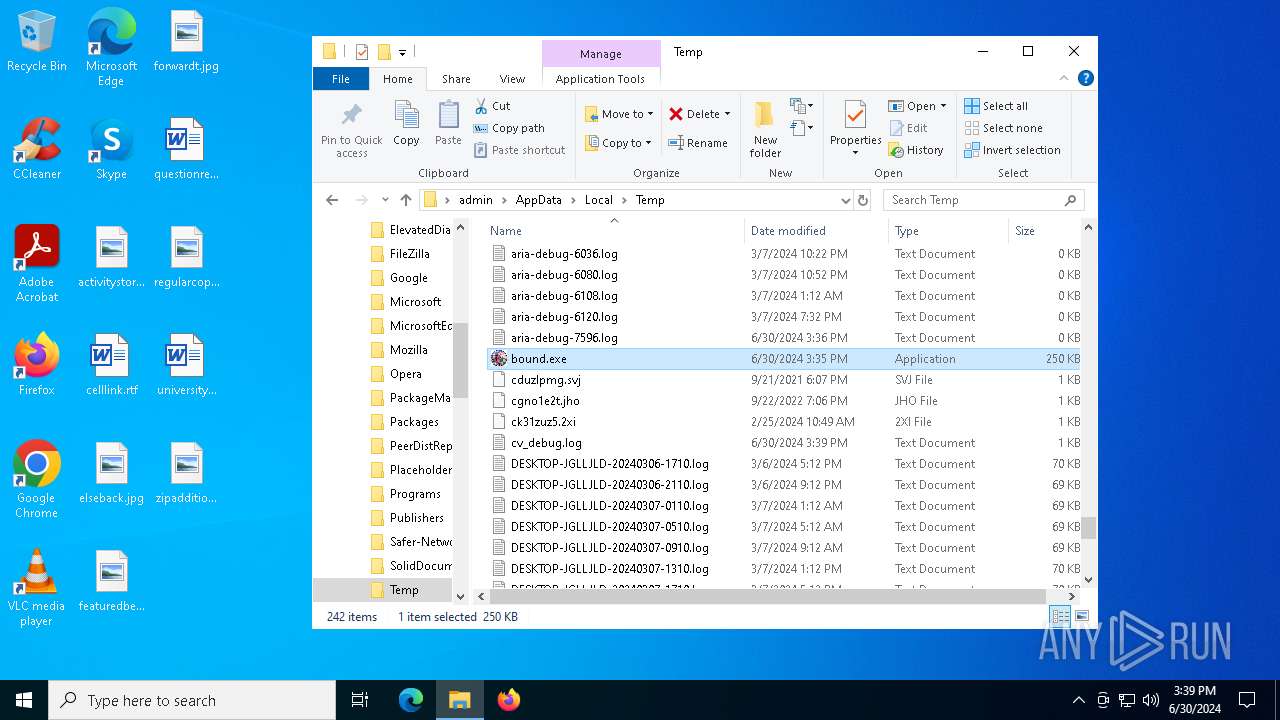
The executable file from the user directory is run by the CMD process
- bound.exe (PID: 6176)
- rar.exe (PID: 6780)
Reads security settings of Internet Explorer
- bound.exe (PID: 6176)
- bound.exe (PID: 5608)
Runs WScript without displaying logo
- wscript.exe (PID: 6388)
- wscript.exe (PID: 8140)
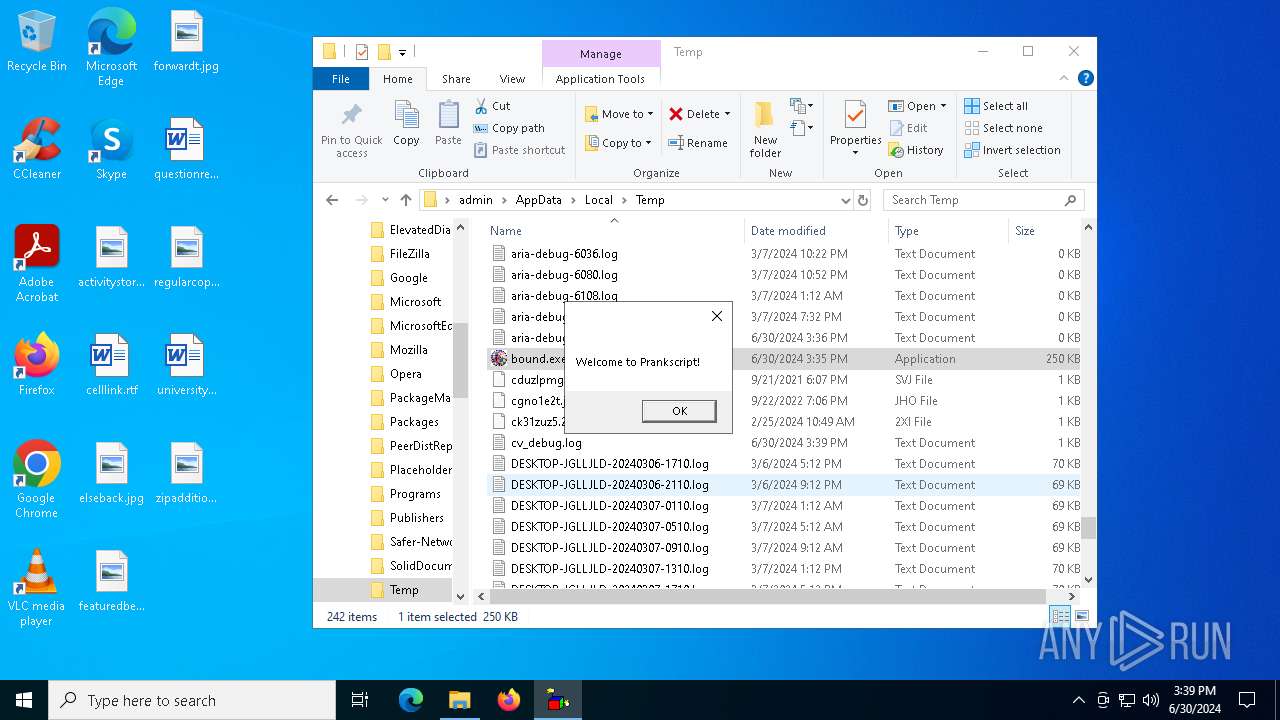
The process executes VB scripts
- bound.exe (PID: 6176)
- bound.exe (PID: 5608)
Get information on the list of running processes
- Prankscript.exe (PID: 4172)
- cmd.exe (PID: 6464)
- cmd.exe (PID: 6760)
- cmd.exe (PID: 6484)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 6720)
- cmd.exe (PID: 6640)
Starts application with an unusual extension
- cmd.exe (PID: 6780)
- cmd.exe (PID: 6800)
- cmd.exe (PID: 7508)
- cmd.exe (PID: 7320)
- cmd.exe (PID: 7644)
- cmd.exe (PID: 7752)
Uses NETSH.EXE to obtain data on the network
- cmd.exe (PID: 6824)
Base64-obfuscated command line is found
- cmd.exe (PID: 6968)
BASE64 encoded PowerShell command has been detected
- cmd.exe (PID: 6968)
Reads the date of Windows installation
- bound.exe (PID: 6176)
- bound.exe (PID: 5608)
Accesses antivirus product name via WMI (SCRIPT)
- WMIC.exe (PID: 6184)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 6968)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 7656)
Accesses operating system name via WMI (SCRIPT)
- WMIC.exe (PID: 6752)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 7148)
Accesses product unique identifier via WMI (SCRIPT)
- WMIC.exe (PID: 6680)
Uses WMIC.EXE to obtain a list of video controllers
- cmd.exe (PID: 8120)
Hides command output
- cmd.exe (PID: 2204)
Accesses video controller name via WMI (SCRIPT)
- WMIC.exe (PID: 7448)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 2204)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- Prankscript.exe (PID: 4172)
Checks for external IP
- Prankscript.exe (PID: 4172)
Runs shell command (SCRIPT)
- wscript.exe (PID: 6388)
- wscript.exe (PID: 8140)
INFO
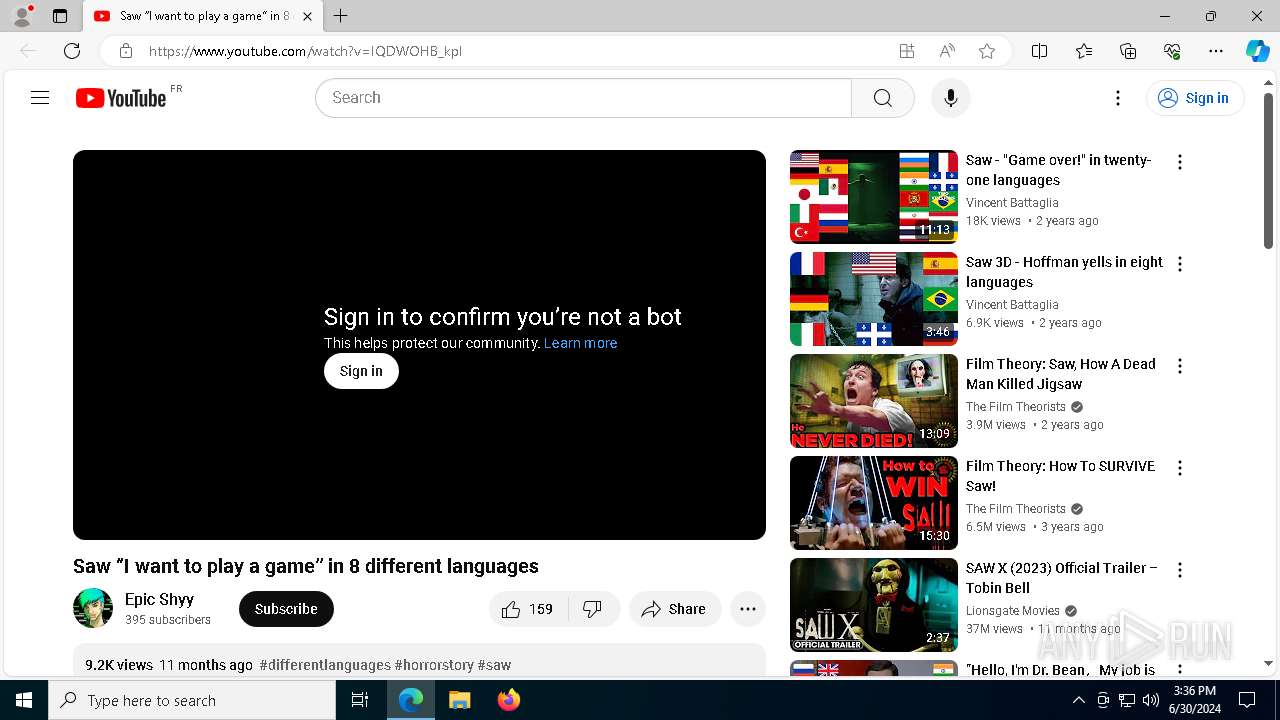
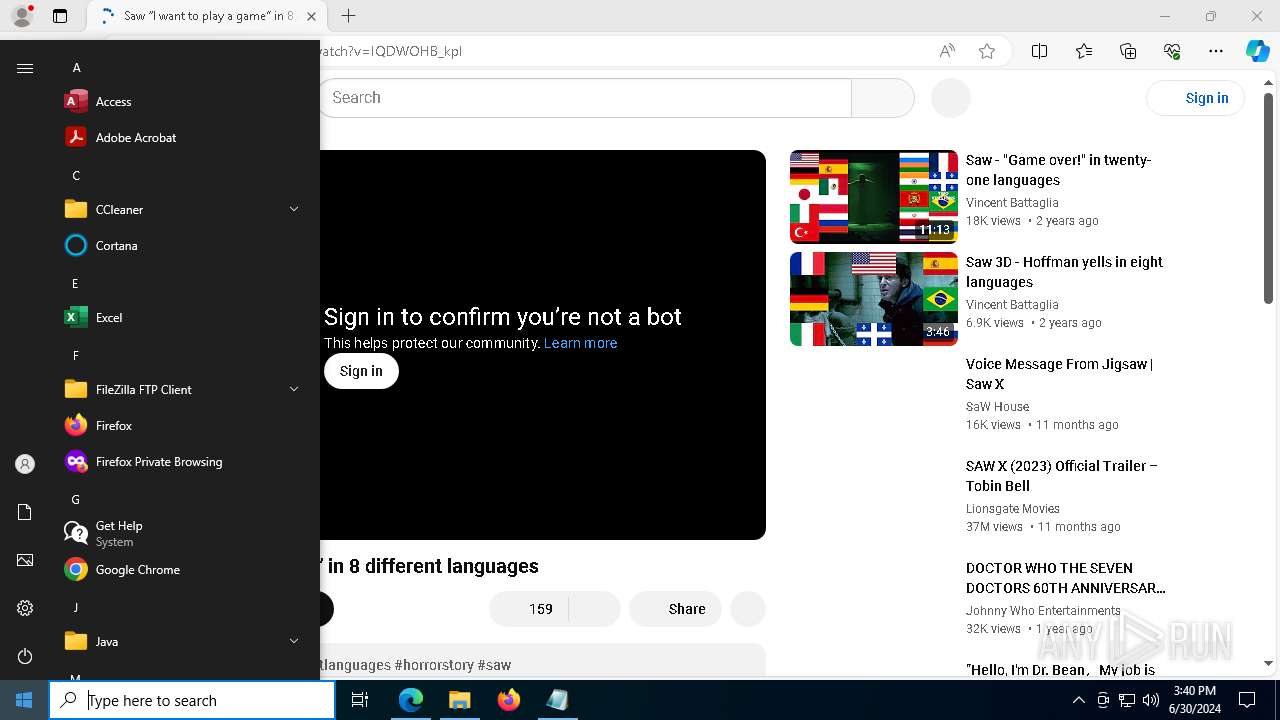
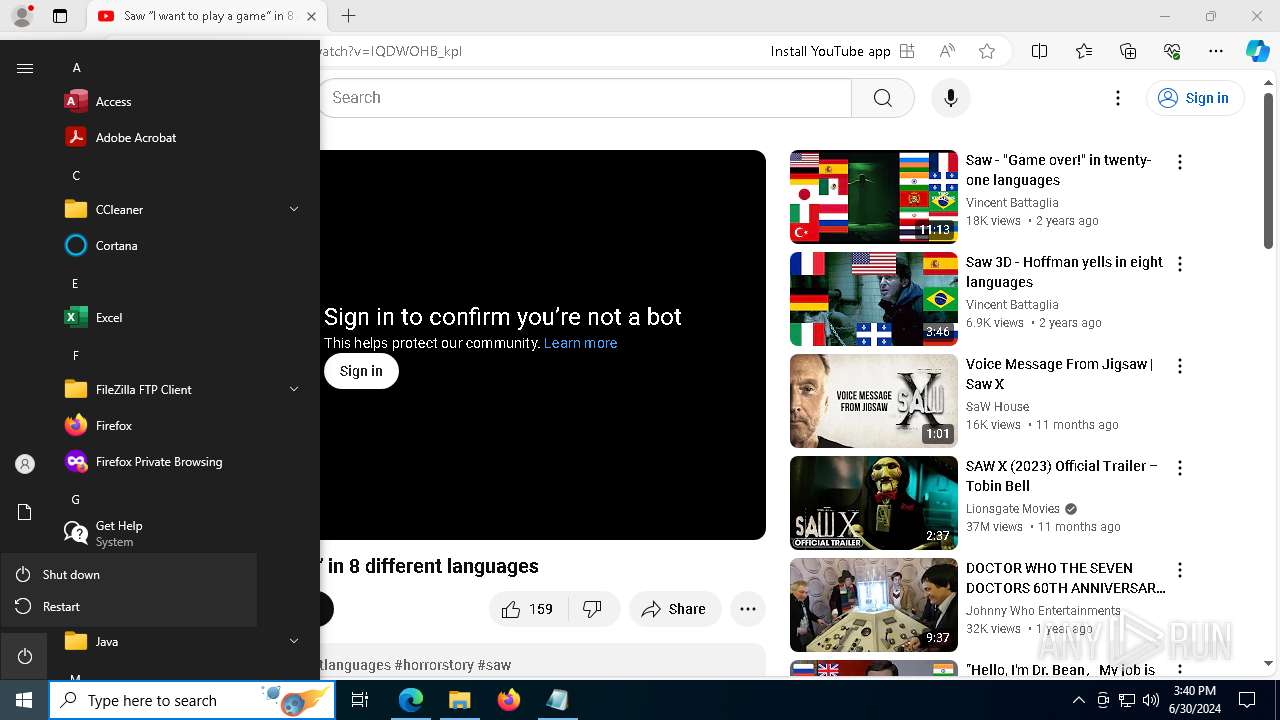
Manual execution by a user
- Prankscript.exe (PID: 5564)
- msedge.exe (PID: 8040)
- bound.exe (PID: 5608)
- bound.exe (PID: 6524)
Reads the computer name
- Prankscript.exe (PID: 5564)
- Prankscript.exe (PID: 900)
- Prankscript.exe (PID: 4172)
- bound.exe (PID: 6176)
- MpCmdRun.exe (PID: 7156)
- identity_helper.exe (PID: 7320)
- identity_helper.exe (PID: 6988)
- identity_helper.exe (PID: 6248)
- bound.exe (PID: 5608)
- TextInputHost.exe (PID: 4208)
Checks supported languages
- Prankscript.exe (PID: 5564)
- Prankscript.exe (PID: 4084)
- Prankscript.exe (PID: 900)
- Prankscript.exe (PID: 4172)
- bound.exe (PID: 6176)
- tree.com (PID: 7132)
- tree.com (PID: 7208)
- tree.com (PID: 7580)
- tree.com (PID: 7464)
- tree.com (PID: 7724)
- tree.com (PID: 7812)
- MpCmdRun.exe (PID: 7156)
- cvtres.exe (PID: 8156)
- csc.exe (PID: 7872)
- rar.exe (PID: 6780)
- identity_helper.exe (PID: 6988)
- identity_helper.exe (PID: 7320)
- TextInputHost.exe (PID: 4208)
- identity_helper.exe (PID: 6248)
- bound.exe (PID: 5608)
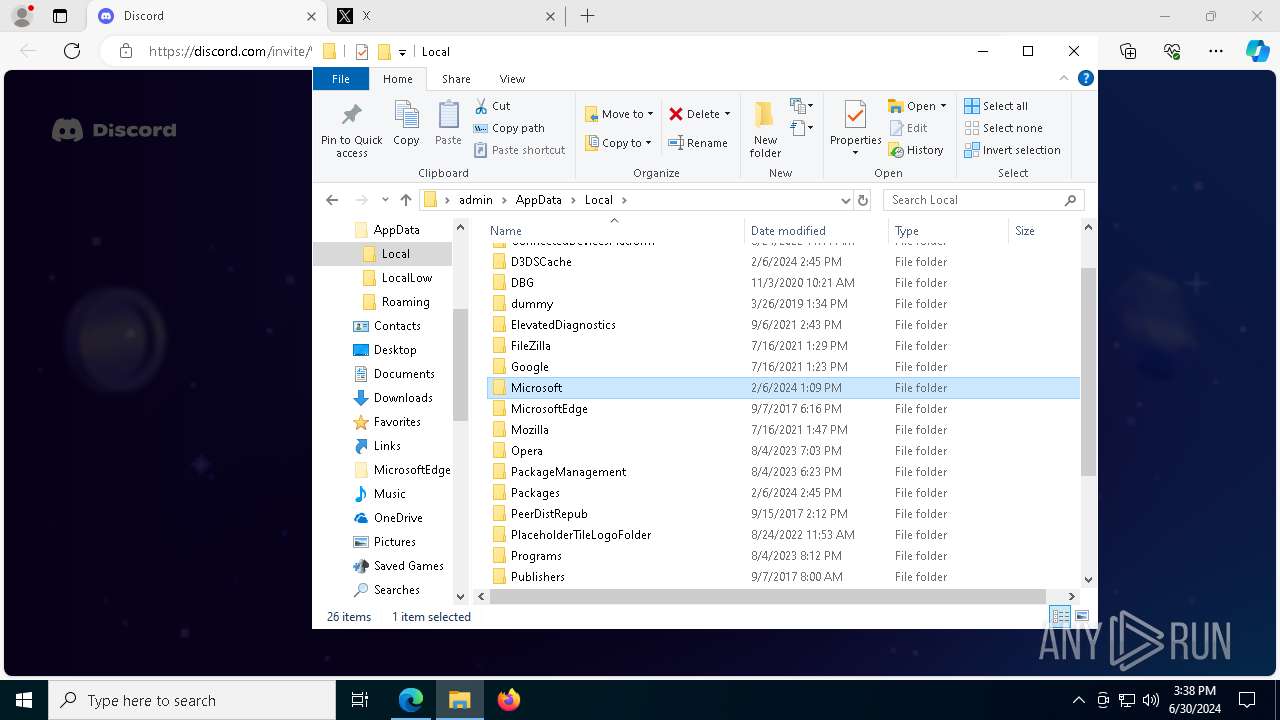
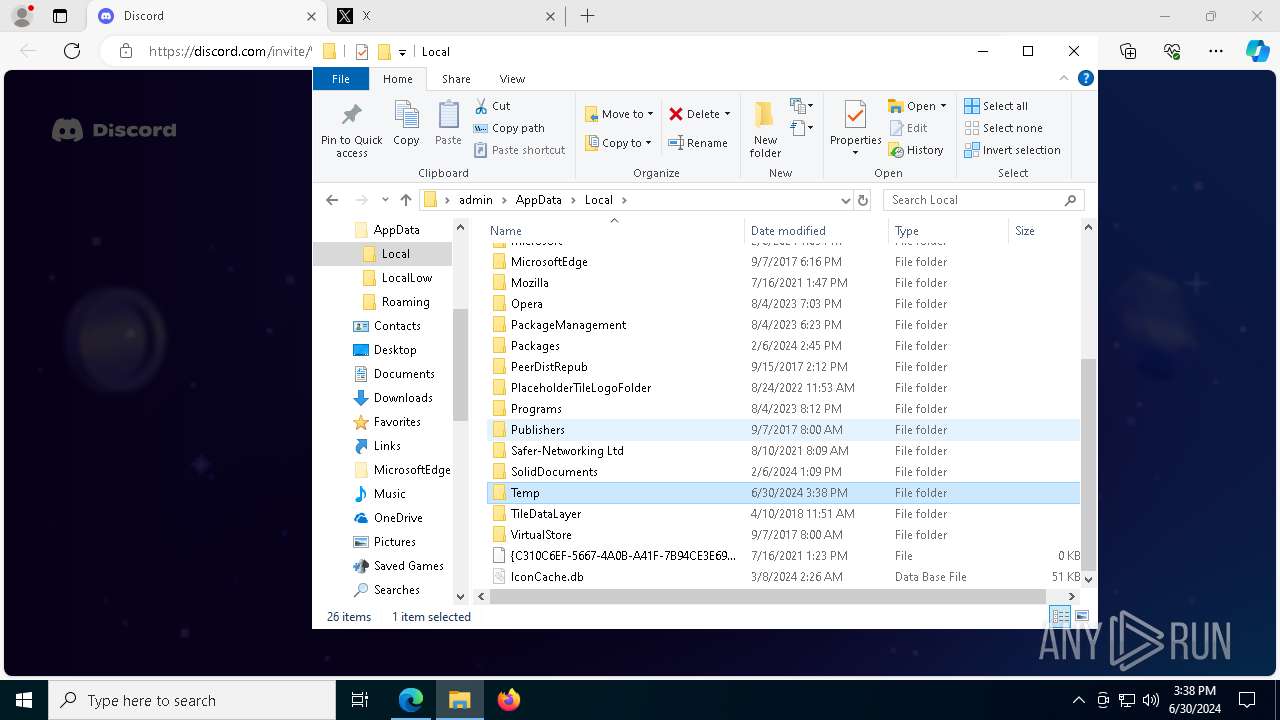
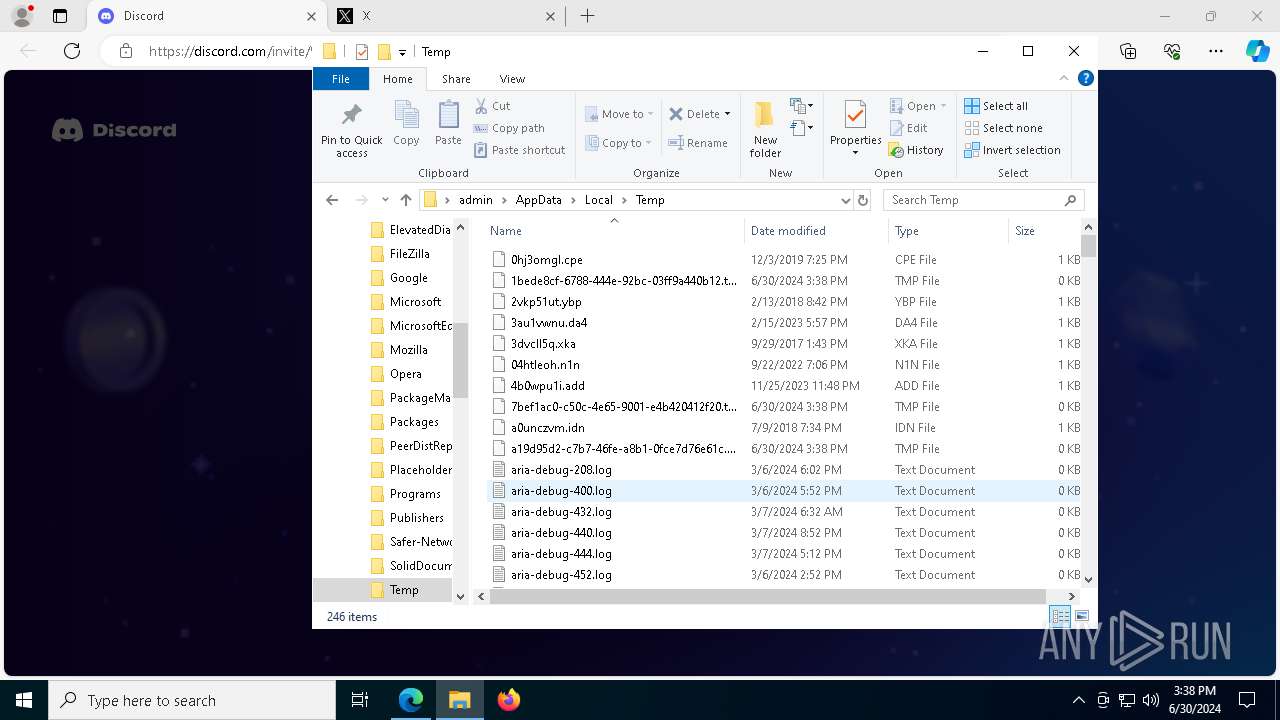
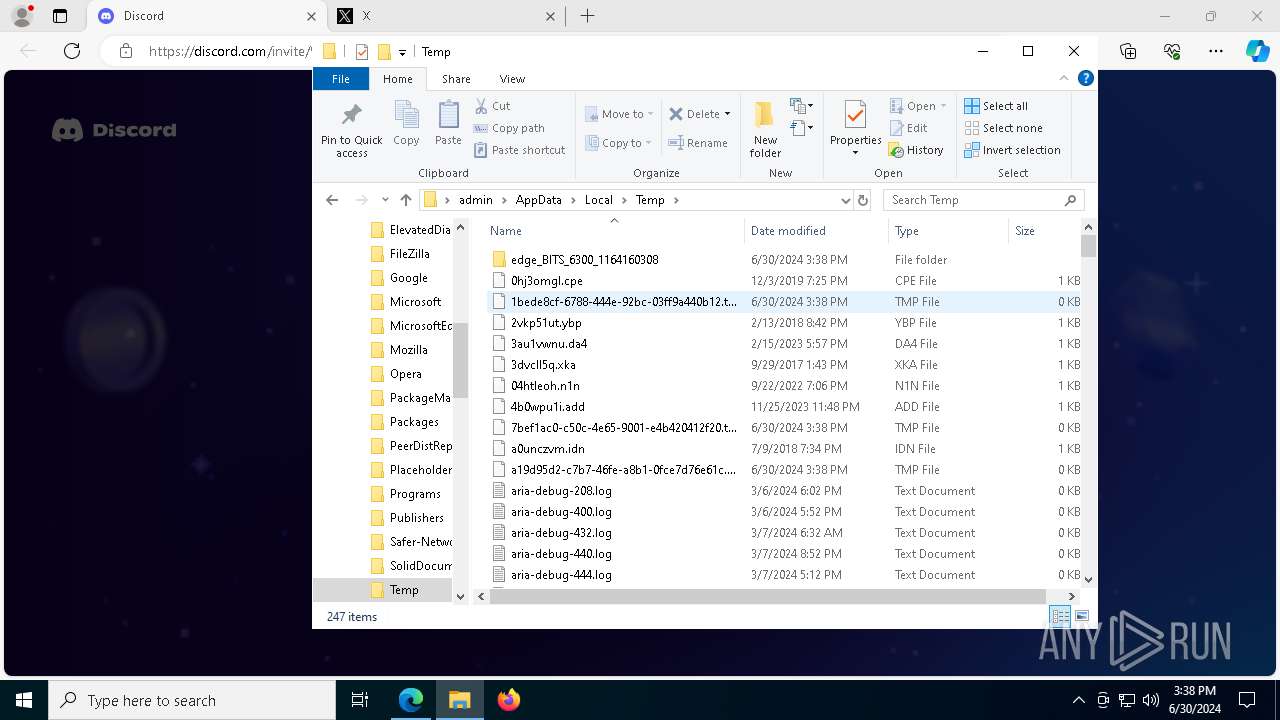
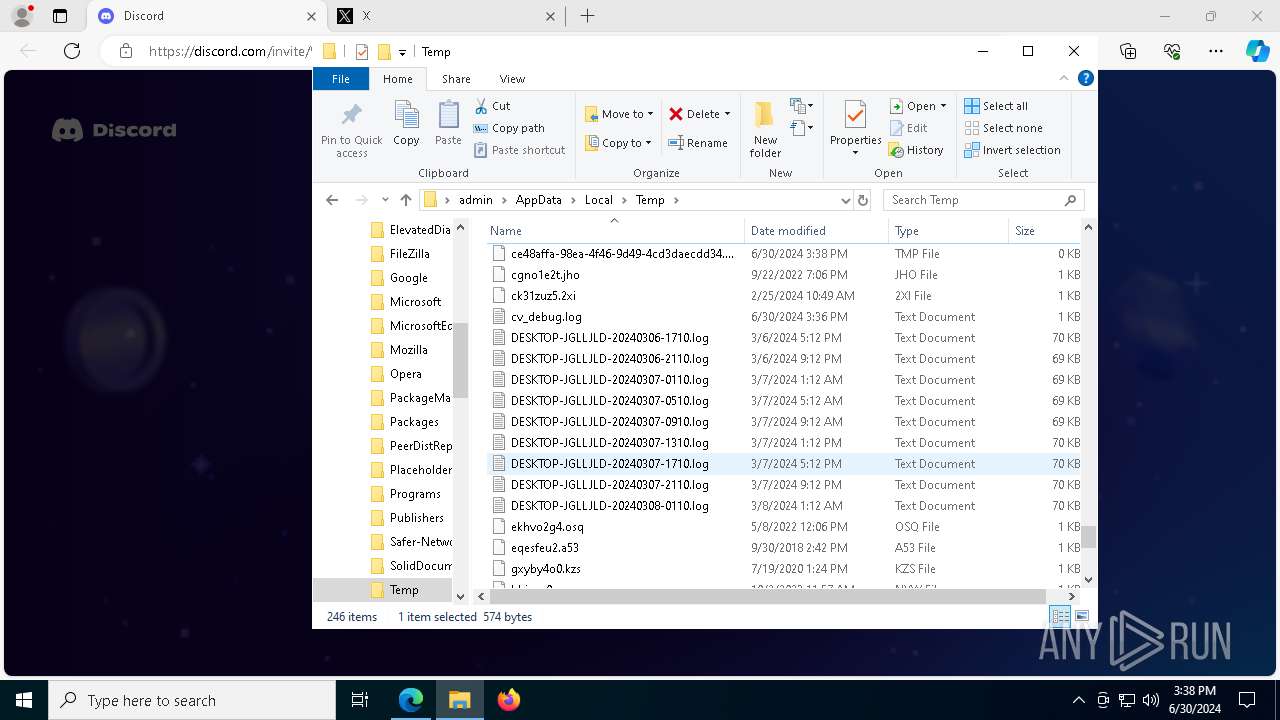
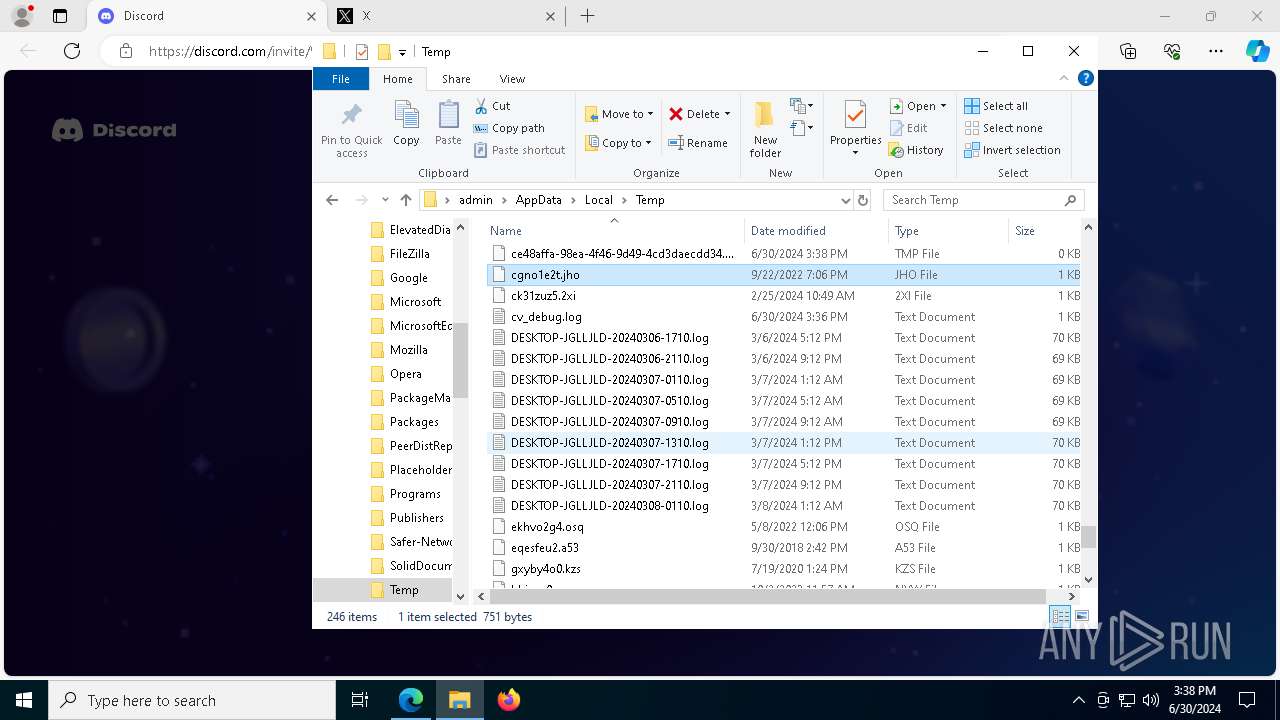
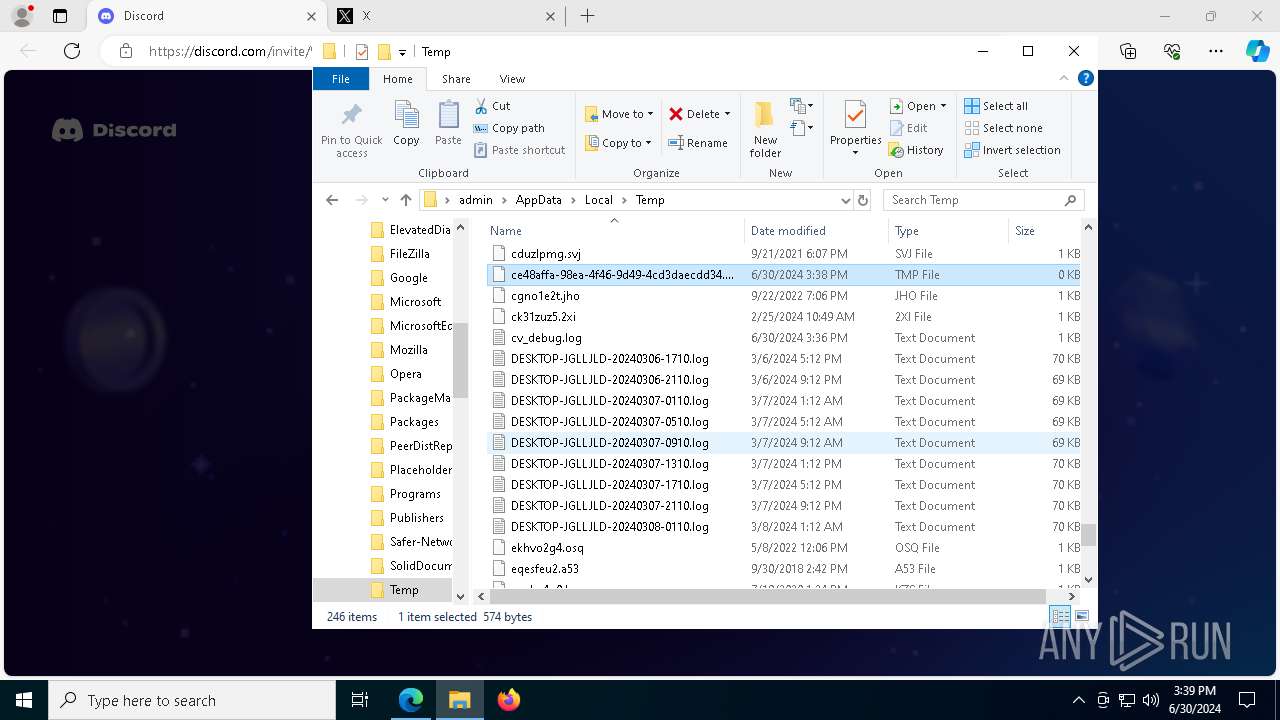
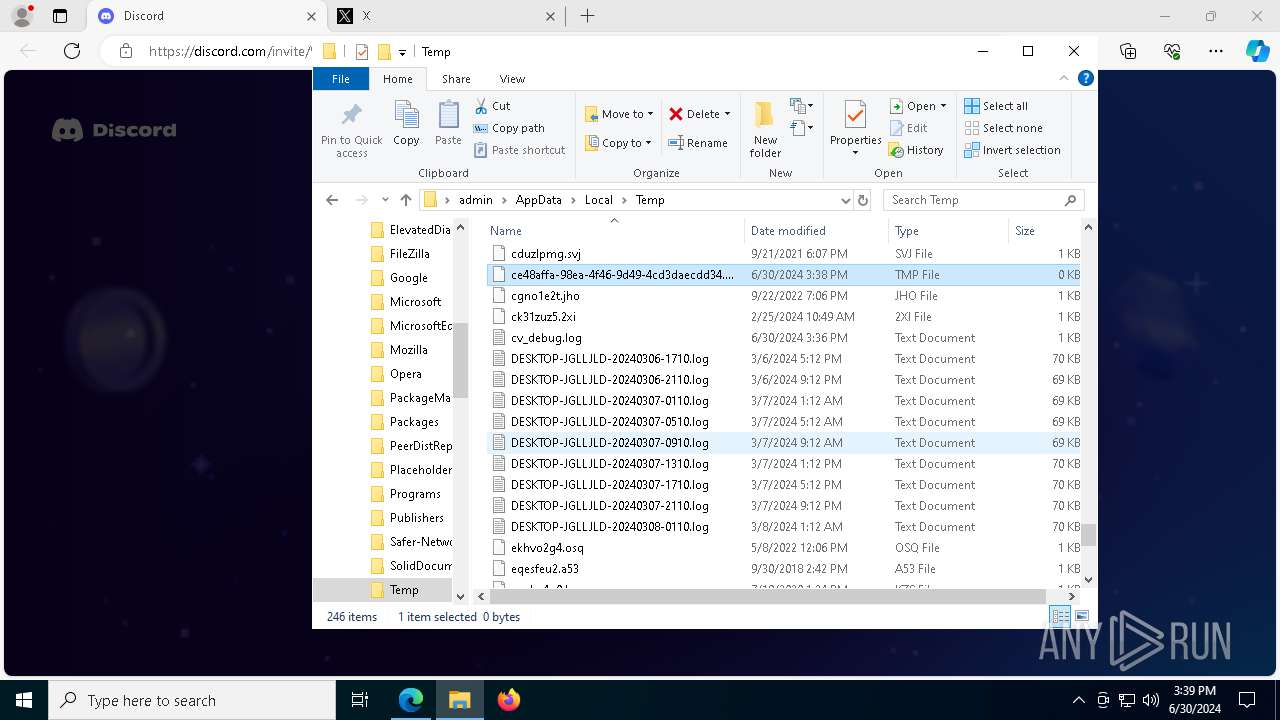
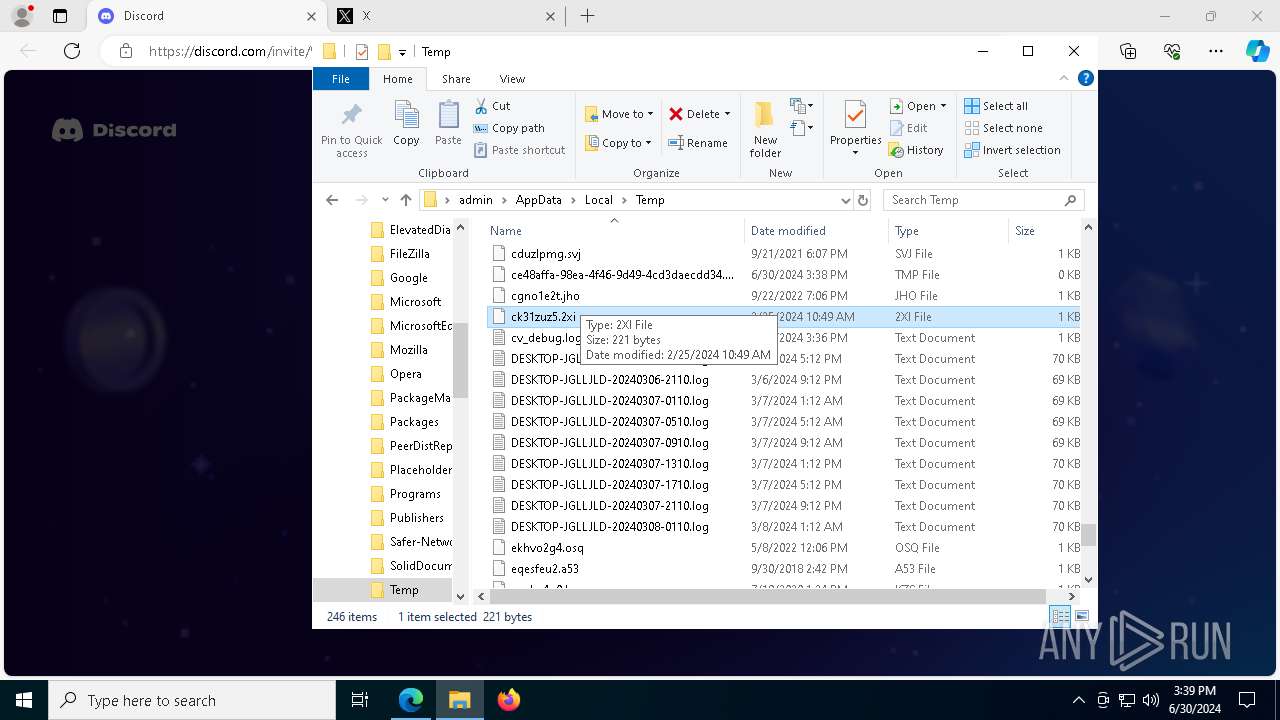
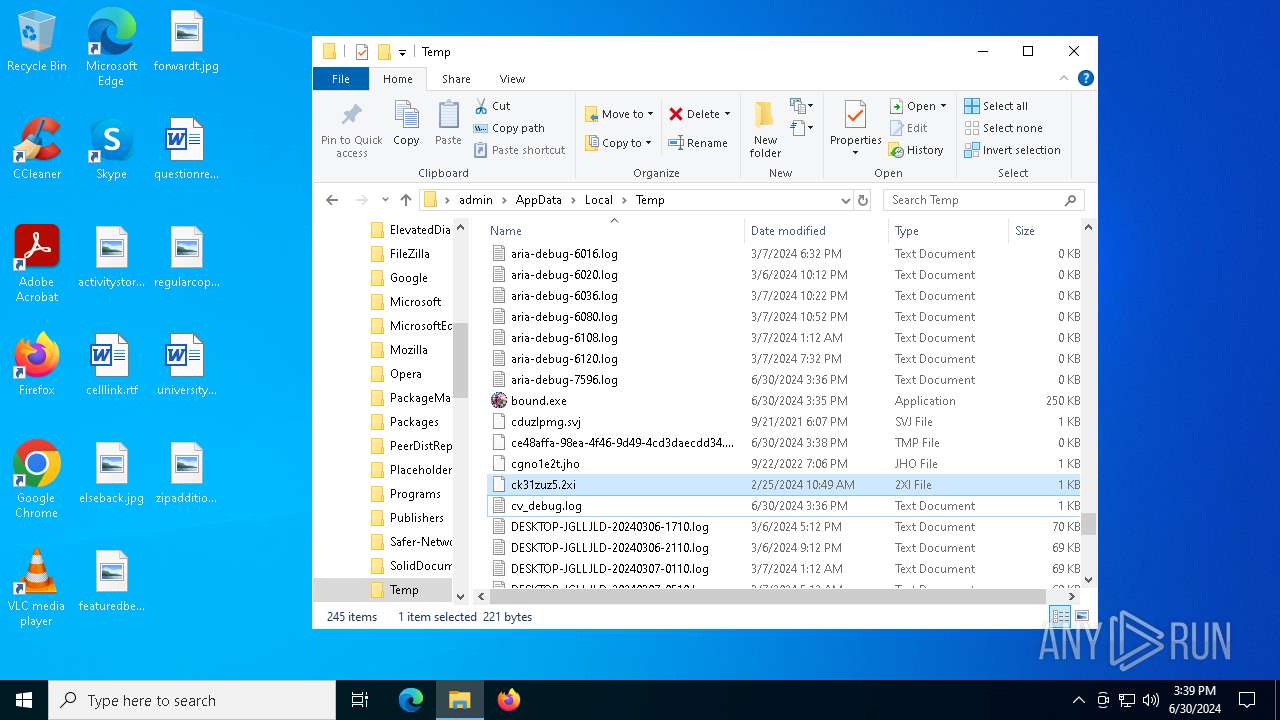
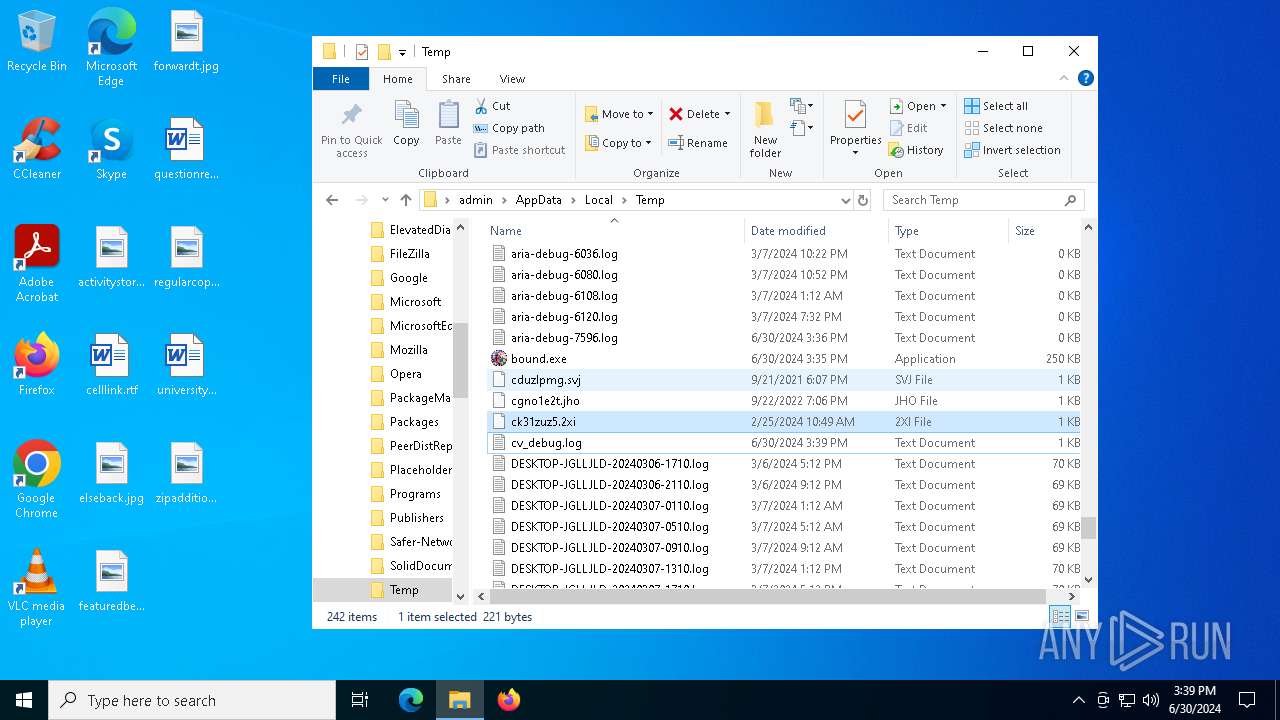
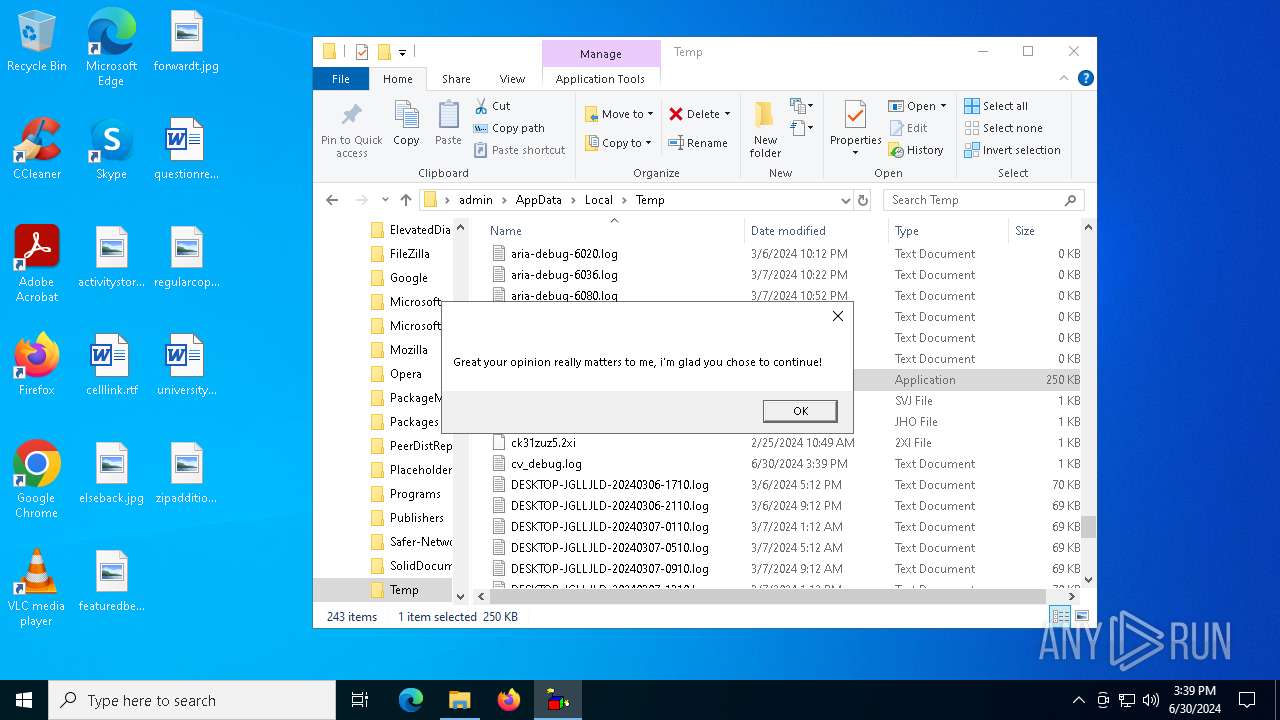
Create files in a temporary directory
- Prankscript.exe (PID: 5564)
- Prankscript.exe (PID: 4084)
- Prankscript.exe (PID: 900)
- Prankscript.exe (PID: 4172)
- bound.exe (PID: 6176)
- csc.exe (PID: 7872)
- cvtres.exe (PID: 8156)
- MpCmdRun.exe (PID: 7156)
- rar.exe (PID: 6780)
- bound.exe (PID: 5608)
Reads Microsoft Office registry keys
- ComputerDefaults.exe (PID: 32)
- msedge.exe (PID: 6952)
- msedge.exe (PID: 8040)
- msedge.exe (PID: 6300)
- msedge.exe (PID: 7776)
Reads security settings of Internet Explorer
- ComputerDefaults.exe (PID: 32)
- WMIC.exe (PID: 6184)
- WMIC.exe (PID: 6752)
- WMIC.exe (PID: 6680)
- WMIC.exe (PID: 7932)
- WMIC.exe (PID: 7448)
The Powershell gets current clipboard
- powershell.exe (PID: 3880)
Process checks computer location settings
- bound.exe (PID: 6176)
- bound.exe (PID: 5608)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6160)
- powershell.exe (PID: 8064)
- powershell.exe (PID: 936)
- powershell.exe (PID: 6168)
- powershell.exe (PID: 7556)
Reads the machine GUID from the registry
- csc.exe (PID: 7872)
- rar.exe (PID: 6780)
Application launched itself
- msedge.exe (PID: 6952)
- msedge.exe (PID: 8040)
- msedge.exe (PID: 7776)
- msedge.exe (PID: 6300)
Drops the executable file immediately after the start
- msedge.exe (PID: 7764)
- msedge.exe (PID: 7776)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
Total processes
395
Monitored processes
248
Malicious processes
12
Suspicious processes
5
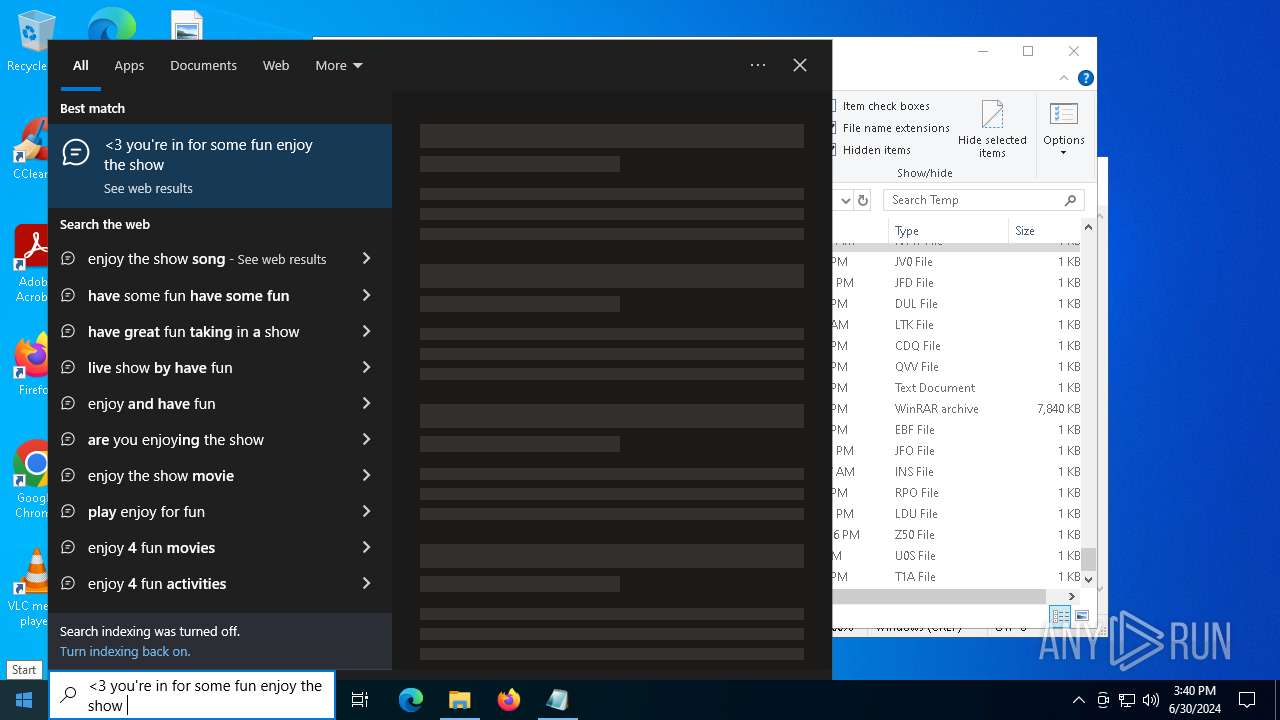
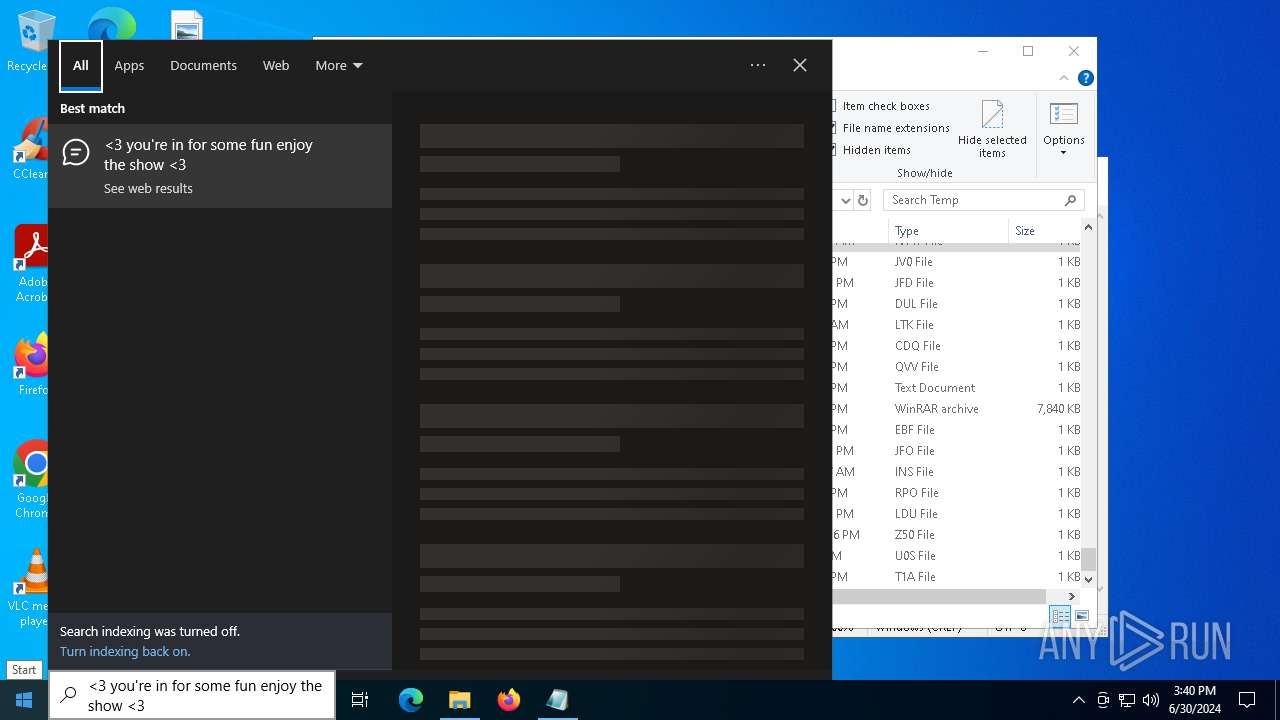
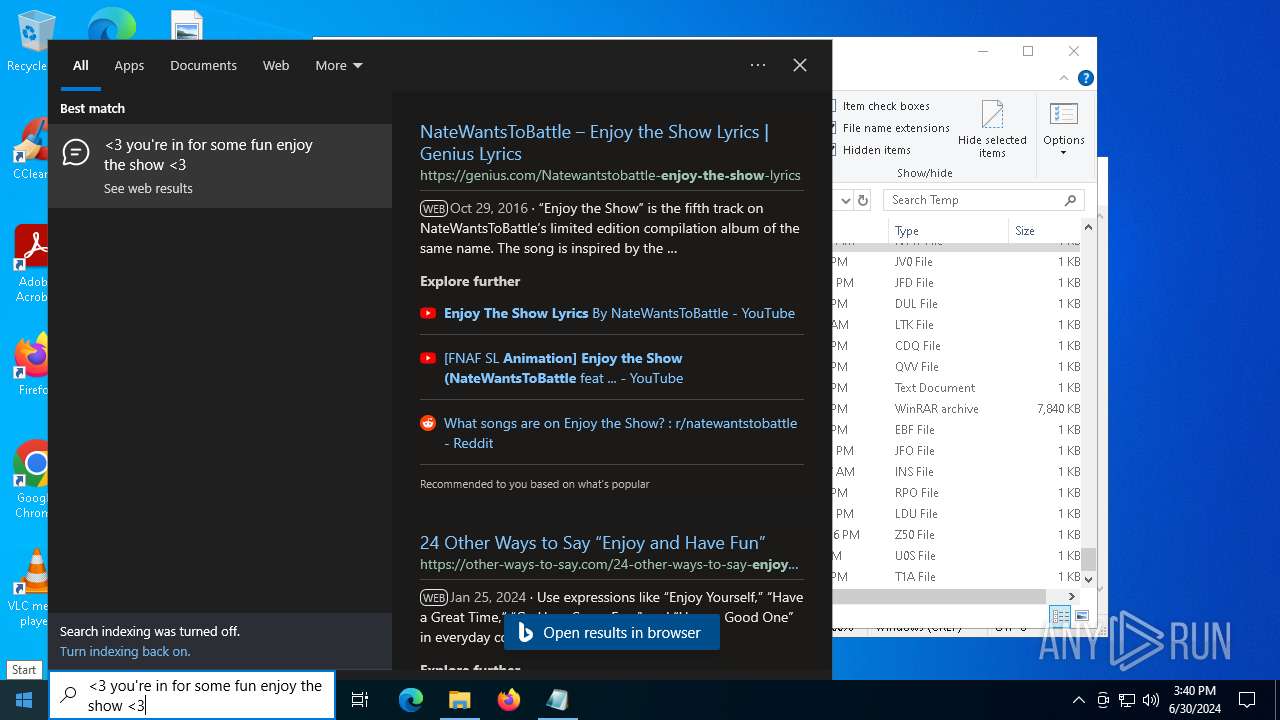
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 32 | "C:\WINDOWS\system32\ComputerDefaults.exe" --nouacbypass | C:\Windows\System32\ComputerDefaults.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Set Program Access and Computer Defaults Control Panel Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 428 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4524 --field-trial-handle=2332,i,14098597635881125232,6560097447798049173,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 544 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 544 | C:\WINDOWS\system32\cmd.exe /c "attrib +h +s "C:\Users\admin\Desktop\Prankscript.exe"" | C:\Windows\System32\cmd.exe | — | Prankscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 544 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2416 --field-trial-handle=2420,i,4793110337285793994,16825750063769279662,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 732 | C:\WINDOWS\system32\cmd.exe /c "computerdefaults --nouacbypass" | C:\Windows\System32\cmd.exe | — | Prankscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 900 | "C:\Users\admin\Desktop\Prankscript.exe" | C:\Users\admin\Desktop\Prankscript.exe | ComputerDefaults.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: ClearType Tuner Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 936 | C:\WINDOWS\system32\cmd.exe /c "reg add hkcu\Software\Classes\ms-settings\shell\open\command /v "DelegateExecute" /f" | C:\Windows\System32\cmd.exe | — | Prankscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 936 | powershell -Command Add-MpPreference -ExclusionPath 'C:\Users\admin\Desktop\Prankscript.exe' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
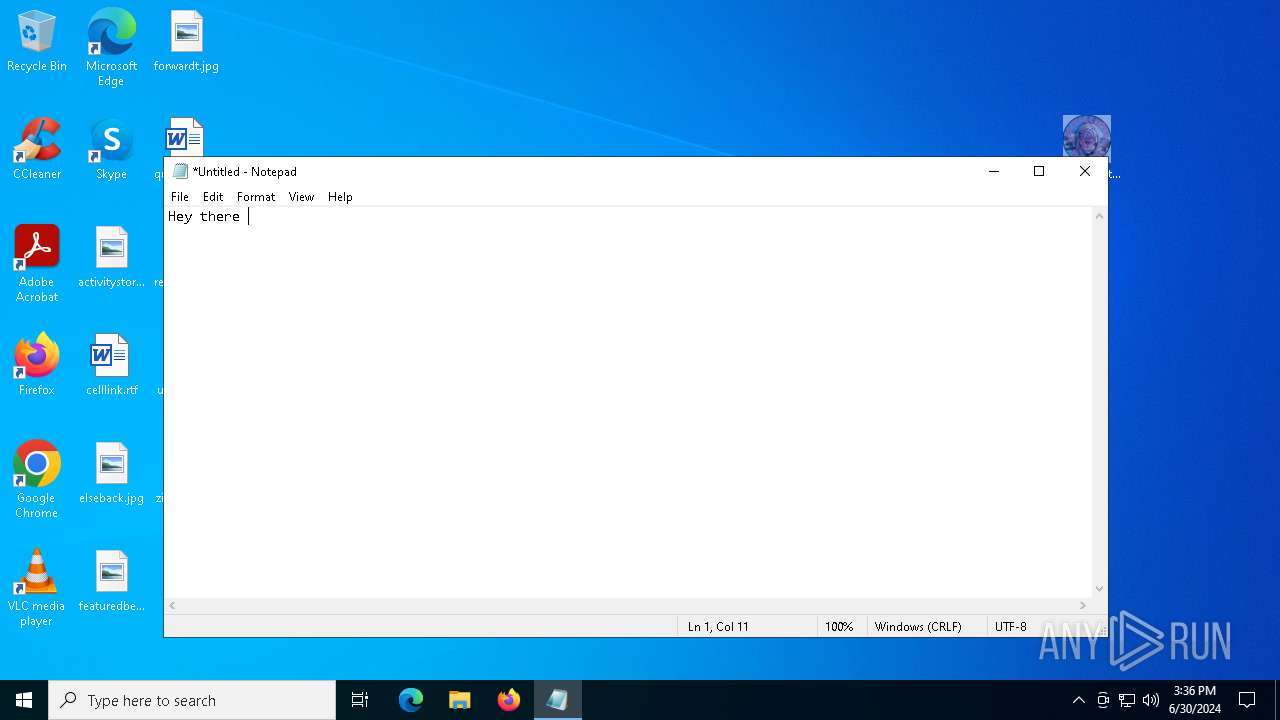
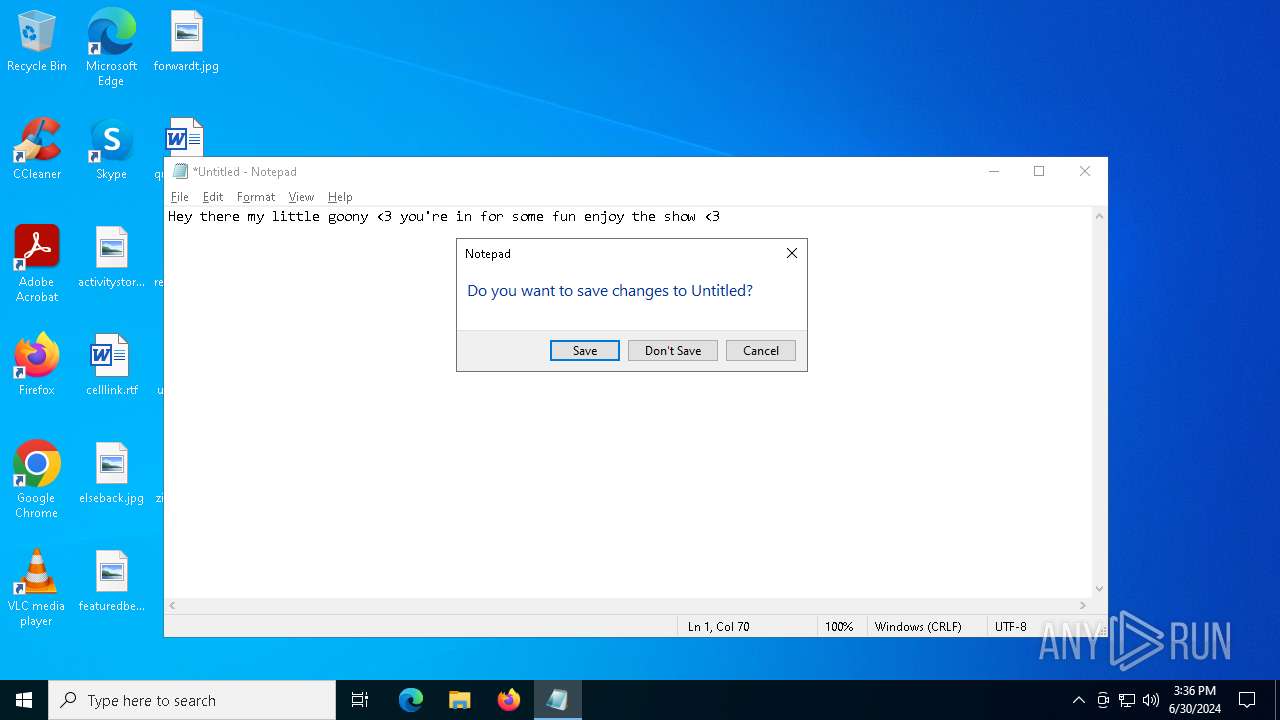
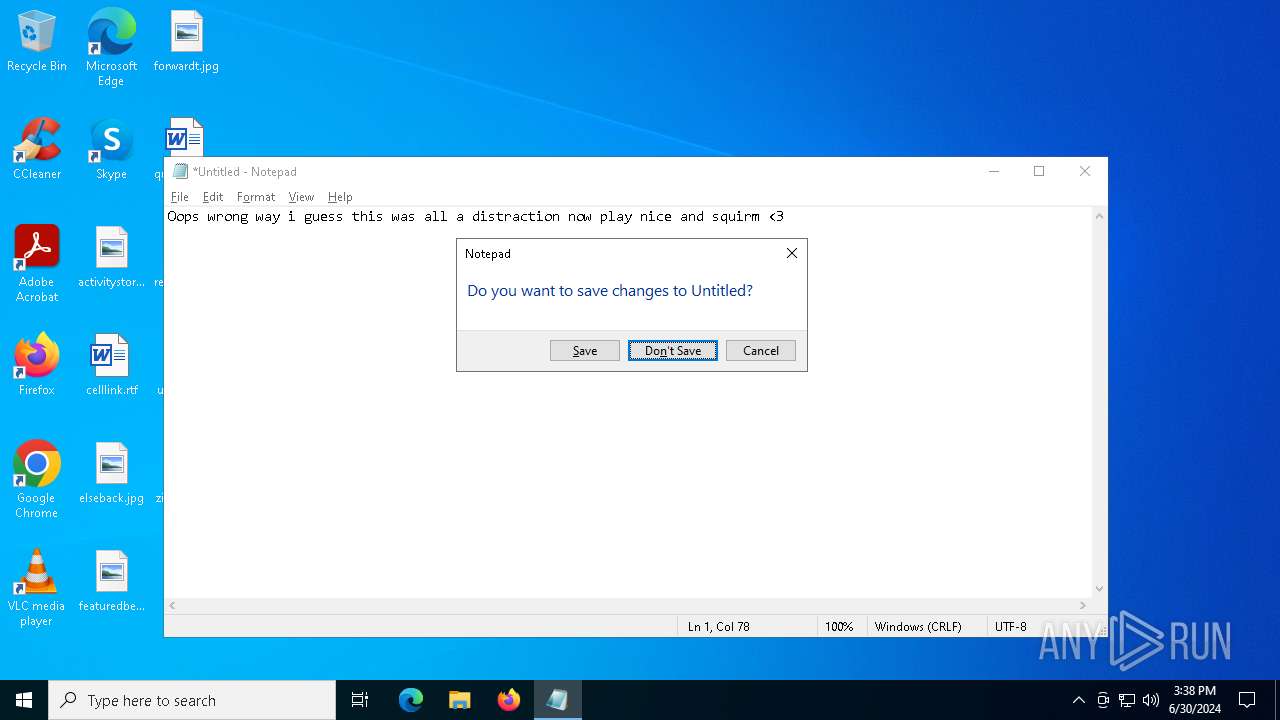
| 936 | "C:\Windows\System32\notepad.exe" | C:\Windows\System32\notepad.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
109 818
Read events
109 336
Write events
473
Delete events
9
Modification events
| (PID) Process: | (1020) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1020) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1020) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (1020) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Prankscript.7z | |||
| (PID) Process: | (1020) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1020) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1020) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1020) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1020) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (1020) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\AppData\Local\Temp | |||
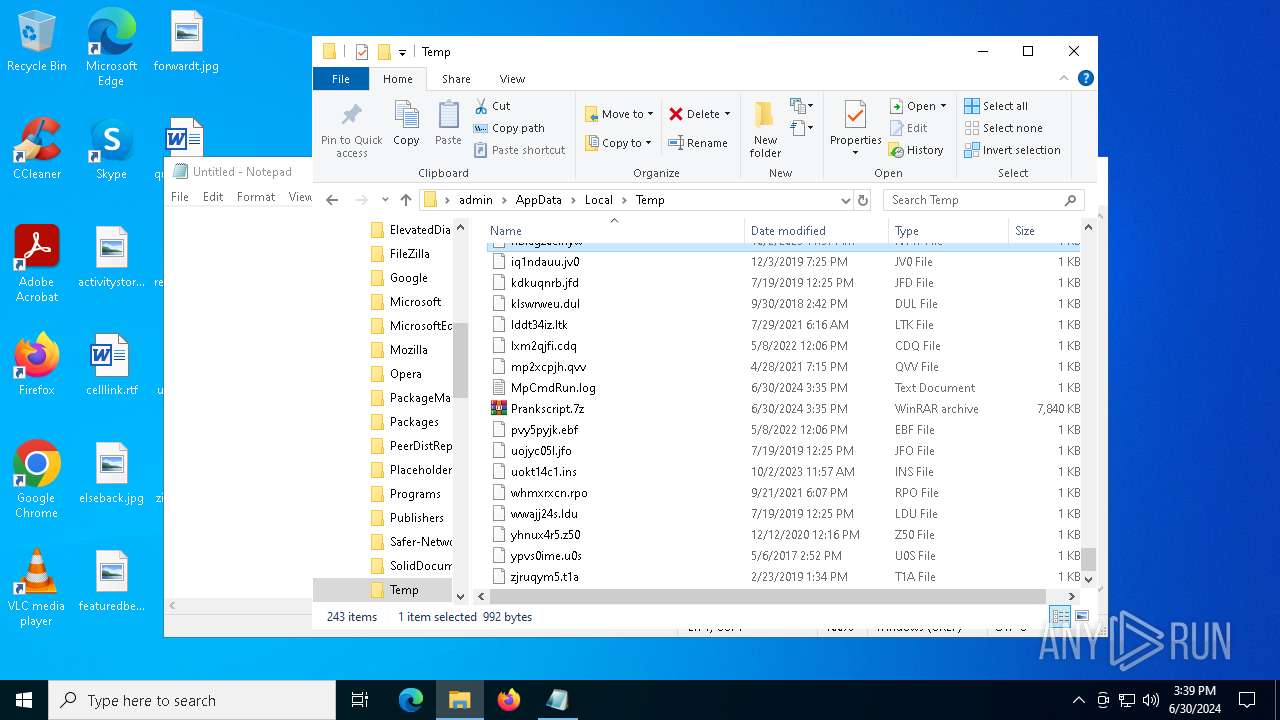
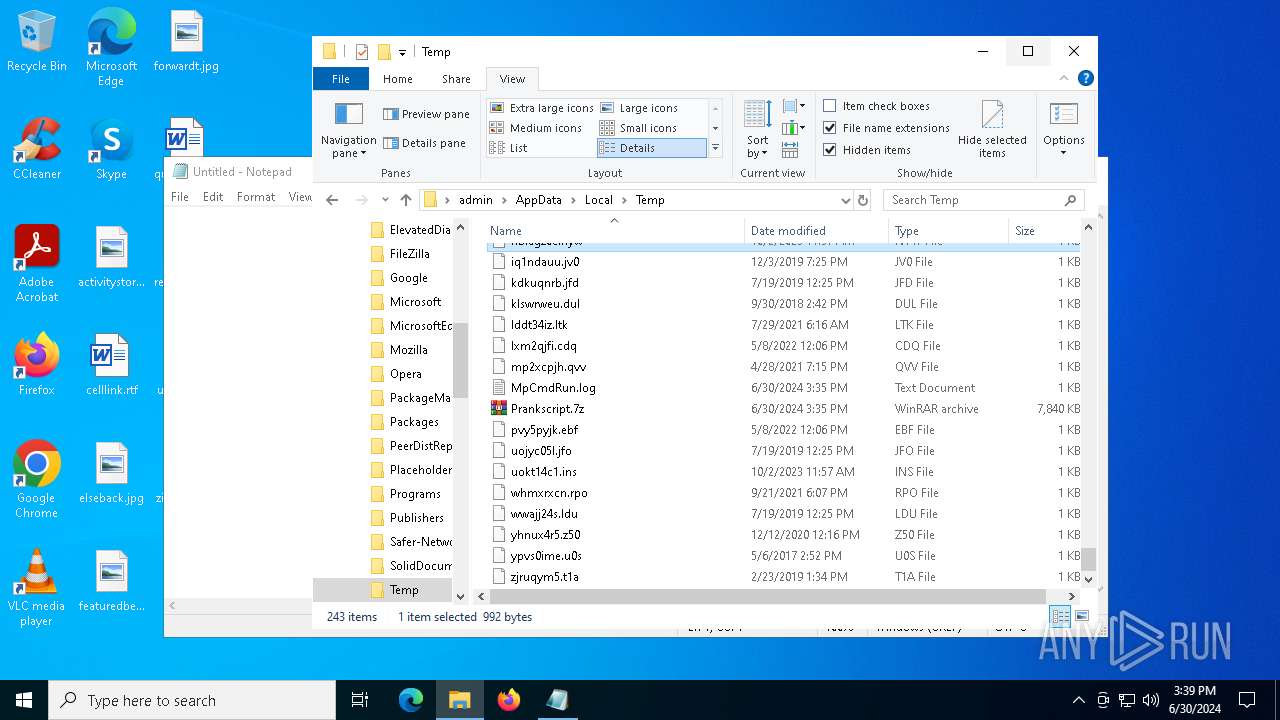
Executable files
46
Suspicious files
899
Text files
275
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1020 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1020.5404\Prankscript.exe | — | |
MD5:— | SHA256:— | |||
| 5564 | Prankscript.exe | C:\Users\admin\AppData\Local\Temp\_MEI55642\_queue.pyd | executable | |
MD5:048E8E18D1AE823E666C501C8A8AD1DD | SHA256:7285EEF53FD485D6093A9AECBE8FC87C6D70AE4E91D41F382A2A3EDFF7EBC6C8 | |||
| 5564 | Prankscript.exe | C:\Users\admin\AppData\Local\Temp\_MEI55642\_bz2.pyd | executable | |
MD5:BA8871F10F67817358FE84F44B986801 | SHA256:9D30387EE07585516F8CE479FCD4E052597835D4149568C1D8382A4A3A0AE7E1 | |||
| 5564 | Prankscript.exe | C:\Users\admin\AppData\Local\Temp\_MEI55642\_sqlite3.pyd | executable | |
MD5:B8AA2DE7DF9BA5EAB6609DCF07829AA6 | SHA256:644669D0875B33AA7E9D3F1856BC8B696F796AD61C7EDB9219F8F0FF1A69531A | |||
| 5564 | Prankscript.exe | C:\Users\admin\AppData\Local\Temp\_MEI55642\_lzma.pyd | executable | |
MD5:ED348285C1AD1DB0EFFD915C0CB087C3 | SHA256:FA84770CCF4394D046ED69EDAEA71957306A25DEF4986EE6650DAF0A2C2D3E43 | |||
| 5564 | Prankscript.exe | C:\Users\admin\AppData\Local\Temp\_MEI55642\VCRUNTIME140.dll | executable | |
MD5:BE8DBE2DC77EBE7F88F910C61AEC691A | SHA256:4D292623516F65C80482081E62D5DADB759DC16E851DE5DB24C3CBB57B87DB83 | |||
| 5564 | Prankscript.exe | C:\Users\admin\AppData\Local\Temp\_MEI55642\_decimal.pyd | executable | |
MD5:94FBB133E2B93EA55205ECBD83FCAE39 | SHA256:F8E8FBEEE7C8454FA42FE47F1DA9C63F6B6E631B0DFF22C80631F426EFCBA78B | |||
| 5564 | Prankscript.exe | C:\Users\admin\AppData\Local\Temp\_MEI55642\_hashlib.pyd | executable | |
MD5:3C1056EDEF1C509136160D69D94C4B28 | SHA256:41E4BB3C6064CB9E8A62E17056AEA19E3D7E6FF1EFC17C18D76118AC4E3B7243 | |||
| 5564 | Prankscript.exe | C:\Users\admin\AppData\Local\Temp\_MEI55642\_ssl.pyd | executable | |
MD5:A9F1BDA7447AB9D69DF7391D10290240 | SHA256:2BB05F7DBD21E67D2A6671411F8AE503DD7538A6767B2169B3033B695557AC13 | |||
| 5564 | Prankscript.exe | C:\Users\admin\AppData\Local\Temp\_MEI55642\libffi-8.dll | executable | |
MD5:08B000C3D990BC018FCB91A1E175E06E | SHA256:135C772B42BA6353757A4D076CE03DBF792456143B42D25A62066DA46144FECE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
39
TCP/UDP connections
217
DNS requests
214
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6760 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bc852310-4978-4192-9f38-f8fcfefc7b93?P1=1720052324&P2=404&P3=2&P4=X0tc7qBa9Ayq4Rg8sKL4DzqOiKGfYLvTO3Ye5pWfCXK8PptVSVEI8BTzBDnA%2fo8af45WAYhHzHDWSfw3Y6Uriw%3d%3d | unknown | — | — | unknown |
6760 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bc852310-4978-4192-9f38-f8fcfefc7b93?P1=1720052324&P2=404&P3=2&P4=X0tc7qBa9Ayq4Rg8sKL4DzqOiKGfYLvTO3Ye5pWfCXK8PptVSVEI8BTzBDnA%2fo8af45WAYhHzHDWSfw3Y6Uriw%3d%3d | unknown | — | — | unknown |
6760 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bc852310-4978-4192-9f38-f8fcfefc7b93?P1=1720052324&P2=404&P3=2&P4=X0tc7qBa9Ayq4Rg8sKL4DzqOiKGfYLvTO3Ye5pWfCXK8PptVSVEI8BTzBDnA%2fo8af45WAYhHzHDWSfw3Y6Uriw%3d%3d | unknown | — | — | unknown |
4656 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | unknown |
1544 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
1972 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | unknown |
3040 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | unknown |
2832 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | unknown |
4172 | Prankscript.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/?fields=225545 | unknown | — | — | unknown |
6760 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bc852310-4978-4192-9f38-f8fcfefc7b93?P1=1720052324&P2=404&P3=2&P4=X0tc7qBa9Ayq4Rg8sKL4DzqOiKGfYLvTO3Ye5pWfCXK8PptVSVEI8BTzBDnA%2fo8af45WAYhHzHDWSfw3Y6Uriw%3d%3d | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
3516 | RUXIMICS.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4656 | SearchApp.exe | 92.123.104.24:443 | www.bing.com | Akamai International B.V. | DE | unknown |
4656 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | unknown |
1544 | svchost.exe | 20.190.160.20:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
1544 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | unknown |
4656 | SearchApp.exe | 92.123.104.18:443 | www.bing.com | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
r.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
gstatic.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
ip-api.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2168 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
4172 | Prankscript.exe | A Network Trojan was detected | STEALER [ANY.RUN] BlankGrabber (SkochGrabber) Generic External IP Check |
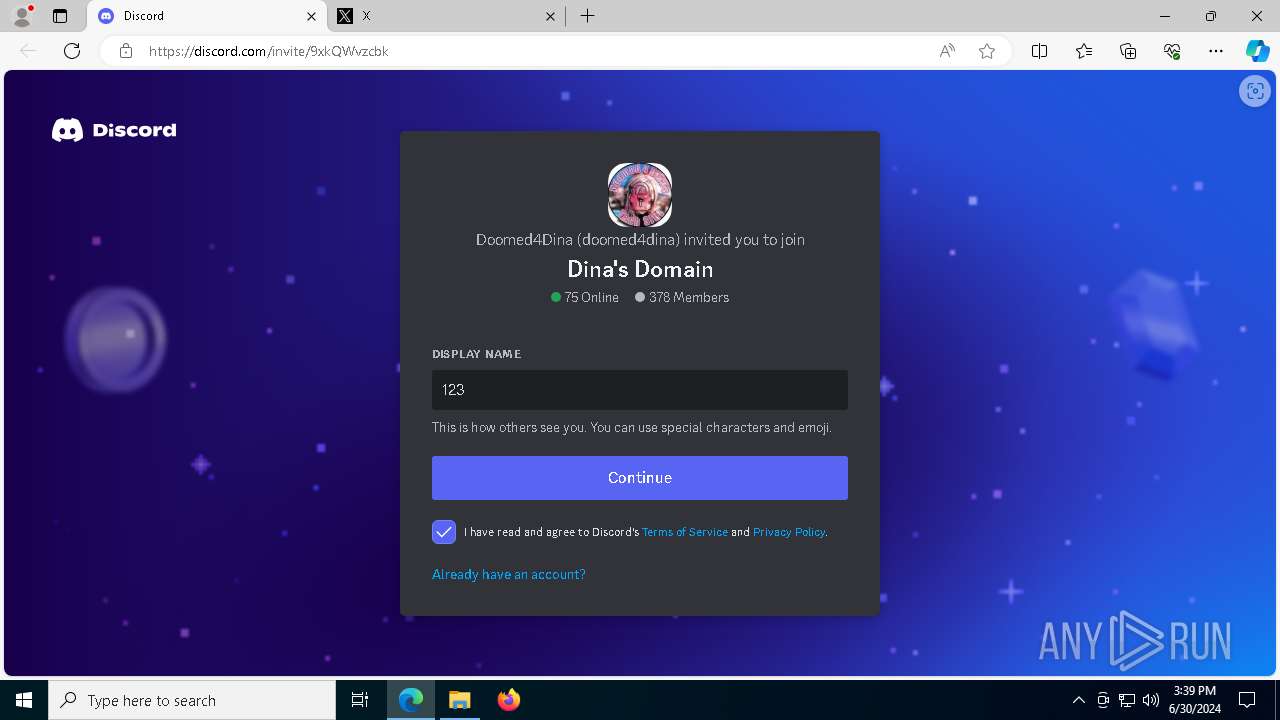
4172 | Prankscript.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |
2168 | svchost.exe | Misc activity | ET HUNTING Telegram API Domain in DNS Lookup |
4172 | Prankscript.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
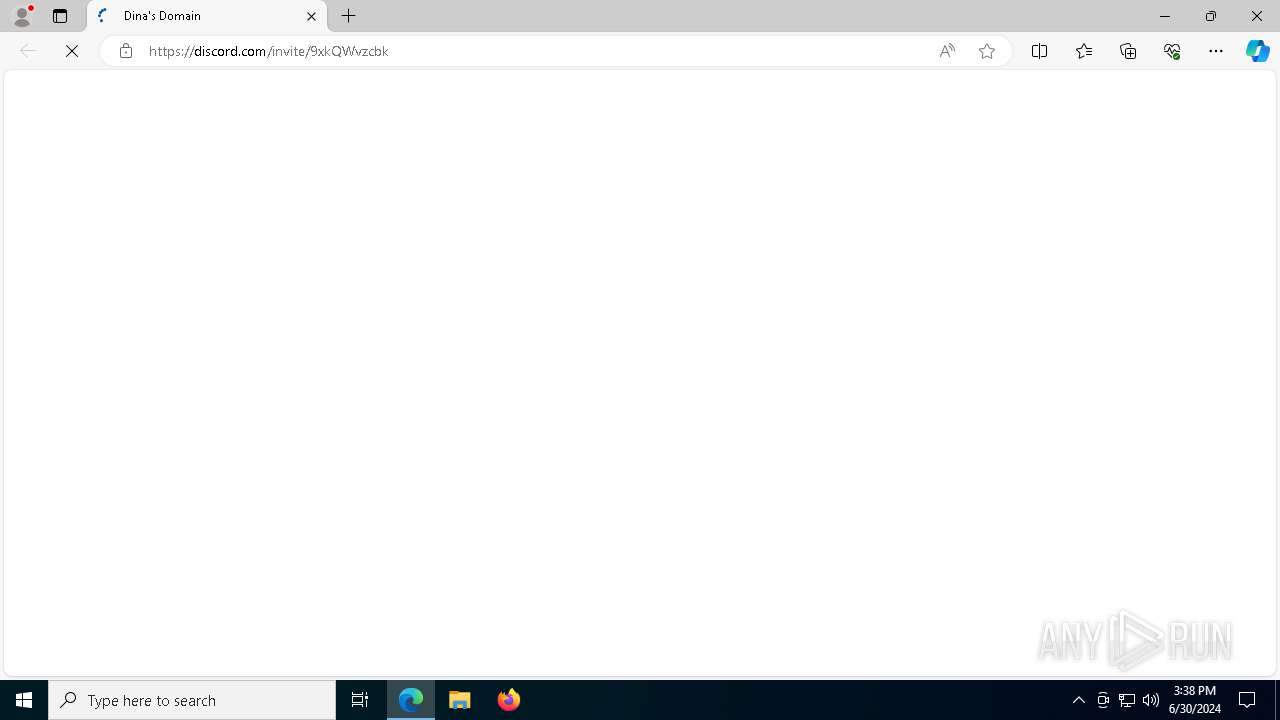
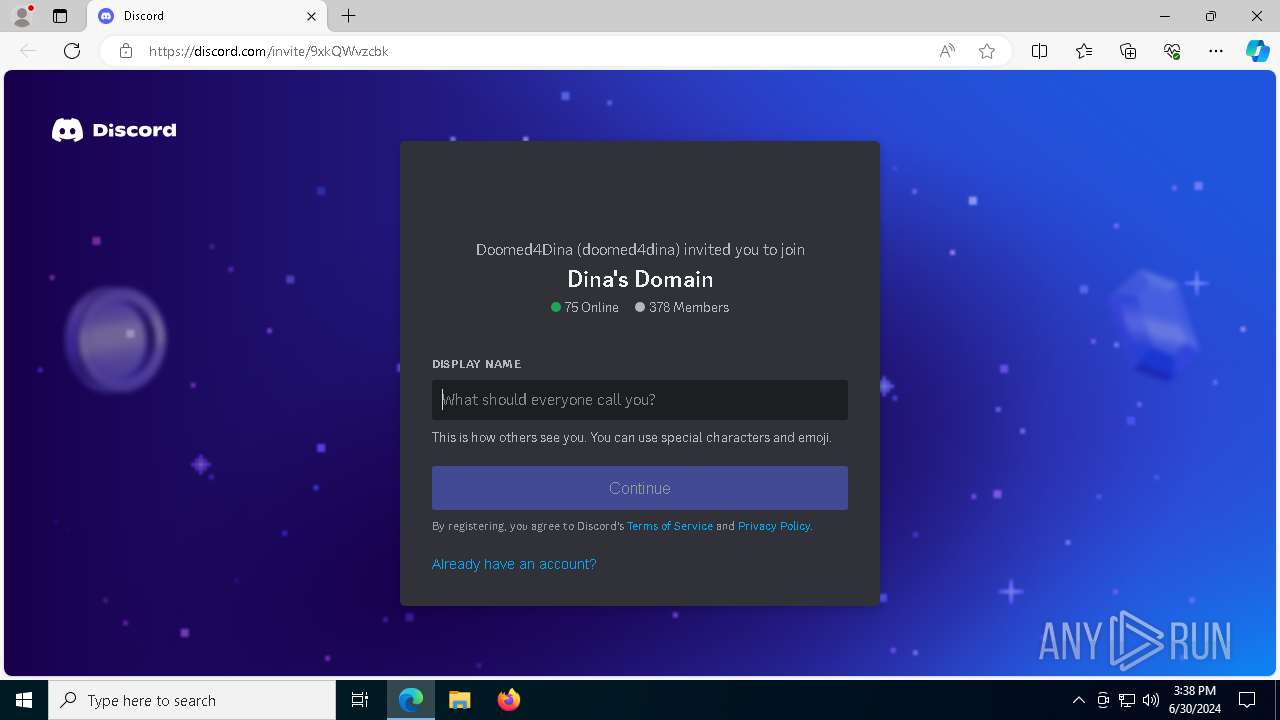
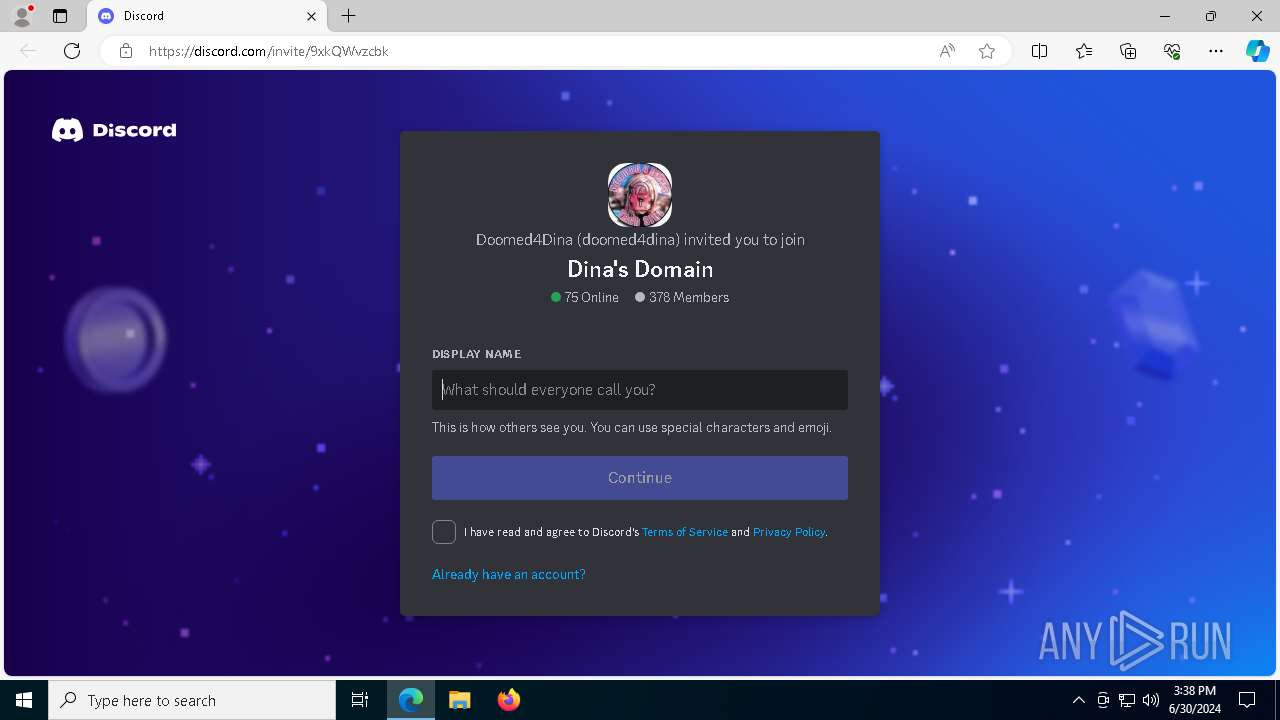
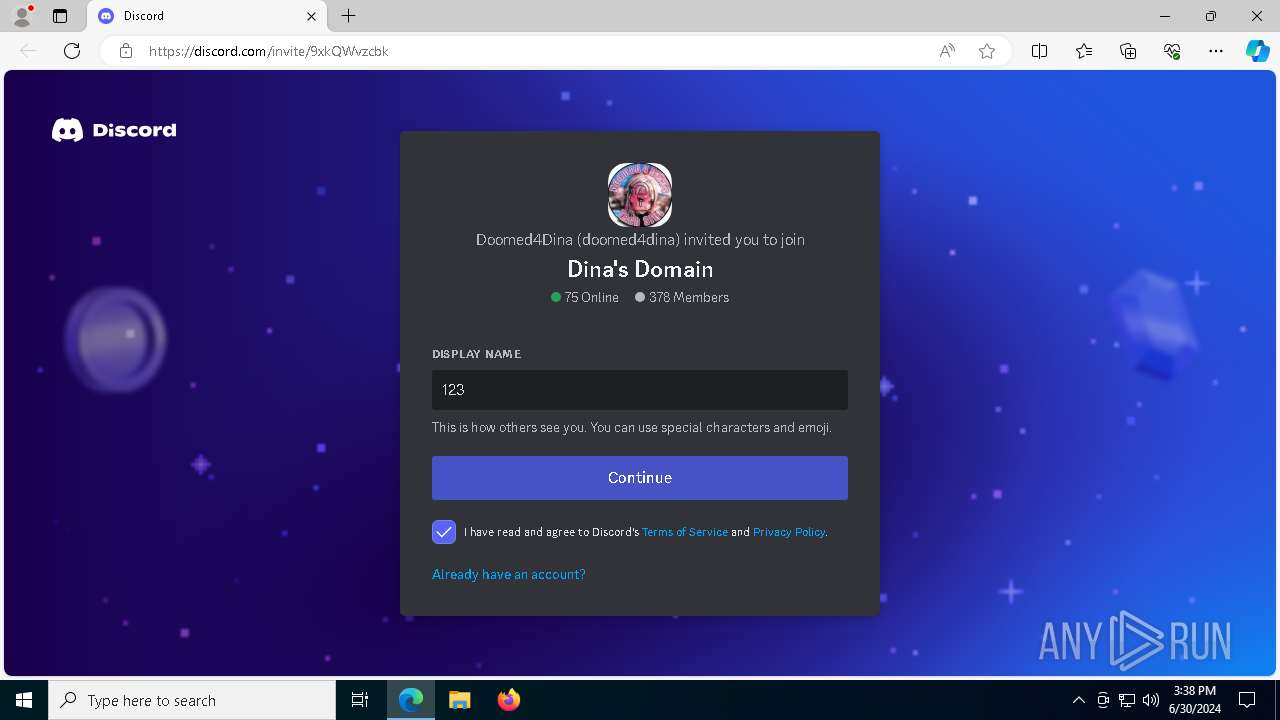
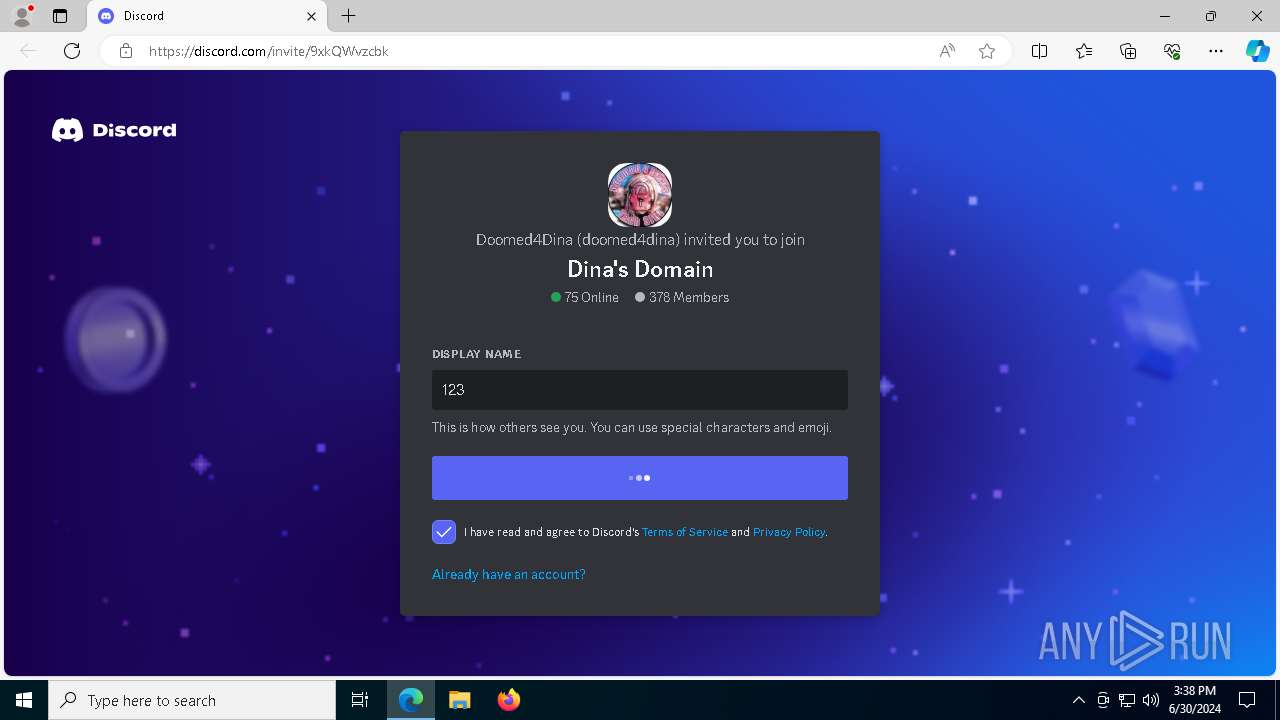
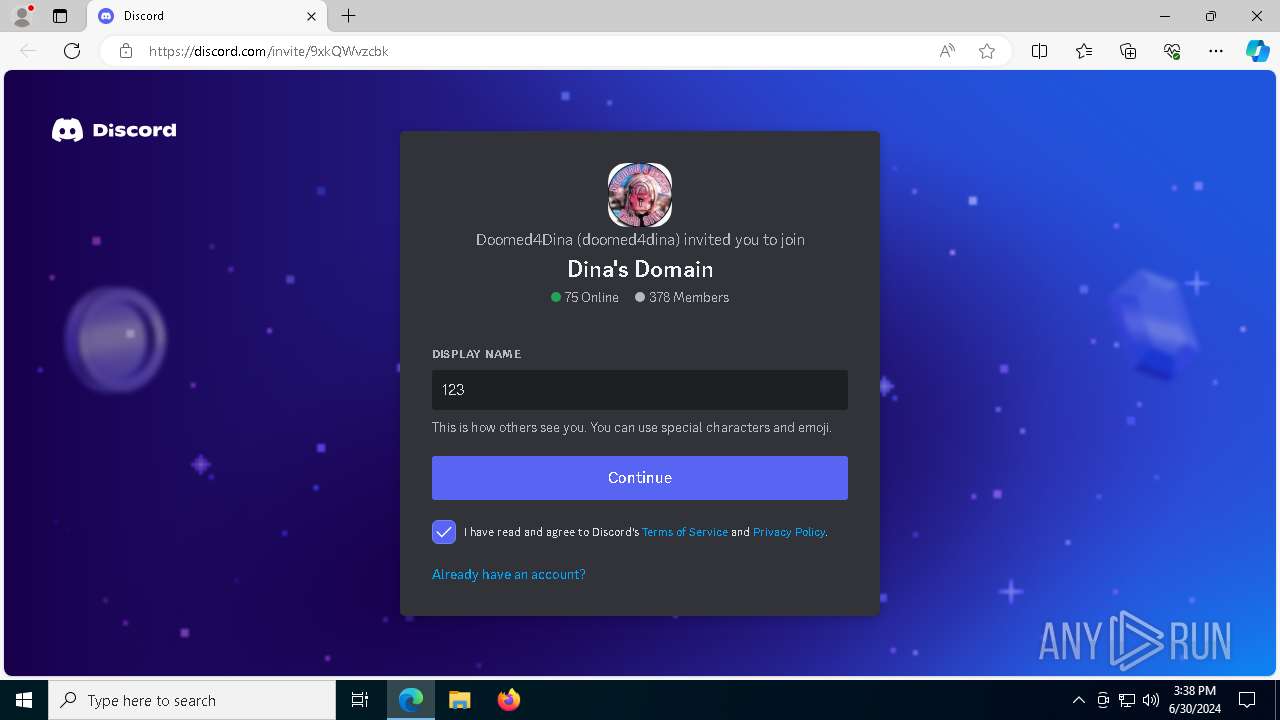
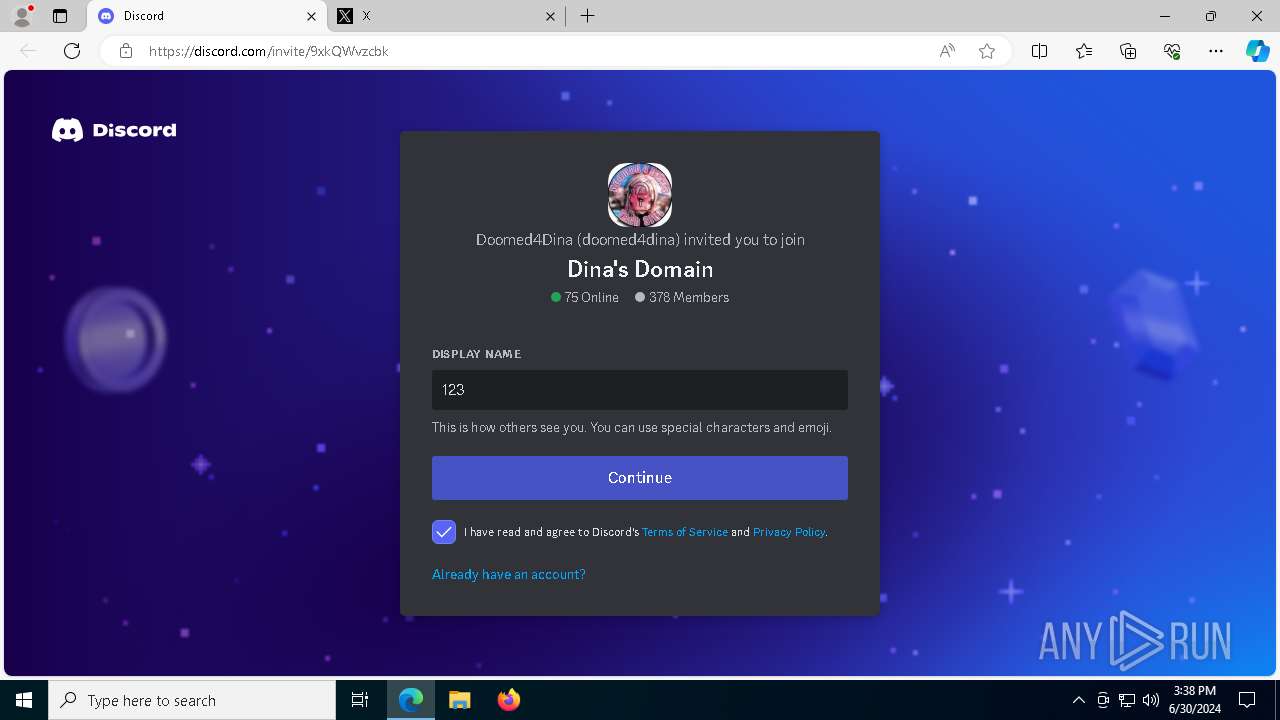
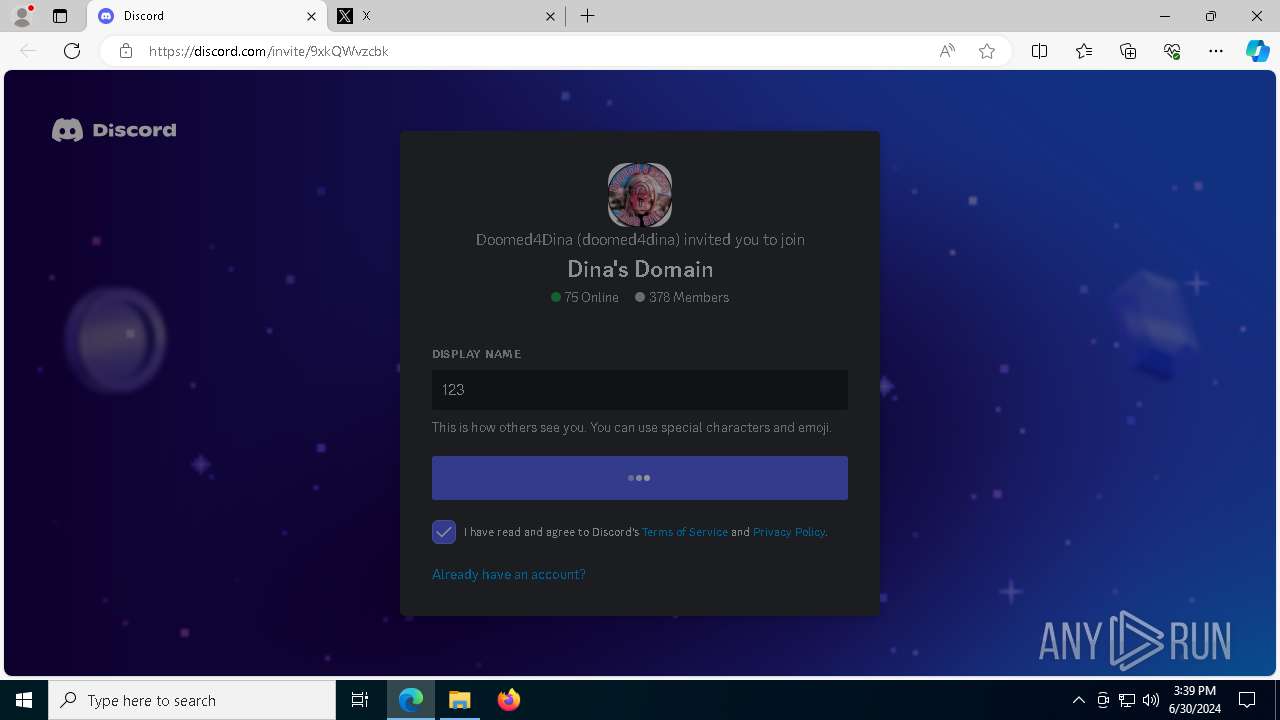
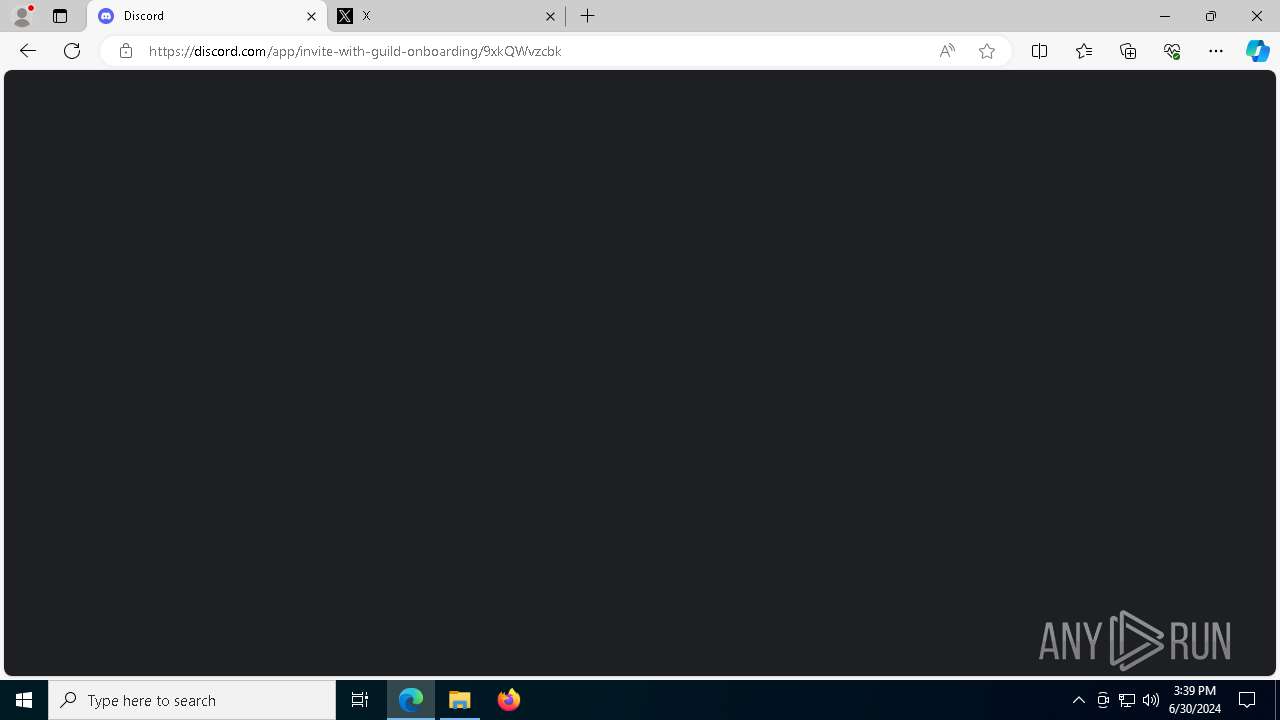
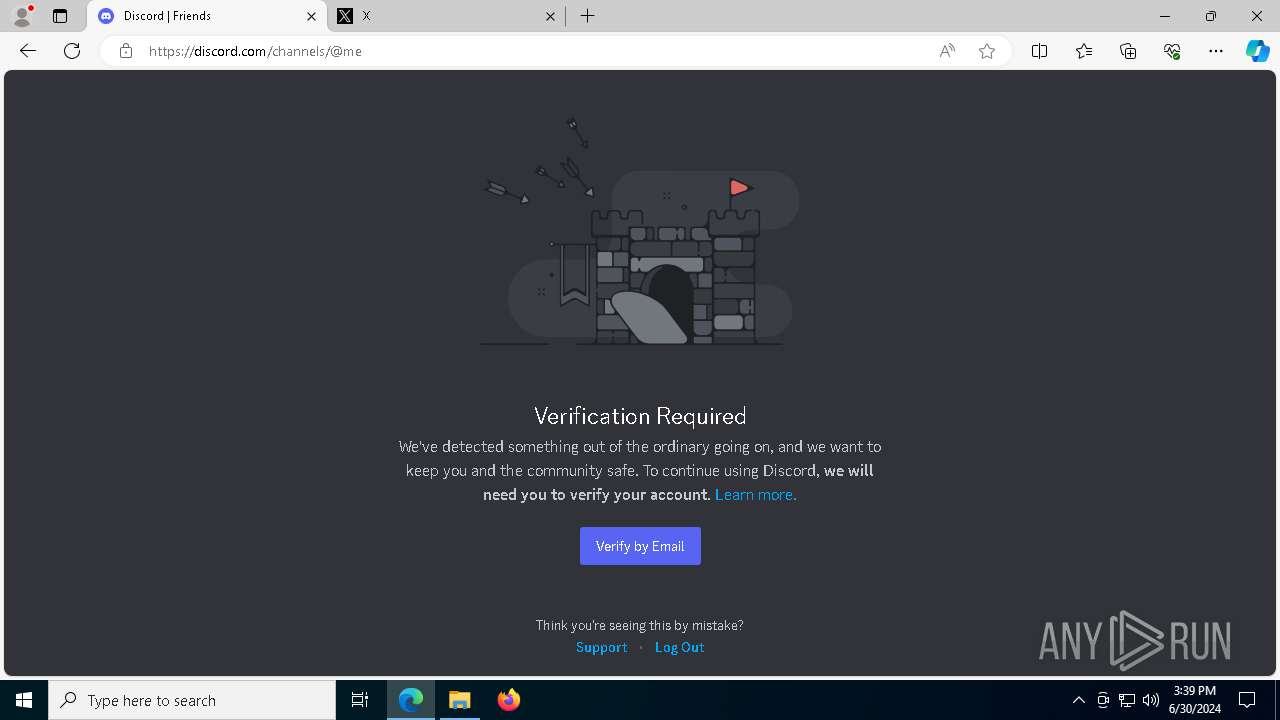
1828 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
1828 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
1828 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
1828 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
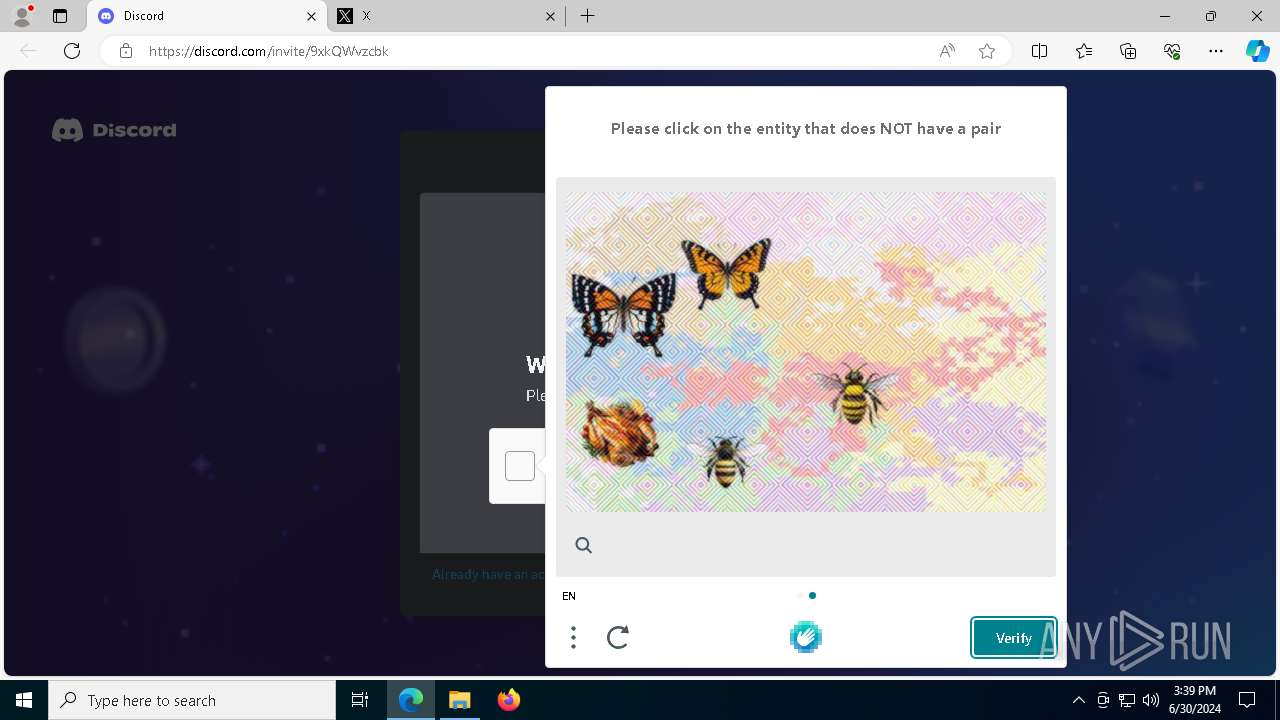
1828 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] hCaptcha Enterprise Challenge |