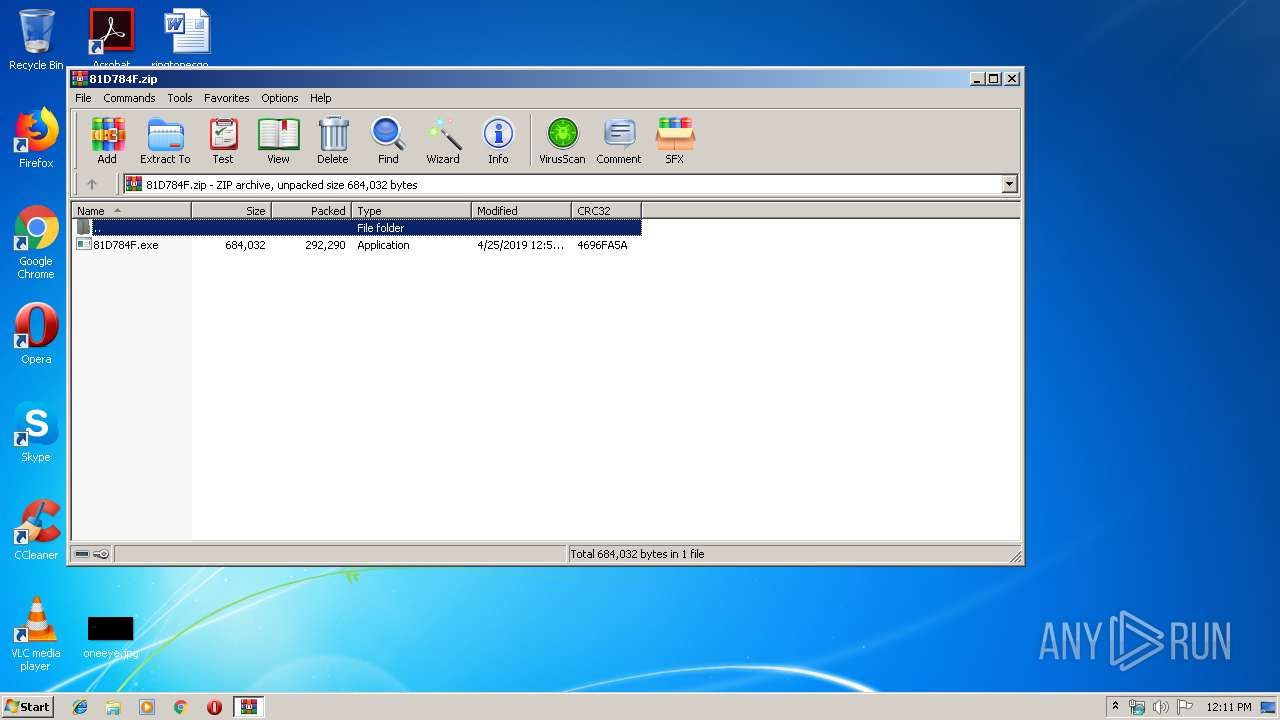
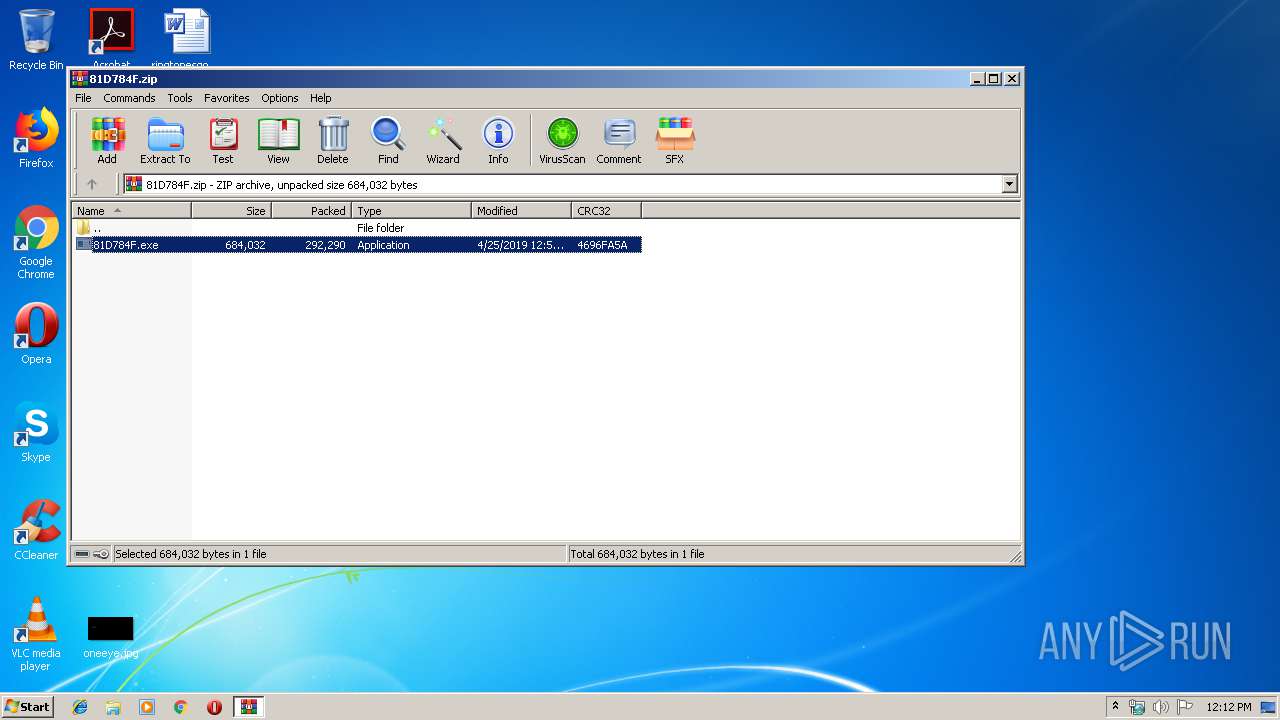
| File name: | 81D784F.zip |
| Full analysis: | https://app.any.run/tasks/b2106abe-22c2-4312-a21d-dfb7076538ad |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | April 25, 2019, 11:11:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 13209C2E44BD728E1727871210B11ECF |
| SHA1: | B0B6FA501A200C150AABA993A525E4AB98B0C08F |
| SHA256: | F47893E482168D03A51788CAE3A36FC932318A9969FE8A67CB0C5231A06CF6E0 |
| SSDEEP: | 6144:IscSdSg0YgdKrOB1xSO7oW+IM4dTD3yMezuKTc7DjQIRHrzk9Nr:V8YFrSiO7oWQg33yMzl30KHrzsNr |
MALICIOUS
Application was dropped or rewritten from another process
- 81D784F.exe (PID: 1712)
- ez7blu.exe (PID: 3748)
- ez7blu.exe (PID: 2244)
- 81D784F.exe (PID: 1476)
- 81D784F.exe (PID: 3468)
- ez7blu.exe (PID: 2956)
Changes the autorun value in the registry
- control.exe (PID: 2700)
Formbook was detected
- control.exe (PID: 2700)
- Firefox.exe (PID: 2304)
Actions looks like stealing of personal data
- control.exe (PID: 2700)
FORMBOOK was detected
- explorer.exe (PID: 252)
Connects to CnC server
- explorer.exe (PID: 252)
Stealing of credential data
- control.exe (PID: 2700)
SUSPICIOUS
Reads Internet Cache Settings
- explorer.exe (PID: 252)
Creates files in the user directory
- explorer.exe (PID: 252)
- control.exe (PID: 2700)
Application launched itself
- 81D784F.exe (PID: 3468)
- 81D784F.exe (PID: 1712)
- ez7blu.exe (PID: 2244)
- ez7blu.exe (PID: 3748)
Starts CMD.EXE for commands execution
- control.exe (PID: 2700)
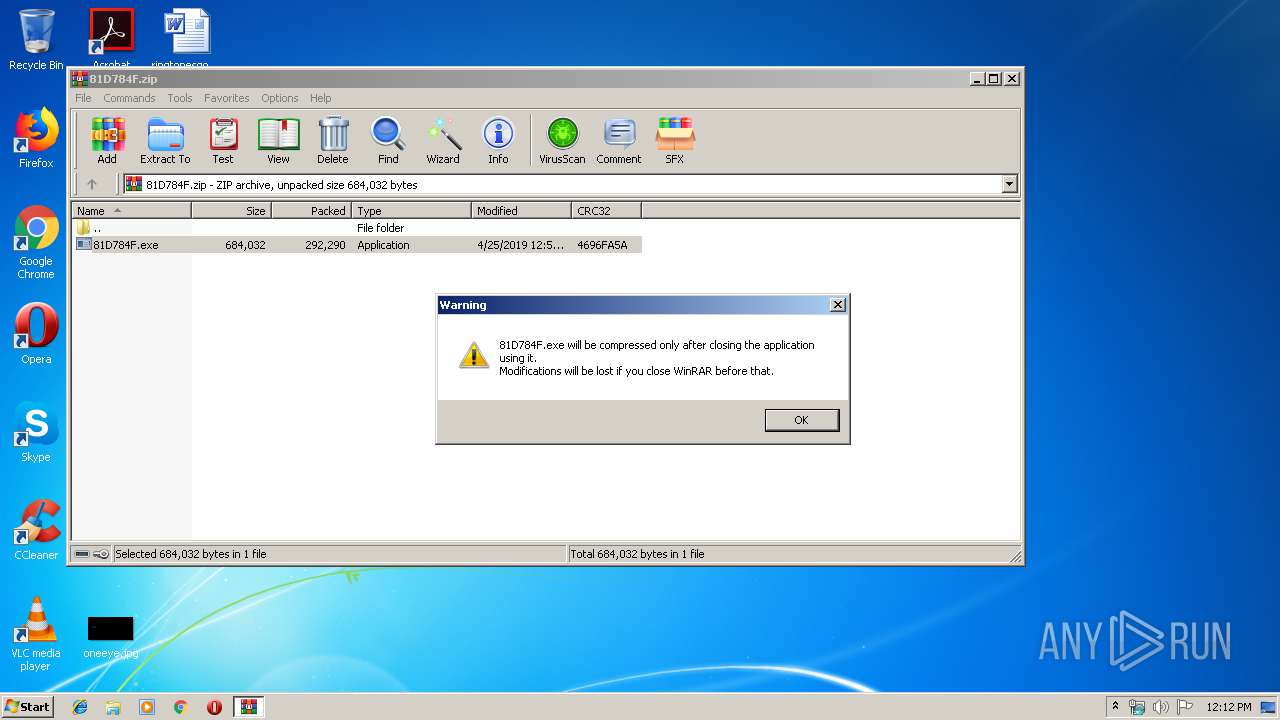
Executable content was dropped or overwritten
- explorer.exe (PID: 252)
- DllHost.exe (PID: 1168)
- WinRAR.exe (PID: 2984)
Loads DLL from Mozilla Firefox
- control.exe (PID: 2700)
Creates files in the program directory
- DllHost.exe (PID: 1168)
INFO
Creates files in the user directory
- Firefox.exe (PID: 2304)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:04:25 00:53:00 |
| ZipCRC: | 0x4696fa5a |
| ZipCompressedSize: | 292290 |
| ZipUncompressedSize: | 684032 |
| ZipFileName: | 81D784F.exe |
Total processes
46
Monitored processes
13
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1168 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1476 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2984.22575\81D784F.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2984.22575\81D784F.exe | — | 81D784F.exe | |||||||||||
User: admin Company: bITPay Integrity Level: MEDIUM Description: cOdE LAboratories, Inc. Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 1712 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2984.22575\81D784F.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2984.22575\81D784F.exe | — | 81D784F.exe | |||||||||||
User: admin Company: bITPay Integrity Level: MEDIUM Description: cOdE LAboratories, Inc. Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 2244 | "C:\Program Files\Tx2p4anah\ez7blu.exe" | C:\Program Files\Tx2p4anah\ez7blu.exe | — | explorer.exe | |||||||||||
User: admin Company: bITPay Integrity Level: MEDIUM Description: cOdE LAboratories, Inc. Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 2304 | "C:\Program Files\Mozilla Firefox\Firefox.exe" | C:\Program Files\Mozilla Firefox\Firefox.exe | control.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
| 2700 | "C:\Windows\System32\control.exe" | C:\Windows\System32\control.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Control Panel Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2956 | "C:\Program Files\Tx2p4anah\ez7blu.exe" | C:\Program Files\Tx2p4anah\ez7blu.exe | — | ez7blu.exe | |||||||||||
User: admin Company: bITPay Integrity Level: MEDIUM Description: cOdE LAboratories, Inc. Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 2984 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\81D784F.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3256 | /c del "C:\Users\admin\AppData\Local\Temp\Rar$EXa2984.22575\81D784F.exe" | C:\Windows\System32\cmd.exe | — | control.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 410
Read events
1 360
Write events
50
Delete events
0
Modification events
| (PID) Process: | (2984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2984) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\81D784F.zip | |||
| (PID) Process: | (2984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (252) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | a |
Value: WinRAR.exe | |||
| (PID) Process: | (252) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | MRUList |
Value: a | |||
Executable files
3
Suspicious files
77
Text files
6
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 252 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\290532160612e071.automaticDestinations-ms | automaticdestinations-ms | |
MD5:— | SHA256:— | |||
| 2984 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2984.22575\81D784F.exe | executable | |
MD5:— | SHA256:— | |||
| 252 | explorer.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012019042520190426\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3468 | 81D784F.exe | C:\Users\admin\AppData\Local\Temp\~DF9826BCF97CFBCEE1.TMP | binary | |
MD5:— | SHA256:— | |||
| 2700 | control.exe | C:\Users\admin\AppData\Roaming\3KARB4UE\3KAlogrc.ini | binary | |
MD5:— | SHA256:— | |||
| 1712 | 81D784F.exe | C:\Users\admin\AppData\Local\Temp\~DFE17F87CD8824C04E.TMP | binary | |
MD5:— | SHA256:— | |||
| 252 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\81D784F.zip.lnk | lnk | |
MD5:— | SHA256:— | |||
| 252 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\1b4dd67f29cb1962.automaticDestinations-ms | automaticdestinations-ms | |
MD5:— | SHA256:— | |||
| 1168 | DllHost.exe | C:\Program Files\Tx2p4anah\ez7blu.exe | executable | |
MD5:— | SHA256:— | |||
| 2700 | control.exe | C:\Users\admin\AppData\Roaming\3KARB4UE\3KAlogim.jpeg | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
13
DNS requests
12
Threats
21
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
252 | explorer.exe | GET | — | 104.28.29.193:80 | http://www.art-finders.com/am/?GRj8Zl=K9VqDWVkX4bPd9hYI0p41UEk0OMfHZwSDwmB7bQPm/+/638IZXOohTXXFvV7uN47ipF+iA==&cb=VT4PGdJ0 | US | — | — | malicious |
252 | explorer.exe | POST | — | 107.164.171.109:80 | http://www.aberdeenme.com/am/ | US | — | — | malicious |
252 | explorer.exe | POST | — | 107.164.171.109:80 | http://www.aberdeenme.com/am/ | US | — | — | malicious |
252 | explorer.exe | GET | 302 | 23.20.239.12:80 | http://www.yocoinvn.com/am/?GRj8Zl=cPEqJ4mfV+iQu9tp0/Ju/jZDpSSu5VktO2ni3bqmUU1NVG3jz+aSW1n81PxoBRBSXAj4Vg==&cb=VT4PGdJ0 | US | html | 184 b | shared |
252 | explorer.exe | POST | — | 107.164.171.109:80 | http://www.aberdeenme.com/am/ | US | — | — | malicious |
252 | explorer.exe | POST | 404 | 198.187.30.241:80 | http://www.boxcay.com/am/ | US | html | 290 b | malicious |
252 | explorer.exe | GET | 404 | 198.187.30.241:80 | http://www.boxcay.com/am/?GRj8Zl=kdCtaWC4LlxdsSODQA5ZThczCjB51n0ynfNvJQ33HVhGLtGmmilpb5d2CHCBeO8mpCstxA==&cb=VT4PGdJ0 | US | html | 326 b | malicious |
252 | explorer.exe | POST | 404 | 198.187.30.241:80 | http://www.boxcay.com/am/ | US | html | 290 b | malicious |
252 | explorer.exe | POST | — | 198.187.30.241:80 | http://www.boxcay.com/am/ | US | — | — | malicious |
252 | explorer.exe | POST | — | 104.28.29.193:80 | http://www.art-finders.com/am/ | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
252 | explorer.exe | 107.164.171.109:80 | www.aberdeenme.com | EGIHosting | US | malicious |
252 | explorer.exe | 23.20.239.12:80 | www.yocoinvn.com | Amazon.com, Inc. | US | shared |
252 | explorer.exe | 198.187.30.241:80 | www.boxcay.com | Namecheap, Inc. | US | malicious |
252 | explorer.exe | 104.28.29.193:80 | www.art-finders.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.forcemajeurecoin.com |
| unknown |
www.yocoinvn.com |
| shared |
www.hnlydgg.com |
| unknown |
www.illustratednight.com |
| unknown |
www.aberdeenme.com |
| malicious |
www.boxcay.com |
| malicious |
www.whygroup-recruit.com |
| unknown |
www.art-finders.com |
| malicious |
www.cursopotenciasexualdohomem.com |
| unknown |
www.xgzdr33.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
252 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
252 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
252 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
252 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
252 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
252 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
252 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
252 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
252 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
252 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
10 ETPRO signatures available at the full report