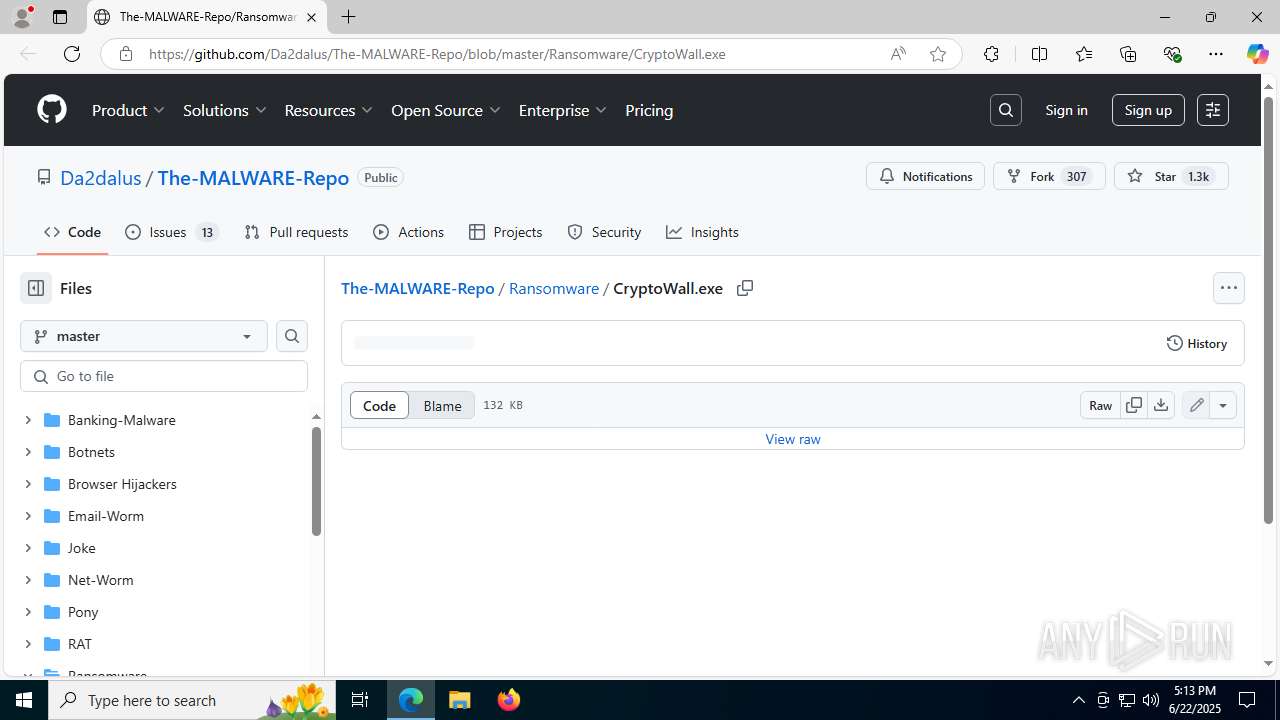
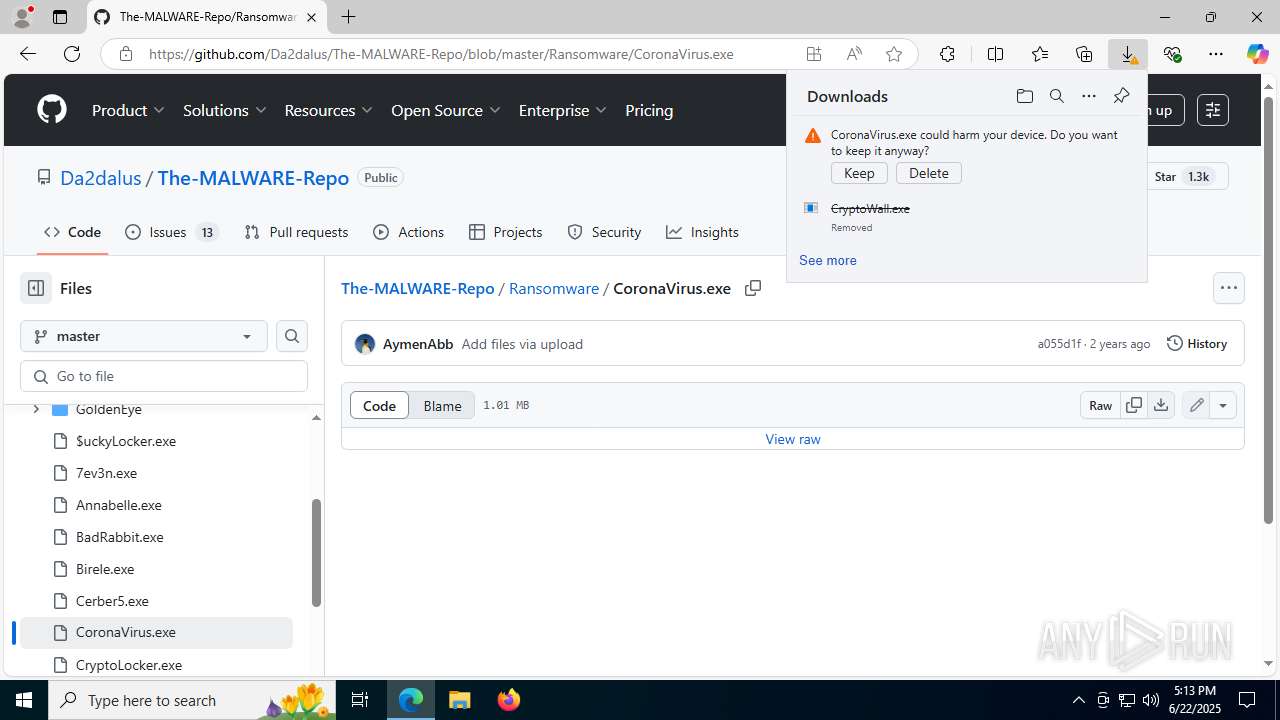
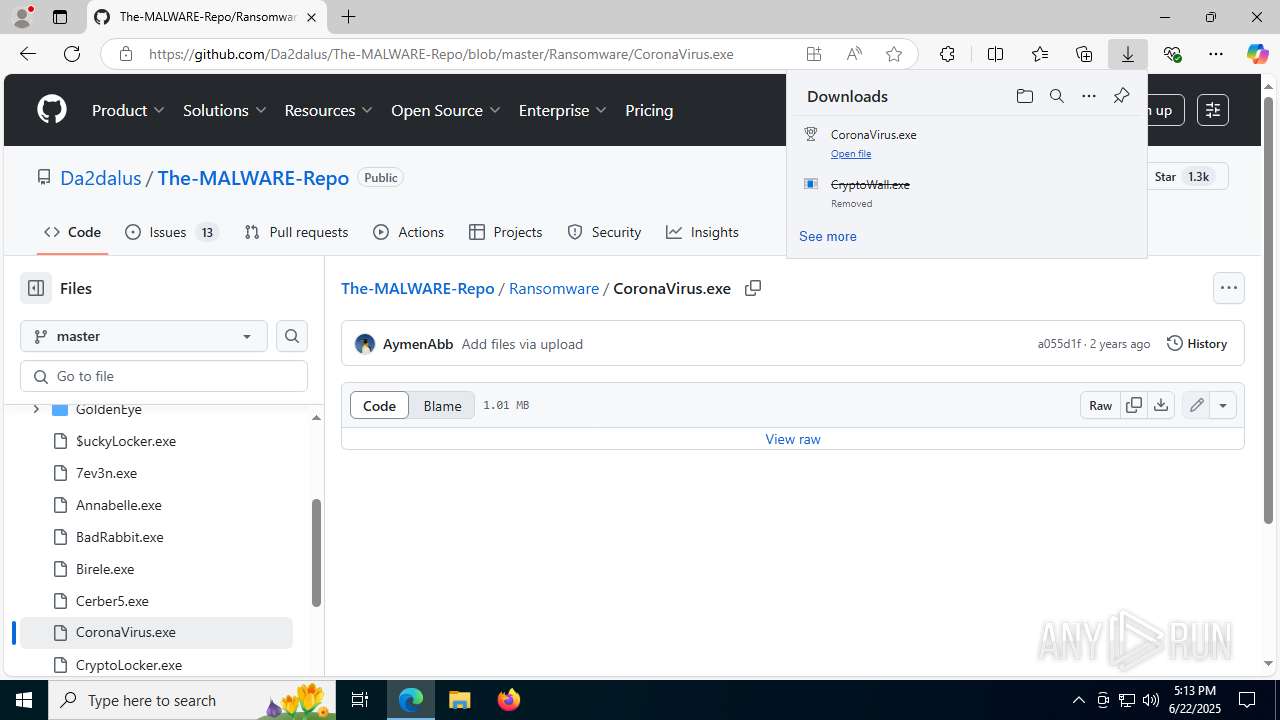
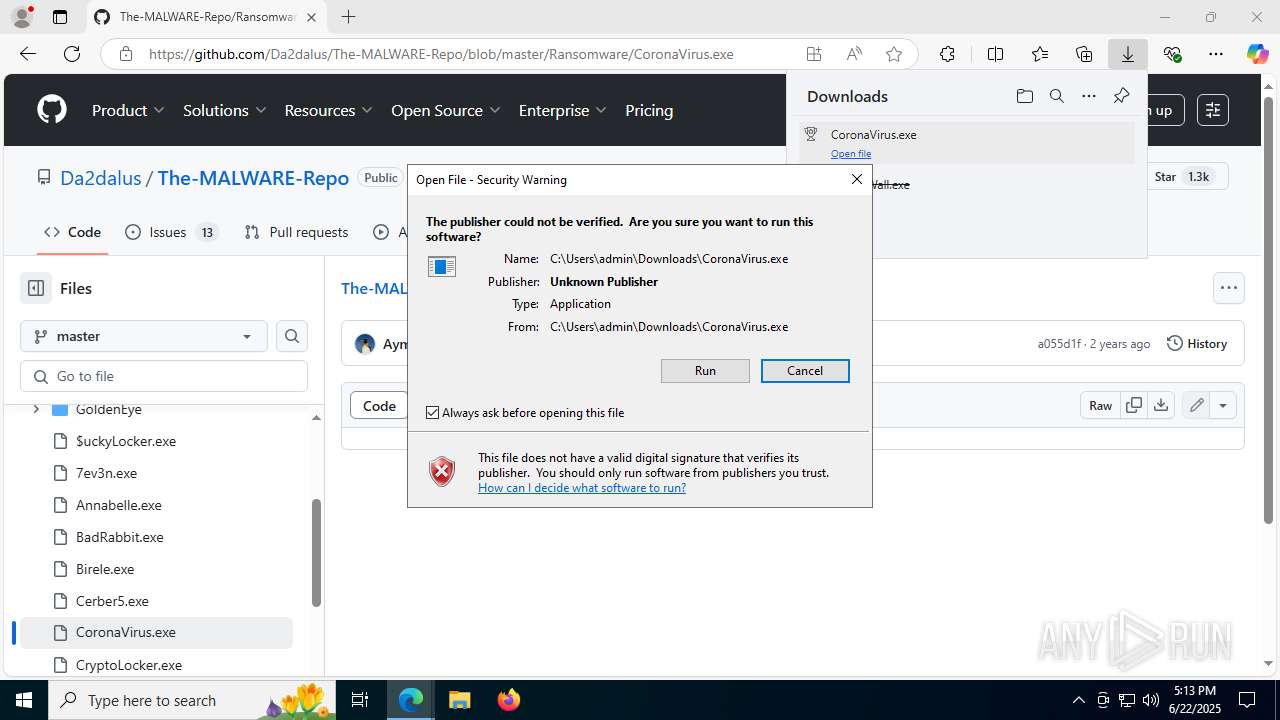
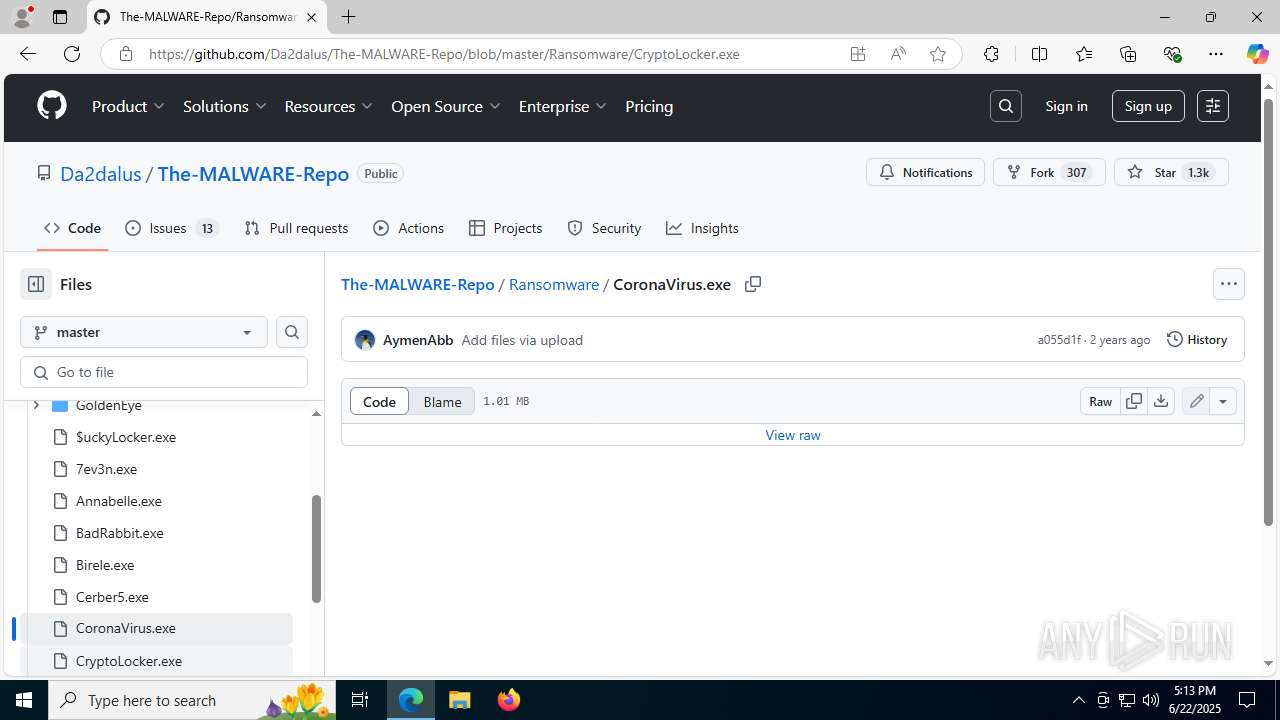
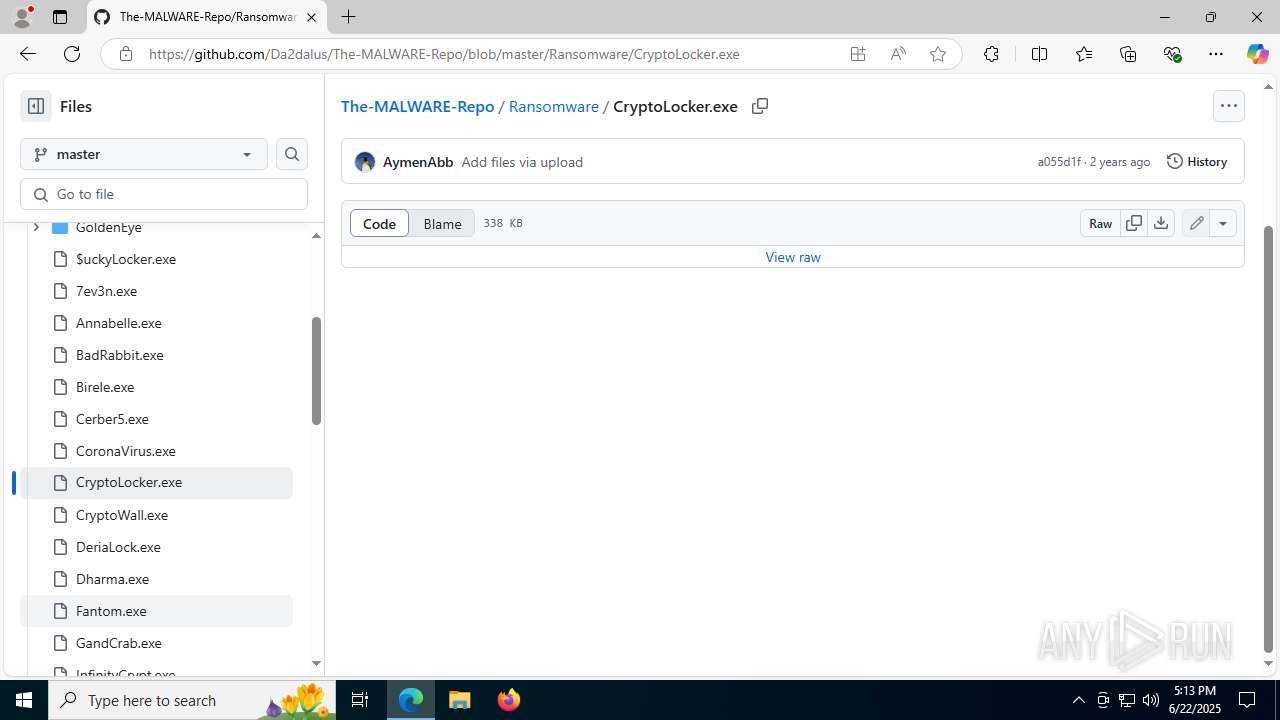
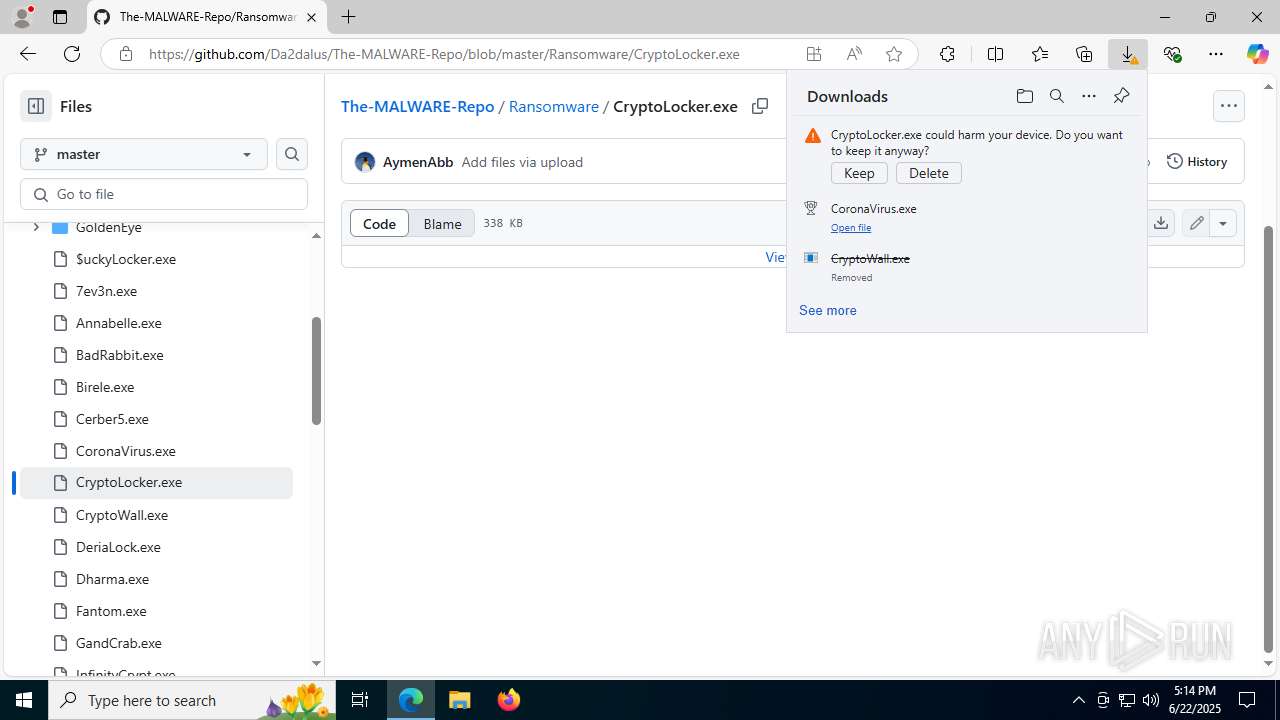
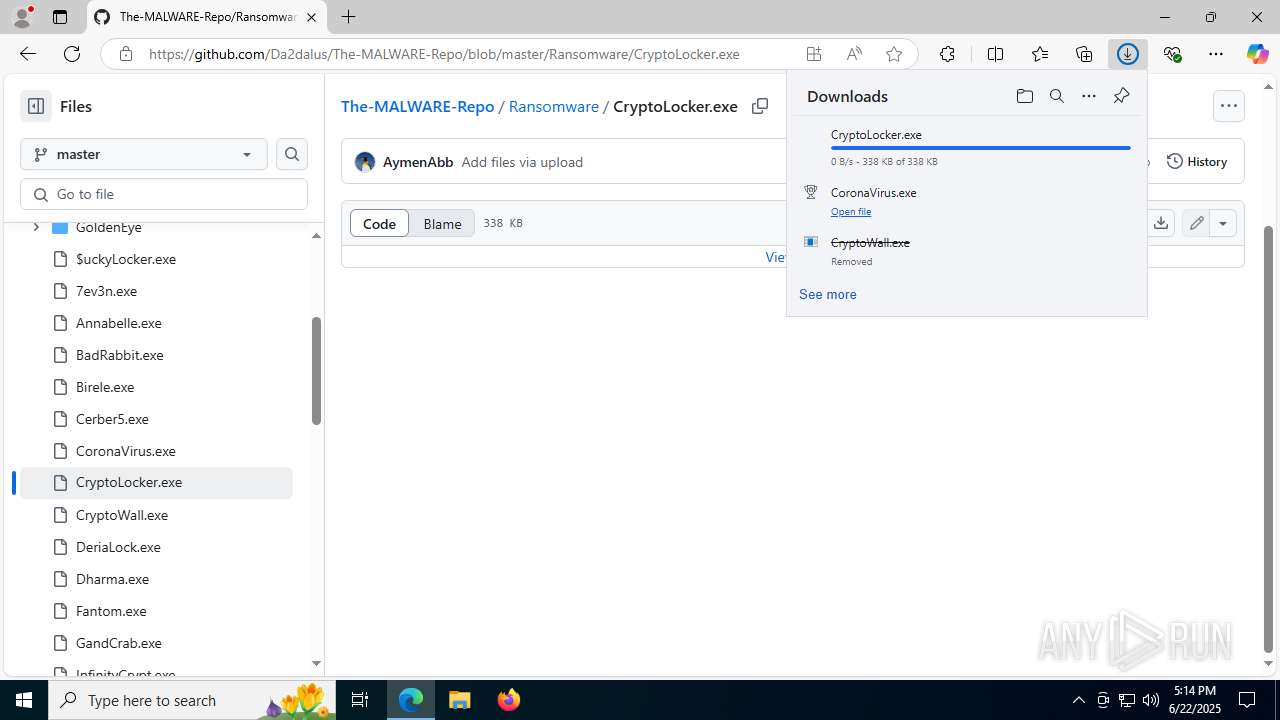
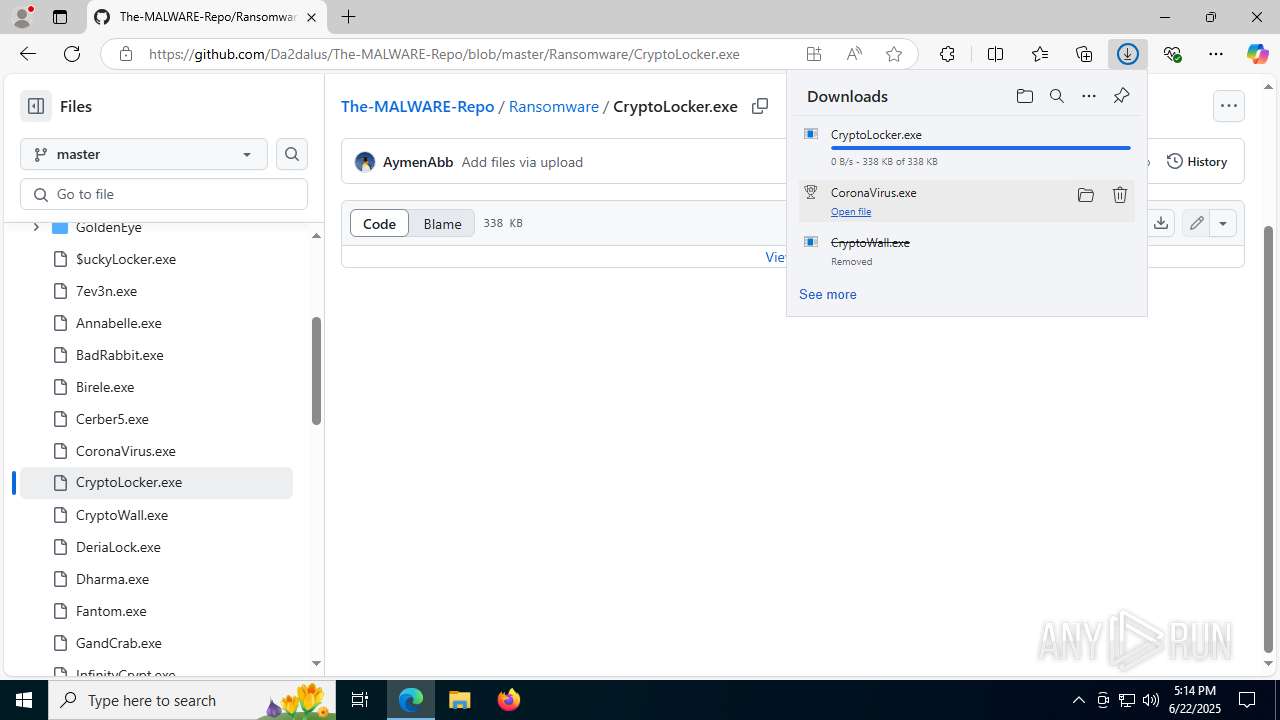
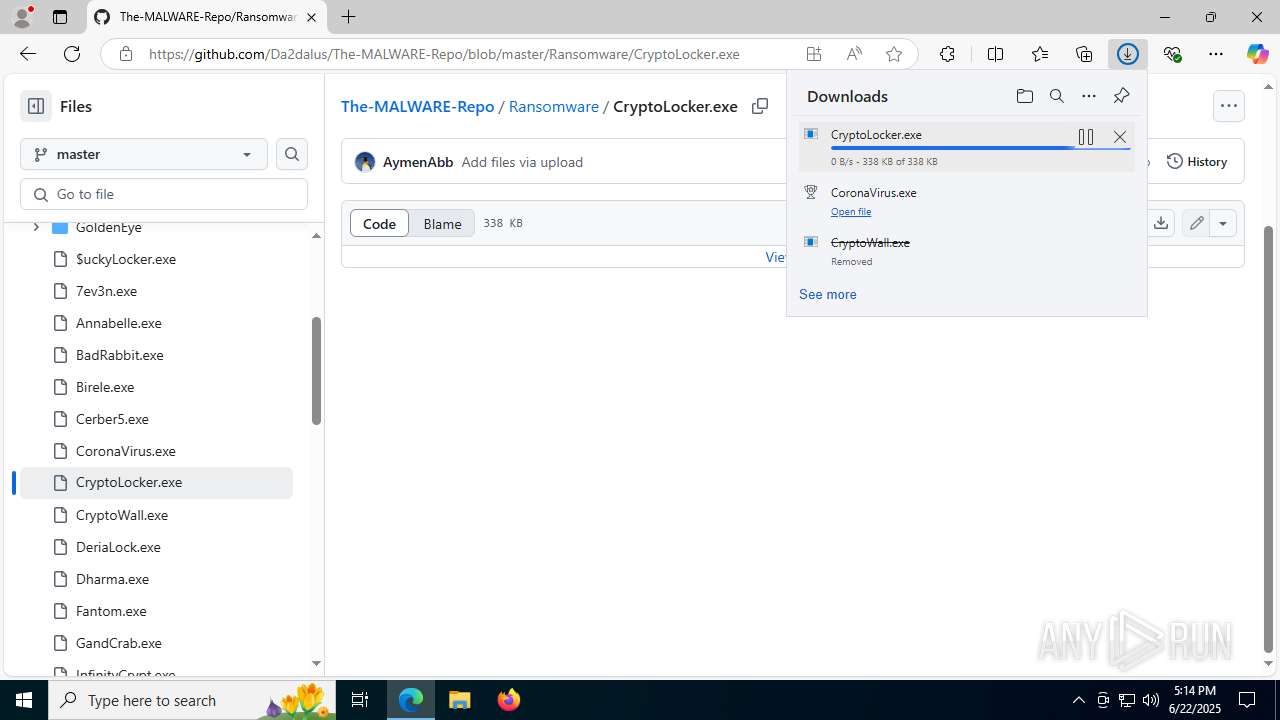
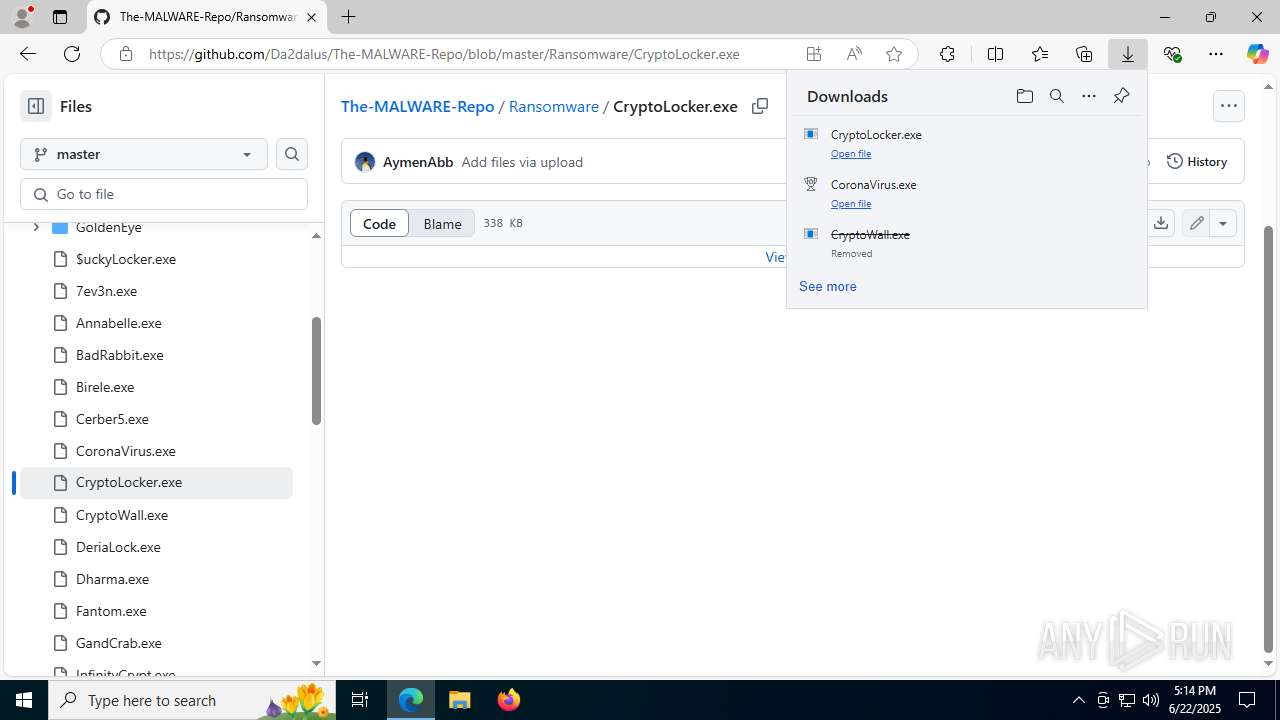
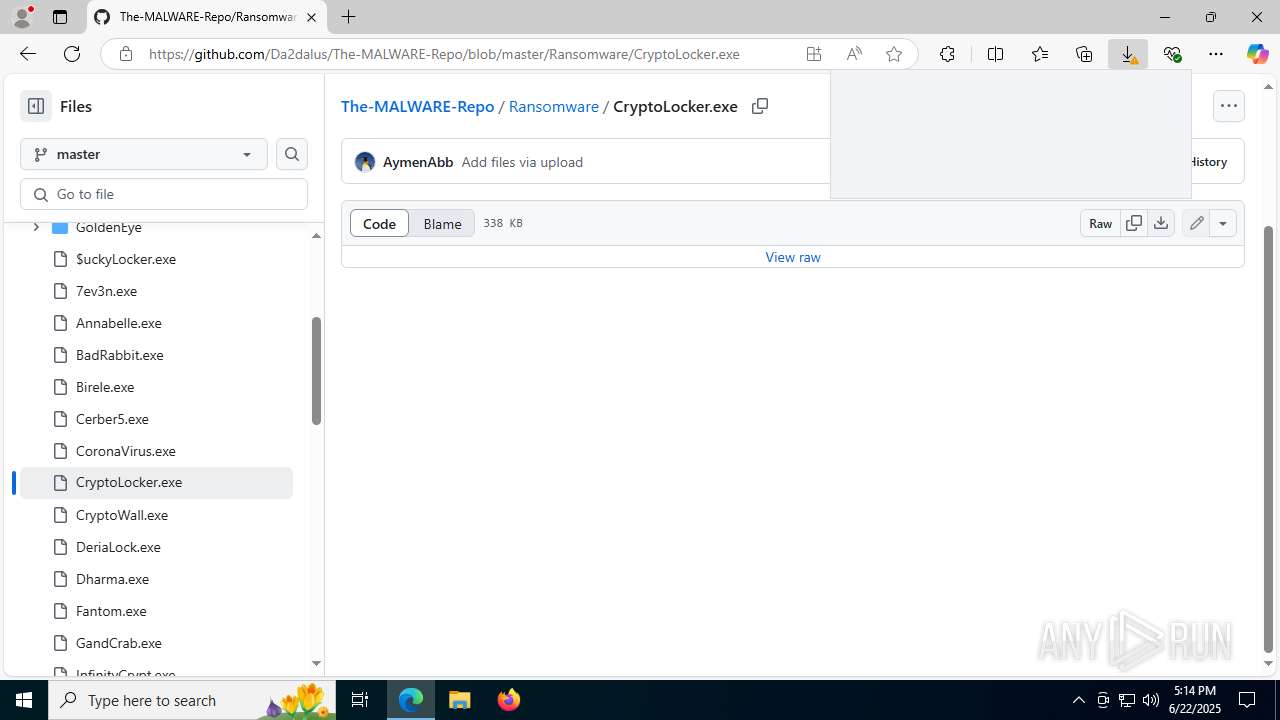
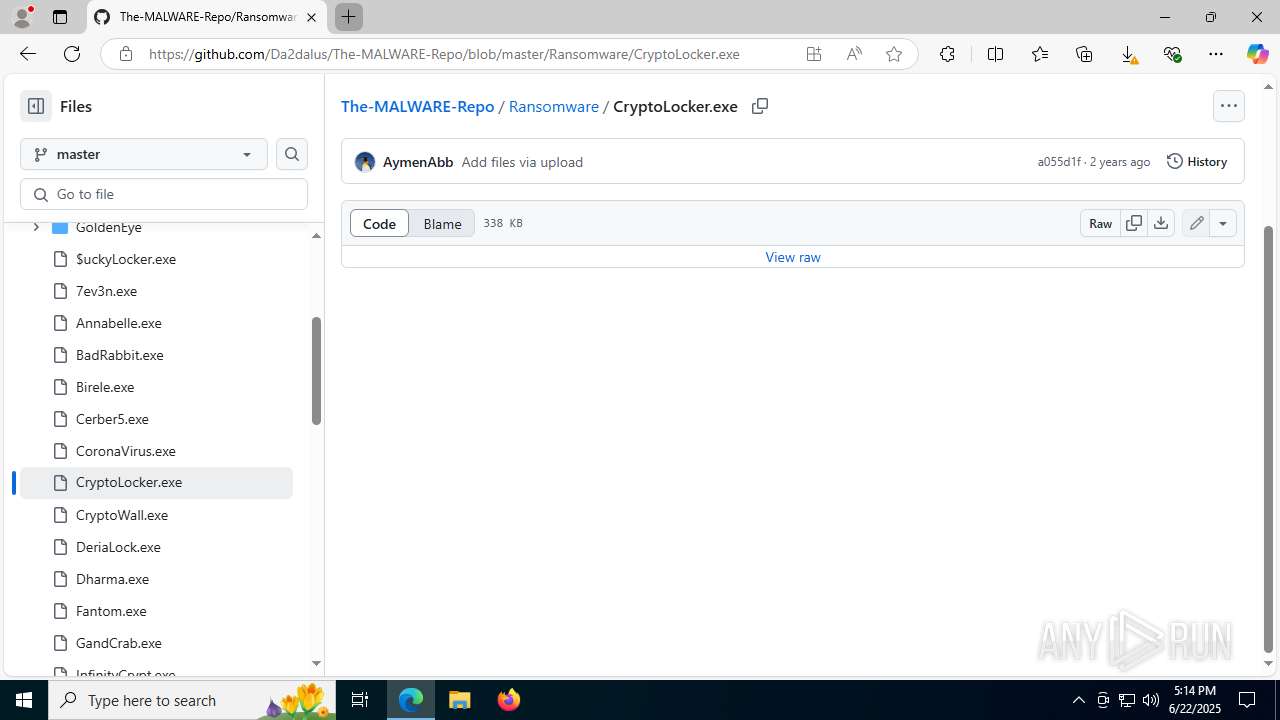
| URL: | https://github.com/Da2dalus/The-MALWARE-Repo/blob/master/Ransomware/CryptoWall.exe |
| Full analysis: | https://app.any.run/tasks/55180ff9-1ccb-42ae-ad1e-83238acc6517 |
| Verdict: | Malicious activity |
| Threats: | Dharma is advanced ransomware that has been observed in the wild since 2016. It is considered to be the second most profitable RaaS operation by the FBI. The malware targets hospitals and state organizations, encrypts files, and demands a payment to restore access to lost information. |
| Analysis date: | June 22, 2025, 17:13:26 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 72ADF322D01EB1D29D75DC10B88EEE0E |
| SHA1: | F751C64069A5959ADDD56E772691297BB0D02669 |
| SHA256: | F453184DA455789EB76E79FC76B661265F5FD08289120B85B03921AE900EBAF0 |
| SSDEEP: | 3:N8tEdJejSOpykOhuKIEHAz4XrN:2ubYSOcry+Az4Xp |
MALICIOUS
Changes the autorun value in the registry
- explorer.exe (PID: 7928)
- CoronaVirus.exe (PID: 7804)
- CoronaVirus.exe (PID: 7768)
- {34184A33-0407-212E-3300-09040709E2C2}.exe (PID: 1156)
DHARMA mutex has been found
- CoronaVirus.exe (PID: 7804)
- CoronaVirus.exe (PID: 7768)
Create files in the Startup directory
- explorer.exe (PID: 7928)
- CoronaVirus.exe (PID: 7804)
- CoronaVirus.exe (PID: 7768)
Deletes shadow copies
- cmd.exe (PID: 8108)
- cmd.exe (PID: 7820)
CORONAVIRUS has been detected
- CoronaVirus.exe (PID: 7804)
Actions looks like stealing of personal data
- CoronaVirus.exe (PID: 7804)
Modifies files in the Chrome extension folder
- CoronaVirus.exe (PID: 7804)
Renames files like ransomware
- CoronaVirus.exe (PID: 7804)
- CoronaVirus.exe (PID: 7768)
RANSOMWARE has been detected
- CoronaVirus.exe (PID: 7804)
- CoronaVirus.exe (PID: 7768)
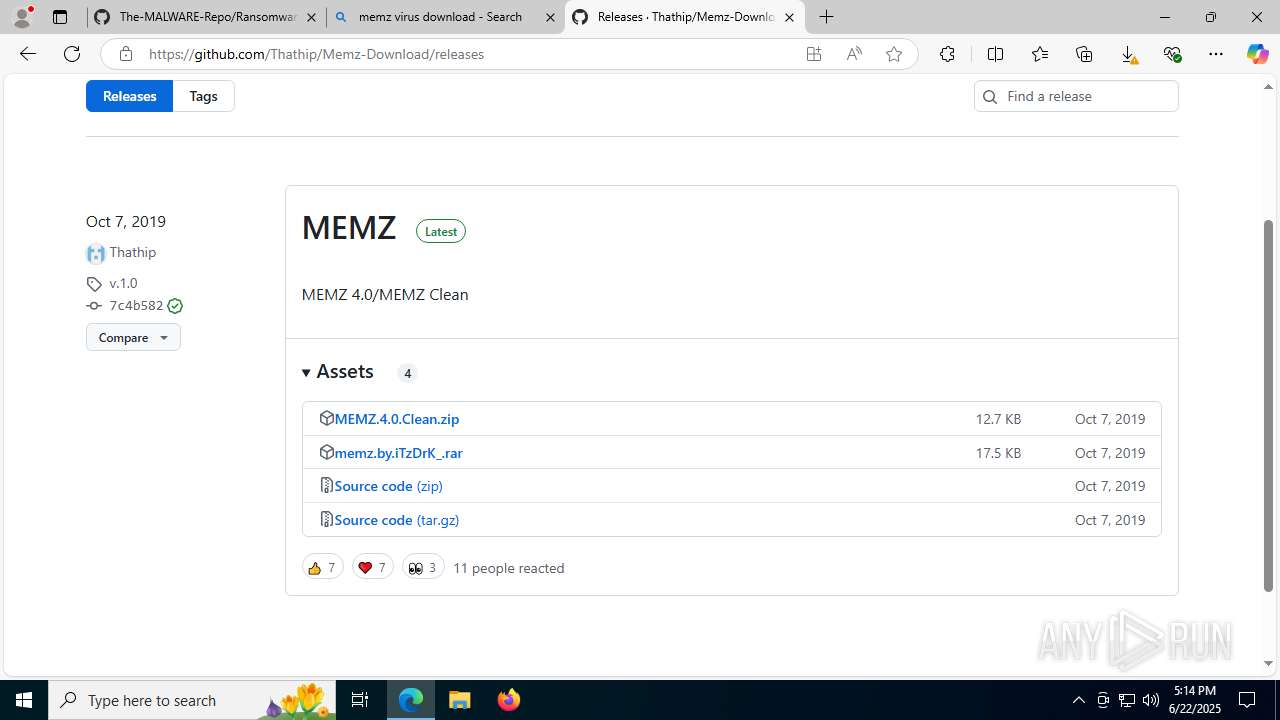
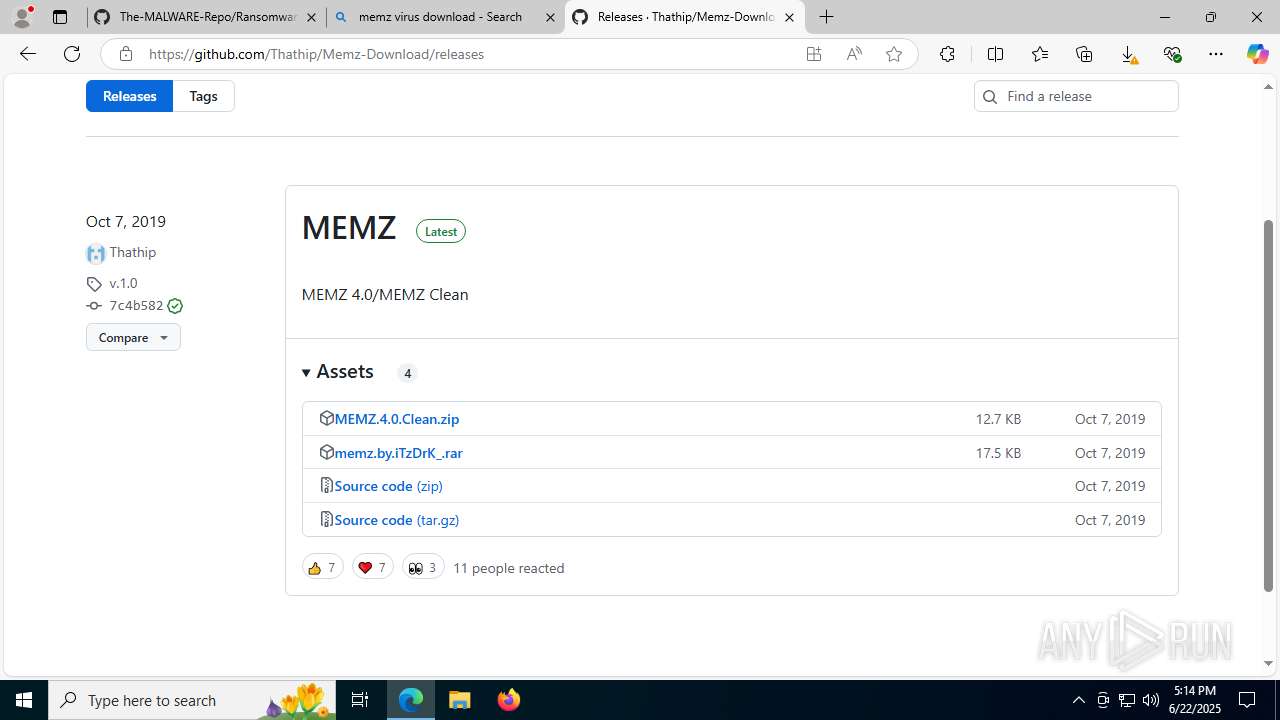
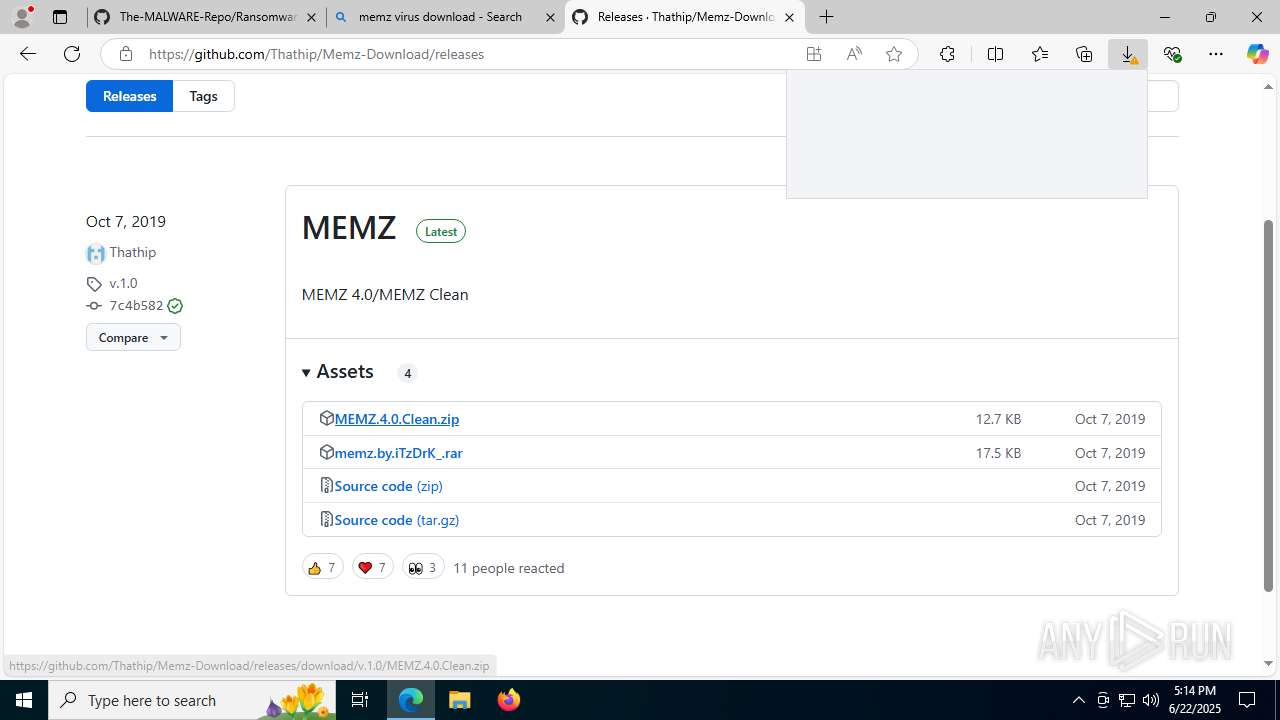
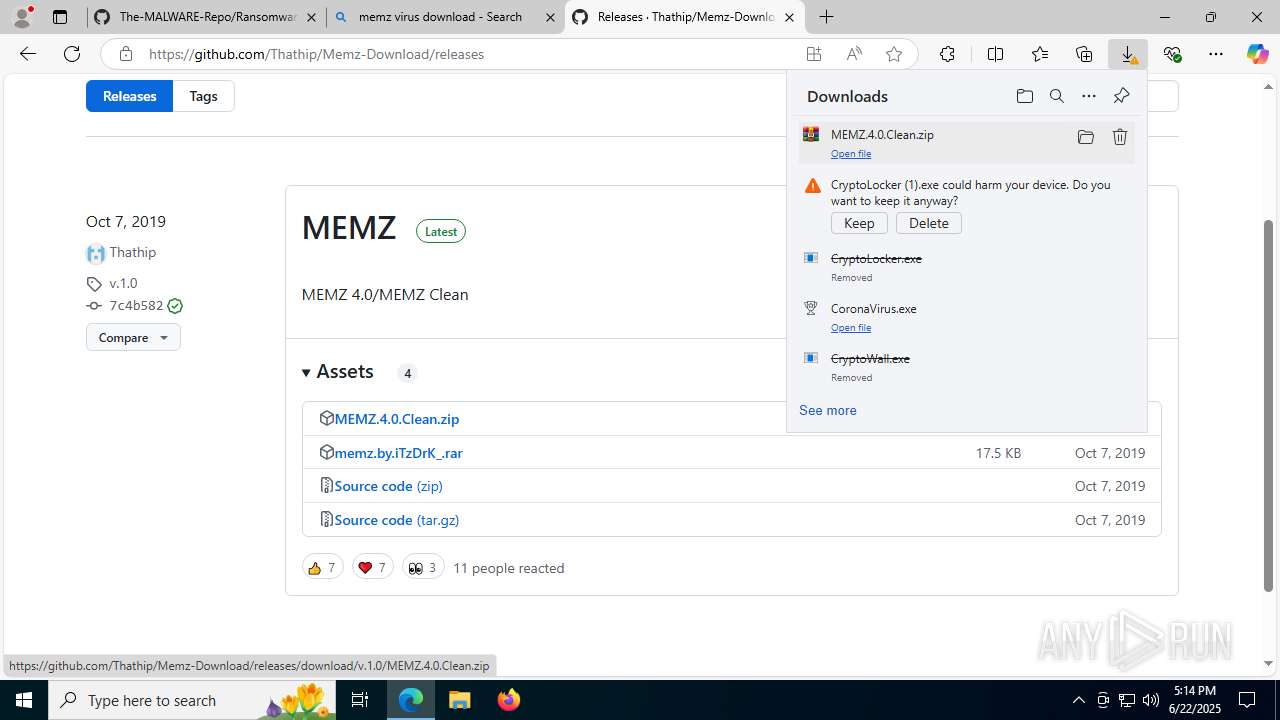
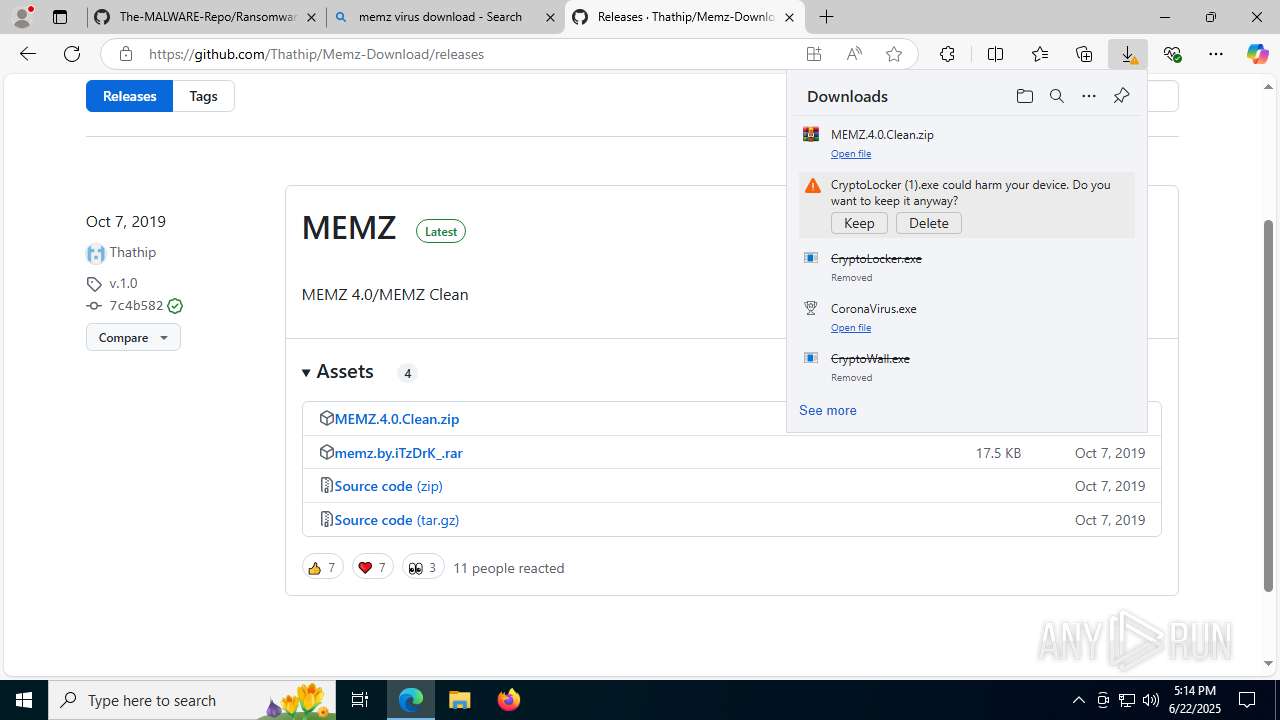
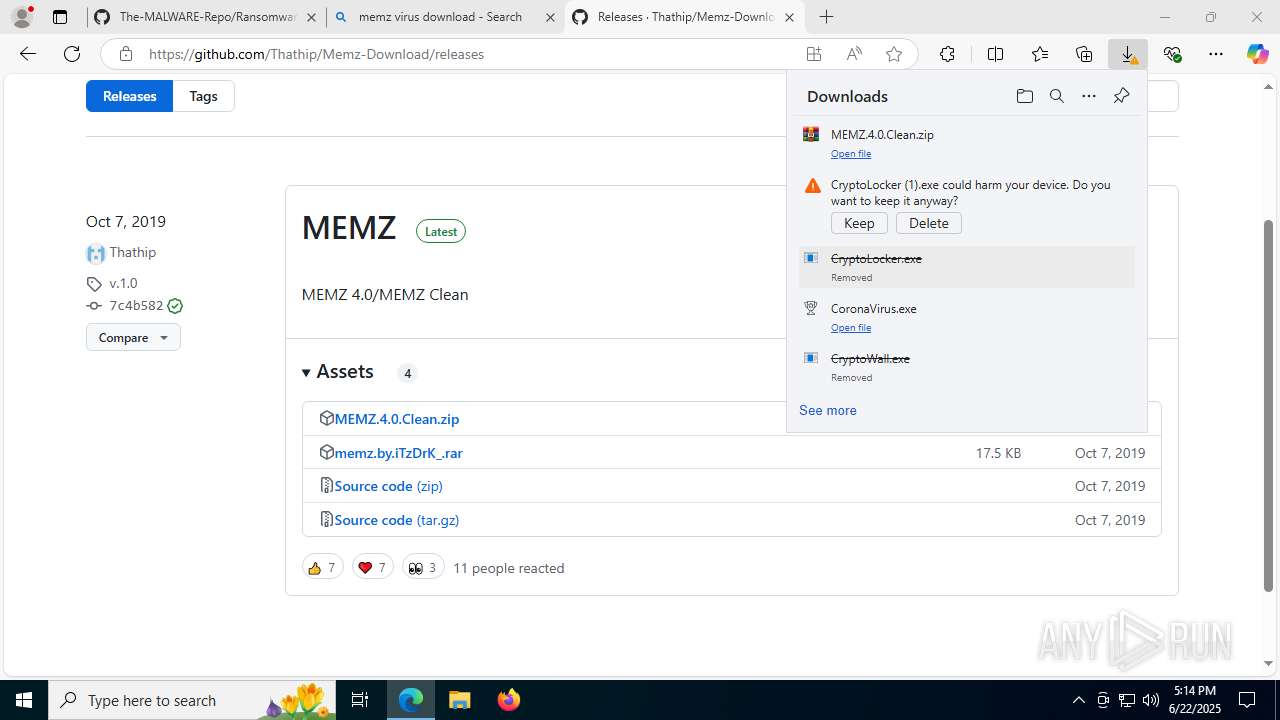
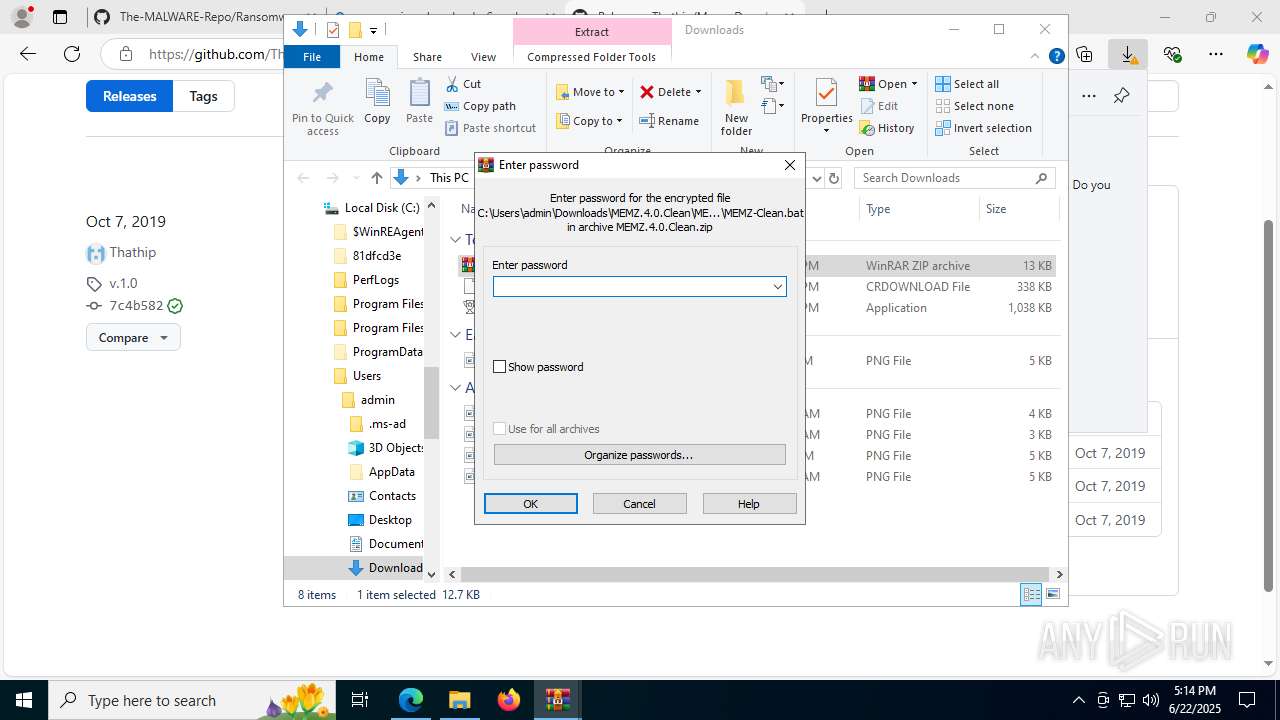
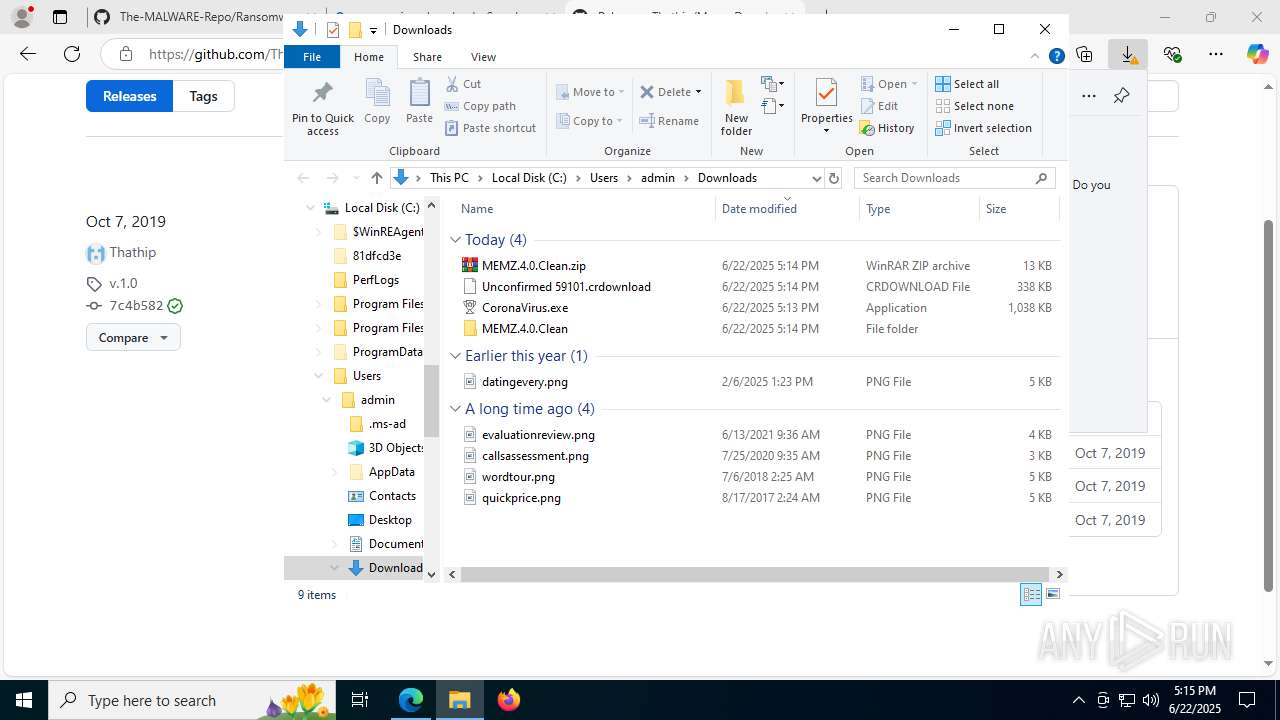
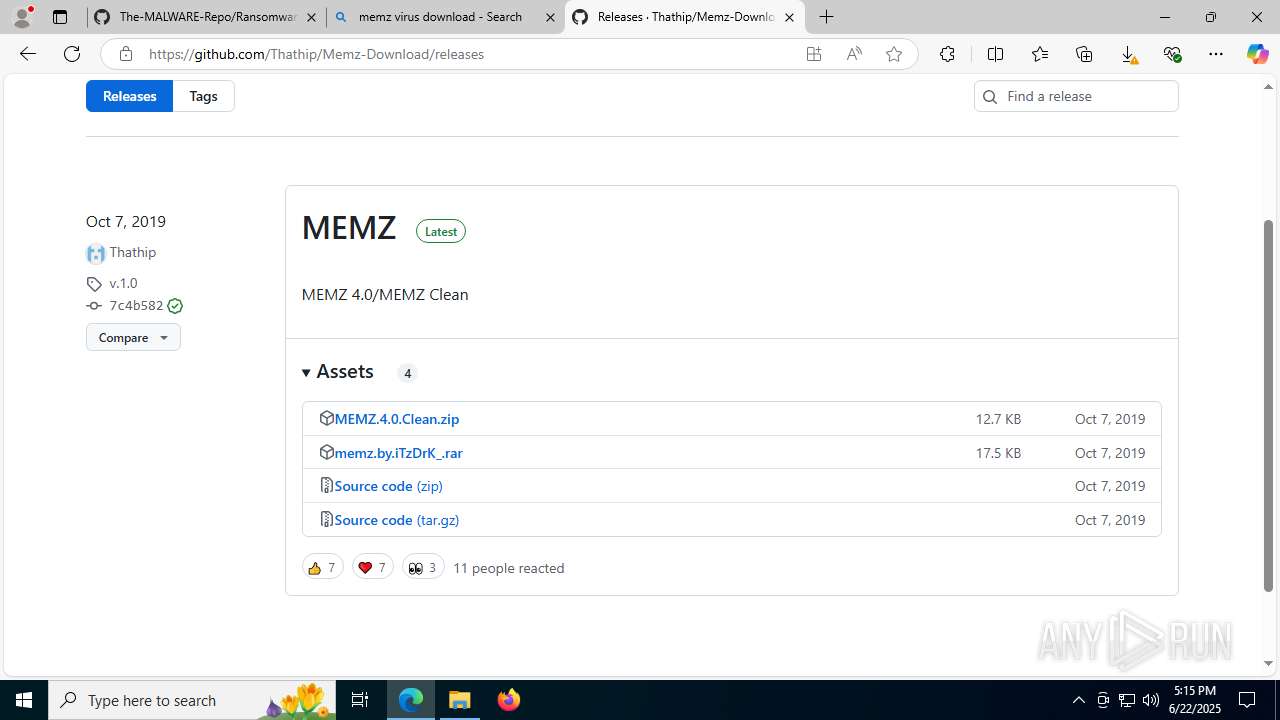
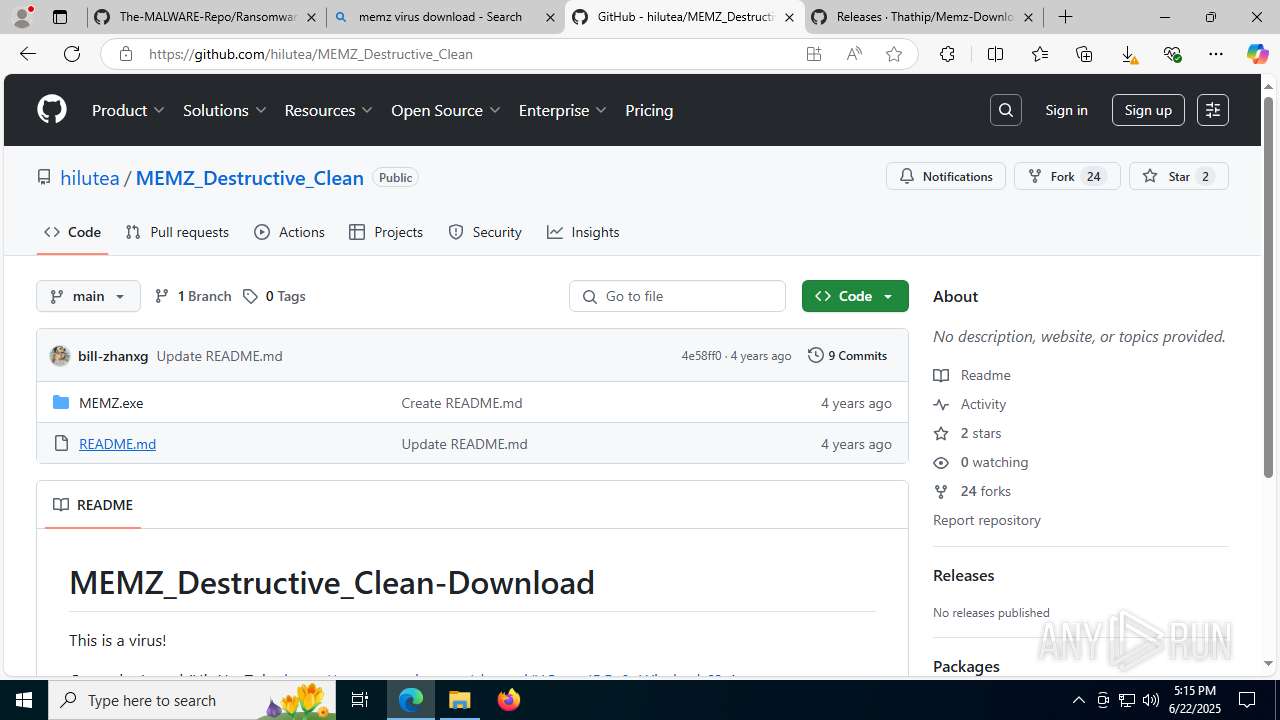
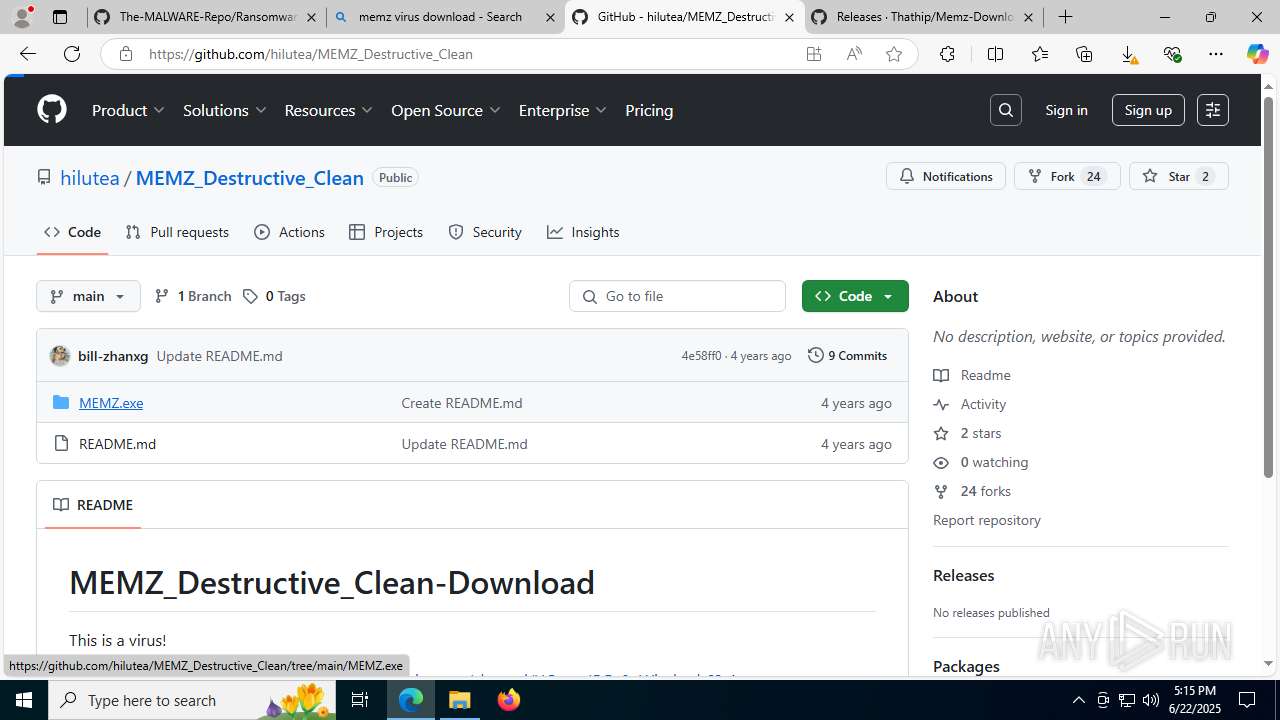
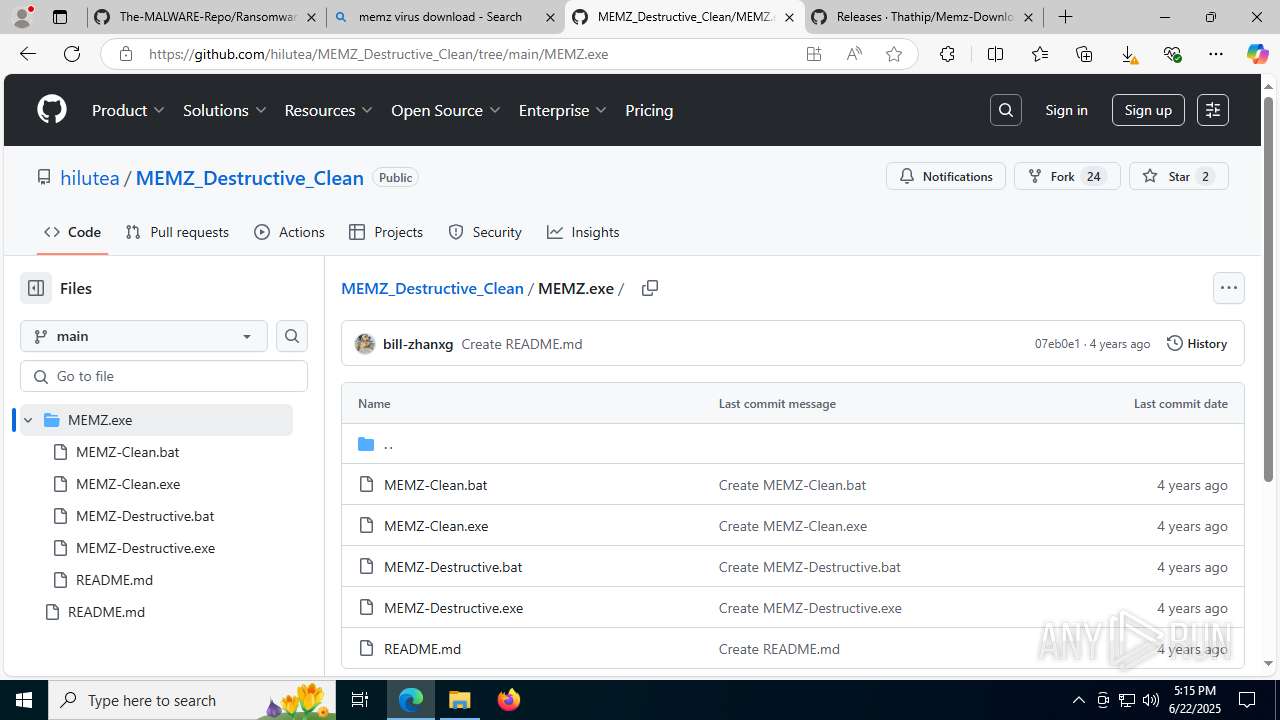
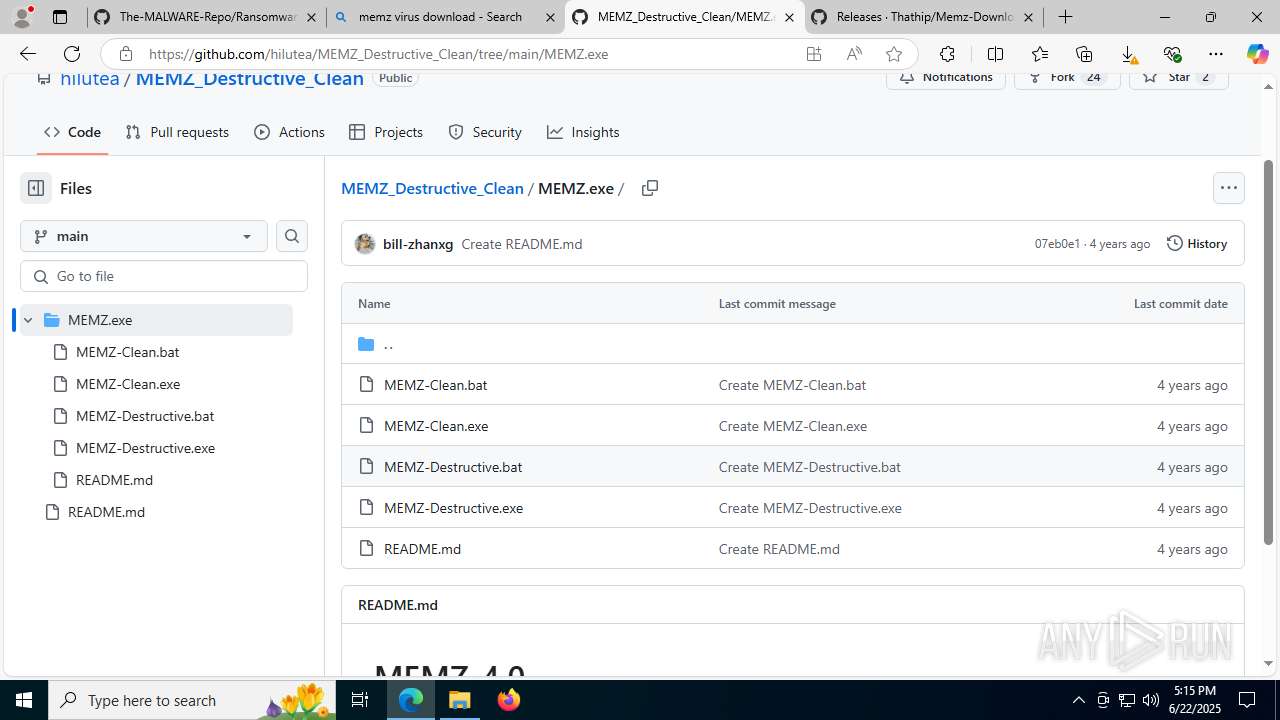
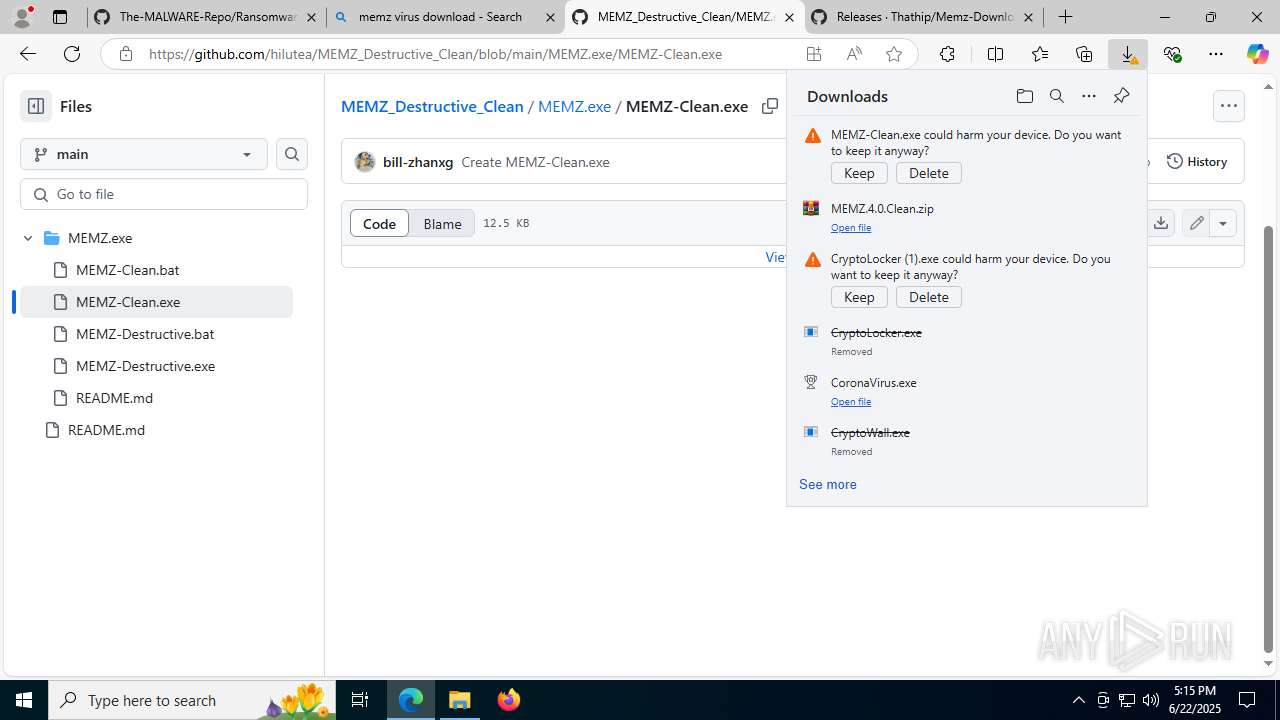
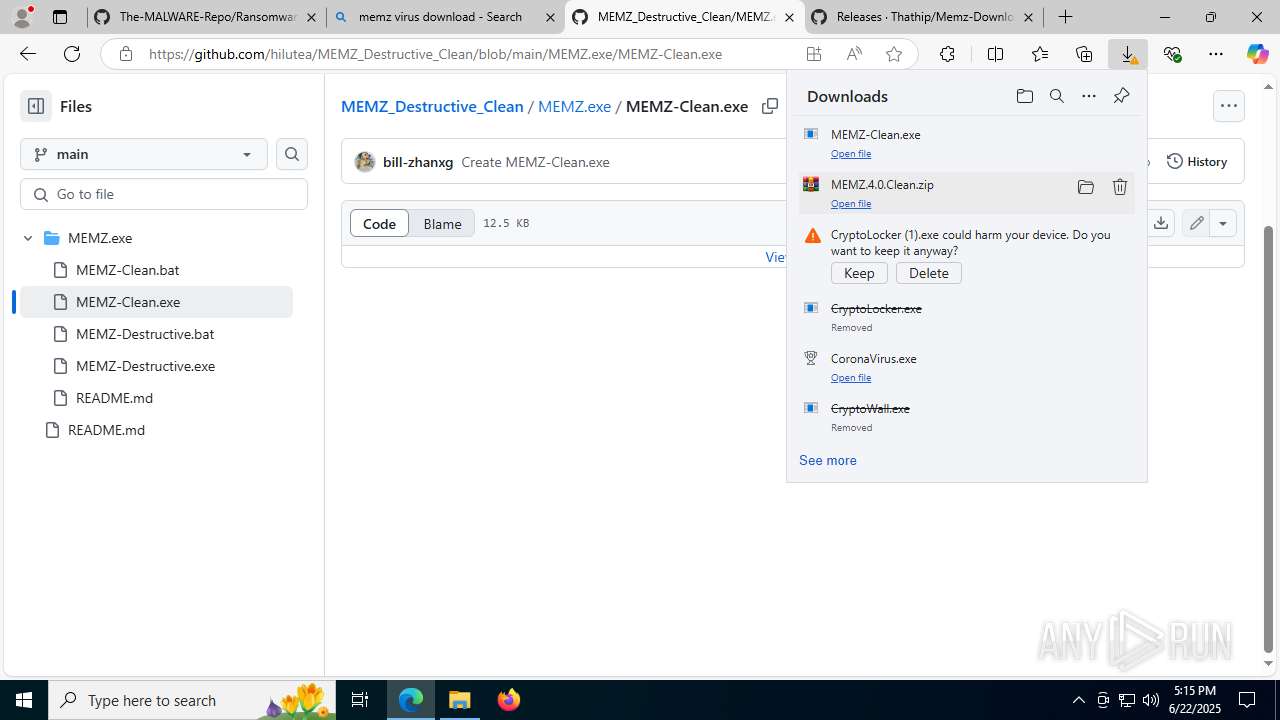
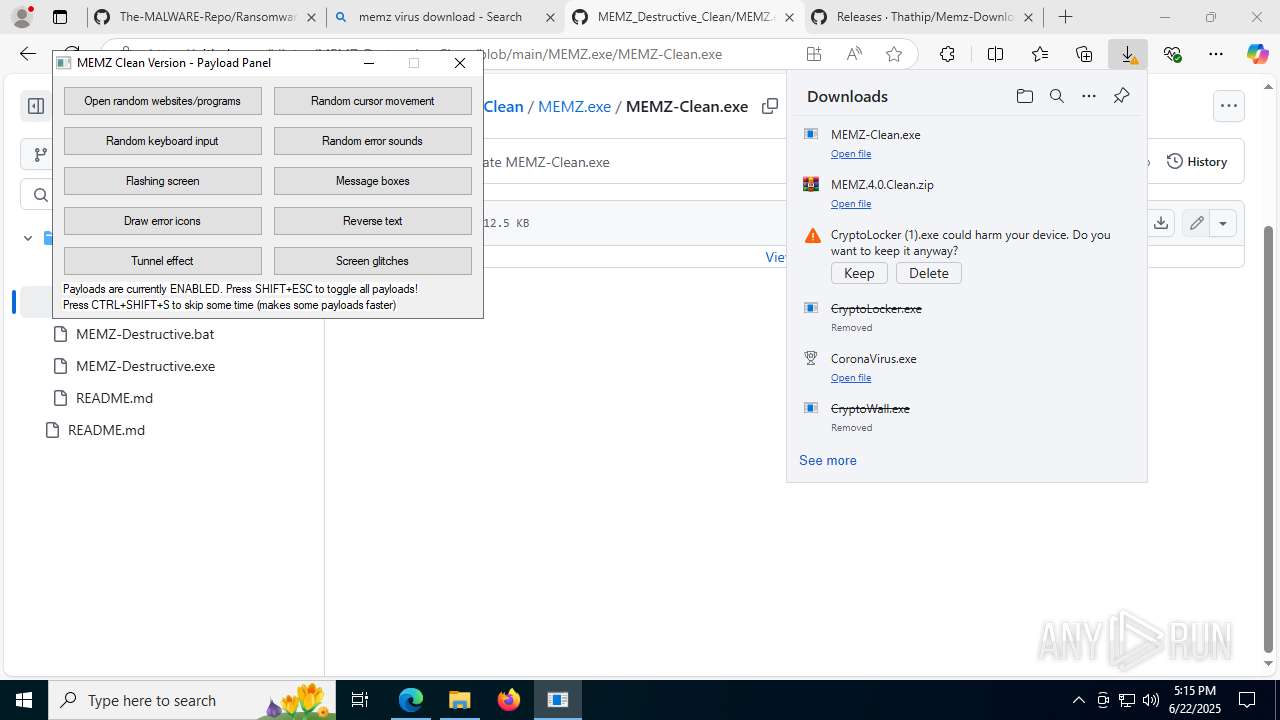
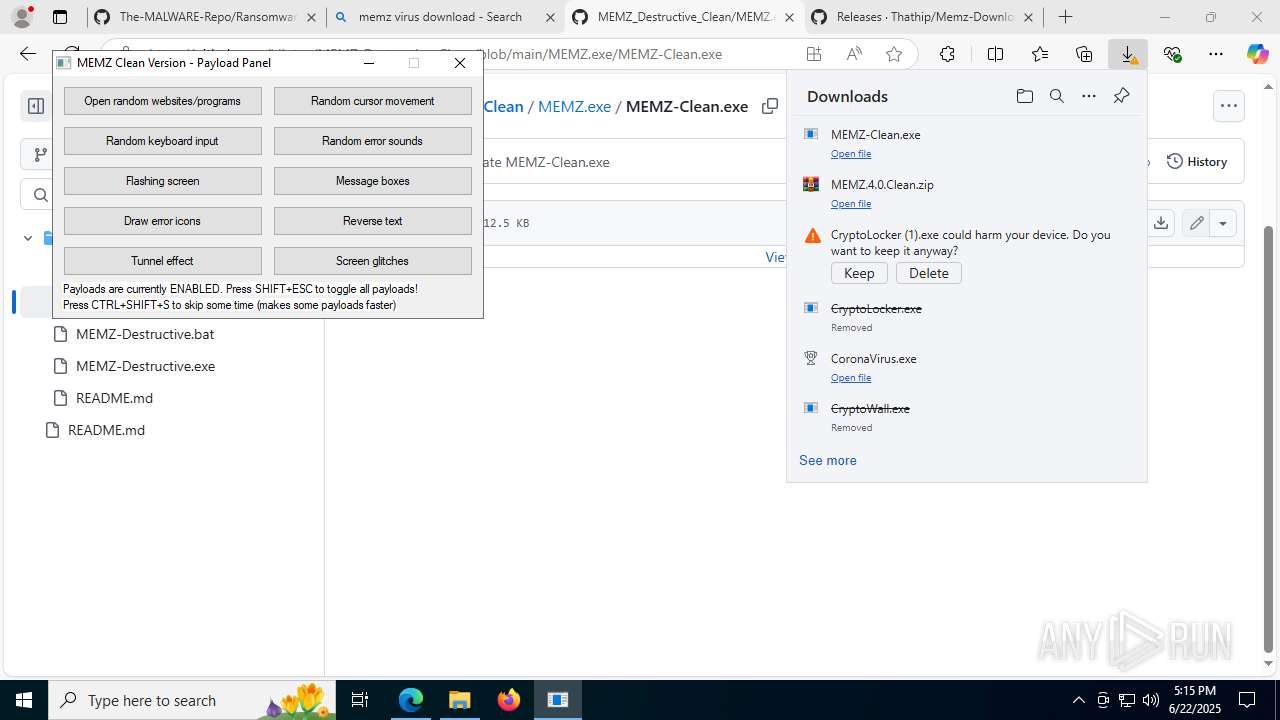
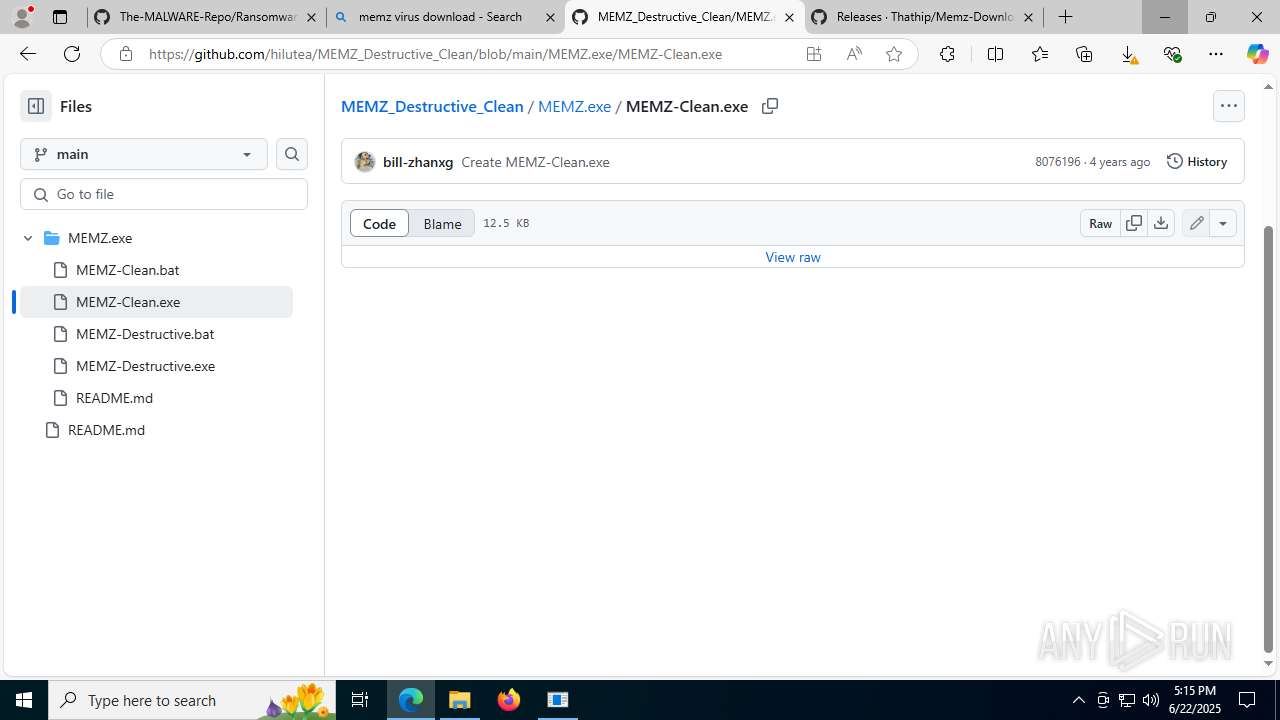
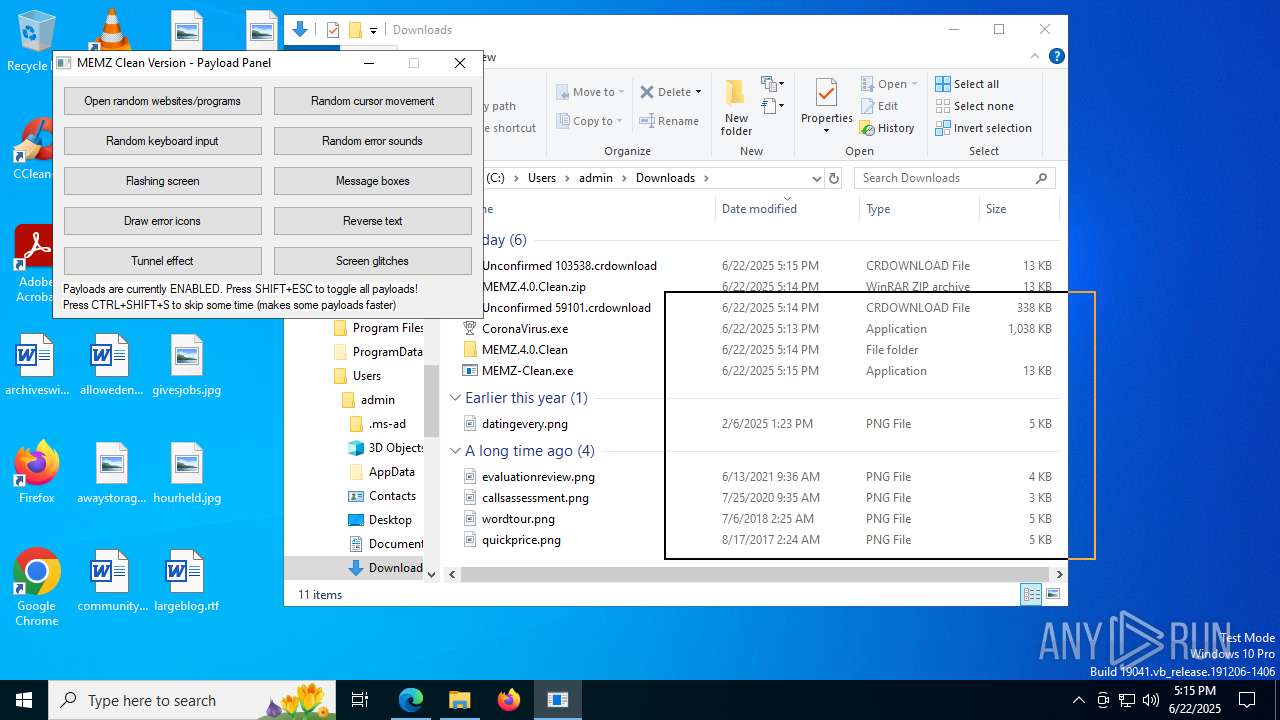
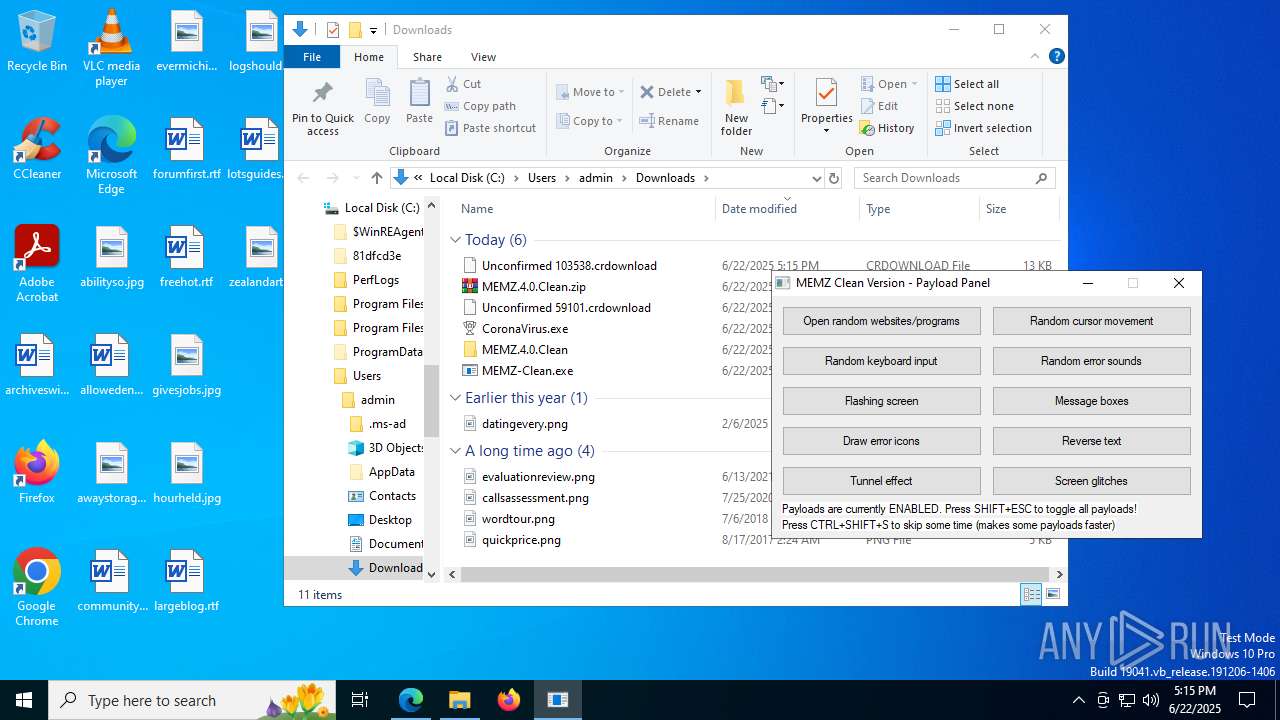
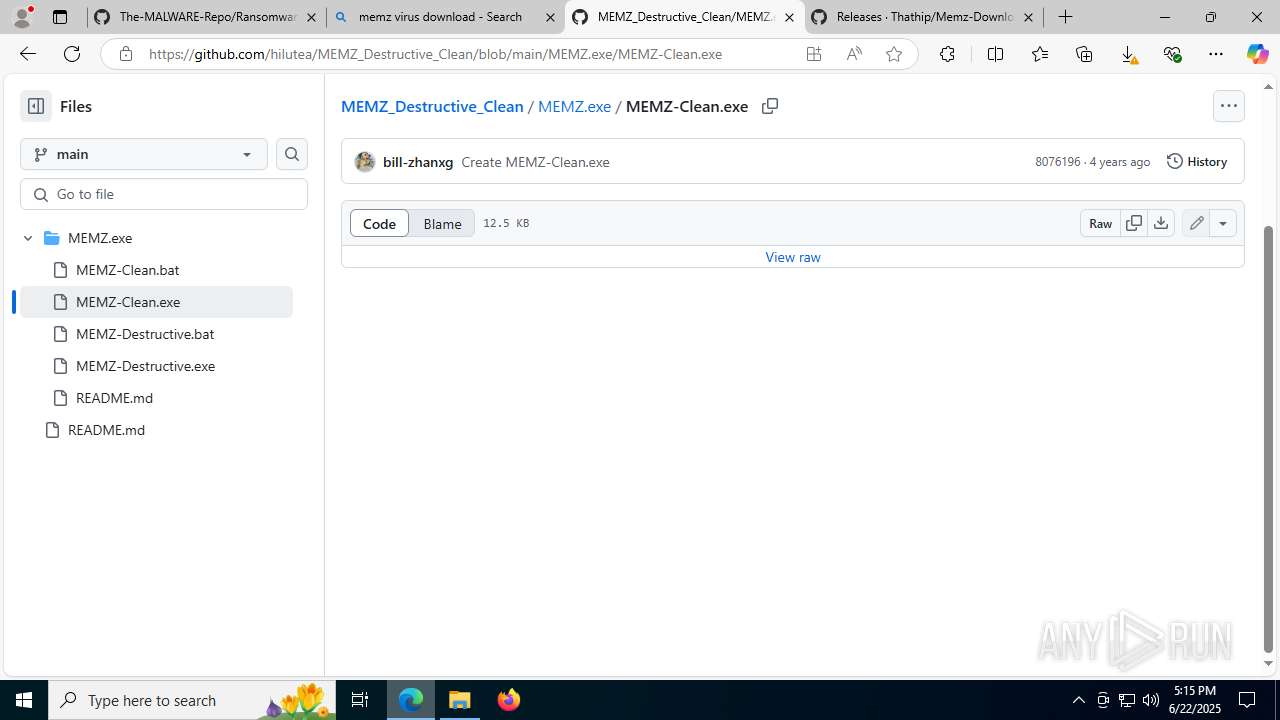
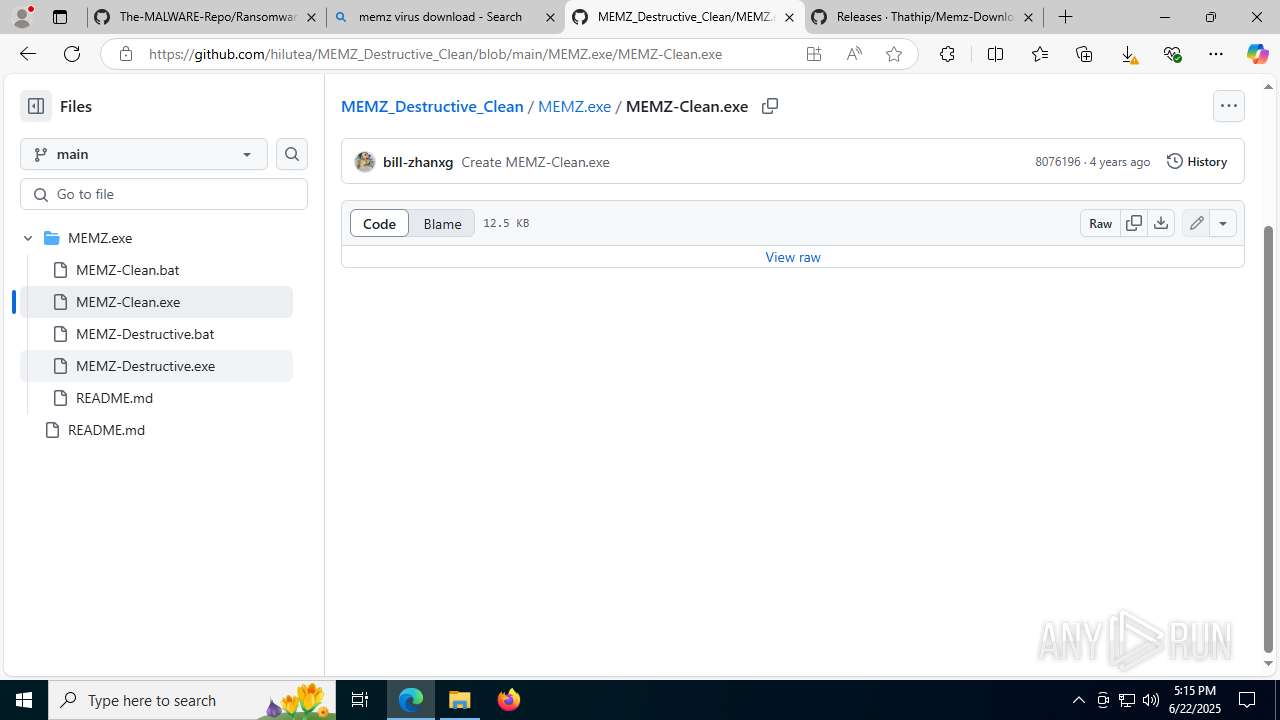
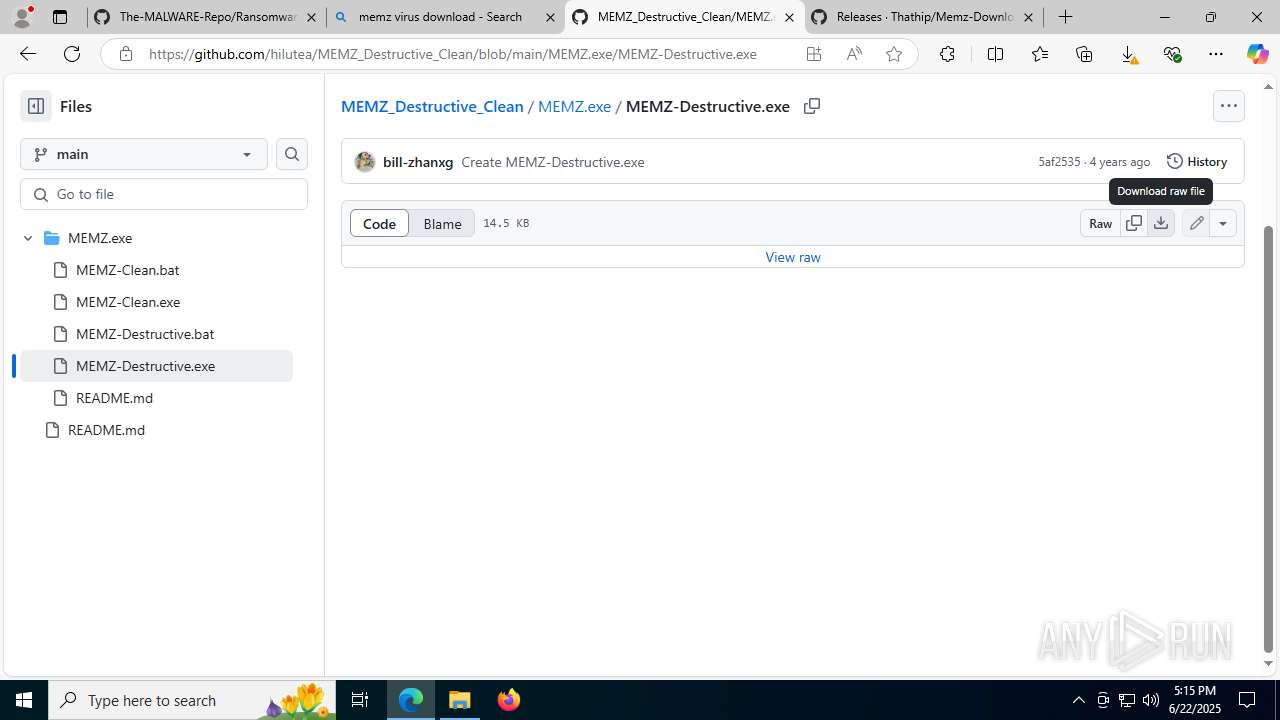
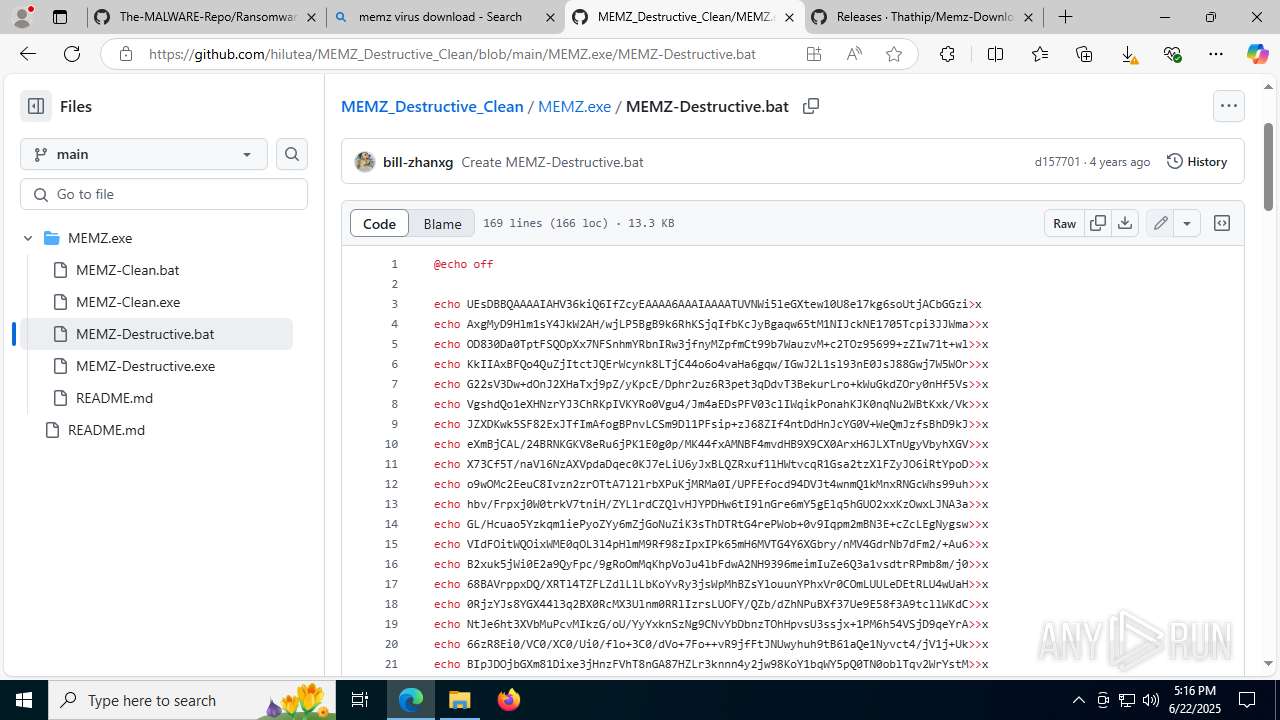
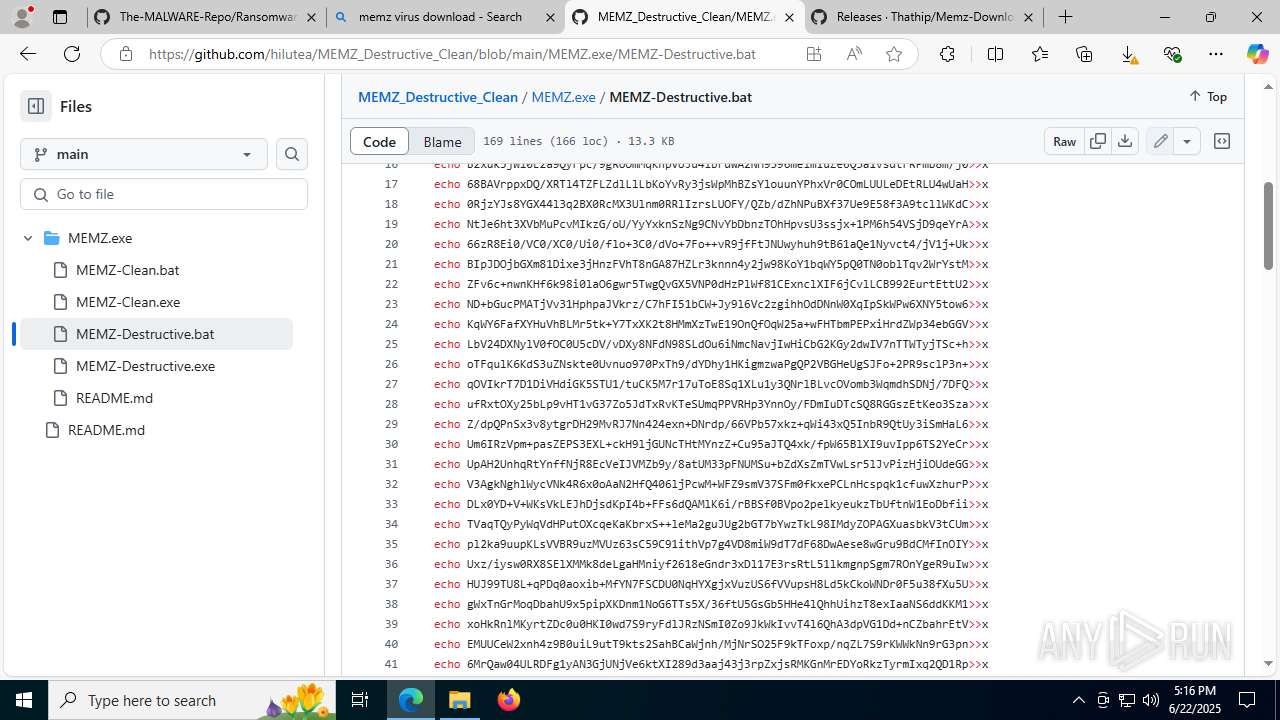
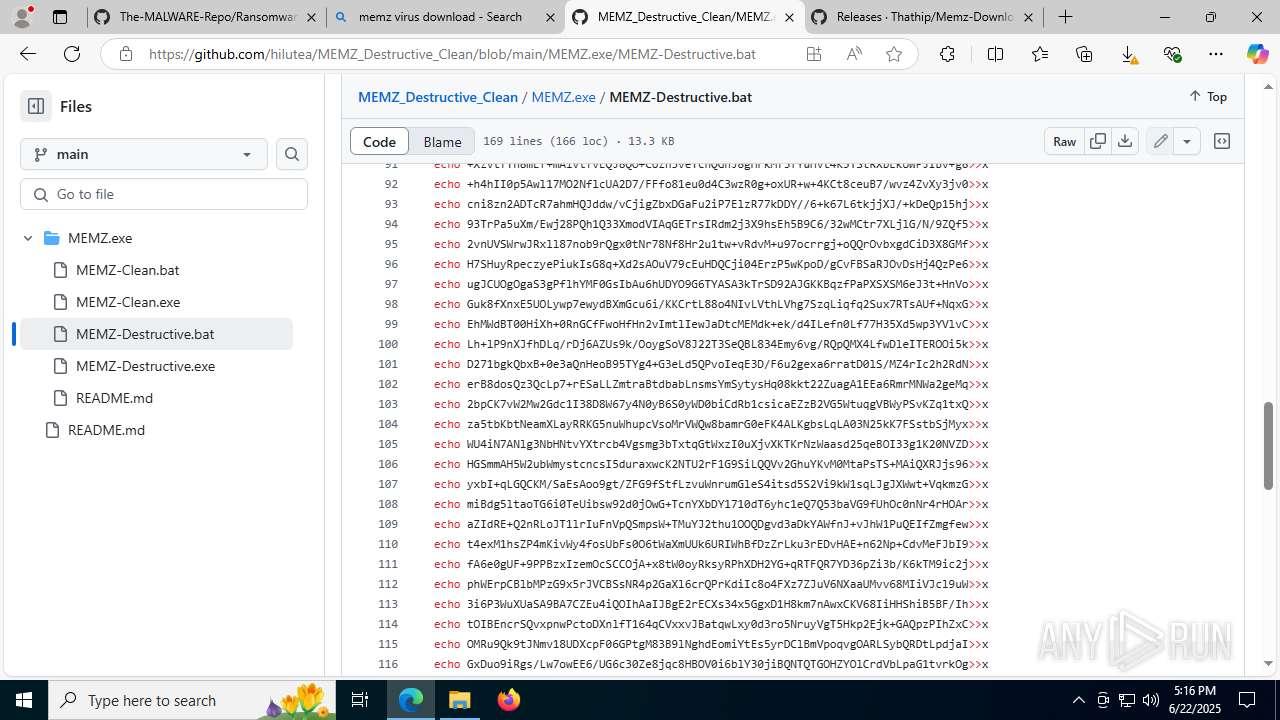
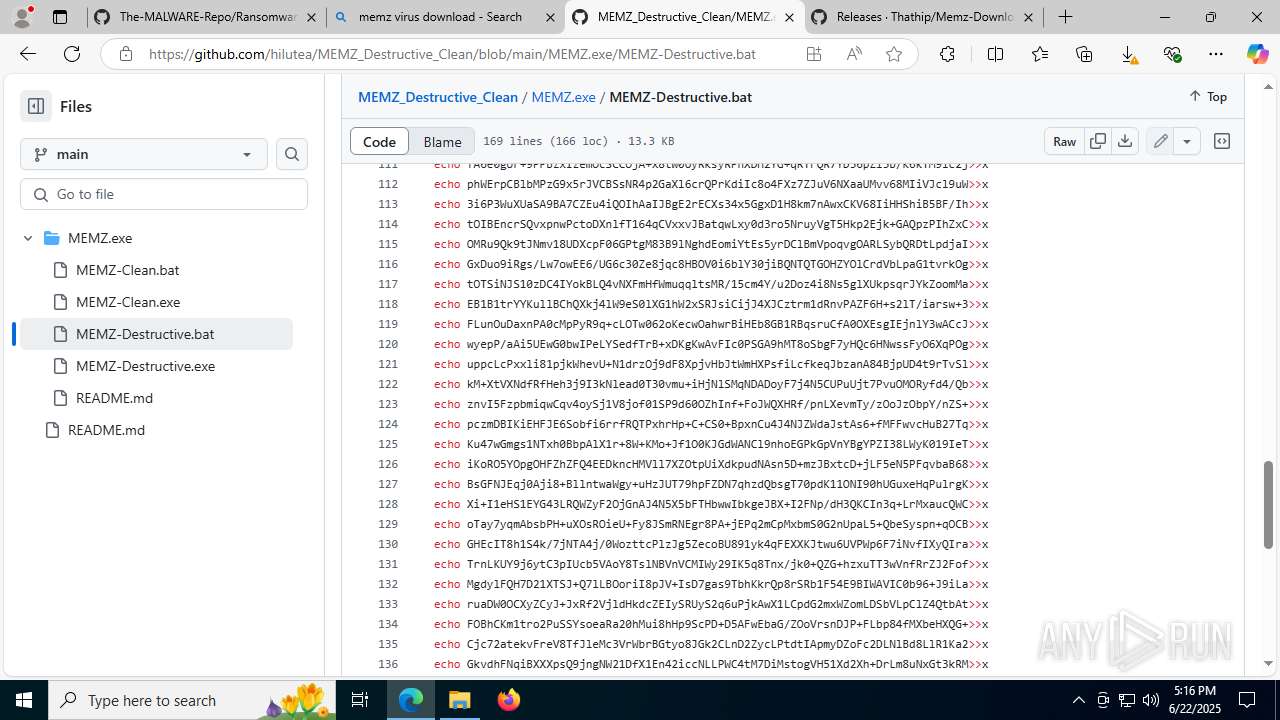
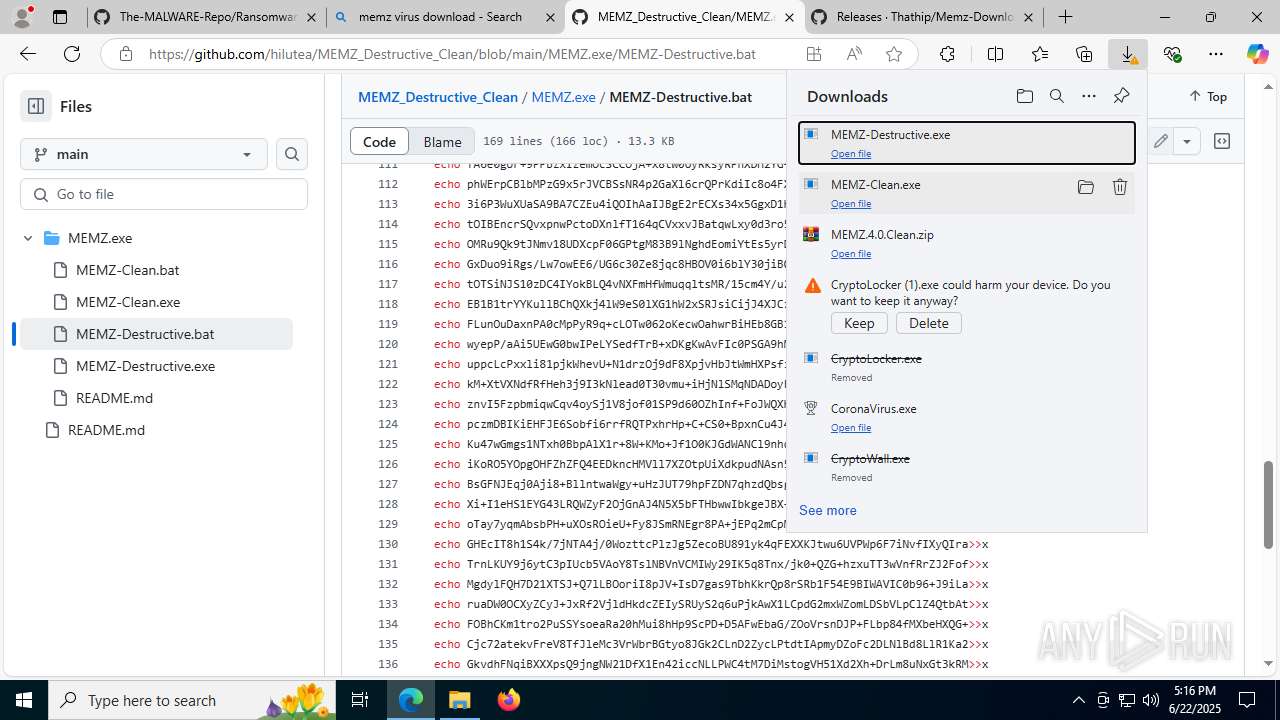
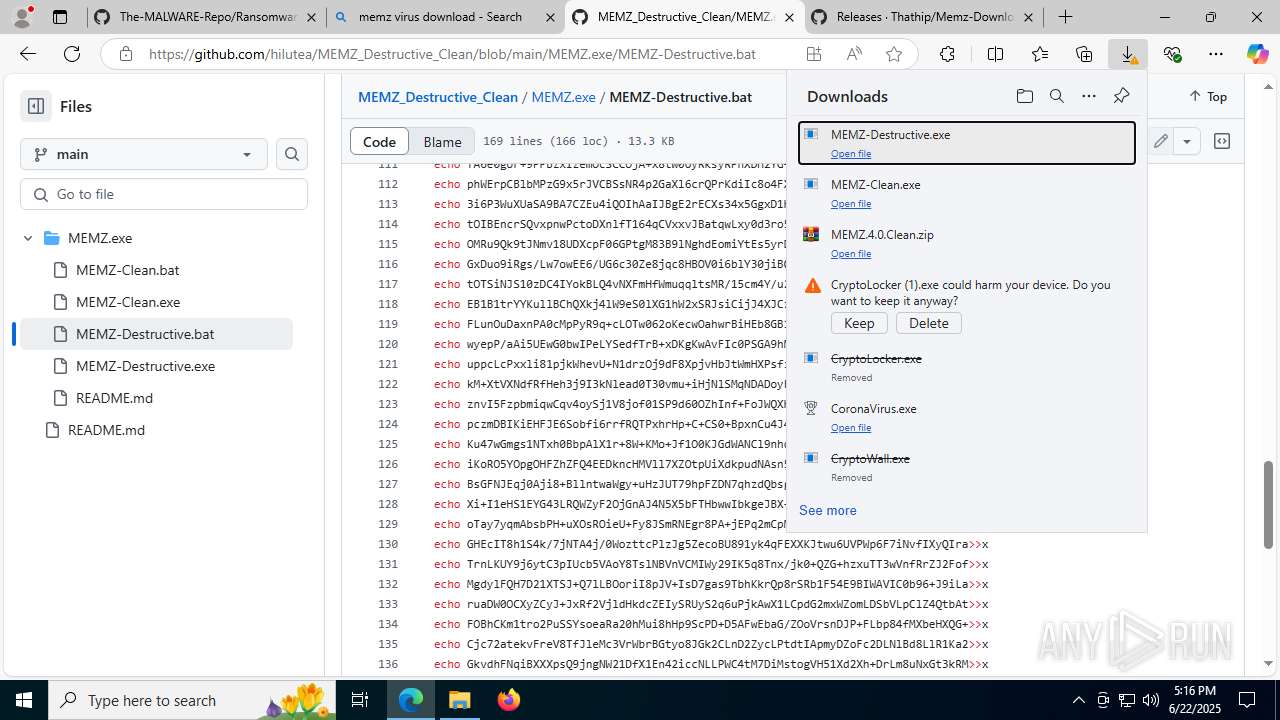
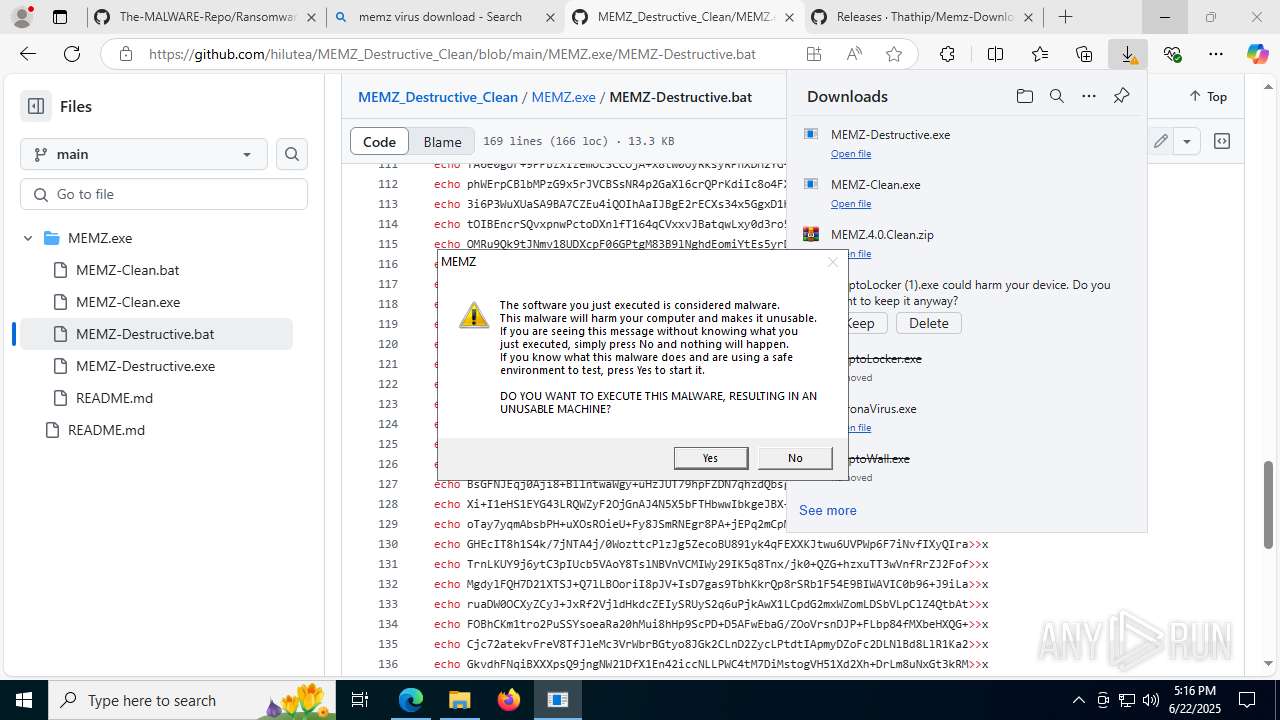
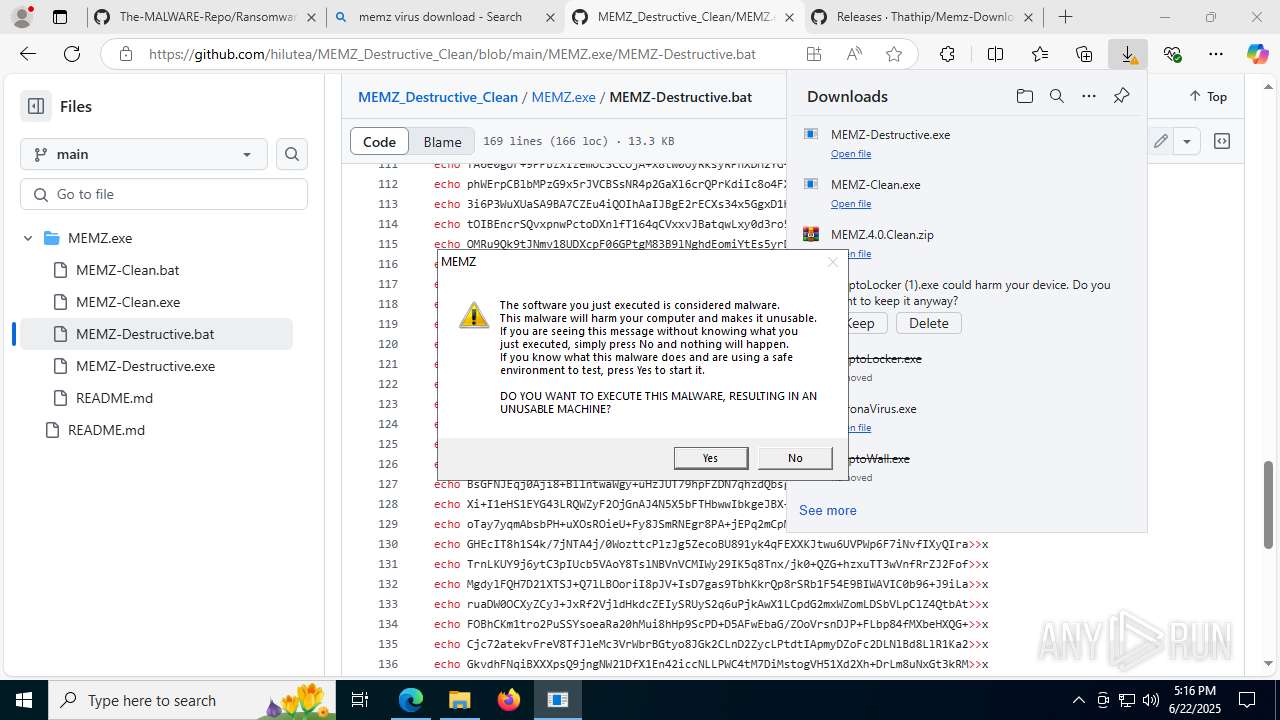
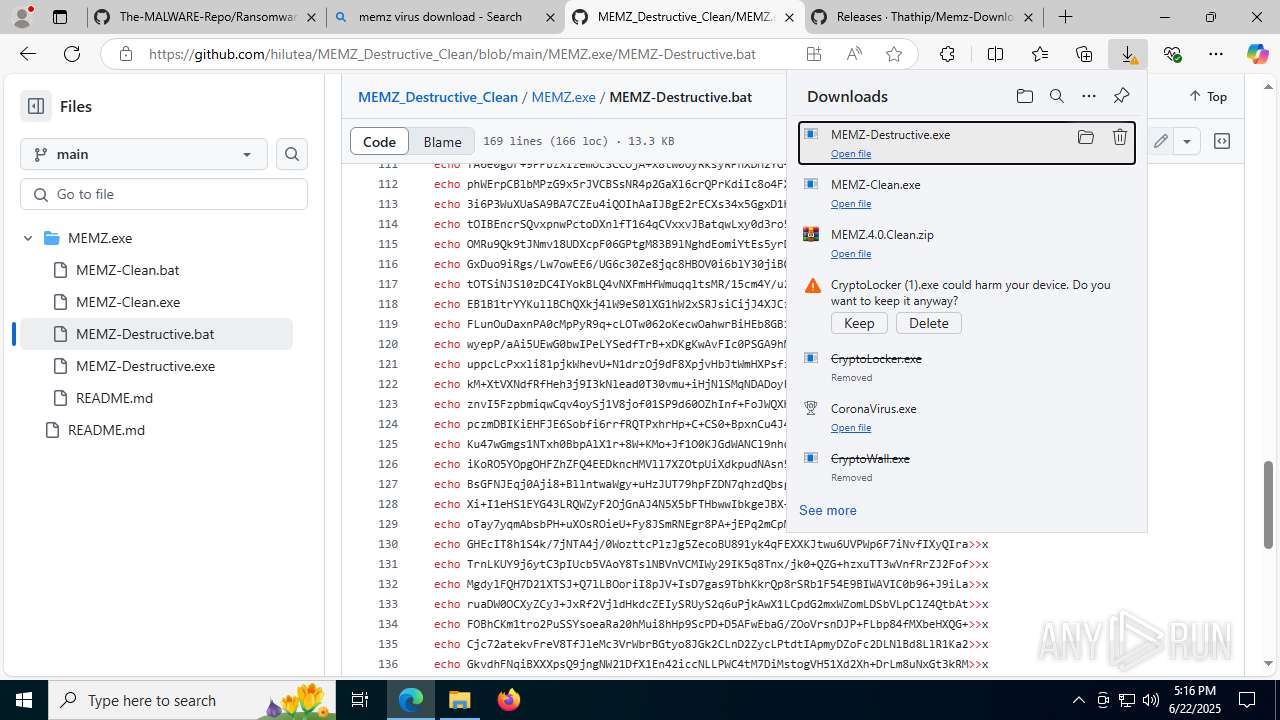
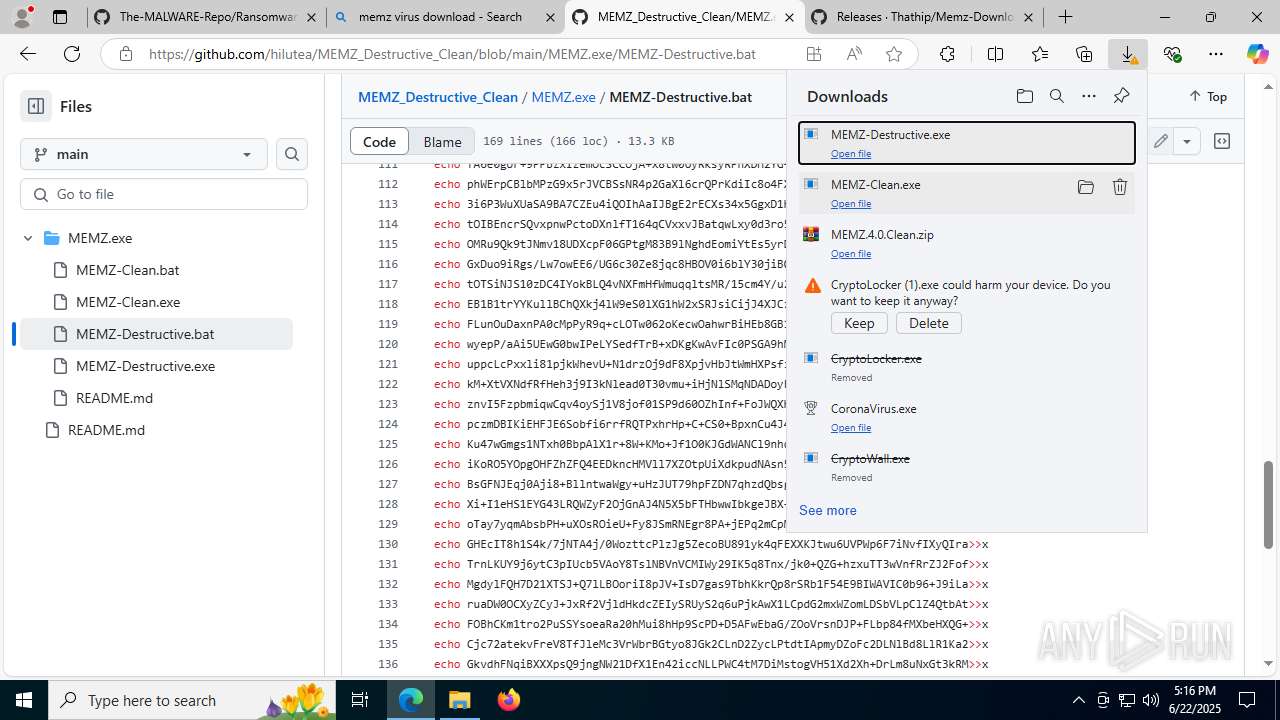
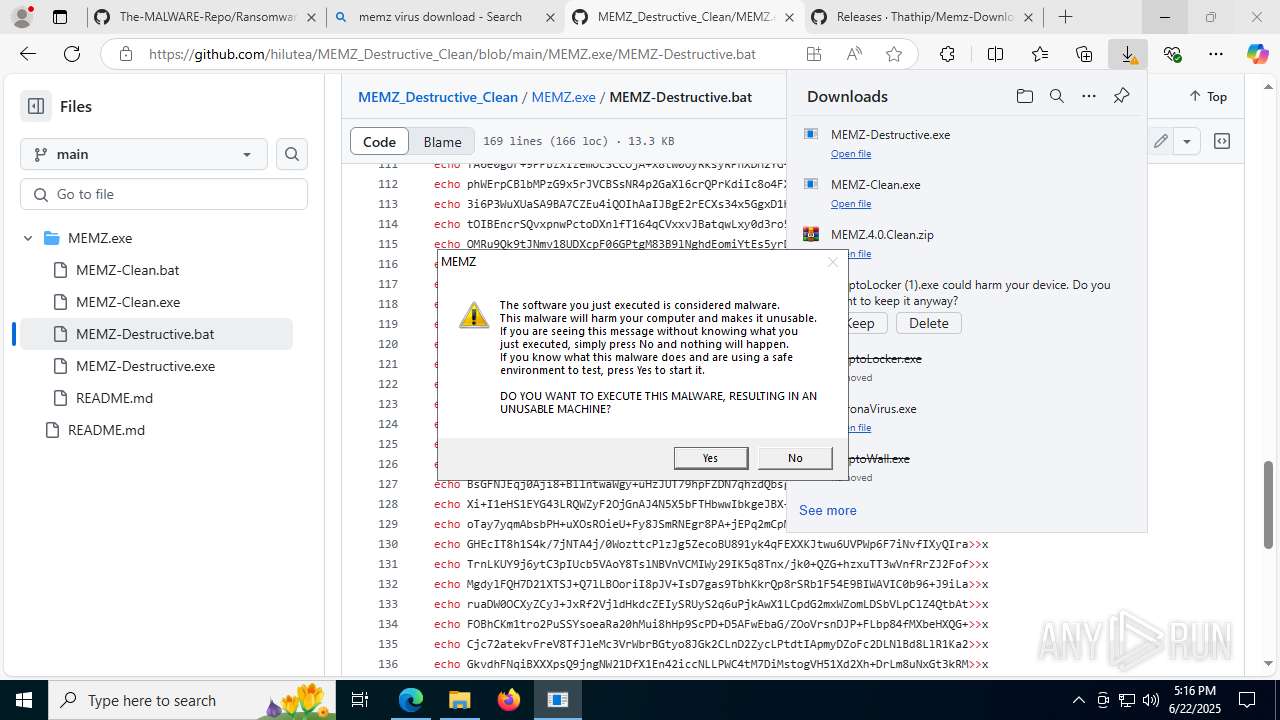
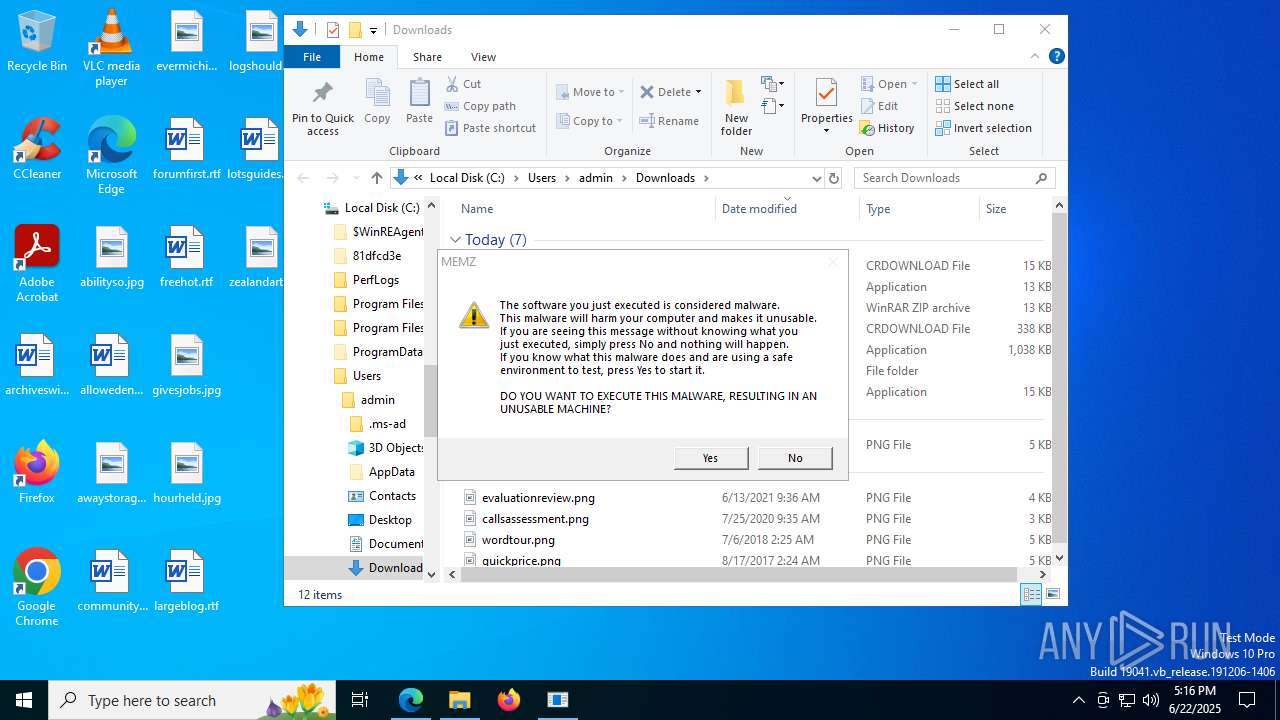
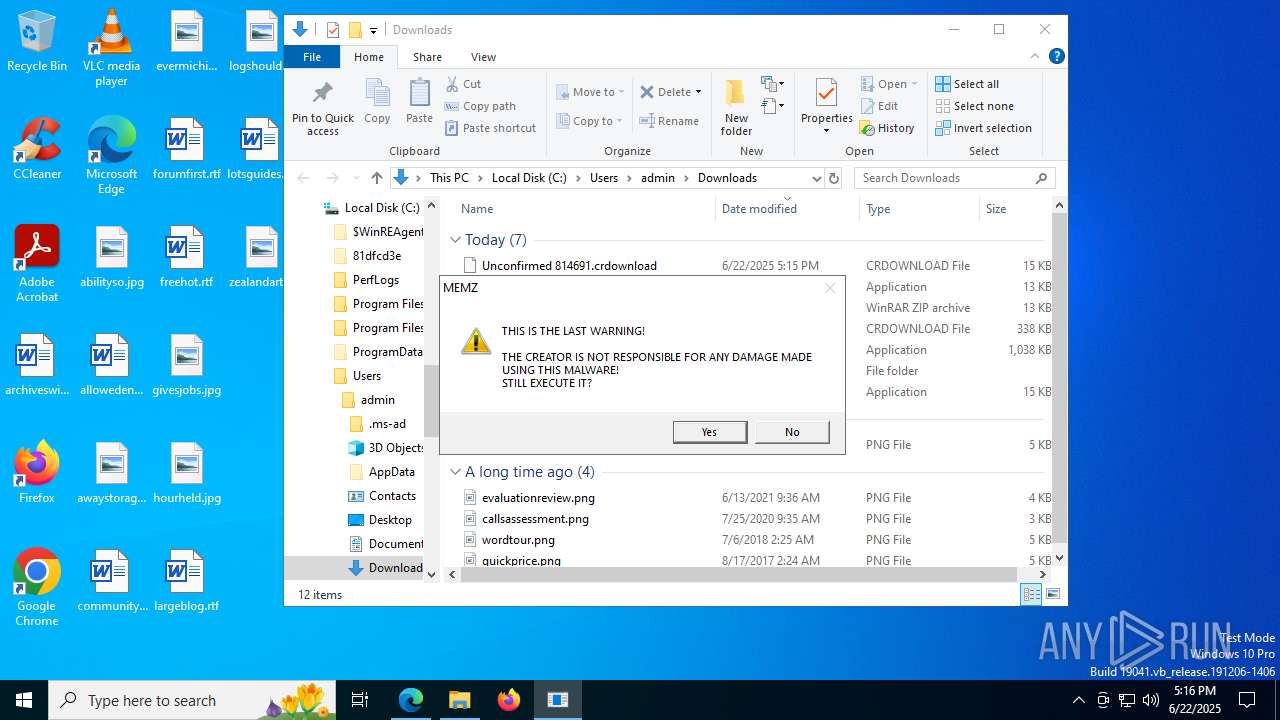
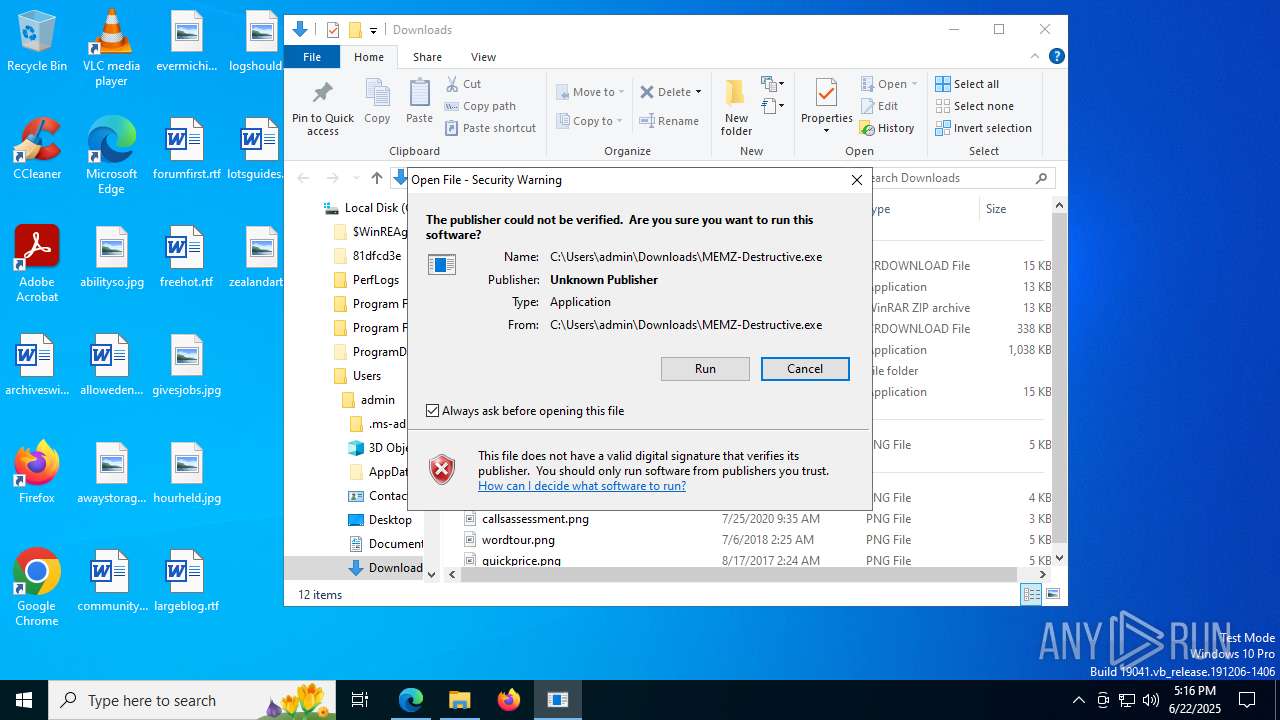
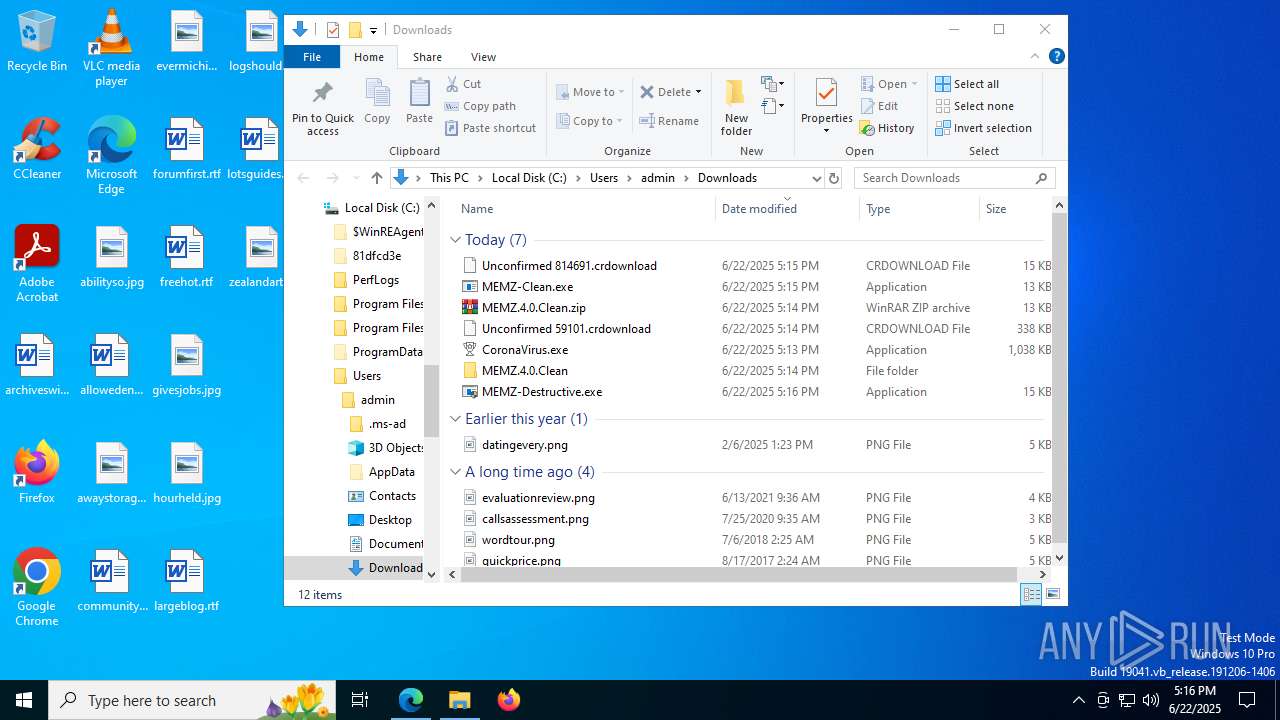
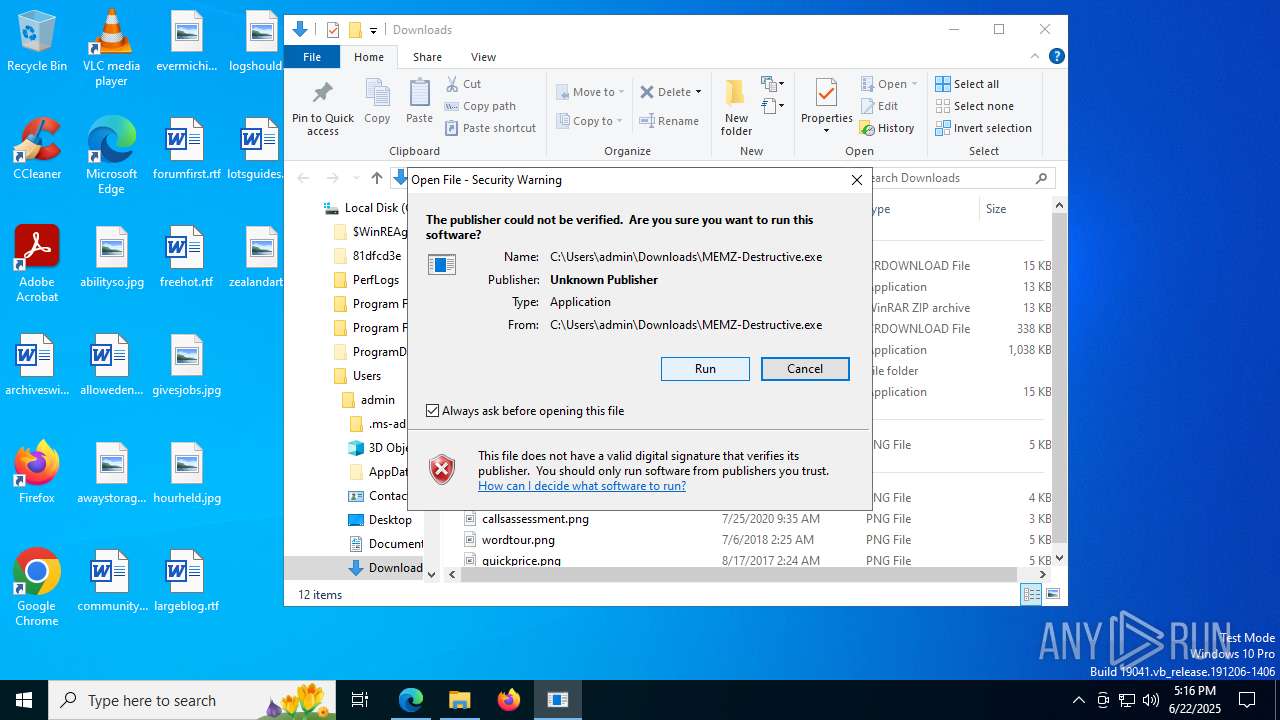
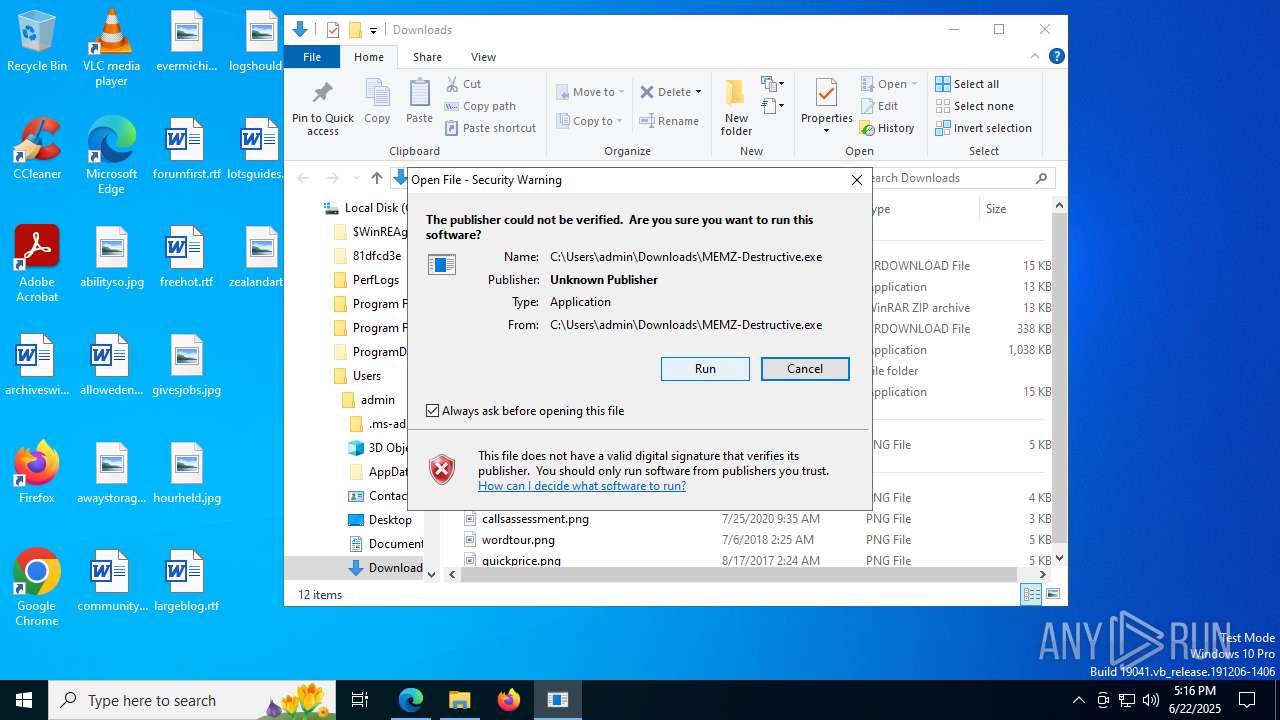
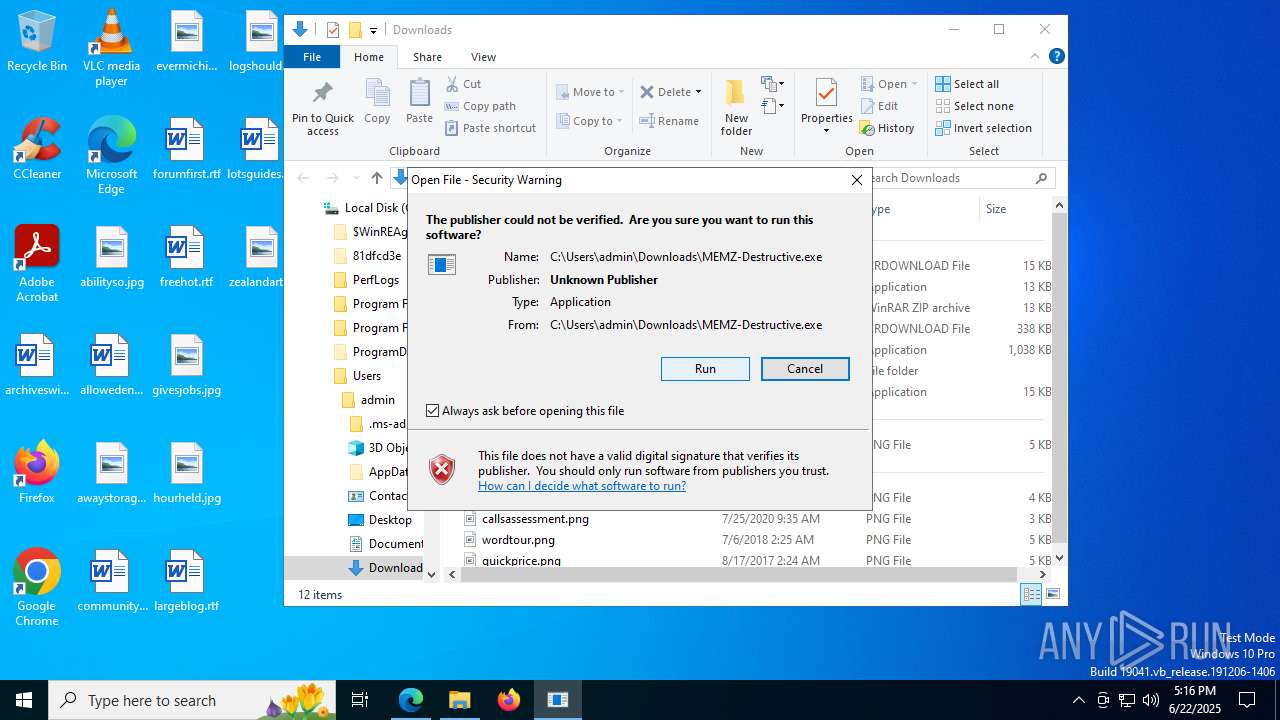
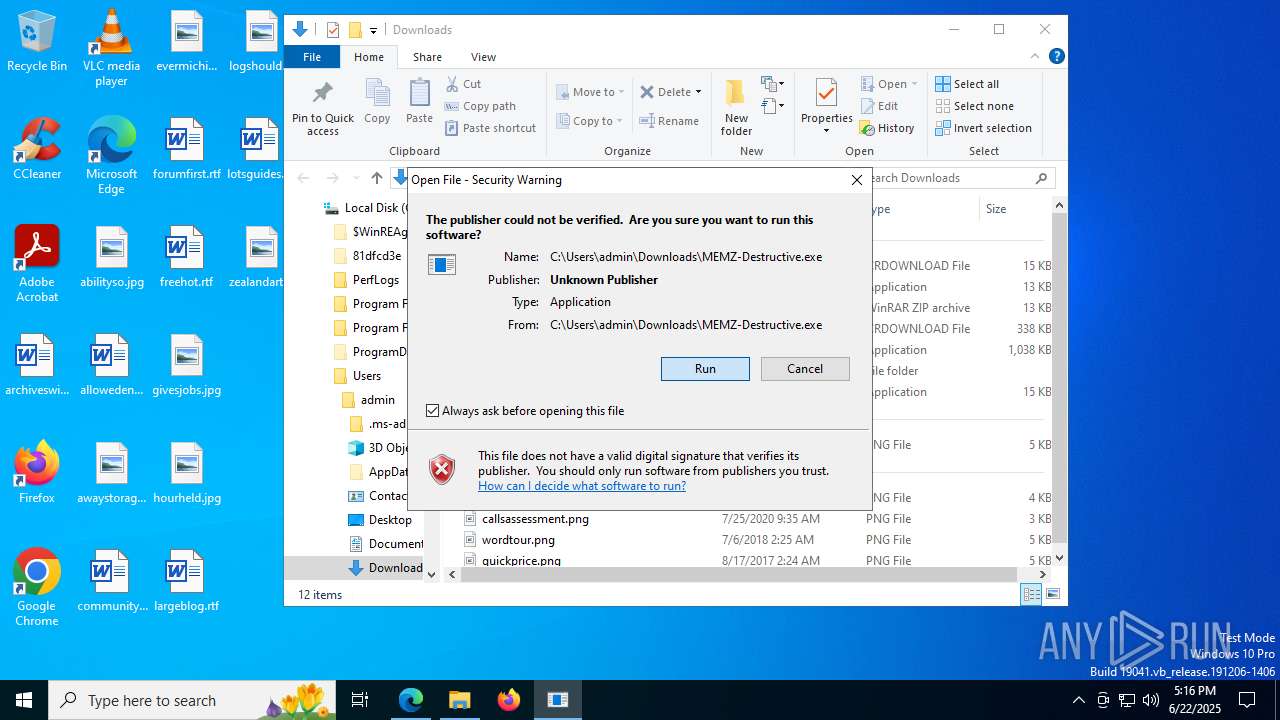
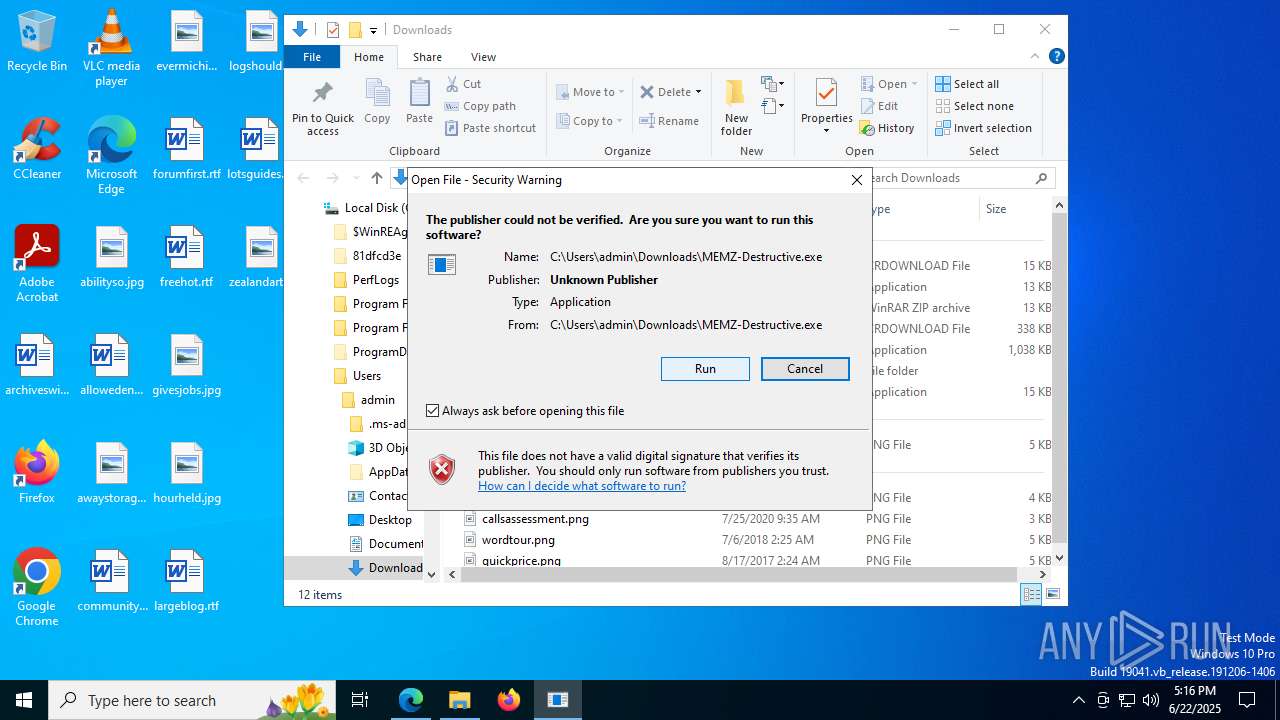
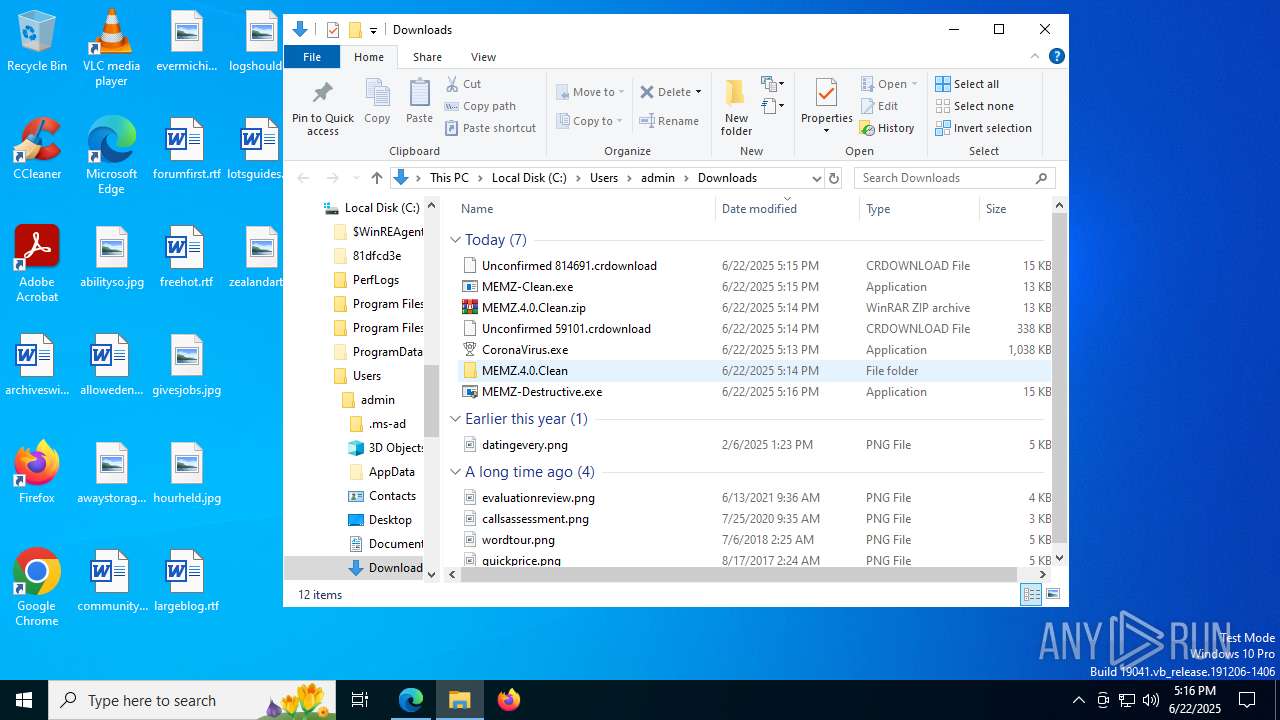
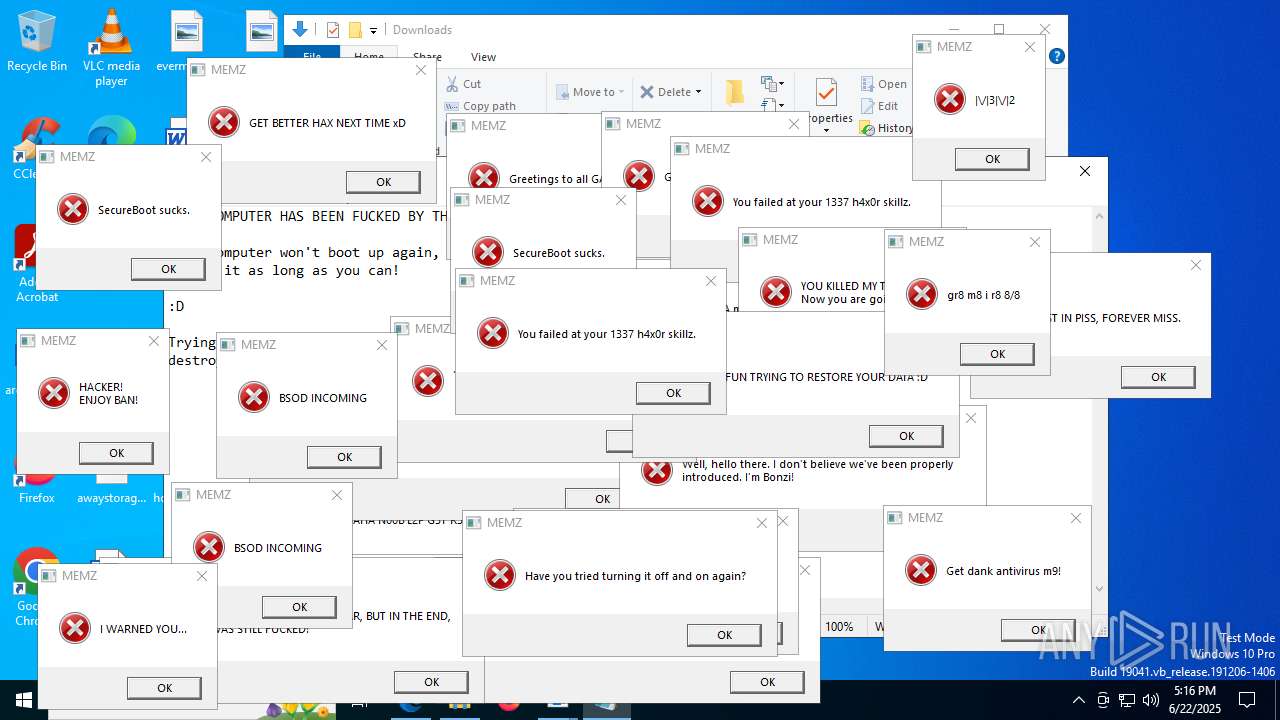
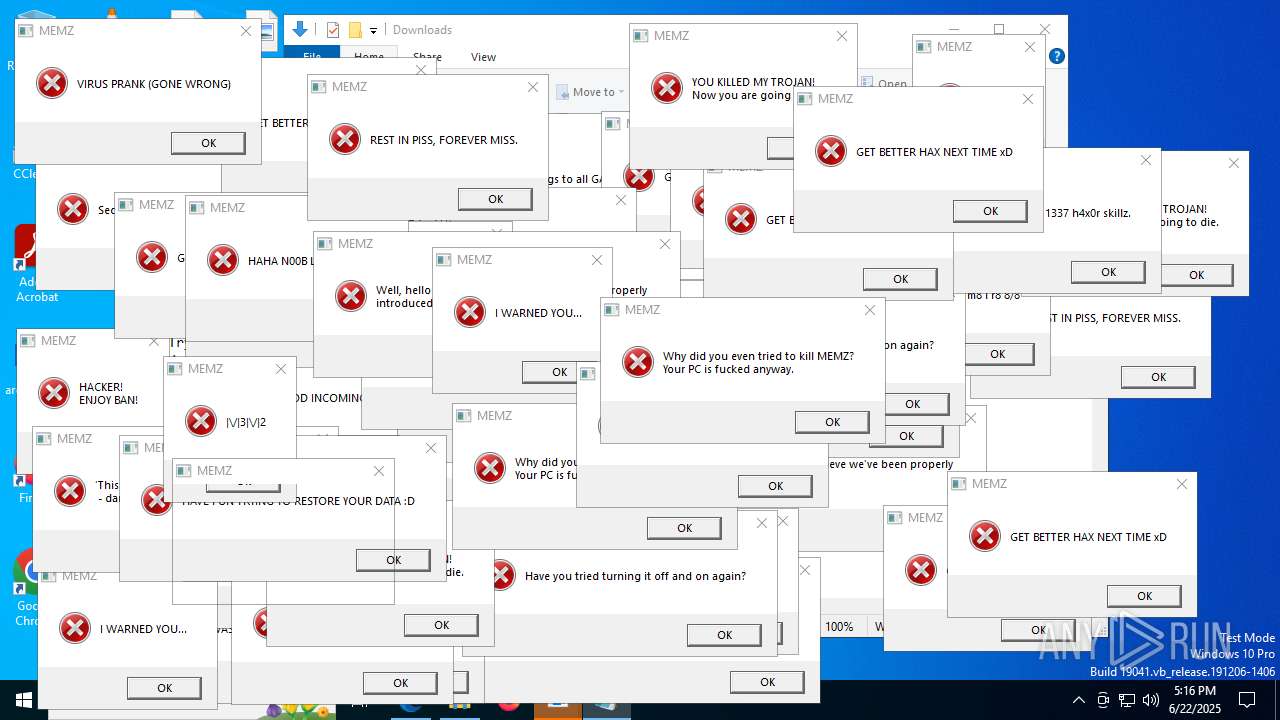
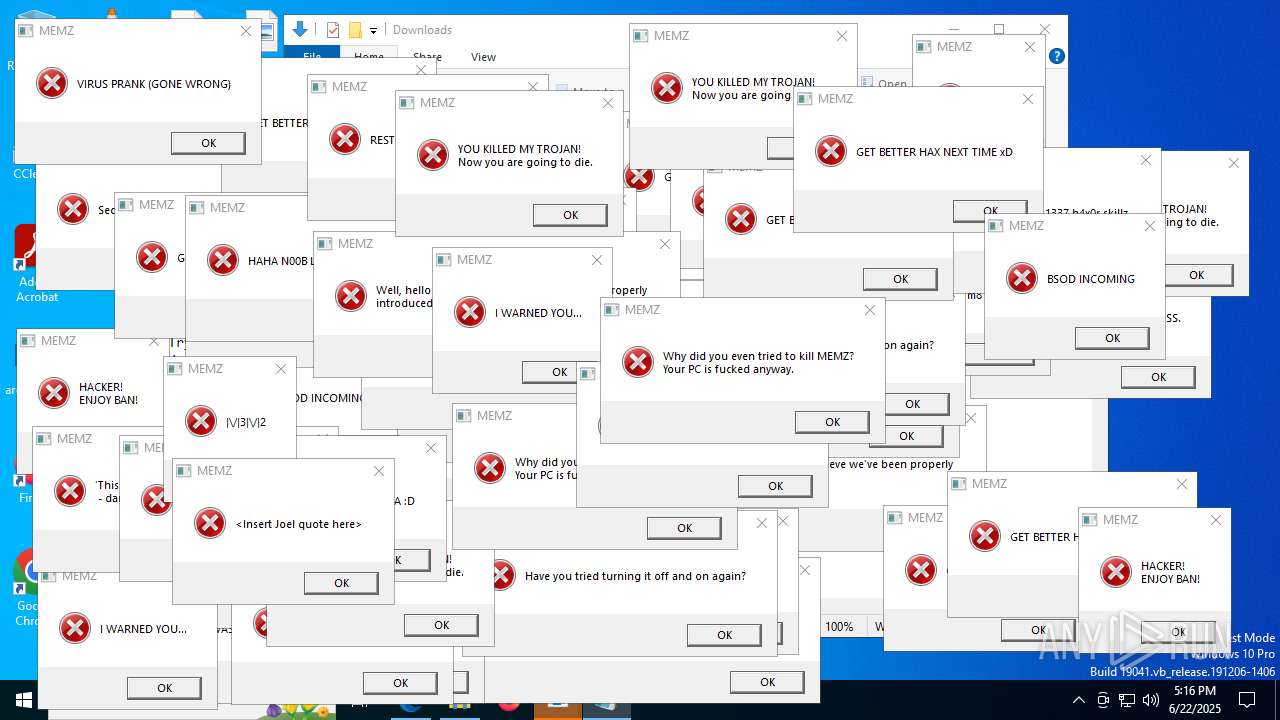
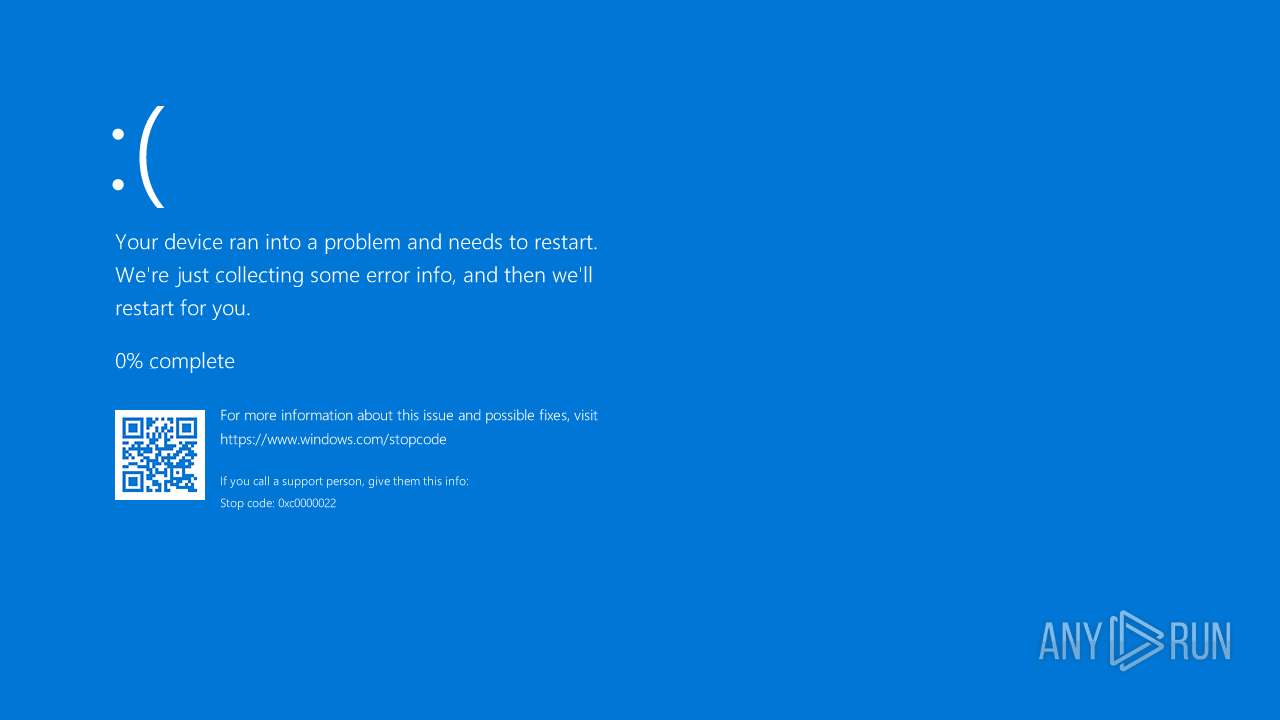
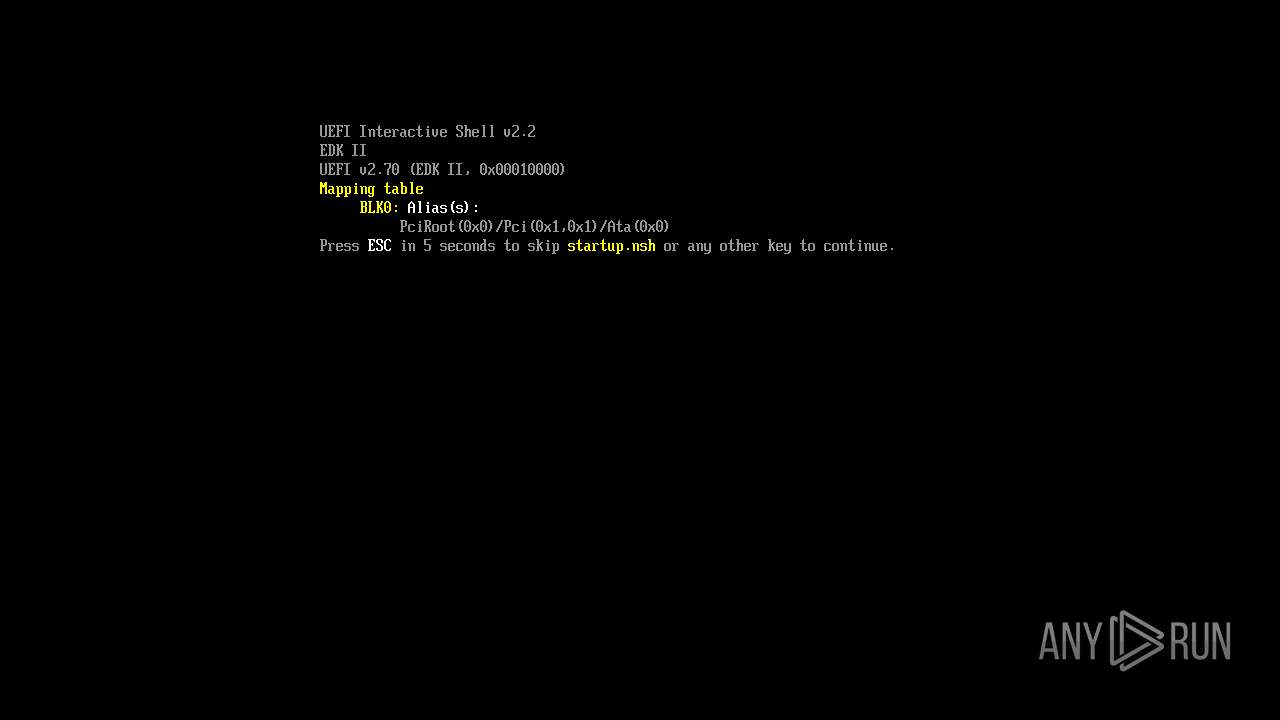
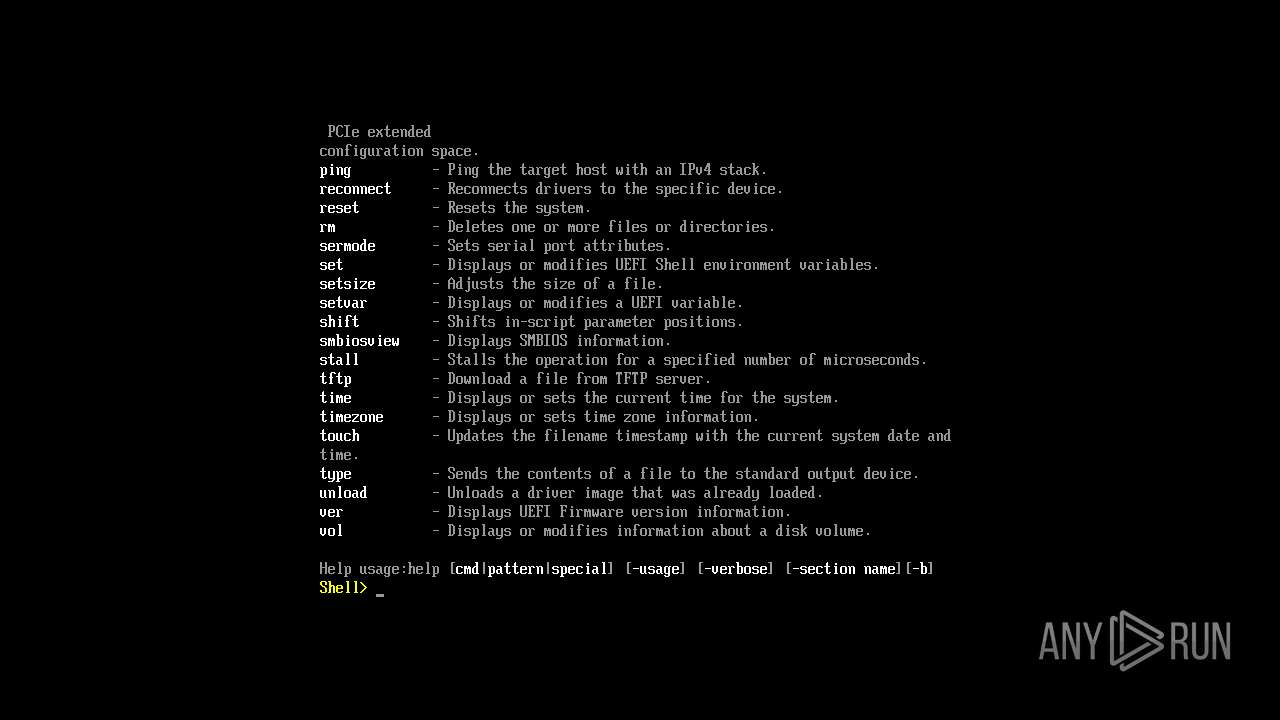
MEMZ has been detected (YARA)
- MEMZ-Destructive.exe (PID: 1480)
SUSPICIOUS
Checks for external IP
- svchost.exe (PID: 7980)
Connects to unusual port
- svchost.exe (PID: 7980)
Executable content was dropped or overwritten
- CoronaVirus.exe (PID: 7804)
- explorer.exe (PID: 7928)
- CoronaVirus.exe (PID: 7768)
Starts CMD.EXE for commands execution
- CoronaVirus.exe (PID: 7804)
- CoronaVirus.exe (PID: 7768)
Creates file in the systems drive root
- CoronaVirus.exe (PID: 7804)
- CoronaVirus.exe (PID: 7768)
- notepad.exe (PID: 4860)
- MEMZ-Destructive.exe (PID: 6240)
Reads security settings of Internet Explorer
- CoronaVirus.exe (PID: 7804)
- {34184A33-0407-212E-3300-09040709E2C2}.exe (PID: 1156)
- MEMZ-Destructive.exe (PID: 1480)
- MEMZ-Destructive.exe (PID: 6240)
Application launched itself
- CoronaVirus.exe (PID: 7804)
- {34184A33-0407-212E-3300-09040709E2C2}.exe (PID: 1156)
- MEMZ-Destructive.exe (PID: 1480)
The process creates files with name similar to system file names
- CoronaVirus.exe (PID: 7768)
- CoronaVirus.exe (PID: 7804)
Process drops legitimate windows executable
- CoronaVirus.exe (PID: 7768)
Executes as Windows Service
- VSSVC.exe (PID: 7496)
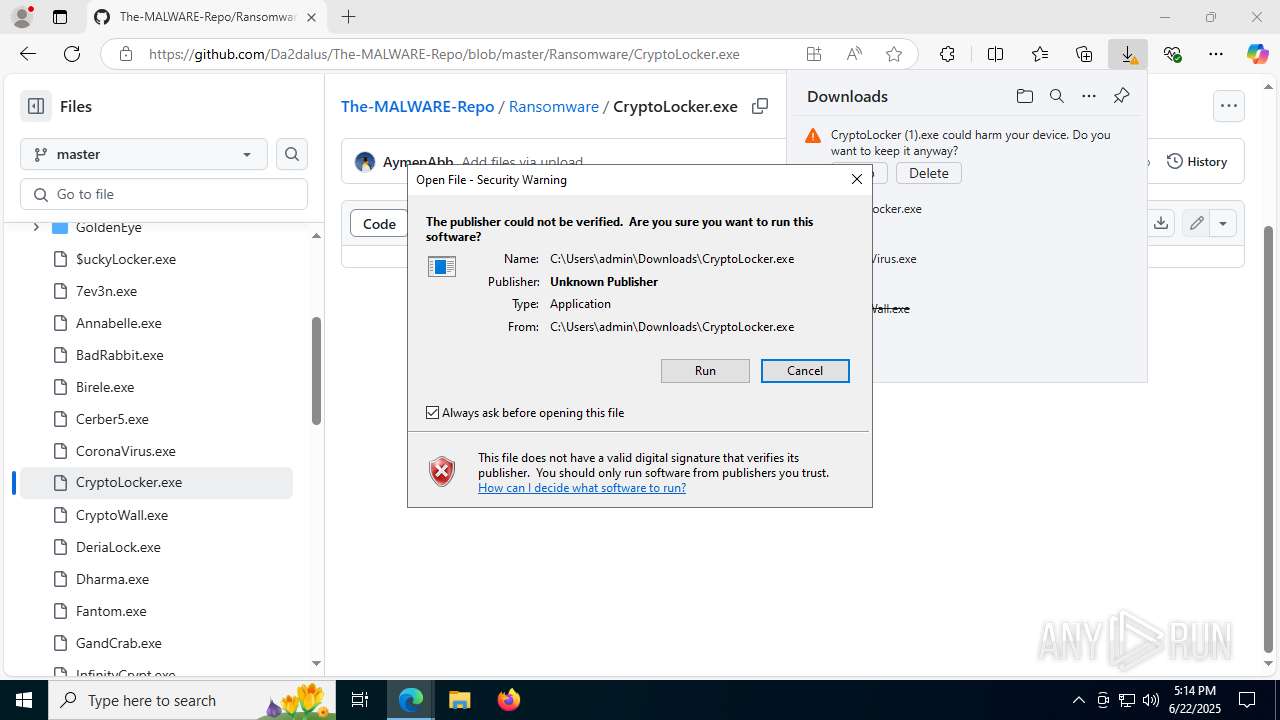
Starts itself from another location
- CryptoLocker.exe (PID: 4460)
There is functionality for taking screenshot (YARA)
- {34184A33-0407-212E-3300-09040709E2C2}.exe (PID: 1156)
- {34184A33-0407-212E-3300-09040709E2C2}.exe (PID: 7460)
- MEMZ-Destructive.exe (PID: 1480)
Start notepad (likely ransomware note)
- MEMZ-Destructive.exe (PID: 6240)
INFO
Executable content was dropped or overwritten
- msedge.exe (PID: 1208)
- msedge.exe (PID: 1488)
Checks supported languages
- identity_helper.exe (PID: 7660)
- CryptoWall.exe (PID: 7908)
- CoronaVirus.exe (PID: 7804)
- mode.com (PID: 5600)
- CoronaVirus.exe (PID: 7768)
- mode.com (PID: 3148)
- CryptoLocker.exe (PID: 4460)
- {34184A33-0407-212E-3300-09040709E2C2}.exe (PID: 1156)
- {34184A33-0407-212E-3300-09040709E2C2}.exe (PID: 7460)
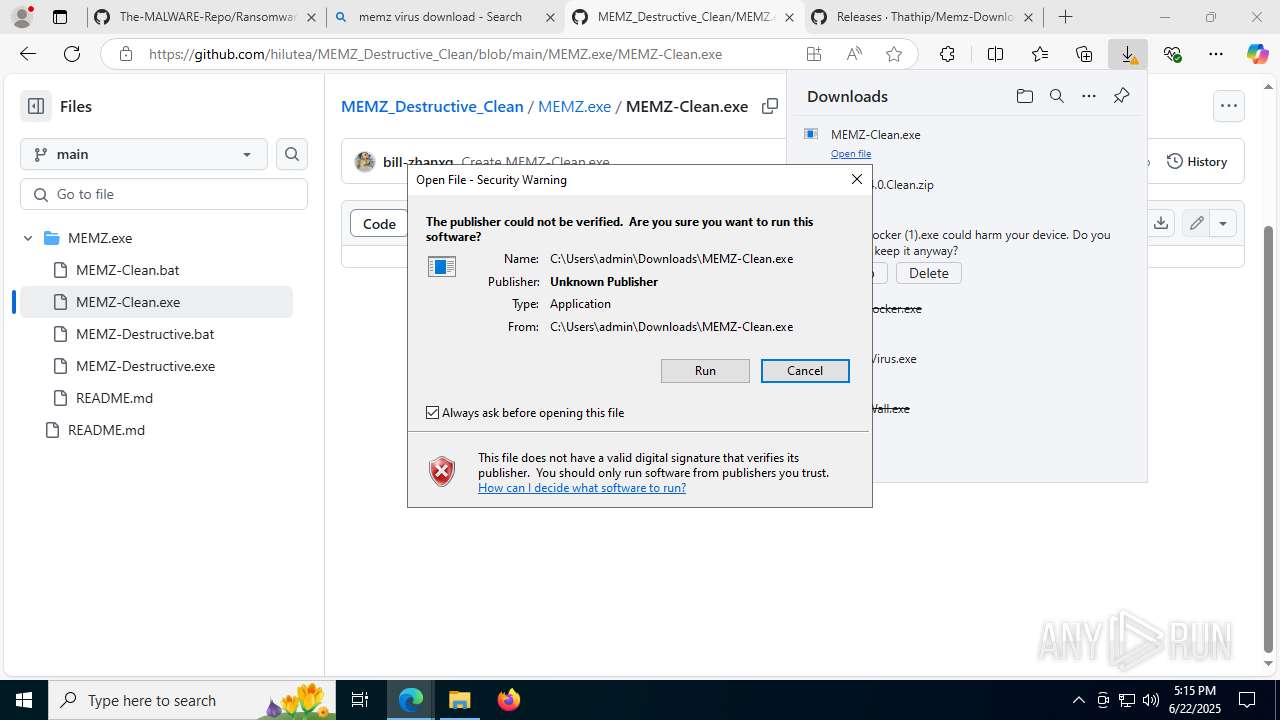
- MEMZ-Clean.exe (PID: 6528)
- MEMZ-Destructive.exe (PID: 7360)
- MEMZ-Destructive.exe (PID: 3880)
- MEMZ-Destructive.exe (PID: 1484)
- MEMZ-Destructive.exe (PID: 8036)
- MEMZ-Destructive.exe (PID: 5008)
- MEMZ-Destructive.exe (PID: 1480)
- MEMZ-Destructive.exe (PID: 8004)
- MEMZ-Destructive.exe (PID: 6240)
Reads the computer name
- identity_helper.exe (PID: 7660)
- CoronaVirus.exe (PID: 7804)
- CoronaVirus.exe (PID: 7768)
- {34184A33-0407-212E-3300-09040709E2C2}.exe (PID: 1156)
- CryptoLocker.exe (PID: 4460)
- {34184A33-0407-212E-3300-09040709E2C2}.exe (PID: 7460)
- MEMZ-Clean.exe (PID: 6528)
- MEMZ-Destructive.exe (PID: 7360)
- MEMZ-Destructive.exe (PID: 1480)
- MEMZ-Destructive.exe (PID: 6240)
- MEMZ-Destructive.exe (PID: 1484)
- MEMZ-Destructive.exe (PID: 8036)
- MEMZ-Destructive.exe (PID: 5008)
Reads Environment values
- identity_helper.exe (PID: 7660)
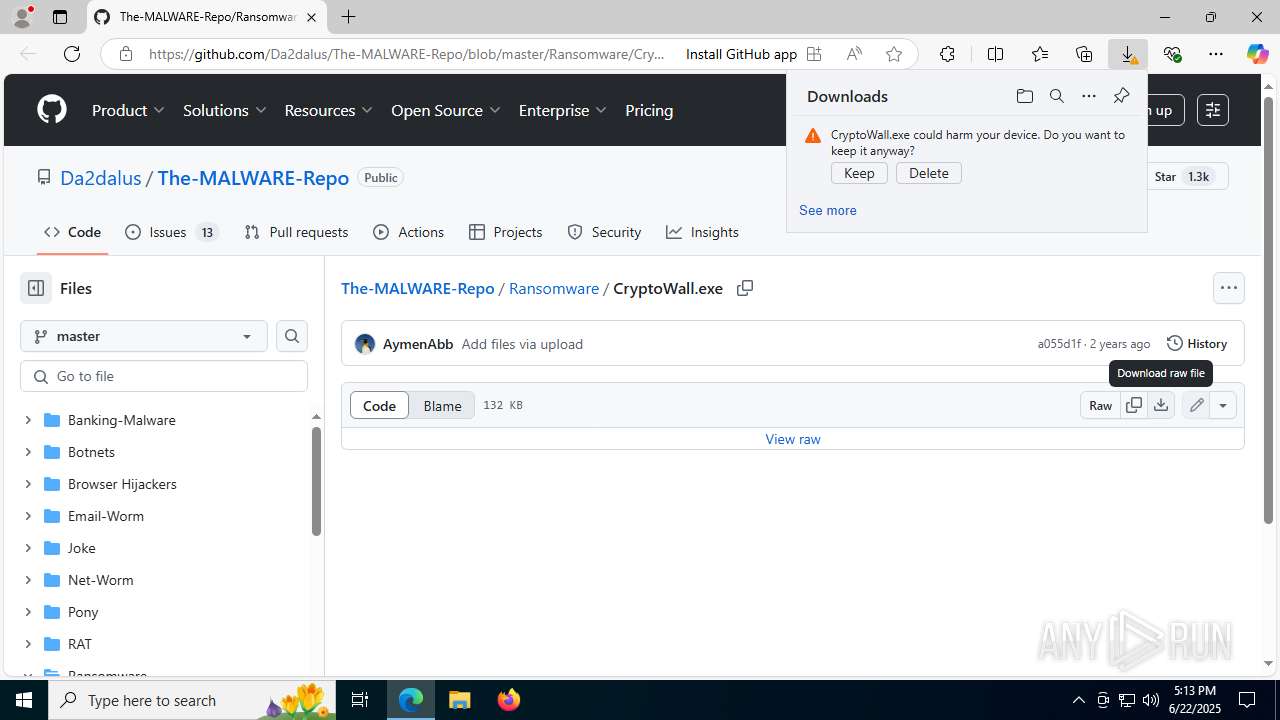
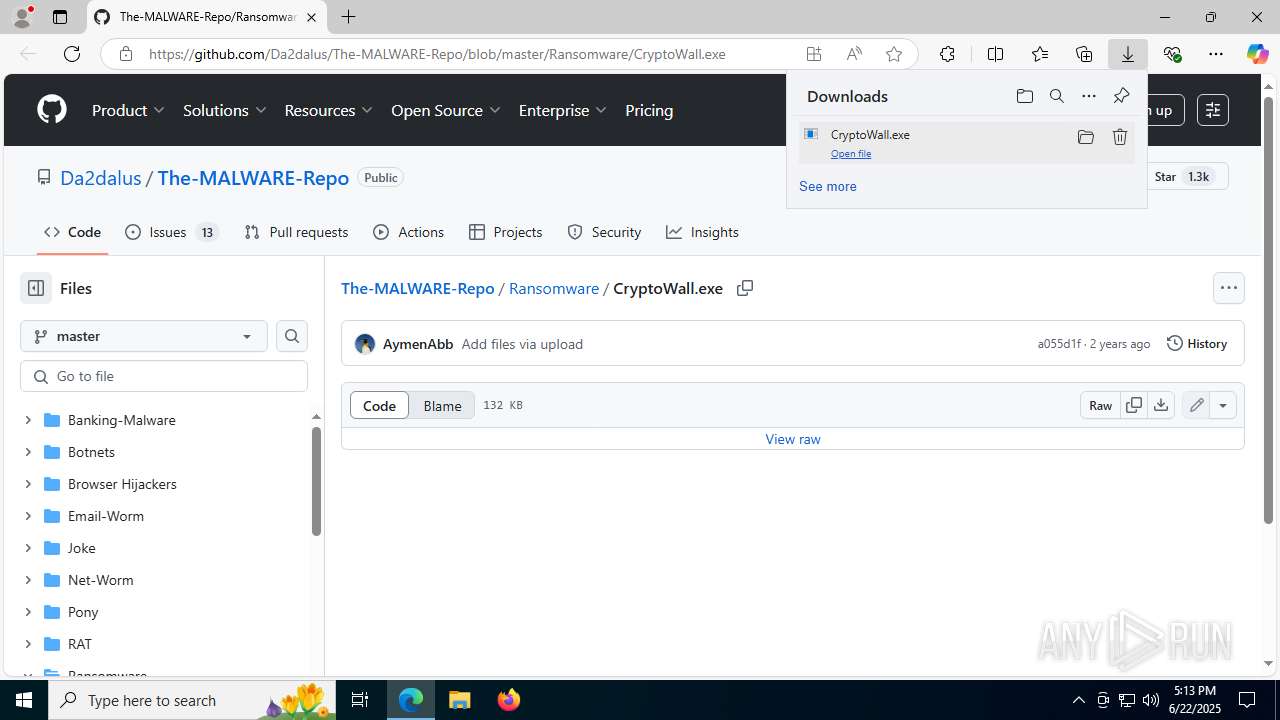
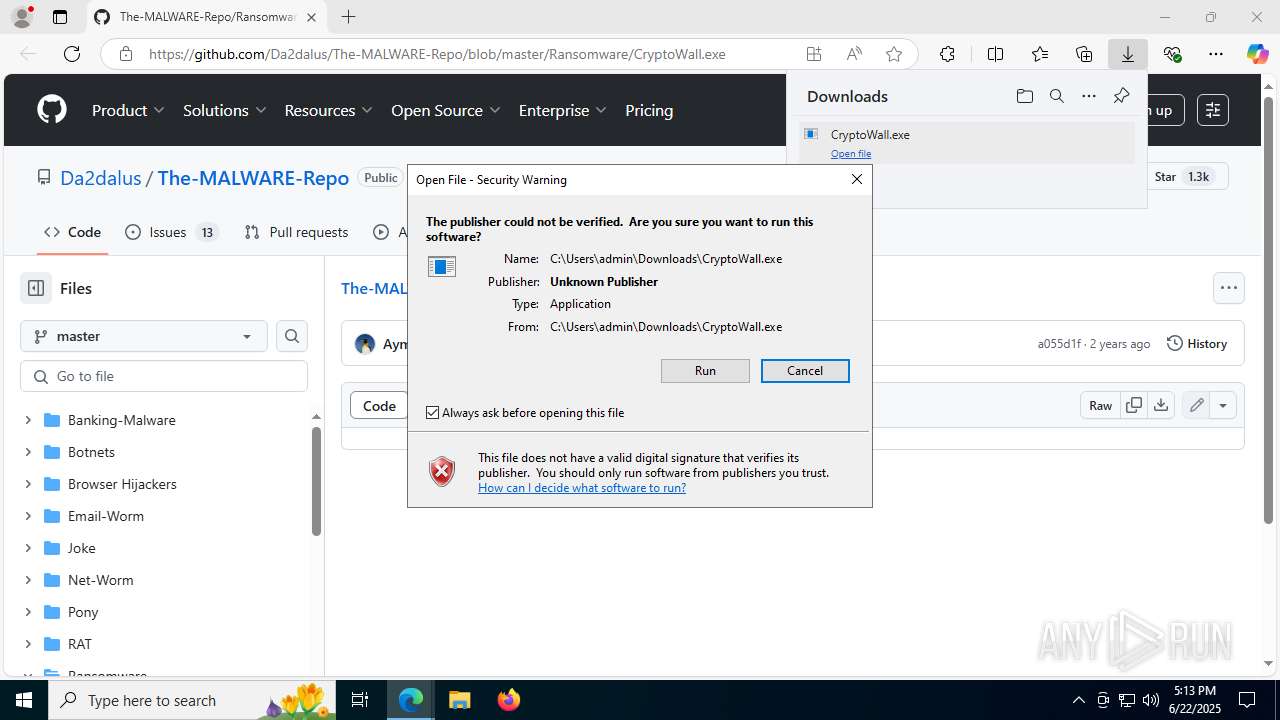
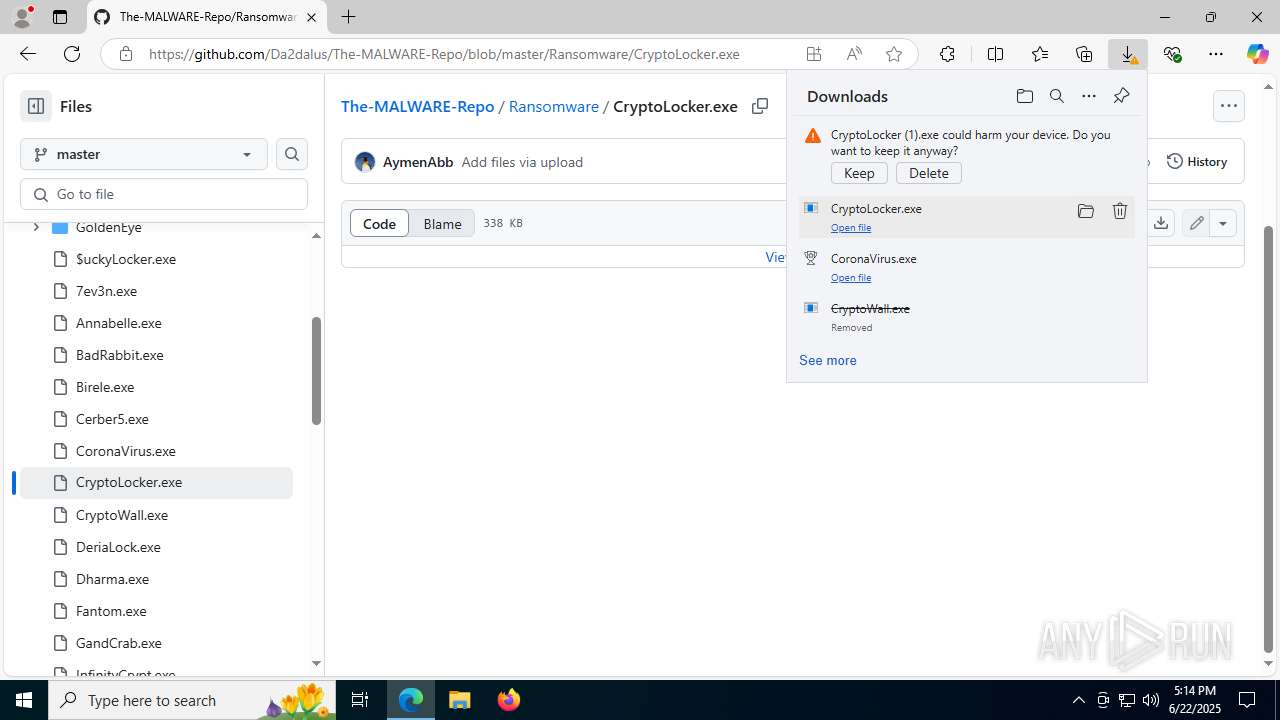
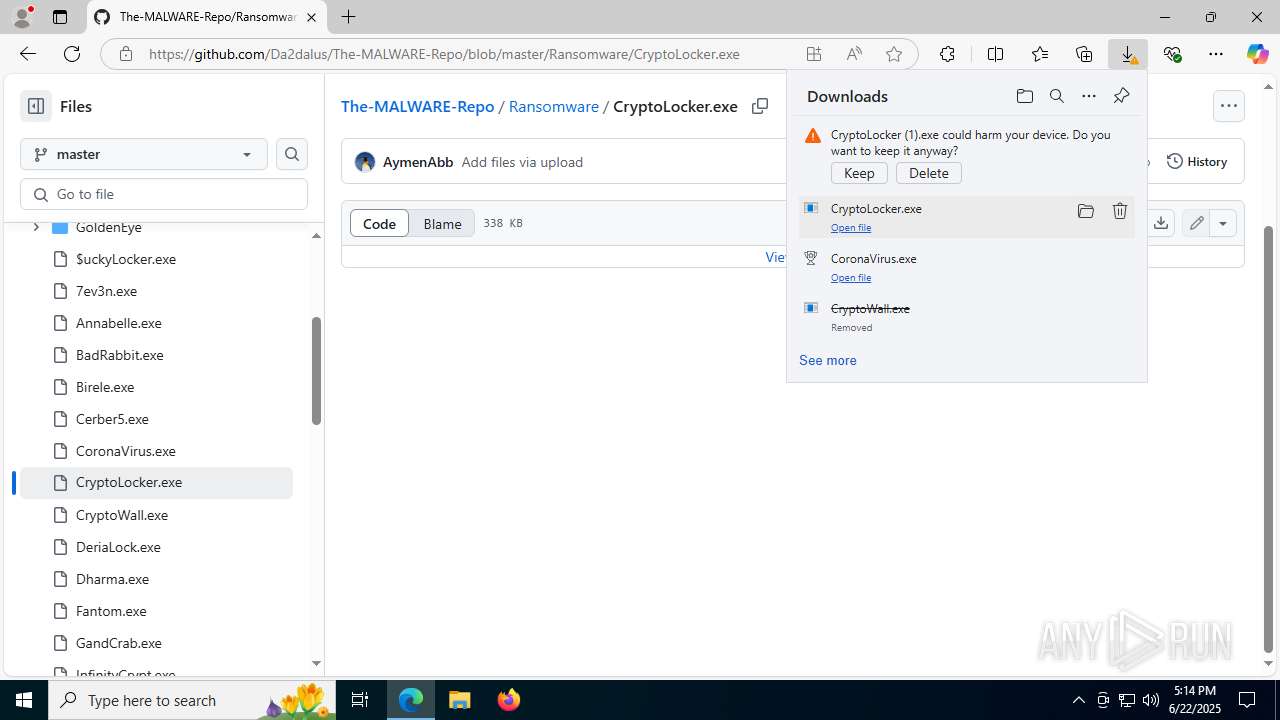
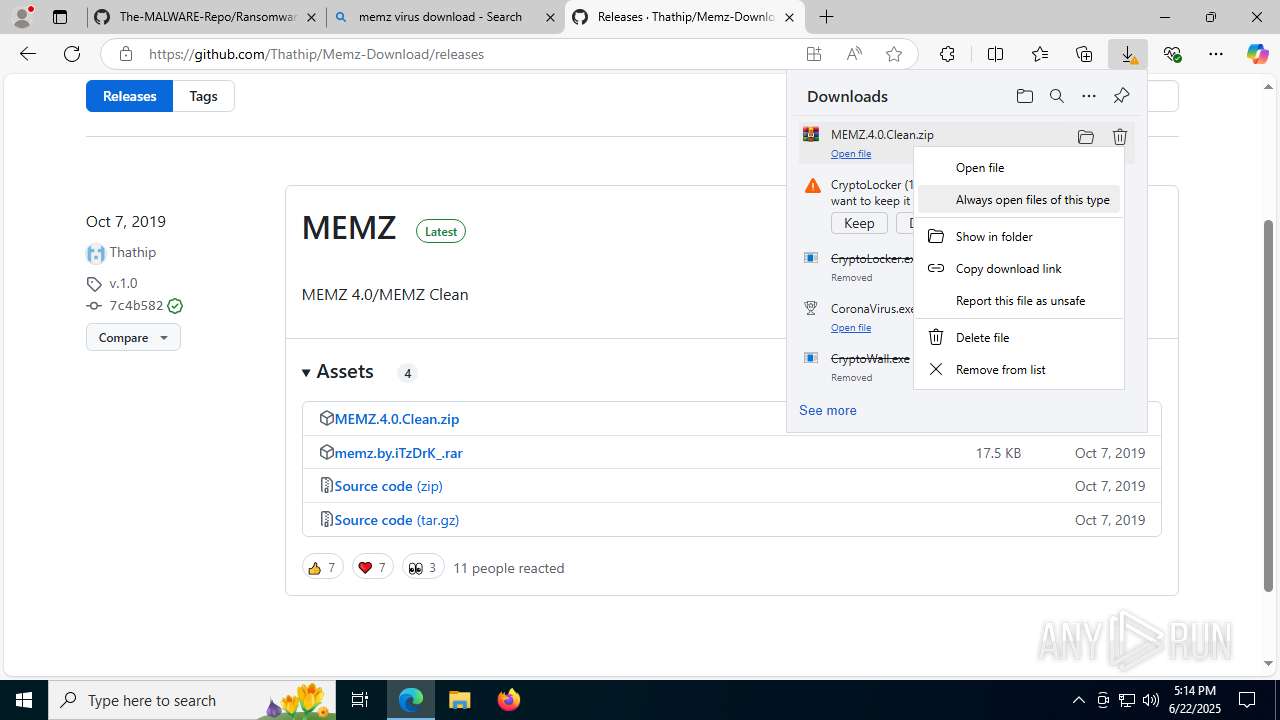
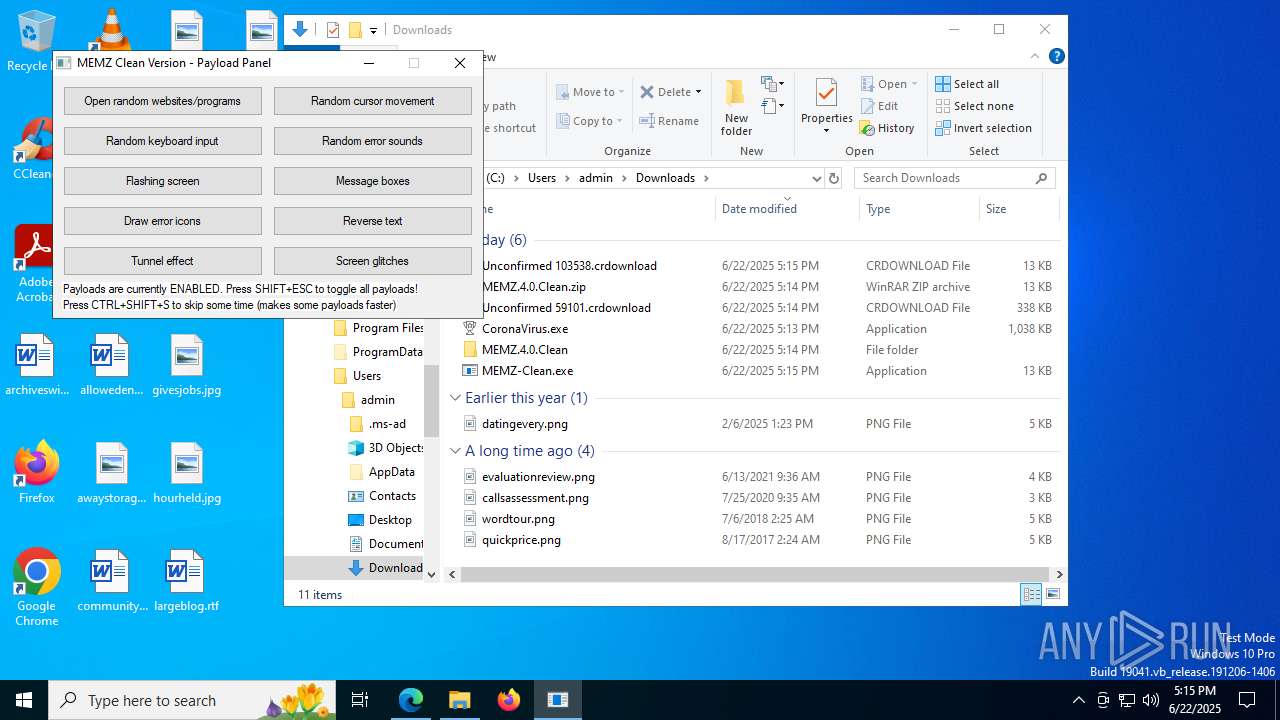
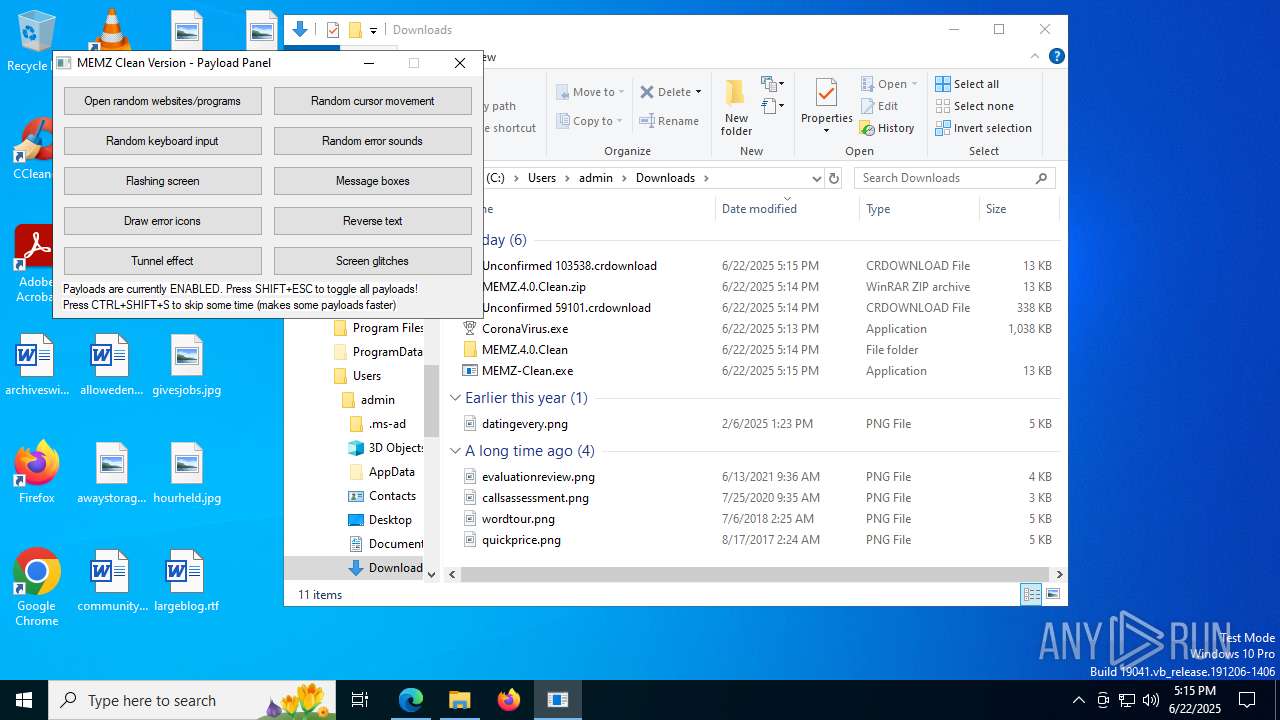
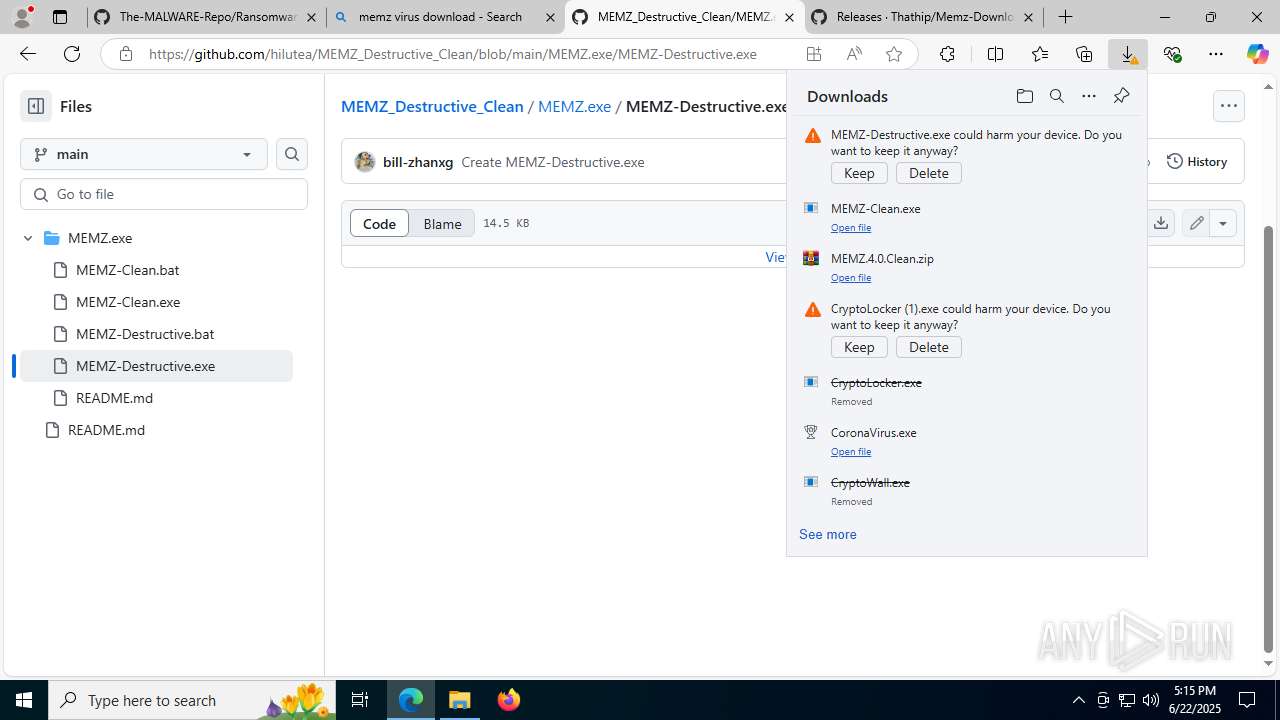
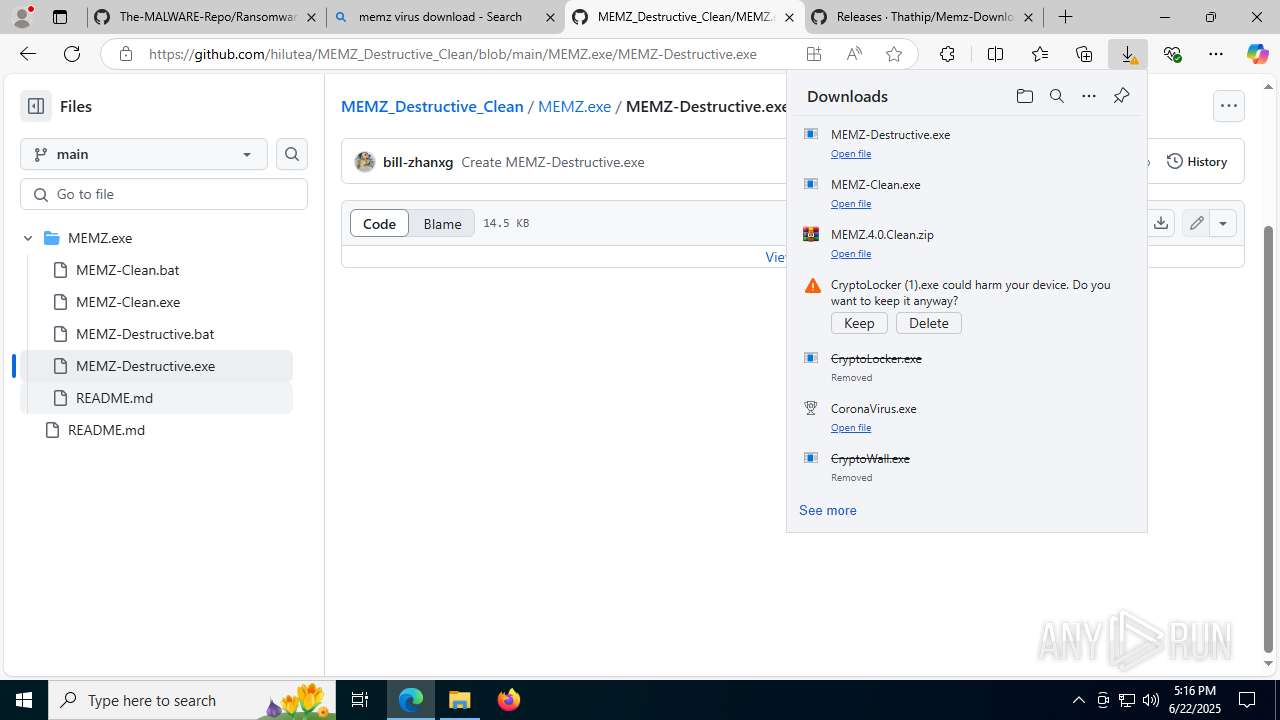
Launching a file from the Downloads directory
- msedge.exe (PID: 1208)
Reads the machine GUID from the registry
- CryptoWall.exe (PID: 7908)
- {34184A33-0407-212E-3300-09040709E2C2}.exe (PID: 1156)
- MEMZ-Destructive.exe (PID: 1480)
- MEMZ-Destructive.exe (PID: 5008)
- MEMZ-Destructive.exe (PID: 1484)
- MEMZ-Destructive.exe (PID: 8036)
Application launched itself
- msedge.exe (PID: 1208)
Creates files or folders in the user directory
- explorer.exe (PID: 7928)
- CoronaVirus.exe (PID: 7804)
- CryptoLocker.exe (PID: 4460)
Launching a file from a Registry key
- explorer.exe (PID: 7928)
- CoronaVirus.exe (PID: 7804)
- CoronaVirus.exe (PID: 7768)
- {34184A33-0407-212E-3300-09040709E2C2}.exe (PID: 1156)
Reads security settings of Internet Explorer
- svchost.exe (PID: 7980)
- notepad.exe (PID: 4860)
Checks proxy server information
- svchost.exe (PID: 7980)
- slui.exe (PID: 6524)
Drops a (possible) Coronavirus decoy
- msedge.exe (PID: 1208)
- CoronaVirus.exe (PID: 7804)
- CoronaVirus.exe (PID: 7768)
Failed to create an executable file in Windows directory
- CoronaVirus.exe (PID: 7804)
The sample compiled with english language support
- msedge.exe (PID: 1488)
- msedge.exe (PID: 1208)
- CoronaVirus.exe (PID: 7804)
- CoronaVirus.exe (PID: 7768)
Launching a file from the Startup directory
- CoronaVirus.exe (PID: 7804)
- explorer.exe (PID: 7928)
- CoronaVirus.exe (PID: 7768)
Process checks computer location settings
- CoronaVirus.exe (PID: 7804)
- MEMZ-Destructive.exe (PID: 1480)
- MEMZ-Destructive.exe (PID: 6240)
Starts MODE.COM to configure console settings
- mode.com (PID: 5600)
- mode.com (PID: 3148)
Creates files in the program directory
- CoronaVirus.exe (PID: 7804)
- CoronaVirus.exe (PID: 7768)
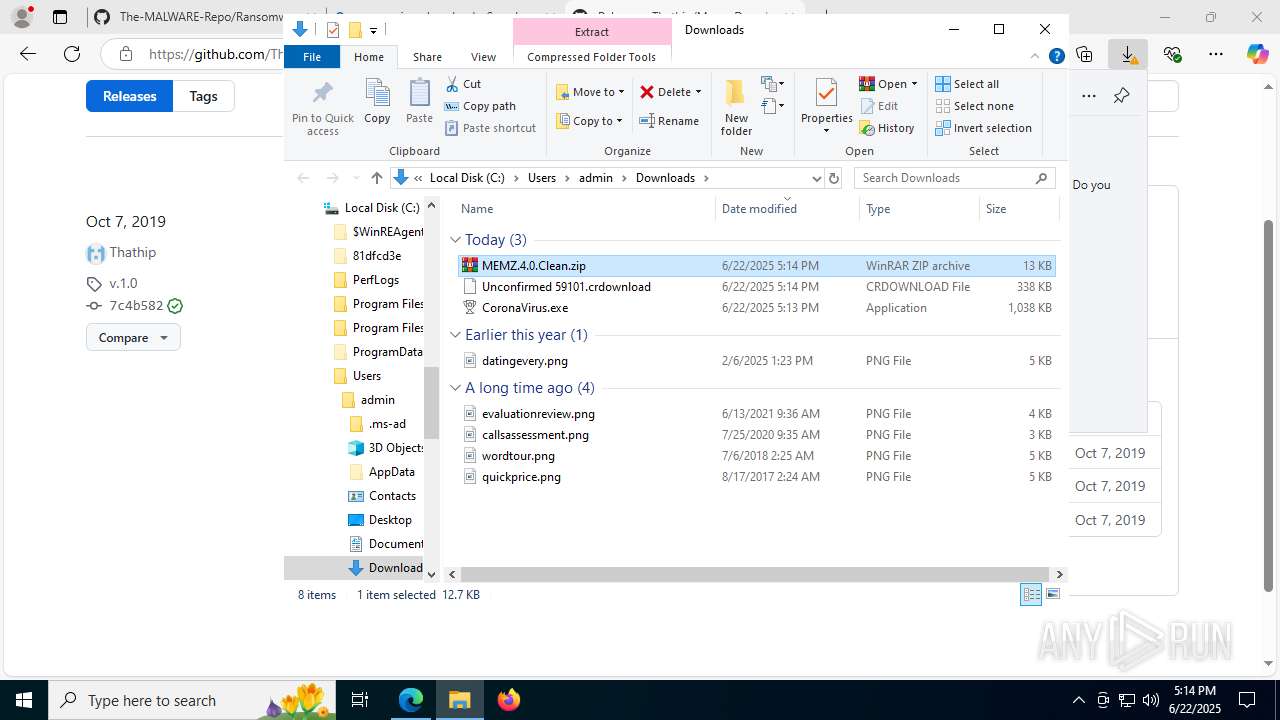
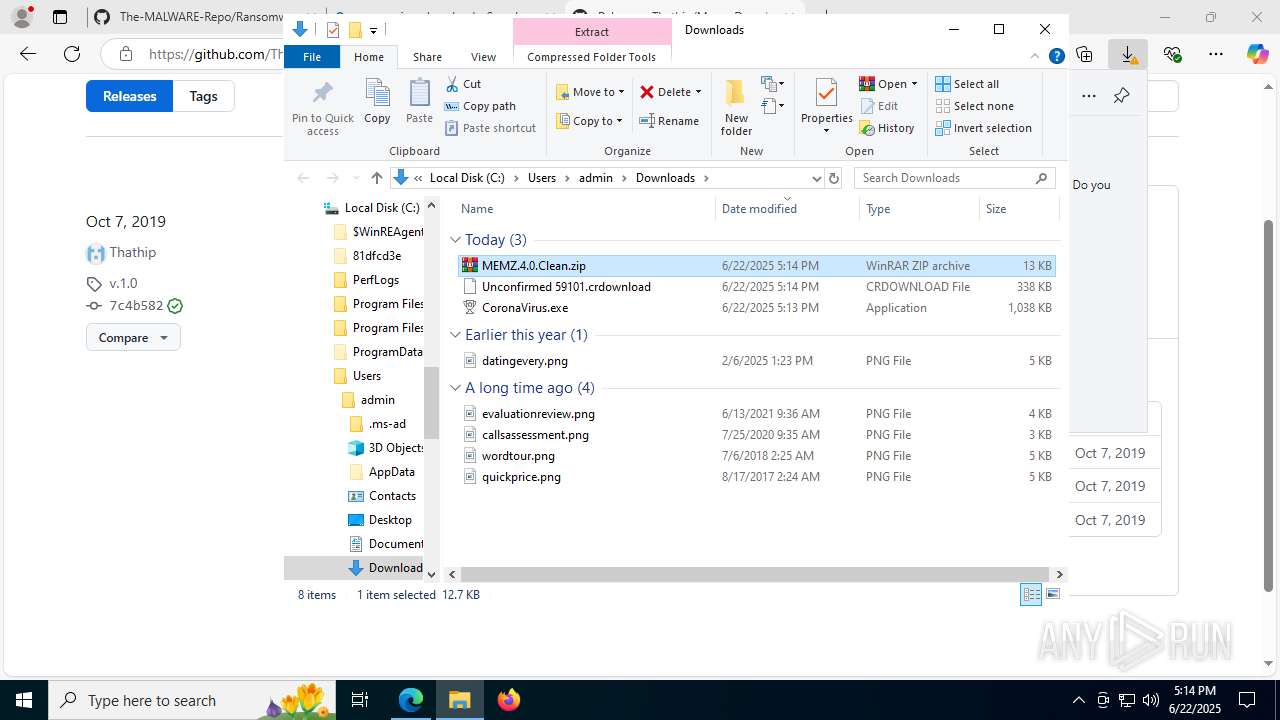
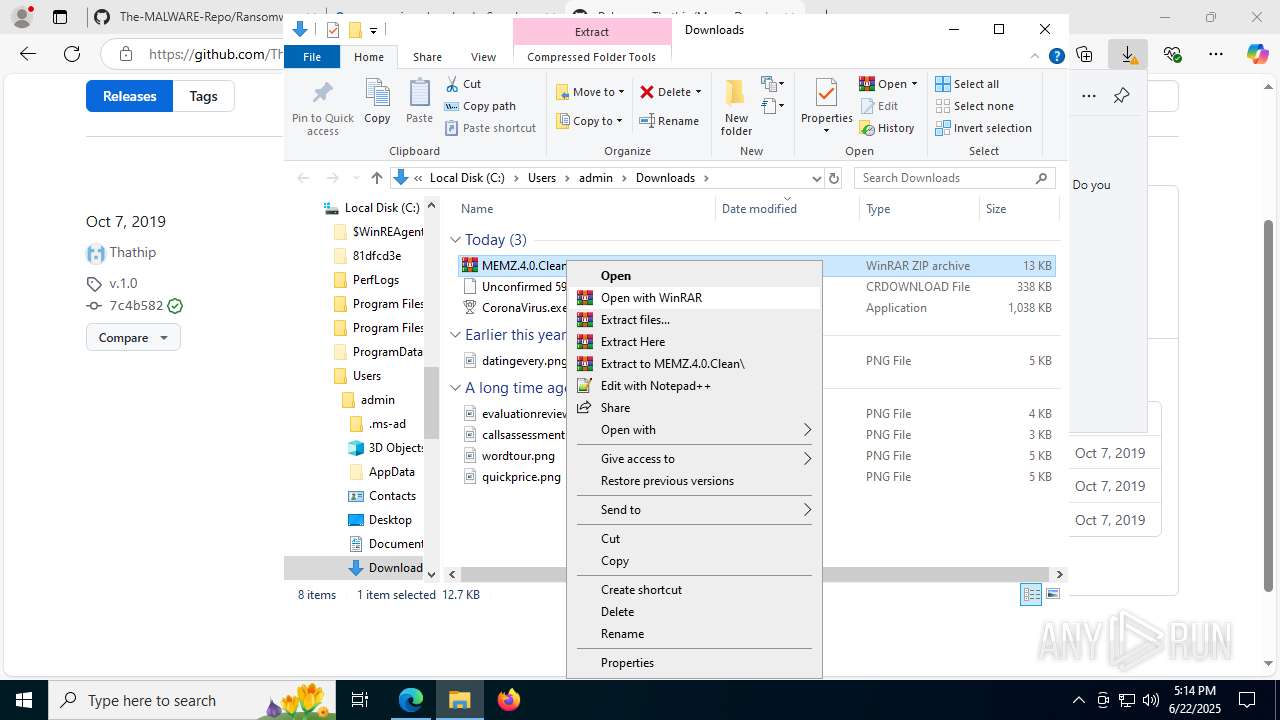
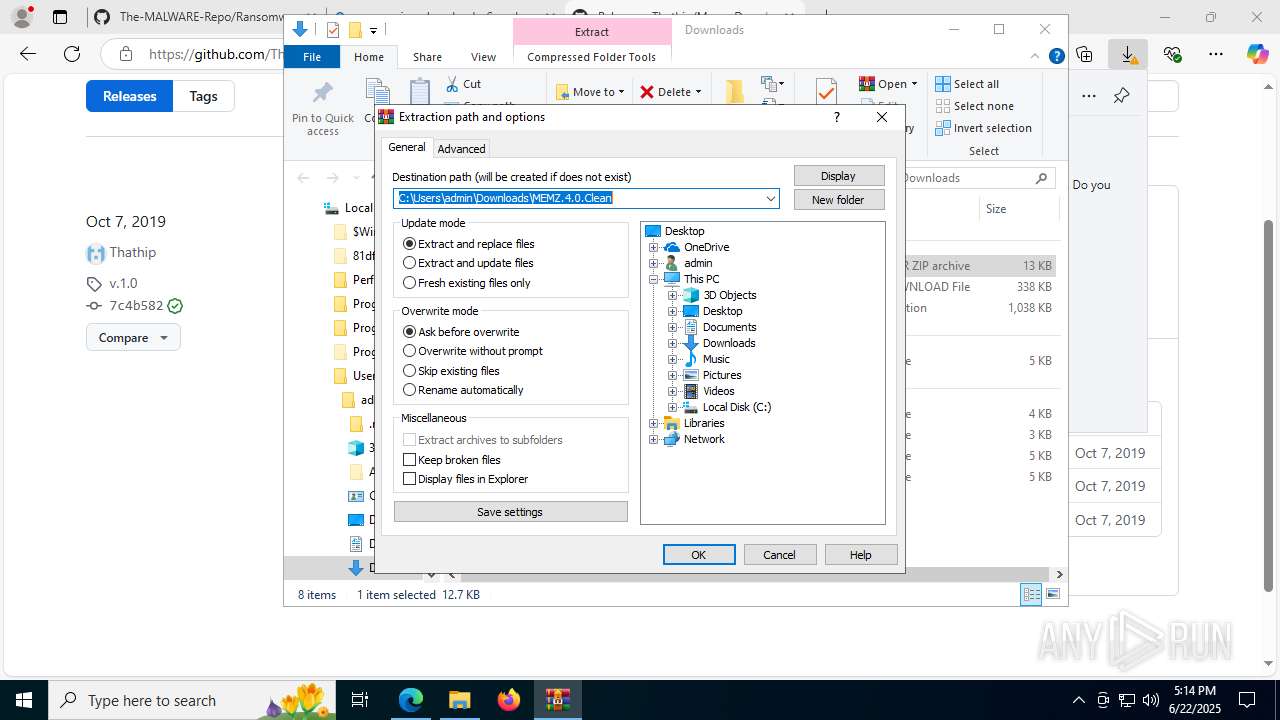
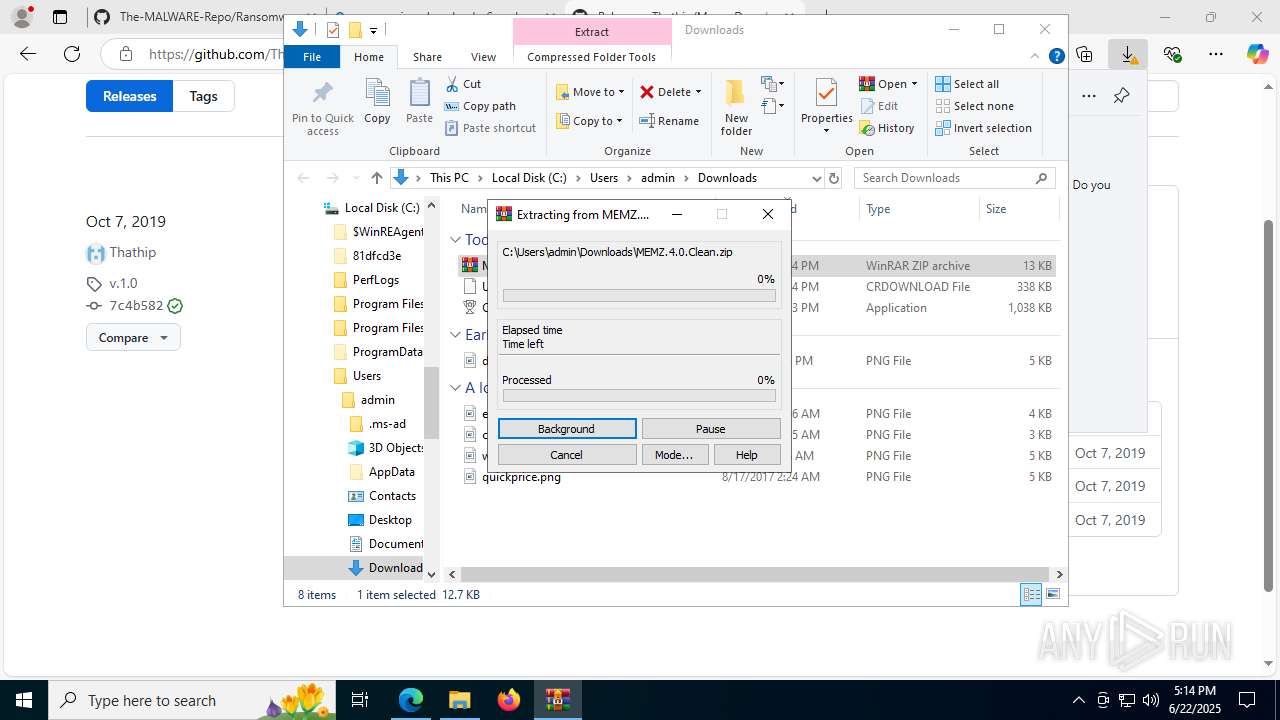
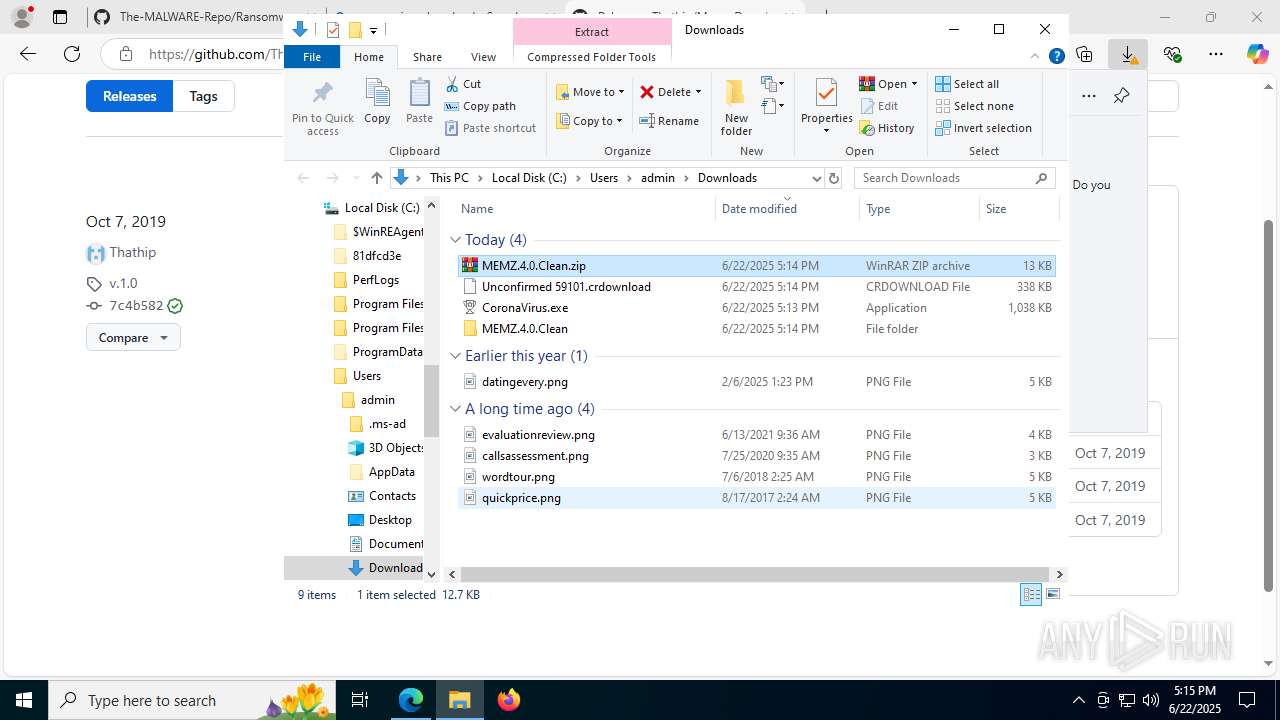
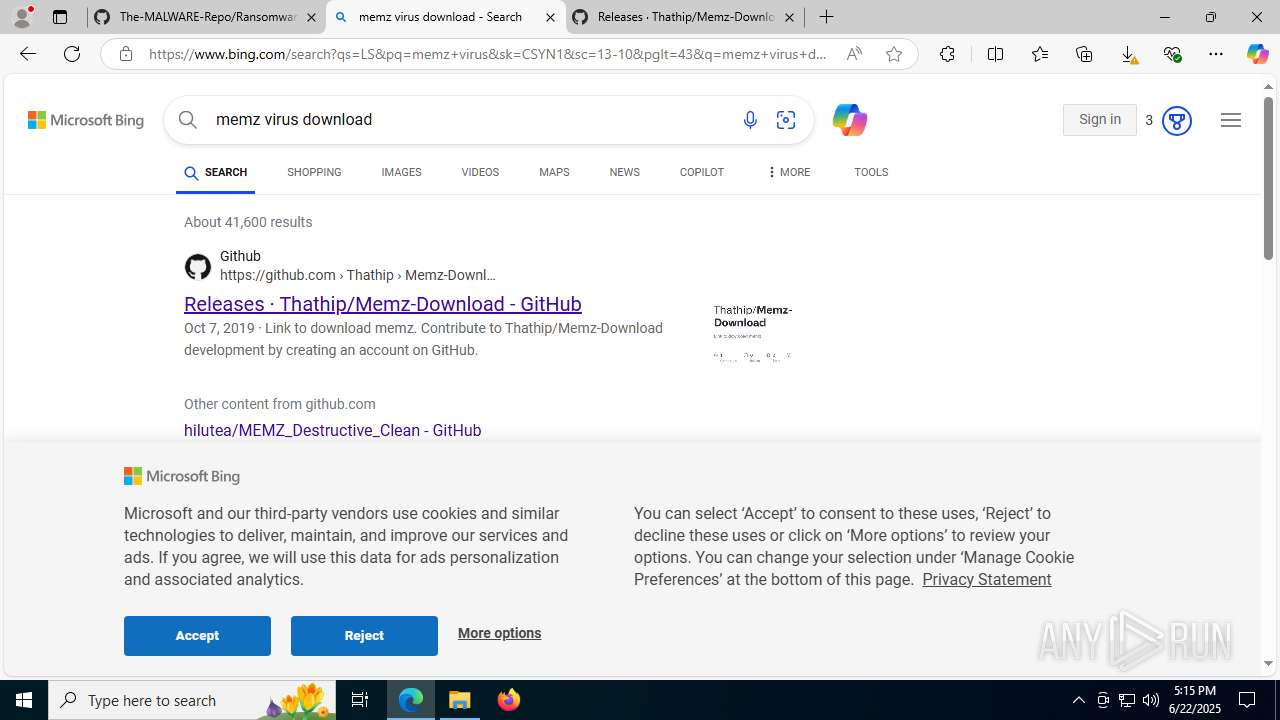
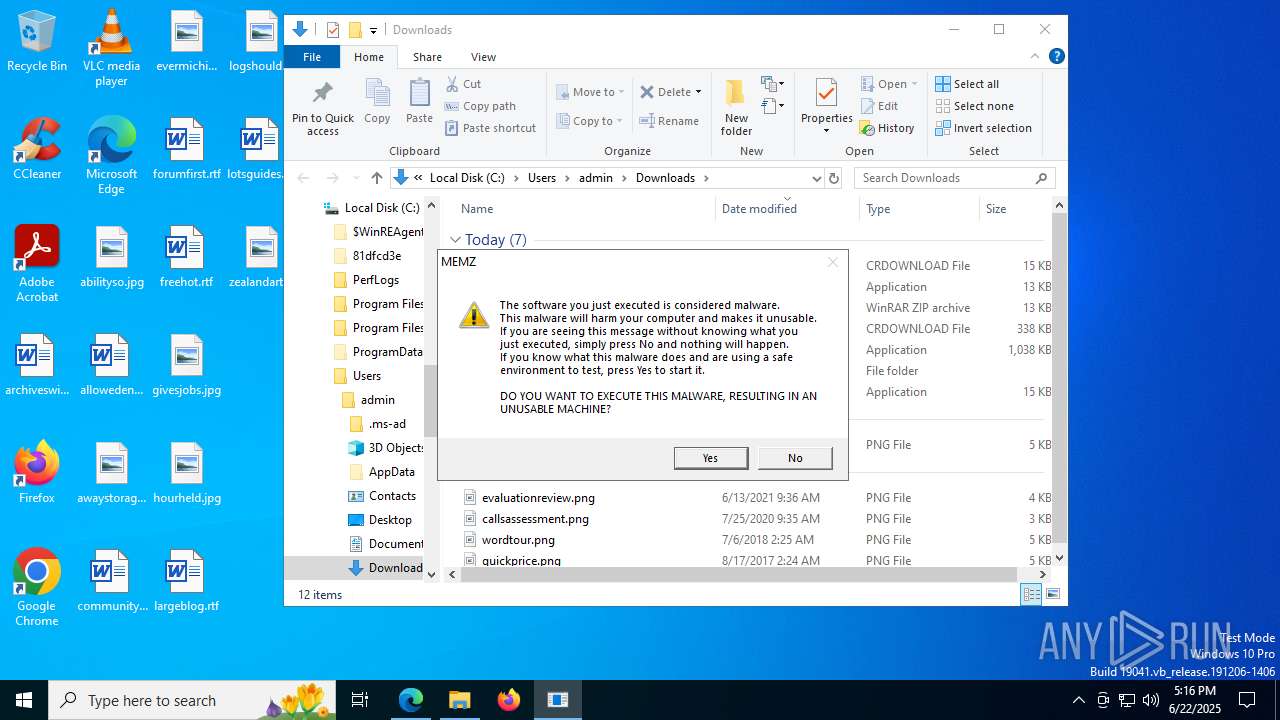
Manual execution by a user
- WinRAR.exe (PID: 768)
The sample compiled with german language support
- CoronaVirus.exe (PID: 7768)
The sample compiled with french language support
- CoronaVirus.exe (PID: 7768)
The sample compiled with Italian language support
- CoronaVirus.exe (PID: 7768)
The sample compiled with japanese language support
- CoronaVirus.exe (PID: 7768)
The sample compiled with korean language support
- CoronaVirus.exe (PID: 7768)
The sample compiled with portuguese language support
- CoronaVirus.exe (PID: 7768)
Reads the software policy settings
- slui.exe (PID: 6524)
The sample compiled with spanish language support
- CoronaVirus.exe (PID: 7768)
The sample compiled with russian language support
- CoronaVirus.exe (PID: 7768)
The sample compiled with turkish language support
- CoronaVirus.exe (PID: 7768)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
233
Monitored processes
88
Malicious processes
8
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 416 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=4256,i,4940162859700964720,1797809114761806590,262144 --variations-seed-version --mojo-platform-channel-handle=4296 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 768 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\MEMZ.4.0.Clean.zip" "?\" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1156 | "C:\Users\admin\AppData\Roaming\{34184A33-0407-212E-3300-09040709E2C2}.exe" "/rC:\Users\admin\Downloads\CryptoLocker.exe" | C:\Users\admin\AppData\Roaming\{34184A33-0407-212E-3300-09040709E2C2}.exe | CryptoLocker.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 1160 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=39 --always-read-main-dll --field-trial-handle=6284,i,4940162859700964720,1797809114761806590,262144 --variations-seed-version --mojo-platform-channel-handle=5904 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1208 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://github.com/Da2dalus/The-MALWARE-Repo/blob/master/Ransomware/CryptoWall.exe" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1296 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=20 --always-read-main-dll --field-trial-handle=7764,i,4940162859700964720,1797809114761806590,262144 --variations-seed-version --mojo-platform-channel-handle=7792 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1336 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=30 --always-read-main-dll --field-trial-handle=6020,i,4940162859700964720,1797809114761806590,262144 --variations-seed-version --mojo-platform-channel-handle=6116 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1480 | "C:\Users\admin\Downloads\MEMZ-Destructive.exe" | C:\Users\admin\Downloads\MEMZ-Destructive.exe | msedge.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1484 | "C:\Users\admin\Downloads\MEMZ-Destructive.exe" /watchdog | C:\Users\admin\Downloads\MEMZ-Destructive.exe | — | MEMZ-Destructive.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 1488 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2240,i,4940162859700964720,1797809114761806590,262144 --variations-seed-version --mojo-platform-channel-handle=2616 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
19 192
Read events
19 112
Write events
67
Delete events
13
Modification events
| (PID) Process: | (1208) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1208) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1208) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1208) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1208) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1208) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1208) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393972 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {1F536983-3C5A-4C5C-998C-157D4413C218} | |||
| (PID) Process: | (1208) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 96FF8B7FC2962F00 | |||
| (PID) Process: | (1208) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393972 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {C21E617F-52D5-4AAA-A044-E7DC247847DD} | |||
| (PID) Process: | (1208) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393972 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {32A1CE9B-8A7C-4529-A0C5-847B2F2DBEAE} | |||
Executable files
440
Suspicious files
18 688
Text files
91
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1208 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF176522.TMP | — | |
MD5:— | SHA256:— | |||
| 1208 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1208 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF176522.TMP | — | |
MD5:— | SHA256:— | |||
| 1208 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1208 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF176542.TMP | — | |
MD5:— | SHA256:— | |||
| 1208 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1208 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF176542.TMP | — | |
MD5:— | SHA256:— | |||
| 1208 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1208 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF176551.TMP | — | |
MD5:— | SHA256:— | |||
| 1208 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF176532.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
145
DNS requests
233
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1488 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:I178SUakQlnYr8yfAbAsrMpb3I3lMT0bpwRQM8BKkzo&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
2668 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7980 | svchost.exe | GET | 308 | 188.165.164.184:80 | http://ip-addr.es/ | unknown | — | — | shared |
1268 | svchost.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7852 | SIHClient.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7744 | svchost.exe | GET | 206 | 208.89.74.21:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1751151540&P2=404&P3=2&P4=eUodbfVGifbZanhWTML%2bnS9E8mHuhq8%2b%2fxFdFiKfeMLxZi1z3RtoWNrn%2btKrqh0%2bbd0S9I1MC0r0D1ET3z8qiw%3d%3d | unknown | — | — | whitelisted |
7744 | svchost.exe | GET | 206 | 208.89.74.21:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1751151540&P2=404&P3=2&P4=eUodbfVGifbZanhWTML%2bnS9E8mHuhq8%2b%2fxFdFiKfeMLxZi1z3RtoWNrn%2btKrqh0%2bbd0S9I1MC0r0D1ET3z8qiw%3d%3d | unknown | — | — | whitelisted |
7852 | SIHClient.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7744 | svchost.exe | HEAD | 200 | 208.89.74.21:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1751151540&P2=404&P3=2&P4=eUodbfVGifbZanhWTML%2bnS9E8mHuhq8%2b%2fxFdFiKfeMLxZi1z3RtoWNrn%2btKrqh0%2bbd0S9I1MC0r0D1ET3z8qiw%3d%3d | unknown | — | — | whitelisted |
7744 | svchost.exe | HEAD | 200 | 208.89.74.21:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1751151541&P2=404&P3=2&P4=CNbmPejeHBAaevXltxKmGa05WcKIooXum%2fpf0Gg1RNpMH8DSu5jGfIMV1iJC1m50jwWFTeAON%2fGjhAbY2Y4npg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4816 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1488 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1488 | msedge.exe | 140.82.121.3:443 | github.com | GITHUB | US | whitelisted |
1488 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1488 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1488 | msedge.exe | 2.16.204.153:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
github.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
github.githubassets.com |
| whitelisted |
avatars.githubusercontent.com |
| whitelisted |
github-cloud.s3.amazonaws.com |
| whitelisted |
user-images.githubusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1488 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
1488 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
7980 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO HTTP Request for External IP Check (ip-addr .es) |
7980 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO HTTP Request for External IP Check (ip-addr .es) |