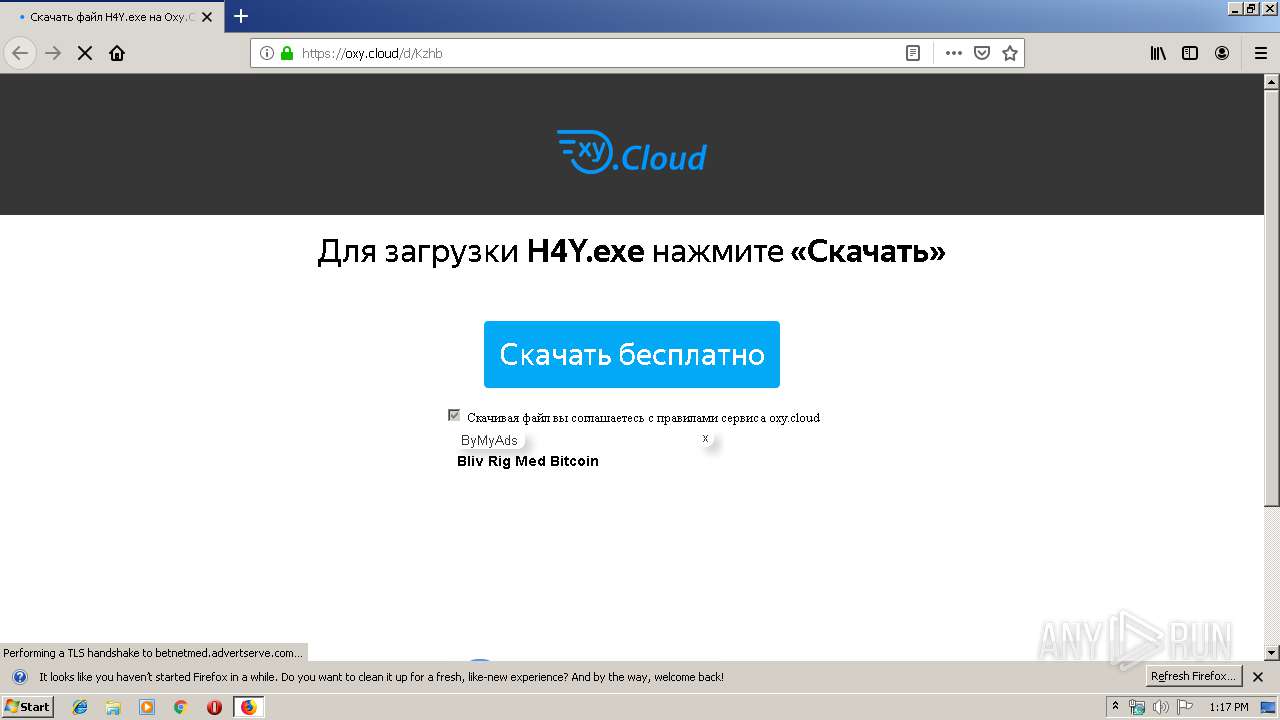
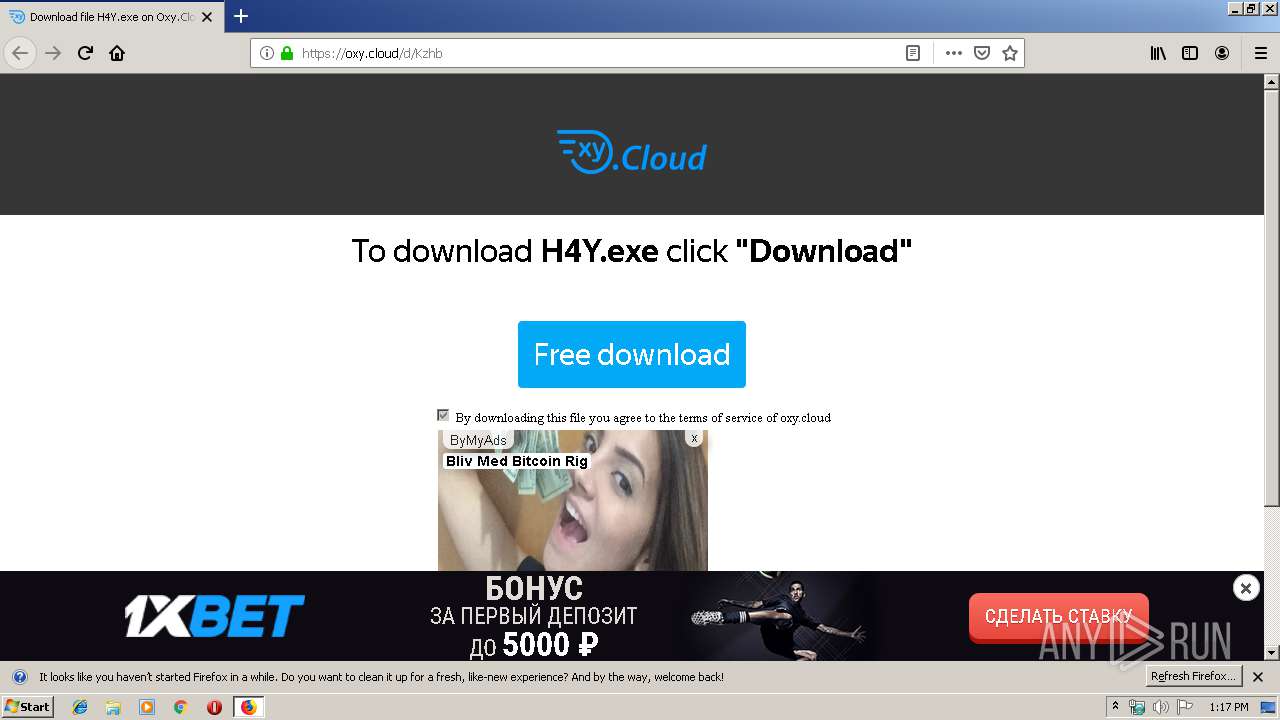
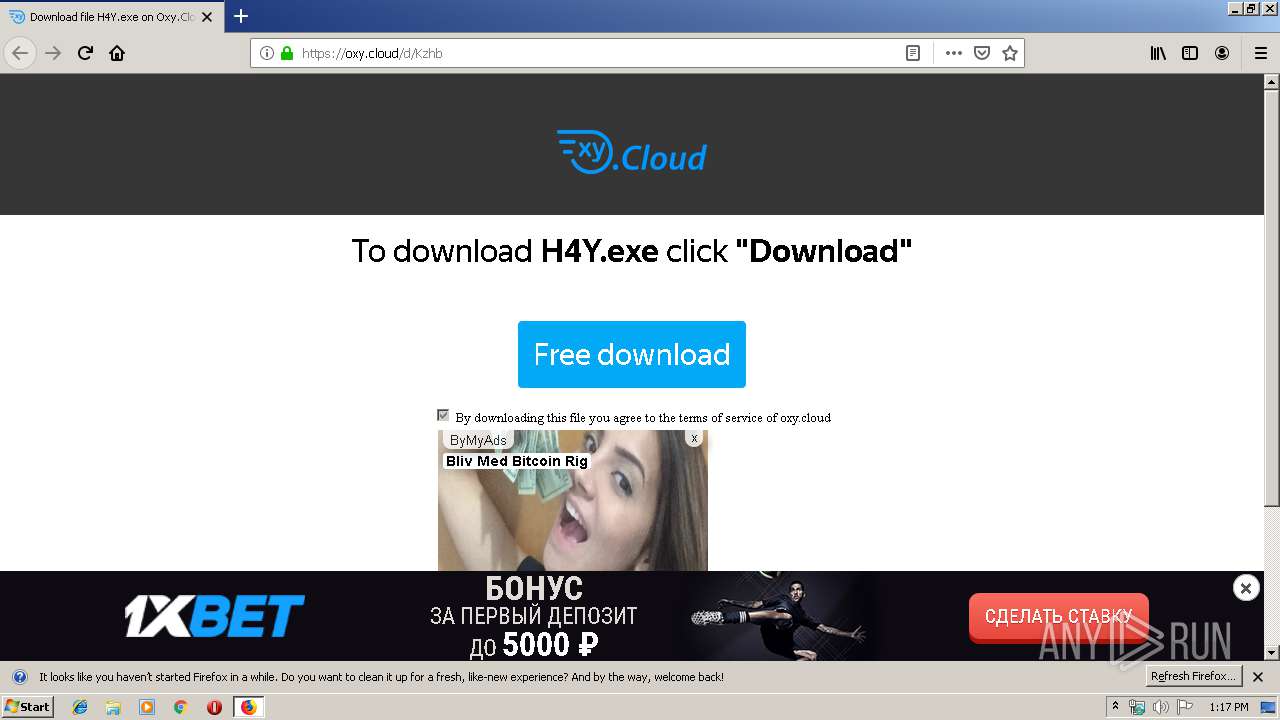
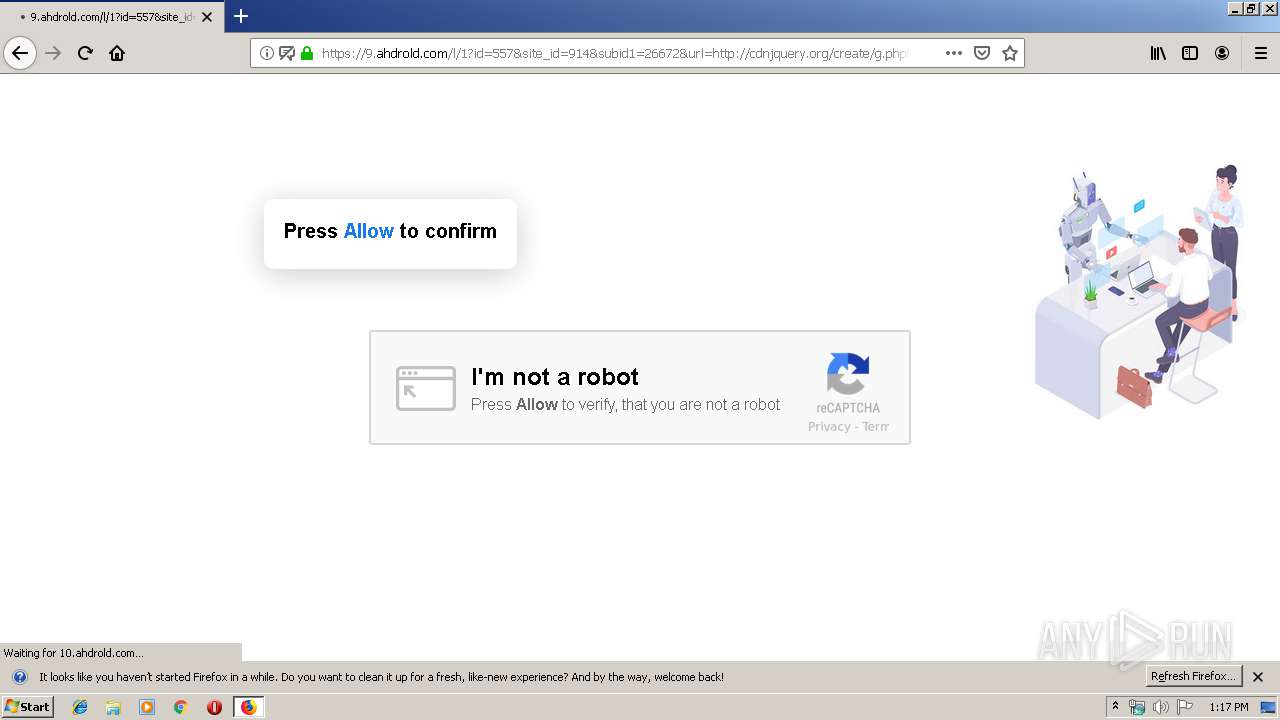
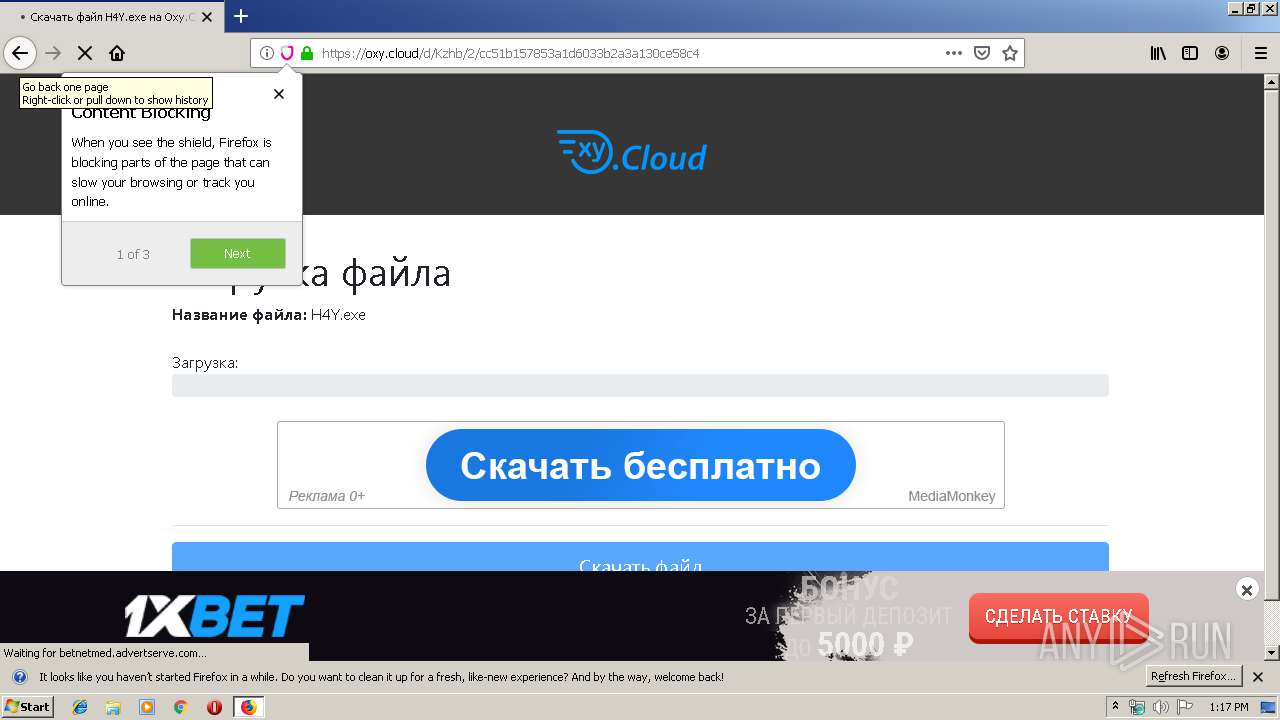
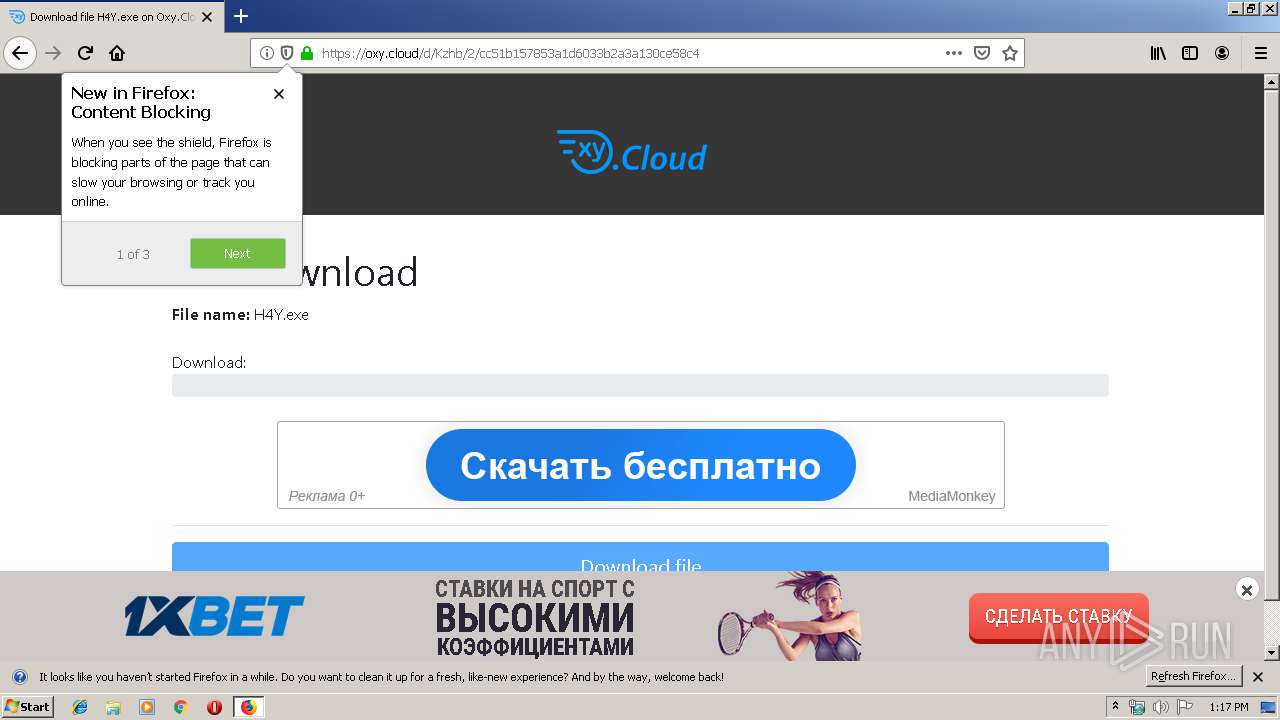
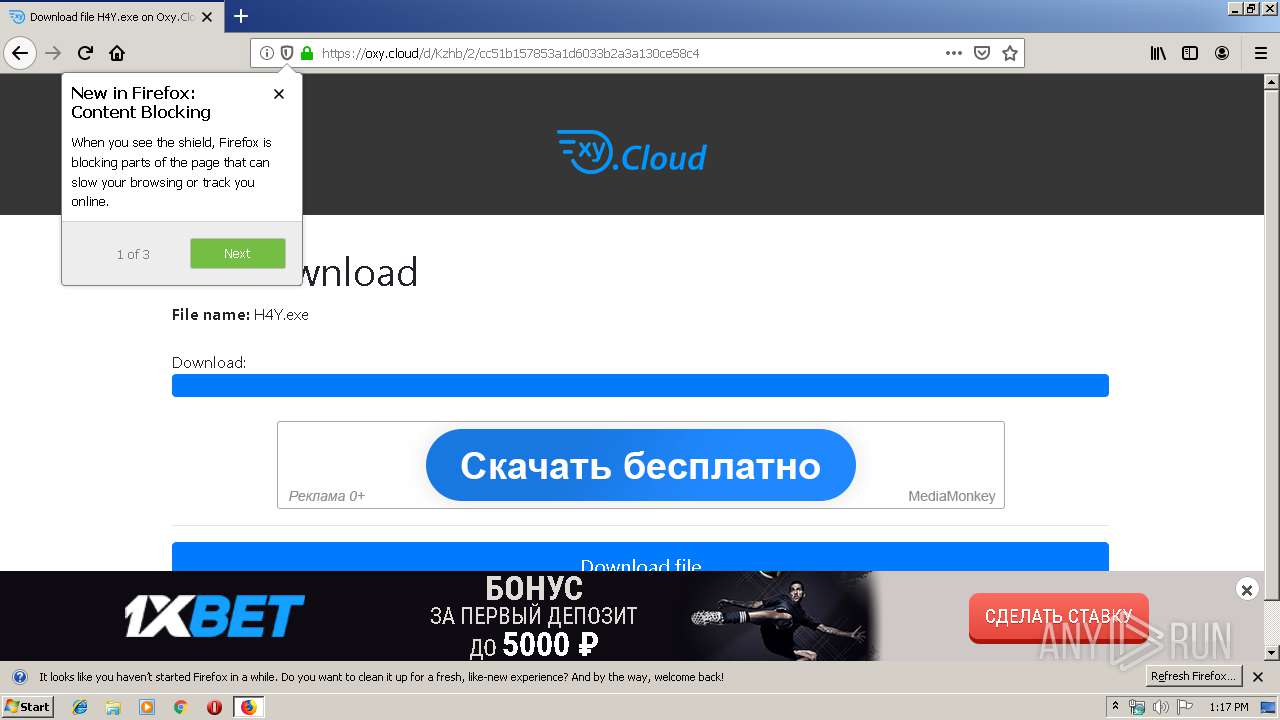
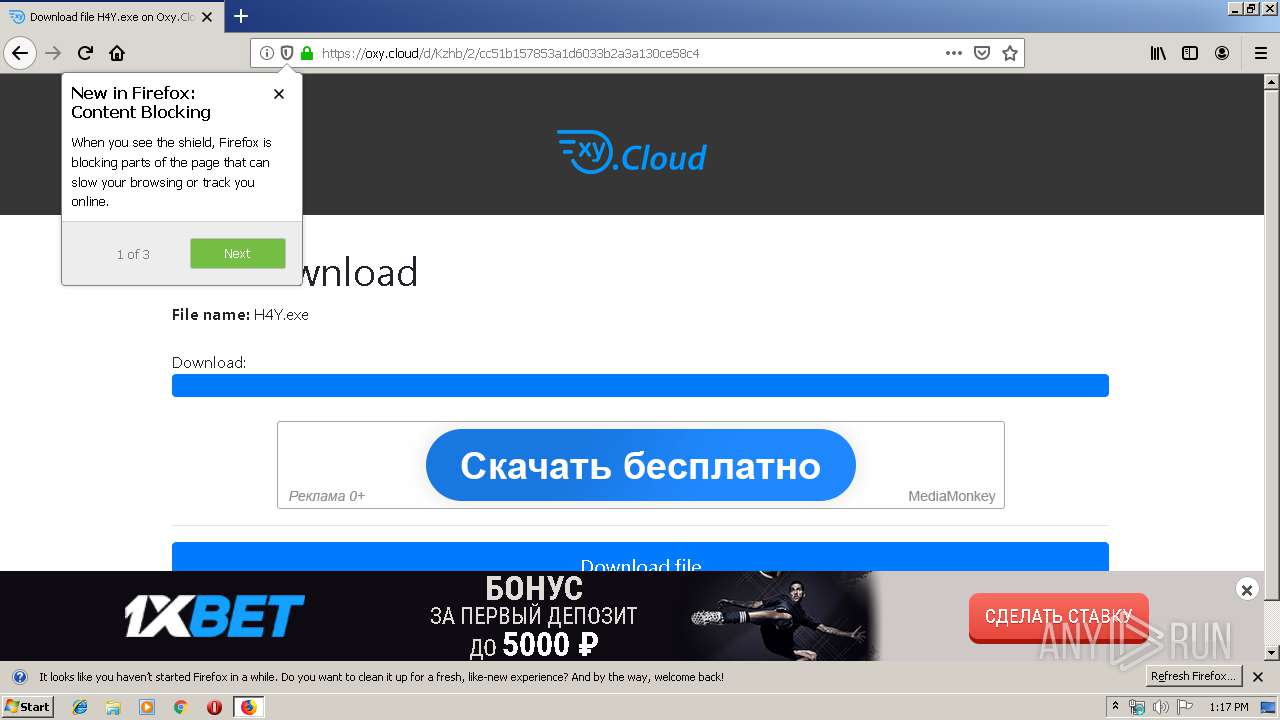
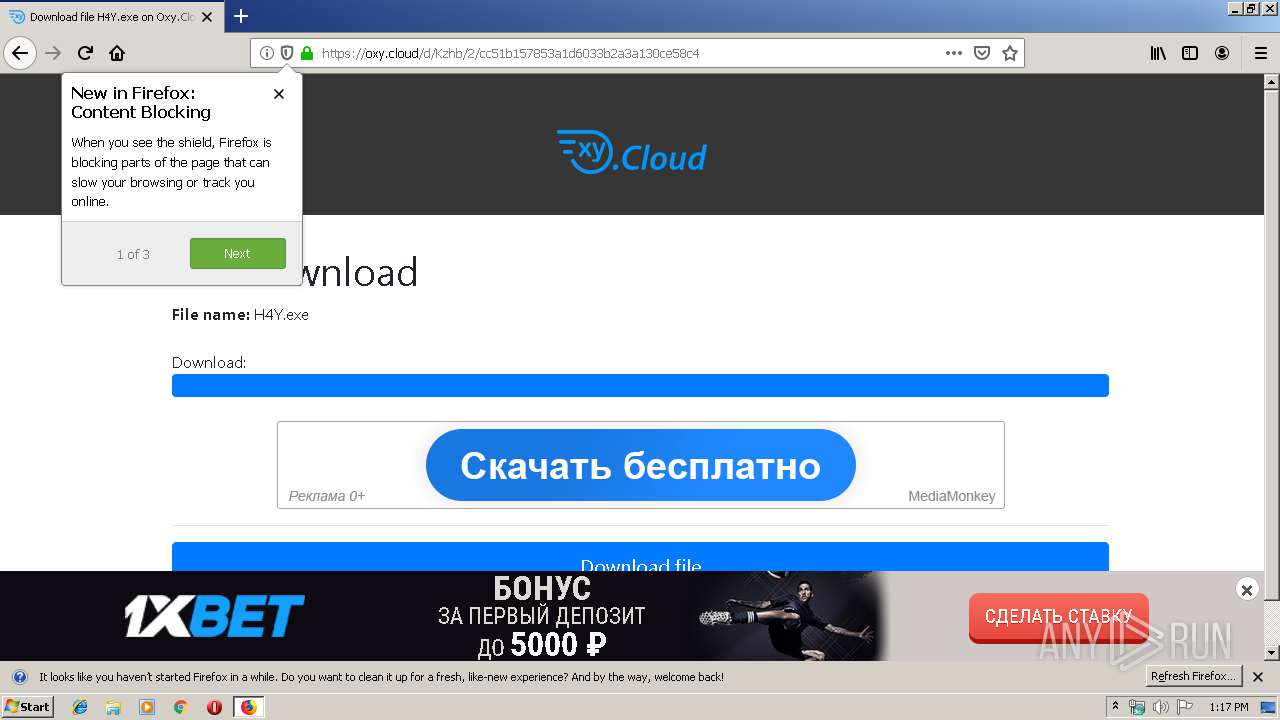
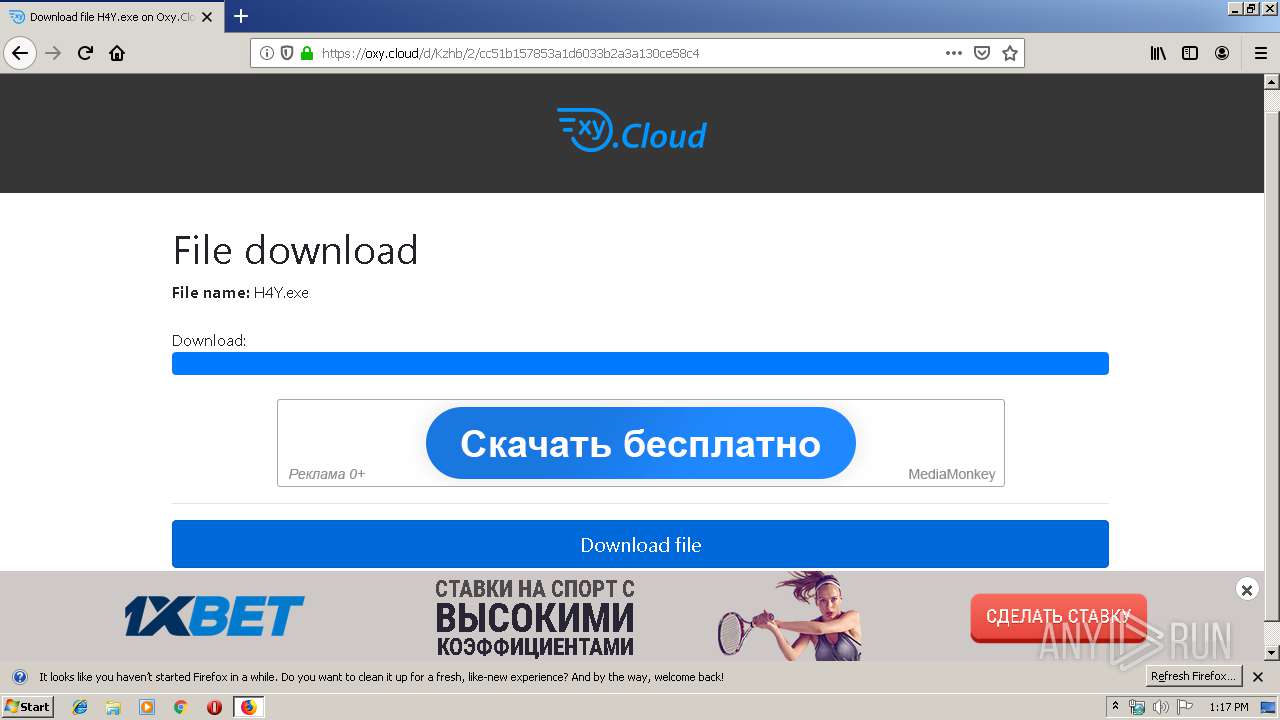
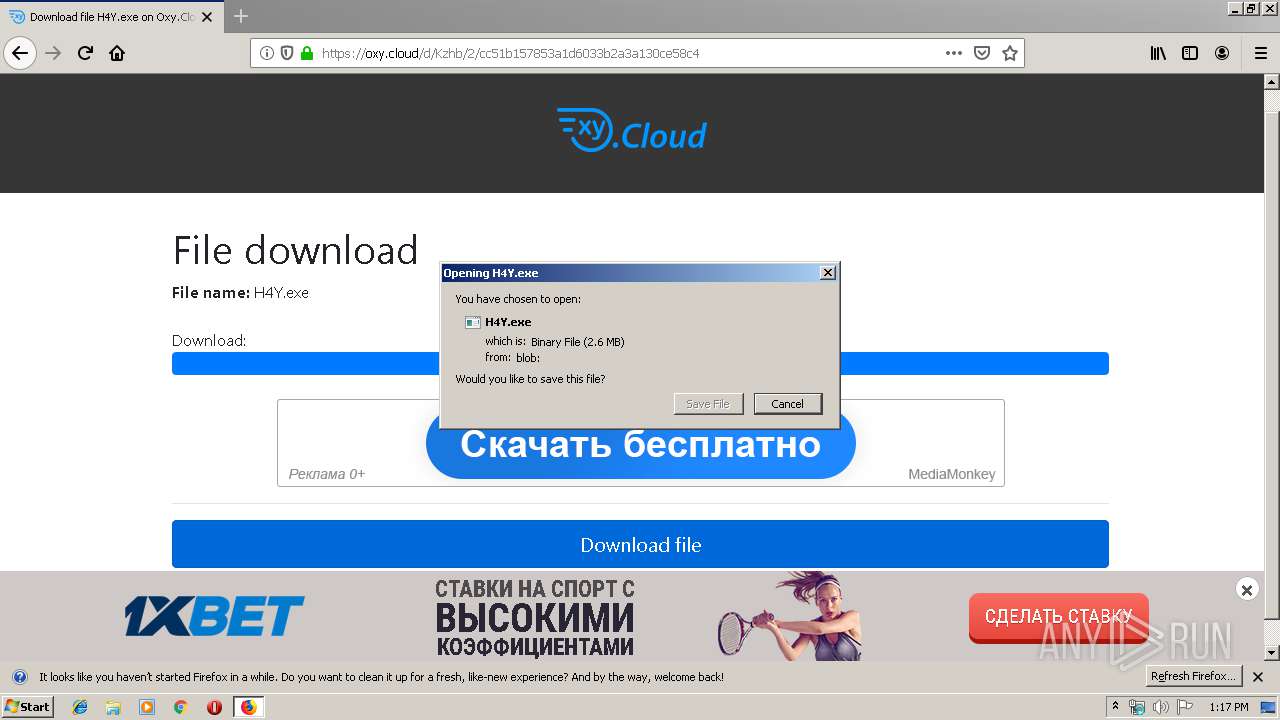
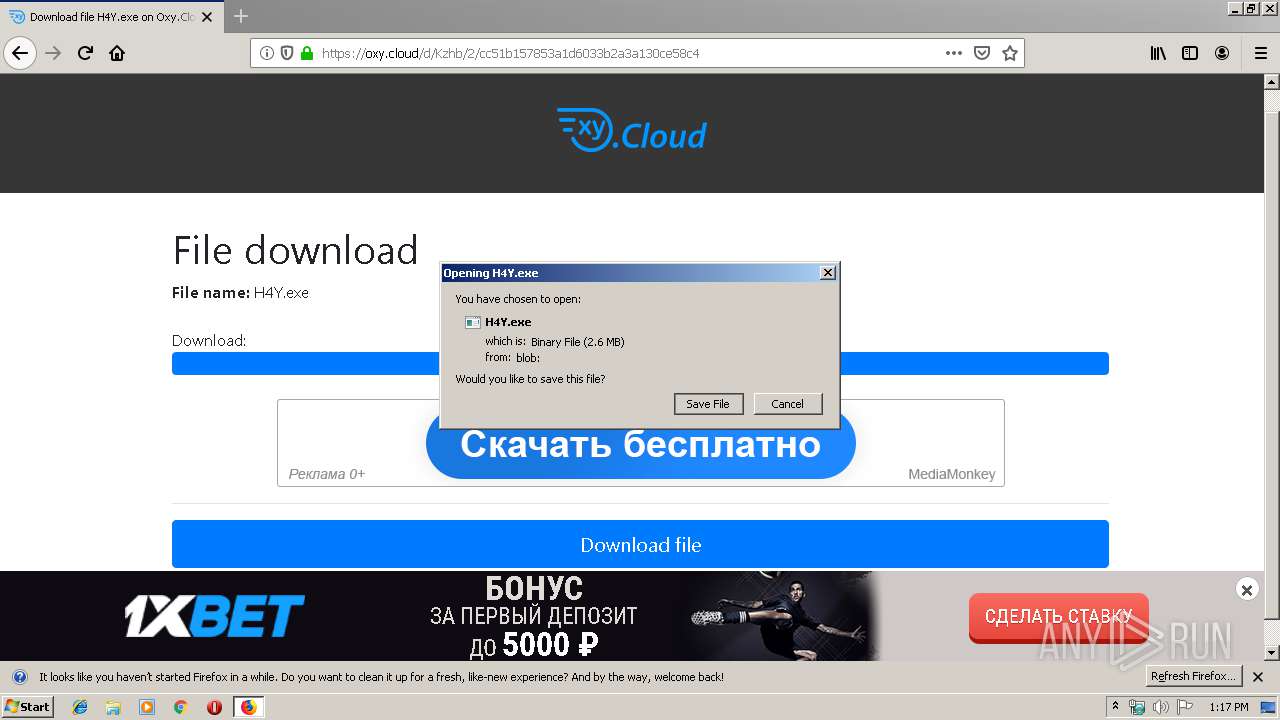
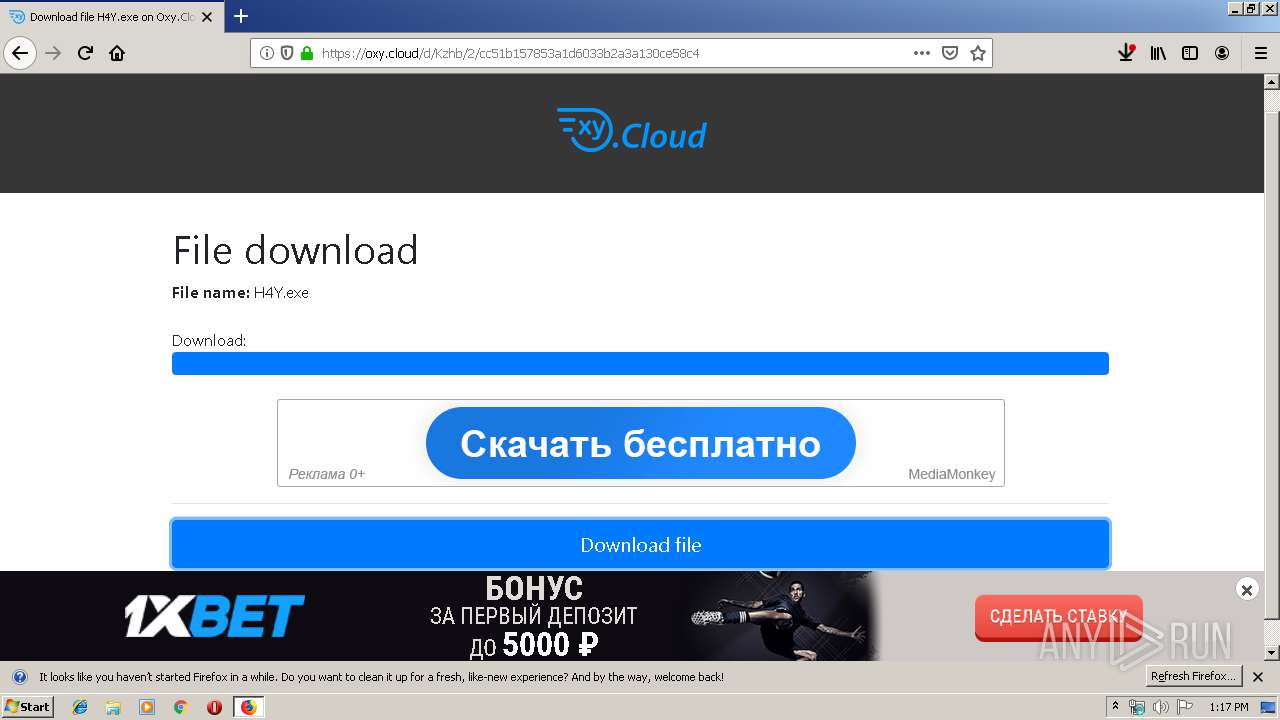
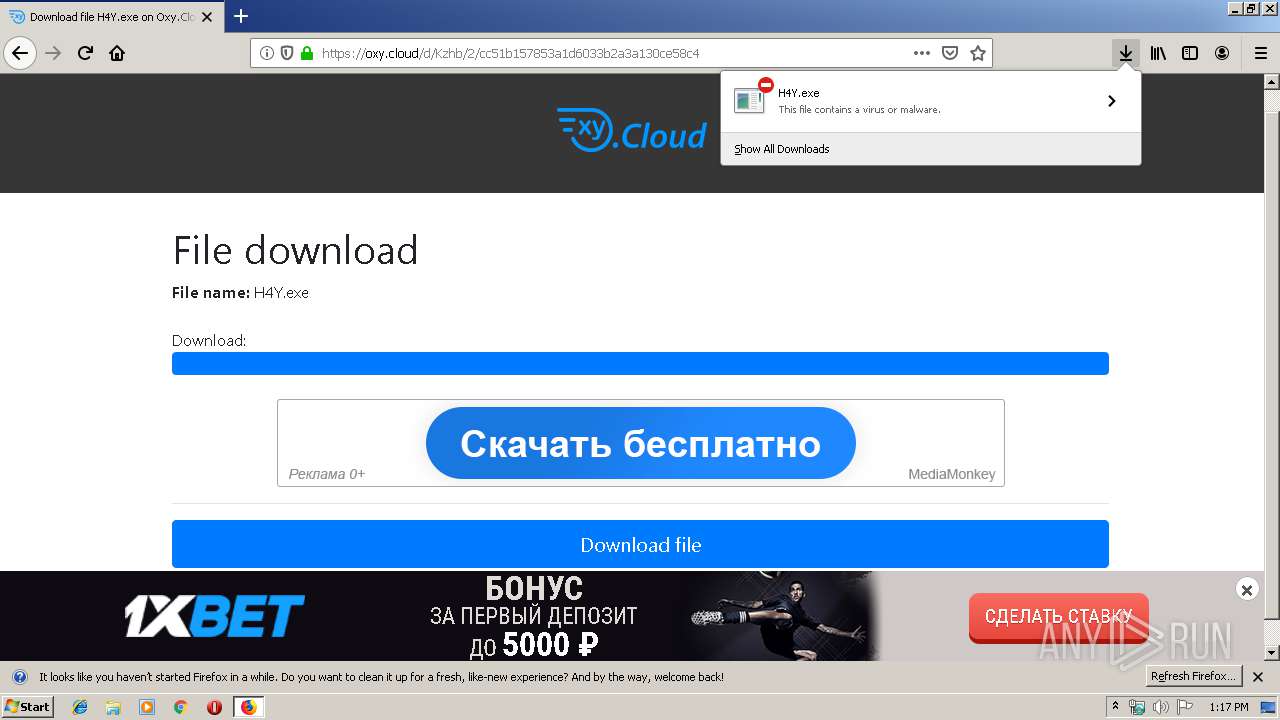
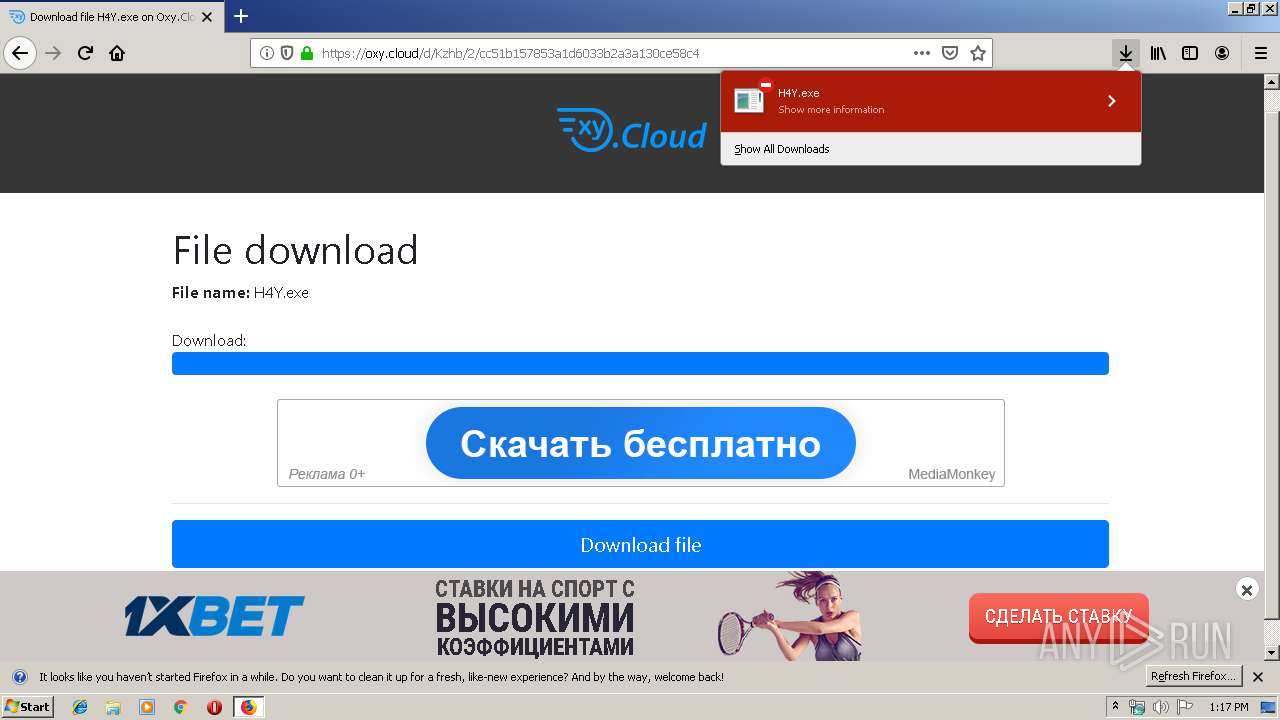
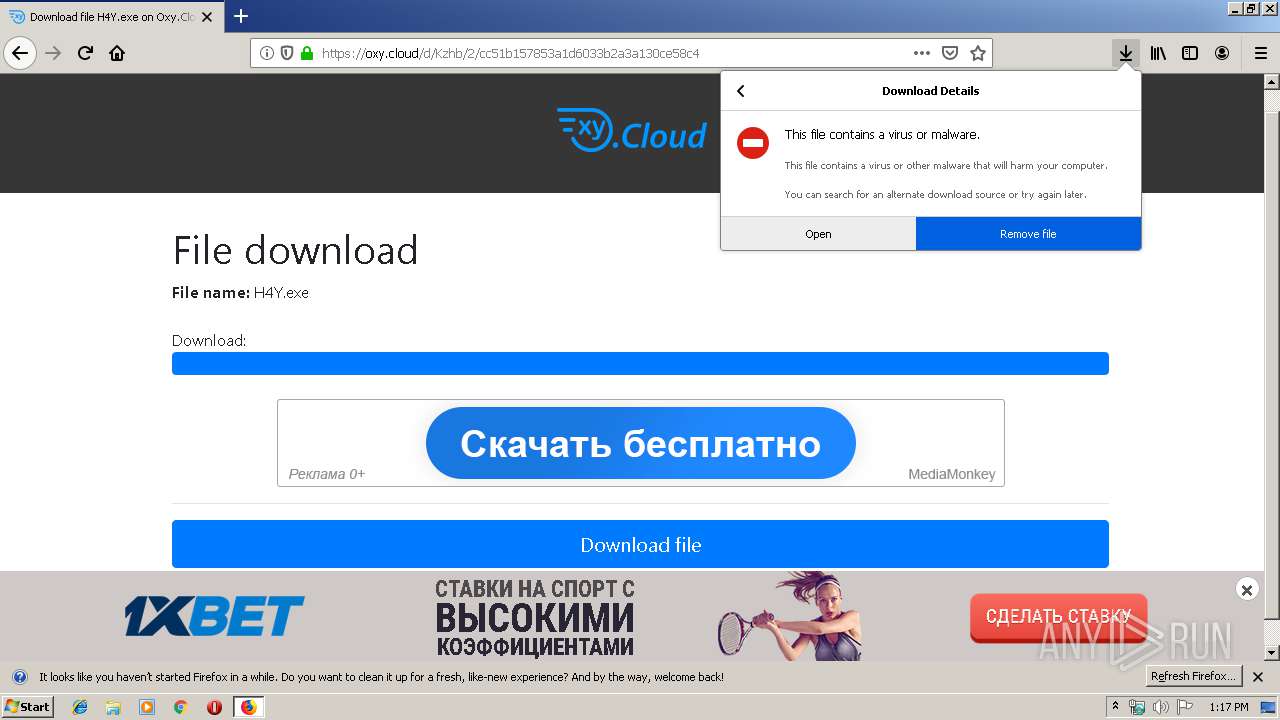
| URL: | https://oxy.cloud/d/Kzhb |
| Full analysis: | https://app.any.run/tasks/8b9e02b5-4901-46fd-8683-890f026b10ff |
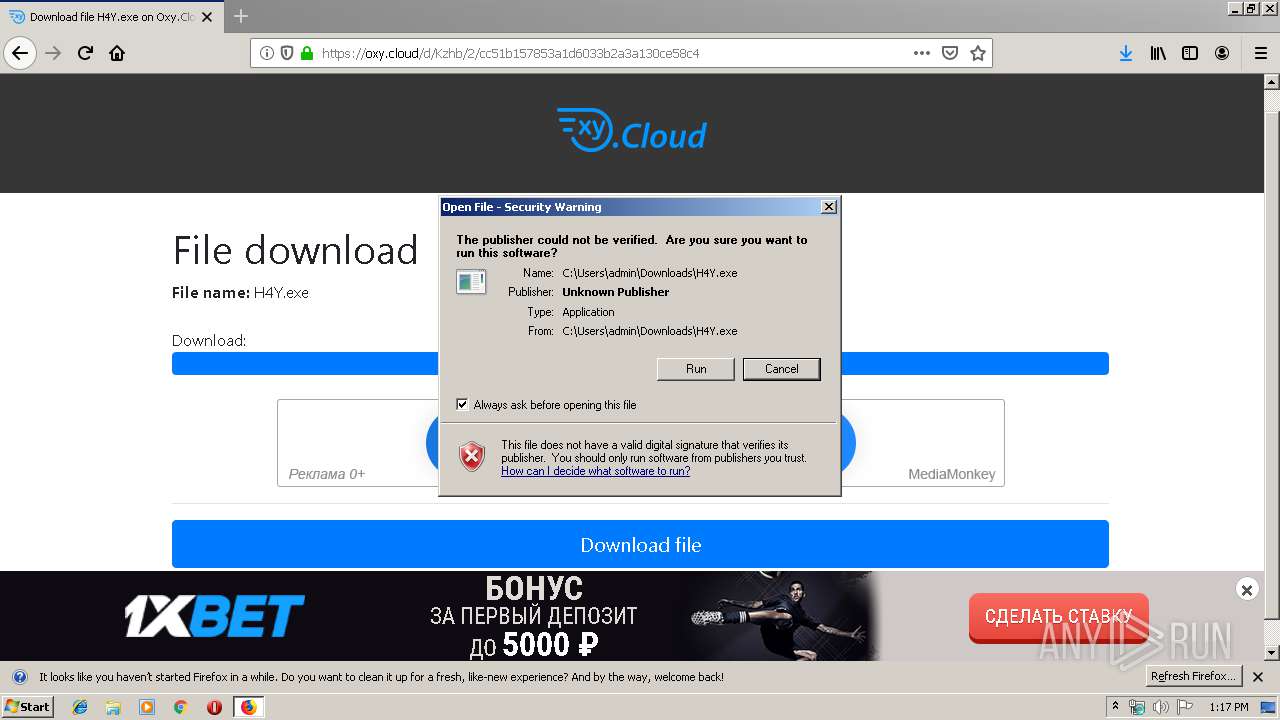
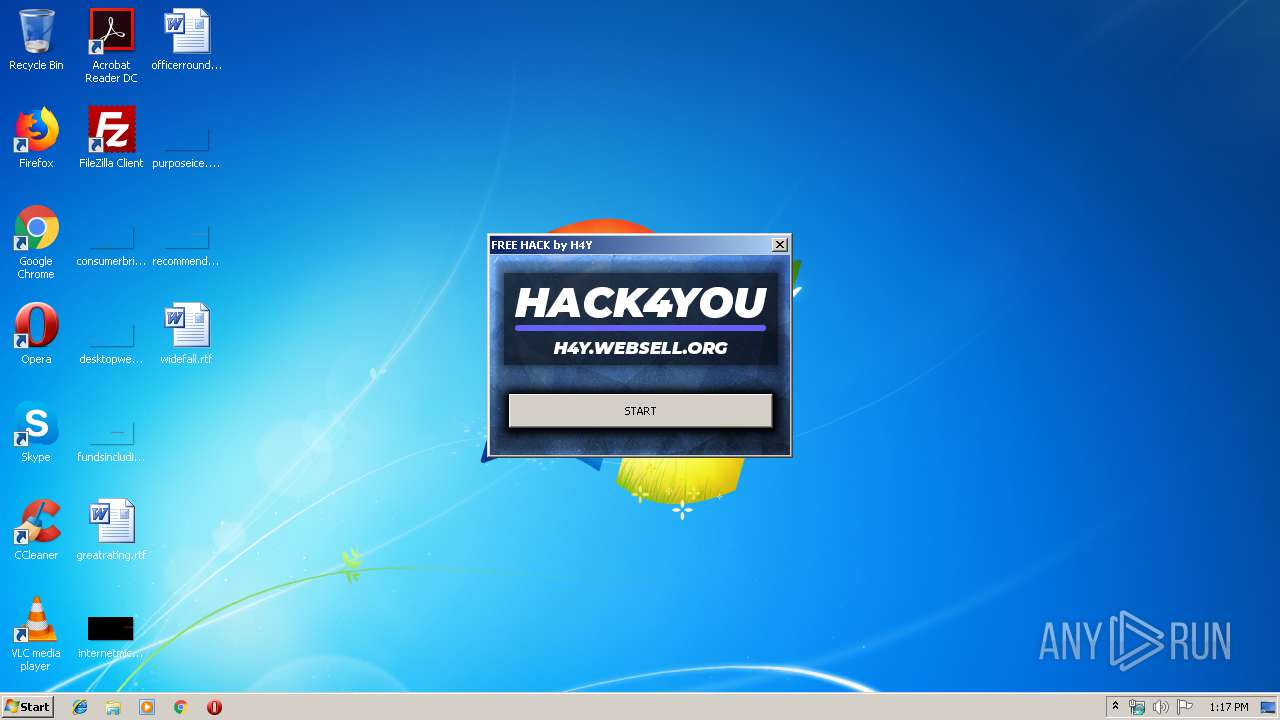
| Verdict: | Malicious activity |
| Threats: | AZORult can steal banking information, including passwords and credit card details, as well as cryptocurrency. This constantly updated information stealer malware should not be taken lightly, as it continues to be an active threat. |
| Analysis date: | December 27, 2019, 13:16:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | F18E6930289687B70FD00AFC0AC6E85B |
| SHA1: | 71011296EA2B64571AEB3EBA5D4D0117C72BB94A |
| SHA256: | F3BF668FFE1B8B97A5BF96FAB80BAFEB77710F8207CCDB5FCDAB403DB28E7201 |
| SSDEEP: | 3:N8UOQGd:2UOh |
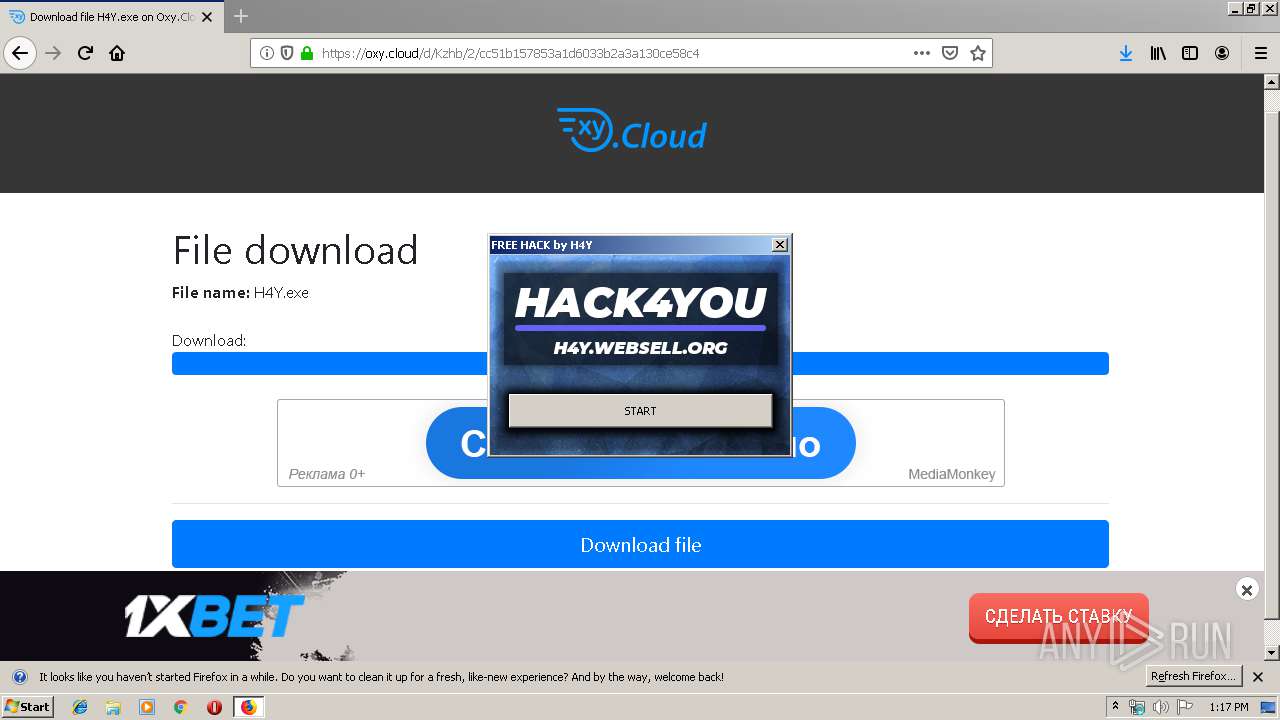
MALICIOUS
Application was dropped or rewritten from another process
- H4Y.exe (PID: 2276)
- conhost.exe (PID: 600)
- h4y.exe (PID: 716)
AZORULT was detected
- vbc.exe (PID: 2076)
Connects to CnC server
- vbc.exe (PID: 2076)
Actions looks like stealing of personal data
- vbc.exe (PID: 2076)
Loads dropped or rewritten executable
- vbc.exe (PID: 2076)
SUSPICIOUS
Creates files in the program directory
- firefox.exe (PID: 1956)
Creates files in the user directory
- H4Y.exe (PID: 2276)
- conhost.exe (PID: 600)
- vbc.exe (PID: 2076)
Executable content was dropped or overwritten
- H4Y.exe (PID: 2276)
- conhost.exe (PID: 600)
- firefox.exe (PID: 1956)
- vbc.exe (PID: 2076)
Executes scripts
- h4y.exe (PID: 716)
Reads the cookies of Google Chrome
- vbc.exe (PID: 2076)
Reads the cookies of Mozilla Firefox
- vbc.exe (PID: 2076)
INFO
Application launched itself
- firefox.exe (PID: 2800)
- firefox.exe (PID: 1956)
Reads CPU info
- firefox.exe (PID: 1956)
Creates files in the user directory
- firefox.exe (PID: 1956)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
46
Monitored processes
11
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 600 | "C:\Users\admin\AppData\Roaming\conhost.exe" | C:\Users\admin\AppData\Roaming\conhost.exe | H4Y.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.17763.404 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 716 | "C:\Users\admin\AppData\Roaming\h4y.exe" | C:\Users\admin\AppData\Roaming\h4y.exe | — | conhost.exe | |||||||||||
User: admin Company: ys5mlvfzniu Integrity Level: MEDIUM Description: yvarrdq5zg1 Exit code: 0 Version: 0.1.8.0 Modules
| |||||||||||||||
| 1908 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="1956.3.818885202\1431381812" -childID 1 -isForBrowser -prefsHandle 1360 -prefMapHandle 1684 -prefsLen 1 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 1956 "\\.\pipe\gecko-crash-server-pipe.1956" 1712 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1952 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="1956.0.948578205\2003081460" -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 1956 "\\.\pipe\gecko-crash-server-pipe.1956" 1164 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 1 Version: 68.0.1 Modules
| |||||||||||||||
| 1956 | "C:\Program Files\Mozilla Firefox\firefox.exe" https://oxy.cloud/d/Kzhb | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2076 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | h4y.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5420 Modules
| |||||||||||||||
| 2112 | "C:\Program Files\Mozilla Firefox\pingsender.exe" https://incoming.telemetry.mozilla.org/submit/telemetry/1d7afbd1-adf8-423e-9b8d-22c06c9ba80d/main/Firefox/68.0.1/release/20190717172542?v=4 C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\saved-telemetry-pings\1d7afbd1-adf8-423e-9b8d-22c06c9ba80d | C:\Program Files\Mozilla Firefox\pingsender.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Foundation Integrity Level: MEDIUM Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2160 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="1956.13.1087627498\852165200" -childID 2 -isForBrowser -prefsHandle 2324 -prefMapHandle 2328 -prefsLen 5996 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 1956 "\\.\pipe\gecko-crash-server-pipe.1956" 2816 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2256 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="1956.20.1867212355\340941007" -childID 3 -isForBrowser -prefsHandle 3896 -prefMapHandle 3540 -prefsLen 7195 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 1956 "\\.\pipe\gecko-crash-server-pipe.1956" 3548 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2276 | "C:\Users\admin\Downloads\H4Y.exe" | C:\Users\admin\Downloads\H4Y.exe | firefox.exe | ||||||||||||
User: admin Company: HACK4YOU Integrity Level: MEDIUM Description: HACK4YOU Exit code: 0 Version: 2.0.3.9 Modules
| |||||||||||||||
Total events
1 676
Read events
1 624
Write events
52
Delete events
0
Modification events
| (PID) Process: | (1956) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 6277721703000000 | |||
| (PID) Process: | (2800) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: 24BE6F1703000000 | |||
| (PID) Process: | (1956) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 1 | |||
| (PID) Process: | (1956) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1956) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1956) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1956) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2112) pingsender.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2112) pingsender.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000093000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2112) pingsender.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
53
Suspicious files
140
Text files
54
Unknown types
102
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1956 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 1956 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 1956 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 1956 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs.js | text | |
MD5:— | SHA256:— | |||
| 1956 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-child-current.bin | binary | |
MD5:— | SHA256:— | |||
| 1956 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:— | SHA256:— | |||
| 1956 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\except-flashallow-digest256.sbstore | — | |
MD5:— | SHA256:— | |||
| 1956 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\except-flashsubdoc-digest256.pset | — | |
MD5:— | SHA256:— | |||
| 1956 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\except-flashsubdoc-digest256.sbstore | — | |
MD5:— | SHA256:— | |||
| 1956 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\google4\goog-badbinurl-proto.metadata | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
74
DNS requests
164
Threats
17
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
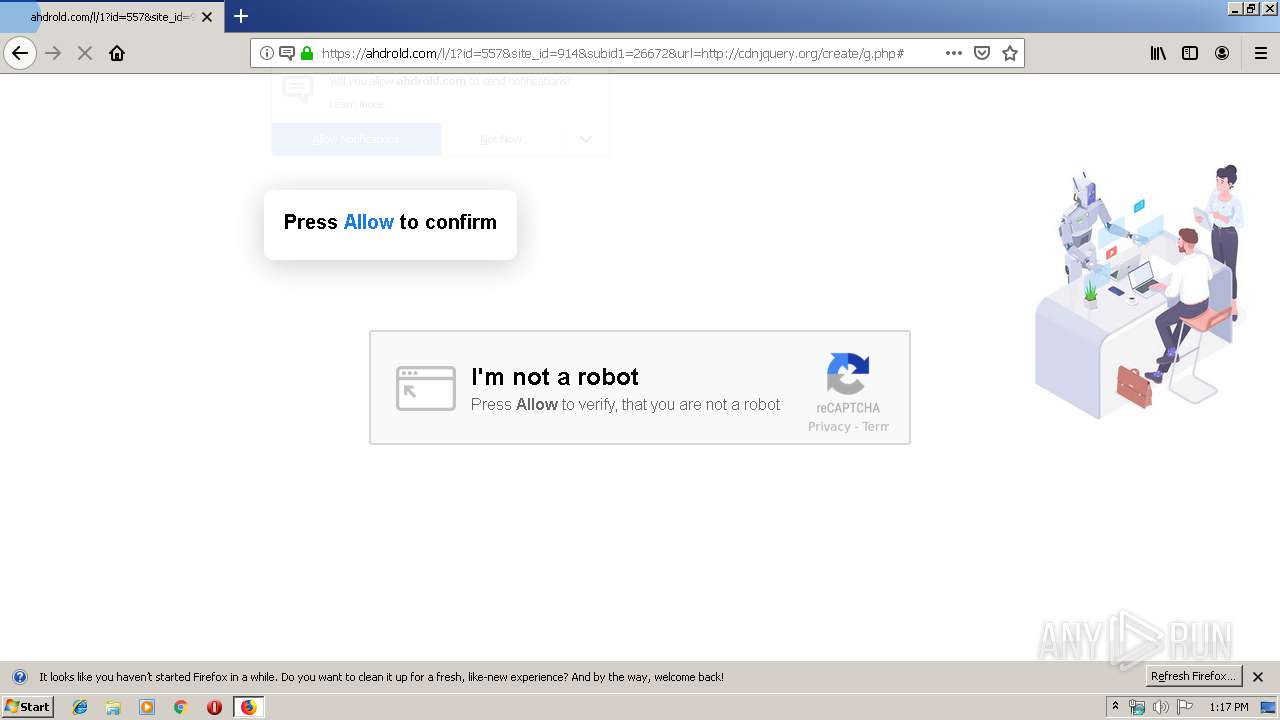
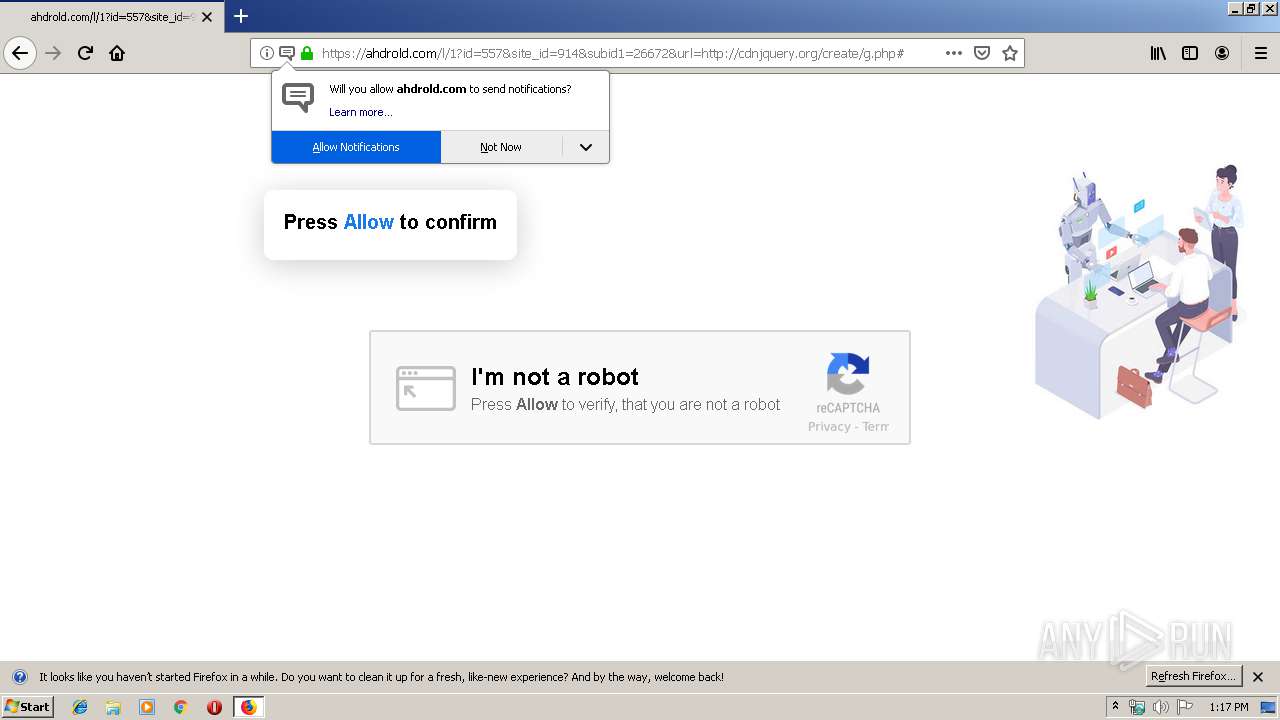
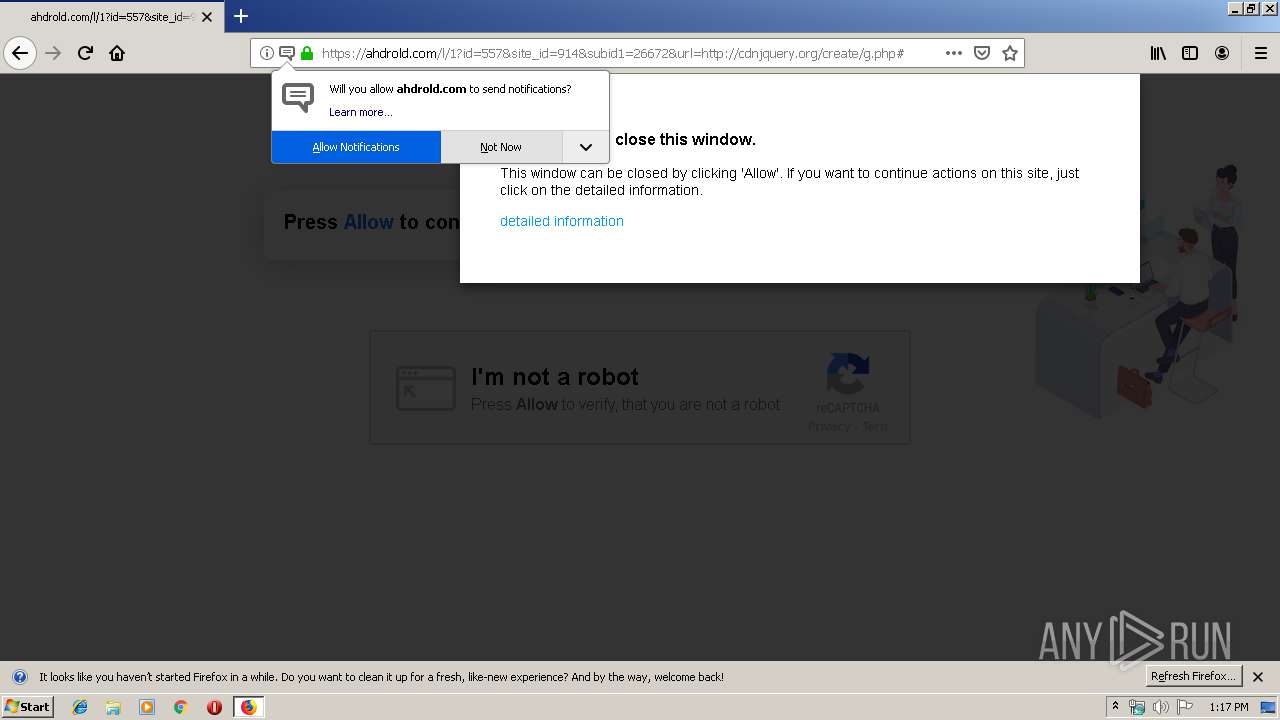
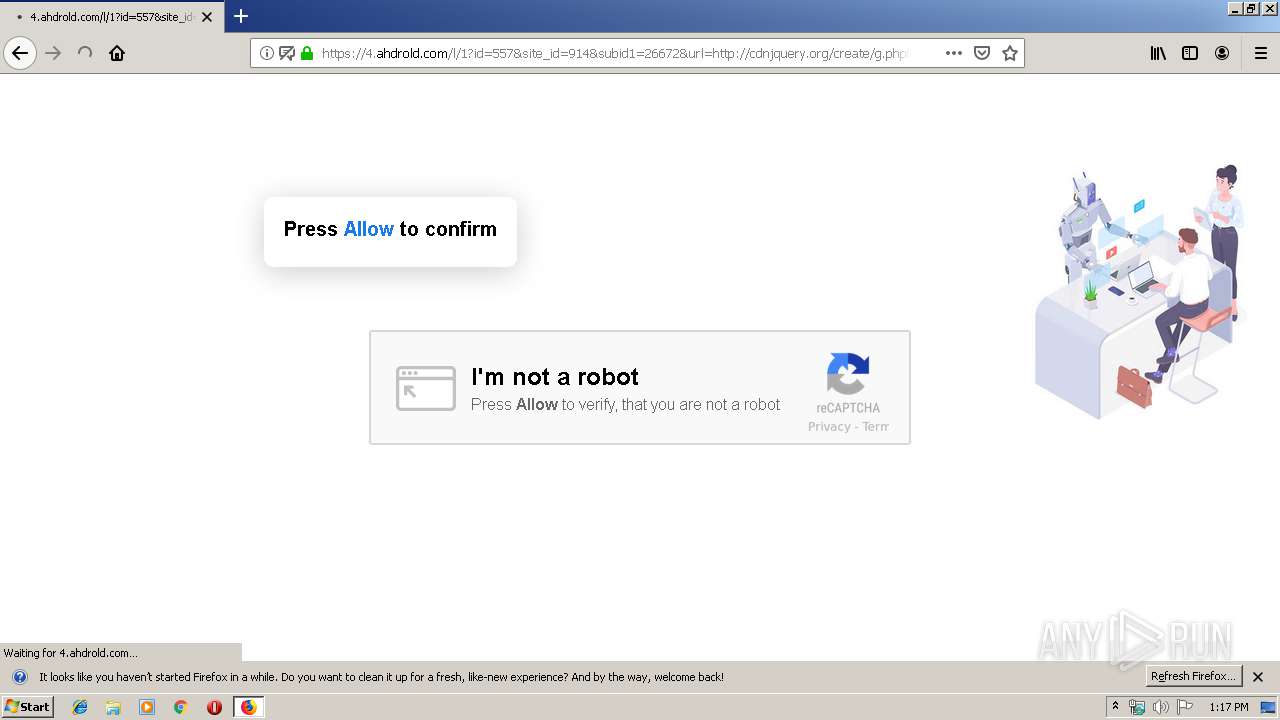
1956 | firefox.exe | GET | 302 | 104.28.2.72:80 | http://cdnjquery.org/create/go.php?potok=kGRGpr&subid_1=26672&bpredirect=aHR0cHM6Ly9veHkuY2xvdWQvZC9LemhiLzIvY2M1MWIxNTc4NTNhMWQ2MDMzYjJhM2ExMzBjZTU4YzQ%3D | US | — | — | shared |
1956 | firefox.exe | POST | 200 | 216.58.205.227:80 | http://ocsp.pki.goog/gts1o1 | US | der | 472 b | whitelisted |
1956 | firefox.exe | POST | 200 | 2.16.186.11:80 | http://ocsp.int-x3.letsencrypt.org/ | unknown | der | 527 b | whitelisted |
1956 | firefox.exe | GET | 200 | 104.28.2.72:80 | http://cdnjquery.org/.well-known/http-opportunistic | US | text | 94 b | shared |
1956 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
1956 | firefox.exe | POST | 200 | 5.45.205.243:80 | http://yandex.ocsp-responder.com/ | RU | der | 1.52 Kb | whitelisted |
1956 | firefox.exe | POST | 200 | 216.58.205.227:80 | http://ocsp.pki.goog/gts1o1 | US | der | 472 b | whitelisted |
1956 | firefox.exe | POST | 200 | 5.45.205.243:80 | http://yandex.ocsp-responder.com/ | RU | der | 1.52 Kb | whitelisted |
1956 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 279 b | whitelisted |
1956 | firefox.exe | GET | 200 | 2.16.186.112:80 | http://detectportal.firefox.com/success.txt | unknown | text | 8 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1956 | firefox.exe | 13.35.253.28:443 | snippets.cdn.mozilla.net | — | US | malicious |
1956 | firefox.exe | 35.163.220.136:443 | tiles.services.mozilla.com | Amazon.com, Inc. | US | unknown |
1956 | firefox.exe | 104.28.3.50:443 | oxy.cloud | Cloudflare Inc | US | shared |
1956 | firefox.exe | 2.16.186.112:80 | detectportal.firefox.com | Akamai International B.V. | — | whitelisted |
1956 | firefox.exe | 52.89.218.39:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
1956 | firefox.exe | 104.17.64.4:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | unknown |
1956 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1956 | firefox.exe | 172.217.18.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
1956 | firefox.exe | 104.18.47.227:443 | adsfire.net | Cloudflare Inc | US | shared |
1956 | firefox.exe | 5.45.205.243:80 | yandex.ocsp-responder.com | YANDEX LLC | RU | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
autopush.prod.mozaws.net |
| whitelisted |
snippets.cdn.mozilla.net |
| whitelisted |
d228z91au11ukj.cloudfront.net |
| whitelisted |
tiles.services.mozilla.com |
| whitelisted |
tiles.r53-2.services.mozilla.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1 ETPRO signatures available at the full report
Process | Message |
|---|---|
conhost.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|