| File name: | Shipment Document BL,INV and packing list.jpg.exe |
| Full analysis: | https://app.any.run/tasks/bb135fc1-aff3-44a8-945b-bd175431fa8c |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | November 13, 2023, 12:03:50 |
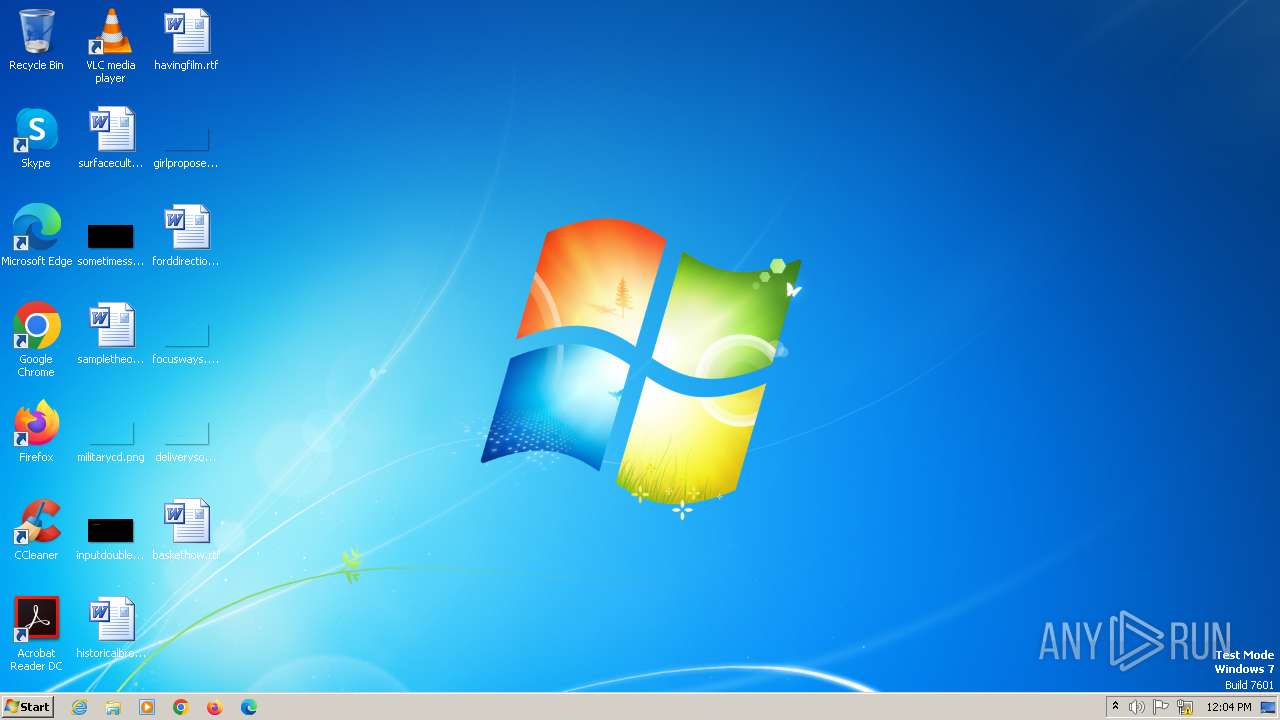
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | AA54CC75551A0903C7C6AD095791CDD7 |
| SHA1: | 47D372A19FC28E8A825ADB9511118FB15FA6C9BA |
| SHA256: | F36F3336AEDC47E7EC061CC5A11589D9E3ADCFF96BBC805A8DA7AC0182D40E22 |
| SSDEEP: | 24576:EVDEvD+JgP0oIkJroobSJLzYk0y37PK0CSozvcxGiy5bcQv:EVDEvD+JgP0oIkJrooYzYty37PKjSozd |
MALICIOUS
FORMBOOK has been detected (YARA)
- control.exe (PID: 2216)
SUSPICIOUS
Starts CMD.EXE for commands execution
- control.exe (PID: 2216)
Application launched itself
- Shipment Document BL,INV and packing list.jpg.exe (PID: 2328)
Reads the Internet Settings
- control.exe (PID: 2216)
INFO
Checks supported languages
- Shipment Document BL,INV and packing list.jpg.exe (PID: 2328)
- Shipment Document BL,INV and packing list.jpg.exe (PID: 2844)
Reads the computer name
- Shipment Document BL,INV and packing list.jpg.exe (PID: 2328)
- Shipment Document BL,INV and packing list.jpg.exe (PID: 2844)
Manual execution by a user
- control.exe (PID: 2216)
Checks proxy server information
- control.exe (PID: 2216)
Reads the machine GUID from the registry
- Shipment Document BL,INV and packing list.jpg.exe (PID: 2328)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Formbook
(PID) Process(2216) control.exe
C2www.i-ooedo.com/fs35/
Strings (79)USERNAME
LOCALAPPDATA
USERPROFILE
APPDATA
TEMP
ProgramFiles
CommonProgramFiles
ALLUSERSPROFILE
/c copy "
/c del "
\Run
\Policies
\Explorer
\Registry\User
\Registry\Machine
\SOFTWARE\Microsoft\Windows\CurrentVersion
Office\15.0\Outlook\Profiles\Outlook\
NT\CurrentVersion\Windows Messaging Subsystem\Profiles\Outlook\
\SOFTWARE\Mozilla\Mozilla
\Mozilla
Username:
Password:
formSubmitURL
usernameField
encryptedUsername
encryptedPassword
\logins.json
\signons.sqlite
\Microsoft\Vault\
SELECT encryptedUsername, encryptedPassword, formSubmitURL FROM moz_logins
\Google\Chrome\User Data\Default\Login Data
SELECT origin_url, username_value, password_value FROM logins
.exe
.com
.scr
.pif
.cmd
.bat
ms
win
gdi
mfc
vga
igfx
user
help
config
update
regsvc
chkdsk
systray
audiodg
certmgr
autochk
taskhost
colorcpl
services
IconCache
ThumbCache
Cookies
SeDebugPrivilege
SeShutdownPrivilege
\BaseNamedObjects
config.php
POST
HTTP/1.1
Host:
Connection: close
Content-Length:
Cache-Control: no-cache
Origin: http://
User-Agent: Mozilla Firefox/4.0
Content-Type: application/x-www-form-urlencoded
Accept: */*
Referer: http://
Accept-Language: en-US
Accept-Encoding: gzip, deflate
dat=
f-start
f-end
Decoy C2 (64)latechdz.com
sdp-ploce.com
ss203.site
sm6yuy.net
needstothink.com
heginstwp.com
blueplumespirit.com
vemconferirshop.click
yorent-auto.com
eleononaly.com
medicalspacelocators.com
7law.info
imacanberra.online
bbtyss.top
onlyanfans.com
varenty.com
fappies.shop
313865.com
hongpools.com
babkacuisine.xyz
usofty.com
jdjnxsu.com
teammonitoringservices.com
retortprocessinglab.com
rooferstakeoff.com
hansonelecs.com
em4ai.com
urbiznet.com
merchantgeniussaiyanflame.com
elegance-x-agency.com
cheekyfancy.com
ciaraile-hair.store
exactix.online
essentiallymotherearth.com
thebrollybuddy.com
associacaoacademicaguarda.com
manjort.xyz
mylifestylelounge.com
ser25kgr.monster
abbiejhooper.xyz
mjp77.com
dompompomdompom.shop
sugikougei.com
tacosantojrz.com
7yyhdjwwqq.com
vri4d.com
53b9fd8cfbfb.info
xlookcoins.top
uncongneniality.shop
coats-34172.bond
amazingpawpalace.com
actionkillsfear.com
supportlakecentral.com
xn--9kq7ik28o.club
lasermywords.com
t5-1682468.xyz
eastonelitesoftball.com
bagpackgalaxy.com
petlove6.com
fryconnect.online
autolusaccess.com
planetbravos.com
80smaoi.top
iit.world
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (72.2) |
|---|---|---|
| .scr | | | Windows screen saver (12.9) |
| .dll | | | Win32 Dynamic Link Library (generic) (6.4) |
| .exe | | | Win32 Executable (generic) (4.4) |
| .exe | | | Generic Win/DOS Executable (1.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2080:06:01 07:08:40+02:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 559104 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x8a5fe |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Sxs Tracing Tool |
| FileVersion: | 1.0.0.0 |
| InternalName: | jHDiP.exe |
| LegalCopyright: | Copyright © 2021 |
| LegalTrademarks: | - |
| OriginalFileName: | jHDiP.exe |
| ProductName: | Sxs Tracing Tool |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
36
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1944 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2216 | "C:\Windows\SysWOW64\control.exe" | C:\Windows\SysWOW64\control.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Control Panel Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
Formbook(PID) Process(2216) control.exe C2www.i-ooedo.com/fs35/ Strings (79)USERNAME LOCALAPPDATA USERPROFILE APPDATA TEMP ProgramFiles CommonProgramFiles ALLUSERSPROFILE /c copy " /c del " \Run \Policies \Explorer \Registry\User \Registry\Machine \SOFTWARE\Microsoft\Windows\CurrentVersion Office\15.0\Outlook\Profiles\Outlook\ NT\CurrentVersion\Windows Messaging Subsystem\Profiles\Outlook\ \SOFTWARE\Mozilla\Mozilla \Mozilla Username: Password: formSubmitURL usernameField encryptedUsername encryptedPassword \logins.json \signons.sqlite \Microsoft\Vault\ SELECT encryptedUsername, encryptedPassword, formSubmitURL FROM moz_logins \Google\Chrome\User Data\Default\Login Data SELECT origin_url, username_value, password_value FROM logins .exe .com .scr .pif .cmd .bat ms win gdi mfc vga igfx user help config update regsvc chkdsk systray audiodg certmgr autochk taskhost colorcpl services IconCache ThumbCache Cookies SeDebugPrivilege SeShutdownPrivilege \BaseNamedObjects config.php POST HTTP/1.1 Host: Connection: close Content-Length: Cache-Control: no-cache Origin: http:// User-Agent: Mozilla Firefox/4.0 Content-Type: application/x-www-form-urlencoded Accept: */* Referer: http:// Accept-Language: en-US Accept-Encoding: gzip, deflate
dat= f-start f-end Decoy C2 (64)latechdz.com sdp-ploce.com ss203.site sm6yuy.net needstothink.com heginstwp.com blueplumespirit.com vemconferirshop.click yorent-auto.com eleononaly.com medicalspacelocators.com 7law.info imacanberra.online bbtyss.top onlyanfans.com varenty.com fappies.shop 313865.com hongpools.com babkacuisine.xyz usofty.com jdjnxsu.com teammonitoringservices.com retortprocessinglab.com rooferstakeoff.com hansonelecs.com em4ai.com urbiznet.com merchantgeniussaiyanflame.com elegance-x-agency.com cheekyfancy.com ciaraile-hair.store exactix.online essentiallymotherearth.com thebrollybuddy.com associacaoacademicaguarda.com manjort.xyz mylifestylelounge.com ser25kgr.monster abbiejhooper.xyz mjp77.com dompompomdompom.shop sugikougei.com tacosantojrz.com 7yyhdjwwqq.com vri4d.com 53b9fd8cfbfb.info xlookcoins.top uncongneniality.shop coats-34172.bond amazingpawpalace.com actionkillsfear.com supportlakecentral.com xn--9kq7ik28o.club lasermywords.com t5-1682468.xyz eastonelitesoftball.com bagpackgalaxy.com petlove6.com fryconnect.online autolusaccess.com planetbravos.com 80smaoi.top iit.world | |||||||||||||||
| 2328 | "C:\Users\admin\AppData\Local\Temp\Shipment Document BL,INV and packing list.jpg.exe" | C:\Users\admin\AppData\Local\Temp\Shipment Document BL,INV and packing list.jpg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Sxs Tracing Tool Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2844 | "C:\Users\admin\AppData\Local\Temp\Shipment Document BL,INV and packing list.jpg.exe" | C:\Users\admin\AppData\Local\Temp\Shipment Document BL,INV and packing list.jpg.exe | — | Shipment Document BL,INV and packing list.jpg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Sxs Tracing Tool Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2896 | /c del "C:\Users\admin\AppData\Local\Temp\Shipment Document BL,INV and packing list.jpg.exe" | C:\Windows\SysWOW64\cmd.exe | — | control.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
352
Read events
335
Write events
17
Delete events
0
Modification events
| (PID) Process: | (1944) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Action Center\Checks\{C8E6F269-B90A-4053-A3BE-499AFCEC98C4}.check.0 |
| Operation: | write | Name: | CheckSetting |
Value: 01000000D08C9DDF0115D1118C7A00C04FC297EB01000000088AF72B0747534094337F63DE35C94A000000000200000000001066000000010000200000003A7AE26404D75DF41C31FF40C5EA8CE90BAF74FA9E9BD7A9ACA34C7048350C1E000000000E8000000002000020000000BD2D56D46506C12C41A6A70B10E79EE53CB79EF36FD2BA8CDD2460CB8F4BE86A300000009B5D1418CBF2EB49F3C4BD4C21D58CA55B82FA3D3ED08AF0EF59D6C7ECAFC1055FA323A80FF7C154B1C9B60253392B6640000000DED9FDCC168073324C3013F1BB125E066EB1A2F09FD2C8E7CC7A793AA992E21EF1C942BF7294D04E036428704009B863B1CB981B97312E2530E3E816780CF7C9 | |||
| (PID) Process: | (2216) control.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2216) control.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2216) control.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2216) control.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000C1000000010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2216) control.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2216) control.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2216) control.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2216) control.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1944) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\156\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
11
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1944 | explorer.exe | GET | 301 | 188.114.97.3:80 | http://www.abbiejhooper.xyz/fs35/?1bhta6=dzNNkqvXSrqLk/11xLO4gWeaxe88QV8D1zeO2Fm139y8zP03qQPqlQBEIX+UMcConLT23Q==&bv=YV8dsLxxrVcxrDR | unknown | — | — | unknown |
1944 | explorer.exe | GET | 301 | 3.77.172.192:80 | http://www.eleononaly.com/fs35/?1bhta6=ObBUnqqnguzBalz1JfRu5Fd6j7RIcnBdskFVtM1FXEqE6WRXoZNOo1JvqDyURVXtoC16Jw==&bv=YV8dsLxxrVcxrDR | unknown | html | 166 b | unknown |
1944 | explorer.exe | GET | 403 | 34.98.99.30:80 | http://www.needstothink.com/fs35/?1bhta6=/UsAxpSA2SFsXln1L3v5OgmIbeqNAE4WVj5H/Kpq1DBTmVH8TxSFc0jRYclmAms6ZuKr4Q==&bv=YV8dsLxxrVcxrDR | unknown | html | 291 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
324 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1956 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1944 | explorer.exe | 188.114.97.3:80 | www.abbiejhooper.xyz | CLOUDFLARENET | NL | unknown |
1944 | explorer.exe | 172.232.187.235:80 | www.uncongneniality.shop | Akamai International B.V. | US | unknown |
2216 | control.exe | 172.232.187.235:80 | www.uncongneniality.shop | Akamai International B.V. | US | unknown |
1944 | explorer.exe | 3.77.172.192:80 | www.eleononaly.com | AMAZON-02 | DE | unknown |
1944 | explorer.exe | 34.98.99.30:80 | www.needstothink.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.abbiejhooper.xyz |
| unknown |
www.uncongneniality.shop |
| unknown |
www.eleononaly.com |
| unknown |
www.needstothink.com |
| unknown |