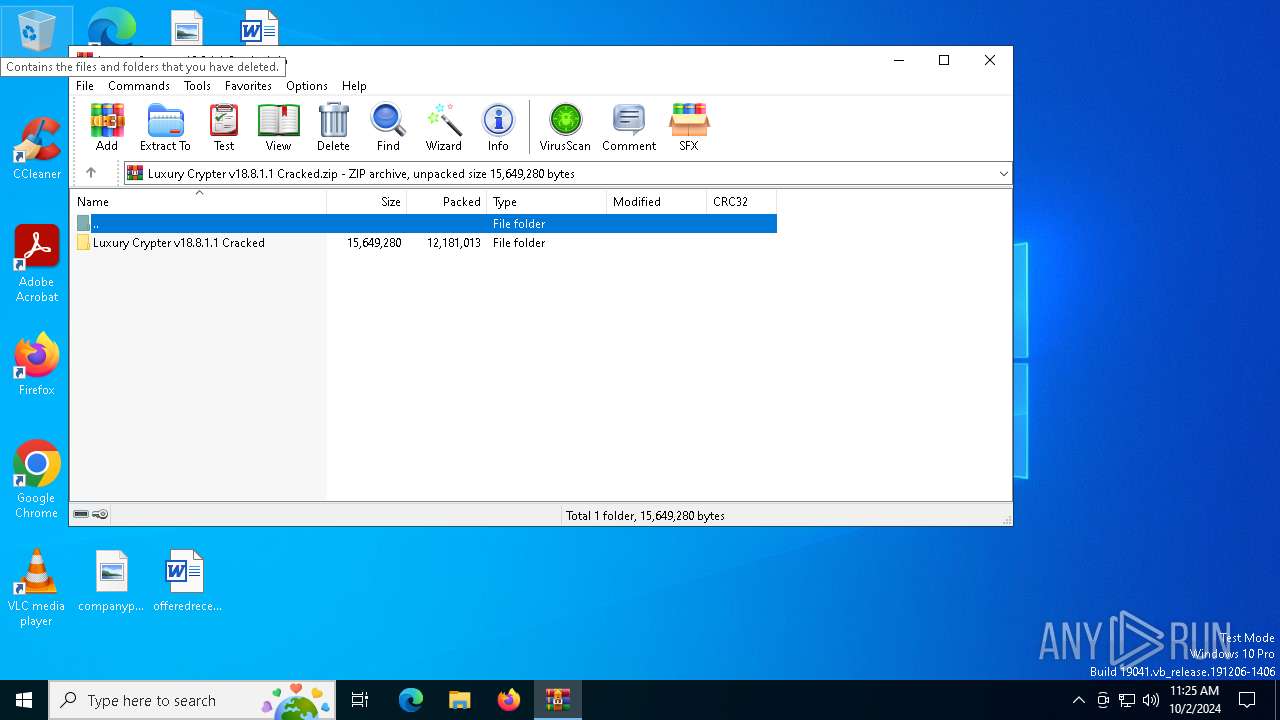
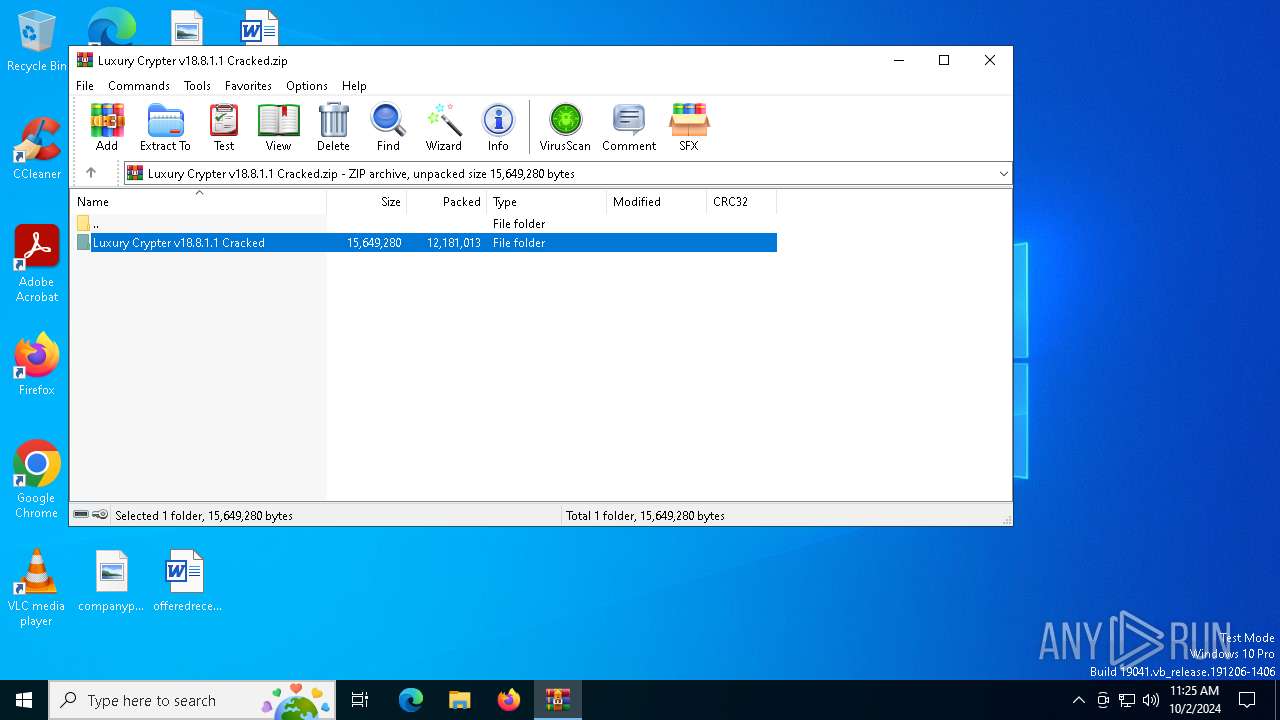
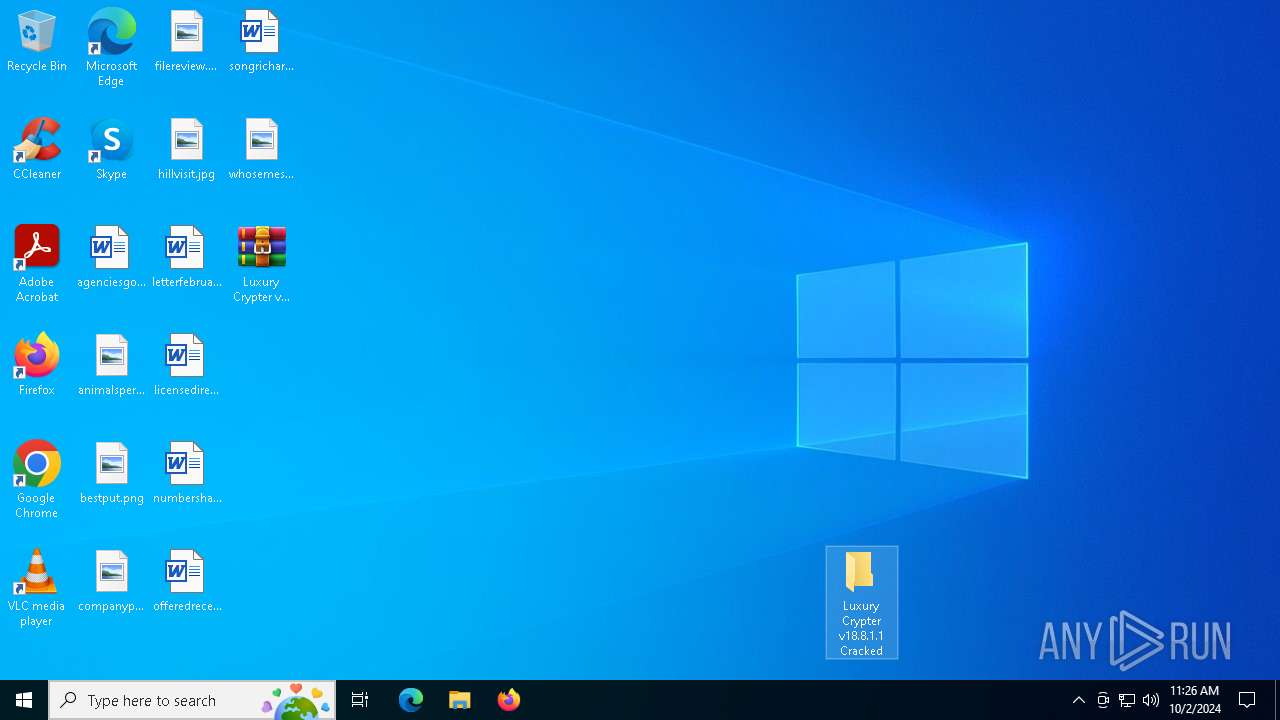
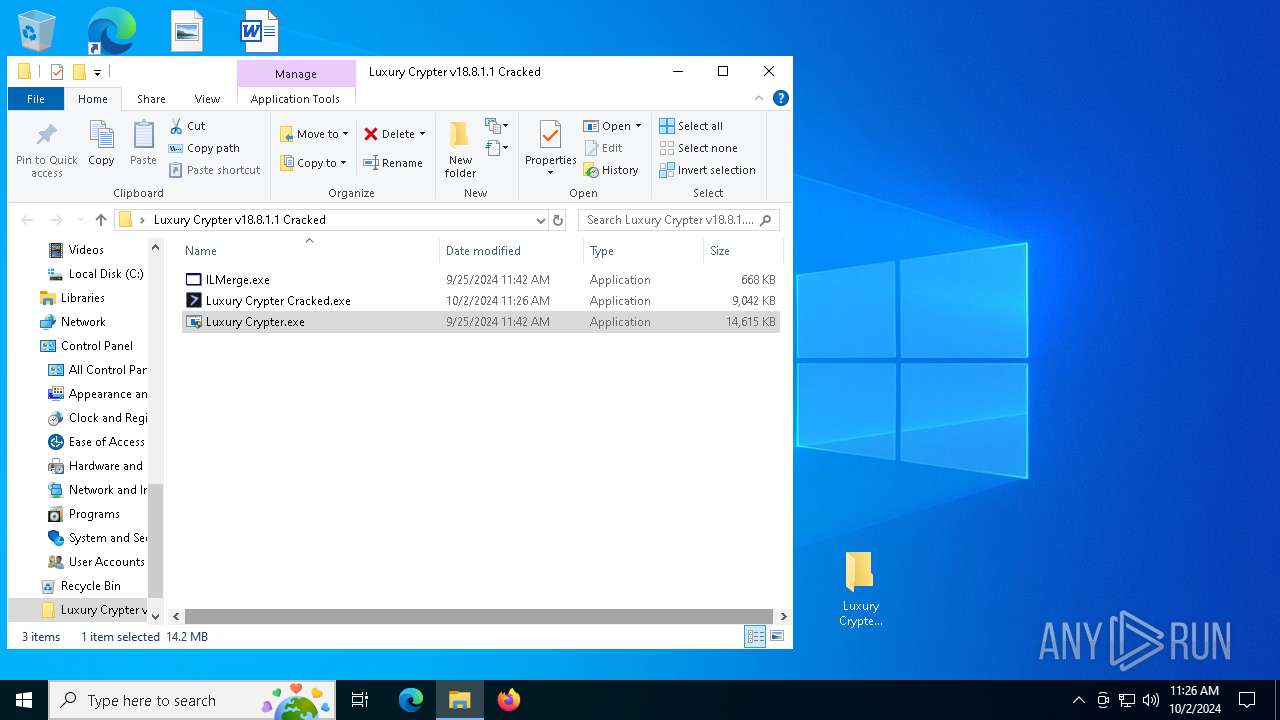
| File name: | Luxury Crypter v18.8.1.1 Cracked.zip |
| Full analysis: | https://app.any.run/tasks/900b3926-18af-4efc-84c5-c95e1ee68045 |
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | October 02, 2024, 11:25:16 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
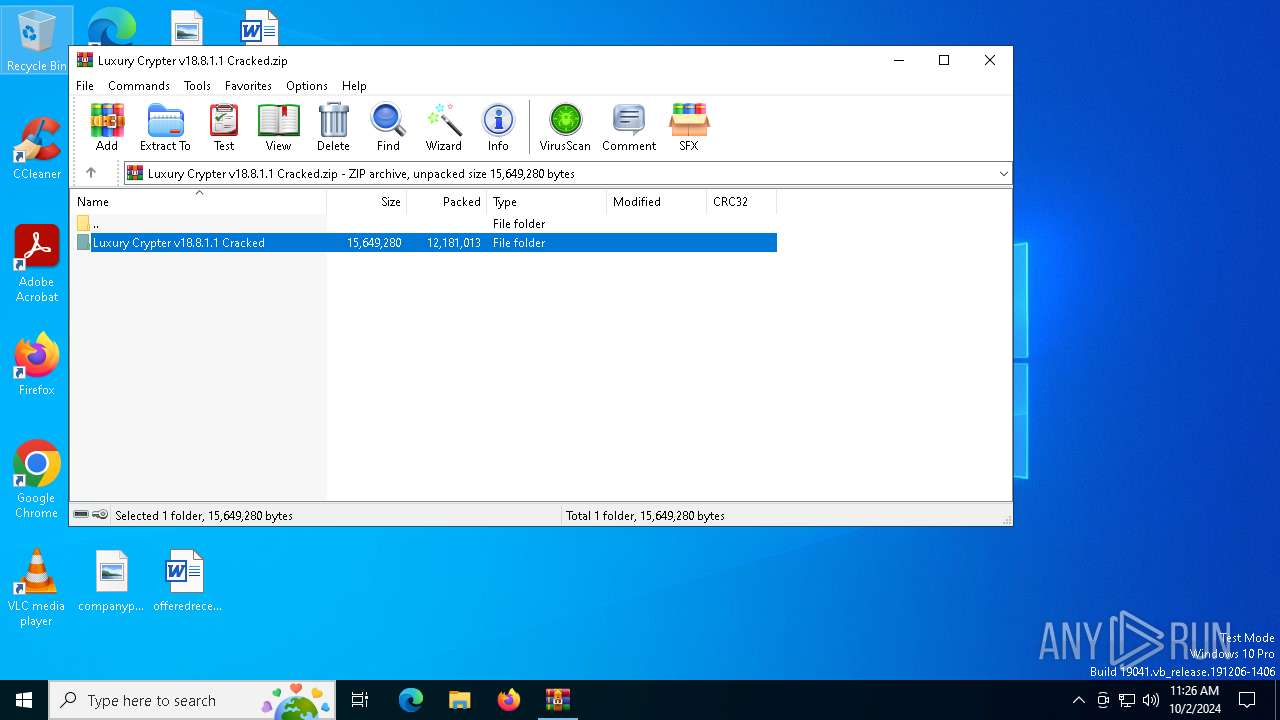
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 201F46873146F95032022AE4A95D9566 |
| SHA1: | D4B2527EDB78B8CC23E6E796753C4E71FB451F2D |
| SHA256: | F350A262919CFF1657CFC541F7331DB47CE615FFB884FDB5B4F20635F53ED72D |
| SSDEEP: | 98304:RLcA+qktk8qf6oeMTvPjzhhgkAQgoo2jxZkJh6fuhoOOuoQQks+6W8OBJWgfv1ee:pG9A+YbgEtH0nN+w3 |
MALICIOUS
Adds extension to the Windows Defender exclusion list
- Python 3.2.9.1.exe (PID: 1008)
- tgxzcjpudyzj.exe (PID: 5500)
Runs injected code in another process
- powershell.exe (PID: 3832)
- powershell.exe (PID: 5240)
Application was injected by another process
- dllhost.exe (PID: 2132)
- dllhost.exe (PID: 7160)
MINER has been detected (SURICATA)
- svchost.exe (PID: 2256)
XORed URL has been found (YARA)
- dialer.exe (PID: 5244)
SUSPICIOUS
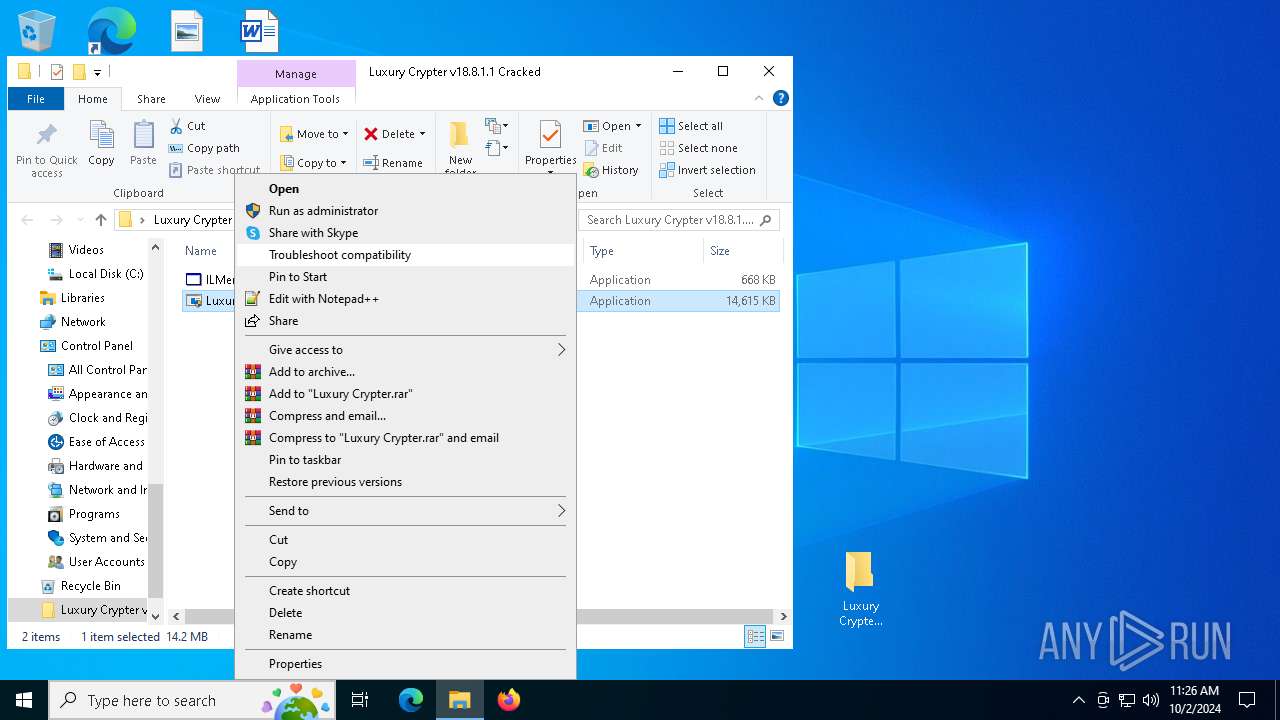
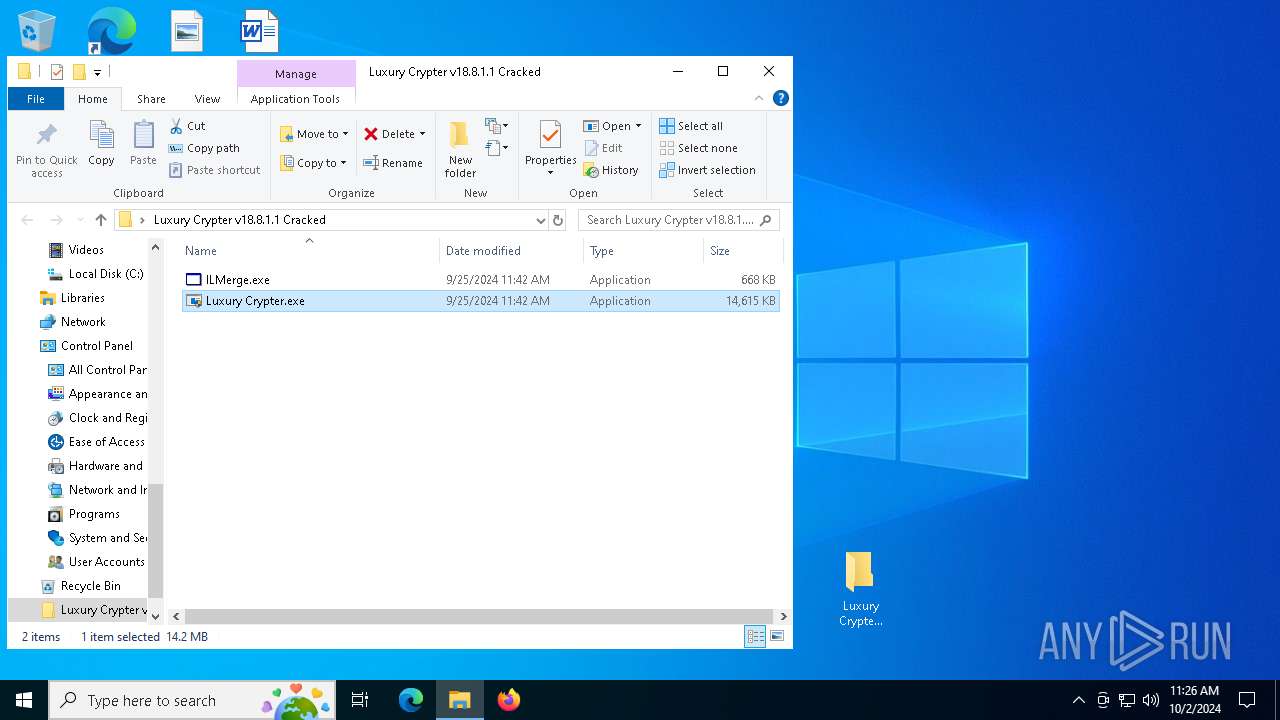
Starts POWERSHELL.EXE for commands execution
- Luxury Crypter.exe (PID: 2776)
- Python 3.2.9.1.exe (PID: 1008)
- tgxzcjpudyzj.exe (PID: 5500)
Base64-obfuscated command line is found
- Luxury Crypter.exe (PID: 2776)
Executable content was dropped or overwritten
- Luxury Crypter.exe (PID: 2776)
- Python 3.2.9.1.exe (PID: 1008)
- tgxzcjpudyzj.exe (PID: 5500)
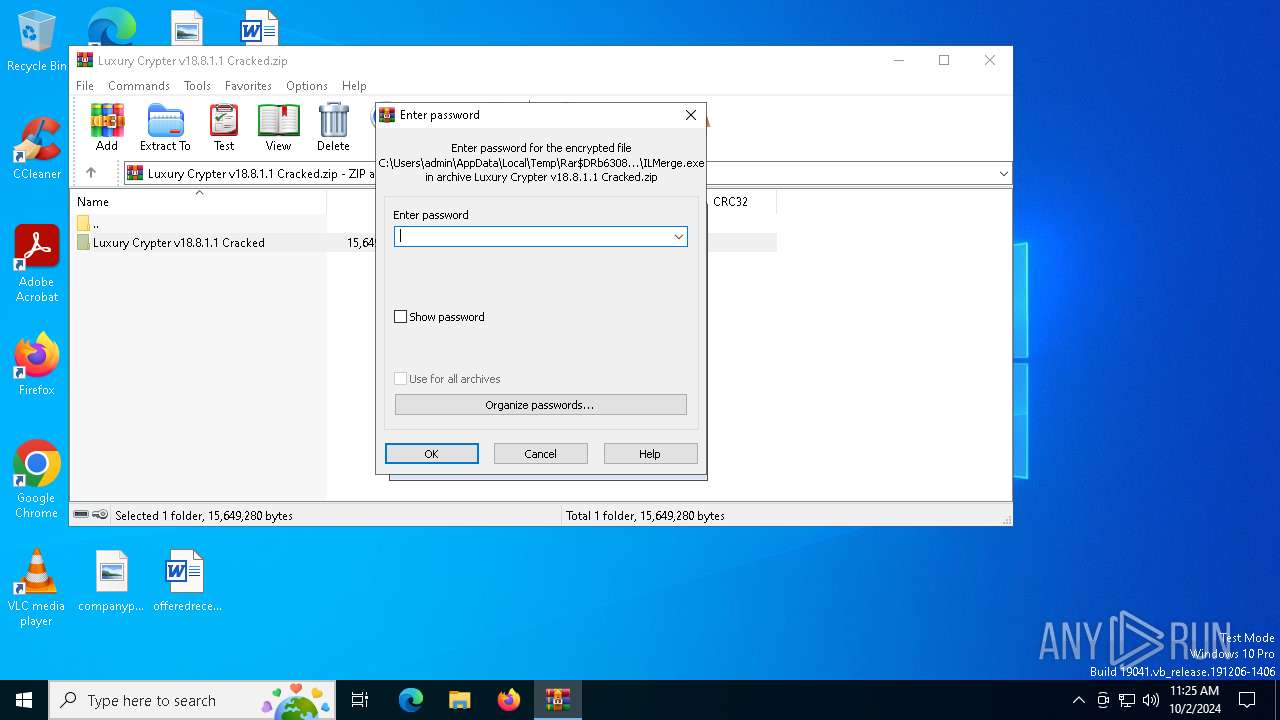
Process drops legitimate windows executable
- WinRAR.exe (PID: 6308)
Script adds exclusion extension to Windows Defender
- Python 3.2.9.1.exe (PID: 1008)
- tgxzcjpudyzj.exe (PID: 5500)
BASE64 encoded PowerShell command has been detected
- Luxury Crypter.exe (PID: 2776)
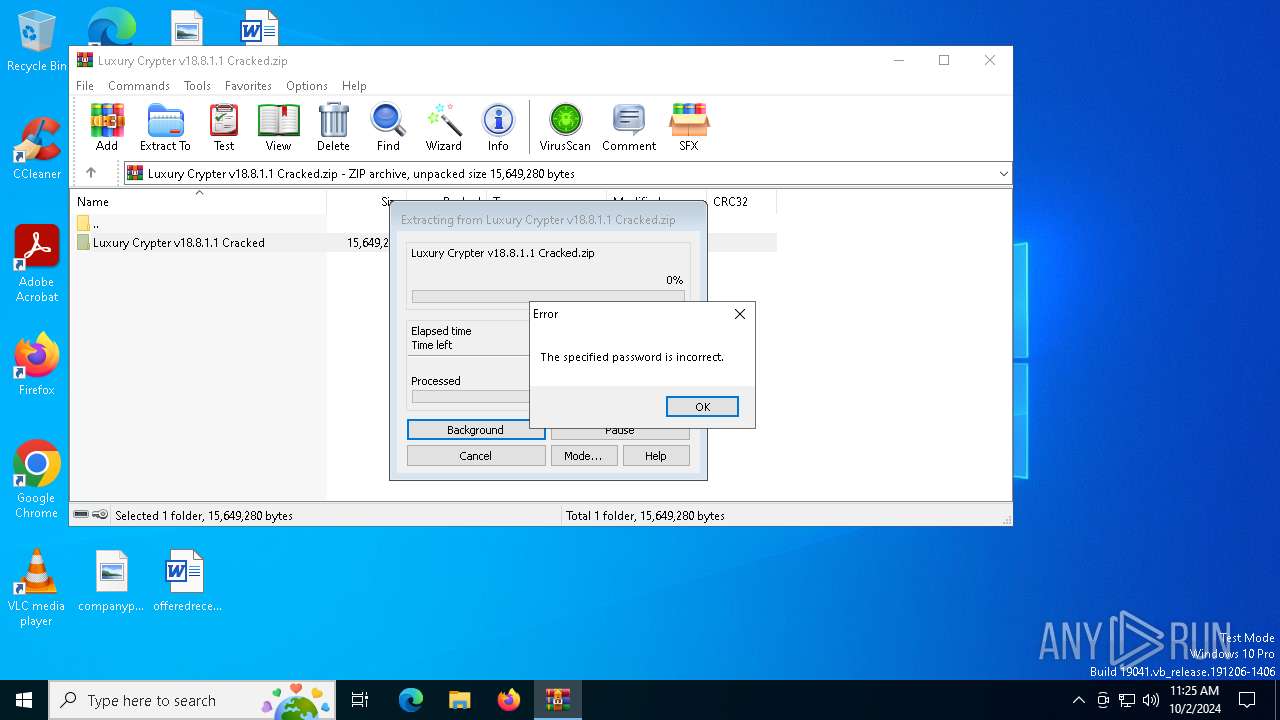
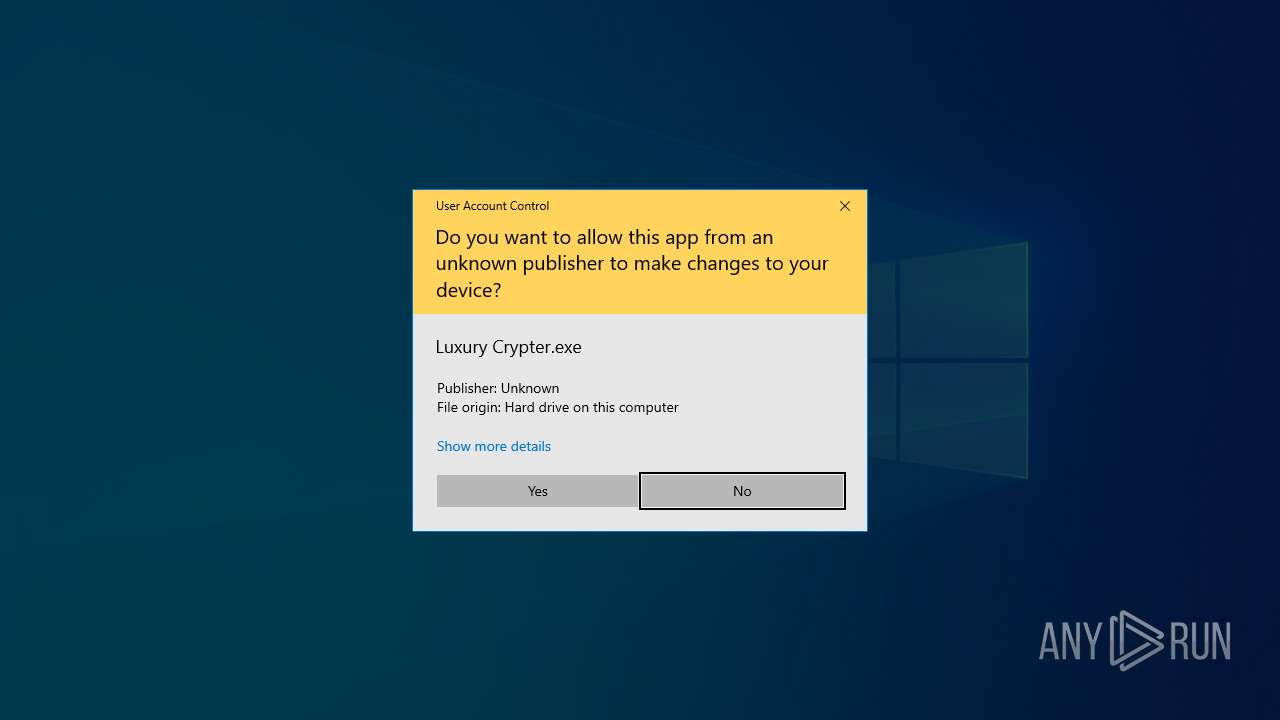
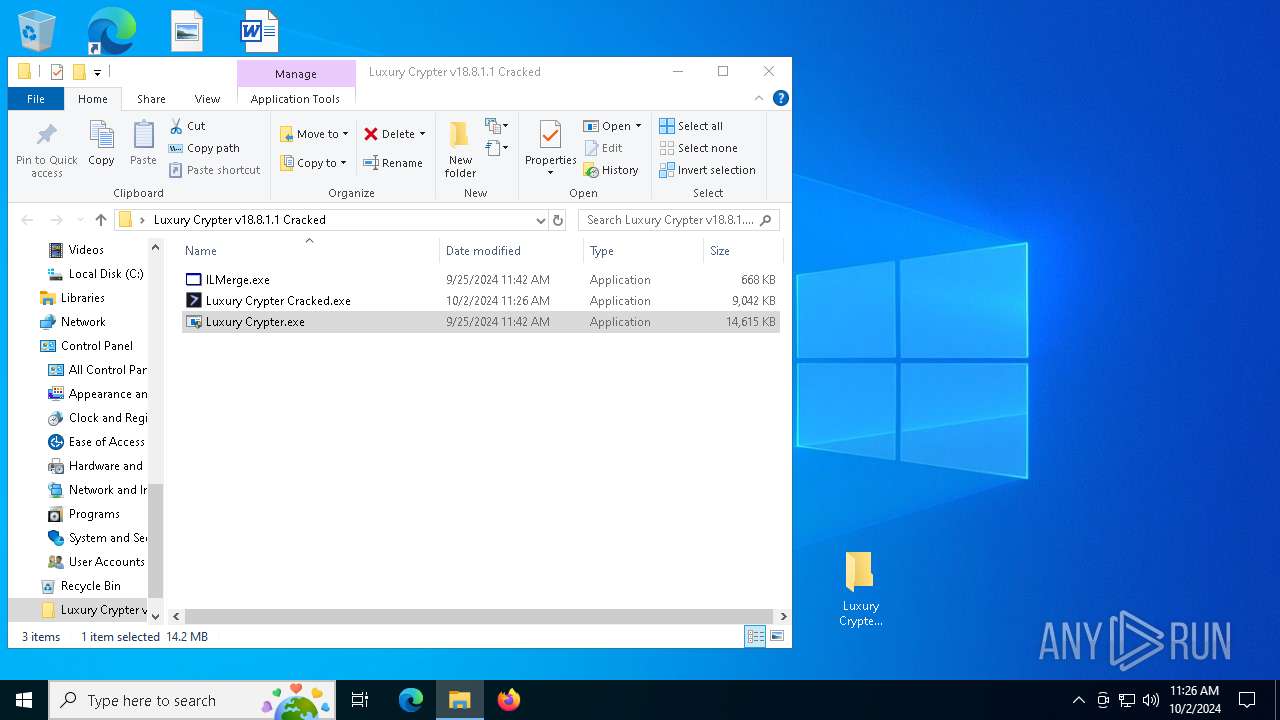
Executes application which crashes
- Luxury Crypter Cracked.exe (PID: 2208)
Script adds exclusion path to Windows Defender
- Python 3.2.9.1.exe (PID: 1008)
- tgxzcjpudyzj.exe (PID: 5500)
Starts CMD.EXE for commands execution
- Python 3.2.9.1.exe (PID: 1008)
- tgxzcjpudyzj.exe (PID: 5500)
Starts SC.EXE for service management
- Python 3.2.9.1.exe (PID: 1008)
- tgxzcjpudyzj.exe (PID: 5500)
The process executes via Task Scheduler
- powershell.exe (PID: 3832)
- powershell.exe (PID: 5240)
Connects to unusual port
- dialer.exe (PID: 5244)
Process uninstalls Windows update
- wusa.exe (PID: 1120)
- wusa.exe (PID: 4092)
Drops a system driver (possible attempt to evade defenses)
- tgxzcjpudyzj.exe (PID: 5500)
Potential Corporate Privacy Violation
- svchost.exe (PID: 2256)
Executes as Windows Service
- tgxzcjpudyzj.exe (PID: 5500)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6308)
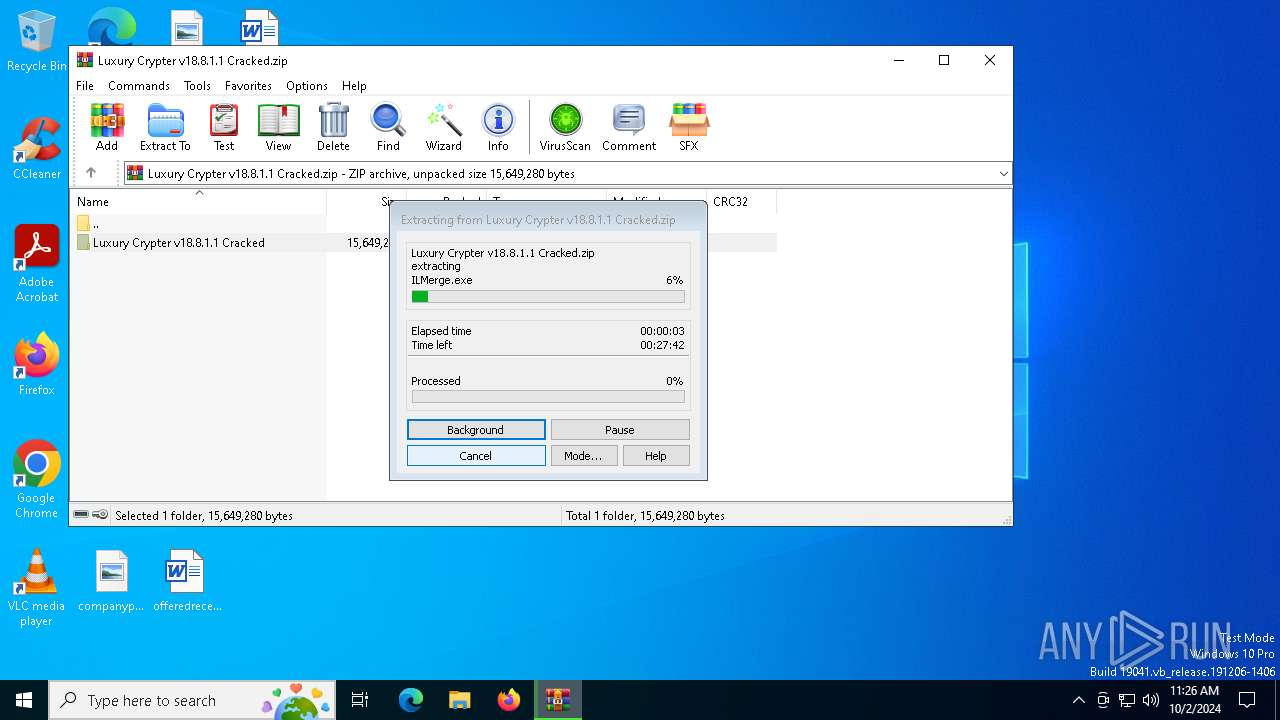
The process uses the downloaded file
- WinRAR.exe (PID: 6308)
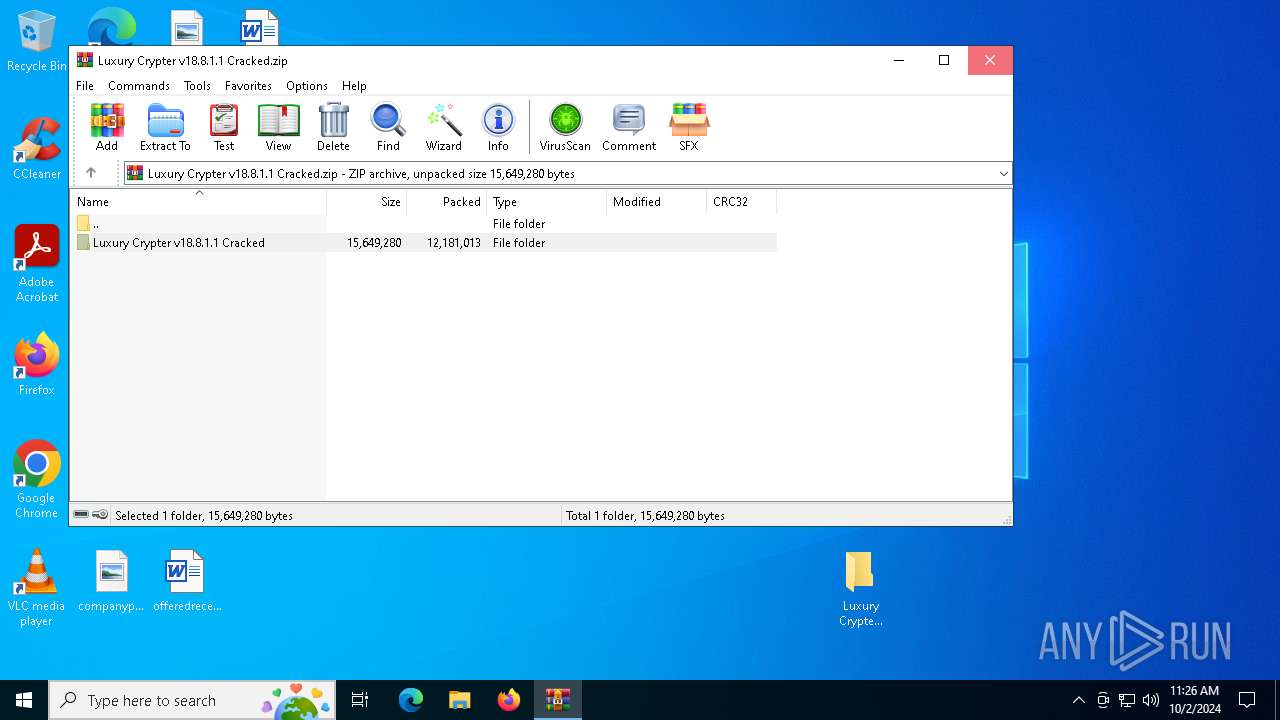
Manual execution by a user
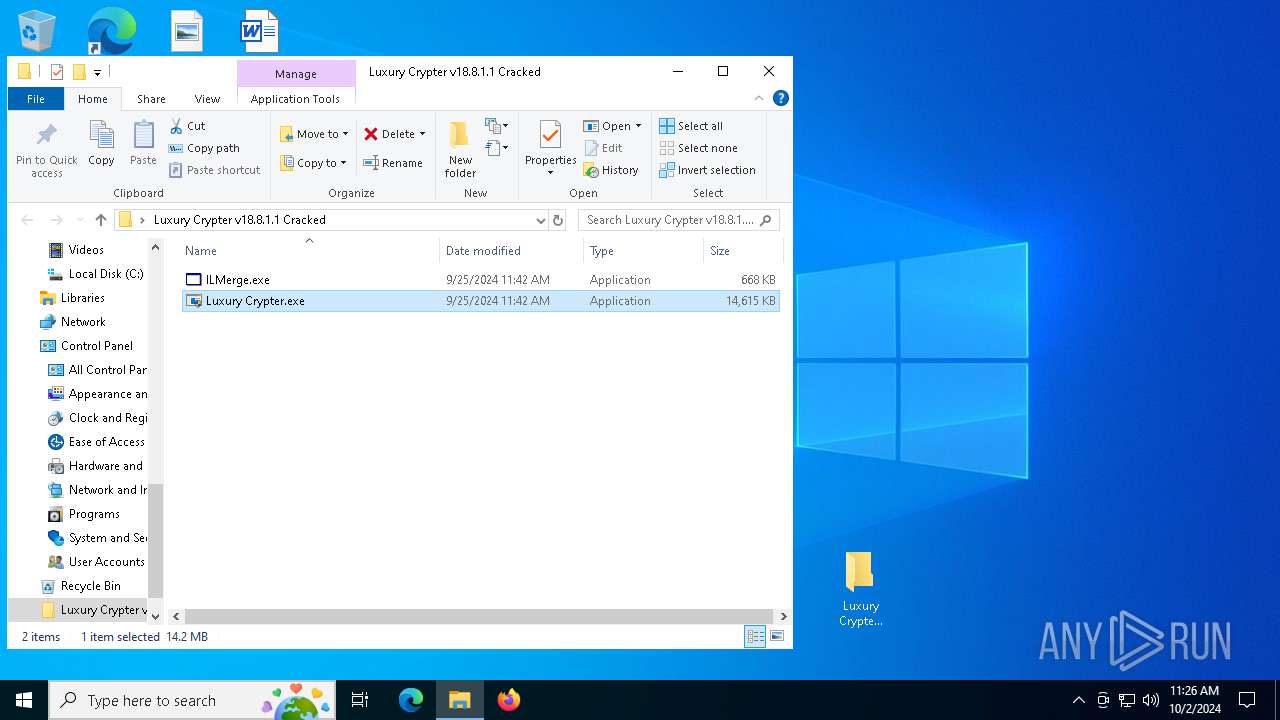
- Luxury Crypter.exe (PID: 2776)
UPX packer has been detected
- dialer.exe (PID: 5244)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
xor-url
(PID) Process(5244) dialer.exe
Decrypted-URLs (1)https://206.12
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:09:25 13:42:22 |
| ZipCRC: | 0x18902b4d |
| ZipCompressedSize: | 258639 |
| ZipUncompressedSize: | 684032 |
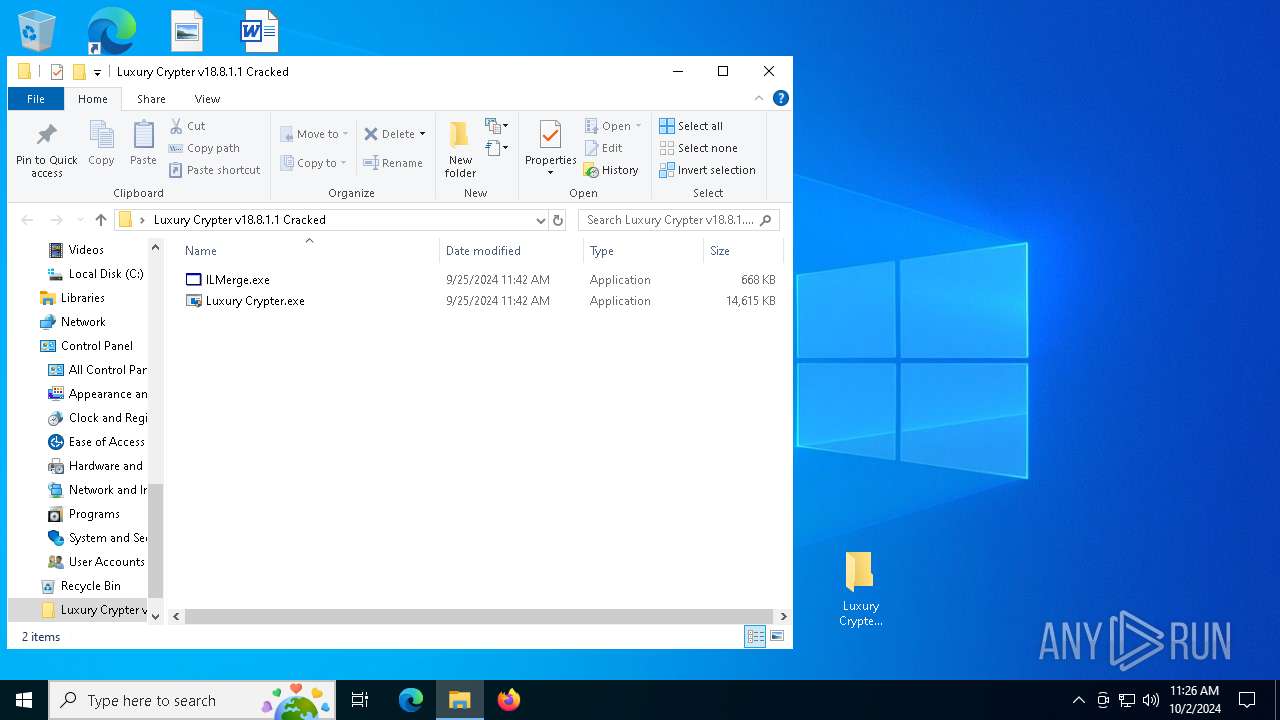
| ZipFileName: | Luxury Crypter v18.8.1.1 Cracked/ILMerge.exe |
Total processes
189
Monitored processes
57
Malicious processes
5
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 440 | C:\WINDOWS\system32\sc.exe stop dosvc | C:\Windows\System32\sc.exe | — | tgxzcjpudyzj.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Service Control Manager Configuration Tool Exit code: 1062 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 640 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 964 | C:\WINDOWS\system32\sc.exe stop wuauserv | C:\Windows\System32\sc.exe | — | tgxzcjpudyzj.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Service Control Manager Configuration Tool Exit code: 1062 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1008 | "C:\Users\admin\AppData\Roaming\Python 3.2.9.1.exe" | C:\Users\admin\AppData\Roaming\Python 3.2.9.1.exe | Luxury Crypter.exe | ||||||||||||
User: admin Company: Microsoft Visual C++ 2015-2022 Redistributable (x64) - 14.40.33810 Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2022 Redistributable (x64) - 14.40.33810 Exit code: 0 Version: 14,40,33810,0 Modules
| |||||||||||||||
| 1120 | wusa /uninstall /kb:890830 /quiet /norestart | C:\Windows\System32\wusa.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Update Standalone Installer Exit code: 87 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1144 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1164 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1256 | C:\WINDOWS\system32\sc.exe stop dosvc | C:\Windows\System32\sc.exe | — | Python 3.2.9.1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1062 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1448 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
35 048
Read events
34 993
Write events
52
Delete events
3
Modification events
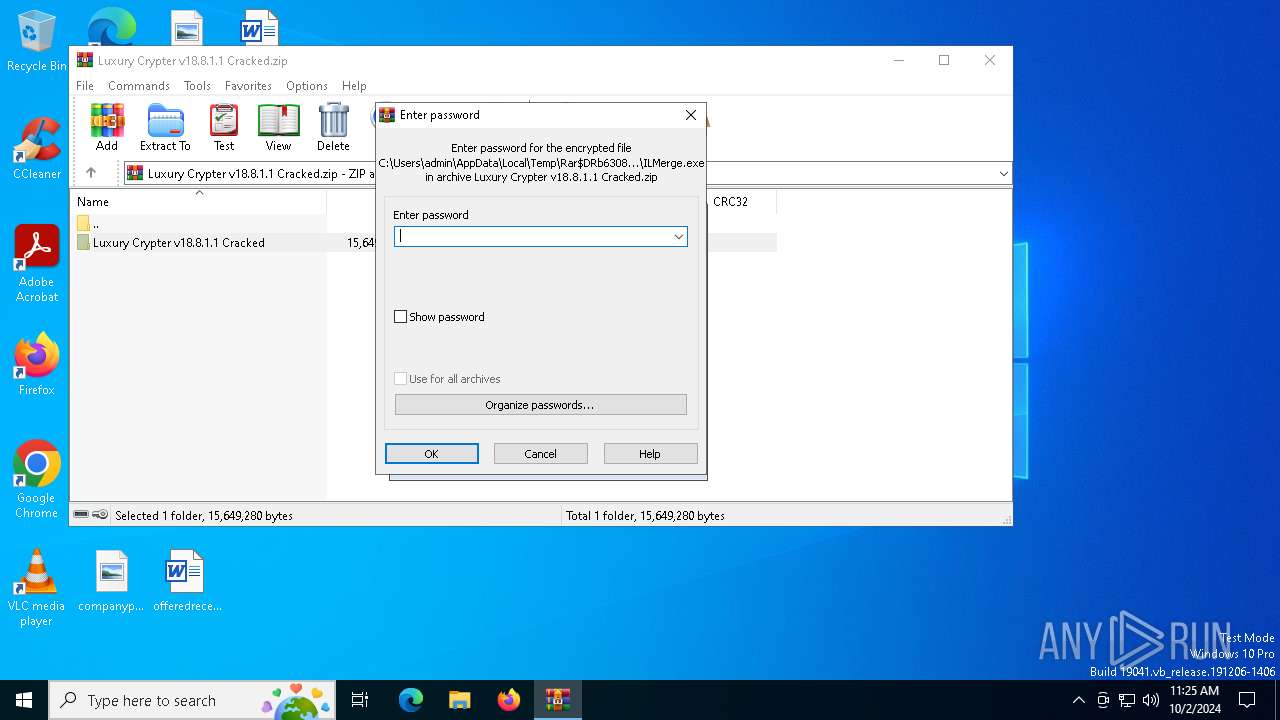
| (PID) Process: | (6308) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6308) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Luxury Crypter v18.8.1.1 Cracked.zip | |||
| (PID) Process: | (6308) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6308) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6308) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6308) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6308) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (6308) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 1 | |||
| (PID) Process: | (6308) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (6308) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
6
Suspicious files
7
Text files
16
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6604 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_Luxury Crypter C_7e3e3b2d62be3a77a95be3eeb7a0a439775782_6f432ba3_2f628226-e126-49a9-851b-0cd7558376ac\Report.wer | — | |
MD5:— | SHA256:— | |||
| 6604 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\Luxury Crypter Cracked.exe.2208.dmp | — | |
MD5:— | SHA256:— | |||
| 6308 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6308.14969\Luxury Crypter v18.8.1.1 Cracked\Luxury Crypter.exe | executable | |
MD5:7333550A13D092889D85D31C1727A618 | SHA256:3CC8FE4908B342C7F493984E6EB91B2C5E6236927AD2F27CACF734CC22903691 | |||
| 6604 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER3293.tmp.WERInternalMetadata.xml | xml | |
MD5:3A0259A83F409566BBF9F0B1DF3B1913 | SHA256:21C7D33279033A444D0E6F765CD92BC332BA6BCEA80B8C7D3F7F21A2C19A91D0 | |||
| 6604 | WerFault.exe | C:\Windows\appcompat\Programs\Amcache.hve | hiv | |
MD5:4F7E72DCC4EF41DC5F8AB4D0506786F4 | SHA256:664C82122D53FCD1CA750BE554BDB0A0A1A35BB79CD670F0F11080162B53FDF3 | |||
| 4896 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ofhpv4az.qxe.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6604 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\21253908F3CB05D51B1C2DA8B681A785 | binary | |
MD5:1B7FD5177461034E4086724C5845E927 | SHA256:065AF18C229898A1C2A8D989911ADCD9B1E2AB14B1953EBF8EAF34AE37EA1627 | |||
| 6604 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\21253908F3CB05D51B1C2DA8B681A785 | binary | |
MD5:9BF69A2A577CFCA39EC10F707EA26923 | SHA256:76F287DBBD29F9766C1D988775E9E80D36D9D749744C655A19E90F58B031C878 | |||
| 6604 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\37C951188967C8EB88D99893D9D191FE | binary | |
MD5:FB64A9EBEDF48D3895381D5B7D80743D | SHA256:EA21D495930AD76F267A33A0F593DBF0C7EA75E457FCAE49A29DAAD8BD920F42 | |||
| 4896 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:085EFD3E0AB3F61E772404D6F4DF6DA6 | SHA256:F8C735E78FEB7BE44517F95BC6C7D3BF78B789F187F3F4C647219A1AE3E3CE88 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
56
DNS requests
23
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6700 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2268 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
992 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6604 | WerFault.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2268 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5152 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
992 | svchost.exe | 40.126.31.67:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3260 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
992 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY Observed DNS Query to Coin Mining Domain (nanopool .org) |
2256 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |
Process | Message |
|---|---|
Luxury Crypter Cracked.exe | CLR: Managed code called FailFast, saying " |
Luxury Crypter Cracked.exe | This assembly was protected by demo version of ArmDot more than 7 days ago
Buy full version at https://www.armdot.com/order.html |
Luxury Crypter Cracked.exe | "
|