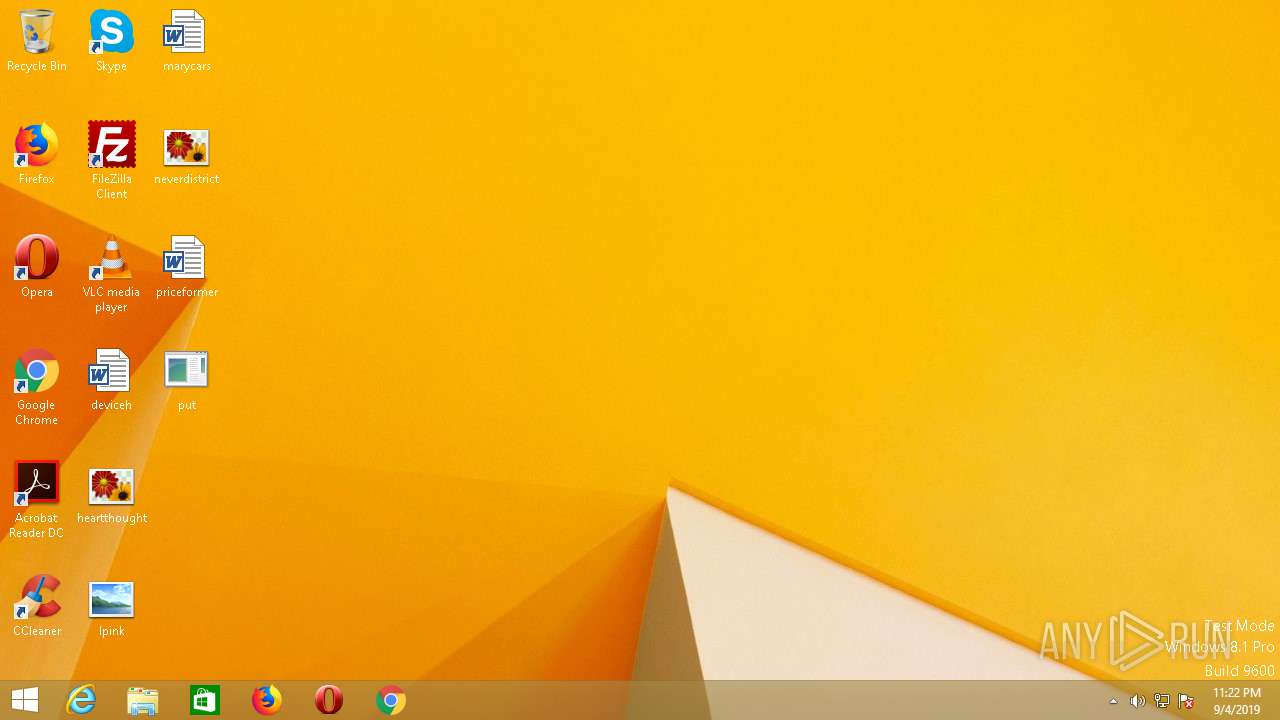
| File name: | put.exe |
| Full analysis: | https://app.any.run/tasks/7be8bd09-7eae-4613-b155-469401a7aca6 |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | September 05, 2019, 06:22:03 |
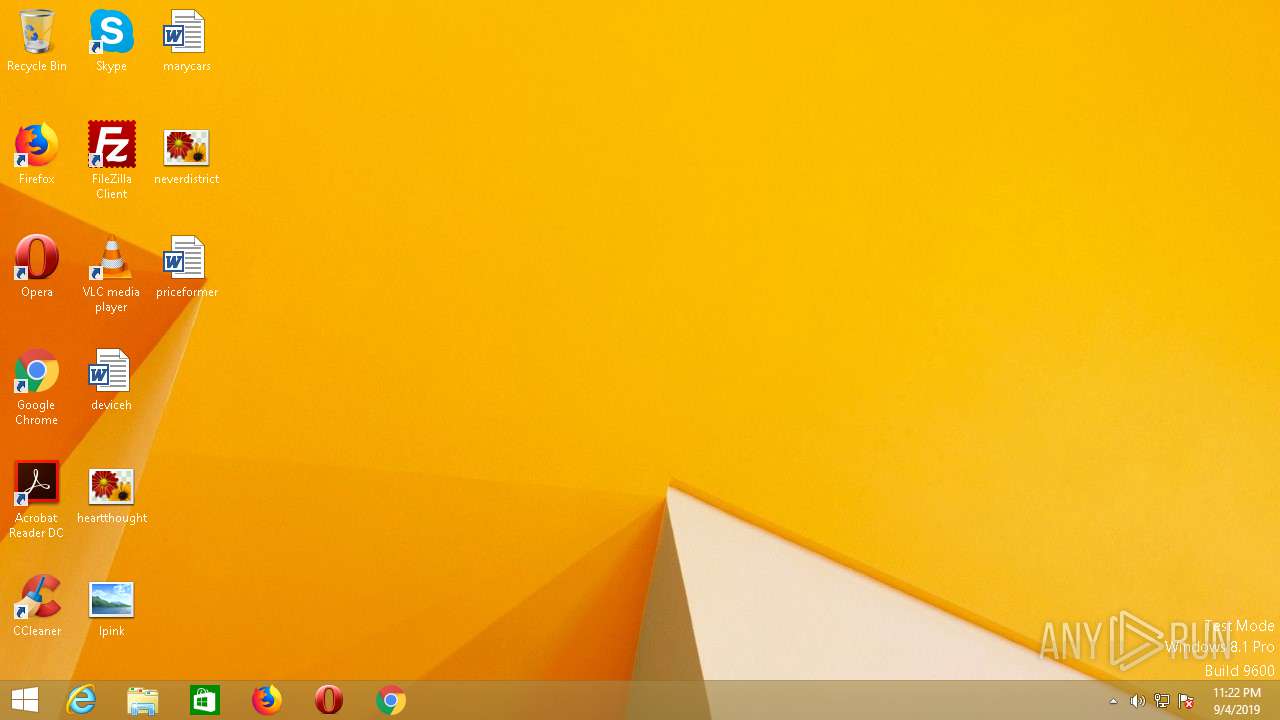
| OS: | Windows 8.1 Professional (build: 9600, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 61254A3F1D7281E2F033EE00302BD53D |
| SHA1: | 0885CBE838C4F00E0F1F7566291AE3B965D93EAE |
| SHA256: | F2C6C6B1C374A29B7CDE659B9EA5B5D0A54D7E795BA7FE16CA3D0FD129B51601 |
| SSDEEP: | 24576:2AHnh+eWsN3skA4RV1Hom2KXMmHaPpD9L3L5GzFptTxRaehNAiq0YHeCj5:Rh+ZkldoPK8YaBDZ3LAzTRxRdVYHN |
MALICIOUS
FORMBOOK was detected
- explorer.exe (PID: 1192)
- netsh.exe (PID: 980)
- Firefox.exe (PID: 2620)
Changes the autorun value in the registry
- netsh.exe (PID: 980)
Actions looks like stealing of personal data
- netsh.exe (PID: 980)
Loads the Task Scheduler COM API
- explorer.exe (PID: 1192)
Connects to CnC server
- explorer.exe (PID: 1192)
Stealing of credential data
- netsh.exe (PID: 980)
SUSPICIOUS
Uses NETSH.EXE for network configuration
- explorer.exe (PID: 1192)
Application launched itself
- put.exe (PID: 2948)
Creates files in the user directory
- netsh.exe (PID: 980)
Starts CMD.EXE for commands execution
- netsh.exe (PID: 980)
INFO
Manual execution by user
- netsh.exe (PID: 980)
Reads the hosts file
- netsh.exe (PID: 980)
Creates files in the user directory
- Firefox.exe (PID: 2620)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:09:03 17:43:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 581632 |
| InitializedDataSize: | 598016 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2800a |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-Sep-2019 15:43:17 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 03-Sep-2019 15:43:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0008DFDD | 0x0008E000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.67525 |
.rdata | 0x0008F000 | 0x0002FD8E | 0x0002FE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.76324 |
.data | 0x000BF000 | 0x00008F74 | 0x00005200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.19638 |
.rsrc | 0x000C8000 | 0x00055C84 | 0x00055E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.87982 |
.reloc | 0x0011E000 | 0x00007134 | 0x00007200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.78396 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.40026 | 1007 | Latin 1 / Western European | English - United Kingdom | RT_MANIFEST |
2 | 2.05883 | 296 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
3 | 2.25499 | 296 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
4 | 3.65355 | 744 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
5 | 3.43704 | 296 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
6 | 4.16139 | 3752 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
7 | 3.34702 | 1428 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
8 | 3.2817 | 1674 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
9 | 3.28849 | 1168 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
10 | 3.28373 | 1532 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
MPR.dll |
OLEAUT32.dll |
PSAPI.DLL |
SHELL32.dll |
Total processes
46
Monitored processes
7
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 336 | "C:\Users\admin\Desktop\put.exe" | C:\Users\admin\Desktop\put.exe | — | put.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 536 | /c del "C:\Users\admin\Desktop\put.exe" | C:\Windows\SysWOW64\cmd.exe | — | netsh.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.3.9600.16384 (winblue_rtm.130821-1623) Modules
| |||||||||||||||
| 980 | "C:\Windows\SysWOW64\netsh.exe" | C:\Windows\SysWOW64\netsh.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 0 Version: 6.3.9600.16384 (winblue_rtm.130821-1623) Modules
| |||||||||||||||
| 1192 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.3.9600.17031 (winblue_gdr.140221-1952) Modules
| |||||||||||||||
| 2620 | "C:\Program Files\Mozilla Firefox\Firefox.exe" | C:\Program Files\Mozilla Firefox\Firefox.exe | netsh.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 66.0 Modules
| |||||||||||||||
| 2792 | \??\C:\Windows\system32\conhost.exe 0xffffffff | C:\Windows\system32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 6.3.9600.16384 (winblue_rtm.130821-1623) Modules
| |||||||||||||||
| 2948 | "C:\Users\admin\Desktop\put.exe" | C:\Users\admin\Desktop\put.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
423
Read events
322
Write events
101
Delete events
0
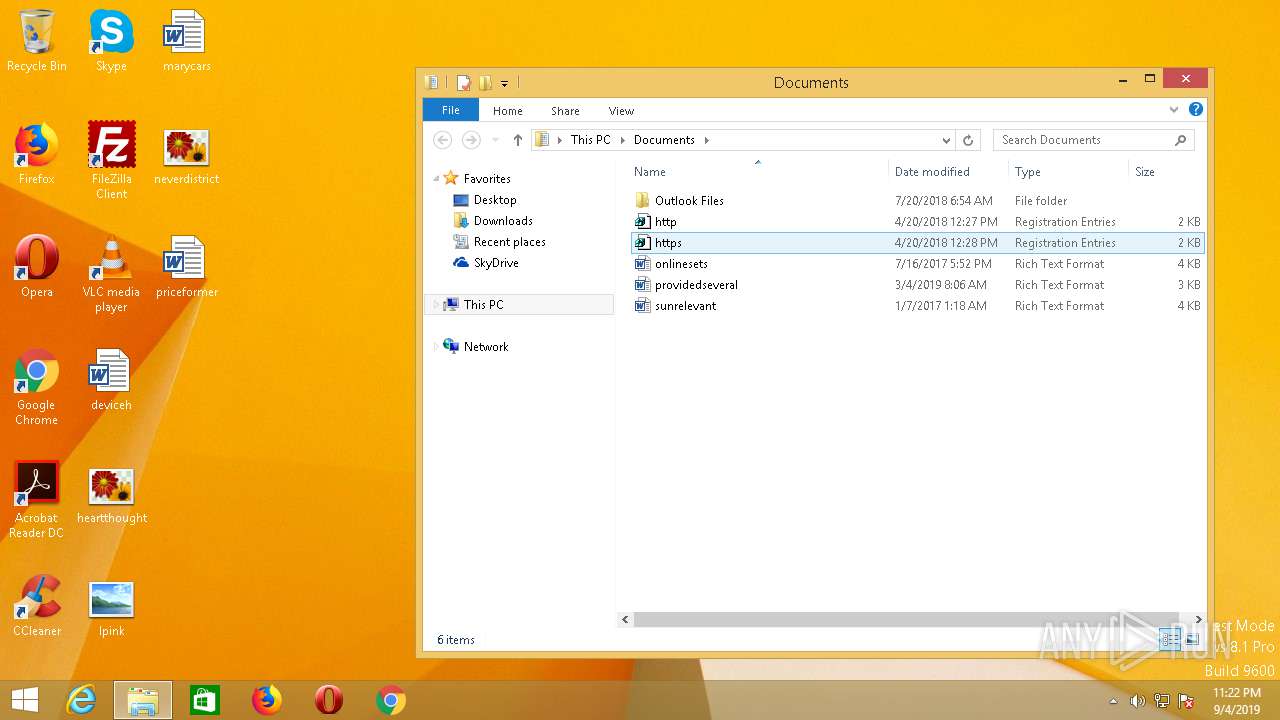
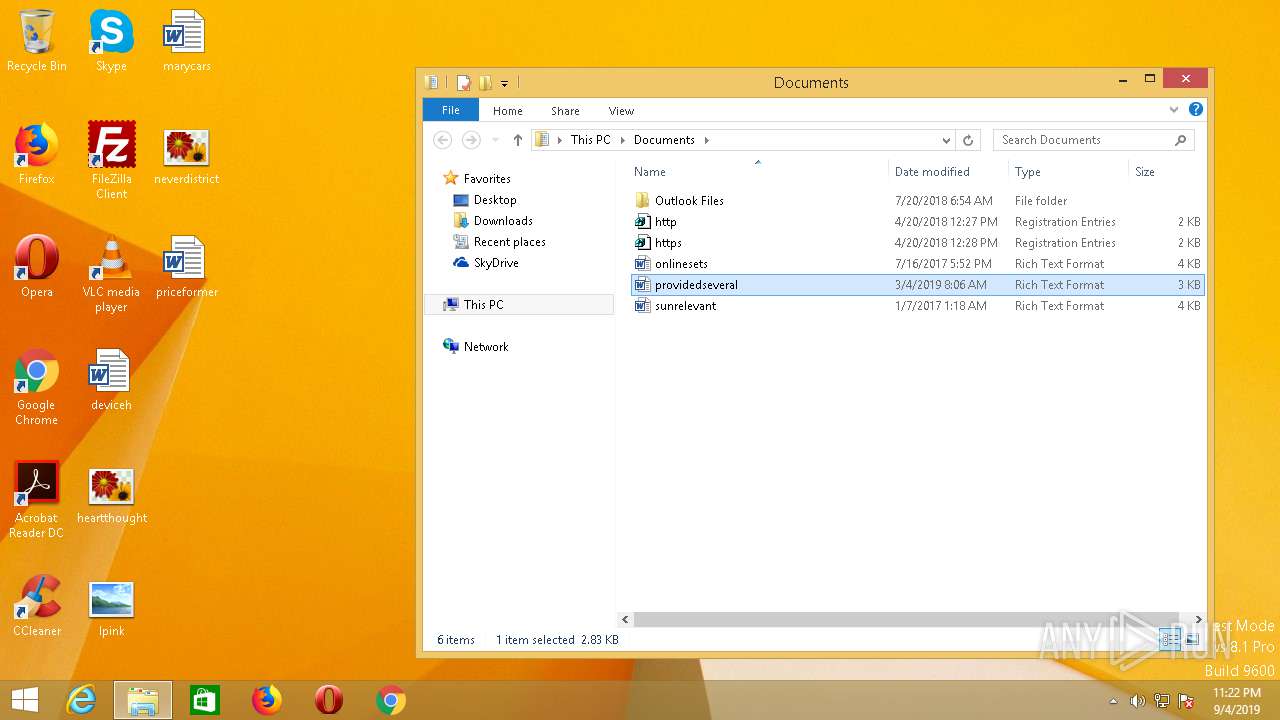
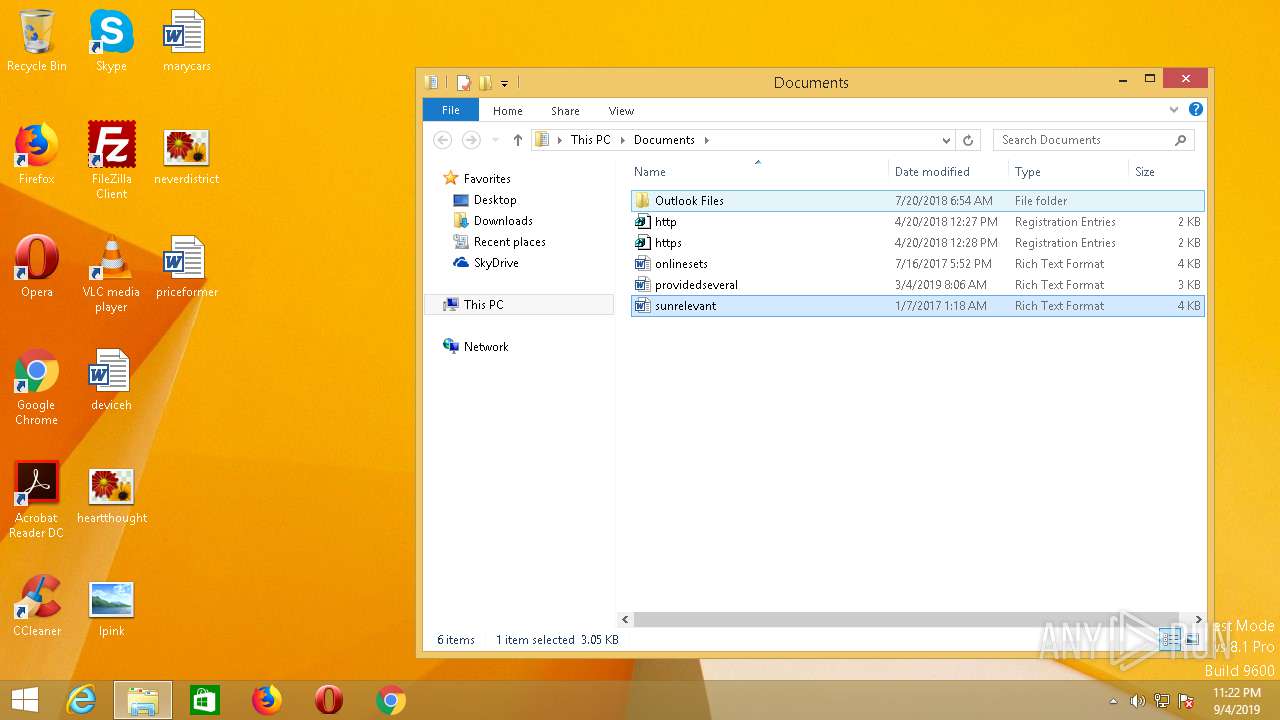
Modification events
| (PID) Process: | (1192) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (1192) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 010000000000000008000000070000000200000006000000050000000400000003000000FFFFFFFF | |||
| (PID) Process: | (1192) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\1 |
| Operation: | write | Name: | MRUListEx |
Value: 02000000000000000300000001000000FFFFFFFF | |||
| (PID) Process: | (1192) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Toolbar |
| Operation: | write | Name: | Locked |
Value: 1 | |||
| (PID) Process: | (1192) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{D0498E0A-45B7-42AE-A9AA-ABA463DBD3BF}\iexplore |
| Operation: | write | Name: | Type |
Value: 3 | |||
| (PID) Process: | (1192) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{D0498E0A-45B7-42AE-A9AA-ABA463DBD3BF}\iexplore |
| Operation: | write | Name: | Count |
Value: 5 | |||
| (PID) Process: | (1192) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{D0498E0A-45B7-42AE-A9AA-ABA463DBD3BF}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070900040005000600160024006D03 | |||
| (PID) Process: | (1192) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Ribbon |
| Operation: | write | Name: | QatItems |
Value: 3C7369713A637573746F6D554920786D6C6E733A7369713D22687474703A2F2F736368656D61732E6D6963726F736F66742E636F6D2F77696E646F77732F323030392F726962626F6E2F716174223E3C7369713A726962626F6E206D696E696D697A65643D2274727565223E3C7369713A71617420706F736974696F6E3D2230223E3C7369713A736861726564436F6E74726F6C733E3C7369713A636F6E74726F6C206964513D227369713A3136313238222076697369626C653D2266616C73652220617267756D656E743D223022202F3E3C7369713A636F6E74726F6C206964513D227369713A3136313239222076697369626C653D2266616C73652220617267756D656E743D223022202F3E3C7369713A636F6E74726F6C206964513D227369713A3132333532222076697369626C653D2266616C73652220617267756D656E743D223022202F3E3C7369713A636F6E74726F6C206964513D227369713A3132333834222076697369626C653D22747275652220617267756D656E743D223022202F3E3C7369713A636F6E74726F6C206964513D227369713A3132333336222076697369626C653D22747275652220617267756D656E743D223022202F3E3C7369713A636F6E74726F6C206964513D227369713A3132333537222076697369626C653D2266616C73652220617267756D656E743D223022202F3E3C2F7369713A736861726564436F6E74726F6C733E3C2F7369713A7161743E3C2F7369713A726962626F6E3E3C2F7369713A637573746F6D55493E | |||
| (PID) Process: | (1192) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Toolbar\ShellBrowser |
| Operation: | write | Name: | ITBar7Layout |
Value: 13000000000000000000000020000000100000000000000001000000010700005E01000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1192) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\47\Shell |
| Operation: | write | Name: | SniffedFolderType |
Value: Documents | |||
Executable files
0
Suspicious files
74
Text files
1
Unknown types
0
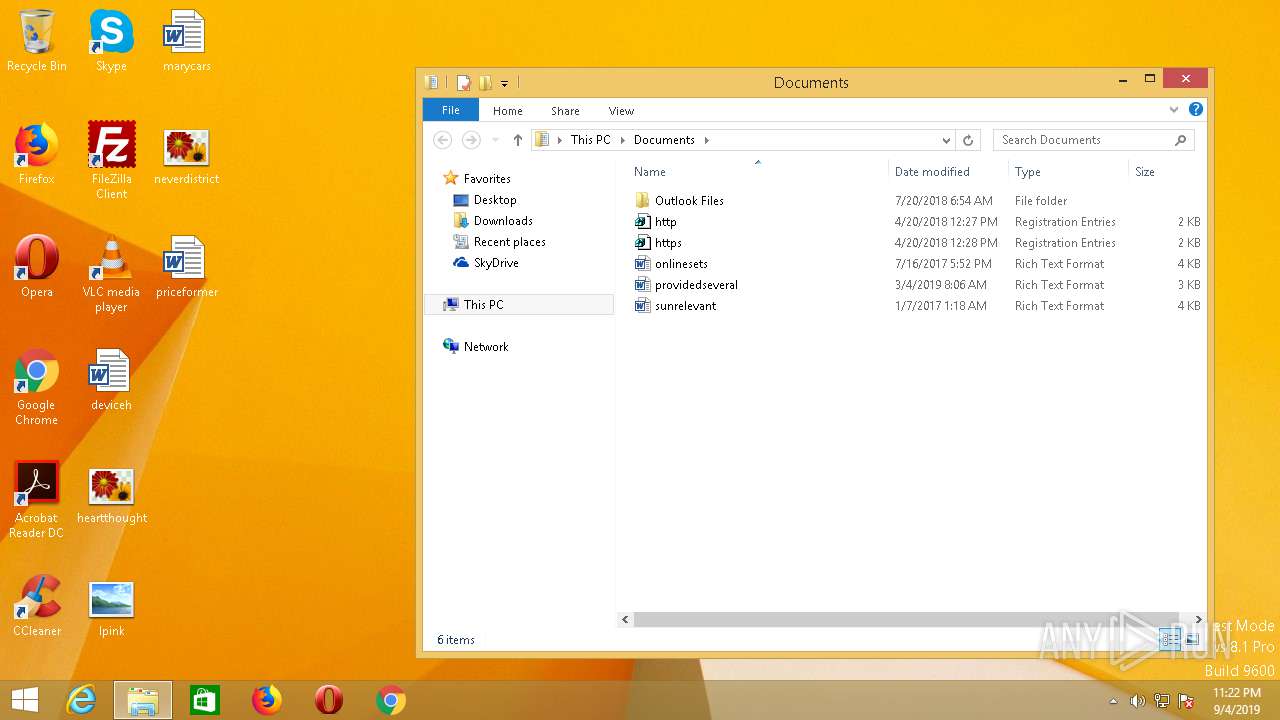
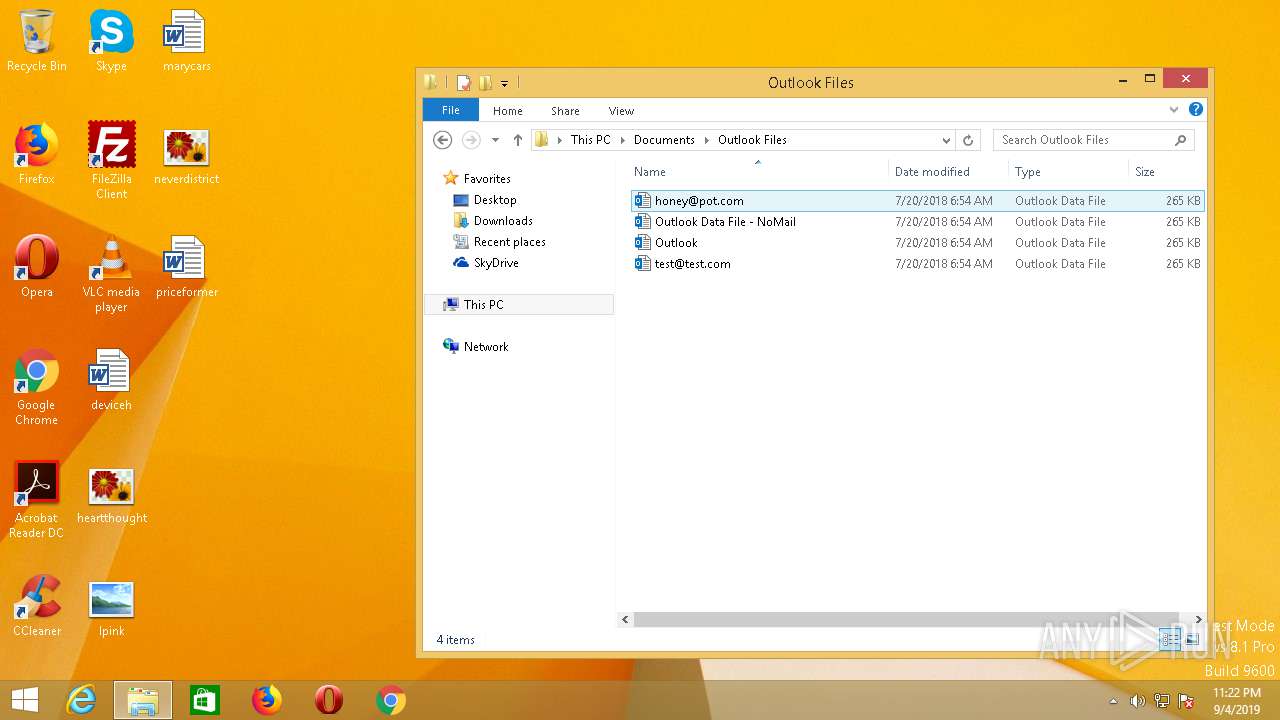
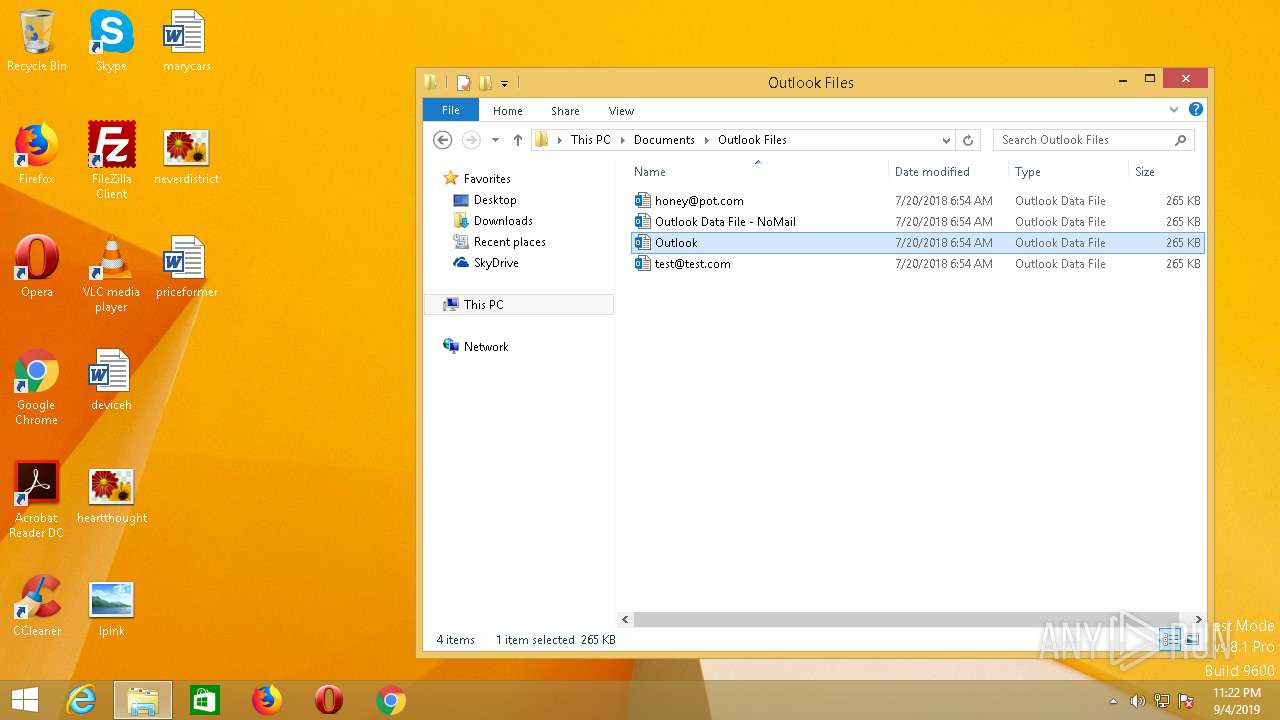
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 980 | netsh.exe | C:\Users\admin\AppData\Roaming\NM0RS99E\NM0logrc.ini | binary | |
MD5:— | SHA256:— | |||
| 2620 | Firefox.exe | C:\Users\admin\AppData\Roaming\NM0RS99E\NM0logrf.ini | binary | |
MD5:— | SHA256:— | |||
| 980 | netsh.exe | C:\Users\admin\AppData\Roaming\NM0RS99E\NM0logim.jpeg | image | |
MD5:— | SHA256:— | |||
| 1192 | explorer.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Explorer\TileCacheLogo-9010046_100.dat | binary | |
MD5:— | SHA256:— | |||
| 980 | netsh.exe | C:\Users\admin\AppData\Roaming\NM0RS99E\NM0logri.ini | binary | |
MD5:D63A82E5D81E02E399090AF26DB0B9CB | SHA256:EAECE2EBA6310253249603033C744DD5914089B0BB26BDE6685EC9813611BAAE | |||
| 980 | netsh.exe | C:\Users\admin\AppData\Roaming\NM0RS99E\NM0logrv.ini | binary | |
MD5:BA3B6BC807D4F76794C4B81B09BB9BA5 | SHA256:6EEBF968962745B2E9DE2CA969AF7C424916D4E3FE3CC0BB9B3D414ABFCE9507 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
42
DNS requests
20
Threats
68
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1192 | explorer.exe | GET | — | 156.239.83.82:80 | http://www.jingtaishihua.com/vh/?Jxol=1jECOXtYKmqJss1eXptEGE1un871WkCmYBYUJfbRctdhwWbAuRD4vwxGSCTt&_hEhq=4h8dfdcPgHmHP | US | — | — | malicious |
1192 | explorer.exe | GET | — | 198.54.117.210:80 | http://www.collegeaveplayers.com/vh/?_hEhq=4h8dfdcPgHmHP&Jxol=RteqqbzertXHdVHsm5LaVqTI5Zrf/BpYciC4DKmUjgBWVb0kEhkzTW98fNOF | US | — | — | malicious |
1192 | explorer.exe | GET | — | 198.251.84.92:80 | http://www.gingkoproduction.com/vh/?_hEhq=4h8dfdcPgHmHP&Jxol=ME/yDdUAc91SOLr8uZL3HNqAV07W8PaaeTvVSKF0wkV4faDF/QPnminOG0Tf&sql=1 | US | — | — | malicious |
1192 | explorer.exe | GET | — | 192.185.0.218:80 | http://www.entertainmentstateline.com/vh/?_hEhq=4h8dfdcPgHmHP&Jxol=FNC1YTr334T44CpPppZv/dwtTrwLj38uHcJokEvuiKH/G8qR5lYKXDkBdQhT | US | — | — | malicious |
1192 | explorer.exe | POST | — | 198.251.84.92:80 | http://www.gingkoproduction.com/vh/ | US | — | — | malicious |
1192 | explorer.exe | GET | — | 202.52.147.82:80 | http://www.bbmindustri.com/vh/?_hEhq=4h8dfdcPgHmHP&Jxol=gI3IbBHqkQc573pK1tsDGvtJuX7EImdYLIKSOQu6IEDFSDnwrjSEpXF6PwPL | ID | — | — | malicious |
1192 | explorer.exe | POST | — | 198.251.84.92:80 | http://www.gingkoproduction.com/vh/ | US | — | — | malicious |
1192 | explorer.exe | GET | — | 198.54.117.210:80 | http://www.mailboa.com/vh/?Jxol=1lDdaAPj3vraGH2X9DQBacqtPm8EwIFJ+GmrA4SY/CCiVaLPq6veVYVHE9JJ&_hEhq=4h8dfdcPgHmHP | US | — | — | malicious |
1192 | explorer.exe | POST | — | 156.239.83.82:80 | http://www.jingtaishihua.com/vh/ | US | — | — | malicious |
1192 | explorer.exe | POST | — | 199.192.20.13:80 | http://www.nimtax.com/vh/ | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1192 | explorer.exe | 162.241.217.57:80 | www.noragamst.com | CyrusOne LLC | US | malicious |
1192 | explorer.exe | 198.54.117.210:80 | www.collegeaveplayers.com | Namecheap, Inc. | US | malicious |
1192 | explorer.exe | 198.251.84.92:80 | www.gingkoproduction.com | FranTech Solutions | US | malicious |
1192 | explorer.exe | 199.192.20.13:80 | www.nimtax.com | — | US | malicious |
1192 | explorer.exe | 202.52.147.82:80 | www.bbmindustri.com | Global Media Teknologi, PT | ID | malicious |
— | — | 198.54.117.210:80 | www.collegeaveplayers.com | Namecheap, Inc. | US | malicious |
1192 | explorer.exe | 173.247.244.139:80 | www.wellesleyandwillow.com | InMotion Hosting, Inc. | US | malicious |
— | — | 162.241.217.57:80 | www.noragamst.com | CyrusOne LLC | US | malicious |
— | — | 202.52.147.82:80 | www.bbmindustri.com | Global Media Teknologi, PT | ID | malicious |
1192 | explorer.exe | 192.185.0.218:80 | www.entertainmentstateline.com | CyrusOne LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.collegeaveplayers.com |
| malicious |
www.smartlily.net |
| unknown |
www.gingkoproduction.com |
| malicious |
www.nimtax.com |
| malicious |
www.xn--fiqs8syw4c07c.com |
| unknown |
www.jingtaishihua.com |
| malicious |
www.bbmindustri.com |
| malicious |
www.mailboa.com |
| malicious |
www.entertainmentstateline.com |
| malicious |
www.skinbowlroulette.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1192 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
1192 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
1192 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
1192 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
1192 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
1192 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
1192 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
1192 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
1192 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
1192 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
26 ETPRO signatures available at the full report