| File name: | CyaX-Sharp.exe |
| Full analysis: | https://app.any.run/tasks/dd550076-a56a-4260-ad2f-f9133838e185 |
| Verdict: | Malicious activity |
| Threats: | Hawkeye often gets installed in a bundle with other malware. This is a Trojan and keylogger that is used to retrieve private information such as passwords and login credentials. This is an advanced malware that features strong anti-evasion functions. |
| Analysis date: | September 19, 2019, 23:55:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 40D4DDFC2166AF4C456539C74DC83306 |
| SHA1: | 8405D167D62040C330EF62823FA03DA5372D0FFA |
| SHA256: | F2C271D3B49A61156AA48B7AF4DEF033E97B8270218FF25EF4D9853F8A0E2369 |
| SSDEEP: | 12288:bjZA9SUif/H0y/UCahdtu5nrOebCWBXrqwtDP1YzS0VwyDWGstYZ:bjZA9on/0hQn5vXTtBcVraGstY |
MALICIOUS
Uses Task Scheduler to run other applications
- CyaX-Sharp.exe (PID: 3016)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 3148)
Detected Hawkeye Keylogger
- CyaX-Sharp.exe (PID: 936)
Actions looks like stealing of personal data
- vbc.exe (PID: 2272)
SUSPICIOUS
Creates files in the user directory
- vlc.exe (PID: 2568)
- CyaX-Sharp.exe (PID: 936)
- CyaX-Sharp.exe (PID: 3016)
Executable content was dropped or overwritten
- CyaX-Sharp.exe (PID: 3016)
Checks for external IP
- CyaX-Sharp.exe (PID: 936)
Loads DLL from Mozilla Firefox
- vbc.exe (PID: 3172)
Executes scripts
- CyaX-Sharp.exe (PID: 936)
Application launched itself
- CyaX-Sharp.exe (PID: 3016)
INFO
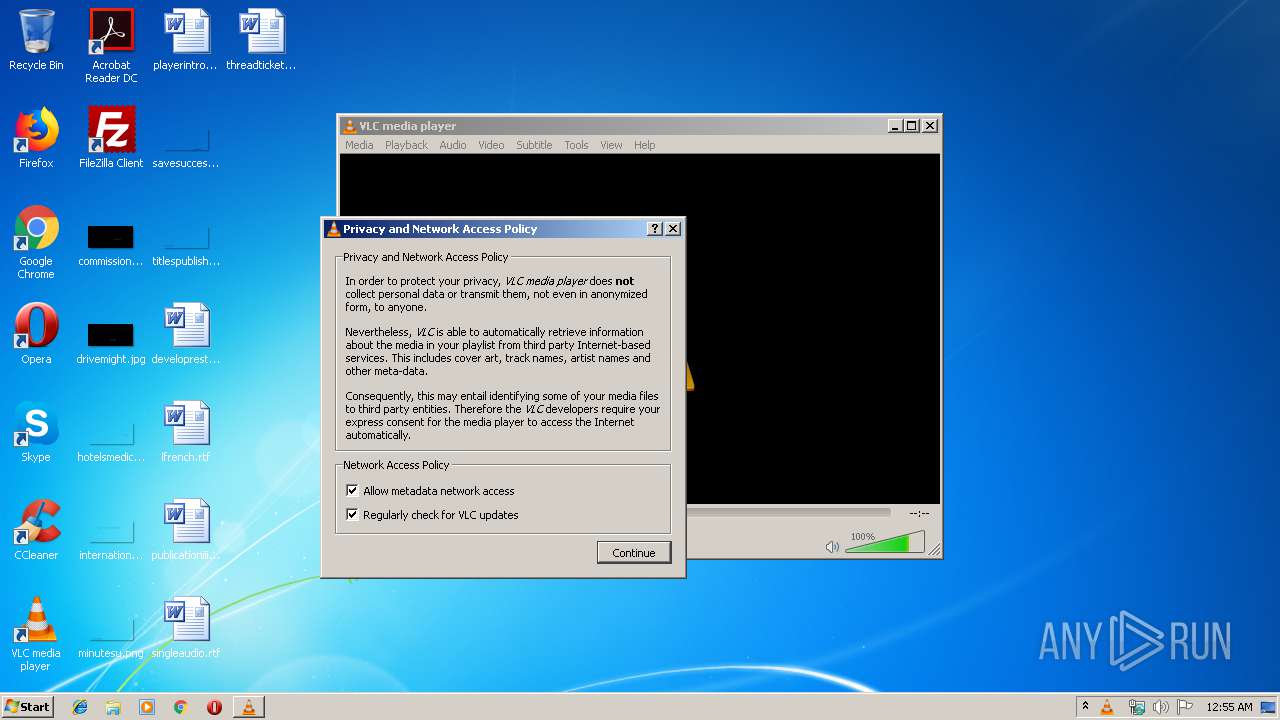
Manual execution by user
- vlc.exe (PID: 2568)
- WINWORD.EXE (PID: 3976)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3976)
Creates files in the user directory
- WINWORD.EXE (PID: 3976)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:09:19 03:32:00+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 571904 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x8d9ae |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | CyaX-Sharp |
| FileVersion: | 1.0.0.0 |
| InternalName: | CyaX-Sharp.exe |
| LegalCopyright: | Copyright © 2019 |
| LegalTrademarks: | - |
| OriginalFileName: | CyaX-Sharp.exe |
| ProductName: | CyaX-Sharp |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Sep-2019 01:32:00 |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | CyaX-Sharp |
| FileVersion: | 1.0.0.0 |
| InternalName: | CyaX-Sharp.exe |
| LegalCopyright: | Copyright © 2019 |
| LegalTrademarks: | - |
| OriginalFilename: | CyaX-Sharp.exe |
| ProductName: | CyaX-Sharp |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 19-Sep-2019 01:32:00 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x0008B9B4 | 0x0008BA00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.90879 |
.rsrc | 0x0008E000 | 0x00000600 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.12167 |
.reloc | 0x00090000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
Imports
mscoree.dll |
Total processes
42
Monitored processes
7
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 936 | "C:\Users\admin\AppData\Local\Temp\CyaX-Sharp.exe" | C:\Users\admin\AppData\Local\Temp\CyaX-Sharp.exe | CyaX-Sharp.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: CyaX-Sharp Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2272 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe /stext "C:\Users\admin\AppData\Local\Temp\holdermail.txt" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | CyaX-Sharp.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5420 Modules
| |||||||||||||||
| 2568 | "C:\Program Files\VideoLAN\VLC\vlc.exe" | C:\Program Files\VideoLAN\VLC\vlc.exe | explorer.exe | ||||||||||||
User: admin Company: VideoLAN Integrity Level: MEDIUM Description: VLC media player Exit code: 0 Version: 2.2.6 Modules
| |||||||||||||||
| 3016 | "C:\Users\admin\AppData\Local\Temp\CyaX-Sharp.exe" | C:\Users\admin\AppData\Local\Temp\CyaX-Sharp.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: CyaX-Sharp Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3148 | "C:\Windows\System32\schtasks.exe" /Create /TN "Updates\HwjXypgJL" /XML "C:\Users\admin\AppData\Local\Temp\tmp807A.tmp" | C:\Windows\System32\schtasks.exe | — | CyaX-Sharp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3172 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe /stext "C:\Users\admin\AppData\Local\Temp\holderwb.txt" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | — | CyaX-Sharp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5420 Modules
| |||||||||||||||
| 3976 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\playerintroduction.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
865
Read events
782
Write events
72
Delete events
11
Modification events
| (PID) Process: | (3976) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | &p& |
Value: 26702600880F0000010000000000000000000000 | |||
| (PID) Process: | (3976) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3976) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3976) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1328807967 | |||
| (PID) Process: | (3976) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1328808080 | |||
| (PID) Process: | (3976) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1328808081 | |||
| (PID) Process: | (3976) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 880F000039F0F5D0456FD50100000000 | |||
| (PID) Process: | (3976) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | nq& |
Value: 6E712600880F000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3976) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | nq& |
Value: 6E712600880F000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3976) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
1
Suspicious files
4
Text files
7
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2568 | vlc.exe | C:\Users\admin\AppData\Roaming\vlc\ml.xspf.tmp2568 | — | |
MD5:— | SHA256:— | |||
| 3976 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR6486.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3976 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{B7041AF2-568B-4A38-A47F-94D73BBF4464}.tmp | — | |
MD5:— | SHA256:— | |||
| 3976 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{55AF3CFE-5C4A-47CB-B3F2-ACE5FF33ABD7}.tmp | — | |
MD5:— | SHA256:— | |||
| 2272 | vbc.exe | C:\Users\admin\AppData\Local\Temp\holdermail.txt | — | |
MD5:— | SHA256:— | |||
| 3172 | vbc.exe | C:\Users\admin\AppData\Local\Temp\holderwb.txt | — | |
MD5:— | SHA256:— | |||
| 936 | CyaX-Sharp.exe | C:\Users\admin\AppData\Local\Temp\CabDC66.tmp | — | |
MD5:— | SHA256:— | |||
| 936 | CyaX-Sharp.exe | C:\Users\admin\AppData\Local\Temp\TarDC67.tmp | — | |
MD5:— | SHA256:— | |||
| 936 | CyaX-Sharp.exe | C:\Users\admin\AppData\Local\Temp\CabDC87.tmp | — | |
MD5:— | SHA256:— | |||
| 936 | CyaX-Sharp.exe | C:\Users\admin\AppData\Local\Temp\TarDC88.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
4
DNS requests
3
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
936 | CyaX-Sharp.exe | GET | 301 | 104.16.155.36:80 | http://whatismyipaddress.com/ | US | — | — | shared |
936 | CyaX-Sharp.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.0 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
936 | CyaX-Sharp.exe | 104.16.155.36:443 | whatismyipaddress.com | Cloudflare Inc | US | shared |
936 | CyaX-Sharp.exe | 104.16.155.36:80 | whatismyipaddress.com | Cloudflare Inc | US | shared |
936 | CyaX-Sharp.exe | 173.201.192.229:587 | smtpout.secureserver.net | GoDaddy.com, LLC | US | unknown |
936 | CyaX-Sharp.exe | 93.184.221.240:80 | www.download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
whatismyipaddress.com |
| shared |
smtpout.secureserver.net |
| malicious |
www.download.windowsupdate.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
936 | CyaX-Sharp.exe | Potential Corporate Privacy Violation | ET POLICY Known External IP Lookup Service Domain in SNI |
936 | CyaX-Sharp.exe | A Network Trojan was detected | MALWARE [PTsecurity] Spyware.HawkEyeKeyLogger (IP Chck) |
936 | CyaX-Sharp.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2 ETPRO signatures available at the full report
Process | Message |
|---|---|
vlc.exe | core libvlc: Running vlc with the default interface. Use 'cvlc' to use vlc without interface.
|