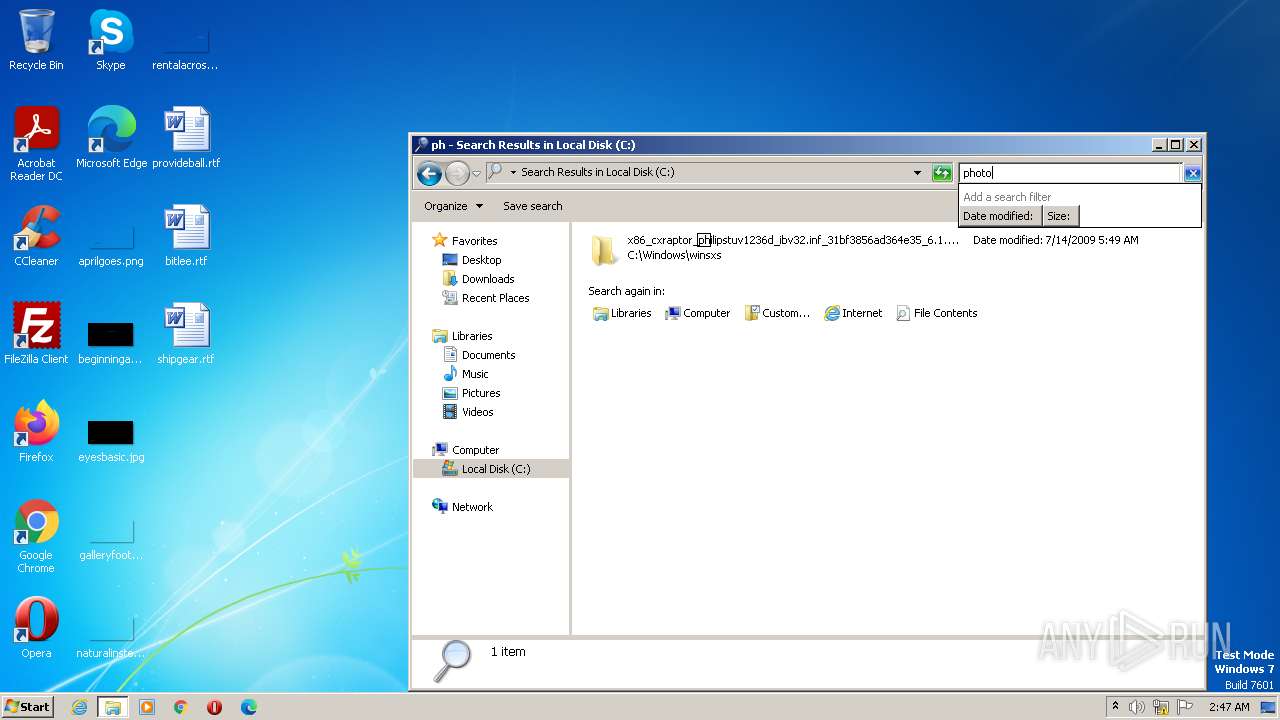
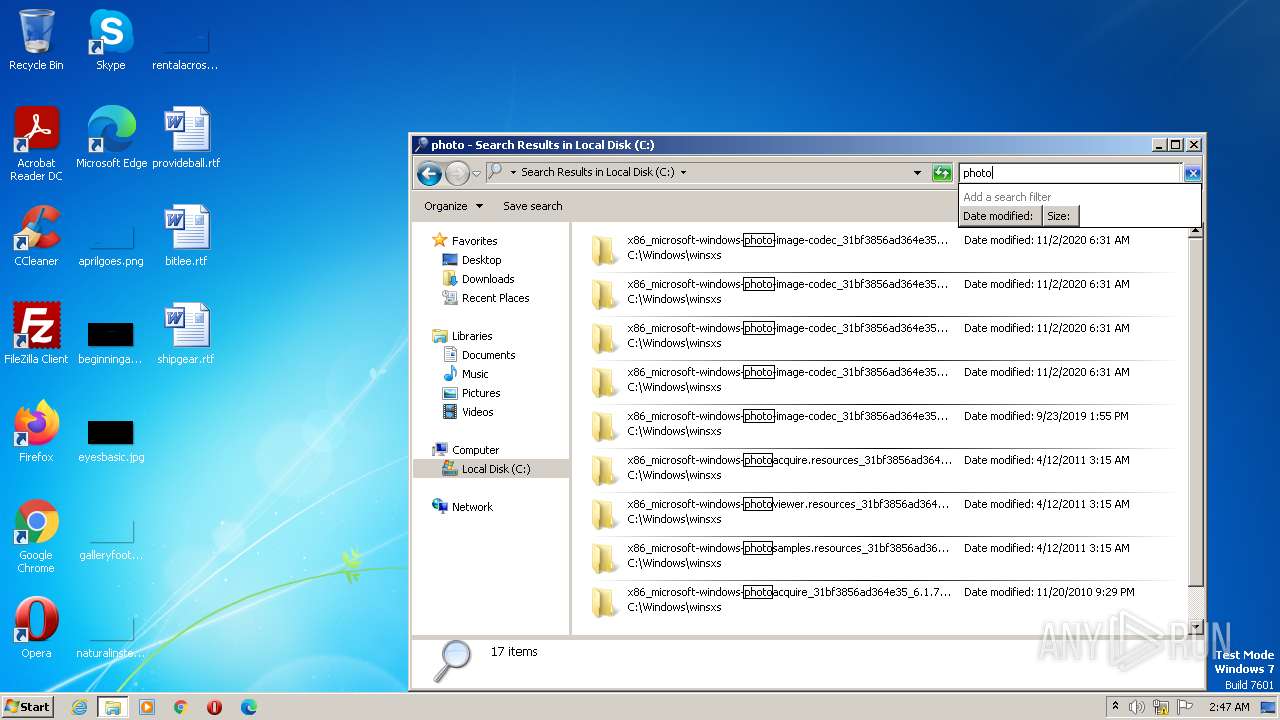
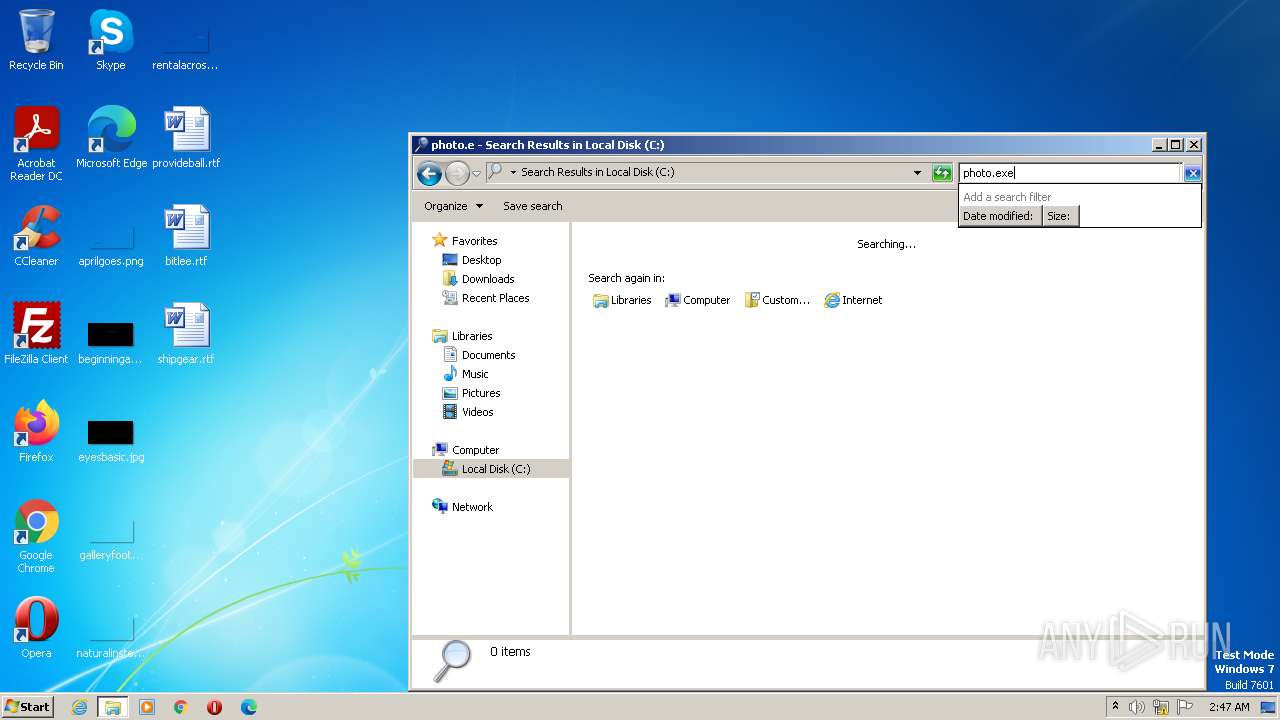
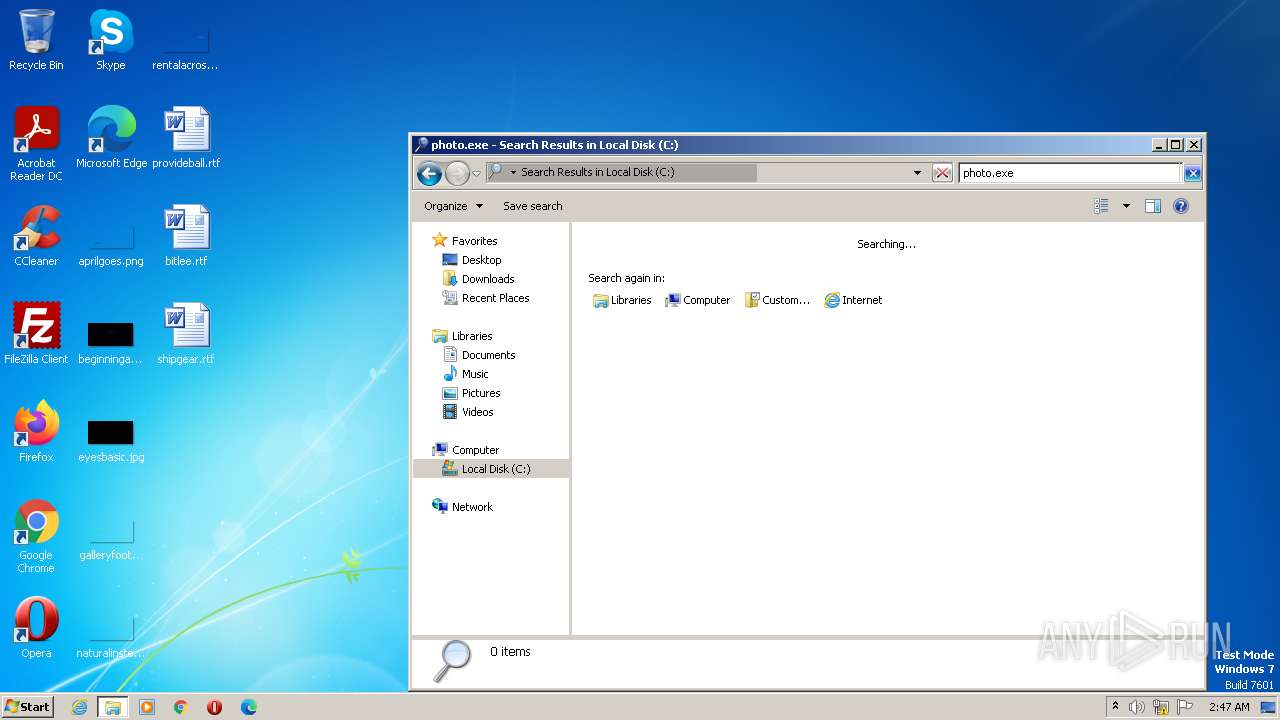
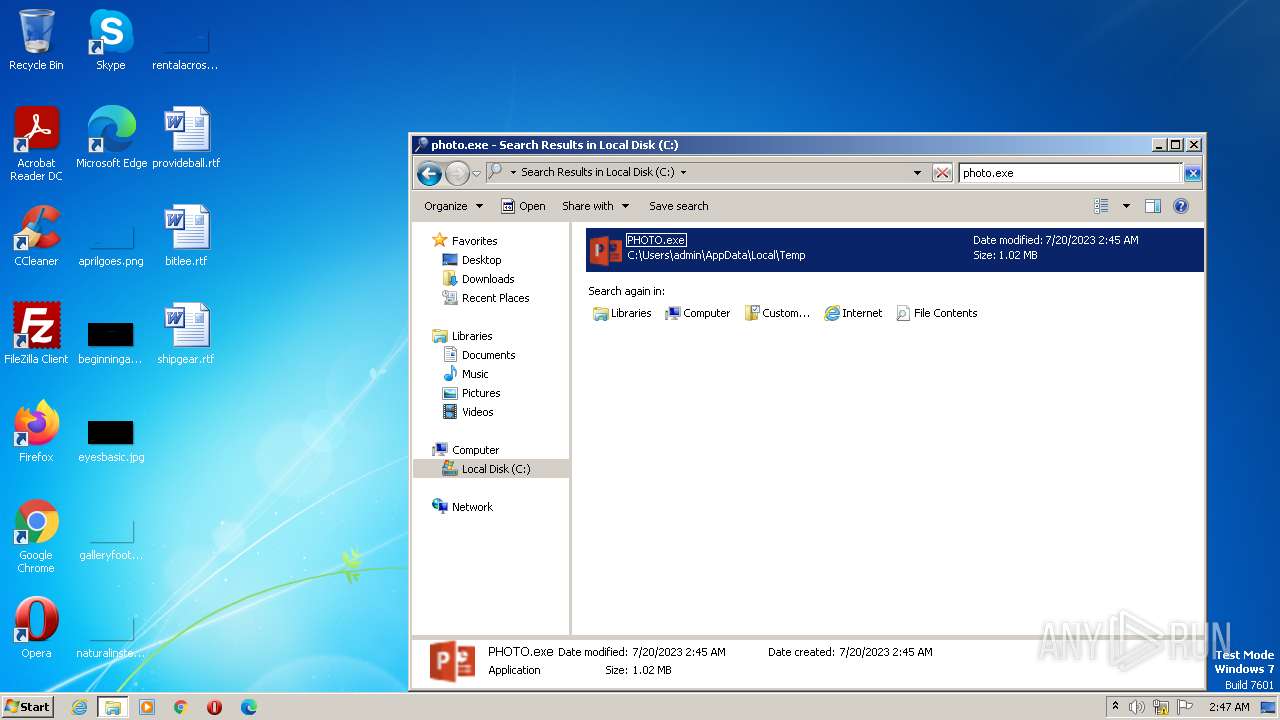
| File name: | PHOTO.exe |
| Full analysis: | https://app.any.run/tasks/c9147f00-4706-48bd-b578-ad6593c7c396 |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | July 20, 2023, 01:45:24 |
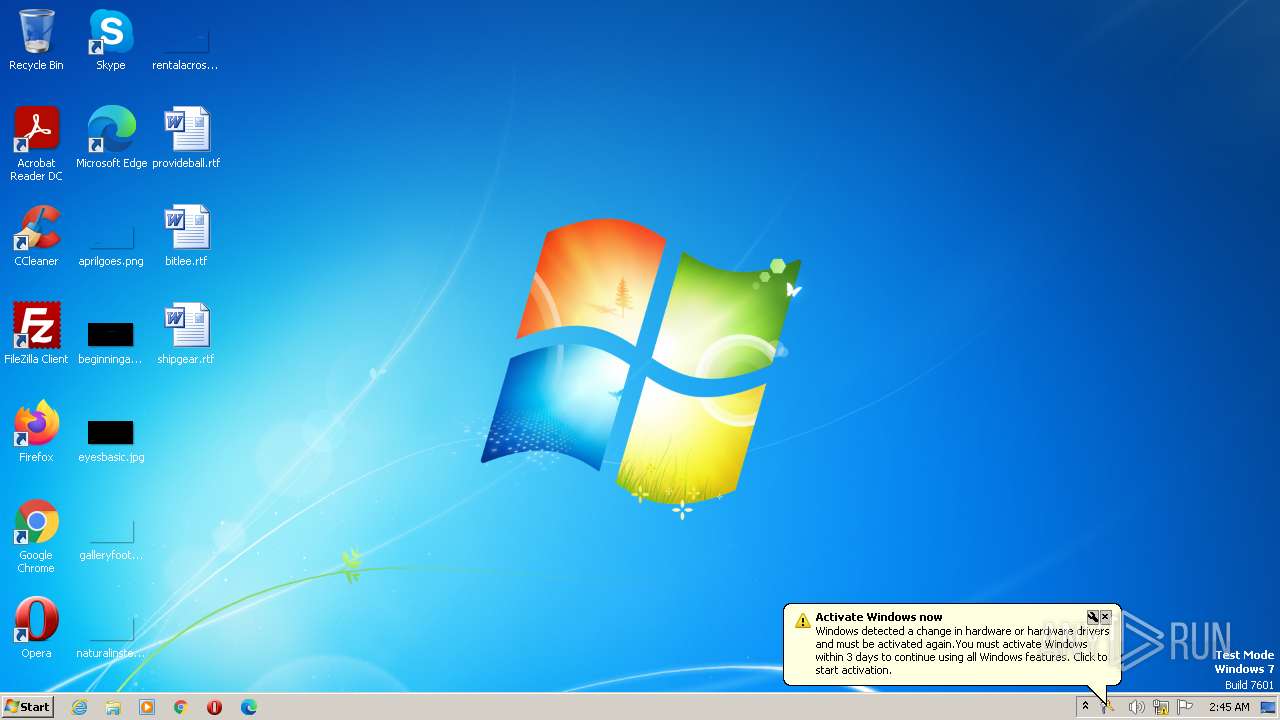
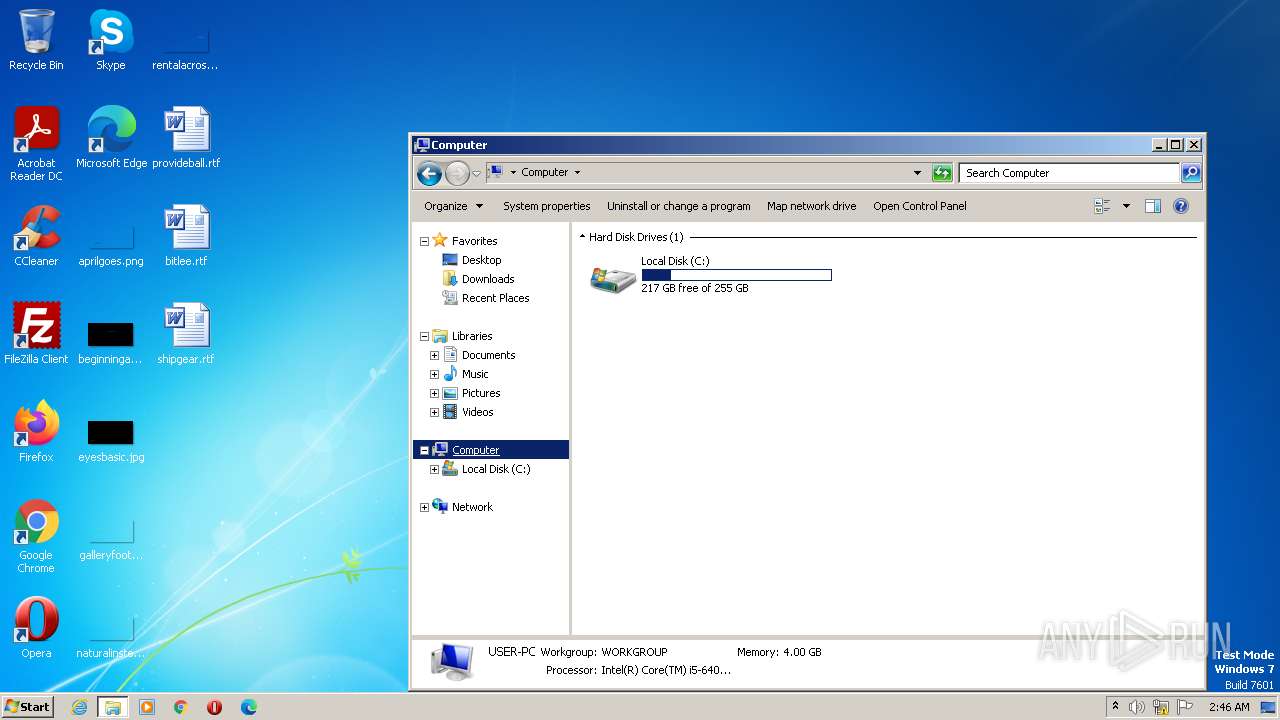
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | F5CE5124818F609EA74FBAFAF084037D |
| SHA1: | F81AC2D9CE1A0FC3E88BE38F123C80AAEF4E7A52 |
| SHA256: | F29CBE65A3306988BA4E1945BCE656ADE7CE94FD178E354300BCD698D86FCB5E |
| SSDEEP: | 12288:uu53usy507Qtc9+0uv1YBorOjAFK5w6/JZffHYYHlCEQQFhhiGqvQIFnUzbLGidF:d5+sym78Pf10oHK5j/Hf5nQQViSzW |
MALICIOUS
Uses Task Scheduler to run other applications
- PHOTO.exe (PID: 3344)
- PHOTO.exe (PID: 2380)
- PHOTO.exe (PID: 1592)
Actions looks like stealing of personal data
- rundll32.exe (PID: 3756)
- explorer.exe (PID: 1312)
FORMBOOK was detected
- explorer.exe (PID: 1312)
Steals credentials from Web Browsers
- explorer.exe (PID: 1312)
FORMBOOK detected by memory dumps
- rundll32.exe (PID: 3756)
Connects to the CnC server
- explorer.exe (PID: 1312)
Unusual connection from system programs
- rundll32.exe (PID: 3756)
SUSPICIOUS
Reads the Internet Settings
- explorer.exe (PID: 1312)
- PHOTO.exe (PID: 3344)
- rundll32.exe (PID: 3756)
- PHOTO.exe (PID: 2380)
- PHOTO.exe (PID: 1592)
Application launched itself
- PHOTO.exe (PID: 3344)
- PHOTO.exe (PID: 2380)
- PHOTO.exe (PID: 1592)
Executable content was dropped or overwritten
- PHOTO.exe (PID: 3344)
Loads DLL from Mozilla Firefox
- rundll32.exe (PID: 3756)
INFO
Checks supported languages
- PHOTO.exe (PID: 3344)
- PHOTO.exe (PID: 2964)
- PHOTO.exe (PID: 2380)
- PHOTO.exe (PID: 1592)
- PHOTO.exe (PID: 2984)
- PHOTO.exe (PID: 3576)
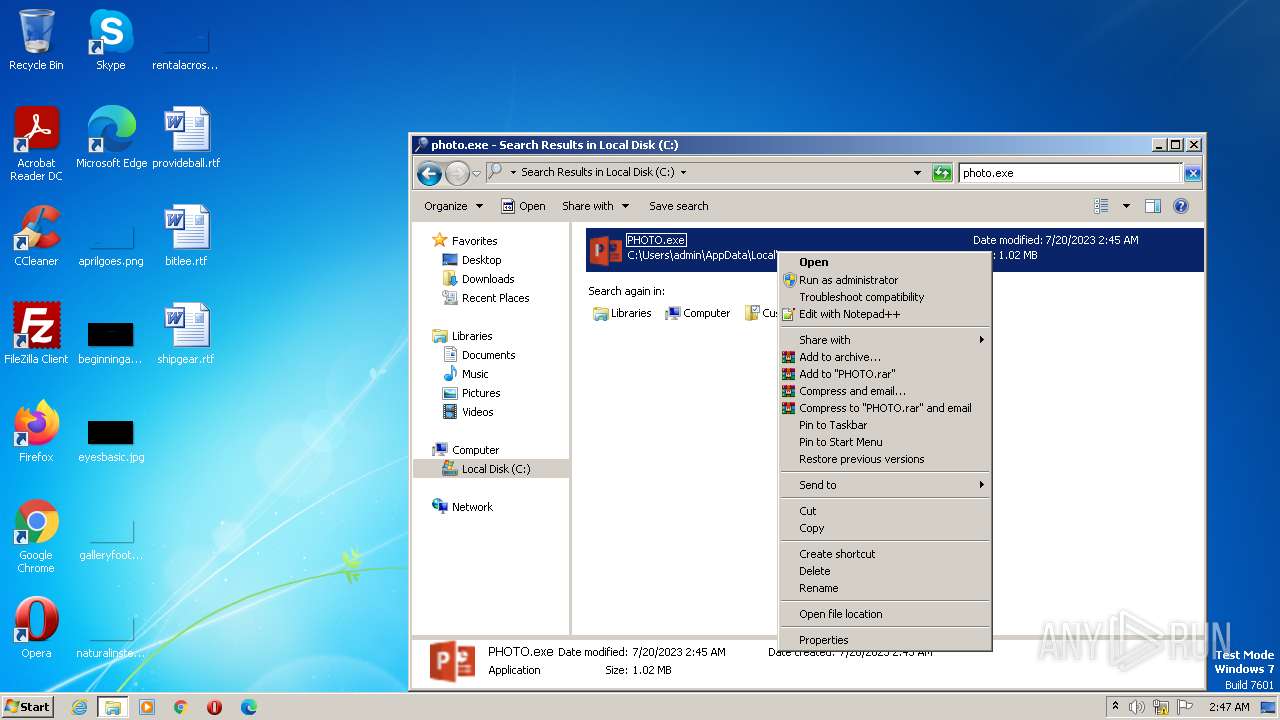
Manual execution by a user
- explorer.exe (PID: 3880)
- rundll32.exe (PID: 3756)
The process checks LSA protection
- PHOTO.exe (PID: 3344)
- explorer.exe (PID: 3880)
- rundll32.exe (PID: 3756)
- PHOTO.exe (PID: 1592)
- PHOTO.exe (PID: 2380)
Creates files or folders in the user directory
- PHOTO.exe (PID: 3344)
- rundll32.exe (PID: 3756)
Reads the computer name
- PHOTO.exe (PID: 3344)
- PHOTO.exe (PID: 2964)
- PHOTO.exe (PID: 2380)
- PHOTO.exe (PID: 1592)
- PHOTO.exe (PID: 3576)
- PHOTO.exe (PID: 2984)
Create files in a temporary directory
- PHOTO.exe (PID: 3344)
- PHOTO.exe (PID: 1592)
- PHOTO.exe (PID: 2380)
Reads the machine GUID from the registry
- PHOTO.exe (PID: 3344)
- PHOTO.exe (PID: 2380)
- PHOTO.exe (PID: 1592)
Checks proxy server information
- rundll32.exe (PID: 3756)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Formbook
(PID) Process(3756) rundll32.exe
C2www.bico-tender.com/s92n/
Strings (79)USERNAME
LOCALAPPDATA
USERPROFILE
APPDATA
TEMP
ProgramFiles
CommonProgramFiles
ALLUSERSPROFILE
/c copy "
/c del "
\Run
\Policies
\Explorer
\Registry\User
\Registry\Machine
\SOFTWARE\Microsoft\Windows\CurrentVersion
Office\15.0\Outlook\Profiles\Outlook\
NT\CurrentVersion\Windows Messaging Subsystem\Profiles\Outlook\
\SOFTWARE\Mozilla\Mozilla
\Mozilla
Username:
Password:
formSubmitURL
usernameField
encryptedUsername
encryptedPassword
\logins.json
\signons.sqlite
\Microsoft\Vault\
SELECT encryptedUsername, encryptedPassword, formSubmitURL FROM moz_logins
\Google\Chrome\User Data\Default\Login Data
SELECT origin_url, username_value, password_value FROM logins
.exe
.com
.scr
.pif
.cmd
.bat
ms
win
gdi
mfc
vga
igfx
user
help
config
update
regsvc
chkdsk
systray
audiodg
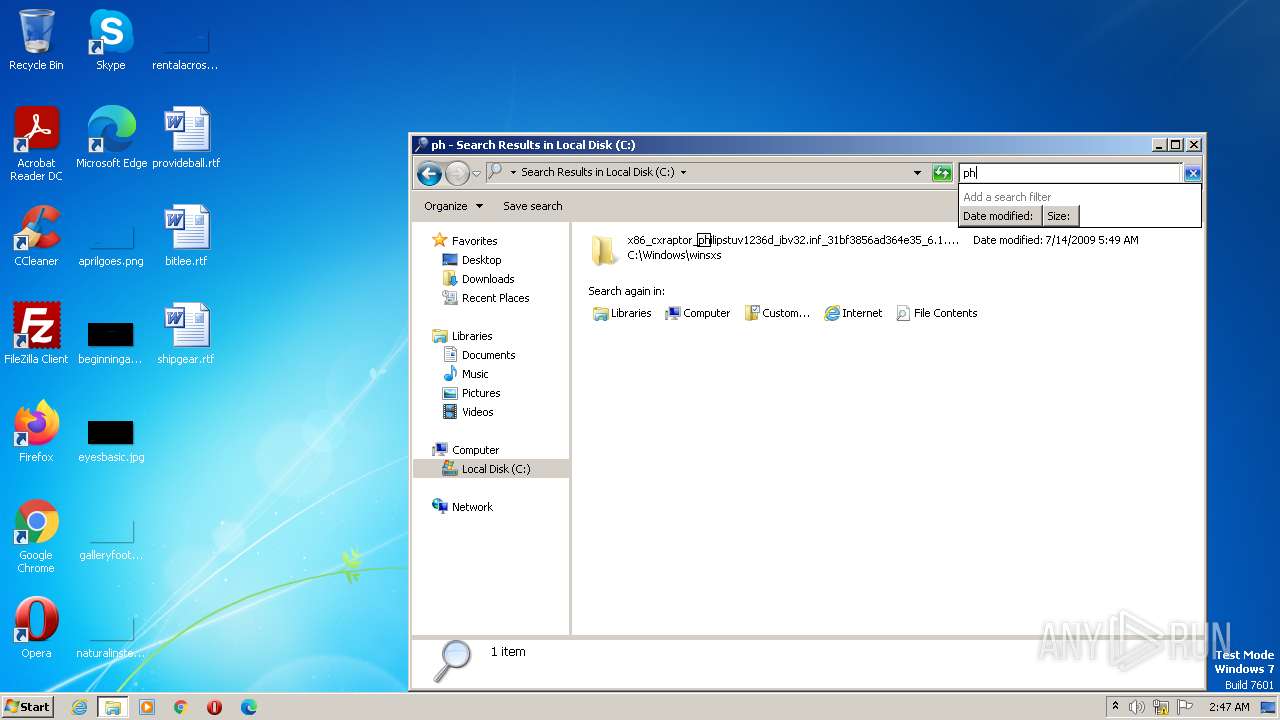
certmgr
autochk
taskhost
colorcpl
services
IconCache
ThumbCache
Cookies
SeDebugPrivilege
SeShutdownPrivilege
\BaseNamedObjects
config.php
POST
HTTP/1.1
Host:
Connection: close
Content-Length:
Cache-Control: no-cache
Origin: http://
User-Agent: Mozilla Firefox/4.0
Content-Type: application/x-www-form-urlencoded
Accept: */*
Referer: http://
Accept-Language: en-US
Accept-Encoding: gzip, deflate
dat=
f-start
f-end
Decoy C2 (64)granlogiasoberana.com
roblox-so.com
buycarsonline.fyi
thesaleworld.com
laterlifegroup.com
lov3stia.com
frdgg.cfd
businessllp.com
margaretsbeautifiedshop.com
123bet.store
sadalagran.com
psychedelicshippiez.com
bonitaspringskayakrentals.com
thorsbyinsurance.com
visionauto-int.com
k3cosmetic.skin
ilogtv.com
one-big-yes.com
houseofmorrow.com
pisigranjariogrande.online
dccasualwear.com
cuemark.xyz
robotics6.com
maddieschiess.com
centraleasy.sbs
attymarket.com
protectordoormi.com
integratedpayment.solutions
diamondtattoo.contact
alliancesecuritiesandcour.com
mountkaalaranch.net
nobodyspuppet.com
ygiciftee-zakroapsala.online
heartfocusedmethod.com
evolutionaryclassics.com
whizfirst.com
redeyeload.site
muslimflyers.com
mihantrade.com
naturalproductsv.online
perfectjobgifts.com
historias-abdl.com
growelevation.agency
humanresourcesai.com
prime-cmed.com
abhishekdanidesign.com
codeonsp.site
vaulteddb.com
drmurilobarbalho.com
sceju29t.xyz
starmapsky.com
winsettfamilyphotography.com
patibannister.com
condotel-vietnam.com
simmonsmotorsales.com
tobenaifusen.com
1yes.store
8565933.xyz
esenarh.com
701fegans.com
info-lani.com
bluenestcapital.com
41749.xyz
manageable-cv.com
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| AssemblyVersion: | 1.0.0.0 |
|---|---|
| ProductVersion: | 1.0.0.0 |
| ProductName: | GreenPixelsCalculator |
| OriginalFileName: | pKhwvZ.exe |
| LegalTrademarks: | - |
| LegalCopyright: | Copyright © 2021 |
| InternalName: | pKhwvZ.exe |
| FileVersion: | 1.0.0.0 |
| FileDescription: | GreenPixelsCalculator |
| CompanyName: | - |
| Comments: | - |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.0 |
| FileVersionNumber: | 1.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x10669a |
| UninitializedDataSize: | - |
| InitializedDataSize: | 12288 |
| CodeSize: | 1067008 |
| LinkerVersion: | 48 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, 32-bit |
| TimeStamp: | 2064:10:13 01:13:27+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 13-Oct-2064 01:13:27 |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | GreenPixelsCalculator |
| FileVersion: | 1.0.0.0 |
| InternalName: | pKhwvZ.exe |
| LegalCopyright: | Copyright © 2021 |
| LegalTrademarks: | - |
| OriginalFilename: | pKhwvZ.exe |
| ProductName: | GreenPixelsCalculator |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 13-Oct-2064 01:13:27 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x001046A0 | 0x00104800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.19666 |
.rsrc | 0x00108000 | 0x00002C1C | 0x00002E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.41053 |
.reloc | 0x0010C000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
Imports
mscoree.dll |
Total processes
63
Monitored processes
19
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 664 | "C:\Windows\System32\schtasks.exe" /Create /TN "Updates\dhnXWPEb" /XML "C:\Users\admin\AppData\Local\Temp\tmp8373.tmp" | C:\Windows\System32\schtasks.exe | — | PHOTO.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1312 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1592 | "C:\Users\admin\AppData\Local\Temp\PHOTO.exe" | C:\Users\admin\AppData\Local\Temp\PHOTO.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: GreenPixelsCalculator Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2240 | "C:\Users\admin\AppData\Local\Temp\PHOTO.exe" | C:\Users\admin\AppData\Local\Temp\PHOTO.exe | — | PHOTO.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: GreenPixelsCalculator Exit code: 4294967295 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2380 | "C:\Users\admin\AppData\Local\Temp\PHOTO.exe" | C:\Users\admin\AppData\Local\Temp\PHOTO.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: GreenPixelsCalculator Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2504 | "C:\Users\admin\AppData\Local\Temp\PHOTO.exe" | C:\Users\admin\AppData\Local\Temp\PHOTO.exe | — | PHOTO.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: GreenPixelsCalculator Exit code: 4294967295 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2528 | "C:\Users\admin\AppData\Local\Temp\PHOTO.exe" | C:\Users\admin\AppData\Local\Temp\PHOTO.exe | — | PHOTO.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: GreenPixelsCalculator Exit code: 4294967295 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2664 | "C:\Windows\System32\schtasks.exe" /Create /TN "Updates\dhnXWPEb" /XML "C:\Users\admin\AppData\Local\Temp\tmp8E75.tmp" | C:\Windows\System32\schtasks.exe | — | PHOTO.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2720 | "C:\Users\admin\AppData\Local\Temp\PHOTO.exe" | C:\Users\admin\AppData\Local\Temp\PHOTO.exe | — | PHOTO.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: GreenPixelsCalculator Exit code: 4294967295 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2720 | "C:\Windows\System32\wuapp.exe" | C:\Windows\System32\wuapp.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Update Application Launcher Exit code: 0 Version: 7.6.7601.24436 (win7sp1_ldr.190409-0600) Modules
| |||||||||||||||
Total events
11 094
Read events
10 162
Write events
929
Delete events
3
Modification events
| (PID) Process: | (1312) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Action Center\Checks\{C8E6F269-B90A-4053-A3BE-499AFCEC98C4}.check.0 |
| Operation: | write | Name: | CheckSetting |
Value: 01000000D08C9DDF0115D1118C7A00C04FC297EB01000000F6D6788197A75D498472ACE88906AC8D00000000020000000000106600000001000020000000822A0AA37BD64DCF095E29F2164E703AE1EF09DC1955E37D2B5F07EC0D9DC876000000000E8000000002000020000000F6E5170D8E8A54BFA6283D84BEAC0836AD43E5CA79E0A347C63795856F407CCD30000000DB0B43955438667F03B8BCD40CBCD0EABF1FBC25F8908345B213D91299A931295DA98D90C9DD2FE8B8A74D8FEACAC4CA400000008AA373F50207B8273EF7C69FA9F8561955D51D29923A7A8A80A32E3F89E7449663AE1558D12A01F64A3ADE7CB625A4122DEA863FC64BC78A4C38008A4C7E43A5 | |||
| (PID) Process: | (1312) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | {S38OS404-1Q43-42S2-9305-67QR0O28SP23}\rkcybere.rkr |
Value: 00000000350000006E000000DA122900000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF80C0FAEEC863D90100000000 | |||
| (PID) Process: | (1312) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 00000000660100009A020000C3CC28013F0000004A0000008E0F0D004D006900630072006F0073006F00660074002E0049006E007400650072006E00650074004500780070006C006F007200650072002E00440065006600610075006C007400000028003E004000A4E75102B8E651020000000000000000000000000000080274E45102000008026CE25102000000000000D26CFFFFFFFF705911750000000000000000A4E251027C900D75000400000000000008E35102FFFFFFFF38EA7000FFFFFFFF080A7400D80E740030EA7000D4E25102F7AF3D7680D0707614F05102081D3E76E4613E766820700008E351020000000071000000BBF2CB00E8E25102A1693E766820700008E351020000000014E551023F613E766820700008E3510200000400000000800400000026E4510298E351025DA5147726E45102D26E147779A51477D6794D7526E4510210E65102000100006400610072E3510226E451026F0061006D0069006E0067005C006D006900630072006F0073006F0066007400CCE351023400000080E35102DE70310033003300350033003800310030003000F8E551025A000000A0E351021DA71477D6610E02D4E351025A00000010E651025C00000011000000104F7000084F7000F8E55102C4E3510220E40000D7F3CB00D0E351025E903E7620E45102D4E3510203943E760000000064561802FCE35102A9933E7664561802A8E45102D8511802BD933E7600000000D8511802A8E4510204E45102000000007800000021E55E004D006900630072006F0073006F00660074002E00570069006E0064006F00770073002E0043006F006E00740072006F006C00500061006E0065006C00000000001F00200000000027000000000000000000002A72D0E83A020000000074ED3A020507DD742AD95BF2FEFFFFFF0F87DB74A36CDB747586DB74B6B3BA8490EE3A0210000000DF0005003C003E0090EE3A02A4ED3A020000000000000000000000000000080260EB3A020000080258E93A020000000000002A7200000500280C6E020000000005000000CC0B6E020100000020EC3A0218EC3A020000000078AC6E023C00000000000000010001000000000020EC3A0218EC3A02F8476E026EA3BC8418EA3A0214051177E4E93A0202000000010000001000000000000000000000003C0B6E020500000000000000280C6E023C0B6E0204590E7700000000B8B86E0202000000B8B86E020100000011000000204F2400184F2400CC0B6E020000000058EB3A023C0B6E0278EA000074A1BC8428EA3A025E90557578EA3A02AC1B000040A1BC843CEA3A02929B5575B01B0B034C06000054EA3A0220170B0360EA3A02549B55751290557540D0877511000000204F2400184F240040170B03CCEA000000A1BC847CEA3A025E905575CCEA3A0280EA3A020394557500000000AC1B0B03A8EA3A02A9935575AC1B0B0354EB3A0220170B03BD9355750000000020170B0354EB3A02B0EA3A02000000007800000021E55E004D006900630072006F0073006F00660074002E00570069006E0064006F00770073002E0043006F006E00740072006F006C00500061006E0065006C00000000001F00200000000027000000000000000000002A72D0E83A020000000074ED3A020507DD742AD95BF2FEFFFFFF0F87DB74A36CDB747586DB74B6B3BA8490EE3A0210000000DF0005003C003E0090EE3A02A4ED3A020000000000000000000000000000080260EB3A020000080258E93A020000000000002A7200000500280C6E020000000005000000CC0B6E020100000020EC3A0218EC3A020000000078AC6E023C00000000000000010001000000000020EC3A0218EC3A02F8476E026EA3BC8418EA3A0214051177E4E93A0202000000010000001000000000000000000000003C0B6E020500000000000000280C6E023C0B6E0204590E7700000000B8B86E0202000000B8B86E020100000011000000204F2400184F2400CC0B6E020000000058EB3A023C0B6E0278EA000074A1BC8428EA3A025E90557578EA3A02AC1B000040A1BC843CEA3A02929B5575B01B0B034C06000054EA3A0220170B0360EA3A02549B55751290557540D0877511000000204F2400184F240040170B03CCEA000000A1BC847CEA3A025E905575CCEA3A0280EA3A020394557500000000AC1B0B03A8EA3A02A9935575AC1B0B0354EB3A0220170B03BD9355750000000020170B0354EB3A02B0EA3A02 | |||
| (PID) Process: | (1312) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | {9R3995NO-1S9P-4S13-O827-48O24O6P7174}\GnfxOne\Jvaqbjf Rkcybere.yax |
Value: 00000000330000000000000033000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF80C0FAEEC863D90100000000 | |||
| (PID) Process: | (1312) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 00000000BB00000000000000BB0000003E000000000000003E0000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C0049006E007400650072006E006500740020004500780070006C006F007200650072002E006C006E006B0000006C006E006B0000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000987880574F8C6244BB6371042380B109000000000000000000006D000000000078AB287598117500084B7600981175000000000000000000DE1C0000E0791401C8D4D60313A91477E01D32BD0C0C00001027000002000000FF560200FCD4D603D8A81477FF560200E07914011CD5D603C05C18029CD5D60300000000A40100005CD500009BC44C010CD5D6035E903E765CD5D60310D5D60303943E76000000004C61180238D5D603A9933E764C611802E4D5D603C05C1802BD933E7600000000C05C1802E4D5D60340D5D6033E000000000000003E0000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C0049006E007400650072006E006500740020004500780070006C006F007200650072002E006C006E006B0000006C006E006B0000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000987880574F8C6244BB6371042380B109000000000000000000006D000000000078AB287598117500084B7600981175000000000000000000DE1C0000E0791401C8D4D60313A91477E01D32BD0C0C00001027000002000000FF560200FCD4D603D8A81477FF560200E07914011CD5D603C05C18029CD5D60300000000A40100005CD500009BC44C010CD5D6035E903E765CD5D60310D5D60303943E76000000004C61180238D5D603A9933E764C611802E4D5D603C05C1802BD933E7600000000C05C1802E4D5D60340D5D6033E000000000000003E0000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C0049006E007400650072006E006500740020004500780070006C006F007200650072002E006C006E006B0000006C006E006B0000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000987880574F8C6244BB6371042380B109000000000000000000006D000000000078AB287598117500084B7600981175000000000000000000DE1C0000E0791401C8D4D60313A91477E01D32BD0C0C00001027000002000000FF560200FCD4D603D8A81477FF560200E07914011CD5D603C05C18029CD5D60300000000A40100005CD500009BC44C010CD5D6035E903E765CD5D60310D5D60303943E76000000004C61180238D5D603A9933E764C611802E4D5D603C05C1802BD933E7600000000C05C1802E4D5D60340D5D603 | |||
| (PID) Process: | (1312) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | {9R3995NO-1S9P-4S13-O827-48O24O6P7174}\GnfxOne\Jvaqbjf Rkcybere.yax |
Value: 00000000340000000000000033000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF403852EEABBAD90100000000 | |||
| (PID) Process: | (1312) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 00000000BC00000000000000BB0000003E000000000000003E0000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C0049006E007400650072006E006500740020004500780070006C006F007200650072002E006C006E006B0000006C006E006B0000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000987880574F8C6244BB6371042380B109000000000000000000006D000000000078AB287598117500084B7600981175000000000000000000DE1C0000E0791401C8D4D60313A91477E01D32BD0C0C00001027000002000000FF560200FCD4D603D8A81477FF560200E07914011CD5D603C05C18029CD5D60300000000A40100005CD500009BC44C010CD5D6035E903E765CD5D60310D5D60303943E76000000004C61180238D5D603A9933E764C611802E4D5D603C05C1802BD933E7600000000C05C1802E4D5D60340D5D6033E000000000000003E0000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C0049006E007400650072006E006500740020004500780070006C006F007200650072002E006C006E006B0000006C006E006B0000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000987880574F8C6244BB6371042380B109000000000000000000006D000000000078AB287598117500084B7600981175000000000000000000DE1C0000E0791401C8D4D60313A91477E01D32BD0C0C00001027000002000000FF560200FCD4D603D8A81477FF560200E07914011CD5D603C05C18029CD5D60300000000A40100005CD500009BC44C010CD5D6035E903E765CD5D60310D5D60303943E76000000004C61180238D5D603A9933E764C611802E4D5D603C05C1802BD933E7600000000C05C1802E4D5D60340D5D6033E000000000000003E0000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C0049006E007400650072006E006500740020004500780070006C006F007200650072002E006C006E006B0000006C006E006B0000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000987880574F8C6244BB6371042380B109000000000000000000006D000000000078AB287598117500084B7600981175000000000000000000DE1C0000E0791401C8D4D60313A91477E01D32BD0C0C00001027000002000000FF560200FCD4D603D8A81477FF560200E07914011CD5D603C05C18029CD5D60300000000A40100005CD500009BC44C010CD5D6035E903E765CD5D60310D5D60303943E76000000004C61180238D5D603A9933E764C611802E4D5D603C05C1802BD933E7600000000C05C1802E4D5D60340D5D603 | |||
| (PID) Process: | (1312) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (1312) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 07000000020000000C000000000000000B000000010000000D000000060000000A0000000900000008000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (1312) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 02000000070000000C000000000000000B000000010000000D000000060000000A0000000900000008000000030000000500000004000000FFFFFFFF | |||
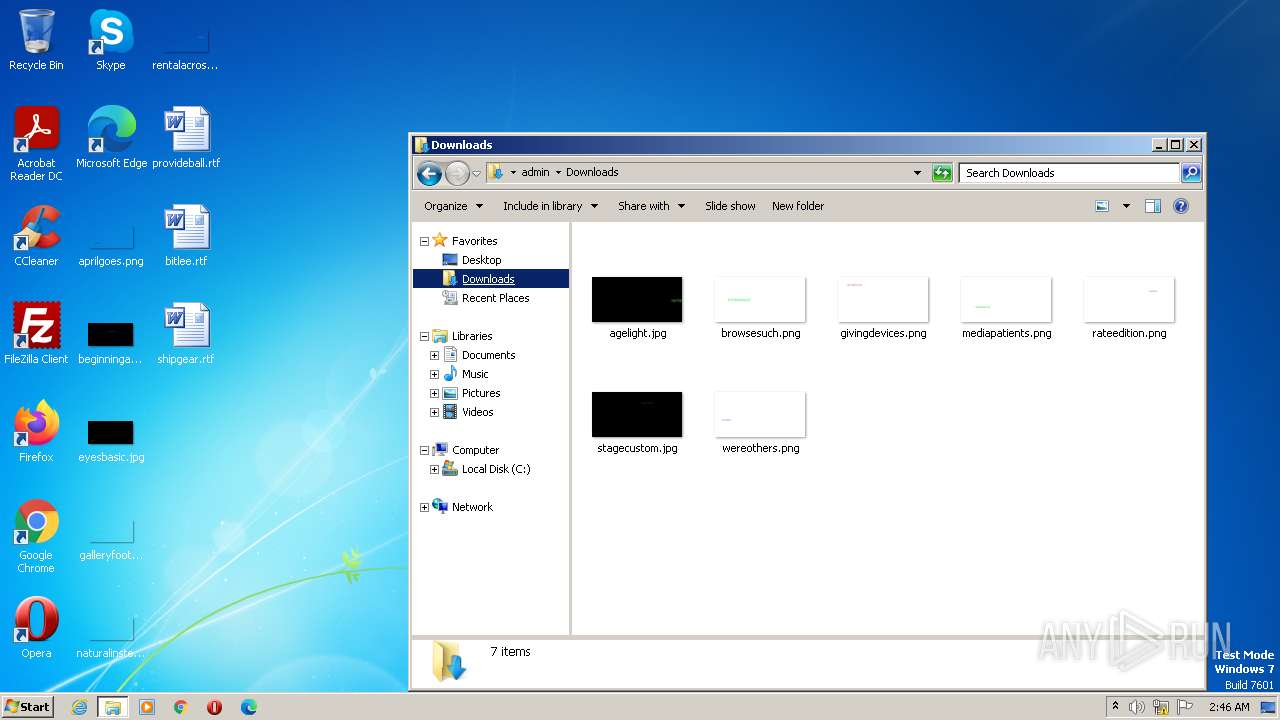
Executable files
1
Suspicious files
4
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3344 | PHOTO.exe | C:\Users\admin\AppData\Roaming\dhnXWPEb.exe | executable | |
MD5:F5CE5124818F609EA74FBAFAF084037D | SHA256:F29CBE65A3306988BA4E1945BCE656ADE7CE94FD178E354300BCD698D86FCB5E | |||
| 3756 | rundll32.exe | C:\Users\admin\AppData\Roaming\L6PR0ST7\L6Plogim.jpeg | image | |
MD5:A80D77D3C0F427FA4C225C268F170DA0 | SHA256:76DADBFE6039D2541C5BE63B977EEF24ED71C2118FF6289906AFDDC6463AD3F0 | |||
| 3344 | PHOTO.exe | C:\Users\admin\AppData\Local\Temp\tmp8373.tmp | xml | |
MD5:B5F4683E8DEAF2F4DA40AF4A564B847A | SHA256:68EBD96DC26F9C2C13490D58EDF24F22FA8B3922175A1CDD903D3F12A322FD65 | |||
| 3756 | rundll32.exe | C:\Users\admin\AppData\Roaming\L6PR0ST7\L6Plogrc.ini | binary | |
MD5:E03F207A7B9CFC4D877ED2EC64BE028E | SHA256:B17183098B6E349844A3151456EDF62C8E41B2348D2445A610C0FF1E29963067 | |||
| 1592 | PHOTO.exe | C:\Users\admin\AppData\Local\Temp\tmpCF85.tmp | xml | |
MD5:B5F4683E8DEAF2F4DA40AF4A564B847A | SHA256:68EBD96DC26F9C2C13490D58EDF24F22FA8B3922175A1CDD903D3F12A322FD65 | |||
| 3756 | rundll32.exe | C:\Users\admin\AppData\Roaming\L6PR0ST7\L6Plogri.ini | binary | |
MD5:D63A82E5D81E02E399090AF26DB0B9CB | SHA256:EAECE2EBA6310253249603033C744DD5914089B0BB26BDE6685EC9813611BAAE | |||
| 2380 | PHOTO.exe | C:\Users\admin\AppData\Local\Temp\tmp8E75.tmp | xml | |
MD5:B5F4683E8DEAF2F4DA40AF4A564B847A | SHA256:68EBD96DC26F9C2C13490D58EDF24F22FA8B3922175A1CDD903D3F12A322FD65 | |||
| 3980 | firefox.exe | C:\Users\admin\AppData\Roaming\L6PR0ST7\L6Plogrf.ini | binary | |
MD5:2F245469795B865BDD1B956C23D7893D | SHA256:1662D01A2D47B875A34FC7A8CD92E78CB2BA7F34023C7FD2639CBB10B8D94361 | |||
| 3756 | rundll32.exe | C:\Users\admin\AppData\Roaming\L6PR0ST7\L6Plogrv.ini | binary | |
MD5:BA3B6BC807D4F76794C4B81B09BB9BA5 | SHA256:6EEBF968962745B2E9DE2CA969AF7C424916D4E3FE3CC0BB9B3D414ABFCE9507 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
42
DNS requests
10
Threats
18
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1312 | explorer.exe | GET | 403 | 15.197.172.60:80 | http://www.1yes.store/s92n/?GXmhB=Mq/SC6coQ5MFqz702ILyn28AnOlPPv4m3KTPH8snSYHEbY+6kRaEn7obstuj/Z8wIUYibA==&Jtp=XPj8cbcpcn&sql=1 | US | html | 291 b | malicious |
1312 | explorer.exe | GET | 302 | 66.23.239.222:80 | http://www.granlogiasoberana.com/s92n/?GXmhB=cfVpJ9M5QbhYrgHRgJB5hJoZeSUYiWFZbZBvVHXgZVHkYmygw8sXAHvTEBQooit2VdPaew==&Jtp=XPj8cbcpcn&sql=1 | US | html | 683 b | malicious |
1312 | explorer.exe | POST | — | 103.224.182.242:80 | http://www.roblox-so.com/s92n/ | AU | — | — | malicious |
1312 | explorer.exe | POST | — | 15.197.172.60:80 | http://www.1yes.store/s92n/ | US | — | — | malicious |
1312 | explorer.exe | POST | — | 35.186.223.180:80 | http://www.701fegans.com/s92n/ | US | — | — | malicious |
1312 | explorer.exe | POST | — | 66.23.239.222:80 | http://www.granlogiasoberana.com/s92n/ | US | — | — | malicious |
1312 | explorer.exe | POST | — | 66.23.239.222:80 | http://www.granlogiasoberana.com/s92n/ | US | — | — | malicious |
1312 | explorer.exe | GET | 301 | 51.222.40.119:80 | http://www.bluenestcapital.com/s92n/?GXmhB=CHsXkzsUy6e+EMXzuiIMz6r/6JcxugcfhalwyoJFYiLSlSAEx3a+myrsTkbstLA2Q/JndQ==&Jtp=XPj8cbcpcn&sql=1 | GB | html | 353 b | malicious |
3756 | rundll32.exe | GET | 409 | 104.17.157.1:80 | http://www.buycarsonline.fyi/s92n/?GXmhB=Q7bHDA4f0STGkNxCP2ZGw74HQ8wKkay7TEPCSa0iKBwCbq7X6EDP1dUSRTnPiwDRPAVy4w==&Jtp=XPj8cbcpcn&sql=1 | US | text | 16 b | suspicious |
1312 | explorer.exe | POST | — | 35.186.223.180:80 | http://www.701fegans.com/s92n/ | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2640 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1312 | explorer.exe | 66.23.239.222:80 | www.granlogiasoberana.com | IS-AS-1 | US | malicious |
3756 | rundll32.exe | 104.17.158.1:80 | www.buycarsonline.fyi | CLOUDFLARENET | — | whitelisted |
1312 | explorer.exe | 35.186.223.180:80 | www.701fegans.com | GOOGLE | US | malicious |
3756 | rundll32.exe | 104.17.157.1:80 | www.buycarsonline.fyi | CLOUDFLARENET | — | malicious |
1312 | explorer.exe | 91.195.240.12:80 | www.centraleasy.sbs | SEDO GmbH | DE | malicious |
1312 | explorer.exe | 34.149.87.45:80 | www.one-big-yes.com | GOOGLE | US | malicious |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1312 | explorer.exe | 103.224.182.242:80 | www.roblox-so.com | Trellian Pty. Limited | AU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.granlogiasoberana.com |
| malicious |
www.roblox-so.com |
| malicious |
www.1yes.store |
| malicious |
www.buycarsonline.fyi |
| suspicious |
www.701fegans.com |
| malicious |
www.bluenestcapital.com |
| malicious |
www.pisigranjariogrande.online |
| malicious |
www.centraleasy.sbs |
| malicious |
www.one-big-yes.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3756 | rundll32.exe | A Network Trojan was detected | ET USER_AGENTS Suspicious User-Agent (Windows Explorer) |
1312 | explorer.exe | Malware Command and Control Activity Detected | ET MALWARE FormBook CnC Checkin (GET) |
1312 | explorer.exe | Malware Command and Control Activity Detected | ET MALWARE FormBook CnC Checkin (GET) |
1312 | explorer.exe | Malware Command and Control Activity Detected | ET MALWARE FormBook CnC Checkin (GET) |
1312 | explorer.exe | Malware Command and Control Activity Detected | ET MALWARE FormBook CnC Checkin (GET) |
1312 | explorer.exe | Malware Command and Control Activity Detected | ET MALWARE FormBook CnC Checkin (GET) |
12 ETPRO signatures available at the full report