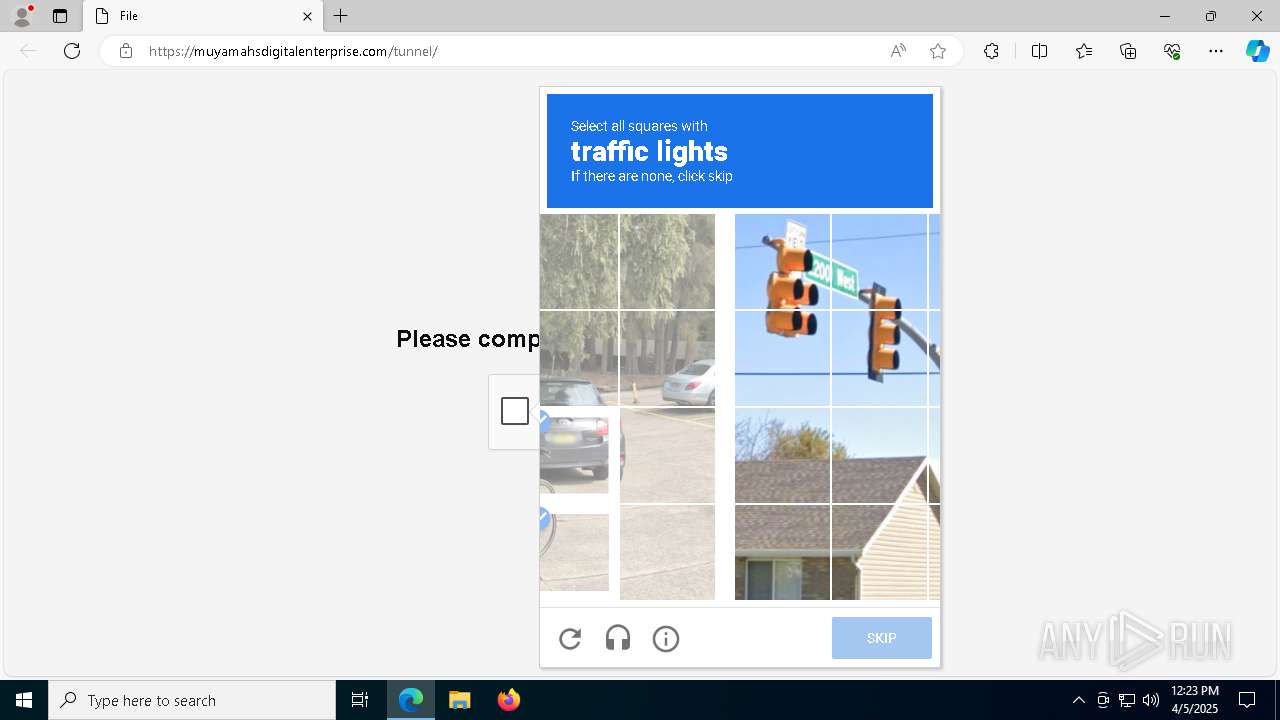
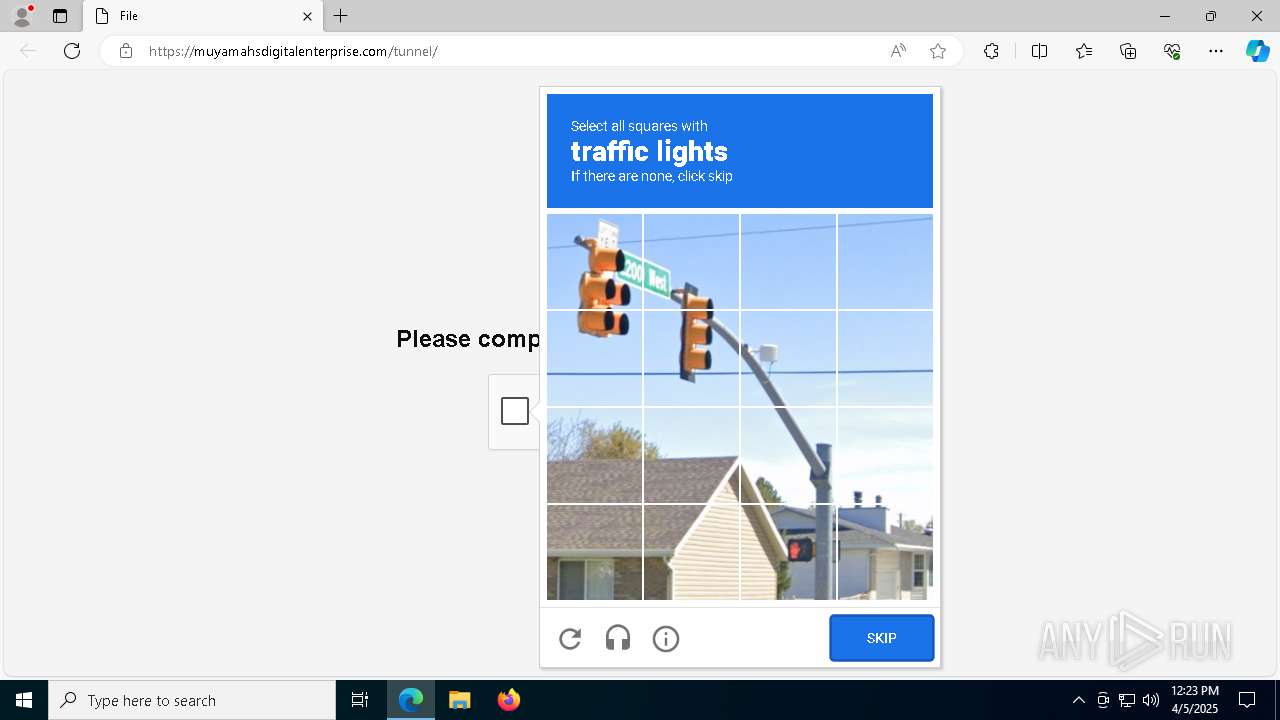
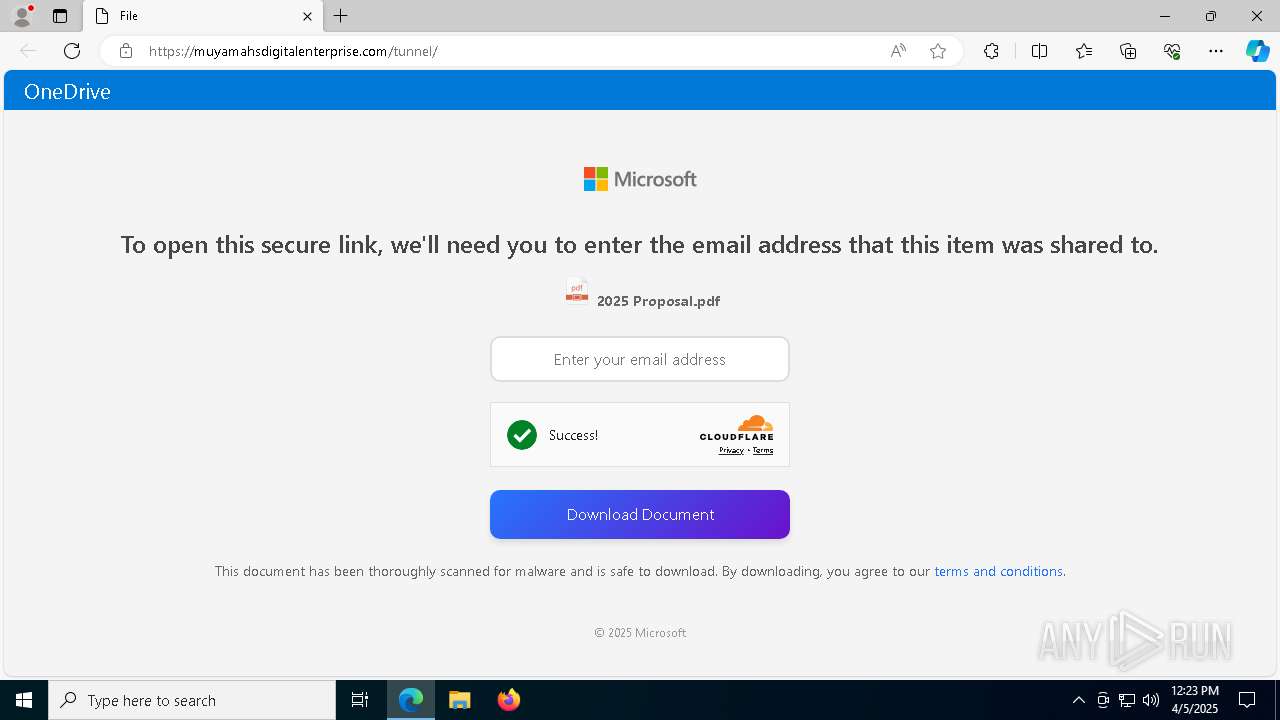
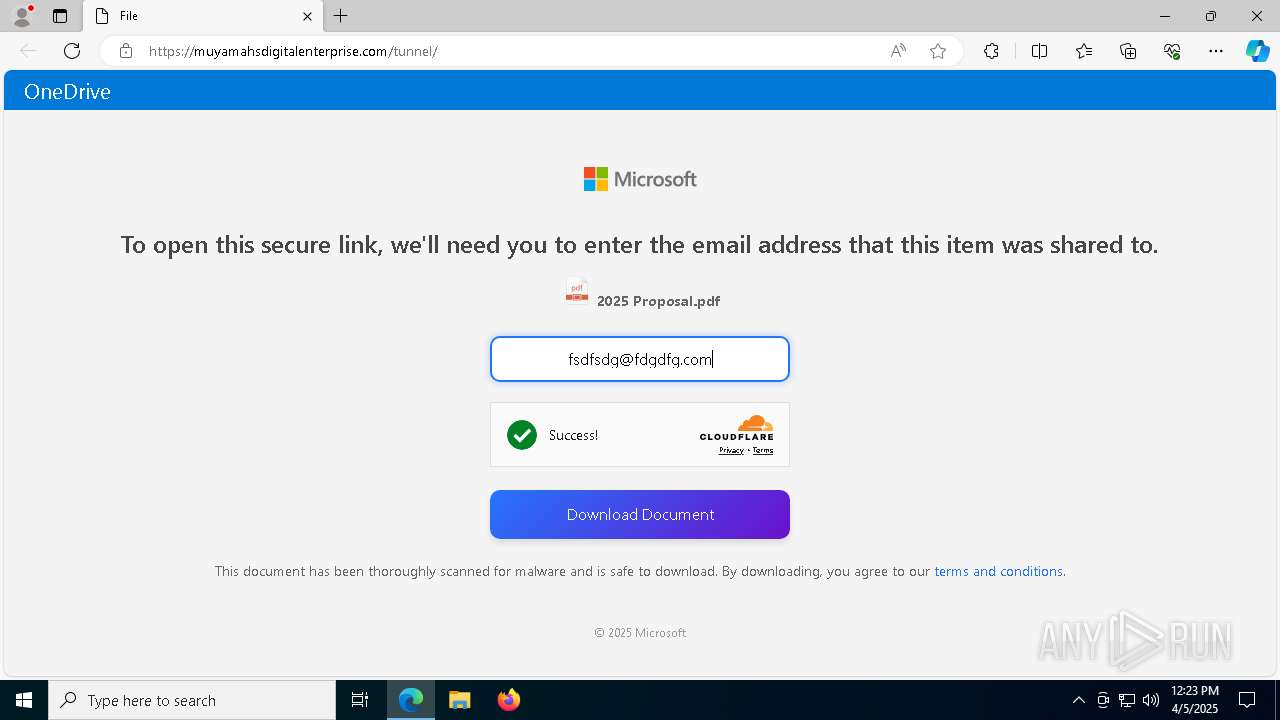
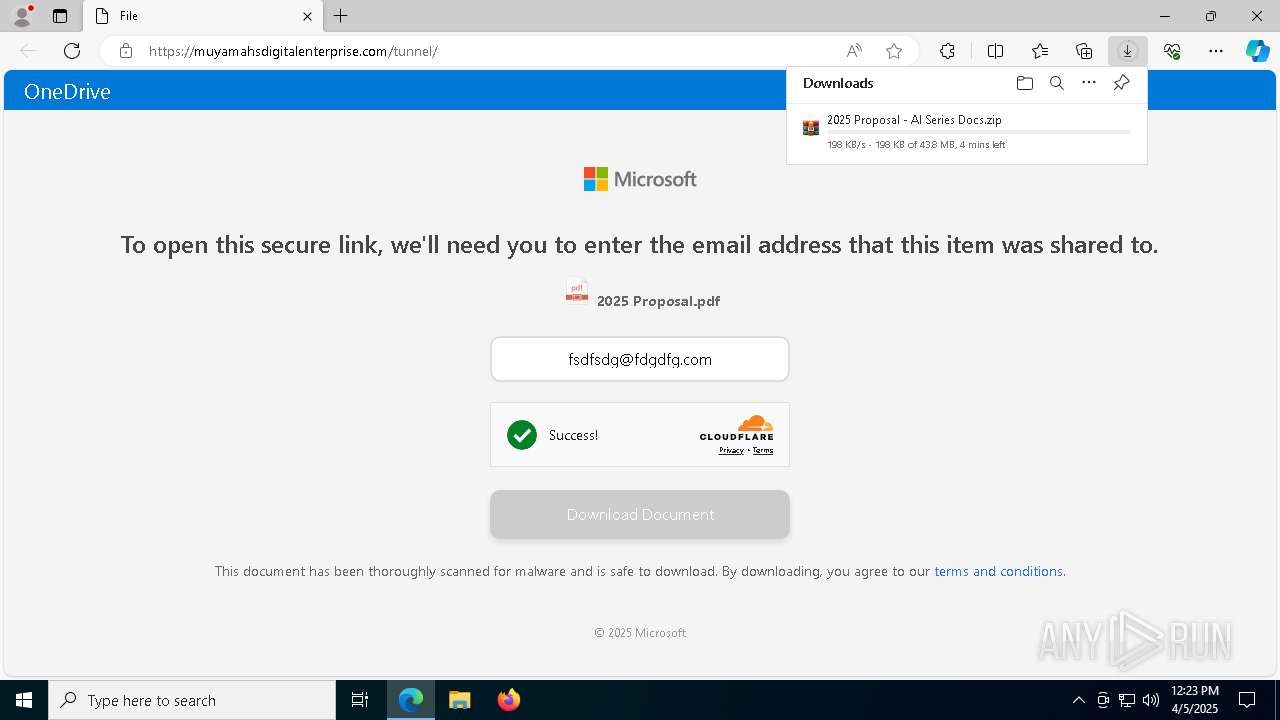
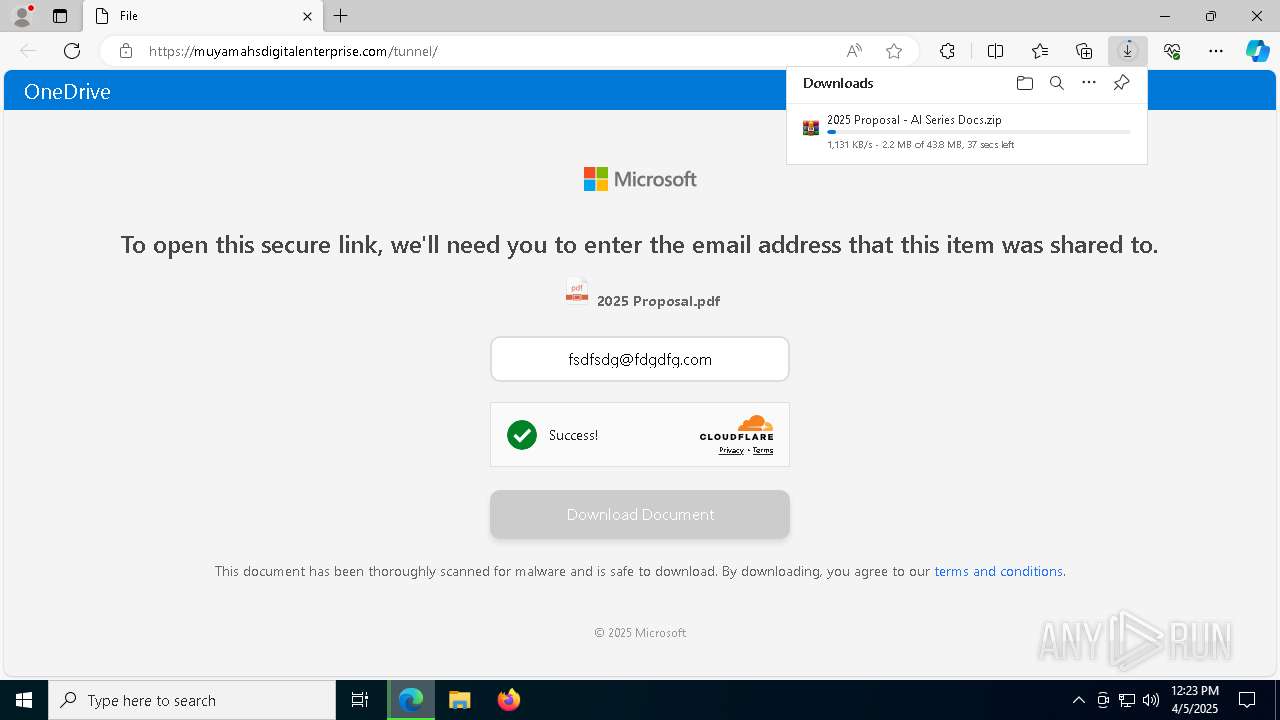
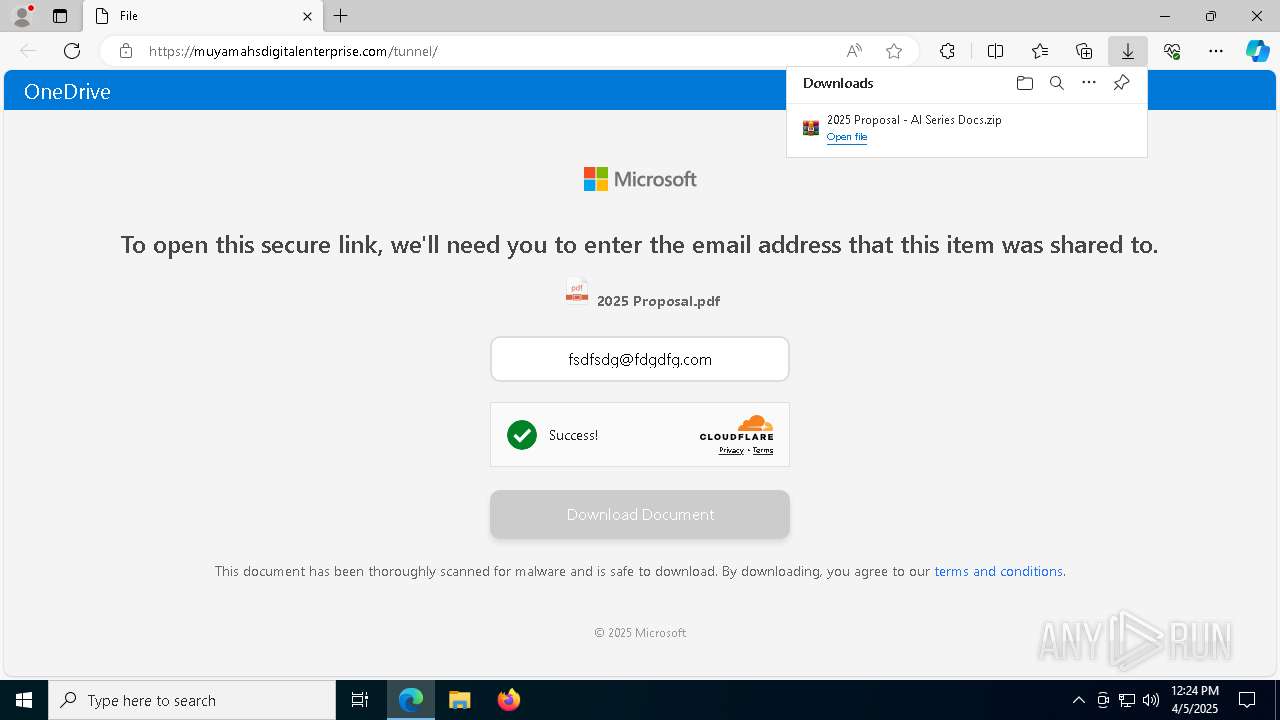
| URL: | https://www.google.dk/url?q=https%3A%2F%2Fmuyamahsdigitalenterprise.com%2Ftunnel%2F&sa=D&sntz=1&usg=AOvVaw1GDc4i398Z_d48kSBaZzBJ |
| Full analysis: | https://app.any.run/tasks/835a5105-547a-4c0d-8fa5-92b65089f10b |
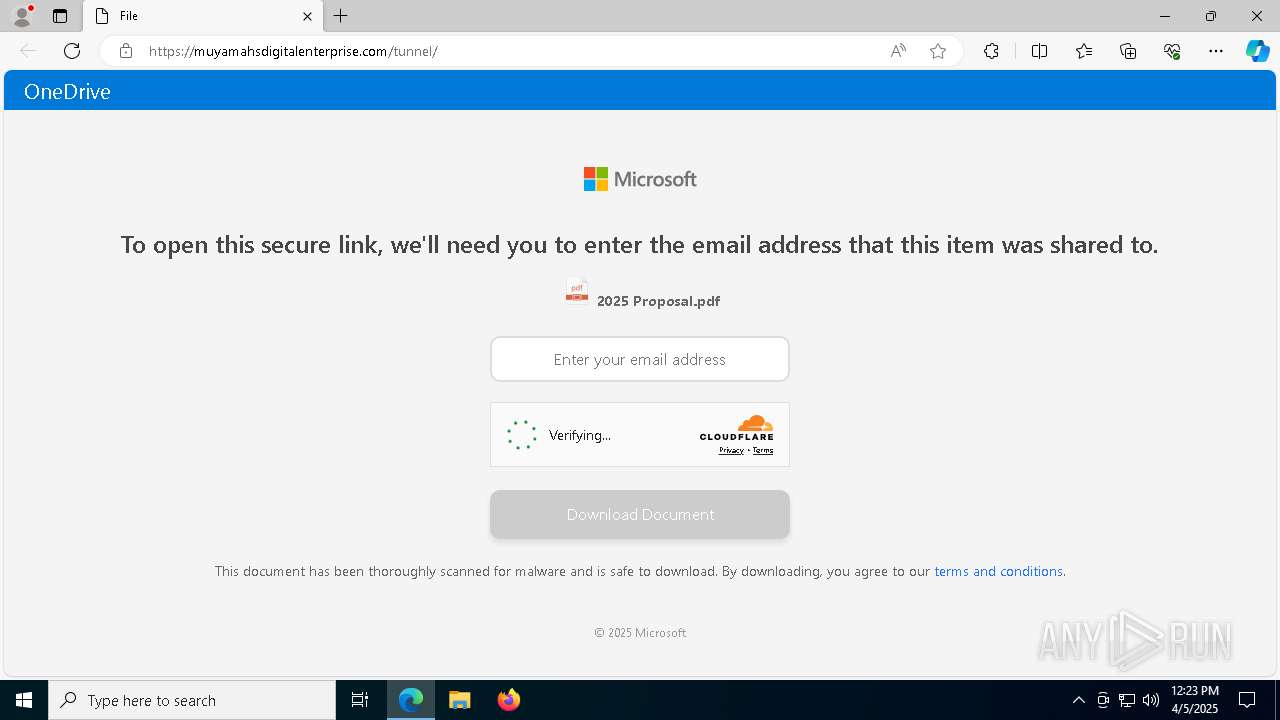
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | April 05, 2025, 12:22:48 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | F6023B3C5FEF99E66D431731A90A6C58 |
| SHA1: | AC7C9F588F289C8622DF4ACE0EDBDBA1C3D0AD8E |
| SHA256: | F21BBBD4AC739E9D5E236BE6D49E687CB191FB7C52AA433F9D72F146372B76C6 |
| SSDEEP: | 3:N8DSLIwZfgBWCXjuhf6vWA2A9eLsxx8LfDCJS7hyXO2WPv:2OLIwZfazuhfkWhuxKzDCJS72O20 |
MALICIOUS
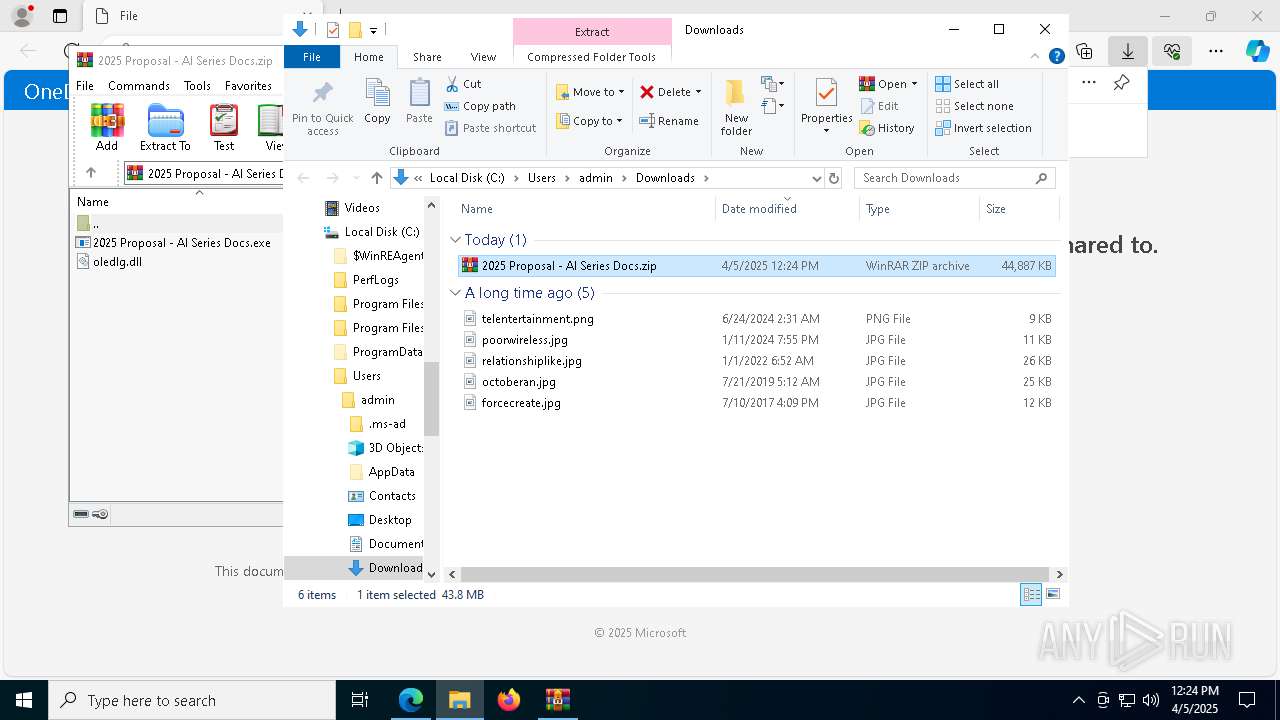
Starts Visual C# compiler
- 2025 Proposal - AI Series Docs.exe (PID: 1812)
ASYNCRAT has been detected (SURICATA)
- csc.exe (PID: 6112)
DISCORDGRABBER has been detected (YARA)
- csc.exe (PID: 6112)
STORMKITTY has been detected (YARA)
- csc.exe (PID: 6112)
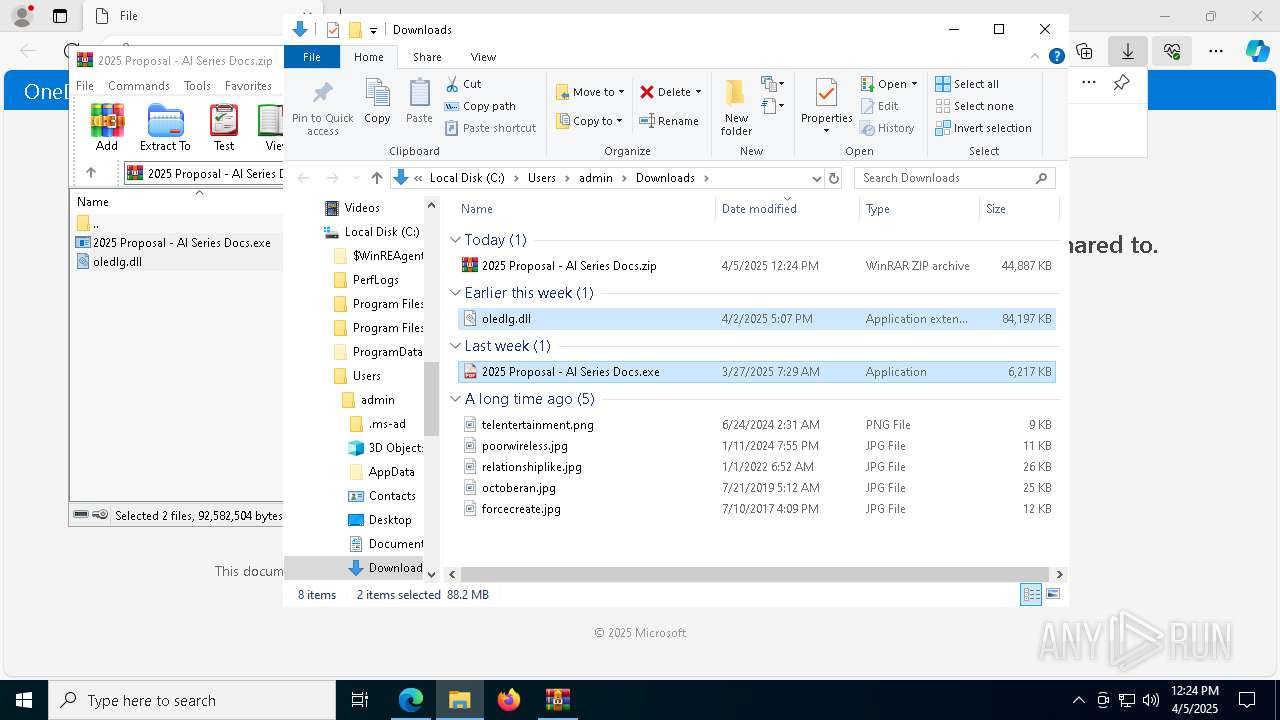
Changes the autorun value in the registry
- reg.exe (PID: 1116)
SUSPICIOUS
There is functionality for taking screenshot (YARA)
- 2025 Proposal - AI Series Docs.exe (PID: 1812)
Contacting a server suspected of hosting an CnC
- csc.exe (PID: 6112)
Starts CMD.EXE for commands execution
- 2025 Proposal - AI Series Docs.exe (PID: 1812)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 4028)
Found regular expressions for crypto-addresses (YARA)
- csc.exe (PID: 6112)
Multiple wallet extension IDs have been found
- csc.exe (PID: 6112)
Searches for installed software
- csc.exe (PID: 6112)
Possible usage of Discord/Telegram API has been detected (YARA)
- csc.exe (PID: 6112)
Connects to unusual port
- csc.exe (PID: 6112)
INFO
Reads Environment values
- identity_helper.exe (PID: 4408)
Reads the computer name
- identity_helper.exe (PID: 4408)
- csc.exe (PID: 6112)
Reads the software policy settings
- slui.exe (PID: 4724)
- slui.exe (PID: 2904)
- csc.exe (PID: 6112)
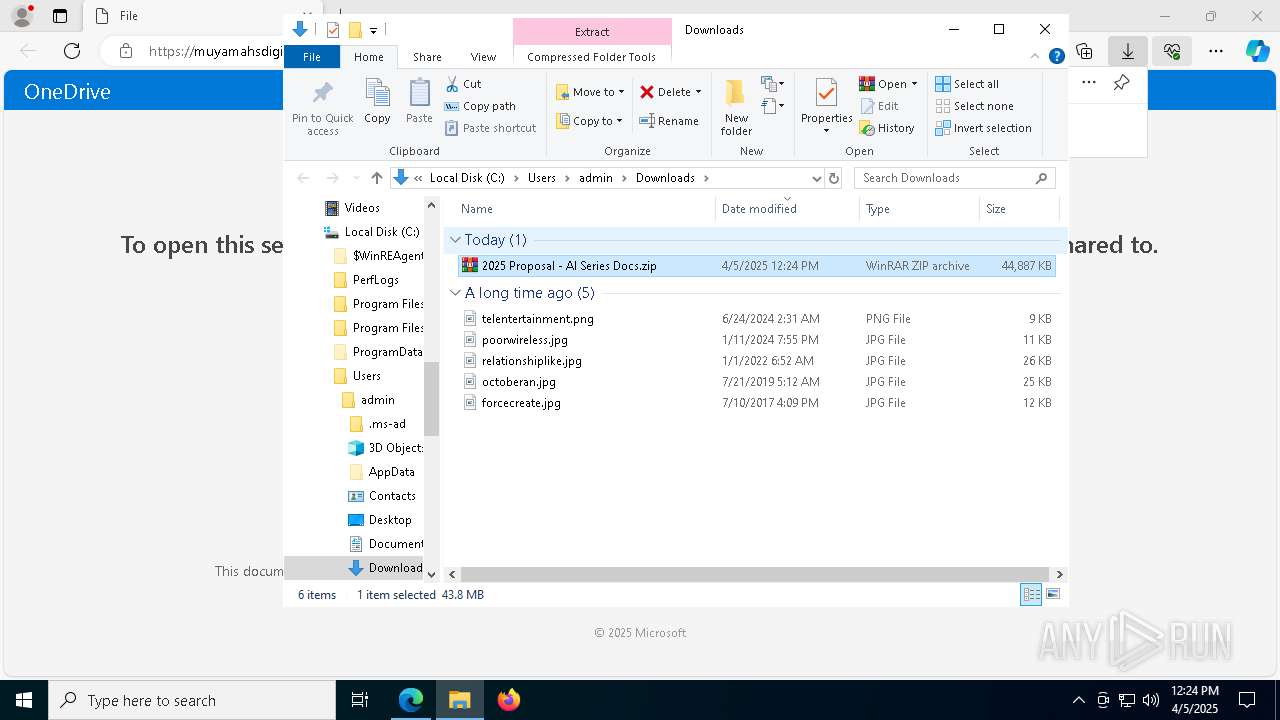
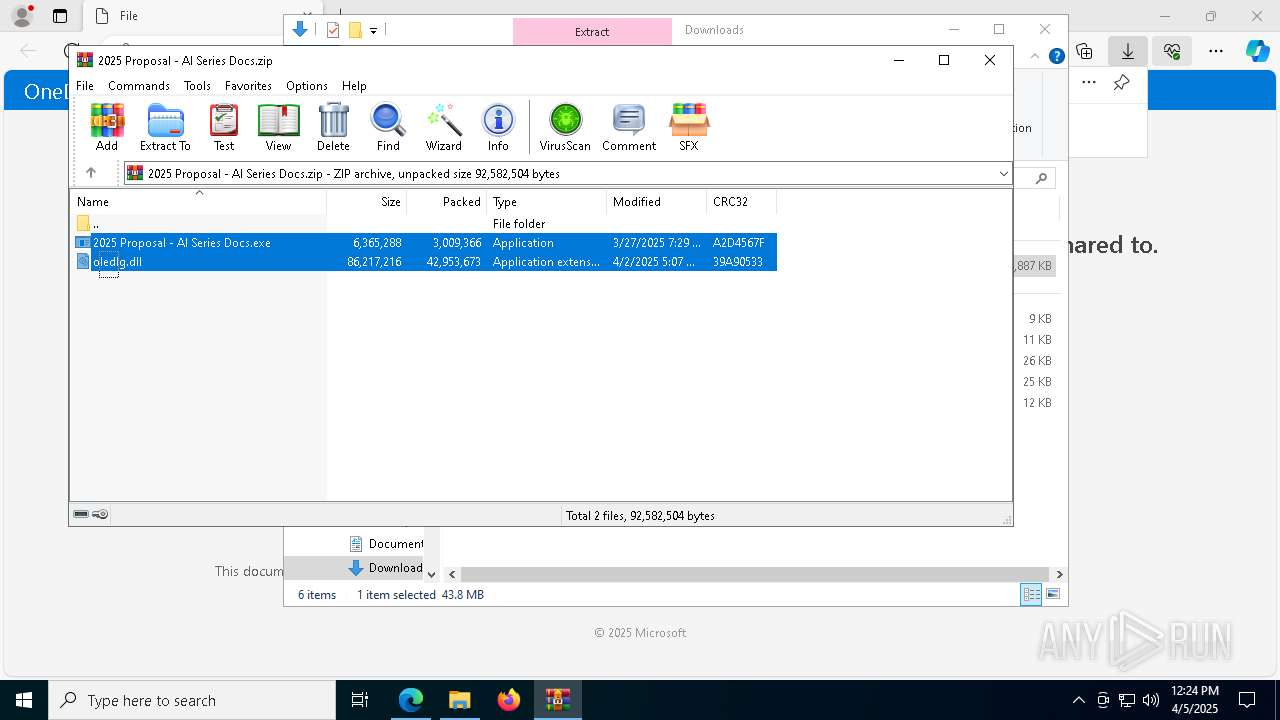
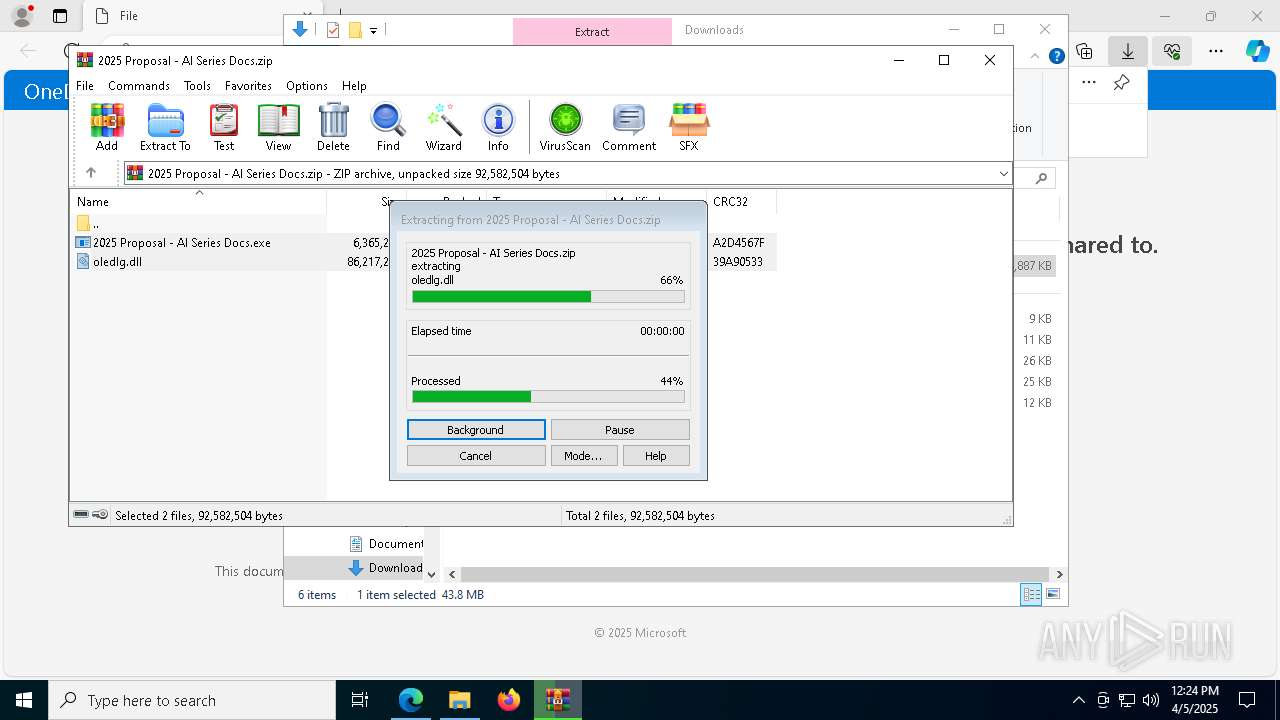
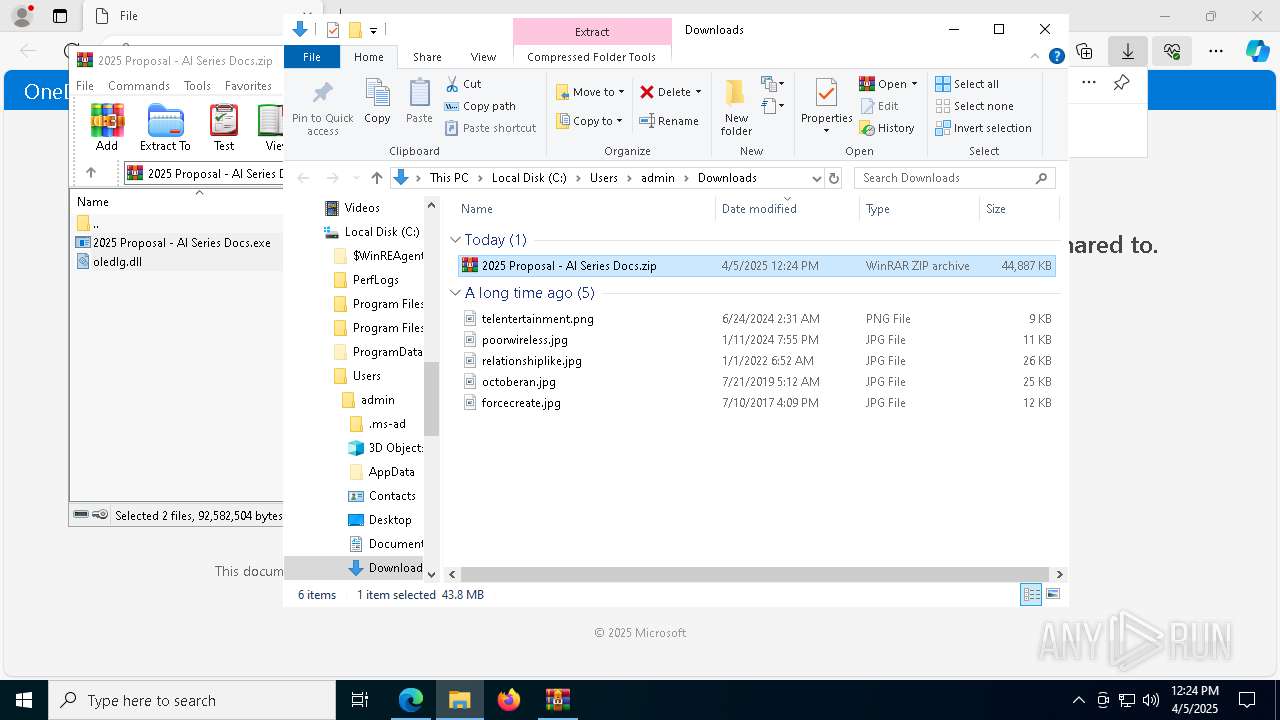
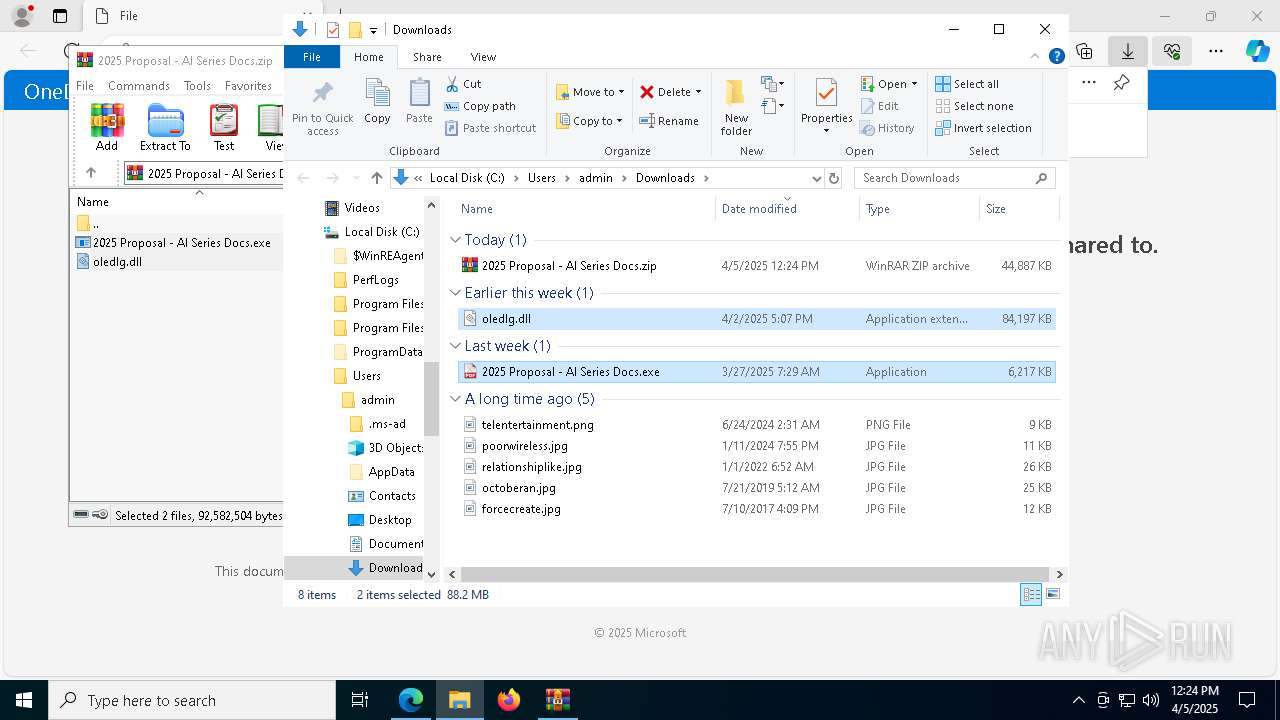
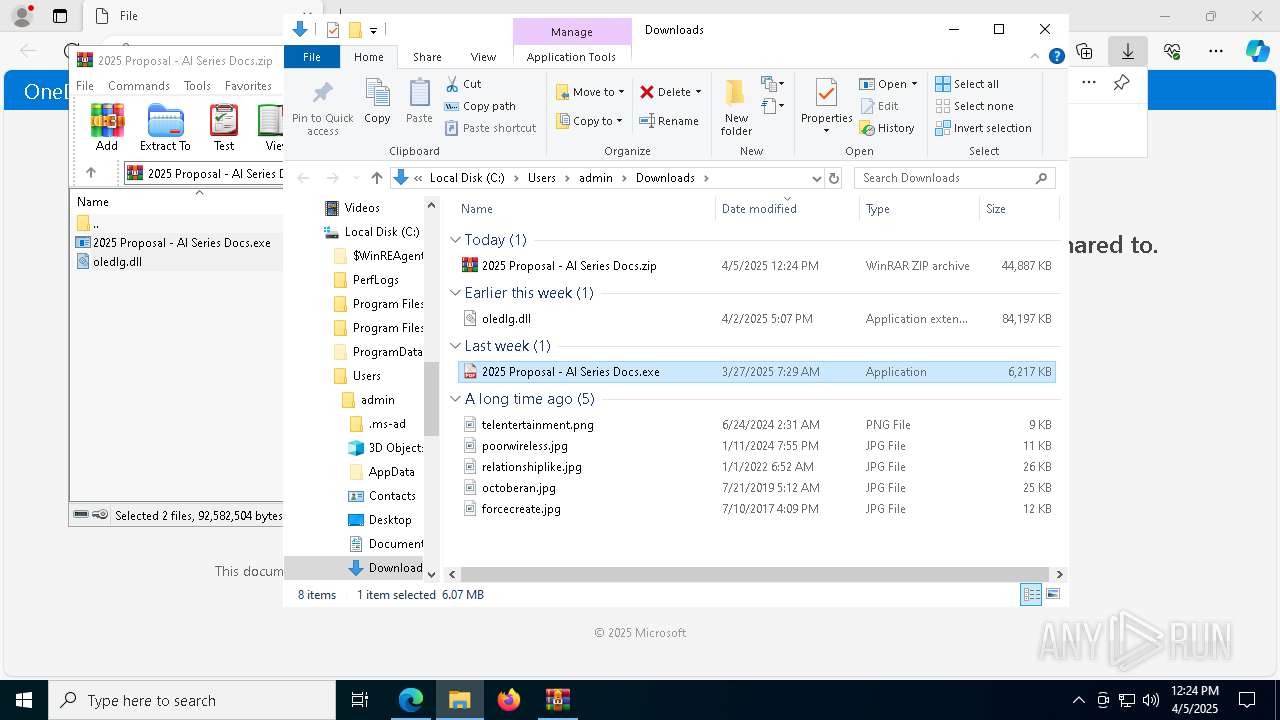
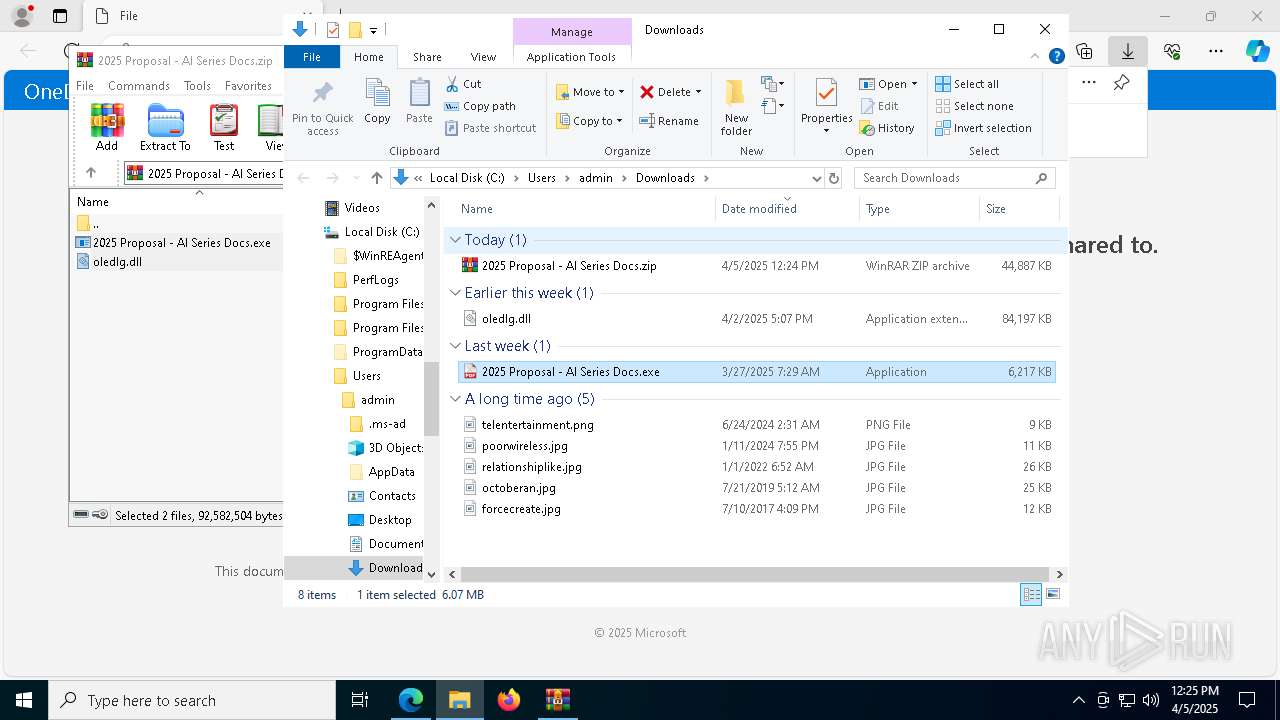
Autorun file from Downloads
- msedge.exe (PID: 7020)
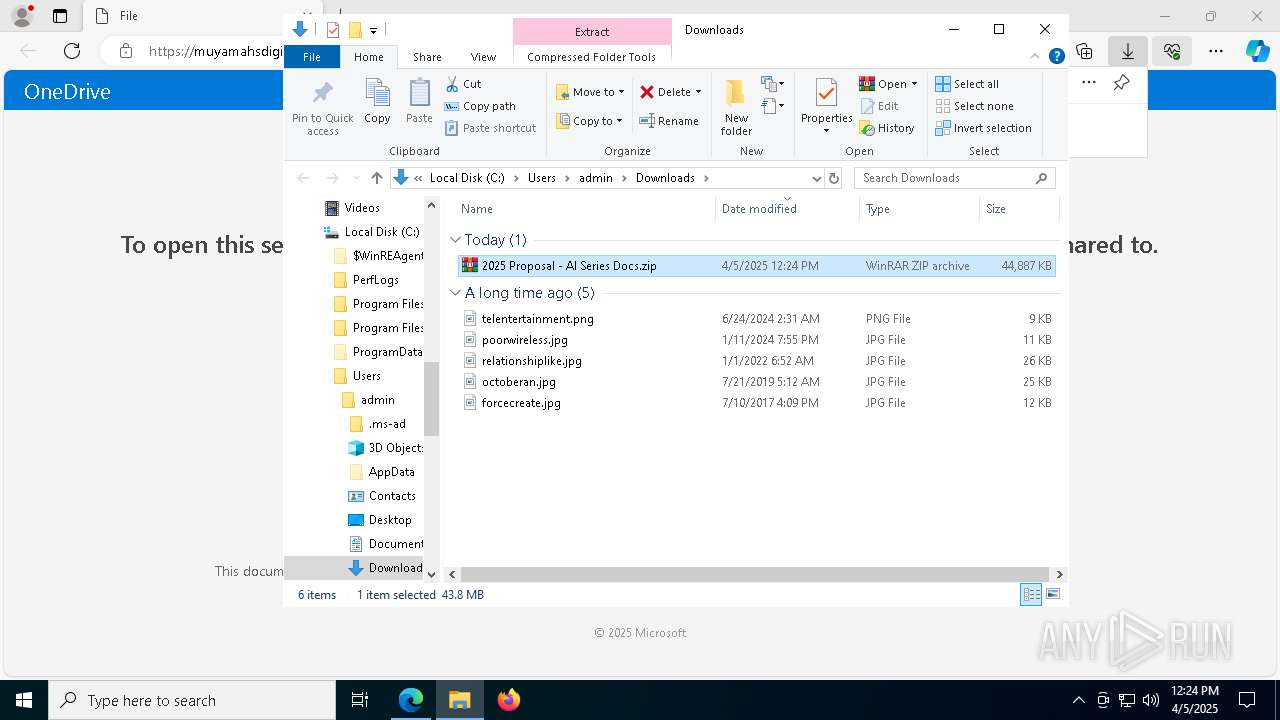
Executable content was dropped or overwritten
- msedge.exe (PID: 7236)
- WinRAR.exe (PID: 8088)
Checks supported languages
- identity_helper.exe (PID: 4408)
- 2025 Proposal - AI Series Docs.exe (PID: 1812)
- csc.exe (PID: 6112)
The sample compiled with english language support
- WinRAR.exe (PID: 8088)
- msedge.exe (PID: 7236)
Checks proxy server information
- slui.exe (PID: 2904)
Manual execution by a user
- 2025 Proposal - AI Series Docs.exe (PID: 1812)
- WinRAR.exe (PID: 8088)
Application launched itself
- msedge.exe (PID: 7244)
Reads the machine GUID from the registry
- csc.exe (PID: 6112)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
StormKitty
(PID) Process(6112) csc.exe
C2 (1)101.99.94.33
Ports (1)4449
VersionRAT + hVNC 6.0.7
Options
AutoRunfalse
Mutexlrienrnhpv
InstallFolder%PreLoadSQLite_TargetFramework%
Certificates
Cert1MIICLTCCAZagAwIBAgIVALQj9s5wHvTgWhgHMbeJ9yDXgc4hMA0GCSqGSIb3DQEBDQUAMGExFDASBgNVBAMMC1BsdW5nZVNxdWFkMRIwEAYDVQQLDAlhbGV4ZWlrdW4xGzAZBgNVBAoMElZlbm9tIEJ5IGFsZXhlaWt1bjELMAkGA1UEBwwCU0gxCzAJBgNVBAYTAkNOMB4XDTI0MDYyMDAyNTMxNloXDTM1MDMzMDAyNTMxNlowEDEOMAwGA1UEAwwFVmVub20wgZ8wDQYJKoZIhvcNAQEBBQADgY0AMIGJ...
Server_SignatureaIXE/nw86bhxZFJLk3k0upj7PljLF3lD1woH2SyjqMOD8g0QX4HrtUegJNqkyEiJUp5AAr0nISxT2aqA+yEZ+kZt9v3LHvLjau3AHFg4zlSGlxSomhc48arIlBVTaGH7jd4l4klIvznKRYXF8R91LiRMh7/t+4lmpYR5PNLIGaA=
Keys
AES7f9d42be0de797d2dbbde01035e474ccc362dd2f9412e7759f3caf07b97c1eaa
SaltVenomRATByVenom
ims-api
(PID) Process(6112) csc.exe
Discord-Webhook-Tokens (1)1016614786533969920/fMJOOjA1pZqjV8_s0JC86KN9Fa0FeGPEHaEak8WTADC18s5Xnk3vl2YBdVD37L0qTWnM
Discord-Info-Links
1016614786533969920/fMJOOjA1pZqjV8_s0JC86KN9Fa0FeGPEHaEak8WTADC18s5Xnk3vl2YBdVD37L0qTWnM
Get Webhook Infohttps://discord.com/api/webhooks/1016614786533969920/fMJOOjA1pZqjV8_s0JC86KN9Fa0FeGPEHaEak8WTADC18s5Xnk3vl2YBdVD37L0qTWnM
Total processes
213
Monitored processes
74
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 456 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=8096 --field-trial-handle=2080,i,8413910997730232782,17266824309635205914,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 456 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6800 --field-trial-handle=2080,i,8413910997730232782,17266824309635205914,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 960 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1056 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5924 --field-trial-handle=2080,i,8413910997730232782,17266824309635205914,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1056 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=8016 --field-trial-handle=2080,i,8413910997730232782,17266824309635205914,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1116 | reg add "HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\Run" /v "Cortex XDR Versus" /t REG_SZ /d "rundll32.exe C:\Users\admin\Documents\Volternon0549303.dll",EntryPoint /f | C:\Windows\SysWOW64\reg.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --onnx-enabled-for-ee --no-appcompat-clear --mojo-platform-channel-handle=6052 --field-trial-handle=2080,i,8413910997730232782,17266824309635205914,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1184 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=31 --mojo-platform-channel-handle=6280 --field-trial-handle=2080,i,8413910997730232782,17266824309635205914,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1672 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3940 --field-trial-handle=2080,i,8413910997730232782,17266824309635205914,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1672 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6604 --field-trial-handle=2080,i,8413910997730232782,17266824309635205914,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
12 745
Read events
12 681
Write events
46
Delete events
18
Modification events
| (PID) Process: | (5072) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5072) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5072) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5072) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (5072) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (5072) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (7244) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7244) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7244) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7244) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
16
Suspicious files
565
Text files
98
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7244 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10be60.TMP | — | |
MD5:— | SHA256:— | |||
| 7244 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7244 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10be8f.TMP | — | |
MD5:— | SHA256:— | |||
| 7244 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7244 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10be9f.TMP | — | |
MD5:— | SHA256:— | |||
| 7244 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7244 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10bebe.TMP | — | |
MD5:— | SHA256:— | |||
| 7244 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10becd.TMP | — | |
MD5:— | SHA256:— | |||
| 7244 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7244 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
54
TCP/UDP connections
88
DNS requests
104
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.39:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5308 | svchost.exe | GET | 206 | 208.89.74.17:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1744052663&P2=404&P3=2&P4=E22vKB9dqpX%2fS4fjNT%2fTW4781dAnp0uF2I7d3S17e%2bcCWWOQ8zGaXbAzGJ%2fl%2bAEDYVGi0PKff6kqW3xebjt3QA%3d%3d | unknown | — | — | whitelisted |
5308 | svchost.exe | GET | 206 | 208.89.74.17:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1744052663&P2=404&P3=2&P4=E22vKB9dqpX%2fS4fjNT%2fTW4781dAnp0uF2I7d3S17e%2bcCWWOQ8zGaXbAzGJ%2fl%2bAEDYVGi0PKff6kqW3xebjt3QA%3d%3d | unknown | — | — | whitelisted |
5308 | svchost.exe | GET | 206 | 208.89.74.17:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1744052663&P2=404&P3=2&P4=E22vKB9dqpX%2fS4fjNT%2fTW4781dAnp0uF2I7d3S17e%2bcCWWOQ8zGaXbAzGJ%2fl%2bAEDYVGi0PKff6kqW3xebjt3QA%3d%3d | unknown | — | — | whitelisted |
5308 | svchost.exe | GET | 206 | 208.89.74.17:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1744052663&P2=404&P3=2&P4=E22vKB9dqpX%2fS4fjNT%2fTW4781dAnp0uF2I7d3S17e%2bcCWWOQ8zGaXbAzGJ%2fl%2bAEDYVGi0PKff6kqW3xebjt3QA%3d%3d | unknown | — | — | whitelisted |
5308 | svchost.exe | HEAD | 200 | 208.89.74.17:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1744052663&P2=404&P3=2&P4=E22vKB9dqpX%2fS4fjNT%2fTW4781dAnp0uF2I7d3S17e%2bcCWWOQ8zGaXbAzGJ%2fl%2bAEDYVGi0PKff6kqW3xebjt3QA%3d%3d | unknown | — | — | whitelisted |
5308 | svchost.exe | GET | 206 | 208.89.74.17:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1744052663&P2=404&P3=2&P4=E22vKB9dqpX%2fS4fjNT%2fTW4781dAnp0uF2I7d3S17e%2bcCWWOQ8zGaXbAzGJ%2fl%2bAEDYVGi0PKff6kqW3xebjt3QA%3d%3d | unknown | — | — | whitelisted |
5308 | svchost.exe | GET | 206 | 208.89.74.17:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1744052663&P2=404&P3=2&P4=E22vKB9dqpX%2fS4fjNT%2fTW4781dAnp0uF2I7d3S17e%2bcCWWOQ8zGaXbAzGJ%2fl%2bAEDYVGi0PKff6kqW3xebjt3QA%3d%3d | unknown | — | — | whitelisted |
6436 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6436 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5328 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.39:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7244 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7500 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7500 | msedge.exe | 216.58.206.35:443 | www.google.dk | GOOGLE | US | whitelisted |
7500 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.google.dk |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
client.wns.windows.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
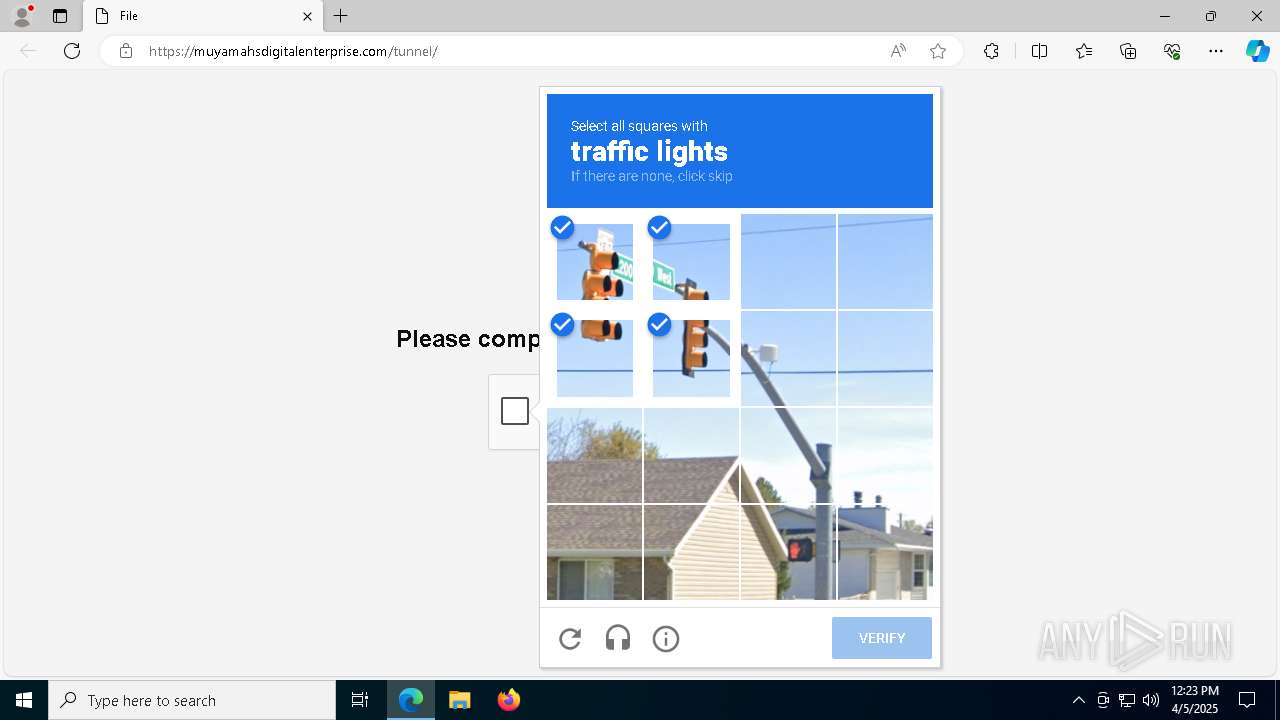
7500 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
7500 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
6112 | csc.exe | Domain Observed Used for C2 Detected | REMOTE [ANY.RUN] Possible AsyncRAT SSL Certificate |