| File name: | PO #51107.DOC |
| Full analysis: | https://app.any.run/tasks/a5771796-bf32-4c0f-bdaf-c15a04d126e4 |
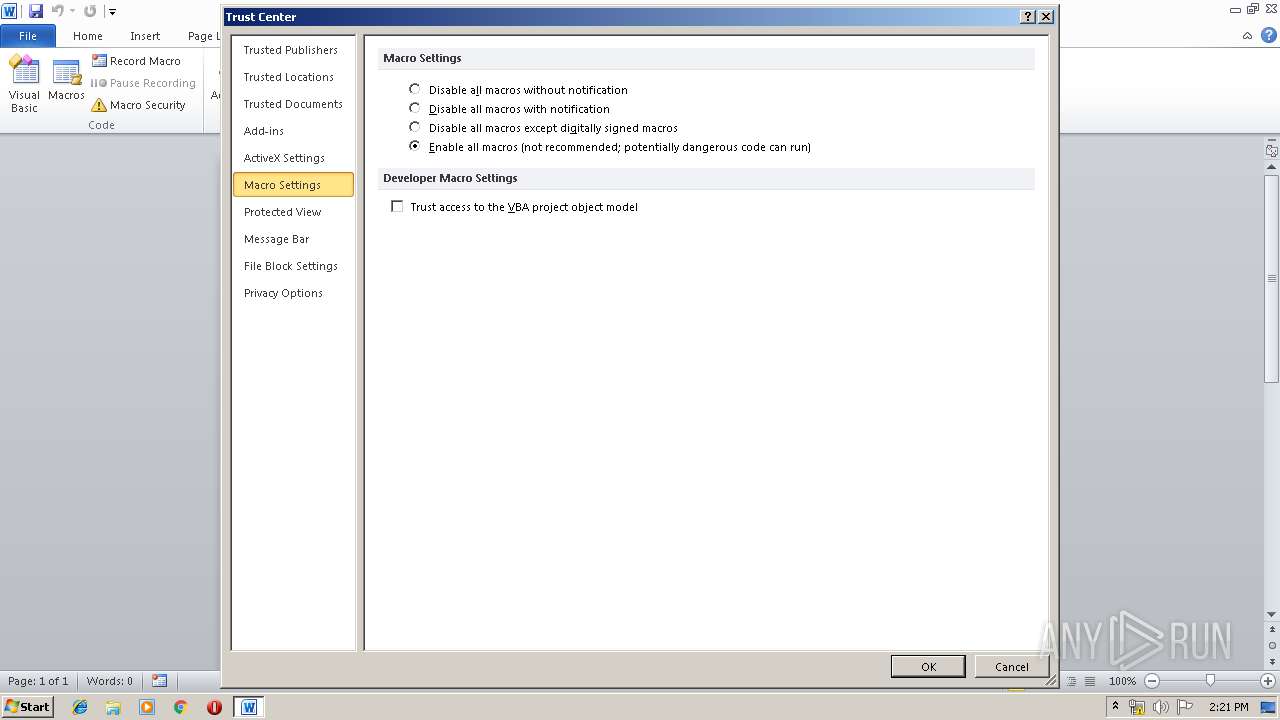
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | April 23, 2019, 13:19:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/rtf |
| File info: | Rich Text Format data, version 1, unknown character set |
| MD5: | 7C50F5B1D58E29651F84530AAAD7FA1B |
| SHA1: | 2A34998A349984BAD6C3C050DCD2652914AC7EB1 |
| SHA256: | F145EB19CBF465F59AC69B40299D7AA43FFF6DD26FF24303DAC6C12D3799B30B |
| SSDEEP: | 1536:qs0/ETrxWaVbFCfXyOrETqx8B7nFCfXyDMETmxulTQFCfXyWUbEt3:q7/cdgzrc+jWMcym3xB |
MALICIOUS
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 2372)
- EXCEL.EXE (PID: 4064)
- EXCEL.EXE (PID: 3260)
Uses SVCHOST.EXE for hidden code execution
- explorer.exe (PID: 252)
Application was dropped or rewritten from another process
- udn4.exe (PID: 3388)
- udn4.exe (PID: 3196)
- udn4.exe (PID: 3236)
- udn4.exe (PID: 2240)
- udn4.exe (PID: 3348)
- udn4.exe (PID: 2872)
Executable content was dropped or overwritten
- EXCEL.EXE (PID: 3260)
Formbook was detected
- svchost.exe (PID: 3880)
- Firefox.exe (PID: 2696)
FORMBOOK was detected
- explorer.exe (PID: 252)
Connects to CnC server
- explorer.exe (PID: 252)
Changes the autorun value in the registry
- svchost.exe (PID: 3880)
Actions looks like stealing of personal data
- svchost.exe (PID: 3880)
Stealing of credential data
- svchost.exe (PID: 3880)
SUSPICIOUS
Application launched itself
- udn4.exe (PID: 3388)
- udn4.exe (PID: 3236)
- udn4.exe (PID: 3348)
Starts CMD.EXE for commands execution
- svchost.exe (PID: 3880)
Loads DLL from Mozilla Firefox
- svchost.exe (PID: 3880)
Creates files in the user directory
- svchost.exe (PID: 3880)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 3260)
- EXCEL.EXE (PID: 2372)
- EXCEL.EXE (PID: 4064)
- excelcnv.exe (PID: 2232)
- WINWORD.EXE (PID: 2800)
Starts Microsoft Office Application
- explorer.exe (PID: 252)
Creates files in the user directory
- WINWORD.EXE (PID: 2800)
- Firefox.exe (PID: 2696)
Reads settings of System Certificates
- WINWORD.EXE (PID: 2800)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rtf | | | Rich Text Format (100) |
|---|
EXIF
RTF
| LastModifiedBy: | Administrator |
|---|---|
| CreateDate: | 2019:04:18 22:26:00 |
| ModifyDate: | 2019:04:18 22:26:00 |
| RevisionNumber: | 1 |
| TotalEditTime: | - |
| Pages: | 1 |
| Words: | 11 |
| Characters: | 68 |
| CharactersWithSpaces: | 78 |
| InternalVersionNumber: | 101 |
Total processes
48
Monitored processes
18
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2196 | "C:\Windows\System32\raserver.exe" | C:\Windows\System32\raserver.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Remote Assistance COM Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2232 | "C:\Program Files\Microsoft Office\Office14\excelcnv.exe" -Embedding | C:\Program Files\Microsoft Office\Office14\excelcnv.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2240 | "C:\Users\admin\AppData\Local\Temp\udn4.exe" | C:\Users\admin\AppData\Local\Temp\udn4.exe | — | udn4.exe | |||||||||||
User: admin Company: dedecoration Integrity Level: MEDIUM Description: gangster's Exit code: 0 Version: 5.5.8.8 Modules
| |||||||||||||||
| 2372 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2696 | "C:\Program Files\Mozilla Firefox\Firefox.exe" | C:\Program Files\Mozilla Firefox\Firefox.exe | svchost.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
| 2800 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\PO #51107.DOC" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2872 | "C:\Users\admin\AppData\Local\Temp\udn4.exe" | C:\Users\admin\AppData\Local\Temp\udn4.exe | — | udn4.exe | |||||||||||
User: admin Company: dedecoration Integrity Level: MEDIUM Description: gangster's Exit code: 0 Version: 5.5.8.8 Modules
| |||||||||||||||
| 3032 | /c del "C:\Users\admin\AppData\Local\Temp\udn4.exe" | C:\Windows\System32\cmd.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3196 | "C:\Users\admin\AppData\Local\Temp\udn4.exe" | C:\Users\admin\AppData\Local\Temp\udn4.exe | — | udn4.exe | |||||||||||
User: admin Company: dedecoration Integrity Level: MEDIUM Description: gangster's Exit code: 0 Version: 5.5.8.8 Modules
| |||||||||||||||
Total events
18 144
Read events
9 301
Write events
8 823
Delete events
20
Modification events
| (PID) Process: | (2800) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | yp= |
Value: 79703D00F00A0000010000000000000000000000 | |||
| (PID) Process: | (2800) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2800) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2800) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1318518814 | |||
| (PID) Process: | (2800) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1318518936 | |||
| (PID) Process: | (2800) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1318518937 | |||
| (PID) Process: | (2800) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: F00A0000E467023CD7F9D40100000000 | |||
| (PID) Process: | (2800) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | sq= |
Value: 73713D00F00A000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2800) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | sq= |
Value: 73713D00F00A000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2800) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
83
Text files
2
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2800 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRFC79.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3260 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR39D.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2372 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR18EA.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 4064 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR1F14.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2232 | excelcnv.exe | C:\Users\admin\AppData\Local\Temp\CVR281D.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2232 | excelcnv.exe | C:\Users\admin\AppData\Local\Temp\~DFA7AB22C9323B000B.TMP | — | |
MD5:— | SHA256:— | |||
| 2800 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF6989E5A121C3264C.TMP | — | |
MD5:— | SHA256:— | |||
| 2232 | excelcnv.exe | C:\Users\admin\AppData\Local\Temp\~DF25AA8EDB2CDFF171.TMP | — | |
MD5:— | SHA256:— | |||
| 2800 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF0C05C9A49470476B.TMP | — | |
MD5:— | SHA256:— | |||
| 2232 | excelcnv.exe | C:\Users\admin\AppData\Local\Temp\~DF89C717040B2E57EF.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
30
DNS requests
13
Threats
52
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
252 | explorer.exe | GET | — | 159.8.40.54:80 | http://www.switzerlandgmbh.com/br/?X2sDANaX=9iUCUuDjw2iNXjIMbYd5SHqFUb7LPDvklatIrGE5L3o/OEsA1t3YiwmlIMmj4uiGqJsycA==&blt=UVhLQHT85TvhG | NL | — | — | malicious |
2372 | EXCEL.EXE | GET | 304 | 45.67.14.61:80 | http://45.67.14.61/G/609118 | unknown | — | — | suspicious |
4064 | EXCEL.EXE | GET | 304 | 45.67.14.61:80 | http://45.67.14.61/G/609118 | unknown | — | — | suspicious |
252 | explorer.exe | GET | — | 192.0.78.25:80 | http://www.semmelhacklab.com/br/?X2sDANaX=aXb0V0GXAtQKP7lgdrX2HUjL1w8HhXkKzAhz9wDe3V/qcCd/Wvu5oh2CpqEt4u8GBSPCXw==&blt=UVhLQHT85TvhG&sql=1 | US | — | — | malicious |
252 | explorer.exe | GET | 301 | 193.254.184.90:80 | http://www.hypervitalpart.com/br/?X2sDANaX=f3L8EFTNQTET4672kd4R52Q+zGXO0dMQLCkmTDqUcdjfVwNvPfDosmCH0aszA3IH82R8/A==&blt=UVhLQHT85TvhG | DE | — | — | malicious |
252 | explorer.exe | POST | — | 185.26.156.62:80 | http://www.desktopweasel.com/br/ | DE | — | — | malicious |
2800 | WINWORD.EXE | GET | 200 | 52.109.32.27:80 | http://office14client.microsoft.com/config14?UILCID=1033&CLCID=1033&ILCID=1033&HelpLCID=1033&App={019C826E-445A-4649-A5B0-0BF08FCC4EEE}&build=14.0.6023 | GB | xml | 1.99 Kb | whitelisted |
252 | explorer.exe | POST | — | 199.192.24.227:80 | http://www.butnir.com/br/ | US | — | — | malicious |
252 | explorer.exe | POST | 404 | 199.192.24.227:80 | http://www.butnir.com/br/ | US | html | 290 b | malicious |
252 | explorer.exe | POST | — | 85.208.112.80:80 | http://www.yagesj.com/br/ | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3260 | EXCEL.EXE | 45.67.14.61:80 | — | — | — | suspicious |
2372 | EXCEL.EXE | 45.67.14.61:80 | — | — | — | suspicious |
4064 | EXCEL.EXE | 45.67.14.61:80 | — | — | — | suspicious |
— | — | 193.254.184.90:80 | www.hypervitalpart.com | Vautron Rechenzentrum AG | DE | malicious |
252 | explorer.exe | 192.0.78.25:80 | www.semmelhacklab.com | Automattic, Inc | US | malicious |
252 | explorer.exe | 185.26.156.62:80 | www.desktopweasel.com | uvensys GmbH | DE | malicious |
2800 | WINWORD.EXE | 52.109.32.27:80 | office14client.microsoft.com | Microsoft Corporation | GB | whitelisted |
2800 | WINWORD.EXE | 52.109.120.29:443 | rr.office.microsoft.com | Microsoft Corporation | HK | whitelisted |
252 | explorer.exe | 199.192.24.227:80 | www.butnir.com | — | US | malicious |
252 | explorer.exe | 85.208.112.80:80 | www.yagesj.com | — | — | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.hypervitalpart.com |
| malicious |
www.semmelhacklab.com |
| malicious |
www.desktopweasel.com |
| malicious |
office14client.microsoft.com |
| whitelisted |
rr.office.microsoft.com |
| whitelisted |
www.butnir.com |
| malicious |
www.yagesj.com |
| malicious |
www.wwwjinsha694.com |
| unknown |
www.switzerlandgmbh.com |
| malicious |
www.hkobgv.info |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3260 | EXCEL.EXE | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |
3260 | EXCEL.EXE | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from dotted Quad by MSXMLHTTP M1 |
3260 | EXCEL.EXE | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3260 | EXCEL.EXE | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from dotted Quad by MSXMLHTTP M2 |
3260 | EXCEL.EXE | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from MSXMLHTTP non-exe extension M2 |
3260 | EXCEL.EXE | Potentially Bad Traffic | ET INFO SUSPICIOUS Dotted Quad Host MZ Response |
3260 | EXCEL.EXE | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
2372 | EXCEL.EXE | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |
4064 | EXCEL.EXE | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |
252 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
19 ETPRO signatures available at the full report
Process | Message |
|---|---|
udn4.exe | User32.dll |
udn4.exe | User32.dll |
udn4.exe | User32.dll |
udn4.exe | User32.dll |
udn4.exe | User32.dll |
udn4.exe | User32.dll |
udn4.exe | User32.dll |
udn4.exe | User32.dll |
udn4.exe | User32.dll |
udn4.exe | User32.dll |